Abstract
To help navigate the complex issues that occur as a result of changing technology, regulations, and user expectations, SeamlessAccess is producing a toolkit that gives librarians a framework for auditing their resource access. Structured into four key areas—Usability, Privacy, Reliability, and Security—the toolkit enables libraries to identify the risks and opportunities that inform decision making and advocate for future investment. This paper explores usability and privacy and features feedback from a librarian about how the toolkit helped identify and address access-related issues, assess potential ethical or legal exposure, and identify best practices and recommended next steps for moving forward. It also explores how this toolkit can serve as a communications tool to enable librarians to improve knowledge and awareness within their teams as well as with key stakeholders outside the library.
Why access matters and the challenge maintaining it
“Stuff that gets used is the easiest stuff to use.”
1
The majority of academic library patrons grew up with the internet and being online is very natural to them. Most of their online experiences occur on the consumer web where they expect to be able to easily and quickly login to access the information that they want. A poor access experience can deter users from library use and encourage use of unsecure pirate sites such as Sci-Hub,
2
and a poor experience also likely decreases research output while having negative implications on the usage data library’s use when making purchasing decisions. However, maintaining resource access is difficult. There are numerous complicating factors including: • multiple new and legacy technologies that are utilized for resource access, including IP addresses, Virtual Private Networks (VPNs), proxy servers, referring URLs, the SIP2 protocol, federated authentication, and SeamlessAccess/IdP discovery • the regulatory environment, including data privacy laws, including the General Data Protection Regulation (GDPR)
3
and the California Consumer Privacy Act,
4
are highly-complicated and change frequently • upcoming changes in the way browsers manage privacy.
5
While these challenges may not singularly appear daunting, at scale they are frequently overwhelming. Most libraries maintain hundreds of subscriptions to journals, books, databases, and streaming media where they will spend weeks fetching and analyzing data, and interfacing with librarians, faculty, and administrators. Typically, assessing the usability and privacy of a publisher’s website is quite far down in the list of priorities.
Introducing the Access Audit Toolkit
With Seamless Access sitting at the crossroads of many of these challenges, the Access Audit Toolkit is being proposed as one solution for addressing them. This toolkit is a framework to assess the quality of the access experience and currently focuses on two aspects of user access: usability and privacy. While this information already exists in various places across the internet, this Toolkit brings it together and is aligned around the user access experience. It also provides recommendations on best practices, industry standards, and offers other advice on how to deliver a more effective access experience. The aim is to make it easy for librarians to understand industry best practices and have a clear place to which to direct deficient vendors when they fall short. The toolkit also serves as a communications tool to improve knowledge and awareness of these issues, both within the library as well as with key stakeholder organizations that sit outside the library. Finally, this toolkit can help libraries to make a business case for investing in improving the access experience by highlighting any gaps between the current access experience and best practices while identifying any improvements needed.
Usability
The first consideration is usability, i.e., how usable is the access experience for library users? This is separated into three categories with examples of questions provided that help users audit the usability of a service provider’s interface. The context is typically as a user landing on a service provider’s website as opposed to the library’s own discovery and resource pages.
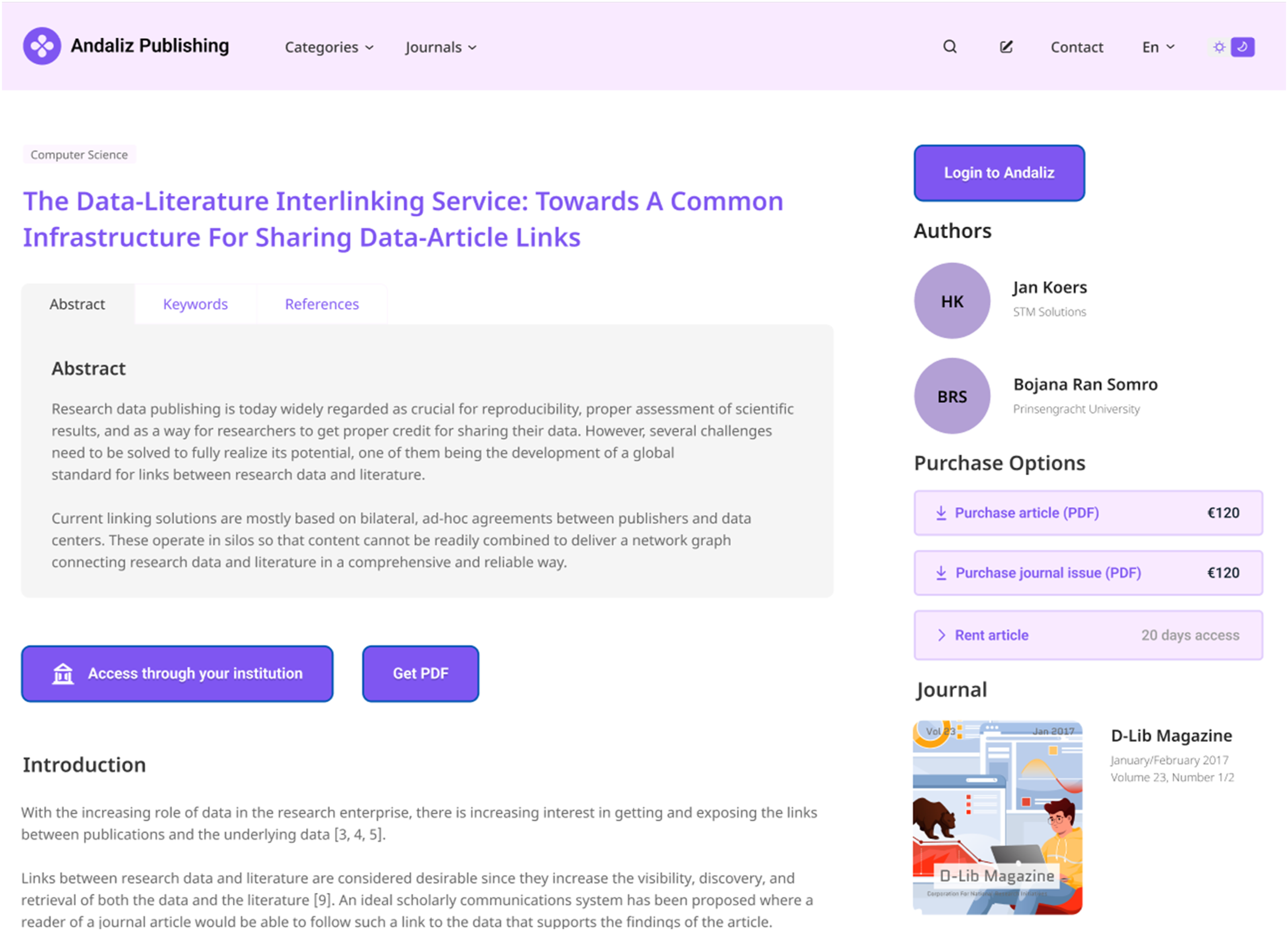
How obvious is it to get access?
The first usability category is whether it is obvious how a user accesses a paywalled resource (Figure 1). A simple way that usability experts test for this is the five second rule: can a new user figure out what to click on to get access within 5 seconds of looking at the web page? Service providers should provide one clear option by which to access the content and avoid presenting users with several equally important options. The interface should focus on addressing the majority of use cases, and avoid shifting the burden to the user to figure out where to click. Above all, access is a function that should be usable as opposed to a marketing opportunity. Three questions have been identified in this category: 1. Is the primary access option clearly distinguished from other options, e.g., different, and more prominent styling? 2. Do options clearly communicate intent? 3. Are there a maximum of three alternative options and are additional options progressively disclosed? Clarity of access entry point.
Can I easily select my institutional affiliation?
The second usability category relates to selecting organizational affiliation (Figure 2). While this is not an issue for IP-authenticated users, many other types of organizational credentials require library users to identify their organizational affiliation; for example, federated authentication, public library cards, or other forms of Security Assertion Markup Language (SAML)-based login. Historically, this has created significant friction for users. Every website offered a different approach to selecting your institution, used different visual layouts, and described the option using a wide variety of language, including technology descriptions such as Shibboleth that mean little to users. Users need to be aware of the authentication level required (individual vs organizational) and ideally, what additional resources are available once they are authorized. Four questions have been identified in this category: 1. Does the list show all institutions? 2. Does the list indicate if an institution may not provide access? 3. Can the complete institutional list be quickly filtered? 4. Is remembering a selected institution allowed?
Is access accessible for all users?
The toolkit’s third usability requirement is accessibility. According to statistics from the U.S. Centers for Disease Control, more than 20% of library users will have at least one disability that can impair their ability to navigate web pages. Many government regulations such as Section 508 of the U.S. Rehabilitation Act (which requires federal agencies to provide individuals with disabilities equal access to electronic information and data comparable to those who do not have disabilities) require websites to be compliant with accessibility standards. Yet many websites fail to comply. Many claim to comply, but few are truly accessible. An annual study of the top one million sites on the internet by a web accessibility non-profit based at the Institute for Disability Research, Policy, and Practice at Utah State University found that 96.8% of home pages had detectable WCAG two failures.
6
WCAG (Web Content Accessibility Guidelines) is a series of standards developed by the Web Accessibility Initiative, which in turn is part of the World Wide Web Consortium (or W3C), and WCAG2
7
is the current standard. Institution selection.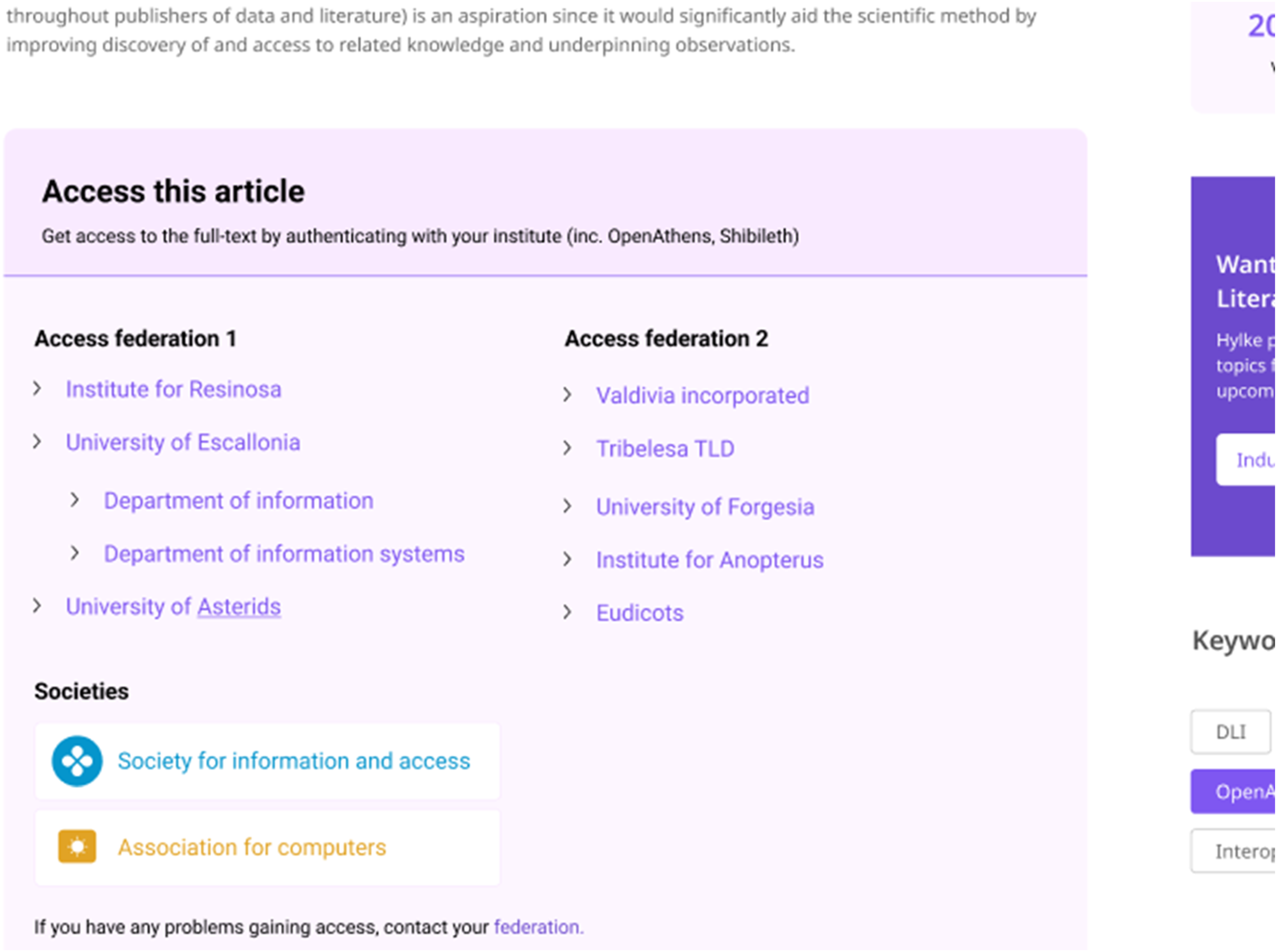
Accessibility is also not just about technical compliance; it is about having considerate interactions, of which five have been identified: 1. Can users navigate the access interface using their keyboard? 2. Is appropriate contrast evident? 3. Can content be easily magnified? 4. Is content, including institutional selection, screen-reader friendly? This enables users with assistive technology to find and select their institution, where all visual cues are also announced verbally and additional guidance is provided. 5. Does the site support non-English languages?
Usability resources
SeamlessAccess has created dedicated resources to provide librarians with more information about usability issues and are divided into three major categories:
Each of these three web pages provides more information about the usability questions, including assistance in understanding the issues, and examples of good and bad practices. There are also links to more technical information on how to address bad practices that can be shared with vendors and other service providers that are not meeting best practices.
Privacy
The second area that is useful for evaluating access to resources is privacy, as considered in Article VII of the ALA Bill of Rights: All people, regardless of origin, age, background, or views, possess a right to privacy and confidentiality in their library use. It is the responsibility of the library to understand how patron data is collected, used, shared, and stored.
There are three lenses through which the examination of privacy issues as they relate to access is considered: 1. What patron data is shared automatically without patron knowledge? a. Is patron data transferred to vendors without patron approval? b. What specific pieces of data are shared, and how much of it is personally identifiable information (PII)? c. How is any shared data stored? d. Is any data shared with third parties? e. Are patron credentials stored securely if used? 2. What data is shared with vendors with patron permission? a. How do patrons authenticate with vendors? b. Are patrons required to share personal information in order to access services? c. Do vendors provide reading lists or savings of reading habits? d. How is permission gained to store patron information? e. Can patrons delete their data if they so desire? 3. What data is collected internally by the library or library IT about patrons? a. What are all of the systems (integrated library system, proxy server, single sign-on, learning management system, etc.,) in use that could collect patron data? b. Is anonymous or pseudonymous access supported in any way? c. Is patron consent required before data is collected? d. Are patron credentials stored securely if collected? e. How is any data that is collected used? In aggregate, and if so how?
Privacy resources
There are numerous resources available that are specific to online user privacy. Of note are the Privacy Field Guides for Libraries, 11 which are structured to give library workers the tools needed to create and be advocates for a safer, more secure library, and the Vendor Privacy Audit found on the Library Freedom Project. 12
Using the toolkit
When assessing the usability and privacy-preserving practices of a vendor’s platform, it is suggested to emulate off-campus access and for the user to begin their research from the open web, which is the use case for most researchers. In this way, authentication is not assumed to have already occurred, but is instead established at the point of need. And finally, consider focusing on one vendor’s platform at a time, then focus on one key aspect that is being audited using the toolkit, then evaluate usability, then evaluate privacy, etc.
Usability
The ease of access to the desired information is generally deemed most important when assessing a publisher’s website for usability, but many times this is complicated by the authentication process and by establishing one’s institutional affiliation. SeamlessAccess greatly simplifies authentication by providing a consistent and easily recognized link to institutional access. Without SeamlessAccess, it is sometimes quite difficult to locate the appropriate link to obtain access, and many sites make the pay option more prominent than the institutional access option which further confuses users.
The same issues with authentication are found when establishing institutional affiliation. When a vendor has enabled SeamlessAccess, the Identity Provider (IdP) discovery flow is very consistent and user-friendly; when the user begins entering their institution’s name, the form auto-populates their selection. Without SeamlessAccess, the user runs into greatly differing interfaces, functionality, and widely-varying user experiences when attempting to establish institutional affiliation. For example, many vendors include such jargon as “sign in with your OpenAthens account,” as if the majority of users have any knowledge or understanding of this.
Privacy
Privacy considerations are more difficult to assess because the information is not transparent to the user; the user community is largely at the mercy of the vendors and publishers to protect patron privacy and oversee personally-identifiable information in the manner they describe. There are typically privacy policies and ample documentation shared on vendor’s sites regarding their use and storage of these data, but it is very concerning that many publishers use third-party data and text analytics tools whose policies are quite different from those of the publisher.
When considering privacy as it relates to the authentication process, typically most vendors do not require any personally-identifiable information (PII) to be stored to access their sites. But if the user does not set up a personal account, which by default shares PII, then they are not able to personalize their experience which means they cannot store articles, citations, abstracts, search queries, etc. Also, vendors are increasingly offering users the ability to opt-in or opt-out of sharing varying levels of information to access their site. There is concern that users are starting to suffer from “consent fatigue,” where they are confronted with numerous pop-up windows that require them to approve or decline something to get to their destinations. With changes in browsers that are coming soon, this is liable to significantly increase.
Summary
Overall, it was found that the tasks in the Toolkit are not overly burdensome or time-intensive. Rather than treating this like a time-limited project and assigning personnel and resources to the Toolkit tasks, these usually can be completed after tending to more urgent priorities on a given day. As these concepts are worked through, certain patterns typically emerge and most of the questions that surface when assessing a publisher’s website are ones that librarians intuitively ask themselves when considering a subscription to a new resource. So, this can be viewed as a much-needed retrospective look at resources that have been around for some time.
By having this information in a consistent format, it offers a way to uniformly document the many questions considered when looking at a new resource in a consistent, formulaic way, and allows for an easier comparison of publisher’s sites. Some additional benefits might include: • Information collected in this audit can be leveraged to make suggestions and negotiate with vendors. • Librarians can utilize this information to assist in publishing an advocacy report and/or privacy statement by the library. • Information gathered can serve as a valuable teaching and training aid in helping users understand the value of their online identity. This is especially a need of our Gen Z population, who are surprisingly unaware of the issues surrounding online user privacy and security.
13
• Information can assist with operationalizing usability and privacy practices in libraries.
As Phase II of this project begins, SeamlessAccess is expanding the scope of the Access Audit Toolkit to cover two additional key areas that impact user access to resources: ○ Security: as users become ever more conscious of the risks of making data available over the internet, the implications of security for resource access and how they vary by the authentication method used should be considered. Issues include: ▪ How easily can access be hacked or faked? ▪ How easily can fraudulent access be shut down? ▪ is the access technology using best practices? ○ Reliability: it seems like old access technologies never die in academia, and this burdens many libraries with legacy access technologies that are less reliable than their modern counterparts. For example: ▪ Is access brittle and/or dependent on other system components such as vendor web applications, browser settings, library infrastructure (e.g., IP addresses, proxy software)?
Potential mechanisms for sharing this information across the library community that would enable publishers and librarians to view findings and contribute to the audit process will also be considered in Phase II.
Statements and declarations
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
