Abstract
In 2020, the European Union announced the award of the contract for the biometric part of the new database for border control, the Entry Exit System, to two companies: IDEMIA and Sopra Steria. Both companies had been previously involved in the development of databases for border and migration management. While there has been a growing amount of publicly available documents that show what kind of technologies are being implemented, for how much money, and by whom, there has been limited engagement with digital methods in this field. Moreover, critical border and security scholarship has largely focused on qualitative and ethnographic methods. Building on a data feminist approach, we propose a transdisciplinary methodology that goes beyond binaries of qualitative/quantitative and opacity/transparency, examines power asymmetries and makes the labour of coding visible. Empirically, we build and analyse a dataset of the contracts awarded by two European Union agencies key to its border management policies – the European Agency for Large-Scale Information Systems (eu-LISA) and the European Border and Coast Guard Agency (Frontex). We supplement the digital analysis and visualisation of networks of companies with close reading of tender documents. In so doing, we show how a transdisciplinary methodology can be a device for making datafication ‘intelligible’ at the European Union borders.
Introduction
The increasing use of digital technologies in more and more areas of social life has raised many questions of opacity and transparency. According to legal scholar Frank Pasquale (2015), we now live in a ‘black box society’. International relations scholars have highlighted the challenges of secrecy when researching security practices (De Goede et al., 2019). More specifically, borders are sites of intensified opacity given the combination of ‘blackboxing’ and secrecy (Martins and Jumbert, 2020; Tazzioli, 2022). Many civil society organisations, digital rights activists and researchers have drawn attention to the opacity of digital technologies combined with the opacity of public sector use of digital technologies (Ada Lovelace Institute, 2020; Big Brother Watch, 2021; Veale et al., 2018).
Faced with both intensified and dispersed forms of opacity and secrecy, critical border and security scholars have used a range of different methods – from document analysis to interviews and ethnographic research – to trace and understand the transformations of digital technologies and particularly their political implications for border control (De Goede et al., 2019; Tazzioli, 2018). While this literature has focused on ethnographic and qualitative methods, investigative journalists have used freedom of information (FOI) legislation for accessing information about technologies tested and deployed by public authorities. A recent investigation into Frontex, the European Border and Coast Guard Agency that runs border control operations, has required investigative journalists from The Guardian in the UK, Der Spiegel in Germany, and Lighthouse Report in the Netherlands to collaborate in collecting and visualising data regarding Frontex’s involvement in pushbacks (Christides et al., 2021). In 2018, Frontex’s opacity was challenged in the Court of Justice of the European Union (CJEU) by two pro-transparency campaigners that were refused information about its maritime and border operations. Frontex refused access to the requested documents on the grounds of ‘public security’. The Court ruled in favour of Frontex, subsequently also demanding that campaigners pay the legal costs (CJEU, 2019). More recently, researchers have started to combine textual analysis with visual and digital methods through digital analysis of images and video recordings. For instance, the academic project Forensic Architecture has revealed pushbacks on the Evros river at the Greece–Turkey border by using the methodology of ‘situated testimony’, developing ‘3D models of the scenes and environments in which traumatic events occurred to aid in the process of interviewing and gathering testimony from witnesses to those events’ (Forensic Architecture, 2020).
In this paper, we propose to advance a methodological agenda for researching opaque border and security practices. We argue that a combination of digital and qualitative methods can help shed light on data-driven transformations at the European Union (EU) borders. We understand these transformations as encompassing the deployment of data-driven technologies or what has come to be known as ‘datafication’. Datafication is not simply the process of collecting data about people, but that of transforming bodies, actions, and things into data that can be processed by algorithms (D’Ignazio and Klein, 2020: 12–13). Thus, datafication ‘marks how especially digital systems fuel, intensify, and automate historical practices of databasing, analysing, and using information’ (Flensburg and Lomborg, 2021: 2). In response to this widespread datafication, ‘digital methods’ have come to name an expansive array of methods to analyse the proliferation of digital devices, social media and data – from digital ethnography and ‘methods of the medium’ to computational methods of data mining and visualisation (Rogers, 2013; Snee et al., 2016). However, there has been limited engagement with digital methods in critical border and security studies. Scholars have tended to focus on qualitative, often ethnographic methods (De Goede et al., 2019) and more recently, on digital methods such as digital ethnographies of migrants’ use of smartphones and social media or digital methods that analyse ‘media journeys’ (Diminescu, 2012; Sánchez-Querubín and Rogers, 2018).
The transdisciplinary methodology we propose in this paper is the result of a collaboration between scholars from different disciplines: computer science, international relations and digital humanities. Moreover, it is inspired by the data feminist approach developed by D’Ignazio and Klein (2020). 1 From the seven principles of their data feminist approach, we focus on four, which we translate into methodological orientations: (a) disrupting the dichotomy between qualitative and quantitative, (b) challenging binaries of transparency versus opacity, (c) examining and challenging power asymmetries and (d) making all the research labour visible. 2 Following this approach, we aim to develop modes of intelligibility rather than just transparency of datafication at the EU borders. Making datafication transparent is not sufficient, as the techniques of governing ‘through vision and observation’ (Flyverbom, 2019: 22) do not amount to knowing or understanding the datafication process that is at stake.
Empirically, we analyse the contracts awarded by two EU agencies involved in the datafication of borders: the European Border and Coast Guard Agency (Frontex) and the EU Agency for the Operational Management of Large-Scale IT Systems (eu-LISA). The two agencies have different tasks of border control and were established at different times: Frontex in 2004 and eu-LISA in 2011. The former is in charge of promoting, coordinating, and developing the European border management (European Union, 2019: Chapter II), while the latter ensures the operational management of the existing EU databases – Schengen Information System (SIS II), the Visa Information System (VIS), European Asylum Dactyloscopy Database (Eurodac) – and the future ones – Entry Exit System (EES), European Travel Information and Authorisation System (ETIAS), European Criminal Records Information System for third country nationals (ECRIS-TCN), as well as their interoperability (European Union, 2018: Chap. II). Both agencies have been key actors in the EU’s integrated border management. Their working agreements, cooperation (formally established in 2014), and recent joint tender calls for contracts of up to EUR 1 billion make this joint analysis particularly relevant (eu-LISA and Frontex, 2014; Frontex, 2021a). Both agencies have attracted much scholarly and public attention given their digital developments – one example is the use of surveillance technology by Frontex and the development of new databases and interoperability requirements by eu-LISA (Jones, 2019; Leese, 2022; Tazzioli, 2018).
Our aim is not to compare the two agencies, but to show how a transdisciplinary method enables modes of intelligibility about datafication at the EU borders. Making intelligible entails understanding that builds upon while going beyond the requirements of making transparent, visible or legible. To this purpose, we start by mapping the companies that have been awarded contracts, their areas of contracted work and making their relations legible. By tracing the main actors involved in the work of datafication and their networks, we can also render intelligible the power relations in the production and transformation of the EU datafied borders. Our methodological proposal starts from the EU’s publication of calls for tender and contract award notices as a born-digital repository (eTender). Digital methods are useful here to repurpose this archive, originally set up for transparency purposes with regards to EU procurement activities. Combining qualitative and quantitative elements, digital methods help us improve large-scale data access as well as reorganise and restructure the archive to understand the presence and development of datafication. They are especially suited for this reorganisation, as they provide ‘a lens that allows researchers working on a problem to view a relevant textual corpus in a different light and at a different scale’ (Mohr et al., 2013). In our case, digital methods revealed different types of categories, linkages and parts of contracts that we followed up with close reading at critical junctures of these categories.
The paper proceeds in three steps. We start with a discussion of methods in critical border and security studies and the challenges that datafication poses for research, given the combined secrecy of borders and opacity of technologies. Secondly, building on a data feminist approach, we discuss our use of digital methods and some of their limitations. Thirdly, we show how qualitative methods of close reading tender documents can address some of these limitations. We conclude with reflections on the broader relevance of this transdisciplinary methodology for research on borders.
Digital technologies at the EU borders
For more than a decade now, the exponential use of digital technologies and related datafication of border governance has raised many questions. Researchers and activists have diagnosed these transformations from the ‘biopolitical’, ‘biometric’ or ‘digital’ borders to ‘socio-digital borders’, ‘iBorders’, ‘big borders’ or ‘deep borders’ (Amoore, 2006, 2021; Broeders, 2007; König, 2016; Metcalfe and Dencik, 2019; Pötzsch, 2015; Walters, 2002). These diagnoses have emerged from qualitative, often ethnographic analyses of practices in situated locations of border governance and security. Other critical scholars and activists have ‘followed the money’ either through EU contracts and research projects (Lemberg-Pedersen et al., 2020; Martin-Mazé and Perret, 2021) or other aid funds to trace how migration and asylum funds have been increasingly subsumed to security purposes (UNHCR and ECRE, 2018, 2020). For instance, Privacy International has highlighted how EU Member States have directly and indirectly invested in border surveillance technologies (Privacy International 2014). Statewatch has shown that EU research funding has often been used to develop biometric identification systems in the name of ‘smart borders’ (Statewatch, 2022).
These different methods, both qualitative and quantitative, have led to nuanced insights about which technologies are used at the EU borders and digital transformations over time. In so doing, researchers have nonetheless continued to contend with the limitations of secrecy and opacity at the EU borders. Secrecy has often been translated into limitations of access, whether to sites, interviews or documents. At the same time, scholars have drawn attention to secrecy as relational, complex and non-binary (Bosma et al., 2019). Similarly, opacity has emerged particularly in relation to how these technologies work and the effects that they have on migrants, particularly the harms that they cause. Unlike secrecy, however, opacity does not refer to hiddenness, but to the incomprehensible or inaccessible ways in which systems work (Wright, 2020: 7). The distinction between secrecy and opacity can also be formulated as that between invisibility and illegibility. This distinction has methodological relevance for the study of borders, as it helps us clarify the ways in which transparency has been mobilised to support research.
Faced with problems of secrecy and opacity, critical border and security scholars have drawn upon transparency as a practice of governance by liberal states. Websites such as ‘Whatdotheyknow’ and training in using FOI methodologically have been some of the tactics made possible by the requirements of transparency (Walby and Luscombe, 2019). Yet, the enactment of the transparent state, which ‘calls forth data publics who can do their own experiments, establish matters of fact, see the state for themselves and disseminate their results to others’ (Ruppert, 2015) has its limits. It relies on the production of revelatory knowledge (Aradau and Van Munster, 2011), while the power of visibility and shaming does not solve the problems of opacity as illegibility. Cultural theorist Clare Birchall points out that the injunction to enact transparency ‘was nearly impossible, necessitating skills and free time most ordinary citizens do not possess’ (Birchall, 2021: 50). Indeed, new networks of professionals and activists have been mobilised to enact and act upon the transparency requirements of the state. These emerging publics need to be both skilled and active, capable of bringing digital methods to the dispersed data that is increasingly everywhere in order to make it visible and legible. Therefore, the use of digital methods has remained limited to research centres, disciplines such as digital humanities and media studies, and civil society actors. In critical research on borders and/or security, only few studies have tried to combine qualitative and digital methods (Martin-Mazé and Perret, 2021). Where digital methods have been used, researchers have often focused on migrant practices, such as migrant use of digital devices and social media, or conversely, digital analyses of how migration and ‘crisis’ are represented on social media (Gillespie et al. 2016; Sánchez-Querubín and Rogers, 2018).
Transparency as practice has further limitations given that the EU datafied borders work at the ‘interface’ of the public–private sector. For Martins and Jumbert, public–private partnerships specifically on border security technologies development are ‘less visible’ and appear opaque (2020: 14). They point out how private ‘expertise’ is presented as a position of ‘objective neutrality’, which removes ‘the need to justify what methods these experts rely on to make their claims’ (Martins and Jumbert, 2020: 12). Lori and Schilde go further in arguing that relations between private and public actors in the context of migration and border control are entangled in a political economy of global security that produces an ‘increased […] opacity’ (Lori and Schilde, 2020: 4). Opacity entrenches asymmetric power relations. This is particularly evident in relation to illegal pushbacks in the Mediterranean, where Frontex’s responsibility has been questioned. Despite public denials by the Frontex ex-director Fabrice Leggeri and repeated statements about respect for ‘fundamental rights’, researchers from Forensic Architecture, NGOs such as Privacy International, and activists from Bellingcat have used digital devices and skills to substantiate the allegations of pushbacks (Bellingcat, 2020; Forensic Architecture, 2020).
Therefore, invocations of transparency aim to transform asymmetries of power between states, citizens, and non-citizens by claiming that institutions and the state itself need to become transparent in order to be held to public scrutiny. Joanna Redden shows that one of the main limits of ‘the transparency ideal is the assumption that greater transparency will lead to greater civic involvement and response’ (Redden, 2018: 3). While transparency promises to lead to ‘asymmetry reduction’ (Alloa, 2018), asymmetries of power can also be enacted or even intensified through claims for transparency, particularly if citizens lack the infrastructures and competences needed to work upon transparency. Indeed, in the case of the EU borders, transparency requirements around public–private partnerships do not reduce or otherwise challenge these asymmetric relations, as the involvement of private companies has increased over the past decades due to the growth in securitisation practices and techno-solutionism in border management (López-Sala and Godenau, 2020). 3
Finally, research methods mobilising transparency as practice and power are also political in that seeing and knowing are assumed to mobilise publics into action. Forensic Architecture, for instance, designs their interventions within a political framework that relies on litigation (Schuppli, 2020). The language of legal trials, of direct and circumstantial evidence and of violation is central to their political work. It is thus important to supplement legal disputes with political contestation, exposing how problems are framed epistemologically and politically (see Tazzioli and Lorenzini, 2020). While seeing transparency as inadequate for governing algorithmic systems, Mike Ananny and Kate Crawford have argued that the limits of transparency can become ‘starting points for reconstructing accountability for systems that cannot be seen into, held still, or fully traced’ (2018: 984). How can we give an account of datafied borders without assuming that technologies and those who design them can be made fully transparent, visible and legible? We propose the terminology of intelligibility as the methodological aim of mobilising transparency to make sense of how problems are framed and dealt with at the EU borders.
To supplement visibility and legibility with intelligibility, we build on the data feminist approach developed by D’Ignazio and Klein (2020). Given our focus on methods for researching datafication at borders, we draw on four principles to develop methodological orientations for our work. Firstly, we disrupt the dichotomies between qualitative and quantitative methods by working with and through the limitations of digital methods. While digital methods are often assumed to be quantitative, we show that they interweave interpretation and quantification. Secondly, we challenge the binaries of opacity and transparency by introducing intelligibility to supplement methods aimed towards visibility and legibility. D’Ignazio and Klein do not reject the importance of transparency, but argue that transparency is limited on its own, as it does not account for the need for reflexivity about one’s positions and power relations (2020: 82). This takes us to the third orientation of our methodological work – to examine and challenge power relations at borders. By focusing on contracts, we can visualise power networks at the EU borders. Finally, a data feminist approach invites us to make all the work of method visible, from formulating questions, to collecting, cleaning, processing and interpreting the data.
In the next section, we discuss the digital methods we have developed starting from contracts awarded by two EU agencies, Frontex and eu-LISA. While the contracts are publicly available as part of a transparency agenda in public procurement, much remains obscure and illegible in the detail of the technologies developed and used, connections between companies, and the actions of these agencies. We conclude the section with reflections on what is required methodologically to develop intelligibility about datafication.
Digital methods: Making datafication at the EU borders intelligible?
Founded in 2004, Frontex had its mandate expanded and strengthened in 2019. Frontex supports border control operations by deploying its own border guard officers and assets. The agency invests in surveillance and datafication solutions to better monitor European borders. For instance, Frontex developed the European Border Surveillance System (EUROSUR), a distributed web-based application for data exchange between Frontex and national coordination centres about the situation at European borders (Jeandesboz, 2017; Tazzioli, 2018). In 2011, the EU also established eu-LISA, which became operational in 2012. eu-LISA oversees the maintenance of IT systems related to border management, asylum and migration (eu-LISA, 2021a; Jones, 2019). As indicated in the introduction, since 2019, the largest calls for tender have been within the framework of interoperability through so-called ‘transversal’ services. Even though eu-LISA and Frontex are two different agencies, they collaborate closely in the datafication of EU borders. Their recent joint procurement makes it even more relevant and pressing to analyse the contracts they have awarded.
Driven by securitisation and techno-solutionism, private actors have taken a significant role in the datafication process of border management in the EU (López-Sala and Godenau, 2020). The UN Special Rapporteur on contemporary forms of racism, racial discrimination, xenophobia and related intolerance, Tendayi Achiume, highlighted that the EU budget for the management of borders migration and asylum for 2021–2027 would make more than EUR 34.9 billion, outsourcing part of its investments to private companies (Achiume, 2020). Moreover, the connections between EU border agencies and private companies are known to be opaque and inaccessible to academics, journalists and activists (Douo et al., 2021; Glouftsios, 2021; Martin-Mazé and Perret, 2021). Yet, these agencies also produce a plethora of publicly available documents, annual reports and information materials, which have been widely analysed in the literature on borders and security (Glouftsios and Scheel, 2020; Leese, 2022; Loukinas, 2021).
However, there has been less attention to the contracts awarded by the two agencies and their calls for tender. Frontex and eu-LISA are constantly issuing calls for tender and increasing relations with private companies (Lemberg-Pedersen et al., 2020). These contracts have been awarded, among other reasons, to develop large-scale databases, interoperable architectures to connect national and international databases, and algorithmic-based systems for aerial and maritime surveillance. Contract award notices and tender documents make visible the relations between the two agencies, public agencies and private actors, and the datafication technologies deployed at the EU borders.
Building on a data feminist approach (D’Ignazio and Klein, 2020), we propose to examine power asymmetries at the border by analysing public procurement information by these two EU agencies and private companies. In this section, we discuss the digital methods we have developed within a transdisciplinary team to analyse these contracts. We reflect on and disrupt the limitations of quantitative methods through qualitative methods. In other words, contracts are analysed automatically by code scripts and qualitatively by the authors. Beyond methods that ‘follow the money’, which work mainly with quantitative data, our digital methodology brings together quantitative and qualitative data in the contracts. Our methodology also challenges binaries of transparency and opacity by aiming to develop intelligibility. As we have seen in the previous section, while the contracts are publicly available (assuming a notion of transparency), technical and coding skills are needed to find hidden connections (reversing opacity). Digital methods allow us to understand how an oligopoly of private companies control the development and implementation of the main biometric database systems at the EU borders. Finally, we make the digital research labour visible by showing the work of data cleaning and transforming unstructured data into structured data.
Concretely, the digital methodology consists of four steps: (a) data acquisition from tender documents made public, (b) structuring information into a dataset, (c) data cleaning and (d) data and network visualisations. First, we retrieved all tender documents from both agencies. We then extracted features from the relevant sections of the document, such as the name of the contractor, year of the contract, total value and the number of tenders. To do so, we used regular expressions (regex) that find string patterns, which in our case are the titles of sections within the contract. This information is structured and stored in a dataset where each row is a contract and each column is a feature of the contract. Then, we cleaned the dataset by standardising company names that change over time or contract values that appear in currencies other than euros. Finally, we visualised this data to shed light on connections between the EU agencies, datafication technologies and private companies.
Hidden labour: Making all the research labour visible
As we previously explained, the empirical material used are contract award notices, which are publicly available on the eTendering platform. 4 This portal allows free public access to calls for tender documents such as contractual documentation, technical specifications, annexes and questions and answers. This EU platform has a search engine whereby users can find documents using a range of criteria, for example, searching by European institution, type of document and award criteria.
Data acquisition. Through the expert search, 5 we queried all eu-LISA and Frontex notices. After executing a query to retrieve all the available contracts on the platform, we obtained contracts issued from 2014 to 2020. This indicated that the EU digital platform stores contracts since 2014. We copied the content retrieved into a file, creating as a result the first corpus of the datafication of borders in the EU. 6 The contract documents are divided into sections consistently. Finally, for each agency, we created two different corpus files, which contain the full text of all contracts (Figure 1).

Making digital labour visible: Diagram of the digital methodology.
Structuring text. The contracts are unstructured data, i.e., data that is not organised in a predefined manner nor easily analysed by a computer program. Generally, this type of data needs to be structured to be analysed. In order to structure and build a dataset from these documents, we used regex functions to find specific sections and subsections.
Data cleaning. Discussions of digital methods and data visualisation often omit the importance of data cleaning, which is a central part of working with data. Making this labour visible is both a methodological step and a feminist orientation to showing every step and decision taken while coding and cleaning data (D’Ignazio and Klein, 2020). We cleaned the data to improve the quality of our analysis. Cleaning up and grouping subsidiary companies with their corresponding parent companies was a laborious task, which is usually hidden in data analysis. We therefore aggregated Gemalto Cogent and 3M Belgium (Identity Management) with Thales, Bull with Atos and Morpho with IDEMIA. We renamed these companies to make intelligible the solidification of power through mergers and acquisitions. We converted the value of contracts from different currencies into EUR given that some Frontex contracts were reported in the Polish currency (Zloty). For the conversion, we used the exchange rate of the date of the contract using an online service. We then transformed commas into dots to normalise decimal points. Finally, we obtained consistent datasets of contract award notices for both EU agencies. 7
Data and network visualisation. As a final step for our methodology, we examined connections between private actors that develop datafication technologies at the EU borders. To do so, we used exploratory statistics and network visualisations, which are powerful instruments that showcase asymmetric relations. We showed the investments of both agencies per year and per type of contract. We also investigated the most expensive contracts and the most awarded contractors. By analysing the content of the contracts, we observed that companies usually apply to tenders as a consortium or group of economic operators. By using network analysis, we then visualised the connections between companies.
Power asymmetries: Who gets EU contracts and for what?
This section presents the overall analysis of the eu-LISA and Frontex contracts.
Descriptive statistics of contracts
We first analysed the main statistical characteristics of our datasets. This step uncovered general characteristics of our data. From 2014 to 2020, we gathered 44 and 144 unique contract award notices by eu-LISA and Frontex, respectively. We created two different datasets given that contracts contain several lots (subdivisions of contracts). This analysis showed a growing interest of both agencies in datafication technologies, awarding a large number of contracts for developing IT and data surveillance systems. The insights are
Our findings show that a large part of the datafication at the EU borders is financed by eu-LISA and developed by French companies which outsource services. Important to highlight is that contracts do not, however, provide information regarding subcontracting.
Data visualisation of contracts
Figure 2 illustrates the money allocated by eu-LISA and Frontex to private companies. Between 2014 and 2020, eu-LISA and Frontex invested EUR 1465M and 434M, respectively. Both agencies have boosted their investments in sub-contracting since 2017, multiplying spending by up to six times. However, eu-LISA’s expenditure is five times larger than Frontex’s. We identified two inflection points in eu-LISA’s budget, related to the maintenance of IT systems and data infrastructures (Figure 2): 2017 and 2019–2020. In 2017, eu-LISA invested EUR 194M in the maintenance of VIS and EUR 5M in the increase of Eurodac’s capacity. This Eurodac spending was needed ‘due to a huge increase in the number of transactions as a result of recent immigration dynamics’, according to the contract (eu-LISA, 2016). Frontex reached its peak spending in 2019, with EUR 51M invested in deportation flights (non-scheduled air transport services and travel agencies and EUR 27M invested in aerial surveillance services).

Million Euros (EUR) spent by eu-LISA and Frontex on border privatisation during 2014–2020. Overall, the increase in private financing has been significant in recent years, causing a rise in expenditure by as much as 500–700%.
Figure 3 shows investment per type of contract. We observe that eu-LISA is investing most in IT services. These contracts are related to well-known datafication infrastructures for border control and migration management (EES, Eurodac, SIS II and VIS). Frontex finances a diverse array of contracts (software, office supplies, surveillance services, data services, interpretation services, etc.). Amongst the most expensive contracts are those supplying aircraft systems for maritime aerial surveillance such as drones delivered in Greece, Italy or Malta. As previously mentioned, deportation flights are also a relevant area of investment when analysing Frontex contracts. Interestingly, Frontex has declared its shift of investment in software and databases to datafied surveillance technologies (Frontex, 2021b).

Million Euros (EUR) spent by the EU agencies per type of contracts during 2014–2020. While eu-LISA is investing in data infrastructures systems for migration governance, Frontex is investing in aerial surveillance and deportation flights.
In Figure 4, we show the top 10 most expensive contracts awarded by eu-LISA and Frontex. In 2020, eu-LISA invested over EUR 400M in the implementation and maintenance of the EES. 8 This system will be used to monitor cross-border movements of temporary visitors to the Schengen area (Jones, 2019). Concretely, one of the contract descriptions establishes the implementation of the shared Biometric Matching Service (sBMS) for EES, which will provide a digital platform where biometric templates will be extracted, stored and compared from biometric samples. Moreover, the contract also includes foreseen evolutions for the future integration of SIS II, Eurodac and VIS with the central sBMS in the context of interoperability. The second most expensive contract (EUR 194M) was awarded in 2016 for the maintenance of VIS – a system used to store information about short-stay Schengen visas. It has the capability to match biometrics for identification and verification of individuals. The third most expensive contract (EUR 187M) was awarded in 2020 to several contractors for designing and supporting core business systems and interoperability components.
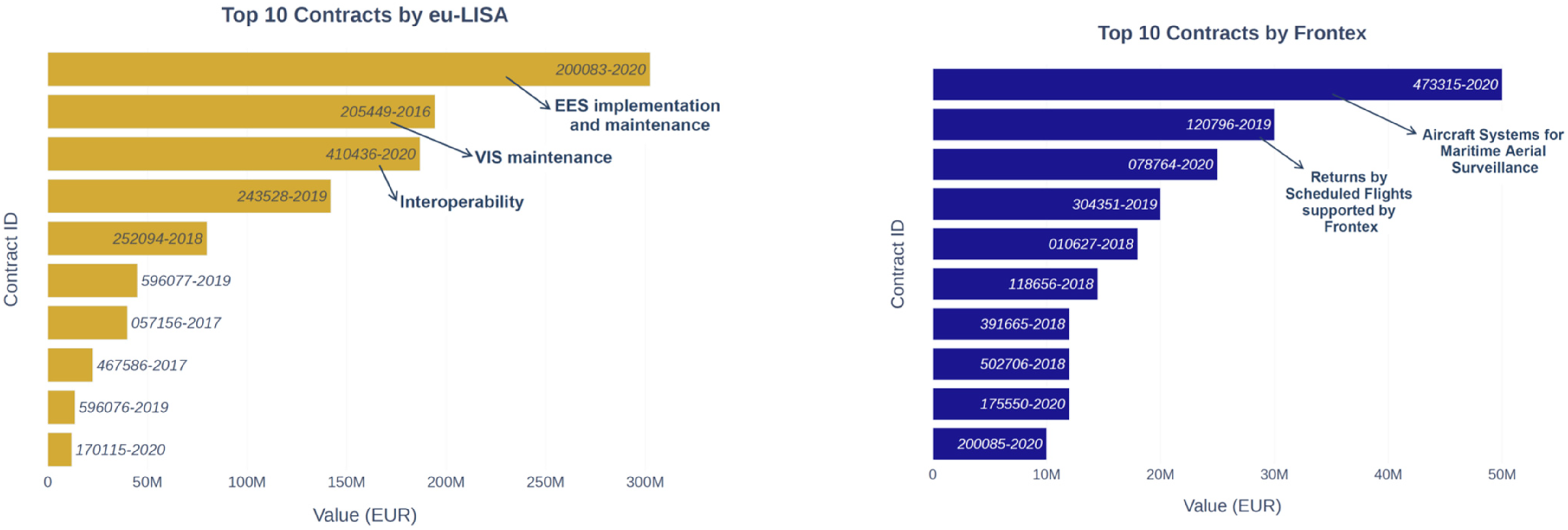
The top 10 most expensive contracts by eu-LISA and Frontex. Most of these contracts are related to datafication technologies.
Frontex’s most expensive contract (EUR 50M) was awarded to acquire surveillance drones for maritime purposes in Greece, Italy and Malta. Their second most expensive contract (EUR 30M) was for financing return operations through deportation flights organised by EU member states. This finding shows that one of the most important activities of Frontex's use of public money is to organise deportation flights, whose violence has been ethically questioned and challenged by civil society and human rights institutions.
Biometric and consultancy companies are the main beneficiaries of the making of datafied EU borders (Figure 5). IDEMIA and Sopra Steria are a consortium of private actors, which won the contract for the implementation of the sBMS part of the EES. IDEMIA is a multinational technology company based in France that sells facial recognition and other biometric technologies to private and governmental actors. Sopra Steria is a France-based consulting, digital services and software development company. The consortium named Bridge 3 (formed by Accenture, Atos and Morpho) was awarded the second most expensive contract to maintain VIS. Accenture is a multinational company based in Ireland, which provides consulting services. Atos is a French multinational IT company. Morpho and Oberthur Technologies merged in 2017 and became IDEMIA. The EUR 187M interoperability contract announced by eu-LISA and Frontex was awarded to a large number of companies: Intrasoft, ARHS Development, Atos, Sopra Steria, Everis and European Dynamics (eu-LISA, 2020a). Finally, IDEMIA, Sopra Steria and Atos have been repeatedly awarded contracts by eu-LISA in order to implement, maintain and update the IT systems for the datafication of borders. As Glouftsios (2021: 54) observed in relation to the VIS database, parts of the specifications were developed during the call for tender by the companies that also won the contract: Sopra Steria and Hewlett Packard (HP).
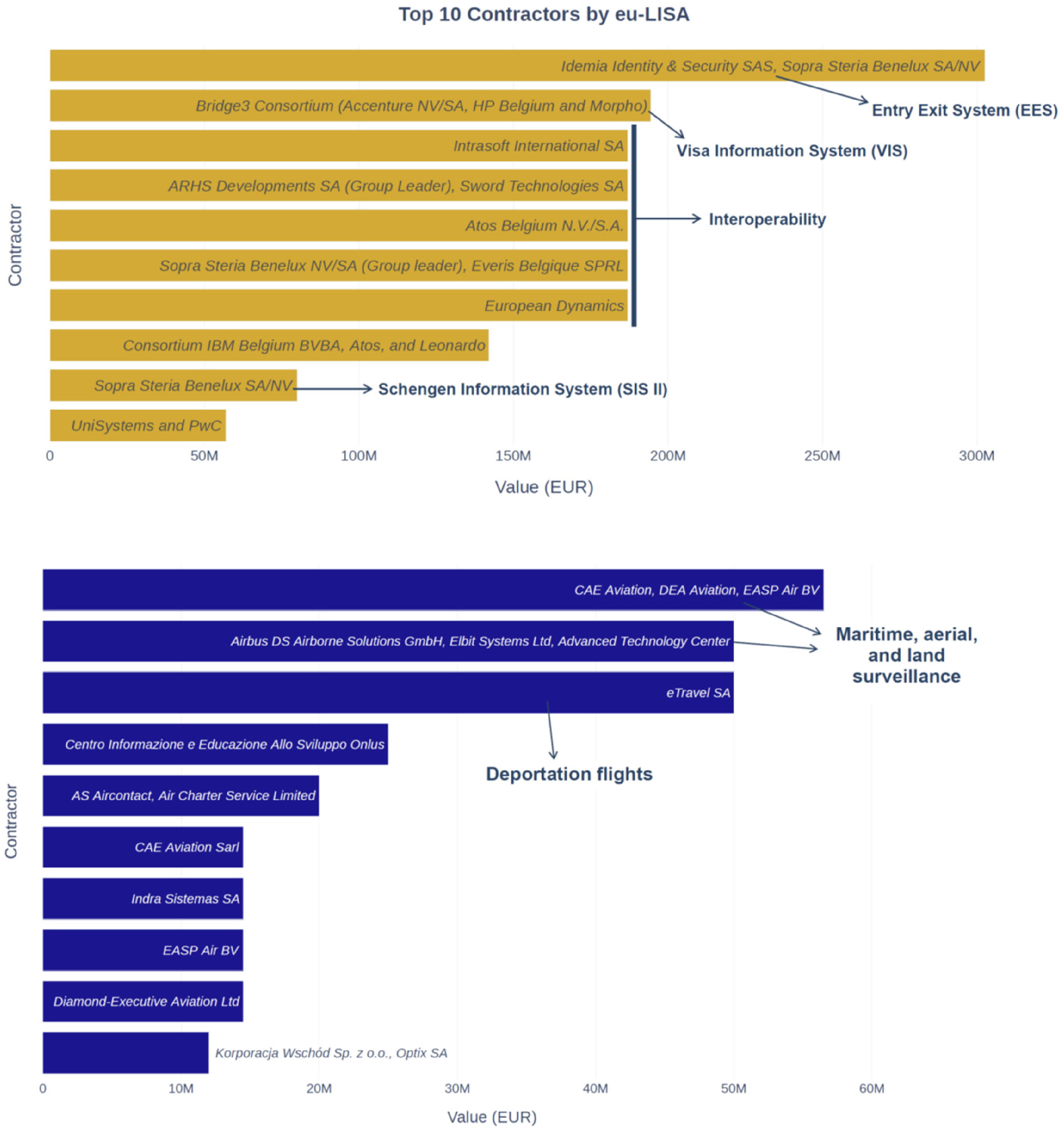
The most awarded contractors by eu-LISA (top) and Frontex (bottom).
Frontex’s most expensive contracts are related to surveillance technologies using a range of datafication practices. The group of actors formed by CAE Aviation, DEA Aviation and EASP Air BV are recurrent beneficiaries of Frontex contracts. They won more than eight contracts related to aerial surveillance systems for border and coast guard functions. CAE is an aviation company based in Luxembourg, DEA is also an aviation company based in the UK, and EASP Air BV is a Dutch-based service provider for aerial maritime surveillance. Airbus and Elbit were also awarded the drones contract in 2020. Airbus is a multinational aerospace corporation, which also produces military aircraft. Elbit is an Israel-based international defence company that develops military platforms, creating new technologies for defence and homeland security. Finally, eTravel SA, one of the biggest travel agencies in Poland, where Frontex is based, won the deportation flights contract.
Figures 6 and 7 visualise the network of private actors with contracts awarded by eu-LISA and Frontex, respectively. In these figures, every node is a company. Two nodes/companies are connected through an edge if they won a contract or entered a call for tender together. The size of companies’ names represents the degree of their node, that is, how strongly it is connected to other companies. The edge thickness expresses the volume of the contract awarded, that is, the thicker the edge the more expensive the contract awarded.

Connections between private actors in eu-LISA. The companies’ names show the most recent name of the company or the name of the company that acquired the previous one(s) at the time of writing.

Connections between private actors in Frontex.
The networks of eu-LISA contracts (Figure 6) clearly indicate several asymmetries in the relationships of the involved actors. There is a noteworthy group of private actors formed by biometric, software, and consultancy companies (Sopra Steria, 3M Belgium, IDEMIA, Accenture, Atos, Everis, Thales, etc.) that frequently are awarded contracts. This cluster represents most of the companies that received the contracts to implement and maintain data infrastructures (Eurodac, EES, VIS and SIS). Moreover, companies that were awarded as a consortium in the past are nowadays part of the same family (Bull’s parent company is Atos, 3M Identity Management and Gemalto Cogent have been acquired by Thales, and the OT-Morpho merger was renamed IDEMIA). Interestingly, these private actors cooperate rather than compete for these contracts. For instance, the joint venture between Atos and Thales has been announced to ‘create the European champion in big data and artificial intelligence for defence and security’ (Atos, 2021), while the partnership between IDEMIA and Sopra Steria develops international and national biometric border control systems (IDEMIA, 2020, 2021). Award-winning or cooperative contract connections within the framework of interoperability are also shown (Sword Technologies and ARHS Development).
Further visual analysis of the Frontex network of contracts reveals that private companies are more dispersed than for eu-LISA (Figure 7). For the network of Frontex contracts, we can observe a relevant conglomerate of six Italian and French interpretation-related companies, and NGOs related to the call for tenders that the EU agency awarded in 2020 for EUR 25M, to establish high quality language and cultural expertise services. The cluster formed by CEA Aviation, DEA Aviation and other companies is also relevant, as they received contracts with a volume of EUR 50M for aerial surveillance systems. The other cluster formed by Elbit, Airbus and Advanced Technology represents another call for tender for drones and maritime surveillance. Finally, the cluster formed by air transport companies (AS Aircontact, Air Charter Service, etc.) is related to the contracts that Frontex awards to organise deportation flights.
Our analysis of contracts awarded by two of the main agencies advancing datafication and border governance has shown how different ecosystems of private actors have emerged around the two agencies. It has also helped us understand which areas have been prioritised for border control and migration management. While datafication is central for eu-LISA, Frontex seems to be involved in a wide range of operations, which is unsurprising given its broader and operational mandate. These digital methods have given us many insights, but much is still missing to make datafication intelligible. In the next section, we build on these digital methods through qualitative analysis of selected tender calls, annexes and associated documents to better understand the datafication of borders. We focus on three aspects that have emerged from the previous sections: infrastructures and devices of datafication, non-binary relations between opacity and transparency, and the politics of datafication.
Interpreting datafication: Qualitative methods
From devices to infrastructures of datafication
The digital visualisation of eu-LISA and Frontex contracts has shown the differences between the networks of private actors around each of these institutions, mainly a much more dispersed network for Frontex and a more centralised one for eu-LISA. What does this tell us about the EU datafied borders? To make the differences between the two networks intelligible, we needed to return to methods of close reading tender documents.
The eu-LISA network is immediately recognisable as infrastructural, in the sense that ‘borders-as-infrastructure consist of large-scale networks that connect to particular local situations’ (Dijstelbloem, 2020: 41). STS scholars have explained the distinction between devices and infrastructures as an analytical one rather than an ontological difference. Thus, ‘infrastructures can be imagined as series of interconnected devices that are joined up to form a web’ (Bowker et al., 2019: 6). Unlike devices, which are often analysed as single instruments, artefacts or technologies, infrastructures bring attention to interconnections. Through this analytical vocabulary, we can understand the increasing importance of infrastructures of datafication. Frontex earlier invested in infrastructure such as EUROSUR. Here, many of their contracts were focused on devices, both digital or non-digital. However, recent joint contracts between Frontex and eu-LISA on Transversal Operations and Engineering Frameworks allow us to trace a move towards joint infrastructures of datafication between Frontex and eu-LISA (eu-LISA, 2020b, 2021b).
The distinction between devices and infrastructures also has political consequences. Our network visualisation of eu-LISA contracts reveals an oligopoly of consultancy and biometric companies that develop automated biometric identification systems. Ordered by the number value of contracts for each database, Table 1 shows that Sopra Steria and IDEMIA are commonly awarded contracts regardless of the database (EES, Eurodac, SIS II or VIS). Building infrastructures makes it difficult to change private actor provision and raises questions about what kind of accountability is possible in relation to these developments. Moreover, a close reading of recent joint calls for tender by Frontex and eu-LISA allows us to offer a more in-depth interpretation of these visualisations and the role of datafication. The companies submitting tenders are required not only to have experience working with large-scale IT systems, but to have developed and implemented systems that are considered ‘critical infrastructure’, systems that are ‘related to a border management system using multimodal biometrics’ and systems ‘supporting law enforcement identification’ (eu-LISA, 2019b: 14; 2020b: 14). The eligible companies for the EES tender need to have experience of producing infrastructures for law enforcement and border management, thus reproducing the same oligopoly of companies.
Summary of the cost of data infrastructures developed for EU migration governance. Since 2014, eu-LISA has invested EUR 806 M in the implementation and maintenance of these systems. Sopra Steria, IDEMIA and 3M Belgium are usually awarded for this purpose.

The money invested in the EES was EUR 444 M when the two contracts were awarded. Subsequently, one contract was modified and its value increased from EUR 142M to EUR 212M (see https://ted.europa.eu/udl?uri=TED:NOTICE:265563-2021:TEXT:EN:HTML).
In the case of Frontex, a close reading of the tender documents highlights that datafication is increasingly incorporated even within contracts which at first sight do not seem to be related to datafication or digitisation. As we have seen in the previous section, one of the largest contracts awarded by Frontex concerns deportation flights. Frontex has been supporting deportations by EU Member States technically and financially (Frontex, 2018). The contract aims to add scheduled flights to the use of charter flights for deportation. While datafication is not present in the contract award notice, the tender documents show that Frontex uses Microsoft SharePoint to manage ‘Frontex Applications for Return (FAR)’ and that the new contract would need to create and implement an interface that interconnects with the Frontex system. Thus, the travel agency would not just secure the tickets and flight connections, but they need to develop processes and technologies for datafication as well. According to Frontex, ‘[t]he Travel Agency will put at the disposal of FAR 3 dedicated servers, respectively dedicated to production environment, training environment and one for developers’ (Frontex, 2018, 5). This digital environment supports data sharing between Frontex and other actors. Frontex contracts for maritime and aerial surveillance similarly place data generation, collection and processing at the heart of the contractual obligations (Frontex, 2019). While devices of datafication appear relatively dispersed given the Frontex operations, we can also see how infrastructures emerge through contracts that embed, extend and standardise interconnections between the various devices that collect, exchange and analyse data. In 2019, Frontex and eu-LISA issued a joint call for tender for the ‘Transversal Engineering Framework’ and ‘Transversal Operational Framework’ to support interoperability and the development of new systems (eu-LISA, 2020b, 2021b). Indeed, these contracts move towards expanding and stabilising infrastructures of datafication at the EU borders.
Neither opaque nor transparent
As the first section discussed, making things transparent is not equivalent to making them intelligible. For instance, public procurement portals, such as TED eTendering, are set up to allow users to hold institutions, governments and agencies to account and be more transparent. In practice, access to information on these platforms can be difficult and requires expert skills. We encountered the first difficulties retrieving the data from the eTendering platform. We had to use the expert search with a specific syntax to gather the contracts from both agencies. Once we could retrieve the contracts, skills of text mining and data analysis were needed to structure and explore this born-digital archive. Moreover, the contracts also needed the labour of ‘data cleaning’ to structure the information they contained. Users without such skills would neither be able to obtain all the contract award notices nor interrogate the data across all the contracts. While the EU also maintains a list of contracts in Excel format, this list contains less information than what appears in the procurement documents. For instance, the description of the contract is not available.
As we started to structure the data, we also noticed that many of the contracts contained unspecified subcontracting provisions. The eu-LISA ecosystem of contracts is centred around a small group of private actors with further layers of opacity and illegibility despite claims of transparency. The contracts indicate a vague network of subcontractors which remain opaque, meaning other private actors who take part in designing and implementing new data infrastructures remain unknown. Therefore, the contracts are neither opaque nor transparent, but entanglements of both.
Close reading of the tender documents shows that opacity is constitutive of EU tenders and contracts rather than diminished through transparency. Contractors for eu-LISA are required to hold a ‘positive security clearance at least at EU Secret level issued by a National Security Authority prior to providing services under the framework contract’ (eu-LISA, 2019b). The guide to candidates also mentions non-disclosure agreements (NDAs) for personnel, although not much detail is provided. All candidates and personnel need to sign a declaration of confidentiality and security both concerning the technical specifications and all information related to the contract. According to these requirements, ‘they will have to declare not to divulge to third parties or use for their own benefit or for the benefit of any third party any document or information not available publicly, even after the completion of the tasks’ (eu-LISA, 2019b: 7). The Annex for the Transversal Engineering Framework outlines comparable requirements for ‘stringent obligations regarding security and professional secrecy’. Similarly, staff from the private companies ‘shall sign an individual declaration of confidentiality (form provided by eu-LISA)’ (eu-LISA, 2020b: 12). The contours of illegibility through secrecy, confidentiality and non-disclosure remain fuzzy, as they encompass more and more practices at the EU borders and cannot be easily traced by researchers or oversight bodies.
Politics of border datafication
Finally, a close reading of tender documents can draw attention to absences and exclusions – following feminist traditions of analysing how distinctions between what counts and what does not are drawn in practice. As accounting technologies, contracts are focused on what counts within the imaginations of market-driven efficiency and innovation. For instance, data protection or other fundamental rights were not discussed in the tender documents. The tender documents do not only reproduce securitising discourses, as in the case of eu-LISA’s EES system, which is envisaged to ‘contribute to the prevention, detection and investigation of terrorist offences and of other serious criminal offices [sic]’ (eu-LISA, 2019a: 3). They also only focus on technical aspects. Annex I of the EES tender call specifies the personnel roles needed for a particular contract. The expert roles envisaged for the EES system are exclusively technical: from programme managers to system architects, system engineers, test engineers and biometric test engineers. The Biometric Test Engineer is tasked to ‘execute the required test case and analyse the result(s)’ in particular in relation to ‘local and performance test’, ‘accuracy test’ and ‘other test defined in the test plan’. The biometric specialist has to ‘analyse and maintain the requirements regarding the biometric matching systems’ configuration in terms of performance, accuracy, data quality, and transaction’ (eu-LISA, 2019a: 24). The annexes for the Transversal Engineering Framework have tens of pages of technical role descriptions such as engineers, administrators and project managers (eu-LISA, 2020b).
The tender documents have no provision for accountability beyond the specification of technical operability and performance. At the same time, the tender documents contain fragments that reveal political decisions at the heart of these infrastructures. In the Guide to candidates, eu-LISA (2019b: 14) highlights that the fingerprint 1-to-N response time should be ‘on average equivalent to one second each 10 million of gallery size (i.e. response time of two seconds for a gallery size of twenty million records)’. Large biometric data and low response time often translate into lower accuracy. Yet, these translations and decisions as to what counts are excised from the contract as technical accountability.
Attention to what is absent in the tender documents makes intelligible what is discounted in the production of infrastructures of datafication. While the European Commission is boosting its position in the global race for AI ethics, there are no discussions in these documents on for example, fundamental rights or the impact of these infrastructures on vulnerable people. While the EU’s recent proposal for AI regulation categorises biometric identification systems as high-risk solution ‘for the purpose of law enforcement’, this regulation does not apply to the biometric databases outlined in Table 1 (European Commission, 2021: Article 83).
Conclusion
The datafication and privatisation of the EU borders have been extensively discussed by border and security studies scholars, civil society actors and activists. This article has proposed to develop a transdisciplinary methodology to make dynamics of datafication at the EU borders (partially) intelligible. We have done this by analysing the contracts awarded by eu-LISA and Frontex between 2014 and 2020. We started with digital methods for analysing the contracts to advance insights about the actors that promote techno-solutions and datafication for border control and migration management. We have supplemented digital methods for the analysis of contracts with close readings of selected tender documents.
Our methodological work has mobilised several principles of data feminism, from making all the labour visible, to challenging dichotomies between qualitative/quantitative methods, disrupting binaries of opacity/transparency and examining power relations. Through our analysis of contracts, we have worked at the interstices of transparency and opacity, demonstrating that we need to supplement the mobilisation around transparency with intelligibility. Our research provides opportunities to attend to power relations by tracing the datafication of EU border and migration control as a thoroughly private undertaking: from the consultancy companies that develop feasibility studies to the private companies that build the technologies, often in collaboration with the same consultancies. Every time one of the border and migration databases needs to be updated, eu-LISA announces a new contract which is likely to be awarded to the companies that designed and implemented them. Importantly, our visualisation has suggested a shift towards infrastructures of datafication to supplement and interconnect devices, highlighted through the rollout of joint tender calls for ‘transversal’ frameworks. While the network of companies being awarded Frontex contracts is much more dispersed in terms of company focus, the network of companies from the eu-LISA database contracts is centralised around the companies that develop and maintain existing and future EU databases. Through close reading of tender documents, we show how datafication enters contracts that may appear removed from datafication – such as Frontex’s deportation flights, when in reality they are linked, dependent and embedded in datafication processes and practices. We have therefore shown that datafication is more extensive and insidious, expanding beyond databases and surveillance technologies to underpin more and more border infrastructures.
However, our methodological work has also been a frustrating process. Contracts are considered a public and transparent resource, but they are by no means sufficient in making the visible and legible into the intelligible. We have described the difficulties and labour linked to data analysis in born-digital archives of unstructured documents. We spent a lot of time discussing workflows and translating concepts between disciplines and cleaning company names and contract values. The transdisciplinary methodology developed was made possible by our different backgrounds, disciplines and skills. Another set of difficulties concerned the limitations of what can be done with the data in the contracts. While these contracts offer many insights, they only enable partial intelligibility, as they produce new opacities, absences and exclusions. As discussions of rights and data protection are obscured or even ignored through the technical processes of datafication and the allocation of private contractors to technical job classifications, datafication remains a privatised, technical, secretive and unintelligible development at the EU borders. This paper paves the way for the use of digital methods to analyse public procurement documents in critical security and border studies. Given that the data and code of this methodology has been made open and publicly available, we hope that academics, activists and journalists might explore other directions of the analysis, such as an analysis of how much money is spent per year on each contract, an analysis of the network of companies together with Europe Horizon and FP7 project schemes, or further connections with border management contracts in EU Member States.
Footnotes
Acknowledgements
We would like to thank the four anonymous reviewers and the editors of Big Data & Society for offering constructive comments and thoughtful suggestions for revision. Earlier versions of this article were presented at the STS-MIGTEC CIRCLE in 2021, the ‘New Voices in Security Studies’ seminar at King’s College London, workshop on ‘Datafication technologies, counter-power and resistance at the EU borders’, also at King’s College London, and at the Community Gathering organised by Amnesty International in October 2021. We are grateful to Amanda Chisholm, Bushra Ebadi, Georgios Glouftsios and Jasper van der Kist for the invitations to present our work. We would like to thank the discussants and participants for the help that they kindly provided to strengthen the argument. We are also grateful to Ibtehal Hussain for her comments and careful reading of the final manuscript and to Marcus Woodcock for his work on analysing companies under the King’s Undergraduate Research Fellowship (KURF) scheme.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship and/or publication of this article: This work was supported by the H2020 European Research Council (Grant No. 819213).
