Abstract
Institutions, publishers, and scholars are grappling with the complex challenges of ensuring security while fostering access to knowledge. The drive to make research more easily available brings with it new cybersecurity risks, from safeguarding sensitive information in publisher databases to protecting the integrity of scholarly content. These challenges underscore the need for a coordinated approach that balances ease of access with robust digital security practices. This paper will examine the intersection of cybersecurity and access within academic publishing, exploring how industry stakeholders can collaboratively address these issues. With an increasing reliance on digital platforms to distribute and access research, ensuring security at all levels—while preserving the openness that drives scholarly innovation—has never been more critical.
An increase in recent cyberattacks on higher education and knowledge institutions
Recent news reports highlight a sharp increase in cybersecurity incidents affecting higher education and research institutions: • Cengage reported that the company experienced more than 8.2 billion cyberattacks in a single quarter, including email spam and phishing attempts.
1
• In 2023, the education and research sector faced over twenty-five hundred cyberattacks per week.
2
• One institution paid $1.14 million to resolve a ransomware attack.
3
• A total of one hundred and forty-four U.S. universities and one hundred and seventy-six universities abroad were hacked by the Mabna Institute, a group of individuals allegedly working on behalf of the Iranian government.
4
Several factors contribute to the rise in cybersecurity threats against higher education institutions. Historically, these institutions have underfunded cybersecurity efforts and often lack robust security measures, making them appear as soft targets to hackers. Moreover, academic environments frequently adopt emerging, untested technologies while simultaneously relying on outdated hardware and software. This paradox further increases their vulnerability. Colleges and universities are also seen as target-rich environments due to the vast amounts of valuable data they hold—including personal information, intellectual property, research data, budget details, and metadata from libraries and publishers. Additionally, these institutions often serve as gateways to publishers’ assets and licensed content.
The role content providers/library vendors play in mitigating risk
Any vendor or publisher whose platform stores data, whether metadata generated by libraries and publishers, or personal, financial, or medical information, has a responsibility to implement foundational cybersecurity best practices. “Protecting the perimeter” entails assessing how sensitive data might be accessed, which raises several important questions: • Is there an administrative dashboard through which the data can be viewed or modified? • Who has access to the back-end systems that store or transmit the data—developers, system architects, or others? • Are there standardized, automated policies in place for data retention and secure disposal?
The answers to these questions, when considered alongside the types of data involved, underscore the need for providers to implement strong perimeter protections. A fundamental starting point is the use of standard, secure authentication protocols, including mandatory multi-factor authentication. Certification and compliance frameworks such as ISO 27001 and NIST 800-53 can serve as valuable guides for identifying and mitigating vulnerabilities. In addition, organizations within the higher education and library communities often provide education and guidance that go beyond formal certification requirements. These organizations frequently draw on best practices from the federated identity community while also adhering to the certifications required by their users. Ultimately, vendors bear significant responsibility in adopting secure practices and collaborating with the community to advance secure authentication methods, such as federated single sign-on.
Steps libraries should take to mitigate cybersecurity risks
Like vendors and publishers, libraries play a vital role in mitigating cybersecurity risks and ensuring that the “handshake” between the customer and provider remains secure. Key strategies include educating librarians and end-users about security threats and data hygiene best practices, fostering strong partnerships with campus or central Information Technology (IT) departments, implementing multi-factor authentication, and supporting technologies such as SAML-based (Security Assertion Markup Language) single sign-on (SSO) and federated access. These efforts are essential to maintaining a secure information environment.
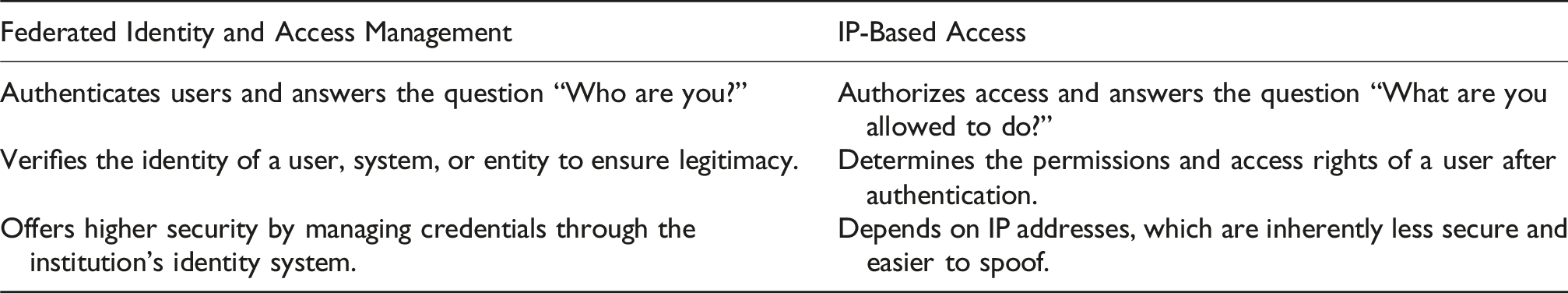
In the context of federated authentication, it is helpful to remember that many institutions still use proxy Internet Protocol (IP) tools to provide access to online resources. Although these tools can be integrated with identity systems that use the SAML, the access they enable is still based on IP addresses. Even when a proxy server verifies user credentials through a SAML-compliant identity provider, access is granted by routing the user through a server that presents a single institutional IP address to the content provider. In this configuration, SAML verifies the user’s affiliation with the subscribing institution, but the authorization itself remains IP-based rather than tied to individual users. From the perspective of publishers, vendors, and service providers, this approach resembles traditional on-campus IP access and lacks the enhanced security and user-specific detail offered by true SAML SSO.
Access methods can be viewed as existing along a spectrum. At one end is on-campus IP access, which requires no user login and does not verify whether the individual is an authorized member of the institution. Proxy access combined with a SAML login introduces a basic check to confirm institutional affiliation, but still does not authenticate users on an individual basis. At the opposite end of the spectrum is full SAML SSO, which securely verifies the user’s identity and their institutional affiliation, offering the highest level of assurance.
AI’s role in cybersecurity
Artificial intelligence (AI), in the context of cybersecurity, introduces both significant risks and promising opportunities. Key concerns include increased susceptibility to social engineering and phishing attacks, the misuse of personal data, and the unauthorized use of content for training large language models (LLMs). Vendors and libraries integrating AI into their workflows, particularly those deploying local LLMs or custom prompt-based implementations, must navigate a range of complex security challenges. These include defending against adversarial prompts and ensuring the responsible AI use by implementing safeguards that prevent the unintended collection of user data and content metadata for training purposes.
At the same time, AI offers valuable opportunities to strengthen cybersecurity. These include advancing best practices for threat detection and prevention, designing systems with privacy-by-design principles, improving incident response planning through greater transparency and communication, and developing educational programs to enhance workforce capabilities in risk mitigation.
The Scholarly Networks Security Initiative (SNSI)
In response to the growing threat of cyberattacks in higher education, the Scholarly Networks Security Initiative (SNSI) is actively working to address cybersecurity challenges that jeopardize the integrity of the scholarly record, the reliability of scholarly systems, and the security of personal data. By bringing together a diverse coalition of publishers, academic institutions, technologists, learned societies, university presses, and other stakeholders, SNSI fosters collaborative efforts that enable these challenges to be addressed more effectively and efficiently.
SNSI offers several guiding principles for how libraries can support and strengthen information security practices in higher education. It also provides practical recommendations for academic librarians seeking to build robust cybersecurity defenses within their institutions, as illustrated in Figure 1. SNSI tips for academic librarians on building strong information security defenses.
These recommendations are broadly applicable to nearly any organization. Investing time, attention, and technological resources in preventive security measures is significantly more effective—and less costly—than responding to a security breach or data intrusion after it occurs. Information security is a shared responsibility that involves all members of an organization in protecting institutional data, as well as the personal information of faculty, staff, and students. It also plays a critical role in preserving the integrity of the institution’s research and academic work. However, for a strong security culture to take root and thrive, this commitment must be visibly championed by leadership at all levels across the organization.
SNSI has also developed a toolkit designed to provide librarians with practical guidance on how they can support their institution’s security team in understanding cyber threats and their broader implications. 5 The toolkit incorporates the unique insights and expertise of Chief Information Officers (CIOs) and Chief Information Security Officers (CISOs) in shaping cybersecurity strategies and their implementation. It also offers information on how to request and apply detailed risk assessments to identify vulnerabilities and foster a collaborative environment for developing and refining cybersecurity policies and procedures.
Conclusion
As the scholarly community becomes increasingly reliant on digital platforms for distributing and accessing research, ensuring security at every level, while maintaining the openness that fosters innovation, has become more essential than ever. The challenges and opportunities discussed in this paper highlight the urgent need for a coordinated approach that balances seamless access with strong, sustainable digital security practices.
Footnotes
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
Declaration of conflicting interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
