Abstract
The central topic of this paper is a mobile phone application, ‘InformaCam’, which turns metadata from a surveillance risk into a method for the production of public proof. InformaCam allows one to manage and delete metadata from images and videos in order to diminish surveillance risks related to online tracking. Furthermore, it structures and stores the metadata in such a way that the documentary material becomes better accommodated to evidentiary settings, if needed. In this paper I propose InformaCam should be interpreted as a ‘forensic device’. By using the conceptualization of forensics and work on socio-technical devices the paper discusses how InformaCam, through a range of interventions, rearranges metadata into a technology of evidence. InformaCam explicitly recognizes mobile phones as context aware, uses their sensors, and structures metadata in order to facilitate data analysis after images are captured. Through these modifications it invents a form of ‘sensory data forensics'. By treating data in this particular way, surveillance resistance does more than seeking awareness. It becomes engaged with investigatory practices. Considering the extent by which states conduct metadata surveillance, the project can be seen as a timely response to the unequal distribution of power over data.
Introduction
Increased access to digital technologies and distribution networks has enhanced the potential for citizen journalism to monitor and report human rights abuses (Center for Research Libraries, 2012). However, the widespread use of these technologies, and that of mobile devices in particular, has also raised a new set of concerns. Firstly, these concerns relate to fears about surveillance and security (WITNESS, 2011). Secondly, digital reporting also raises the issue of authentication because digital material is highly vulnerable to manipulation (Center for Research Libraries, 2012: 64). This is further complicated by the volume of images and video that is captured and uploaded, which leads to a third issue: a ‘fire hose' that needs to be sorted through, evaluated and maintained (Center for Research Libraries, 2012). The credibility of digital reporting is not only an issue for activists but for (international criminal) courts as well (The Human Rights Center at the University of California, 2012: 13). According to the Human Rights Electronic Evidence Study by the Center for Research Libraries (2012: 64), ‘the resulting profusion of digital documentation has created new challenges of managing and authenticating vast amounts of evidence, from a multitude of sources, many of them unidentified.’ Against the backdrop of these concerns citizen journalists and human rights activists and organisations are faced with the question of how to investigate and document an event using digital technologies whilst at the same time avoiding the risks of traceability that might endanger the citizen journalist. This paper discusses the ways in which the InformaCam project tries to deal with these issues.
InformaCam is a mobile phone application for managing metadata embedded in photo and video files. It is aimed at resolving two, sometimes paradoxical, dimensions involved in documenting conflicts: the need to document violence, and the need to protect oneself from online surveillance. In one of the first articles in this journal, Couldry and Powell argue that ‘emerging cultures of data collection deserve to be examined in a way that foregrounds the agency and reflexivity of individual actors as well as the variable ways in which power and participation are constructed and enacted' (2014: 1). The InformaCam project is such an example of how actors engage with data collection and analysis for the very specific purpose of investigation and evidence production.
To highlight this investigatory dimension that is part of anti-surveillance activism, InformaCam is introduced as a ‘forensic device’. First of all, it is important to stress that the term ‘forensic device' stems from a particular reading of the term forensics, not as a disciplinary practice of the forensic sciences, but as the ‘production of public proof'. According to Weizman et al.: ‘Etymologically, “forensics” is derived from a Latin term meaning “before the forum” and refers to the practice and skill of making propositions through objects before professional and political gatherings or courts of law' (2010: 59). In the reading of the term as proposed by Weizman et al. the focus shifts from scientific practices, which serve legal procedures, to the skills and the (spatial) settings of evidence production beyond the disciplinary institutions of the law only. Secondly, the term ‘device' refers to a particular form of action. A device, according to Callon and Muniesa (2005), is a way of arranging things to make something work. In other words, a device establishes what in Actor Network Theory (ANT) is called a ‘translation' (Latour, 1983; Law, 1992). I work in line of ANT-associated studies on devices (Barry, 1999; Callon, 2004; Callon and Muniesa, 2005) by looking at how connections are being made between elements from diverse fields; in my case, these are connections between (meta)data and requirements from the domain of law. The material for this case study consists of the (online) publications about the app and personal interviews with developers of InformaCam. By not only looking at the application itself, but by tracing the project back to the philosophy of and writings of the developers, I show how InformaCam is an assemblage in which technical practices are tied to the domain of the law in such a way that something innovative emerges. In the case of InformaCam, what is made to work is a particular form of producing evidence with respect to digital images, through a range of interventions. In his work on protest sites, Andrew Barry has shown how activists re-organise public space for the demonstration of facts (Barry, 1999; Callon, 2004: 125). Analogously, I will point out how the developers of InformaCam set the conditions for metadata to gain evidentiary capacity. As I will argue, InformaCam translates metadata from a potential surveillance risk into a method for the production of public proof, and in that way, it acts as a ‘forensic device'. Looking at InformaCam in this way allows one to make explicit that activism in the context of surveillance not only focuses on awareness raising and protection measures, but has an investigatory dimension as well. Moreover, it shows how the metadata are not ready made, nor do they speak for themselves, but they are constructed in such a way that they gain agency, that is, evidentiary capabilities.
In the following paragraphs, I will first explain the basic idea behind InformaCam. Then I will provide some background to the use of the term forensic device. After that I will describe the metadata categories deployed in the project and the interventions made by the developers. Concluding, I will state that whereas metadata are initially seen as a risk, the InformaCam project re-articulates this risky subject matter as material that can be used for evidence production.
What is InformaCam?
InformaCam is developed by The Guardian Project (not to be confused with the newspaper The Guardian). The Guardian Project is an open source software company that helps mobile device users to protect their communication from intrusion and monitoring. One of the developers describes the twofold goals of the company as follows: ‘to give users control over how much data they provide as they pass media along the pipeline, and to increase awareness and visibility of the various issues that converge around their data as it circulates' (Holmes, 2011: 56). Part of the project is to provide people with useful tools that can be used by non-specialists. As stated on their website: The Guardian Project aims to create easy to use apps, open-source software libraries and operating system modifications, and customized mobile devices that can be used and deployed around the world, by any person looking to protect their communications and personal data from unjust intrusion and monitoring. (The Guardian Project, 2013a).
InformaCam is designed to support people in managing metadata that come with making images and videos. In a general sense, metadata can be defined as ‘data about data'. Metadata can be defined in a very specified sense as well, depending on the setting in which they play a role. In the digital context, the simplest description would be data about the context in which a file was produced, edited or stored. Metadata can be distinguished on different levels, such as ‘system metadata, file system metadata, application metadata, document metadata, email metadata, business metadata, geographical metadata and many more' (Raghavan, 2013: 101). The type of metadata that is relevant for this article is ‘application metadata', data that are embedded in the file which ‘describes and moves with the file when it is moved or copied' (Sedona, 2007: 4). 1
Metadata can pose a surveillance risk. When an image is created with a mobile phone, the image is stored with an extra layer of information that can include things such as the model of the phone and GPS data. When posting images or videos online one also uploads the metadata embedded in the file along with it, creating an online ‘record', thus enabling those with the right tools or expertise to extract the metadata and gain certain information about the creation of the file. This can prove highly risky for the producers of documentary material in oppressive or security-obsessed regimes, because they can potentially be tracked down. (For example by connecting different images made by the same device that is owned by a journalist known by name or by using the GPS data to determine the location of a person on a picture.) 2
InformaCam is part of a larger project, SecureCam, in which InformaCam's predecessor, the anti-surveillance app ObscuraCam, allows users to remove identifying metadata. ObscuraCam can strip metadata and obscure faces. If somebody wishes to share an image, ObscuraCam diminishes the chance that the producer of the image, or the persons depicted in the image, can be identified or located (The Guardian Project, 2013b). Technically speaking, InformaCam is based upon similar principles, but it makes an additional and opposite move: metadata are not obscured but deliberately captured and safely stored in case one wants to make this information public in the future. InformaCam enhances mobile devices with a ‘witness mode', that is, an extra functionality that uses the sensors of the mobile device in order to make the registration of contextual metadata available to, and manageable for, the user. When activated, the app registers ‘sensory and atmospheric data throughout the session' (The Guardian Project, 2012). This includes data types such as: current timestamp, user’s public (PGP) key, Image Regions created in the image/video, current latitude and longitude, all cell IDs that are visible, altitude, compass bearing, WIFI-networks (The Guardian Project, 2012; personal communication). 3 After having made an image or video, one could add specific metadata about the setting in which the image was taken as well, as for instance, information about the content and the producer of the footage. The contextual metadata and the annotations can be valuable for authenticating the image.
The application therefore provides the possibility of making two versions of the documentation: one version is produced without the identifiable metadata and another is safely stored with all the metadata. The data-poor version (Figure 1) can be distributed to any network of choice, whether that is YouTube, friends’ networks or (citizen) journalists. The data-rich version (Figure 2) can be sent to a trusted party, which could be for example one’s own e-mail address, a friend, or a support organisation such as WITNESS. This happens automatically through an encrypted channel via Tor.
4
Screenshot of the interface: a data-poor version for sharing. Image provided by The Guardian Project. Screenshot of the interface: a data-rich version for storage. Image provided by The Guardian Project.

The layer of metadata and the images can be disentangled when posted online, but they are stored together if one ever needs them in court or for other evidentiary purposes. In this way, InformaCam has merged two of the problems mentioned at the start of this paper, that of mobile tracking and that of digital authentication. (The third problem, the one of sorting through a large volume of images, will be addressed later in the paper.) The developers have produced a tool that allows users to take control over the circulation of data by intermediating between two different settings that have different requirements, the risky environment of public space and the evidentiary setting of public proof. In other words, the tool allows two different ways of ‘making data public’. It is the second setting that I will focus on now. For it is here that the app enters the world of forensics.
Forensics as the production of public proof
Forensics is usually understood as ‘forensic science'. It refers to the scientific practices, methods and techniques that are related to the investigation of crime. 5 The forensic sciences are those sciences that investigate, on behalf of the court, the principal investigator, or on behalf of the defence (depending on the legal system), specific material assumed to be related to a criminal offence. The forensic sciences can offer potential evidence for a decision that is subsequently to be made by the court. Forensics are hence associated with highly specialized laboratory work conducted by experts that make material, which is relatively invisible for ‘untrained eyes', visible for the public in court (Jasanoff, 1998b). However, studies into how scientific and technologically mediated data become witnessed facts tell us that the objects of the forensic sciences never speak for themselves. Scientific and technologically mediated data are in need of particular translations to become convincing in the courtroom when data are presented in front of the judge and jury (Jasanoff, 1998b: 719).
Although studies into science and law have shown that the forensic sciences do not operate isolated from publics or social practices (M’charek, 2008; Toom, 2010), forensics can be understood in an even broader sense. This interpretation of forensics goes back to the etymological understanding of the term. The Latin word ‘forensis' refers to ‘the art of the forum' (Forensic Architecture, 2015), and can also be translated as ‘public speaking'. Weizman explains how the meaning of forensics has shifted over time: The Roman forum to which forensics pertained was a multidimensional space of politics, law, and economy, but the word has since undergone a strong linguistic drift: the forum gradually came to refer exclusively to the court of law, and forensics to the use of medicine and science within it. This telescoping of the term meant that a critical dimension of the practice of forensics was lost in the process of its modernization—namely its potential as a political practice. (Weizman, 2013: 9).
As the practice of forensics centres around a piece of material, the concept also invites one to take questions concerning the relevance of this material very seriously. To explain this point better I draw on the work by Susan Schuppli on forensic media (forthcoming). Schuppli shows how technical objects can contain ‘trace-evidence': inscriptions of (violent) events. Her examples include documentary material that is degraded by radiation (Chernobyl documentary by Shevchenko in 1986), film material that has been copied and edited (the ‘Loshi video' depicting a massacre in Kosovo in 1999; for an analysis see Schuppli, 2014), and video footage that has metadata embedded (an anonymous execution video shot in Sri Lanka in 2009). In her framing, the object becomes ‘informed material', a term inspired by the philosopher of science Isabelle Stengers, and it denotes the way ‘their internal composition is enriched by information' (Schuppli, 2013). Such material can depict events not only in representative terms, but the materials themselves become enriched as well through the inscriptions along the way. Schuppli shows the different ways in which matter that has archived traces of events articulates itself as a witness of these events. Her concern is with how matter that is ‘informed’ takes on the role of a witness, that is, how matter can speak and testify. She uses the concept of ‘material witness' as an operative concept to describe the process by which that happens. This term is rooted in legal jargon (from the US context). When a witness becomes ‘material' to a case it means it holds crucial information (Leonardi, 2010). In Schuppli's case studies, the question about the material witness becomes one that is concerned with the inscriptions being made along the trajectory of material becoming a piece of relevant evidence. These inscriptions can be accidental influences, but they can also be legal formats with which materials need to comply in order to gain credibility in court.
What I take from the reading of ‘forensics' as proposed by Weizman et al. is the displacement of forensic practices, which allows one to grasp the participation of actors other than scientists and lawyers in the investigation of affairs. Schuppli's work directs attention to how material, including digital material, changes along a trajectory and how that requires us to rethink procedures of evidence giving. InformaCam is concerned with practices of archiving trace evidence and with the issue of how to make documentary material relevant through particular inscriptions. However, InformaCam is also an experimental application: it is, at the time of writing, ‘in the making'. That also means that it does not (yet) deal with passed events that it can document. In fact, it is the organisation of public proof in future that the application directs itself towards. It is also the organisation of public proof about which ANT-scholars have produced fruitful studies.
Devices for arranging the production of public proof
Classic examples of ways to organise public proof are legal trials and scientific demonstrations (Jasanoff, 1998b; Latour, 1983; Shapin and Shaffer, 1985). These are endeavours, or ‘devices' as in social-material arrangements, constructed to prove particular states of affairs. These devices require solidity because they build on rules or protocols that stay more or less the same and which allow a replication of testing and decision making (Callon, 2004: 125). A less procedural way of thinking about public proofs, and therefore relevant to this case study, is Andrew Barry's understanding of the ‘demonstration' (1999). Barry starts with drawing an analogy between scientific demonstrations and political demonstrations. The scientific demonstration has always been an important object of study in science studies. These studies have shown that scientific demonstrations heavily depend on the participation of witnesses and controlled behaviour, and thus, on a controlled public space (Epstein, 1995; Latour, 1983; Shapin and Schaffer, 1985). According to Barry, political demonstrations share a family resemblance with scientific demonstrations because they require a similar reorganisation of public space. In Barry's understanding, ‘to conduct a political demonstration can be a matter of making visible a phenomenon to be witnessed by others' (1999, 77).
One of Barry's examples is an extra-parliamentary action: an occupation in a forest against potential road constructions. The site of the occupation, the landscape, was not just the background for the protest. As a ‘setting' it became part of the protest itself because it exposed a potential truth claimed by the protesters. It showed ‘the fact that humans, land were mutually implicated' (1999: 81) and the emerging reality of environmental destruction. In this way, the activists crafted a space in which there emerged something to point to. As can be taken from the title of Barry’s piece, ‘site’ and ‘sight’ become interconnected. Barry describes at length the style of conflict resolution between the activists, the literature they produced and the material and social discipline needed to organise the camp. He also describes how the protest involved an ‘art of demonstration' and a careful orchestration of how (electronic) media participate in the way the demonstration is witnessed.
In sum, Barry shows that devices for public proof can also be displaced from the formal arenas of public proof giving. At the same time he describes that, although these settings might be less protocolised, spaces for public proof giving still need a lot of work to be established. Barry's take on the matter provides useful pointers for analysing InformaCam. The InformaCam project is, in an experimental way, involved with a range of interventions through which it tries to establish such spaces and connections. Thus, in line with more ‘formal devices' such as the trial and the experiment, InformaCam can also be seen as a device that is engaged with creating the conditions for the production of public proof. As InformaCam is experimental, it provides insights into how a forensic device is being set up.
Enriching and ordering metadata
As will be explained in more detail, the InformaCam project turns metadata from a risky matter of surveillance into something that is expected to have evidential value. Metadata can have evidential value because ‘[m]etadata refers to data about the data that is stored within a source of digital evidence' (Raghavan, 2013: 101). Metadata offer a narrative potential: a piece of evidence can tell something about itself through its metadata because contextual information is captured within the (digital) object itself. However, as mentioned earlier, data often need narrative techniques to become witnessed as facts. Framed in more philosophical terms, following Schuppli (forthcoming), capturing data by which material becomes ‘informed' is not always sufficient to turn it into a ‘witness’: the material has to be able to articulate its relevance to a case. Similarly, InformaCam does more than merely ‘capturing' data. The specific way by which data are captured and organised is crucial for turning it into a witnessing machine. The following paragraph describes in more detail through which categories the InformaCam project organises code and why. It also shows how software developers draw together concepts about digital networks, law and ethical perspectives, into the same project.
The lead developer of the project, Harlo Holmes, reflects upon The Guardian Project's app development in her master's thesis. She describes how EXIF data contain various specified fields and allow for free comments. EXIF stands for ‘Exchangeable image file format’ and is the standard used for specifying and annotating image files by digital cameras. She argues that a large amount of the EXIF data fields are filled up with intellectual property data. Referring to Manovich's concept of ‘cultural transcoding', a concept that addresses the translation of cultural formats into computer code (Manovich, 2001: 64), she states that: The EXIF specification's treatment of the copyright tag is a remarkable example of the process of ‘cultural transcoding' posited by Lev Manovich. In the specification, the EXIF tag descriptions are usually no more than 3 lines in length; the copyright section, however, occupies quadruple the space. (Holmes, 2011: 30) Obscura openly challenges the law of the smartphone by overriding its unencrypted media database and by allowing users to rein control over the embedded EXIF data. To interact with the app encourages direct exposure to the new laws of images, allowing users to actively participate in the politics newly embedded into the photographic act. (Holmes, 2011: 57–58)
The interaction between human rights and software is of central concern to the Project Director of WITNESS (which is the NGO that collaborates on InformaCam), Sam Gregory. Gregory (2012) presents some of his ideas in a publication that discusses alternative ways of making human rights visible. One example is a proposal for a new kind of licensing system, one that ‘recognizes intentionality'. His proposal is to give a twist to digital material, but one that is different from copyright or Creative Commons licenses that deal with intellectual property rights and the possibility for remixing. His type of license would embed a proposed human rights use into the metadata. His second example relates to rethinking witnessing in the digital age ‘in line with the primary principle that every human being is possessed of “inherent dignity” – a concept that runs through every right included in the UDHR' (2010: 11). An important concern in this context is the avoidance of re-victimization of victims on film through the widespread circulation of media. Gregory continues to argue that this comes with an ethical obligation for the one who is witnessing to do so carefully with respect for the victim: ‘Contemporary thinking on testimony, witnessing and trauma also places a heavy emphasis on the responsibility of the witness to abuse to represent it responsibly and with ethical integrity – to be, so to speak, the “ethical witness”' (2010: 11–12). WITNESS wants to contribute to ethical forms of witnessing by translating professional notions of informed consent (inspired by medical practices, social science and international human rights and humanitarian law) into the practice of technological devices (2010: 12). 6
InformaCam is an implementation of some of the ideas mentioned above. This is done by what one could call ‘enriching metadata': InformaCam structures how metadata are embedded in the image. An (early) blog post on the project mentions four metadata categories: Data, Consent, Intent, Genealogy. 7 The category ‘Data’ sounds very general, but it represents the data that ‘captures the moment of capture’. As explained by The Guardian Project’s website: ‘This category includes all standard metadata (timestamp, acquired sensory data, location and movement data) that have been collected during the lifetime of the image, from the moment it was opened to the instant it was saved' (The Guardian Project, 2012). InformaCam does not capture traffic but only publicly visible identifiers. ‘Consent’ resonates most explicitly with human rights culture. A user of the application can add free text to images indicating whether the subject has given consent to be filmed. As touched upon earlier, the approach of WITNESS is to translate ideas of consent into technical devices, by for example tools giving ‘prompts on consent during those filming/upload processes' (Gregory, 2010: 15). This is an implementation thereof. ‘Intent’ is more experimental and is directed to the circulation of digital material. It indicates ‘information about the media’s creator and the permissions for sharing' (The Guardian Project, 2012), and could therefore be considered as a materialisation of what Gregory (2012) proposed: ‘a licensing system that recognizes intentionality'. This ‘tag of intent’ will say something about what kind of ‘use’ the producer envisions with a particular digital object and is an attempt to create ‘human rights media' as a particular piece of media and bring that into circulation (Gregory, 2013, personal communication). ‘Genealogy' refers to the main indicator of the chain of custody (or ‘data integrity’, which means that data should be left in tact until it reaches the court). This is addressed through a digital hash embedded into the file on the moment the image was made to indicate its original state. 8
Besides these main categories, the developers make use of an ordering device entitled J3M (JSON Evidentiary Mobile Media Metadata), which is described as ‘a format that can be used to easily describe the origins, context, and content of any image or video taken with a mobile device' (j3m.info, 2013). This is to be understood as a way of structuring metadata. The aim of J3M is to: [m]aintain a trusted record of a media object’s chain-of-custody (…); Express the context surrounding the media object’s capture (…); Embed extra user input from forms or surveys into the media object as signed metadata (…); Provide metrics for analyzing the content of the media object to mathematically determine that it was created by the device indicated in its metadata. (j3m.info, 2013). Screenshot of metadata ordered through J3M. Image provided by The Guardian Project.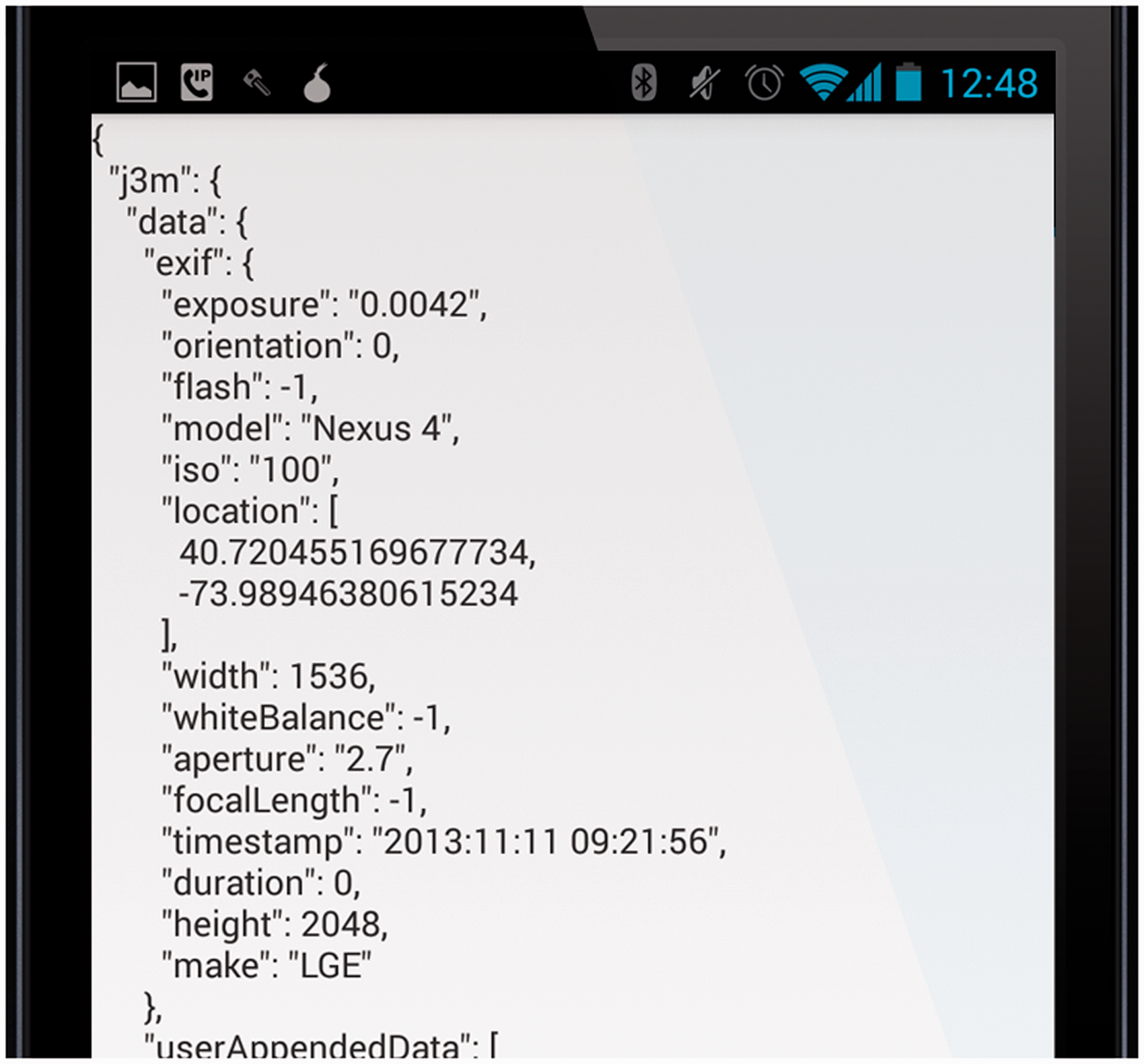
The above mentioned categories and J3M show a first insight into how the people involved with InformaCam actively shape metadata. They do so in a way that would help forms of narration firstly with respect to the context of the event, secondly with respect to the content of the material, the relation between the producer of the image and the people depicted, and, finally, his or her relation with the digital object itself. It is an example of an emerging culture of data collection in which actors on the ground exercise their agency by constructing and curating data for particular purposes (Couldry and Powell, 2014).
Organising conditions of public proof
At the time of writing, InformaCam just released its beta-implementation. Therefore, real life experiences of how InformaCam is put into use are not yet available. However, InformaCam allows for organising the settings for the production of public proof in multiple ways. I discuss three of these ways below.
A first intervention has already been discussed, which consists of tying images to regimes of evidence. As highlighted in the previous paragraph, the categories of InformaCam show how the project developers pull in different kind of formats into the application. The chain of custody, an important issue for investigatory purposes in legal settings, is accommodated with a digital hash that J3M embeds in the file. In addition, notions of ethical witnessing from the human rights arena are redesigned as an awareness prompt. In this way, in Holmes’ words, the developers are ‘ingraining' categories borrowed from legal and human rights discourse into the metadata (Holmes, 2013, personal communication). It is interesting to see how these inscriptions organise the capturing of data before the images are even being made. This has its analogy in other legal practices. In his work on the workings of law (2010), Latour explains how, in the context of the French Council of State, some (governmental) documents are prepared for legal use before being used in a legal setting. They are, in other words, already ‘profiled' before making it to the court. Files, according to Latour, are ‘made ripe for use' (2010, 70). The operation of law, he argues, cannot be understood without these preparations. Similarly, software developers are undertaking preparatory work to ‘ripen up' digital data for legal use.
Whether this material will make it in the end to the international human rights courts is most difficult to foresee. In the context of this discussion, it is important to take note of the different legal systems with respect to the admission and evaluation of evidence (Jasanoff, 1998a; Van Koppen, 2007). In the adversarial system in the United States exist specified legal requirements with respect to scientific evidence (the Daubert Criteria). 9 It has been claimed that these admissibility rules, together with the litigation structure in the United States, provide opportunities for the critical evaluation of science and technology, especially when compared to inquisitorial systems found in many continental countries (Jasanoff, 1998a; Van Koppen, 2007). In inquisitorial systems, the prosecutor is responsible for the ‘dossier work’ and the admissibility of scientific and technological data is less subject to public discussion in the courts. International human rights courts consist of a mixture of legal systems, but tend to follow civil (continental) law in relation to the admission of evidence. This implies that the threshold for the admissibility of evidence is low. With respect to electronic evidence the international tribunals require no particular standards and in terms of admissibility trial chambers are relatively free in their assessment (O’Neill et al., 2011). The rules for (electronic) documentary evidence therefore vary from court to court and the development of standards proceeds very slowly (Center for Research Libraries, 2012: 65): ‘[R]equirements are better established for national and local courts than for international courts and tribunals' (Center for Research Libraries, 2012: 51). In their review of a series of human rights O’Neill et al. state that ‘procedural rules at international courts and tribunals offer little guidance on what must be shown to authenticate new forms of E-evidence' (2011: 9). 10 The number of cases in which metadata have played a role is still rather limited, and hence there is little case law to draw conclusions from about what to expect in the near future. A request by the International Criminal Court Prosecutor for a protocol for ‘born-electronic evidence’ was denied by the Chamber (O’Neill et al., 2011: 51). However, as explained in the same report (p. 42), the authentication of e-evidence can play an important role in opening up investigations into human rights violations. Despite the lack of existing standards, there is a realization that they might develop in the years to come. According to the authors of the same review, the potential future development of restrictive demands concerning e-evidence, which might be inspired by the more extensively documented (commercial) US litigation context, could be dangerous for international human rights proceedings, since the burden placed on people bringing in evidence may preclude those without access to equipment of sufficiently high standards. That is the reason why InformaCam is a significant project: whereas requirements for metadata in the legal domain of international human rights procedures are not yet defined, the developers of the project are already working towards developing a specific socio-technological standard of which they hope it will also become accessible for activists.
In this context it is important to know that The Guardian project will soon launch the InformaCam system as the ‘CameraV App’. 11 And in June 2015 the IBA launched a spin-off called ‘Eyewitness for Atrocities App’. This app is built on the open source implementation that was made in collaboration with the Guardian Project. That means that the concepts behind the project are now being brought into practice. Next to offering the tools, the developers of InformaCam do also try to find ways to familiarize courts with their techniques. According to Sam Gregory, they are looking for what they call ‘demonstration projects' that can help demonstrate the evidentiary value and applicability of J3M data and the InformaCam project (Gregory, 2013, personal communication). At the same time they are aware of the dangers of putting a very heavy weight on people bringing in evidence whilst not everybody has access to the right equipment to secure such standards: ‘We're also cautious though not to create a situation where there is an insistence on extra metadata for proof since we know that there will be many contexts where valuable evidence is missing this' (Gregory, 2013, personal communication).
A second intervention is related to the insight that mobile devices have capabilities that can organise forms of witnessing on the ground. Through Bluetooth the app can detect other devices that have InformaCam activated nearby. In this way the app can show that multiple devices were present at the same place at the same time, or that people have made similar documentation at the same time with regard to the same event (Holmes, 2013, personal communication). One potential user group is the Georgia Legal Services Program that helps migrant workers (Making Cameras Count, 2013). It happens that bosses deny that people came to work, leaving workers without payment. It is for such situations that InformaCam could mobilize self-tracking: through the simultaneous use of Bluetooth detection, people would be able to try to prove their presence, or at least that of their phones. Therefore, the application does not only aim to produce images of events, it would also put oneself, or one's collective, on the map. So one way in which InformaCam invites material to become more ‘informed' is by capturing (collective) presence. It captures not only contextual metadata that refers to location, device number, etc., but it enacts a collective body of witnesses. Figure 4 is an example of how the presence of devices can be mapped through Bluetooth.
Map that visualises cell towers, WIFI, Bluetooth and movement. Image provided by The Guardian Project.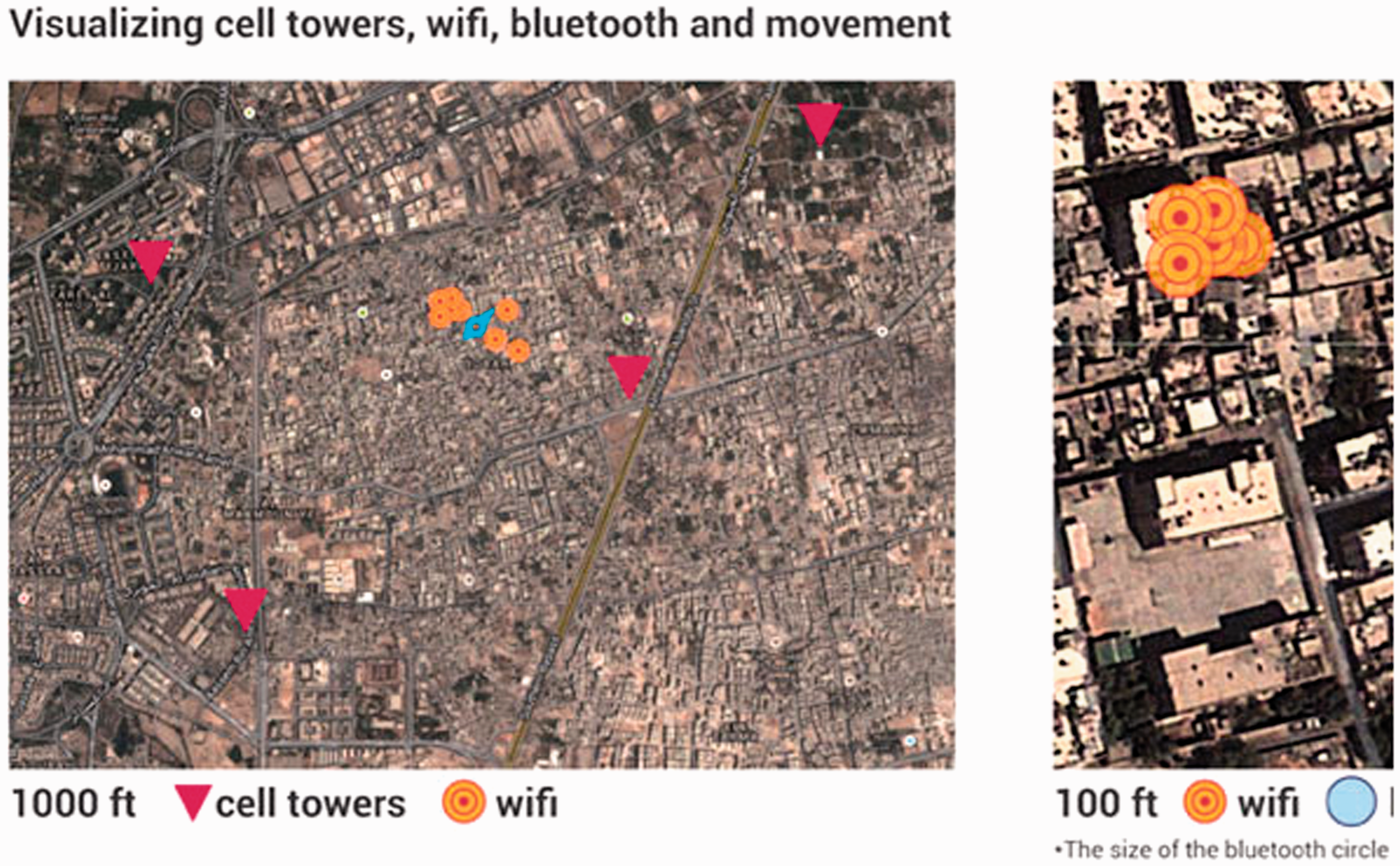
With a third intervention, the J3M-library makes a particular form of forensic data analysis possible. According to Harlo Holmes, it is not the app itself that she expects to do all the work: it is the openly available library that opens up the perspective to distribute J3M to other applications and platforms such as YouTube (Holmes, 2013, personal communication).
12
Gregory adds that the distribution of J3M into the public domain aims to open up research possibilities through J3M itself. The library is inscribed into the files and subsequently read out again. So the device works by structuring data in such a way that material can be pulled together after capturing it. According to Gregory, multiple J3Msources embedded in InformaCam material can be used for timeline mapping and comparison between multiple angles. It could enhance constructing a chain of explanation of what happened in an event (2013, personal communication). There are already several projects that map events on the basis of (EXIF) metadata online. See for instance ‘The Rashomon Project', an open-source online toolkit that assembles and analyses videos and photos from ‘contested events'. Their aim is to enhance a nuanced understanding by providing multi-perspective timelines and interactive viewing features (The Rashomon Project, 2015). The approach of the InformaCam developers is therefore an example of how actors ‘on the ground' challenge ‘conventional data collection' (Couldry and Powell, 2014: 4). Figure 5 below presents the InformaCam System Architecture. From the left to the right it shows the app, the two versions of the documentary material that the app produces, the methods for verification, and lastly, the analysis dimension in the project (‘J3MScan Advanced Search and Analysis').
InformaCam System Architecture. Image provided by WITNESS and The Guardian Project.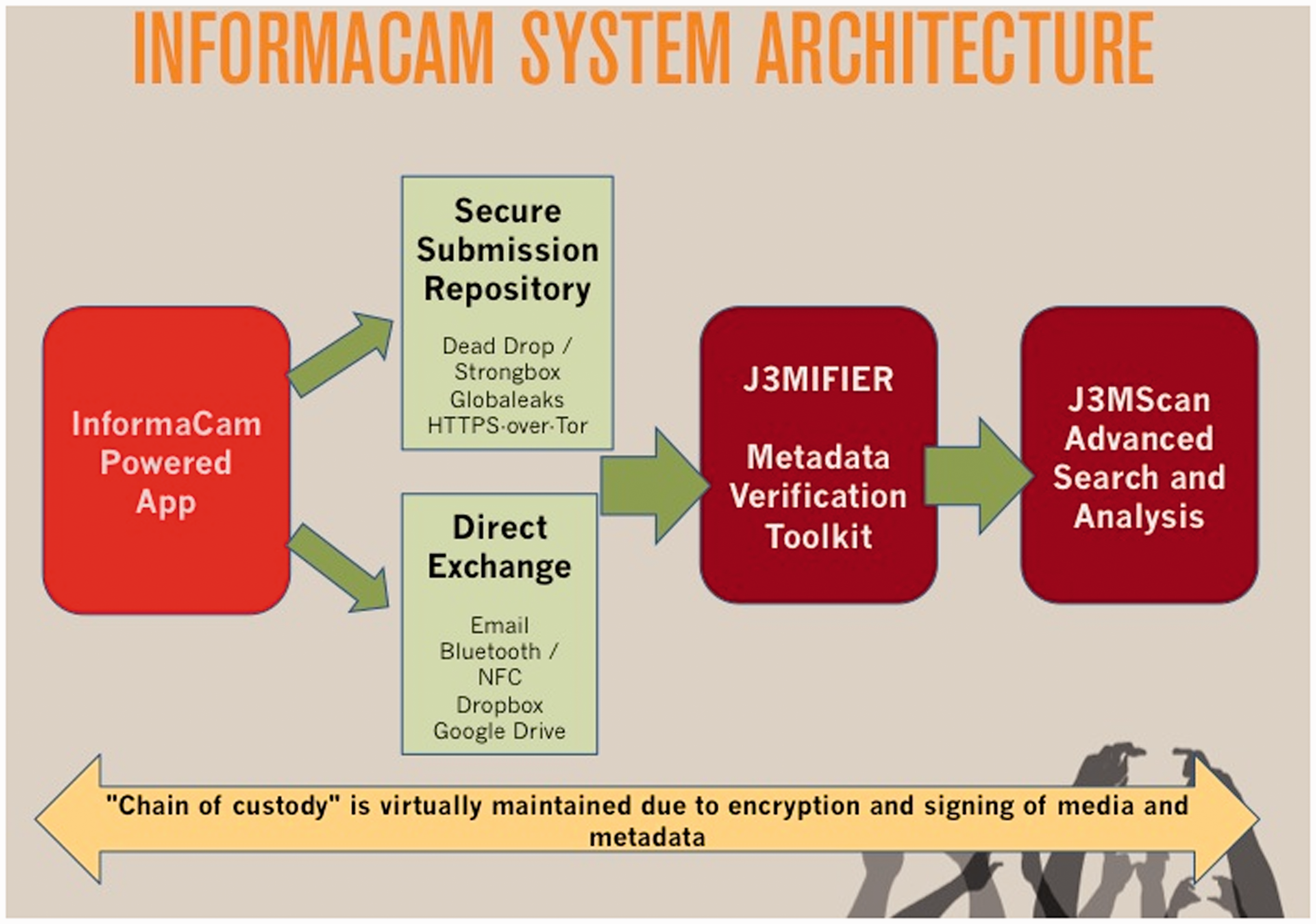
A forensic device for activism
InformaCam takes part in an emerging trend of projects that aim to enhance the verification of online information. There exist websites for tracking users’ location footprint on the basis of GPS data, tools for revealing EXIF data attached to images, and tools for showing whether images have been altered. (See, for instance, the website of the Verification Handbook for an overview (Silverman, 2014).) On the other side of the spectrum there are plenty of tools that help users to protect their identity, to browse anonymously or to securely encrypt their data. (See for instance, http://prism-break.org.) According to the developers, InformaCam is, as far as they know, the only app that combines this many capabilities (‘enhanced metadata through sensors, cryptographic verification/hashing/signing, secure storage and transmission’) and that is offered as a free and open source app that runs on inexpensive smartphones (Freitas, 2013, personal communication).
Moreover, InformaCam is prefigurative to legal standards. As mentioned earlier in the paper, Andrew Barry has shown how activists can be involved in carefully modifying and constructing spaces that allow proof to emerge, and how they can invent new forms of demonstration. The actors involved with the InformaCam project do a similar thing with respect to networked technologies. They actively engage with how data can be handled by making InformaCam intervene in different parts in the trajectory of an image. By transcribing law into code before the event, controlling how data is captured on the ground, and by the enhancing research capabilities for post-event analysis, the InformaCam project invents a form of what we could call ‘sensory data forensics’. Mobile phones, sensory data, users' interaction with technology, legal formats and code are tuned in such a way that together they allow for the production of public proof, and hence operate as a forensic ‘device’ in the ANT sense of the word. It also indicates a medium-specific collaborative practice to witnessing, which can be better understood when taking into consideration that particular software communities have particular approaches to code (Coleman, 2009; Kelty, 2008). The people behind InformaCam are not waiting until jurisprudence catches up with new evidentiary modes, but are already intervening through the media landscape.
There seems to be a paradox to the idea that images should remain ‘in tact' to retain the chain of custody on the one hand and the practice of adding data-points to structure images for analysis on the other hand. But as we can read in the work of Kelly Gates, this paradox characterizes the practice of video forensics by forensic experts as well. Looking at the disciplinary practice of video forensics in particular, Gates describes how in preparing CCTV video material, forensic investigators use narrative techniques such as annotating, zooming and composing timelines, sometimes with the use of sophisticated software. Metadata can also be attached to images to enhance search and retrieval and cross-referencing (2013: 251; 255). As Gates critically points out, the practice of video forensics points to a new conceptualization of (computational) objectivity: Here I want to suggest that the use of digital imaging technologies to make visible what is invisible and invest images with indexicality points to a new conceptualization of objectivity. This way of thinking about objectivity holds that neutral, scientific results can be achieved through the application of computational forms of analysis – automated, algorithmic techniques performed by computers. (2013: 252.)
Concluding remarks
The InformaCam project signals an innovative way of thinking about surveillance risks: surveillance risk is not just something to be ‘informed of' or to be avoided; it is something that can be hacked in order to become an empirical object. The project has re-articulated what used to be a problem into its working material. For the people involved in the InformaCam project, the circulation of data is a problem but at the same time it is material that can be analysed and used for other things.
InformaCam shows in what direction activism in the context of surveillance can develop. It seems to do away with the gaze as a central organising principle. Instead of being primarily concerned with what can be seen (on an image), the project shows how attention shifts to the ‘art of looking’, which is concerned with how to organise which data counts (including one’s own position, location, etc.). In short, it becomes engaged with investigatory practices through code. It is what Thomas Keenan (inspired by the use of the concept by the photographer Sekula) calls ‘counter-forensics’. This concept refers not to countering forensic investigations, but to the tactical adoption of forensics in the context of activist struggles (Keenan, 2014: 69). 13
This investigatory dimension raises a few critical questions: Doesn’t the project become too much of a surveillance project itself? Doesn’t it perform analytic work in service of authorities that attempt to monitor people? Do people who use this tool, by collectively mapping events and their devices, endanger themselves? When asked about this, Harlo Holmes admitted this constitutes a potential risk, but she also argued that many states have access to this kind of data already (as InformaCam captures only public data) and many people are not aware of it yet. She regarded using InformaCam as taking a step forward in terms of the ‘equality of arms’ (Holmes, 2013, personal communication). Recent developments have underlined the invasiveness of state surveillance. The National Security Agency (NSA)-disclosures by Edward Snowden in 2013 (Greenwald, 2014) have shown that the NSA uses many techniques for metadata analysis. This includes programmes such as ‘HAPPYFOOT’ for collecting mobile phone location data and ‘Co-Traveler Analytics’, which detects devices being present together at particular locations (Soltani and Gellman, 2013). Tools such as InformaCam, therefore, can be seen as a timely response to the unequal distribution of power over data.
Footnotes
Acknowledgements
I would like to thank Susan Schuppli, Shela Sheikh and Sam Gregory for their comments to a previous version of this paper, Niels ten Oever, Tamira Combrink and the anonymous reviewers for their critical remarks, and the developers of the project, Harlo Holmes and Nathan Freitas for taking time to correspond with me about their work.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
