Abstract
In this article, we will analyse contemporary carceral surveillance dynamics, namely the increasing storage and exchange of prisoners’ biometric data. Drawing on qualitative research conducted in prisons, policing and security settings, we will explore how prisoners’ bodies are reduced to information and broken up into data flows. These flows move within and beyond prison walls, impacting how prisoner's data is shared (in)formally with other criminal justice actors (e.g. police forces). Such interstitial connections allow us to better explore the permeability and porosity of prison boundaries. Overall, we argue that prisoners’ data doubles are not spatially or physically restricted within cells and walls, as they circulate and are virtually managed at a distance. We urge to revisit and rethink the use of panoptic conceptual models when researching carceral spaces, its technological infrastructures and surveillance dynamics.
Introduction
This article explores how surveillance is enacted in prisons and, in particular, how prisoners’ biometric data is increasingly stored and exchanged within and beyond the carceral space. We will look at biometric tools used for identification purposes (such as photographs, fingerprints and DNA) and AI tools that monitor physiological signals (e.g. heartbeat) aiming to detect emotional states. Indeed, carceral spaces are increasingly embedding digital technologies in its physical and virtual infrastructure to enhance security and surveillance (McKay, 2022). For example, data analytics increasingly impact prison management, connecting different institutions and facilitating digital interactions with prisoners. Another example of prisons’ digitisation and datafication is the application of biometrics to control movement and identity (McKay, 2022), namely the physical access of prisoners, prison staff and visitors. Nonetheless, this article is mainly focused on confined bodies and we will particularly explore the use of prisoners’ biometric data.
The terms ‘techno-carcerality’ (Gidaris, 2020) and ‘carceral automaton’ (McKay, 2022) are useful when exploring how confinement can be mediated by technologies, particularly when considering the mobility of the prisoner's body. In this article, we argue the confined body can circulate within and beyond prisons, as data flows from that human body, navigating both physical and virtual spaces as a ‘data double’ (Haggerty and Ericson, 2000). This argument contributes to literature on prisons, punishment and confinement, namely work developed by surveillance studies scholars, digital criminologists and carceral geographers (Haggerty and Ericson, 2000; Lyon, 2018; Moran, 2015).
In the following section, we go beyond Foucault's panoptic model and its architectural apparatus (Foucault, 1977) to present alternative interpretive frameworks in the analysis of carceral surveillance dynamics. By contextualising these decentralised dynamics in a computerised and networked society and, drawing on the work developed by Haggerty and Ericson (2000), we consider how the prisoner's body is reconfigured and transformed into information, so it is ‘rendered more mobile and comparable’ (613). This occurs through a process of de-territorialisation that results in a decorporealised body that is reassembled through data flows to circulate within and beyond prison walls as a fluid and mobile data double (Haggerty and Ericson, 2000). As stated by Brown (2006): ‘the body extends outward into data; it is dis-assembled and re-assembled in networks’ (231).
We then investigate how data flows within and beyond prisons, considering how prisoners are managed and controlled, and how the carceral space is virtually connected with other Criminal Justice institutions (e.g. police forces). The surveillant assemblage (Haggerty and Ericson, 2000) is particularly relevant here to analyse the heterogeneity of actors and data involved in contemporary carceral surveillance dynamics. This analysis is complemented by insights from science and technology studies and the need for a criminology of hybrids (Brown, 2006) to consider the relationships and interactions between humans and non-humans in a non-binary and non-hierarchical way. Indeed, the focus on technosocial networks and assemblages is relevant to better understand how surveillance dynamics ‘arise at the interstices’ (Brown, 2006: 225), involving a complex array of human and non-human actors.
Through the use of such analytical tools and empirical evidence from observations, informal conversations and interview data, we demonstrate that prison's boundaries are permeable and porous to different actors. Firstly, we highlight how these changing surveillance dynamics and penal rationalities impact the work developed by prison staff and their interactions with the prisoners. Secondly, we highlight the connection and collaboration between different Criminal Justice institutions, impacting how prisoners’ information is constantly recorded and shared (in)formally within and beyond prison walls. Lastly, we briefly consider emerging technologies, namely AI tools that engage with emotion and intention to physiologically monitor the prisoner, as these tools are trialled in carceral spaces worldwide.
Rethinking the panopticon: The confined body as ‘data double’
The panoptic style of architecture, with a central watchtower surrounded by a circle of cells, has been the main metaphor used for understanding surveillance mechanisms (Foucault, 1977). Inspired by Bentham's penitentiary design, Foucault's interpretation of the panopticon as a diagram for a model of power, reveals how disciplinary mechanisms 1 are exercised through permanent visibility between the watchtower and the cells. Indeed, ‘the panopticon is a machine for dissociating the see/being seen dyad: in the peripheric ring, one is totally seen, without ever seeing; in the central tower, one sees everything without ever being seen’ (Foucault, 1977: 202). Bentham (2010 [1791]) and Foucault (1977) develop this architectural vision of surveillance as involving mechanisms of watching over subjects that are physically and spatially circumscribed. Such panoptic model is usually illustrated by the prison, with its spatial and physical characteristics allowing a constant observation of the prisoners and their movements in an enclosed space. The illusion of constant surveillance based on a ‘system of permanent registration’ (Foucault, 1977: 196) allows the central tower and the panoptic establishment to build knowledge about everyone through constant control and record-keeping.
In this article, we will consider other interpretive frameworks that allow us to go beyond Foucault's panoptic model as the guiding theoretical approach in the analysis of carceral surveillance dynamics. More recent theoretical explanations have moved beyond these architectural dimensions to situate contemporary surveillance mechanisms in a post-panoptical world (Bogard, 2006; Boyne, 2000; Lyon, 2018). This is particularly relevant when analysing forms of communication and information management that operate beyond the institutional and architectural levels.
The shift from a disciplinary to a control society (Deleuze and Guattari, 1987; Deleuze, 1992) exemplifies the move beyond the panopticon as a metaphorical representation of power. Such conceptualisation of control is illustrated by more abstract and fluid mechanisms that can operate at a distance and not just in a particular physical space where individuals are distributed (Deleuze and Guattari, 1987; Deleuze, 1992; Haggerty and Ericson, 2000). Haggerty and Ericson (2000), drawing on the work developed by Deleuze and Guattari (1987), developed analytical tools that contextualise these mechanisms in a computerised and networked society. The concept of assemblage 2 allows a better understanding of decentralised and mobile contemporary surveillance, in particular when directed towards the body (Haggerty and Ericson, 2000). In their words, the human body is ‘broken down’ into discrete flows ‘by being abstracted from its territorial setting’ (Haggerty and Ericson, 2000: 611). This process of de-territorialisation leads to the reconfiguration of this body into information, annihilating the need for a physical presence in a confined space. Going beyond institutional boundaries and its central watchtowers, this body ‘is then reassembled in different settings through a series of data flows’. The result is a decorporealised body, a ‘data double of pure virtuality’ (Haggerty and Ericson, 2000: 611) that relies on digital networks, its trails of information and opaque flows (Haggerty and Ericson, 2000).
We will argue that the confined body is reduced to information and, as a data double (Haggerty and Ericson, 2000), circulates within and beyond prison cells and walls. Through a process of re-assembly, this information is shared in dispersed, searchable databases and no longer is this confined body solely captured by the prison watchtower as a single entity. The boundaries are blurred and data flows more freely, as prisoner's records are not just kept within prison's walls. With the constant expansion and ubiquity of information infrastructures, the newly available means of control go beyond the paper file-based bureaucratic processes, relying more on computing machinery and abstract personal data that circulates between different containers. David Lyon (2003) would use the term leaky containers and, in his words, ‘the gates and barriers that contain, channel and sort populations and persons have become virtual’ (Lyon, 2003: 13). By allowing a connection between the interior and exterior of the prison, we will argue that prisoners’ data doubles are not spatially restricted within the physical boundaries of the prison, as they circulate and are virtually managed at a distance.
Contemporary surveillance mechanisms are not limited to the physicality of confined spaces such as prisons. The information gathered about the prisoner is no longer just kept in a dossier available to staff when documenting the ‘case record’ (Goffman, 1961). As we will explore, these boundaries are permeable and porous, allowing an exchange of information between the interior and exterior of the prison. When considering the blurriness of these boundaries, we will argue that the confined body circulates within and beyond prison walls as a data double (Haggerty and Ericson, 2000). Data flows beyond the architectural enclosed space and, involved in this process, there are humans and machines (in its networked, digital and electronic forms) permeating these barriers. Such analysis is crucial when considering ‘the nature of the prison boundary and open a space for debate over the kinds of permeability, porosity, transfer, exchange and other boundary-crossing processes which are observed to take place’ (Moran, 2015: 88)
Methodology
We draw on empirical evidence from two wider qualitative studies exploring the impacts of biometric technologies: one more focused on traditional identification tools (e.g. photographs, fingerprints and DNA) and another more focused on soft biometrics, namely on AI-driven techniques that engage with emotional behaviour and intention. The former project was developed in Portugal (2011–2015) and the latter in the UK (2020–2023), involving different stakeholders and criminal justice institutions, public and private bodies (e.g. prisons, police forces and security sector). Such time span and diversity of actors (human and non-human) allow us to contextualise the trends around biometric data collection in carceral settings, both spatially and temporally.
These interstitial connections are valuable when exploring the permeability and porosity of prison boundaries, as it was possible to navigate different institutional spaces and interact with different actors. By adopting interstitiality as a valuable analytical key, it is possible to discover participants’ experiences in hybrid, interstitial spaces, namely inside and outside prisons. Indeed, these interstitial connections between the interior and exterior are better understood when ‘in-between’ different boundaries. Such hybridisation also applies to our interactions with various human and non-human actors (Brown, 2006) and how we analyse these relationships in both physical and digital spaces.
Following an interpretive and constructionist approach, our analysis uses empirical evidence from semi-structured interviews, informal conversations and observation data. More specifically, this article draws on semi-structured interviews conducted with 18 members of staff based in Portuguese prisons (10 prison guards and 8 probation officers) and 11 policing and security stakeholders (mainly in the UK). Direct observation was also conducted in three male prisons of different sizes and security levels located in the north and south of Portugal. As we visited prisons for extended periods of time, it was possible to observe specific encounters between staff and prisoners, namely procedures of biometric collection and/ or storage (e.g. capturing the prisoners’ photographs or visualising the electronic systems used by staff). In addition to these instruments for data collection, informal conversations were also held with various actors who operate in prison, policing and security spaces. This was particularly relevant when visiting police stations and participating in technology exhibitions and other events with both Criminal Justice practitioners and private security companies. Such engagement allowed an in-depth understanding of the surveillance dynamics, in particular how data is increasingly exchanged within and beyond the carceral space. Detailed records and field notes were kept following these interactions and encounters and the interviews were audio recorded 3 and subsequently transcribed verbatim (with the exception of 1 probation officer that rejected audio recording). The data were systematically coded following principles of analytic induction (Charmaz, 2006). We then subjected the data to multiple readings to develop the initial categories into more abstract, focused codes.
A heterogeneous sample of participants was obtained considering their length of service, type of role and rank. 5 out of 10 prison guards interviewed held senior positions (3 senior and principal officers and 2 prison governors) and they were all male. Their length of service varied from 1 to 27 years. The probation officers 4 were mainly female (7 in 8) and their length of service varied from 3 to 35 years. These members of staff usually join the prison administration as social workers, but some of the participants interviewed had a different qualification in social sciences or humanities (sociology, education or even psychology). The policing and security stakeholders were mostly police officers either working (4) or already retired (3) 5 from various British police forces. Other interviewees were affiliated with at least 3 different British policing professional or independent bodies and organisations. These interviewees were mainly male (10 in 11).
Computerised record-keeping in prisons
Control mechanisms and surveillance dynamics in carceral spaces have changed, shaping old and new forms of bureaucratic administration. These transformations are linked to more general trends such as penal expansion, 6 increasing focus on risk management strategies (Ericson and Haggerty, 1997) and algorithmic risk assessments. Prisoners’ dossiers no longer sit in dusty file cabinets looking like towering paper monoliths. These records are now in the digital domain and virtually stored in computers and databases. These interconnected platforms store information related to prisoners’ routine in prison (such as work, sports, educational, cultural and recreational activities), penitentiary information and disciplinary record, health and judicial information, visits or even identification information (e.g. photographs). In this article, we mainly consider the use of biometrics, nonetheless in this section, we will more generally contextualise the digital trails left by confined bodies in carceral spaces.
The informatic systems have become essential bureaucratic entities in the adaptation of the penal system to the information age. As explained by McKay (2022), ‘the new digital technologies are harvesting detailed prisoner data: biometrics, emotional and behavioural patterns, mental health, vocal prints, real-time activities and movements; basically, surveillance of every micro aspect of a prisoner's quotidian existence’ (106). New mechanisms of control and surveillance are introduced with computerised record-keeping, allowing the selection of certain forms of knowledge over others (Haggerty and Ericson, 2000), impacting the criminal justice practitioners’ work (Ericson and Haggerty, 1997). These new mechanisms lead to an increasing adoption of formalised instruments as a significant development in the systematisation and standardisation of knowledge (Aas, 2004). Katja Franko Aas (2004) exemplifies precisely how the police, prison and probation officers use structured forms of communication to fill in different documents. The narrative gives place to the database and there is a standardisation of identity descriptions to classify its objects, reinforcing a categorical view of the offenders (Aas, 2004).
Our interviewees (prison staff) highlight the need to constantly collect information in the course of their work. Prison guards mention the need to use the occurrence log and constantly fill in other ‘paperwork’ (not necessarily literally, paperwork here means form-filling and administrative work). Probation officers also emphasise how their work must be translated and ‘rearranged into paper’ (Officer Clara) and digitally recorded in electronic systems, as the written records allow a greater visibility, organisation and standardisation of information. From the perspective of these officers, such standardisation allows a better evaluation of the prisoner and a ‘more objective and rigorous’ work (Officer Mariana). The probation officers highlight the ‘very bureaucratic logic’ in which ‘everything has to be registered’ (Officer Afonso) and how they are being ‘increasingly pushed to paperwork’ (Officer Daniela). In the words of Bouagga (2015), ‘from a relationship based on assisting the inmate, their primary mission has turned to advising the judge in a context of significant bureaucratization and standardisation of procedures’ (165, 166).
As we will explore in this article, when analysing carceral surveillance dynamics, we need to consider not only the reconfiguration of penal power and bureaucratisation, but also the interplay between architecture, people and technology (Hancock and Jewkes, 2011). These connections allow us to understand the role of informatic, surveillance systems and to comprehend how prisoners’ information is stored and shared in carceral spaces. However, as briefly explored, these bureaucratic administration transformations also impact the relationship between prison staff and prisoners (Bouagga, 2014; McKay, 2022). As it is mentioned by Bouagga (2014: 83), ‘the use of computer further increases the distance between prison counselors and prisoners’ and ‘the individual one-on-one work with inmates [is] threatened by a trend toward bureaucratisation’ (Bouagga, 2015: 156). The officers perceive this bureaucratic logic as harmful, considering that all these ‘written tasks’ have a significant impact on their positive relationship and interactions with prisoners. 7
The use of tools such as computers and electronic databases allow the officers to distance themselves from prisoners, helping to manage their ambiguous roles in terms of social intervention and control (Bouagga, 2014, 2015). In this context, technologies ‘have the potential to enhance certain existing tensions; tensions between control and rehabilitation; punishment and empowerment as well as access and disconnection’ (Kaun and Stiernstedt, 2020: 1583). According to prison staff interviewed in Portugal, it is a very peculiar and complex role precisely because they need to develop a ‘supportive relationship’ with the prisoners while still having a ‘function of control’ (Officer Afonso). Indeed, they play a significant role in the control mechanisms put in place to evaluate the prisoner within the judicial system. Resonating with our findings, the study developed by Bouagga (2014, 2015) in French prisons 8 also highlights this ambiguity at the level of control and social intervention: ‘you have to be at the same time in a caring attitude, displaying empathy, concern, while you are also evaluating and controlling!’ (Bouagga, 2014: 85).
The probation officers often highlight how ‘everything that happens in the prison is recorded’ (Officer Ilda) and all of them have computers on their desks that allow them to do this electronically. As Officer Ilda mentioned: ‘everything is recorded and we can quickly have access to it without leaving this desk [points at the computer], we can have access to the prisoner's life. Obviously, this is only completed with the personal–direct relationship each officer has with each prisoner’. However, not only are these interactions mediated by bureaucratic processes, but the relationship between prison officers and prisoners is destabilised through the transformation of its spatial and temporal configurations. When exploring the links between modernity, time and space, Giddens’ notion of disembeddedness (1990) can be helpful to understand how these relations can ‘[be lifted out] from local contexts of interaction and [restructured] across indefinite spans of time-space’ (Giddens, 1990: 21). Indeed, these electronic systems impact these interactions and ‘may enhance and exacerbate the complex horizontal and vertical relationships instituted between prisoners and prison officers’ (Hancock and Jewkes, 2011: 626). AI applications in this context will potentially impact these relationships further, replacing human tasks and interventions 9 (Puolakka and Van De Steene, 2021).
To better understand such ‘dual role’, involving both social intervention and punitive control functions, it is important to consider how the penal system has undergone significant changes (Hannah-Moffat, 2005). These transformations impact the work carried out by prison staff and shape how prisoners’ information is collected and shared in large, computerised systems: as part of risk assessment processes that aim to situate these individuals in categories (Aas, 2004) according to their perceived levels of dangerousness (Feeley and Simon, 1994).
When interacting with participants based in different Portuguese prisons, prison officers would normally highlight the importance of having different interconnected platforms to share information (such as the disciplinary record, different daily activities such as work, sports, educational, cultural and recreational activities) so it is possible to access prisoners’ routine through the use of networked computer systems. According to these officers (particularly those with more years of service), the computerisation has significantly impacted their work as it makes it possible to virtually monitor and control the prisoner at a distance. These records are no longer just stored in filing cabinets in a paper-based format: they are now remotely accessible and searchable. An example of that is how the electronic system allows them to check older records automatically, whereas ‘in the past, to check the archives and to identify and see it on the paper, was a lot more difficult’ (Officer Mariana).
In the next section, we explore the use of prisoners’ biometric data, namely how the Portuguese Prison Information System (SIP – Sistema de Informação Prisional) 10 gathers different elements of biometric identification, such as photographic portraits and specific characteristics or physical marks (article 4. (1) Decree-law no 51/2011 11 April). Secondly, in other contexts, we consider the use of AI analytics to monitor life signals, movement and detect emotional behaviour through biometric sensing.
Surveillance beyond prisons: Exchange of information with police forces
Police work depends heavily on information collection and management (Ericson and Haggerty, 1997; Haggerty and Ericson, 2000), so it is crucial that police authorities manage to incorporate data collected by other criminal justice institutions. In the words of Haggerty and Ericson (2000), ‘police organizations have secured routine, and often informal, access to a host of non-police databases’ (616). Indeed, there is a collaboration between different institutions, be they the police, the prison or the justice system more generally. In this section, we will explore how there is an exchange of information between the prison and the police, both through formal and informal channels.
We will analyse the Portuguese example in more detail, but there are many other case studies in other jurisdictions that could be used to explore how prisons and police exchange prisoners’ information. To briefly illustrate this in the UK, The Police National Computer (PNC), a national database where criminal conviction information is stored and shared with all police organisations, can also be accessed by non-police agencies, namely prisons. Currently, there are 43 British prisons with PNC equipment installed that can be used for ‘security categorisation of prisoners’, risk assessments, management of security intelligence, etc. Indeed, ‘for a wide range of risk assessment purposes that help to keep prisons safe and secure places to live and work’ (MoJ and HMPPS, 2023: 4). Recent policy framework (MoJ and HMPPS, 2023) applied to England and Wales, sets out how to use PNC information lawfully in prisons and how to comply with police requirements and guidance to ‘audit, monitor and control’ use of this system. The College of Policing's Code of Practice (2023) also provides relevant guidance and principles for an ethical use of this system. 11
The Portuguese Prison Information System (SIP) is formally available not only to Portuguese prison services but also to other dependencies of the Ministry of Justice (MoJ) such as Polícia Judiciária (PJ). PJ is the national criminal investigation police agency responsible for investigating most crimes (Article 7 of Law No. 49/2008). This police force manages the Integrated Criminal Information System (SIIC, Sistema Integrado de Informação Criminal) that aims to centralise and manage national criminal information (equivalent of the British PNC). This integrated system (SIIC) allows access to external electronic databases such as the SIP (Miranda and Machado, 2019). Leandro (prison governor) illustrates how SIP is used by prison staff to upload prisoners’ information (for instance, their photographs) and how such personal details are then automatically available at the national level. He also explains how police institutions like PJ can directly access these records and how prison staff play a significant role in this collaboration with policing professionals: We give them [police] everything – they have access to all our information about the individual – who is who – they already know out there and even know better than we do – but internally they have access to our information, not only disciplinary issues, everything: whatever they want to look at out of curiosity or for legal purposes. We do not have access to their part, although the Ministry is the same. But the police very often ask us for information regarding visitors and (…) I would respond very often… I would provide information by legal means… and I already gave a lot of information, quite a lot. We are an integrated part of the system and we must have this type of collaboration. We are the Ministry of Justice (MoJ) and I think this [exchange of information] works at the level of the ministry. PJ, courts, MoJ… But if, for example, a colleague from PSP or GNR [police forces from a different Ministry] asks – and that already happened to me – ‘Oh xxx check there if this guy is in prison’ and I can do that, I check SIP, put the name of the individual, a quick search and if that guy is in prison X, I can tell right away that guy is there, see? It is easier and I just say ‘it is in X prison, entered the day such and such and such’.
Probation officers raised a few issues regarding access to prisoners’ information, namely its anonymity and secrecy. Our participants agree these records should be protected, as they are recorded and stored with the purpose of monitoring individuals in the prison context. As Officer Ilda puts it: ‘such records are about a citizen who is here to serve a sentence and that has to do with his/her social rehabilitation but has no interest nor should be made available to the police’. However, as we explore in this section, the information stored in electronic systems is available both formally and informally to third parties, namely police forces. Indeed, in the words of Officer Ilda, ‘we have links with the police… They often ask us who visited so-and-so in a given period?’ For these participants, the use of surveillance and electronic systems allows a more efficient system of information registration. From their perspective, the constant recording and storage of data is also indispensable to guarantee a collaboration with other criminal justice institutions. Such logic follows the growing global trend to create digital collaboration platforms. 12
The following image (Figure 1) presents the different flows that illustrate how prisoners’ information is shared between the interior and exterior of the prison. It presents the diverse elements of information that are shared with the different police forces, both formally (via the electronic system SIP) and informally (direct contact with prison staff): daily activities, disciplinary record, visitors, date and time of entry and elements of biometric identification, such as photographs, physical signs, fingerprints and DNA (biological sample).
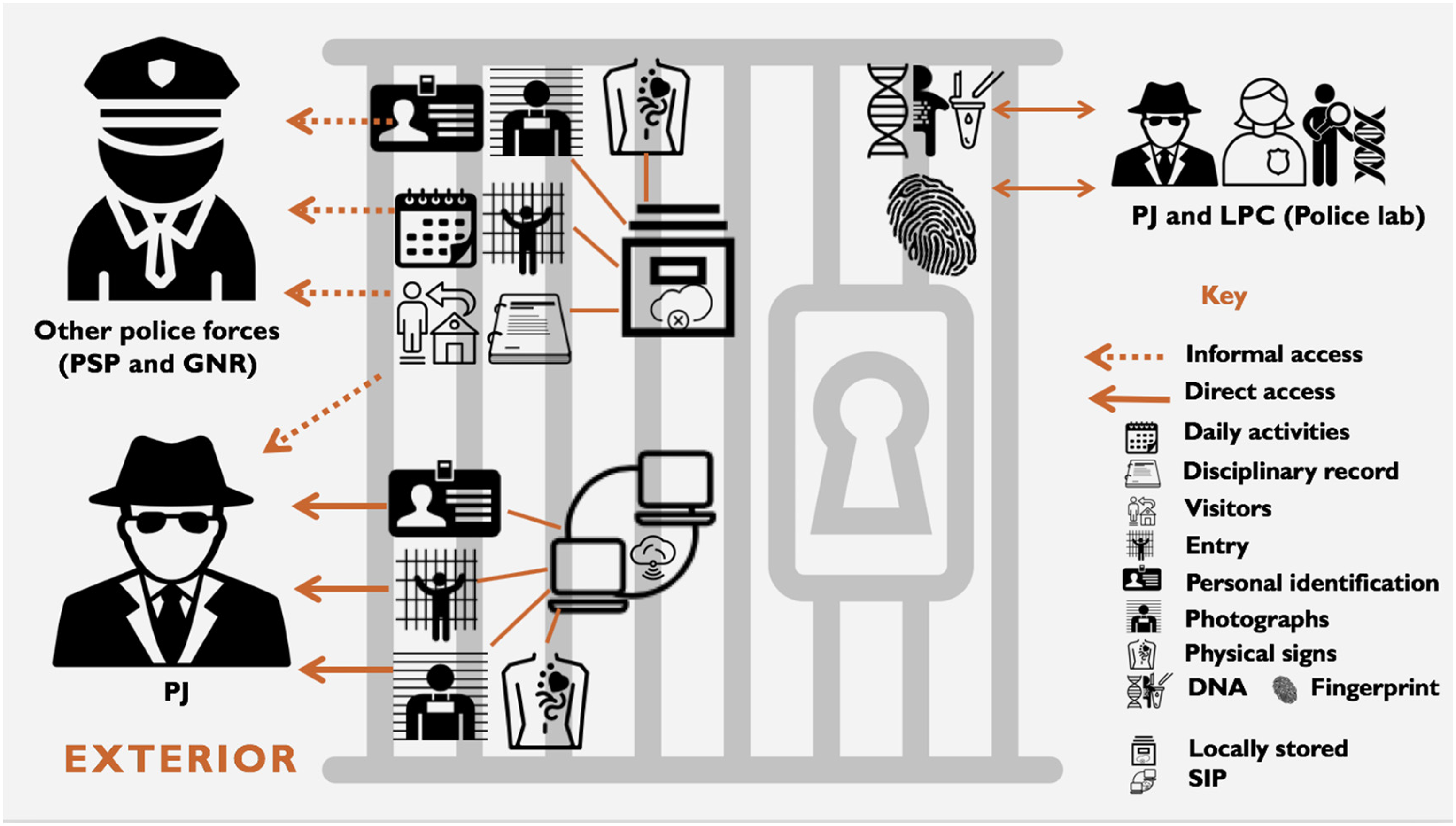
Prisoners’ information flowing within and beyond prisons.
Prisoner's biometric identification: Photographs, fingerprints and DNA
We will now briefly consider three specific examples of biometric identification: the use of photographs, fingerprints and DNA. The current technological landscape, in particular when considering the use of networked computer systems (Haggerty and Ericson, 2000), must be addressed in more detail. Foucault's vision of the panopticon based on transformations during the eighteenth and nineteenth centuries does not allow us to understand these contemporary developments.
The photographs taken to prisoners when they enter the prison are normally stored electronically in the SIP (Miranda and Machado, 2019) and, as previously discussed, PJ can formally access these photographic portraits. However, when more specific elements are needed (for instance, a tattoo in a specific part of the prisoner's body), PJ can still use informal contacts to request that more detailed photographs are taken and shared. The other police forces (PSP and GNR) do not have access to this electronic system (as previously explained, these forces are not part of the MoJ), so they usually proceed by requesting any photographic portrait that is needed to prison staff. Officer Nelson (24 years of service) illustrates this process of collaboration between prison, courts and police authorities: When the courts want some data, they ask us – as it is the case with photographs, right? GNR is the same but most often by phone. They call, identify themselves and then we confirm the identification. They ask us to send [photographs] and sometimes we send by email prisoners’ identification elements so they are recognised by witnesses… PJ do not ask as much – why? I think they have access to our system, I believe. Only in more specific situations: to know if a prisoner has a tattoo… if there is no photograph we go and check. And it already happened once [getting a request from them] asking us to see if the prisoner had certain [physical] signs. Without collaboration, we do not go anywhere.
Apart from the SIP storage of prisoners’ photographic portraits (MoJ electronic platform), during the fieldwork it was possible to observe in one of the prisons that these photographic records are also locally stored in computers. The officer responsible for the storage of such records, visibly pleased with his strategy, manages to record and organise all the prisoners’ photographs by creating different folders in his computer. According to Ramiro (27 years of service), this strategy is put in place to manage all the informal requests from police forces such as GNR and PSP often requiring prisoners’ photographs. Officer Nelson explained that these informal strategies are needed so the collaboration between prison and police is possible when the electronic system is not accessible by the police authority. In his words: ‘how these photos are stored, here and in other prisons, … well, we understand that we might need them [to share them in the future]. But nothing tells us that we must keep these photographs [in the computer]’. Indeed, the reasoning for storing these photographic portraits is not associated with prison dynamics but rather with the need to collaborate with external institutions such as police forces.
At the beginning of the twentieth century, fingerprinting was one of the dominant criminal identification systems, constantly used to identify prisoners (Cole, 2001). Indeed, one of its first applications was in prisons, complemented with anthropometric measurements and photographs (Miranda, 2020). As these identification systems developed, their application in the criminal justice system varied depending on the context of use. While in prisons the anthropometric measurements dominated and the fingerprint was only deemed a supplement, police forces quickly adopted fingerprints. This was mainly due to being a quicker and inexpensive process that allowed police authorities to ‘[deal] with large numbers of petty offenders’ (Cole, 2001: 156). The fingerprint is also valuable to police as a forensic identification tool, playing a role in criminal investigations. However, currently fingerprints are rarely used in Portuguese prisons
13
and, according to officers interviewed with more years of service, that has not happened on admission for more than 20 years. Fingerprinting is no longer seen as part of ‘admission procedures’ that aim to ‘[shape] and [code the prisoner] into an object that can be fed into the administrative machinery of the establishment’ (Goffman, 1961: 26). As briefly mentioned, lofoscopic identification procedures are usually associated with police investigations and, indeed, police authorities often travel to prisons to collect prisoners’ fingerprints. In the words of the supervising Officer Valter: The fingerprint is collected here and I already saw that a lot of times – then that is used outside of the prison. Therefore, in a police investigation, the authorities very often come to the prison to collect fingerprints to compare with an ongoing investigation. It is not for our own use, let's say, within the prison system. They are the ones that come here [for that collection]. One of those [biological sample collections] was done in this office.
While in this particular prison where Officer Mateus is based these collection procedures were only sporadic, in a different and larger prison it was possible to observe that the biological sample collection always occurred within prison boundaries. In such situations, PJ (the national criminal investigation police agency) would send a police team to the prison to collect the prisoners’ sample through buccal swabs. It was possible to verify that when the DNA database was implemented these procedures would normally occur in the exterior. However, due to the need to collect these samples more quickly to a larger quantity of prisoners, the police teams have been travelling more often to prisons to carry out such procedures and not the other way around. The governor of this prison explores these transformations regarding the collection of prisoners’ biological samples: It is not a daily thing, but very often yes. With the buccal swab, the collection of a biological sample, even some days ago [that happened] and I already prepared the paperwork. The police (PJ), the police scientific laboratory, (…) they come here very often. (…) They created a DNA database and because there is a large number of prisoners, it is better for them to come here and do their work with a lot of them, instead of sending prisoners to the exterior. So (…) they come here with their own [things] for that… they come here and other prisons. (….) There is space and the prisoners are here, so they just need to bring a team [smile]. When they come, they send a fax to tell us who are the prisoners [that are going to be subject to biological sample collection]. (Valério, 25 years of service)
Goffman's model of total institution, characterised by a bureaucratic form of management and control, implies a well-defined division that separates inside from outside. The total institution is circumscribed by physical barriers such as locked gates and high walls that confine the inmates (Goffman, 1961). However, as we have explored in this section, such spatial and physical arrangements are now complemented by more permeable barriers that allow an exchange of information between the prison and the outside world. In the words of Bogard, ‘networks have too many holes, too many openings. There are too many virtual connections, too many observers of observers, too many points of recording’ (2006: 118). Bauman's notion of ‘liquid institution’ (2000) allows to understand precisely how we can situate such data flows beyond its physical barriers. By allowing such connections, these barriers have become blurred. The confined bodies are not entirely ‘cut off’ or enclosed, as they can circulate within and beyond prison walls as a data double (Haggerty and Ericson, 2000).
Surveillance within prisons: Emerging biometric sensing, video and AI analytics
Surveillance technologies can be introduced in carceral spaces ‘[appearing] to promote and encourage flexibility of movement while retaining high (but discreet) levels of security’ (Hancock and Jewkes, 2011: 625). From CCTV and body-worn cameras to biometric monitoring and other electronic tools, prisoners’ bodies are scrutinised in more subtle ways (Bauman, 2000; Crewe, 2011; Ministry of Justice, 2023). This is certainly well illustrated with the use of AI tools and multiple sensors. Aiming to reduce prison staff, different technologies have been adopted by Prison Services around the world ‘to achieve operational efficiencies’ (McKay, 2022: 105).
In Singapore, this is demonstrated by detection systems such as AVATAR (advanced video analytics to detect aggression) and VADAR (video analytics to detect abnormal behaviour), facial recognition cameras in cells and wrist tags (McKay, 2022). In Malaysia, AI tools are deployed in the analysis of CCTV footage to examine behavioural patterns, aiming to prevent fights (Kaun and Stiernstedt, 2020). In the Netherlands, automated emotion recognition software is also used for prisoner monitoring (McKay, 2022). In China, prison-surveillance systems aim to prevent violence and self-harm using AI and a network of sensors and emotion and behaviour recognition cameras to monitor facial expressions and gait (Article 19, 2021). Indeed, through video analysis and the recognition of micro-expressions, these systems use ‘image recognition that detects light vibrations on faces and bodies’ (Article 19, 2021: 21). For example, AI deep learning systems developed by Taigusys Computing aim to infer prisoners’ feelings and emotions based on facial traits (e.g. muscle movements), body movements more generally, voice or other biometric traits (Taigusys, 2018). These systems have been deployed in approximately 300 prisons and detention centres in China, coupling algorithmic analysis with a network of 60,000 cameras (Standaert, 2021).
In the UK, cameras and AI-based video analytics are also deployed in prison context (Liverpool) to detect ‘suspicious behaviour’ and avoid smuggling (Puolakka and Van De Steene, 2021: 131). In this context, one of our policing and security participants discussed similar prison technology projects that have been debated for more than a decade. Aaron explained a trial where multiple sensors within the prison cells would capture prisoners’ physiological information, namely on movement, breathing and heart rate. As further explained by Aaron, sensors mounted on different facilities would collect sensing data (namely vital sign information): [this] was for use in cells where it had ultrasonic transmitter receivers built into the beds in cells, and it was for people who’d either choked or had a heart attack or whatever (…) Cameras weren’t in cells at the time because it wasn’t allowed. So, they had this… It detected their breathing rate, any change in body movement, and things like that, and then the algorithm again would pick up those changes, but it was trialed in a couple of cell blocks, and it was very early days. It was probably, cranky, 15 years ago, I guess. Well, the computer processing wasn’t anything like we’ve got now. So, it kind of wasn’t taken up because it wasn’t good enough to be able to detect the failure of life signs. (…) The technology wasn’t available, you know?
Even if the trialled system described by Aaron could not rely on cameras 15 years ago, as these devices were not allowed in cells at that time, this has certainly changed since then. For example, in the wake of the COVID-19 pandemic, prisons continued to develop partnerships with technology companies to operate virtual visits more widely. Throughout pandemic restrictions, these virtual visits required devices with Internet connection and cameras allowing facial recognition checks. While physically restricted within carceral space, prisoners also increasingly appear virtually in court using video technologies (McKay, 2015). Video link technologies have been embedded in prisons, networking its infrastructure with other criminal justice institutions for the sake of efficiency, accessibility and speed (McKay, 2015). Not only these technologies allow the prisoners’ body to circulate beyond prison walls as a data double (Haggerty and Ericson, 2000), ‘they [also] fundamentally change the site of adjudication, the spatial dynamics and human interactions, and impact on prisoners’ embodied encounters with the law’ (McKay, 2015: 262).
As previously explored, when considering current AI developments in this context, the use of video surveillance and intelligent analysis to detect motion or any abnormality in prisoner behaviour is certainly another example of a more emergent trend (Puolakka and Van De Steene, 2021; Sun, 2022). Our participants, both consultants in a large telecommunication and video analytics company (and retired British police officers), explain recent progress in physical detection. As explained by Bruce: There is a big push now in the industry to deliver those sort of analytics to the point that, so for example, most of it is about physical sensors, I guess. It's like… if you want to detect whether someone's breathing or whether there is unusual movement in a cell where you’ve got a prisoner that maybe they’ve gone higher than they should have done, (…) it tends to be more of a physical sort of detection. I think we’re probably on the cusp of developing some of these things to add to that really. I think we’re probably quite good at the physical detection in analytics.
Due to an alarming global increase of prisoner deaths in custodial contexts (Tomczak and Mulgrew, 2023), particularly due to nonnatural causes (death by suicide), these new technological systems have also been targeting such confined bodies and its physiological signals. Dean discussed the use of these technologies to monitor vital sign information, highlighting the potential use of AI solutions to prevent prisoner deaths in custodial contexts (particularly suicide): Even within the cells themselves, now we have technology for anti-ligature and stuff like that to analyze, but that's all aligned as well, so it's about having a responsibility now to keep these people safe within the cell complex. Having worked in custody a long time ago as a sergeant, it's a very responsible job. People do die in custody. And that is your worst nightmare. So, you know, are they taking drugs from a concealed place on their body? Are they putting stuff in their mouth? Are they doing anything to their wrists? Are they trying to make ligatures for their neck? Anything that can detect that sort of emotion and behavior would be beneficial from the point of view of saving their life, but there's a huge cost involved in any deaths too. You could set cameras up (…) if you add to that the sensory emotional stuff that could detect, you know, perhaps their heart rate was high, that they were sweating, all that sort of stuff. Then why not? … ‘It's just,’ it's just another layer really. ‘You’re giving them,’ it's just more information to the operator to say, ‘have a look at this person’.
In this final section, we explore emerging technologies that are seamlessly embedded in carceral spaces worldwide. Spatially, the integration of different technological capabilities means there are different layers to how the confined body is monitored within prison boundaries. Indeed, these tools aim not just to watch and identify an individual, but also to make inferences, and detect feelings and intention. These overlapping layers associated to different technological capabilities can be extended to other forms of incarceration and coercive confinement (e.g. immigration detention centres). Temporally, it is also relevant to consider how new technology adoption is justified under certain circumstances and for what purposes. The example of virtual and court visits and the wide use of web-enabled devices with cameras during the COVID-19 pandemic is relevant here. Now, in the aftermath of this pandemic, these technologies still endure in carceral spaces, integrating a complex technological infrastructure involving not just prisons and other criminal justice institutions, but also private security sector and tech companies. Beyond biometrics, we also witness the rise of counter-drone systems, developed and implemented as a cutting-edge solution for prison airspace protection. However, this complex technological ecosystem deepens the layers of surveillance within prison walls, linking a seemingly enclosed space with a digital, interconnected and networked world.
Conclusion
The penitentiary design with a central watchtower surrounded by cells is no longer sufficient to theoretically comprehend contemporary surveillance dynamics (Bogard, 2006; Boyne, 2000; Haggerty and Ericson, 2000; Lyon, 2018). We must go beyond Foucault's panoptic model as an interpretive framework when analysing carceral surveillance. It is essential to move beyond prison walls when understanding how the prisoners’ body is reconfigured into information, flowing as a data double (Haggerty and Ericson, 2000) through physical and virtual boundaries.
The porosity and permeability of these boundaries allows prisoners’ information to circulate between the interior and exterior of the prison. The blurriness of these boundaries impacts our contemporary understanding of the total institution (Goffman, 1961) and carceral space, both physically and digitally. As technologies challenge the portrayal of prisons as enclosed architectural structures and confined spaces (Jewkes and Reisdorf, 2016), further reinterpretation and reflection is needed to better acknowledge the significance of fluid digital networks and technological systems in carceral settings. In a networked world, the prison walls and cells act as porous barriers that mediate how prisoners’ information is shared between different criminal justice actors, internally and externally. The nature of the prison boundary has changed (Farrington, 1992; Moran, 2015; Scott, 2010), allowing an exchange of data with other institutions (namely police forces) via formal and informal channels. The prisoners are uncovered in a web of connections and their data flows beyond these boundaries.
Situating our analysis in these interstitial connections between the interior and exterior, we explored in more detail how prisoners’ biometric identification (e.g. photographs, fingerprints and DNA) is shared with police forces. In the Portuguese context, at a formal level, the direct access to databases such as SIP allows data to be shared with other MoJ institutions (i.e. PJ). But there are also informal exchange practices that involve other police forces (such as PSP and GNR) to overcome the limitations emerging from the (lack of) interconnection of databases. It is fundamental to develop further socio-legal research exploring how information is shared between different institutions and how prisoners’ information is used for various purposes in these interstitial spaces. This is particularly relevant when there are problematic informal practices of data exchange and there is the need to map how these practices are (or not) formally regulated (e.g. in different data protection regimes in Europe such as the EU Law Enforcement Directive 2016/680).
We also briefly discuss the development and implementation of emerging AI-driven technologies and their impacts on prison interventions; in particular, we look at biometric sensing to detect emotional behaviours (e.g. reading vital signs as a response to managing death by suicide or tracking emotions to prevent aggressive behaviour). Following the COVID-19 pandemic, we also illustrate recent developments with virtual visits operated using web enabled devices with video and facial recognition capabilities and court appearances using video link technologies more widely. Further research should historically situate and contextualise the impact of these emerging technologies on different forms of bureaucratic administration in carceral spaces. For example, such transformations will potentially impact the future work developed by criminal justice practitioners, particularly prison staff, shaping their relationship with prisoners and their management, following risk assessment processes that aim to situate the confined bodies in specific categories (Aas, 2004).
These transformations at the level of penal rationalities and the materialisation of risk in the form of bureaucracy and surveillance are defining characteristics of what Feeley and Simon (1992) termed the ‘new penology’. Such risk assessment and collaboration with institutions and organisations is intensified due to constant information registration and the use of computerised systems. We argue that prisoners are subject to classification schemes, risk management and surveillance that reflect the role of the institutions involved, their control strategies and asymmetric exercises of power, knowledge and authority. This article aims to contribute to the analysis of such transformations and rationalities by highlighting how prisoners are managed within and beyond prisons in relation to risk, surveillance and control. This occurs through a proactive intervention that combines different elements (physical/digital, human/non-human, formal/informal, institution/network, interior/exterior) that increasingly allow the exchange of information between different criminal justice actors and, potentially, involving the security technology private sector as well.
By examining contemporary carceral surveillance dynamics, this article aims to contribute to the literature in social studies of surveillance, digital criminology, carceral geography, probation and prison studies more generally. It does this by stressing the relevance of alternative interpretive frameworks in the analysis of these dynamics and the need to (re)visit traditional theoretical models (namely the panopticon and total institution). It also emphasises the importance of adopting an interstitial lens when conducting research in specific carceral settings (e.g. prisons and other forms of coercive confinement) to better understand the connections between different actors (human and non-human), institutional spaces (e.g. different criminal justice institutions and private/ public sector) and its intersections with both physical and digital domains. Further empirical and interstitial work is needed to continue exploring the impact of digital networks and technological infrastructures in incarceration and, consequently, its repercussions on how different (non)human and institutional actors interact with each other.
Footnotes
Declaration of conflicting interests
The author declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
This work was supported by the Economic and Social Research Council [Grant Number ES/T00696X/1] and through funding from the Foundation for Science and Technology – FCT (Portuguese Ministry for Science, Technology and Higher Education) through the grant SFRH/BD/70055/2010. Thank you to the reviewers and editors for their valuable feedback on earlier drafts of this article.
