Abstract
Clinics and hospitals have already adopted more technological resources to provide a faster and more precise diagnostic for patients, health care providers, and institutes of medicine. Security issues get more and more important in medical services via communication resources such as Wireless-Fidelity (Wi-Fi), third generation of mobile telecommunications technology (3G), and other mobile devices to connect medical systems from anywhere. Furthermore, cloud-based medical systems allow users to access archived medical images from anywhere. In order to protect medical images, lossless data hiding methods are efficient and easy techniques. In this paper, we present a data hiding of two-tier medical images based on histogram shifting of prediction errors. The median histogram shifting technique and prediction error schemes as the two-tier hiding have high capacity and PSNR in 16-bit medical images.
Introduction
Mobile and digital media are getting more and more popular on Internet and cloud services. In social networks, many multi-media such as images, videos, and audios are produced by different aspects of the human activities. Moreover, telemedicine applies telecommunication and information technology to offer clinical health care from a distance. In critical care and emergency situations, health informatics, medical, and imaging data are transmitted from doctors and healthcare professionals to discuss patient issues. Therefore, E-Healthcare data management plays a crucial role in modern hospitals. Over Internet and cloud services, digitized healthcare systems have provided easy access, viewing and sharing of digitized medical images to patients, doctors, medical professionals, health care providers, and institutes of medicine. Medical images may provide for teleconferences among clinicians, interdisciplinary exchanges between radiologists for consultative purposes, and distant learning of medical personnel. For illegal purposes used for insurance, for example, digital medical malignant nodule images may be modified on lung parenchyma in chest CT scan images. Therefore, data hiding schemes (Wang
Reversible data hiding schemes (Li
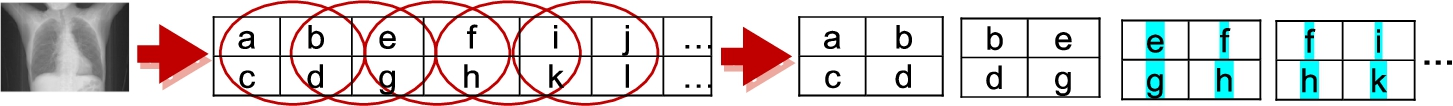
The image I is partioned into a set of
Considering resource sharing data in Cloud computing environments, stego-images may be disturbed by various techniques such as a chaotic Hénon function to obtain encrypted images (Huang
Most of image data hiding techniques (Huang
In this paper, two-tier structures, histogram-shifting of median and prediction error, are utilized to embed secret messages. The rest of this paper is presented as follows. The second section demonstrates our method. The fourth section shows the outcome of the experiments. Conclusions are presented in the last section.
In this paper, we apply a block median preservation technique (Luo
Data Embedding
At first, we partition image I into a set of
Tier-1 Data Hiding
In the tier-1 data hiding, we adopt the histogram shifting method (Luo
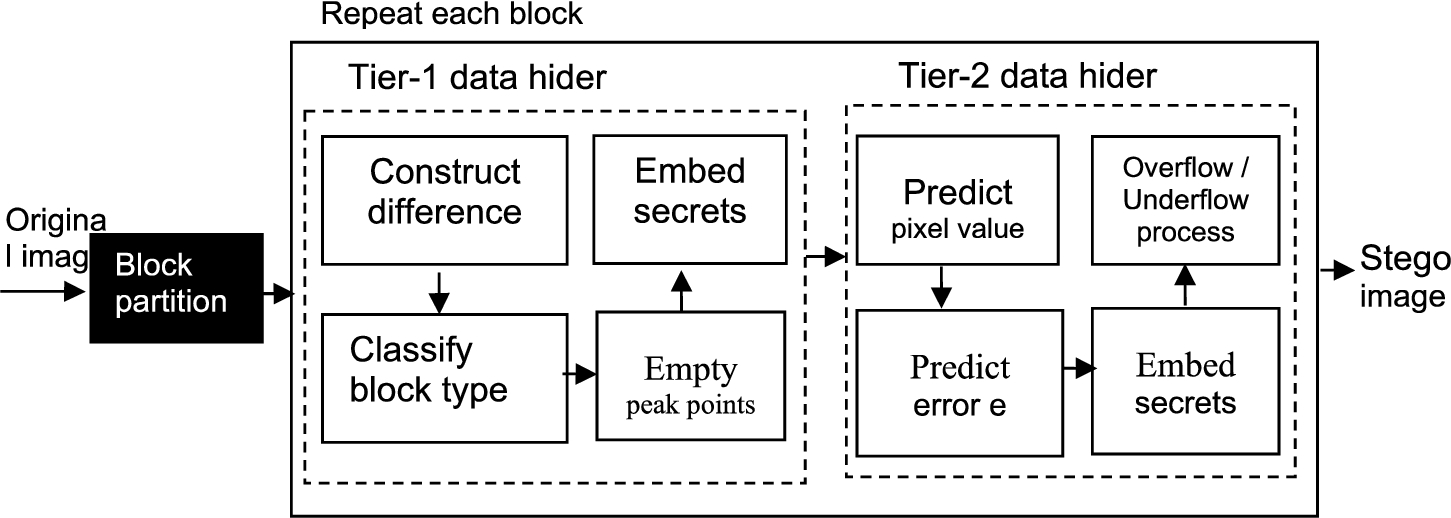
Diagram for the framework of two-tier medical image data hiding based on histogram shifting of prediction errors at the sender side.
At this step, we find median values of each block. Let four pixel values
In this step, all blocks will be classified into two types, Type I and Type II. Let
Embedding level (EL) is a parameter to adjusting capacity by histogram shifting. Let EL =
In this step, we apply histogram shifting to differentiate types of blocks. The strategies of the secret embedding are demonstrated as follows:
The definition of Type I is
The secrets will be embedded as Eq. (4) repeatedly.
The definition of block Type II-1 is presented as follows:
We will apply Eq. (6) to embed secrets
In a Type II-2 block, the definition is demonstrated as
In a Type II-3 block, the definition is demonstrated as
In order to adjust the quality of stego-image, we apply threshold in the embedding process. Let a set of
Let predict pixel
In order to restore the cover image correctly, we process the overflow/underflow by the shifting histogram from the embedding stage without a location map or compression (Kim
Further, we adjust image histograms to prevent overflow/underflow problems. On low underflow/overflow rates of high bit-depth medical images, unsinged bit images will produce underflow problems.
Because modern medical devices provide high quality images, medical images can range from 0 to 65535 for a 16-bit image. Therefore, the utilization rate of 16-bit depth is lower than 8-bit depth shown in equations (15), (16). In other words, we can utilize empty histogram bin to process overflow/underflow problem by shifting histogram of the whole image.
In respect of preserving boundary pixels, our method can restore the original-image from the stego-image successfully. Thus, the boundary pixels will be preserved. After the process of embedding, our method also can preserve the boundary pixels shown in Fig. 5. The 16-bit depth unsigned images are tested with threshold 21. In Fig. 5(b) and (c) the preserved boundary of the medical image when EL are changed from 5 to 20 is shown. In the same way, another test of the preserved boundary is shown in Fig. 5(e), (f).
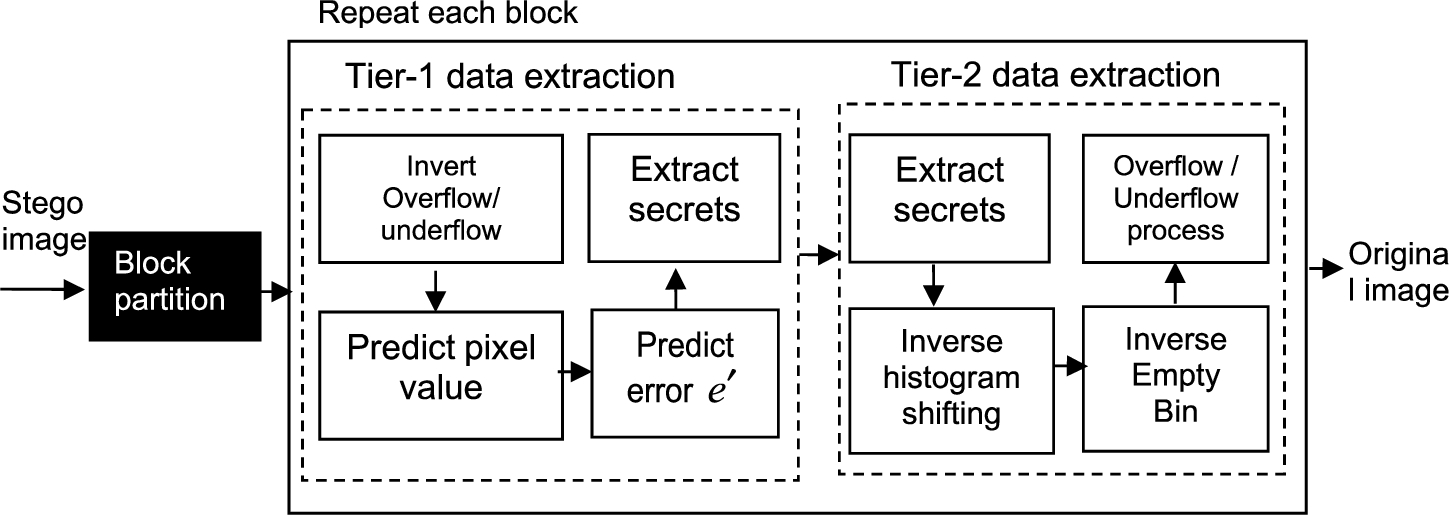
Diagram for the framework of two-tier medical image data extraction based on histogram shifting of prediction errors at receiver side.
In order to extract data, we need the embedding level and overflow/underflow distance as parameters. The data extraction will extract secret messages correctly and restore the stego-image back to the original without any distortions, described in detail below as shown in Fig. 3 Similar to the data embedding process, we partition the stego-image into overlaying blocks with
In tier-2 data extraction, we perform the extraction of prediction-based reversible data hiding method. There are four stages: inverting overflow/underflow process, predicting pixel value, predicting error
Tier-1 Data Extraction
There are three stages: extracting secrets, inversing histogram shifting, and inversing empty bin in tier-2 data extraction demonstrated as follows.
In order to extract secrets and restore the original image, we apply histogram shifting to the intermediate image block from tier-1 data extraction at this stage. Let the elements of the intermediate block be
Next step, repeat n times when EL is equal to
According to Embedding level (EL), there are different strategies to inverse histogram described as follows.
If EL = 0,
If EL > 0,
If EL is greater than 0, we perform the inversion of empty bin according to the following formula:
After inversing empty bin, we add a median value of a block to elements of the block. Finally, we construct each block as the original image.
In this paper, we demonstrate two-tier medical images data hiding based on histogram shifting of prediction errors to experiment on medical images with DICOM. The peak signal-to-noise ratio (PSNR) is applied to measure the quality.
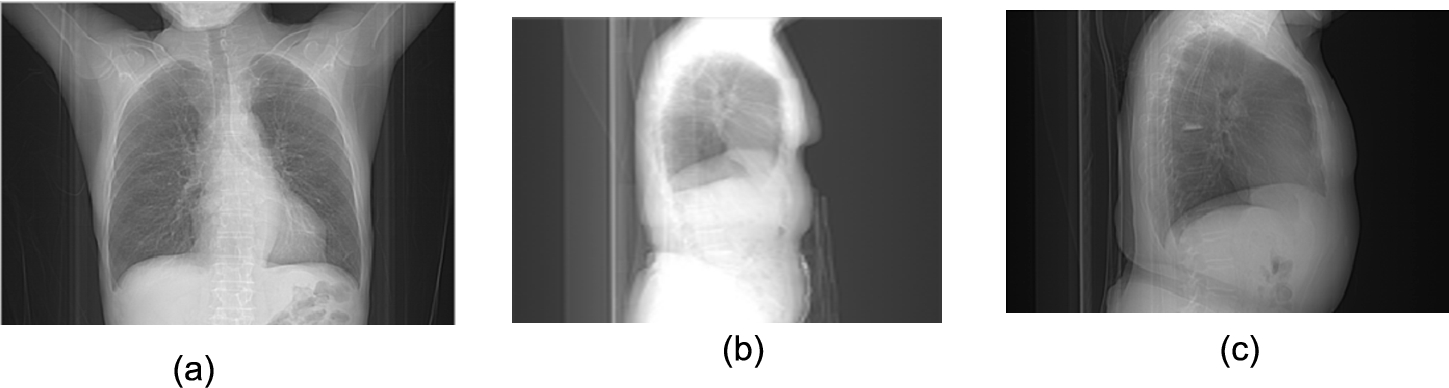
(a) CT image with signed
The results for a signed 16-bit grayscale medical image.
The results for an unsigned 16-bit grayscale medical image with different embedding levels.
The results for a signed 16-bit grayscale medical image.
In this paper, we also used Lena and airplane with 8-bit depth
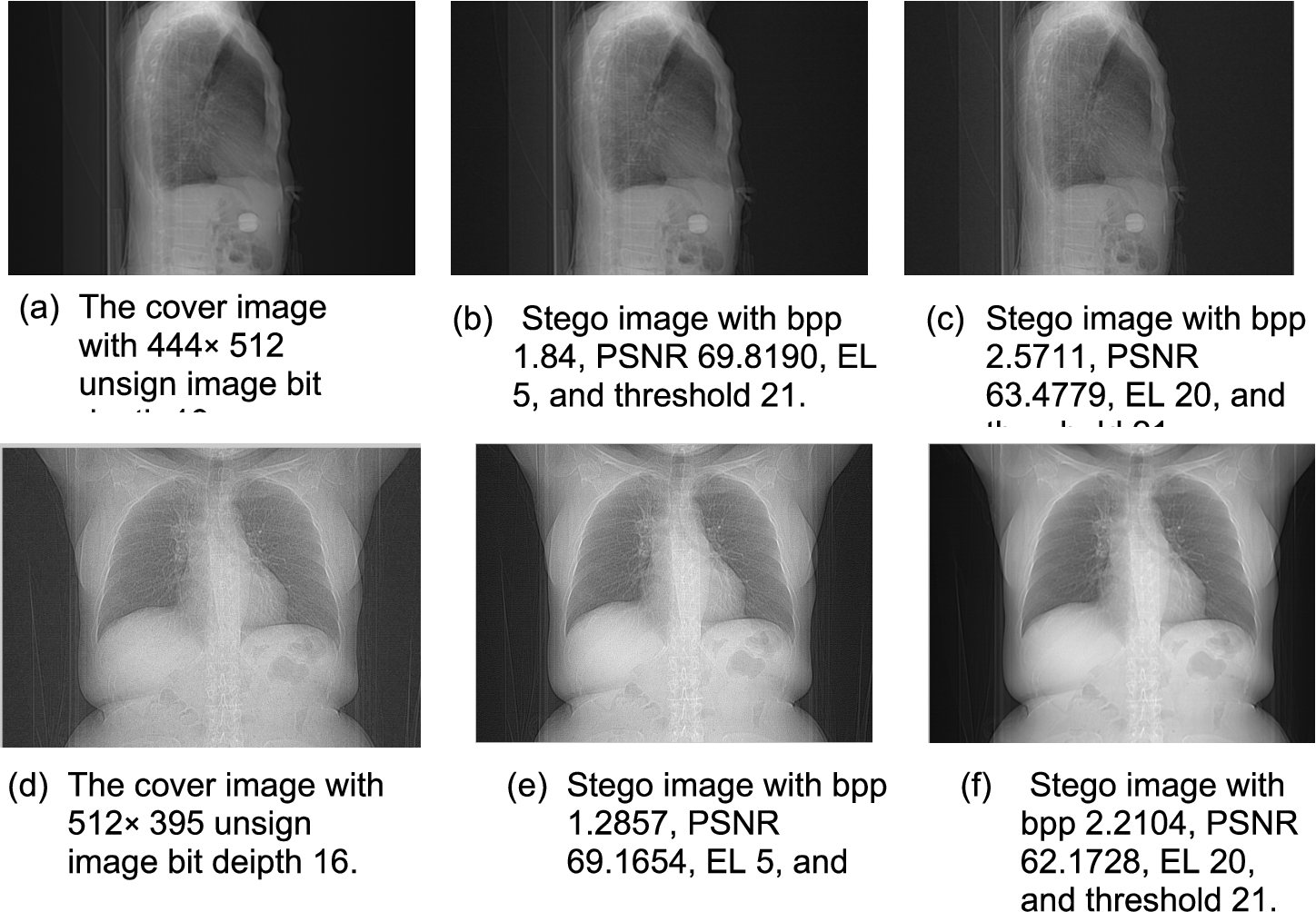
The result for boundary preserving with EL 5 and 20.
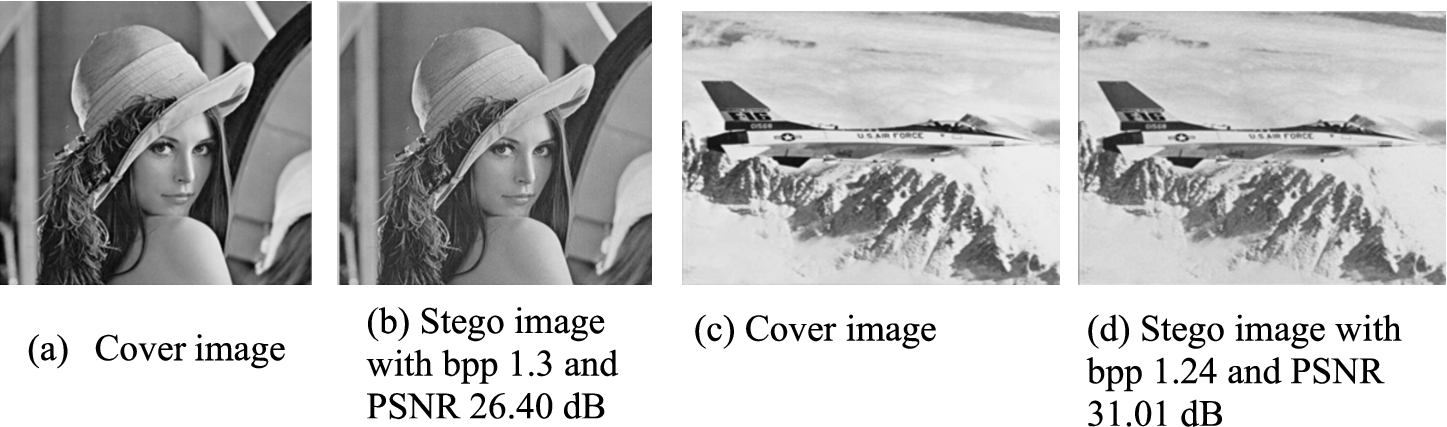
Two cover images with stego-images: (a), (b) Lena (c), (d) F-16.
The results for Lena and airplane with 8-bit depth.
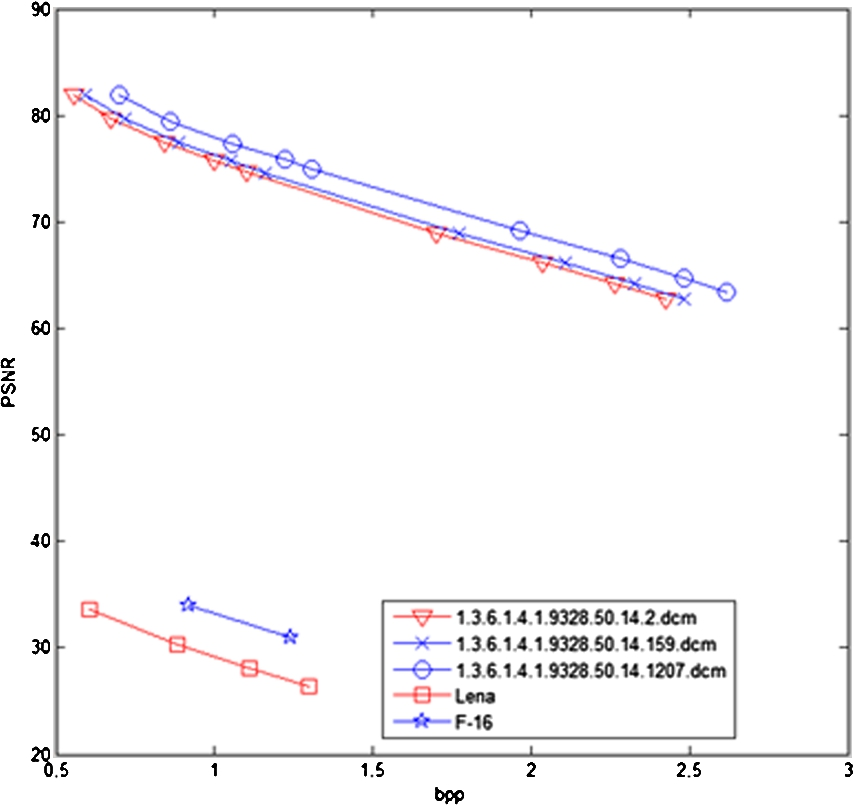
The results for a 16-bit grayscale medical Image and a 8-bit image.
The results for the comparison of median and prediction methods.
The embedding algorithm is used to embed the secret data into the cover image as a stego-image. Stego-images are transmitted over the Internet. If stego-images are altered or destroyed due to certain attacks, our method has the basic characteristics of data hiding to protect secret data. Because the secret data is hidden in the cover image, it is difficult for the human visual system to detect any unperceivable secret data.
In our method, there are two layers of block median retention technology and a predictive reversible hiding method to hide secret data. Therefore, our method is a technique that resists the attack of this technique without parameters such as threshold, EL and overflow/underflow methods. We also applied 2 × 2 overlapping blocks to partition the image. If a hacker changes the secure covert image over the network, the secure covert image cannot be extracted correctly.
Conclusion
We have proposed the data hiding of two-tier medical images based on histogram shifting of prediction error. The median histogram shifting technique and prediction error schemes as the two-tier hiding have high capacity and PSNR in 16-bit medical images. The overlapping block partitions have also been adopted in this scheme, and it has performed well. At the Tier-1 data hider, the median histogram shifting technique is based on a multi-level histogram shifting mechanism. Due to adopting two types of embedding strategies, the block medians are able to be preserved. Therefore, the stego-image utilizes these block medians to convert the stego image to the original image successfully. At the Tier-2 data hider, the prediction error scheme applies a pre-determined threshold and the absolute difference of the neighbouring pixels to decide whether the current pixel is embeddable.
Footnotes
Acknowledgements
In this paper, we adopt medical images from the cancer imaging archive (NBIA, 2018) and thank National Cancer Institute for providing the CT image data for this study for free. Most of the medical devices provide 16 or more bits of image information at each pixel (Culjat ![]() ). Therefore, a very large number of histogram is empty. Those histograms can be utilized to process overflow/underflow problems.
). Therefore, a very large number of histogram is empty. Those histograms can be utilized to process overflow/underflow problems.
