Abstract
This teaching case describes the 2022 Costa Rican ransomware attack national emergency—presenting stakeholder perspectives of perpetrator and prey along with a proactive cybersecurity defense framework (IMSBI), crisscrossing cryptocurrency laundering and ethics.
Act 1: The predator
Alia, armed with some sweet tea and spiced biscuits, returned to her desk, quietly acknowledging her colleague, Anton, as they prepared their ransomware attack strategy. 1 Alia and Anton had their untraceable “.onion” websites (.onion sites are unregistered and untraceable) using Tor browsers, and ProtonMail emails open. Both were switching their chat messages between Signal Private Messenger and IRC (Internet Relay Chat), both encrypted with no IP 2 -logging. They were seasoned but unscrupulous black-hat hackers 3 working for an infamous ransomware outfit called Conti.
Alia and Anton were the Conti hackers working to deliver custom ransomware for a 3rd-party cybercrime outfit nicknamed WizardSpider. Alia and Anton would provide the attack vectors (the ransomware software) and WizardSpider would use it to attack specific high-value targets, mainly organizations and government agencies willing and able to pay a ransom. When a ransom was received, WizardSpider would pay a ransomware provision royalty to Conti. Conti was offering a franchise, and anyone, whether a disgruntled employee or a cybercriminal outfit, could be an ad-hoc franchisee. This was RaaS (Ransomware as a Service), an emergent, malicious business endeavor (Kshetri, et al., 2022).
“What should be our attack strategy?” Anton asked. “Should we go for a technical attack? There are always vulnerable unpatched firewalls, exposed ports, and RDP (Remote Desktop Protocol) vulnerabilities. Or should we use a different strategy?” Alia turned and spoke with certitude, “Organizations are throwing money at cybersecurity technologies, everything from patches to intrusion detection systems (IDS), and even honeypots to lure and trap hackers. But, in the mad dash to invest in cybersecurity technologies, most of these organizations forget to improve their antiquated processes and train their users. So, let’s try capitalizing on antiquated processes and user naivete by phishing user credentials using spam emails.
And remember that the attack timing must be spot-on. Let’s launch the attack when the security is low. That often happens during changes and transitions such as elections and the start of holidays, including specific days of the week such as Fridays and Sundays, when staff are relaxed, and their guard is down. Targets are more likely to pay up when they get to work on a Monday and panic sets in!” Alia smiled.
Anton replied, “Attack when the target relaxes. Demand ransom when the target panics. The playbook is so easy.” Alia added, “Let’s not forget that we need to give them a very short time window to pay up, that time pressure causes them to be even more careless.” Anton, raising an eyebrow, opportunistically added, “Perhaps we can even plant a second trap while they are panicking trying to bring their systems backup, and taking down their own defenses while they do! Sometimes in the panic they create new usernames with blank passwords just to see if they can get into their data.”
Alia calmly remarked, “Well, we could, and trigger it later, but we don’t want to annoy our affiliates, so let’s stick to what we are paid to do. In any event, our affiliate, WizardSpider, might want to attack multiple related systems, no doubt triggering a series of attacks over many days or weeks, continuing, and escalating the panic.”
Act 2: The prey
It was Monday, April 18, 2022. It was another beautiful Costa Rican morning with a warm spring sun rising over the cool green forest and blue sea. Emilio, a senior manager for the Costa Rican Ministry of Finance (Ministerio de Hacienda), was on a handsfree Bluetooth conference call in his car, driving briskly towards his office. Despite feeling flustered, sweaty, and uneasy, Emilio’s voice was calm, his demeanor composed, but his instructions, terse! The conference call was ablaze with one single topic of panic.
No Costa Rican Finance Ministry employees were able to access the tax and customs databases!
The timing was particularly interesting. Post-elections, a new government was in waiting. The previous president, Carlos Alvarado Quesada, was handing over the Presidency to Rodrigo Chaves Robles on May 8th.
Since Sunday night, a series of Twitter messages under the username BetterCyber had been retweeted around the world. They began with the following (Figure 1). Initial hacker message (courtesy Security Affairs (2022)).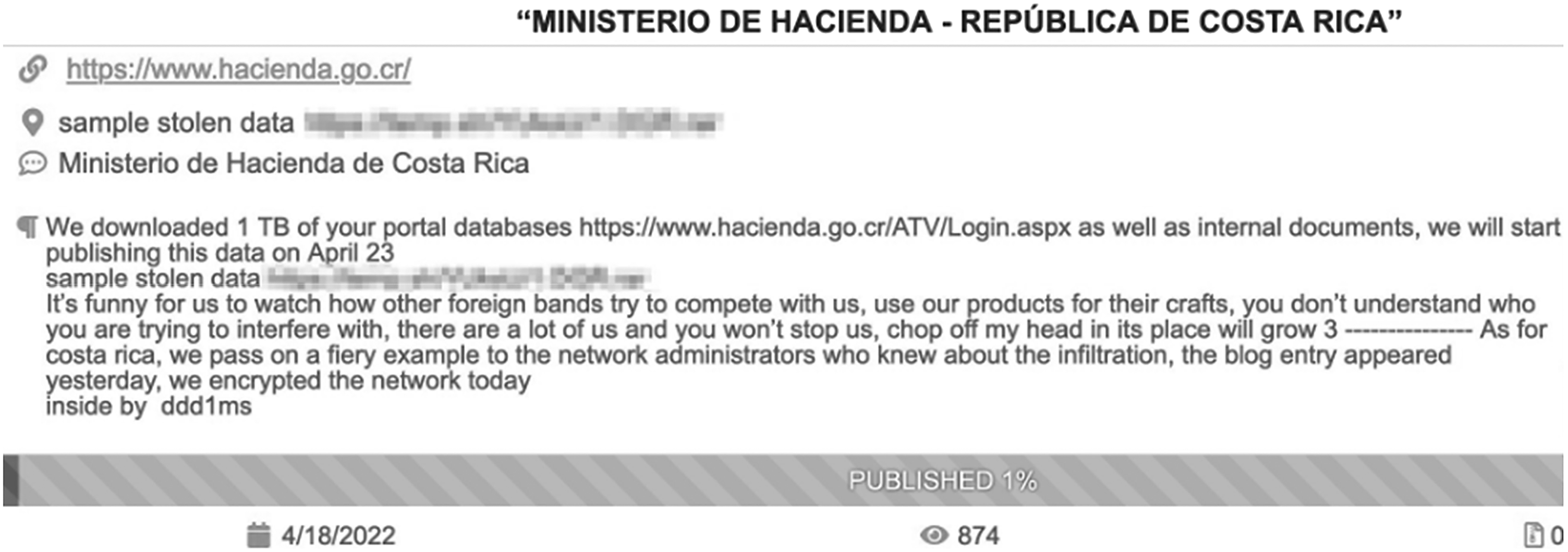
Everyone on the conference call knew what these messages presaged. The Costa Rican Ministry of Finance was a Ransomware attack victim. And Conti was the perpetrator. According to the tweet, hours had passed between the blog post about a ransomware hack and exfiltration and encryption of 1 TB (Terabyte) of taxpayer files. Hundreds of servers and two main systems, the Virtual Tax Administration (ATV), used for tax filings, pensions, and returns and the Customs Information System (TICA), for customs control, were crippled.
As Emilio entered the Finance ministry building, there was muted chaos. In a couple of hours, the Finance Ministry, via an official press release and through social media, would inform all Costa Ricans that “due to technical problems,” tax filing deadlines would be extended, without any reference to the ransomware hack.
The Conti ransomware hackers kept communicating via an anonymous Twitter channel, bypassing government efforts to control and censor information about a ransomware attack. “We ask only 10m USD for keeping your taxpayers' data” and “We will continue to attack the ministries of costa rica until its government pays us. Attacks continue today”, followed by “If the minister cannot explain to his taxpayers what is going on, we will: 1) have penetrated his critical infrastructure, gained access to over 800 servers, downloaded over 900 GB of databases and over 100 GB of internal documents, databases in the MSSQL mdf format, there is more than just the email, first name, last name… If the minister considers that this information is not confidential, we will publish it. The leak problem is not the Ministry's main problem, their backups were also encrypted, 70% of their infrastructure will probably not be able to be restored and we have backdoors in a large number of their ministries and private companies. We ask for a significantly small amount of what you will spend in the future. Their export business is already in trouble and they've already lost the $10 million they could have paid us.”
Emilio knew that an attack on a country’s government Finance systems might simply be the tip of the iceberg: should the government hush up on the ransomware attack, especially during political transition? Other government databases and systems are connected either directly or indirectly to tax records—what if any of these systems were also attacked and hacked? Could the country operate? What could be the fallout—economic, political, social?
Costa Rican attack timeline.
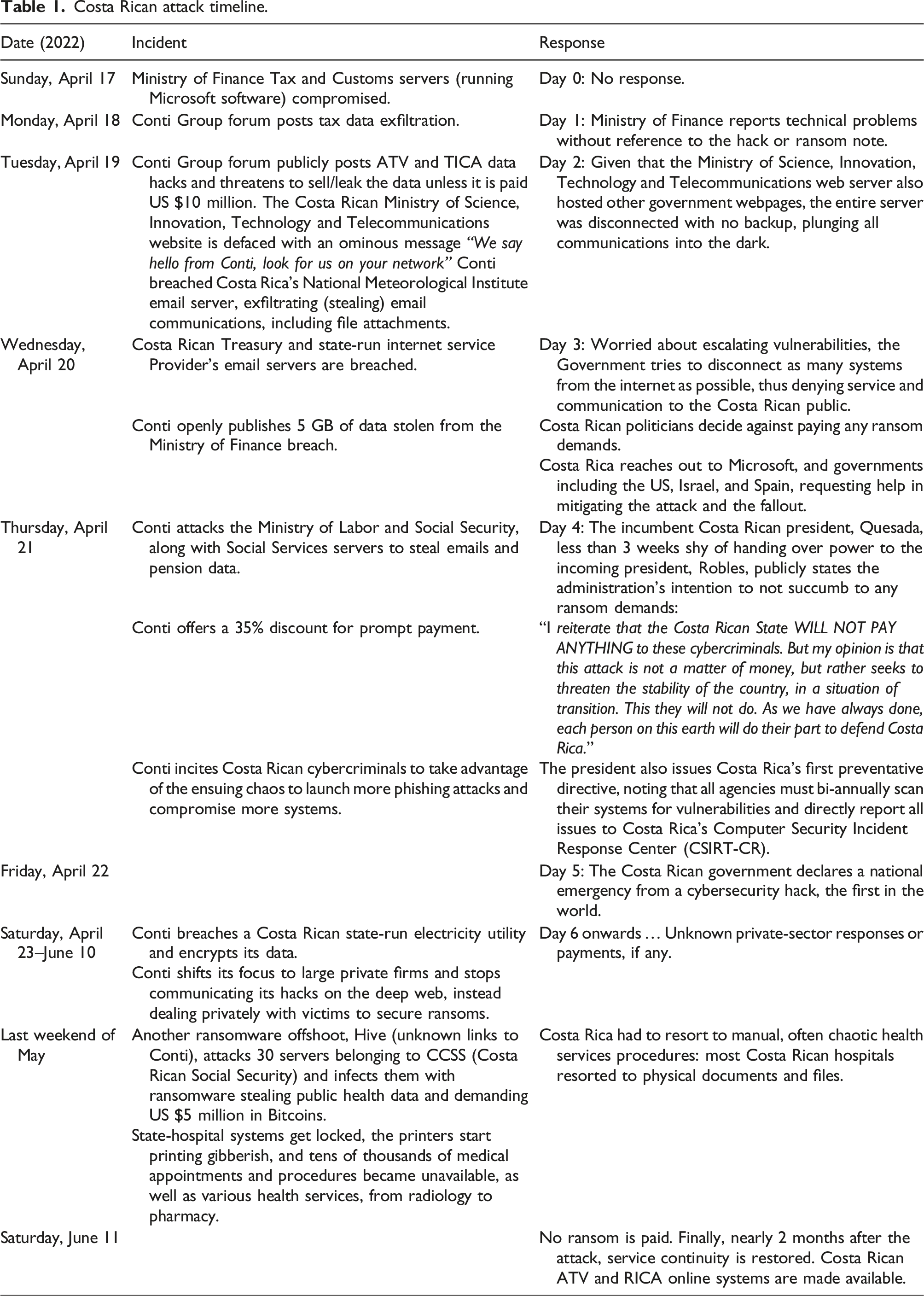
The attack on the Costa Rican government, was, according to Conti, “the beta version of a global cyberattack on an entire country” with the potential to overthrow a government.
Had the systems administrators been negligent and not noticed the blog? Even if they had noticed the blog, was there a well-defined IRP (Incident Response Plan) process to mitigate the threat?
But what could they do about it? What could they have done to prevent it?
Act 3: The context
Ransomware: Exfiltrate and extort
We live in a digitally transformed age full of innovative conveniences—and of digital hacks. All of us are constantly on the defense. A 2021 IBM report on the Cost of a Data Breach (IBM, 2022), ransomware attacks have grown exponentially with digital transformation. The average incident cost is nearly $4.62 million for a ransomware attack, including payment, lost business, response management, and mitigation.
Ransomware hacks use obfuscated malware to breach and lock systems and violate data confidentiality (privacy), integrity (accuracy), and availability (accessibility) by hijacking data using encryption or exfiltration (stealing) (Diffee and Datta, 2018). Ransomware criminals then attempt to extort a ransom for a decryption key (Leo, et al., 2022), often threatening their victims with selling the data on the dark web or publishing the data on the Internet until a ransom is paid (Kara and Aydos, 2022).
Ransomware’s primary motive is financial (Connolly and Borrion, 2022). Ransomware criminals monetize their hacks by locking companies out of critical systems by encrypting files and then demanding a ransom for decryption. Ransomware criminals mainly focus on critical and/or sensitive data such as public taxes, health records, student data, financial data, and corporate operational and R&D data.
Ransomware has spun its own criminal ecology. The dark web (or darknet) hides perpetrators’ locations (e.g., IP addresses). Highly encrypted messaging apps allow cybercriminals to conspire and communicate, circumventing law enforcement methods to track and trace communications. Darknet marketplaces such as Russian Market or Sheep and untraceable crypto wallets such as Monero (XMR) work like shell companies, hiding perpetrators’ footprints.
Unsurprisingly, not unlike the growth of piracy in the Horn of Africa, ransomware hacks have become a lucrative business model in impoverished economies, from North Korea to Brazil and from Iran to Russia.
Ransomware criminals commonly use two main approaches, both of which were used in the case of Conti’s Costa Rican ransomware hack.
The first approach relies on accessing and exfiltrating data with the intention of releasing the data typically in a drip-feed manner onto the internet, causing exposure for the victim(s) and damaging the business credibility and reputation of the source, if a ransom is not paid. This approach is typified by an initial leakage of a very small amount of data, as proof-of-concept that the threat is real. The approach allows cybercriminals to leverage long-term blackmail and extortion.
The second approach relies on breaching systems and encrypting the source data where it resides, charging a ransom for a decryption key, with data exfiltration being a secondary objective. In this scenario, there is not usually a drip-feed of data at any point, rather the hackers’ leverage resides in the inability of the target company or organization to access their own data, crippling business functions and continuity. This second approach is rather like “Why steal the painting from the museum, when we can stop everyone looking at it?”
Ransomware criminals are unscrupulous (Bajpai and Enbody, 2020), but their targets have the following common set of denominators, which help explain why there are so many ransomware attacks on education,
4
healthcare, and government municipalities: 1. Organizations that deal with sensitive information such as personal records, credit card data, transaction histories, citizen data, or mission-critical operational data that simply cannot function without access to their data. 2. Organizations whose technological systems have been built up over many years, using different software, a range of systems of different vintage, running on dated hardware and involving a mix of embedded systems or operating systems: such complex systemic collections can have many weaknesses, including poorly patched software, a mix of user management and security controls, and use functionality created at a time before cyber-intrusion was as prevalent. 3. Organizations that operate with tight operational budget and resources such as public sector agencies where service provisioning supersedes cybersecurity concerns. Such organizations often suffer from processes and people that are poorly designed and poorly trained to deal with cybersecurity, commonly lacking even basic continuity plans and protocols.
Un-traceability of the perpetrators is core to the ransomware model (Conti, et al., 2018). Though many cybercriminal outfits let it be known who is behind an attack, they do not want their identities or whereabouts known, and they do not want any paid ransom to be traceable. The emergence of digital cryptocurrencies has radically heightened ransomware attacks and dangers. Ransomware criminals demand their financial ransom be paid using untraceable cryptocurrencies, compounding the crisis further (Kshetri and Voas, 2017).
The paradox of cryptocurrencies: Transparency and opacity
Cryptocurrencies, or digital currencies that are encrypted to avoid being stolen, are rapidly becoming the mainstay of global capital markets, trying to replace physical currencies (Hafner, 2020; Liu and Tsyvinski, 2021). But cryptocurrencies are paradoxical.
Bitcoin, the first cryptocurrency, created in 2009, was built using a “blockchain” philosophy, where every currency transaction (block) was transparent, verified and linked together as a “chain” ledger that could not be changed or refuted. Since then, the world has experienced a cryptocurrency mushroom, from central bank-issued “GovCoins” such as China’s DigiYuan to untraceable, laundered “Monero,” ransomware criminals’ lingua franca.
A blockchain infrastructure works as a series of process steps. 1. Blocks on the Blockchain (think of each block as a database tables) have the following attributes: a. A Header, which consists of i. The Merkle Root (the hash tree that concatenates nodes with an SHA256 algorithm to make sure that it has integrity, and the nodes (leaves) and their branches are unaltered). b. A Timestamp. c. The previous block hash that identifies the origin of the transaction, and d. A Nonce (number used once and changes with time)—the missing piece of the puzzle that blockchain miners need to solve (called PoW or Proof of Work). i. To create a new cryptocurrency, for example, a new Bitcoin, Bitcoin miners must find a nonce value that, when plugged into the hashing algorithm, generates a hash value that is lower than the target difficulty. 1. Solving the nonce is not mathematically challenging but has a very low probability (e.g., rolling 1000 dice pieces and having all show a 5). 2. Each cryptocurrency transaction creates a transparent and verifiable PoW block. 3. Each is connected by a hash that acts as an identifier for that specific cryptocurrency (think of it as the ID number on each of your $, €, or £ note). 4. Every new block references the old block with a previous hash (prevhash). 5. So, the entire hash sequence serves as a ledger (chain) for the block. 6. Unlike general databases, you can only perform CR (Create, Read) and not UD (Update, Delete).
A blockchain infrastructure offers a structured process to create (mine) and transact cryptocurrencies. There are many different types of blockchain infrastructures, some open (transparent) and some opaque—hiding the transactions and the keeping the transactors anonymous—therein lies the paradox. And ransomware cybercriminals leverage this anonymous yet speedy transaction process to extort ransom via a series of cryptocurrency laundering outfits.
If a ransom is paid using a cryptocurrency, the criminal is immediately paid, the payment cannot be traced, and the transaction cannot be undone. Cybercriminals don’t wait 5 days for “checks to clear”! For example, Monero, a popular cryptocurrency used by ransomware cybercriminals, uses an untraceable “RandomX” blockchain infrastructure.
Indeed, two inherent blockchain characteristics provide cybercriminals with a ‘safe’ way to receive a ransom (Clohessy et al., 2020): 1. Pseudonymity that allows users to hide their identity for financial transactions. The blockchain model obviates a need for any third-party organization to verify a transaction: A sends bitcoins to B directly, verifiably, securely, and demonstrably, without any financial clearing house or bank to handle the transaction: provided enough bitcoins are in one’s digital wallet, one can transact. 2. Immutability, essentially proof that a transaction has occurred. Payment of a financial amount is written indelibly into the block “chain” and cannot be edited or undone, and so the cybercriminal can be certain that funds have been transferred to their digital wallet.
As such, cryptocurrencies are the mainstay of cybercriminal payments, a core tool in their toolbox, with the advantages of immediacy of payment, hidden identity, and verification of transaction without fear of being traced later. If ransoms are paid, the monies are gone into the cyber-ether, a one-way trip.
Act 4: Proaction is the best defense
Despite the beautiful and verdant Costa Rican summer, there was a sense of despair and gloom. Emilio and his team had been busy putting out fires. Their data had been leaked and sold. The public had lost confidence in the new government’s ability to manage a cybersecurity crisis.
Good heavens, cybersecurity attacks even culminated in declaring a National Emergency!
As systems were being restored for operational continuity, Emilio was tasked with creating and guiding a preventative policy for the future. He, along with heads of Costa Rica’s Computer Security Incident Response Center (CSIRT-CR), eagerly anticipated the arrival of Elsa and Maya, two cyber-preparedness experts heading a joint UK–US task force. Elsa and Maya were arriving as advisors to the Costa Rican government on post-breach protocols.
The Costa Rican group had one and only one question in mind-one that would define their agenda.
How should organizations prepare themselves to combat and respond to ransomware attacks and extortions?
Proactive preparedness
The digital age and the 4th Industrial Revolution is an age of innovative technologies conveniences—and digital hacks. But, as the adage goes, the minute you invent a new mousetrap, the mice get smarter.
Interestingly, malware, including ransomware, operates on a simple premise: identify the most accessible weakness in either the technology, the process, or the people. Then set the trap!
The Costa Rican ransomware hack began with the ransomware criminals getting their hands on an employee’s compromised login credentials. The ransomware attackers used that information on a VPN (Virtual Private Network) connection, originally meant for secure, encrypted access, to enter the Costa Rican Ministry of Finance Systems. Even though the perpetrators lurked in the shadows, moved laterally from one system to another, they remained unnoticed.
Insofar as the Ministry of Finance was concerned, all was in order, mainly because there were no processes in place to check for unapproved systems access behaviors. Ransomware malware is designed to be destructive and hidden. Therein lies the rub. If organizations do not have well-defined processes to monitor who’s accessing what inside and across systems, organizations remain woefully ignorant of how or when a malware got in, prevention, detection, and mitigation (recovery) become harder with every passing moment, and a ransomware attack can become a debacle.
Organizations need to know how to keep their doors sealed, how to detect if already in and, critically, how to get back in business even if breached.
That is what Emilio wanted to talk about. He was feeling the pressure from the new government not to have the debacle repeated.
Maya took over the conversation, took a deep breath to gather her thoughts, and began.
“To stop ransomware attacks, every organization must focus on four specific activities: IMSBI (Identify & Monitor, Secure, Backup, Insure)”.
Maya and Elsa continued, outlining what each of these 4 activities entailed…
Identify and monitor systems (hardware and software), data
In a digital economy, every passing day adds a larger digital footprint where organizations use systems to store data, and people and systems access data.
The Costa Rica ransomware attack highlights how the government had not adequately identified all systems and people accessing confidential and sensitive public tax data, allowing the malware to hide in the system and exfiltrate data without their knowledge.
Identification does not begin and end with an inventory. Systems run, people, work, and data flows. Data is not just at rest but in motion. Monitoring of systems, data, and people is therefore indispensable.
Data is the salient resource for every operation and strategy, and it is imperative that organizations know the following: 1. What types of data do we have, and have we classified and valorized them based on their confidentiality, sensitivity, and use? 2. What systems are accessing what data and when? Which systems should access what data and how? What parts of the data should different systems accessed? Should access be limited to certain time and conditions? 3. Who should approve access to specific data and what data can be accessed by whom?
In Costa Rica’s case, the government had never identified or inventoried its systems or classified its data in terms of their sensitivity or operational needs. In short, there were no data and IT security governance in place. Alia and Anton from the Conti ransomware group, as well as WizardSpider, the ransomware affiliate, knew that already. Months before the attack, WizardSpider had joined multiple Costa Rican government social networks and befriended Costa Rican government employees’ professional groups where users requested and dispensed advice.
In these virtual professional communities, WizardSpider targeted users that openly bemoaned about their work to quickly learn about process failures, data disorganization, and other operational problems such as lack of transparency and approvals. They fed that information to Conti, providing Conti information as ammunition to strategize on their ransomware attack vector and attack surface.
The Conti ransomware attack used a compromised user VPN credential to access the system and install a malware called CobaltStrike, whose main job is to disguise itself as a legitimate system process, set up a remote command-and-control (C2C) to subsequently download the ransomware and steal the data. It was the same malware used in the infamous 2020 Solarwinds’ Orion server Sunburst hack (Datta, 2021). But, because there were no data or systems monitoring mechanisms in place, there were no directed security, no backups, and no Cyber-Insurance as a hedge.
Similarly, systems that could access sensitive and mission-critical data were never systematically allocated or monitored. As a result, even when the CobaltStrike malware created new threads (system processes) to access other systems, data files, and networks, no flags were raised and the issue was not escalated as a concern.
Unsurprisingly, the clandestine breach and data exfiltration were never noticed, even though the systems had been breached and malware had been installed more a fortnight before the ransom demand.
Secure Systems and data
Once systems and data are identified and monitoring mechanisms are instituted, they must be secured. But security is not a single standard black-box solution. Instead, security measures must be specific—corresponding to specific systems and specific data.
One of the most devastating, and perhaps even active today, hack was the 2020 Solarwinds’ Orion Server Sunburst hack (Datta, 2021). Solarwinds had a multitude of vulnerability-management software to protect its systems but nothing that secured its software update supply-chain. That left the update process unguarded, and the Sunburst malware disguised itself as an update via GitHub. Thousands of clients installed the malware, which even affected the US departments of Commerce, Defense, and Energy. SolarWinds’ oversight on securing its GitHub software update misconfiguration led to a worldwide calamity.
To protect against ransomware, organizations must secure their entire software supply chain, from endpoint devices to access the network to 3rd party vendors.
Secure data using encryption
Encryption, or the secure encoding of data to make it unreadable even if compromised, ensures that “the loss of possession does not entail the loss of confidentiality.” The Costa Rican government did not encrypt its data. Nor did a lot of SolarWinds Orion server customers, allowing perpetrators an easy exfiltration of sensitive data.
Secure data integrity
Data integrity is meant to ensure that data has not been tampered with or corrupted or missing in any way. While blockchains are meant to provide an infrastructure for ensuring end-to-end data verifiability and integrity, blockchains are still an emerging technology with a multitude of creases that need ironing. So, companies must devise ways to ensure data integrity so that they can guarantee the authenticity of the data used to process, store, or recover.
A database administrator (DBA) working for a Swiss telecoms company oversaw the running of daily and weekly backups of its production Oracle database, with millions of billing entries related to mobile phone calls, charges, durations, routing, and so on. Common server scripts automated the backups.
One Monday morning, while dealing with a deluge of emails, the DBA realized that the production database was corrupted. The DBA restored the database from the daily backup from the preceding Sunday evening, losing a few hours of precious mobile phone data. However, the backup was empty!
The problem arose from an insecure and unmonitored data integrity process. The backup script pointed to a wrong database that was no longer in use. The clone had the correct table structures and relationships, but no data. The DBA had restored the production database using an empty backup, over-writing corrupted data files with empty files. The company had failed to periodically audit and ensure data integrity.
Organizations need to rigorously check data integrity, with only one assumption—that integrity has failed, and initiate better processes that can verifiably ensure integrity.
Secure users and secure processes
Securing users requires organization-wide training and securing processes requires reconfiguring exiting ways of doing business. The SolarWinds attack is a prime example of how an inefficient software update supply chain process can introduce unknown vulnerabilities. The 2021 Colonial Pipeline ransomware attack that disrupted petrol stations across the US Northeastern states was caused by a compromised VPN password—the same cause behind the Costa Rican government ransomware attack. The issue stemmed from an employee reusing the same VPN username and password on a public site—leading to an easy compromise. Hackers then used the compromised credentials, called “credential stuffing,” to access the corporate VPN.
One of the solutions to eschew user errors, the weakest link in any cybersecurity effort, is to implement a “zero-trust” security strategy based on granting users least permissions and privileges, based on the POLP (Principle of Least Privilege) philosophy.
POLP is a great “minimal privilege” policy solution that restricts users to access the least amount of resources under their job purview. Any extra resources, especially sensitive data that a user might want to access would require a digital approval and would be logged, therefore creating a moving perimeter. In addition, companies also use privileged bracketing that limits access-time for all software accessing data, reducing the chances of a malware or hackers loitering and sniffing to find data that can be exfiltrated or encrypted for disruption or profit. Organizations are also relying more and more on AI (Artificial Intelligence) to monitor problematic, flaggable behavior in systems, bots, 5 and users.
A notable threat under IMSBI is emerging technologies, particularly, IoT endpoints. Among new technologies that are increasing complexities, allowing cybercriminals to penetrate systems to hide in the shadows, are IoTs, network-connected endpoint “smart” devices—smartphones, smart plugs, smart bulbs, smart door openers, and smart fridges—the list goes on.
Convenient and cheap, IoTs are everywhere, including in the government conference room. When the projector turned on, the conference room sensed and automatically lowered the screen, dimmed the lights, and pulled down the window shades. Hackers could leverage these IoTs and turn them into botnets—remotely controlled zombies that can infiltrate systems, exfiltrate or encrypt data, and wreak havoc on command.
There had been a growing number of industrial IoT attacks, from a Chrysler Jeep’s control taking over with a hacked OBD controller, a remotely robotic car painting arms hacked to overpaint, or, menacingly, the Mirai botnet attack that used IoT cameras’ default passwords to even bring down a large swathe of the Internet! While individual IoT hacks were rare, hackers could use individual IoTs to hack into other connected systems sharing the same network—a serious concern in an age of WFH (Work from Home).
IoT endpoints operate in the frontline but are also weak points—backdoors to the castle keep. Unless secured, IoTs can be the unprotected doorway to malware whose intention is to attack more critical technologies and data.
No system is secure and vulnerable to ransomware and other hacks unless systems and data are well-identified and monitored, secured based on data and systems priority, backed up locally and in the cloud, and insured as a post-attack hedge.
Backup systems and data
Data and Systems backups create useable, periodic snapshots of system configurations and data for purposes of recovery and restoration.
Where to backup: Systems and data can be backed up in various locations: dedicated connected servers, external USB or hard drives, or in the cloud (remote, Internet-based servers). Regardless of the backup location, organizations must embrace backup as an operational imperative.
Some organizations find it prudent to practice backups across multiple locations, backing up critical systems and data (e.g., applications, configurations, transaction logs, sensitive user data, and permission settings) for purposes of operational continuity and compliance
How to backup: Cloud backups, especially with legitimate backup providers, not only offer accessibility but also additional security such as encryption, MFA, logging and monitoring, access control, backup periodicity, and recovery procedures. Reputable cloud data backup organizations such as Google Docs, MS OneDrive, and Amazon S3 often practice object-storage setups for data immutability. In data immutability, changes are never overwritten but added as a revision and reported, if needed. Every single system change, data access, and/or file changes are logged as new versions with a user- and system-log and timestamp. Some cloud-storage and backup services even practice object locking to stop any lock systems and files to prevent unauthorized access.
Although established cloud backup services are generally secure, and frequent backups are “baked in,” organizations, as a part of their IRP (Incident Response Planning) and BCP (Business Continuity Planning) should regularly run simulations of restoring critical systems from backups, to be sure that they work when needed.
When to backup: Backup periodicity, that is, the frequency and type of backups, can be informed by the criticality of potential loss: can the company cope with an hour’s loss of data, a day, a week? And companies need to know how long it takes to restore from backups should the need arise, as it can create more downtime and loss of earnings.
The 2021 ransomware attacks against the Dutch company Hoppenbrouwers Techniek highlight the importance of backups. Hoppenbrouwers Techniek, a Dutch automation and engineering company, foiled a ransomware attack by an infamous cybercriminal group called REvil, using backups and good internal communications over an intense weekend effort. REvil had infiltrated MSPs (Managed Service Providers) via Kaseya VSA, a popular IT management software. Luckily, Hoppenbrouwers had a backup in place that had backed up all data until Friday noon. So, Hoppenbrouwers communicated with all its employees to secure more than 80% of various devices in use and restoring over 70 terabytes of data across 150 files and application servers from their Friday backup and was back in business by Monday.
Backup strategies should also consider backup data integrity, as discussed in the Swiss Telecom’s empty database. Malware can corrupt backups and remain latent, sometimes triggered long after infection. It’s important to know that backups are free from any malware; otherwise, a future restore could reinsert malware into the organization. So, backups need to follow a 3C model: clean, complete, and cooperative. Backups should be clean and free from malware, complete as in having integrity, and cooperative as being able to easily recover and integrate systems and data, whether due to a systems failure or a cyberattack.
Insure systems and data
Like any insurance, cyber-insurance is a hedge against cyberattack losses, be it from disruption or ransom. While proaction is the best defense, cybersecurity breaches are gaining ground.
Cyberattack costs are more than a financial setback or inconvenience. Rather, the costliest aftermath of a ransomware attack is the loss of revenue from business discontinuity. Can customers and vendors access our site to request and deliver services, respectively? Is there data integrity or are we using corrupted data? The 2021 ransomware attack that encrypted Colonial Pipeline’s billing system (Datta and Acton, 2022) and data left Colonial Pipeline unable to bill customers leading to a total disruption of gasoline provisioning in the northeast US and millions in lost revenue. In such instances, cyber-insurance offers a risk hedge.
In the case of Costa Rica where the entire public data was compromised, tantamount to an identity theft of the entire Costa Rican population and business entities, government might face a dilemma of the cost and effort feasibilities of issuing new identities to reduce counterfeit claims and maintain operational continuity (also called BCP—Business Continuity Planning). That could cost a government hundreds of millions.
Finally, cyber-insurance can force organizations to become proactive, given that cyber-insurance vendors commonly audit an organizations systems and data governance (policies surrounding the operation and protection of data).
The ransom—business continuity ethics
Elsa and Maya refreshed themselves with fresh fruit and some sparkling water. Even though they had been invited to offer useful advice, they knew very well that Costa Rica was in dire straits.
Elsa spurred the conversation, “There is a financial cost to downtime, even in instances where backups are solid, available, and systems are recoverable. But after an IT failure, or a cyberattack, the first step is determining the facts – what has been compromised, and what exactly do we need to restore or recover. The next step is the ‘how’ and ‘what’ to restore! And once restored, validation checking takes more time, before any recovered data or systems go ‘live’”.
“These things take time, during which an organization may not be able to transact, possibly losing business.”
Maya added, “Imagine the airline whose car rental partner cannot take bookings because of a breach. It’s not just the car rental company suffering, the airline’s reputation can suffer, as can its flight sales. The car rental company needs insurance that covers not only their own loss, but this transitive effect on the irate airline losing business. It’s important to be insured for this, and insurance costs alone will prompt organizations to be better prepared.”
Emilio spoke, with a certain desperation in his voice, “We are facing an existential dilemma in Costa Rica! Our customs databases are compromised and inaccessible. So are our tax databases. Every single day the Costa Rican government is losing $32 million. We are sitting on the fence. Should we pay the once-off $10 million and resume operations, or should we deny ransom and lose in multiples so that we do not set a precedent?”
Elsa and Maya gently nodded, in agreement with the latter. The rest of the group was reticent, but it was a matter they had been debating since the ransomware demand—should we pay the ransom to get back our identities and our business?
“I understand your dilemma,” Elsa remarked. “However, once data is breached and exfiltrated, there is no certainty on how many digital copies might be existence. Paying the ransom does not ascertain that digital copies of the data have not been sold or are being sold elsewhere, as we speak. In the dark web, news travels faster than the speed of light and can attract many more cybercriminals to the waterhole. Then, it’s ransom’s labor lost – because…” Elsa paused and added, tersely, “there is no honor among thieves!”
“So, our advice is not to pay!”
Act 5: Intercepting the ransom trail
The day was winding down. Emilio and other government officials had taken copious notes. They would need to establish a task force and a committee to implement the IMSBI framework across all government agencies as well as every government contractor that worked with them.
Emilio raised his hand and spoke in earnest, “We are eager to follow your defensive IMSBI best practices framework. But ransomware is about stealing and extorting money. Beyond defense, if we are to eliminate ransomware threats, why isn’t making every ransom traceable the first step? Every ransomware demand is a cross-border crime, and, like any cross-border crime, it is important to trace the money. Although traceability is a core blockchain attribute, cybercriminals have found ways to circumvent traceability. How do they manage that?”
Maya responded, “You’re spot on! Cybercriminals have created ransomware as a business model for the digital age. All business models need monetization and a capital market to manage finances. This has popped up an entire financial ecology – an ecology of cryptocurrency laundering. Consider groups such as Clop and FancyCat, both recently dismantled! Now, mind you, Clop and FancyCat weren’t ransomware criminals. Instead, they laundered cryptocurrencies for cybercriminals on the dark web”.
“Cryptocurrency laundering operations constantly change their modus operandi to evade prying eyes of law enforcement. However, there are common operational denominators.”
Crypto-launderers: • Operate out of large macro-cryptocurrency exchanges, hiding their nefarious money laundering among millions of legitimate transactions. • Prefer that cybercriminals request payments in “privacy coins” such as Monero, Dash, ZCash, and Verge. Privacy coins operate on untraceable blockchains that conceal user identities, do not require receiver and sender verification, and disguise the transaction to make the entire transfer process untraceable. When cybercriminals request Bitcoins, crypto-launderers advise cybercriminals to not use pseudonyms and instead use several “unlinked” addresses via a private channel to disguise the recipient. • If paid by Bitcoins and/or Privacy coins, as a common precaution, use cryptomixing, for a fee. Cryptomixers, as the name suggests, use a money-laundering process that combines huge amounts of licit and illicit cryptocurrency transactions across many licit and illicit users. These cryptocurrency combinations of various denominations and values make it very difficult to spot a single ransom transaction. Cryptomixers then deposit the funds back to cybercriminals at random intervals and random amounts, thus obfuscating and laundering the “dirty” ransom. • Further employ an obfuscation process called crypto chain-hopping that combines multiple Privacy coins across their corresponding blockchain infrastructures rapidly and in random succession. The basis for crypto chain-hopping is that it is difficult for law enforcement to track rapidly hopping transactions across various blockchain infrastructures.
Elsa, quietly listening to Maya, spoke, carrying the momentum.
“Only a handful of Crypto-launderers dominate the scene, with 25 crypto-launderers managing nearly 50% of ransoms (European Union Agency for Cybersecurity (ENISA)). Ransomware developers have evolved to a RaaS (Ransomware as a Service) business model, where Ransomware groups use affiliates as franchisees to launch attacks using their malware and then collecting a part of the laundered profits while even offering customer service (Datta and Acton, 2022).”
Maya appended, “While RaaS reduces Ransomware cybercriminals’ risk by diversifying the risk appetite to affiliates, they all tend to rely on their crypto-laundering ecology. That creates an opportunity and allows us and international law enforcement agencies to follow the money and crack down on the money supply, therefore making it more difficult for ransomware cybercriminals to receive and move money”.
“The problem, though, lies in the number of emerging cryptocurrencies and their own blockchains, each touting a newfound privacy feature. While privacy is a marvelous prerogative, it makes it very difficult for law enforcement to trace and close ransomware operation!
“But how much privacy would society be willing to sacrifice for security? It is Damocles’ sword – it cuts both ways!”
Conclusion
Even a malware can bring down a behemoth; this teaching case described a ransomware attack on an entire government and, by extension, an attack on a nation at a time of governmental change.
The paper forwards IMSBI as a Cybersecurity best-practice framework, describing a set of activities organizations should implement to secure their systems and processes from hacks and ransomware attacks. In the process, the paper provisions ethical considerations for decision making around whether ransoms should be paid. The IMSBI framework provides a systematic, proactive structure for organizations. The ethical questions provide ample opportunity for perspective-based debate and discussion.
Further, it is notable that it is a confluence of emergence of revolutionary technologies (such as cryptocurrencies via blockchain facilitating ransom payments) in addition to evolutionary technologies (such as the reliance of many organizations on myriad legacy technologies as a “soup” of overall IT systems—sourced, developed, and updated over time) have provided criminals with various open doors for malware breaches.
But commensurate with such a focus on technologies, and independent of such, is the ongoing and pervasive lack of attention to poor organizational processes that provide the cybercriminal with foci, and the tendency of many human behaviors to prioritize ease over care when using organizational systems. Whether systems are patched, or technology is modern, weaknesses pervade in poor processes and in careless behaviors—enticing ransomware predation.
Questions for discussion
1. What are the ethical issues in this case study? Should the Costa Rican government have paid the ransom to protect its citizens and economy? Would that set a precedent? 2. Who were the stakeholders affected by the attack? Were the stakeholders equally affected? What could you have done to protect each stakeholder group? 3. Is it the government’s responsibility to protect its citizens’ identities and/or other personal data? How would paying or not paying a ransom be informed by this? 4. Offer three ways you would have advised Costa Rica to defend itself from such an attack. Were there human errors, were there process errors (the way the government stores information), and were there technology errors? 5. Considering that the government was losing US $32 million daily because of the attack, is it reasonable to consider paying a once-off $10 million ransom? And is it more reasonable to pay the discounted amount? 6. What assurances might the government have had around future data leaks, if a ransom were to be paid? 7. How do cryptocurrencies work and why do ransomware criminals use them? Did the use of cryptocurrencies in the Ransomware attack compound the problem or help solve it? Debate and discuss.
Footnotes
Acknowledgments
We would like to acknowledge feedback and advice from various cybersecurity penetration-testing firms based in the UK and the US.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
