Abstract
Accusations of Russian hacking in the 2016 US presidential election has raised the salience of cyber security among the American public. However, there are still a number of unanswered questions about the circumstances under which particular policy responses are warranted in response to a cyber-attack and the public’s attitudes about the conditions that justify this range of responses. This research investigates the attributes of a cyber-attack that affect public support for retaliation. It finds that cyber-attacks that produce American casualties dramatically increase support for retaliatory airstrikes compared to attacks with economic consequences. Assessments of attribution that have bipartisan support increase support to a lesser extent but for a broader range of retaliatory measures. The findings have important implications for ongoing debates about cyber security policy.
Introduction
In August 2016, candidate Hillary Clinton told an audience that “As President, I will make it clear that the United States will treat cyber-attacks just like any other attack. We will be ready with serious political, economic, and military responses” (Williams, 2016). The assertion is consistent with a Pentagon task force report from 2013 indicating that a cyber-attack should be regarded “like any other attack,” and that the use of armed military force should be considered an appropriate retaliatory action (Defense Science Board, 2013). Despite the apparent agreement, when confronted with Russian meddling in the 2016 United States election, decisions about whether and how to retaliate for any interference were mired in debate both within and across the political spectrum (Sanger, 2016a). While President Obama and prominent Republican Senators such as John McCain and Lindsey Graham called for aggressive measures against Russia, President-Elect, Donald Trump suggested that Russia’s role in the attack was unclear and that retaliation was inappropriate (Volz and Schectman, 2016).
Embedded in these emerging debates about how to respond to cyber-attacks are three key considerations. The first is whether victims can ever be certain about the source of attack, which is necessary for retaliation – against whom do they retaliate? Second, what types of attacks justify military retaliation as a state’s right of lawful self-defense? Third, under what conditions would the public support retaliation to a cyber-attack? This article engages those three sets of questions by investigating how the first two factors – attribution and the nature of attack – affect the third, public attitudes about retaliation.
It proceeds first by discussing how debates about the intersection between cyber security and the use of force have evolved in the prior decade. Next, it makes an argument for why the public is a relevant yet often overlooked actor in discussions about cyber security, and advances propositions about the circumstances in which the public is likely to favor the use of force in retaliation for a cyber-attack. It then briefly outlines the experimental design followed by a discussion of core findings: assessments of attribution that have bipartisan agreement consistently increase support for retaliation; whether a cyber-attack produces American casualties dramatically increases support for retaliatory airstrikes; and partisan differences about attitudes toward Russia in general do not carry over into support for particular retaliatory policy options. The article concludes with implications for ongoing debates about cyber security policy.
Existing cyber security frameworks
The International Committee of the Red Cross defines cyber warfare as “means and methods of warfare that consist of cyber operations amounting to, or conducted in the context of, an armed conflict” (International Committee of the Red Cross, 2013). A Department of Defense (2011) memorandum similarly defines cyber warfare as “an armed conflict conducted in whole or part by cyber means…to deny an opposing force the effective use of cyberspace systems and weapons” (Vice Chairman of the Joint Chiefs of Staff, 2010). Cyber-attacks are not explicitly covered under existing laws of war, which took shape in a pre-cyber environment. Indeed, according to one perspective, only an armed attack can justify the use of military force, and cyber-attacks do not meet this threshold (O’Connell, 2012: 6).
A competing camp, reflected in US cyber policy, suggests that the law of armed conflict applies in full in this domain. The Nuclear Weapons Advisory Opinion by the International Court of Justice reinforces the inherent right of self-defense in response to “any use of force, regardless of the weapons employed” (Ohlin et al., 2015; Schmitt, 2013). The United States’ 2011 International Strategy for Cyberspace affirms that the US has “the right to use all necessary means – diplomatic, informational, military, and economic – as appropriate and consistent with international law” in response to a cyberattack (Hughes, 2016; Obama, 2011). This applies irrespective of whether the perpetrator is a state or a “patriotic hacker” acting on behalf of a state but without its direction since states are implicated if “the person or group of persons is in fact acting on the instructions of, or under the control of, that State in carrying out the conduct” (Mačák, 2016: 3).
Even within the latter camp, questions of when the attack threshold is crossed and how to respond are unresolved. Amidst this ambiguity, the “notion of equivalence” – that an attack will warrant a commensurate response – has increasingly informed the thinking of United States on what constitutes an act of war in the cyber domain (Gallington, 2011; Gorman and Barnes, 2011). According to former legal adviser to the State Department, Harold Koh (2012), kinetic attacks, or “cyber activities that proximately result in death, injury, or significant destruction would likely be viewed as a use of force.”
Complicating debates about the appropriate legal framework to apply to cyber-attacks is the question of source attribution, which would be required for a retaliatory strike. Attribution is difficult in large part because online perpetrators can often remain anonymous and networks are complex (Rid and Buchanan, 2015: 7). A second problem is that, as Joseph Nye (2011: 22) suggests, “cyber intrusions that plant logic bombs in the infrastructure may go unnoticed for long periods before being used and, even then, can be difficult to trace.” Third, states that have the capacity to carry out a large-scale attack also likely have organizational capacity, technical savvy, and therefore ability to hide their covert operations, including in the cyber domain (Lindsay and Gartzke, 2016).
The public opinion context
Beyond the unanswered question of retaliation is the political context underlying states’ responses to a cyber-attack. As Charles Dunlap (2011: 84) suggests, the threshold for what constitutes an “act of war” that would justify military retaliation is as much political as legal. There are several reasons to expect that the public would be an important consideration in these political discussions. First, public attitudes create political incentives for democratic leaders to make particular choices about the circumstances under which they carry out the use of force. Public opinion, as Leslie Gelb noted in his study of the Vietnam War, was the “essential domino” around which both sides (the US and Viet Cong) based their strategies (Klarevas, 2002: 418).
Second, the process of assessing the attack and identifying attribution would likely take time since “cyber incidents are reviewed on a case-by-case basis” (Murdock, 2016). As such, leaders would have ample opportunity at least to perceive the “public mood” – “the notion that a rather large number out in the country are thinking along certain common lines” – if not read poll numbers themselves (Kingdon, 1984: 153).
Third, the lack of policy agreement and protocol on cyber-attacks would likely open the door to public influence. Lack of consensus would enhance the effect of public opinion insofar “elites may arbitrate between competing views by determining what is most popular” with supporters, with mass attitudes acting to cue elites (Steenbergen et al., 2007: 20).
Fourth, observational data suggest that cyber security is a salient issue for the public. When asked whether individuals see cyber-attacks as a serious threat, 94% of the public indicated that the threat was either very serious (69%) or somewhat serious (25%). A Pew Research survey of a subset of the public – cyber researchers, policymakers, and engineers – found that 61% believed that a major attack that caused “widespread harm” would take place by 2025” (Lee et al., 2014).
While the observational data shed light about the public’s attitudes regarding a cyber- attack, they also leave unanswered questions about how the public would react to the questions about attribution and magnitude that are central to academic debates about cyber warfare and that would inevitably feature prominently in policy debates about whether to use force in retaliation for a cyber- attack.
Hypotheses on public attitudes
Our primary expectation is that the “notion of equivalence” resonates with the public and drives its attitudes about policy responses. In practice, this would mean that individuals’ attitudes about retaliation will correspond with the nature and magnitude of the initial cyber-attack. Attacks involving American fatalities (referred to as kinetic attacks) will be more likely to prompt support for aggressive action such as military force than non-kinetic attacks that fall short of having a physical effect. Moreover, within a particular type of attack (kinetic or non-kinetic), larger-scale attacks are more likely to engage US interests, and therefore support for retaliatory action, than smaller-scale attacks (Herrmann et al., 1999: 562).
Our first hypothesis is as follows:
H1a (non-kinetic/kinetic): Kinetic attacks involving fatalities will generate higher support for retaliation than non-kinetic attacks.
H1b: (scale): Large-scale attacks will generate higher support for retaliation than small-scale attacks.
Second, we expect that uncertainty regarding the source of the cyber-attack will affect how individuals think about retaliation. 1 Individuals tend to have “ambiguity aversion” and are likely to shy away from taking actions in the face of uncertain probabilities (Kahneman and Tversky, 1979). While the tools for judging attribution have improved (Rid and Buchanan, 2015), government officials almost always speak in qualified terms about the perpetrator of an attack. But according to Lindsay (2015: 57), “an unconvincing attribution case, even if nominally correct, can undermine the legitimacy of a retaliatory act in the eyes of skeptics, especially in a democratic constituency.” Taken together, we expect the following:
H2 (Attribution): Higher levels of certainty regarding attribution will increase support for retaliation.
Third, we expect the cyber security issue to be ripe for partisan influence. As Zaller (1992: 100) suggests, the combination of being politically salient and lacking clear precedent in terms of how to respond offer fertile ground for the effect of elite consensus on public attitudes. Indeed, high-profile episodes including accusations of election hacking make it topically relevant. However, it is a relatively new policy issue and even the government is trying to grapple with “a complex calculus” of policy options and their costs and benefits (Sanger, 2016b). Despite legislative leaders arguing that cyber security “cannot become a partisan issue,” the polarization that defines the contemporary political landscape suggests that partisan divides are likely on the issue of cyber as well (Kim and Everett, 2016). Thus, to the extent that political elites agree on questions of attribution, public support for retaliation is likely to increase (Fandos, 2016; Gajanan, 2016; Hosenball, 2016). We therefore expect the following:
H3 (Elite consensus): Elite consensus on attribution will increase support for retaliation.
Research design
We designed a survey experiment to test these hypotheses. Two thousand subjects were recruited from Amazon’s Mechanical Turk 2 online labor market and asked about their support for the use of force in response to varying types of cyber-attacks. We used a 2 × 2 × 2 × 2 factorial design that varied two main parameters, each with two subsets of factors. 3
The first two varied aspects of the attack itself, which correspond with hypothesis one. The first consisted of the difference between attacks with physical consequences (kinetic) and those that were primarily economic (non-kinetic). In the non-kinetic scenario, the cyber-attack targeted “the computer systems of several of the nation’s banks, causing an uncontrolled transfer of funds out of the system.” In the kinetic scenario, the cyber-attack targeted “computer systems of several of the nation’s nuclear power plants, causing core meltdowns and widespread radioactive contamination.” The second consisted of the magnitude of attack. For example, in the smaller-scale non-kinetic attack, “hundreds of Americans had lost $3 billion in savings stolen out of their bank accounts” compared to thousands of Americans who had lost $30 billion. In the smaller-scale kinetic scenario, “hundreds of Americans had fallen ill with radiation sickness and hundreds more had died,” compared to thousands who were ill and died for the larger-scale scenario. Although the nuclear scenario was qualitatively different from the banking scenario, these differences were nearly inevitable given that we were testing the effect of American fatalities.
The second two factors varied aspects of attribution, corresponding with the second and third hypotheses. First, we considered degrees of certainty regarding the perpetrator’s involvement, suggesting either that the culprit was “probably” or “almost certainly” involved in the cyber-attack. 4 For purposes of external validity, we selected Russia because of its purported involvement in a range of cyber-related activities. Indeed, if we had used a hypothetical country, it is likely that respondents would have associated the action with Russia so we opted for explicitly designating the country as Russia despite the challenges to generalizability. To be sure, Russia’s military power and nuclear status might be more likely to deter a US retaliation compared to a non-nuclear country and conversely a “least likely” case for individuals favoring aggressive retaliatory measures. If we find public support for such measures against Russia, then we might expect it for other less powerful countries as well.
Next, along different lines of attribution, we allowed for the prospect of political contestation regarding the diagnosis. In one condition, “US intelligence officials in the CIA and FBI have said” that Russia is involved, and in a condition implying elite consensus, respondents were told that this is an “assessment that has bipartisan support,” whereas the elite dissensus treatment suggested that it “does not have bipartisan support.”
To gauge support for different policy responses to the cyber-attack, we randomized four dependent variables. We queried whether individuals would support gathering more information before responding; economic sanctions; a similar cyber-attack against the perpetrator; and air strikes against Russia.
Results
Figure 1 shows the way in which different attributes of the cyber-attack affected support for the use of force. Each category below compares the key factors that we speculated could affect how individuals think about responding to cyber-attacks, showing attitudes about whether the United States should gather more information, whether individuals would support a similar cyber-attack against the perpetrator, economic sanctions, or airstrikes. Each of the factors is compared with a “baseline,” such that high impact is compared to a baseline of smaller-scale attack, kinetic (whether Americans were killed in the attack) versus non-kinetic, whether attribution was almost certain versus probable, and whether the intelligence estimate did or did not have bipartisan support.
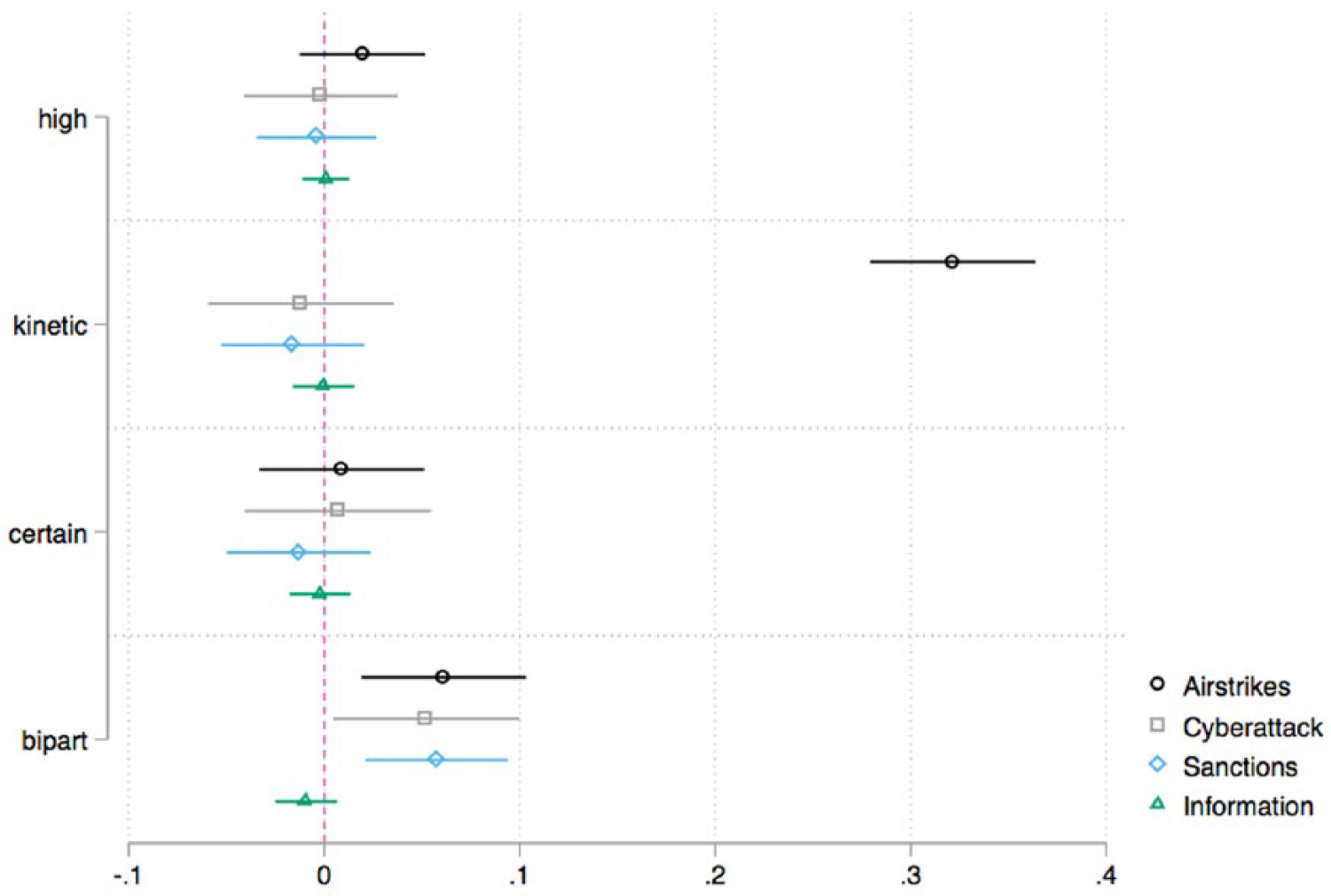
Estimated treatment effects for the four main attributes of cyber-attack, along with 95% confidence intervals from ordinary least squares regressions characterizing respondents’ reactions to four different policy options.
As Figure 1 shows, the factor most strongly affecting attitudes about how to respond to the cyber-attack was whether the attack killed Americans or not. For scenarios involving American fatalities, support for airstrikes increased by about 32% compared to when a cyber-attack involves financial costs, although the kinetic scenario had no impact on support for sanctions or a reciprocal cyber-attack.
Whether the assessment had bipartisan support was a consistently important factor influencing support for retaliation, which increased by about 6% for sanctions, a reciprocal cyber- attack, or airstrikes. Whether the impact of the attack was high or low increased support for airstrikes by almost 4%, though this just missed significance at the 5% level. Individuals appeared unable to distinguish between attacks varying just by orders of magnitude.
Despite expecting that the degree of certainty about the attribution would affect individuals’ support for particular policy responses, this factor had no appreciable impact, perhaps because respondents are unable to distinguish between “probably” and “almost certainly.” Furthermore, it may be that individuals actually assigned lower probability to “almost certainly,” as some scholars (Mosteller and Youtz, 1990: 6) have found, or that the partisan cues diluted the effect of the certainty of attribution. 5
While Amazon Turk is suitable for treatment effects, the question of representativeness often arises. We therefore disaggregated the data based on one of the most politically relevant considerations, which is partisanship. We found that individuals had clear partisan differences in terms of their attitudes toward Russia, as shown in Figure 2, consistent with recent survey data showing that Democrats are more hostile than Independents or Republicans.

Fraction of respondents who view Russia as an enemy or unfriendly (by party identification).
These differences, while stark, did not carry over to how the respondents thought that the US should respond to cyber-attacks from Russia. As Figure 3 shows, about 36% of Republicans supported airstrikes in retaliation to a cyber-attack on the US compared to 31% of Independents and 33% Democrats, but these differences are not statistically significant.

Fraction of individuals who support retaliatory airstrikes (by party identification).
All the policy preferences of the respondents followed this pattern – in which partisan differences on Russia did not carry over into attitudes about particular retaliatory options toward Russia – except for on economic sanctions. There the Democrats did appear to be more supportive than either Independents or Republicans (90% of Democrats versus 76% of Independents and 81% of Republicans). Even here though, there was remarkable convergence of bipartisan support for sanctions.
Based on qualitative responses expressing concern about escalation with a nuclear weapon country such as Russia, we suspect that factors about power, escalation, and nuclear weapons acted as a structural deterrent to more aggressive responses in ways that minimized partisan differences, though we think this warrants additional study.
Conclusion
Accusations of Russian hacking in the 2016 US presidential election raised the salience of cyber security. However, there are still a number of unanswered questions about the circumstances under which particular policy responses are warranted and the public’s attitudes about the conditions that justify this range of responses. In this research, we focused on how the certainty of attribution and the nature of attack affected public opinion.
We found that individuals support the notion of equivalence in that the nature and magnitude of the initial cyber-attack influence support for aggressive forms of retaliation. When a cyber- attack’s effects cross over into actual fatalities, for example, the public is considerably more likely to support airstrikes in return. Partisan effects had the most consistent effect on support, with bipartisan consensus about attribution increasing public support for a range of retaliatory measures. Scholars have long viewed partisan consensus as an important determinant of public attitudes, but it may be even more relevant in an era of political polarization. With consensus even more difficult to reach, the public may view this outcome as requiring a higher evidentiary standard and thereby an even more important signal of the assessment’s objective merits.
This study represents the first known investigation of public attitudes toward cyber security, but it should not be the last. Other scholars should consider varying attributes that were bracketed for this analysis. For example, how does the nuclear status of the perpetrator affect respondents’ willingness to retaliate? Does Russia’s nuclear status deter respondents from supporting the use of force – which could lead to escalation – in more acute ways than would be the case than if the culprit were non-nuclear (e.g., Iran)? How would the public respond to considerably lower levels of kinetic cyber-attacks on infrastructure with few or no deaths? Would disagreement within the intelligence community or from the private cyber sector affect respondents’ attitudes about retaliation? Recent political debates suggest that the issue of cyber security is here to stay. It behooves scholars to carry out additional systematic social scientific inquiry about the relationship between cyber-attacks, attribution, and domestic policy preferences.
Footnotes
Acknowledgements
The authors would like to thank Mariel Barnes, Sarah Maxey, Jeff Friedman, Jon Lindsay, and Rebecca Slayton for helpful feedback on earlier versions of the manuscript.
Correction (June 2025):
Declaration of Conflicting Interest
The authors declare that there is no conflict of interest.
Funding
This research received no specific grant from any funding agency in the public, commercial, or not-for-profit sectors.
Notes
Carnegie Corporation of New York Grant
This publication was made possible (in part) by a grant from Carnegie Corporation of New York. The statements made and views expressed are solely the responsibility of the author.
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
