Abstract
Workflow Management Systems are rapidly evolving and increasingly used in a variety of industries, allowing organizations to automate and enhance their business processes. Hence, they are open to collaboration throw inter-organizational workflows to achieve common objectives. Thus, organizations could thereby adapt to highly dynamic environments and abrupt sudden changes like during epidemics. One of the particular interests for security researchers is to ensure workflow resiliency, which means ensuring the completion of the workflow execution given a defined set of security constraints without violating the security policy. However, the rigid application of security constraints restricts some task-organization assignments, which leads to the workflow satisfiability problem. Moreover, a wise selection of collaborating organizations is very important for secure resilient inter-organizational workflow execution. Therefore, we aim in this paper to propose a resilient inter-organizational workflow assignment plan selection approach to select a valid task-organization plan that allows a resilient inter-organizational workflow complete execution. Our proposed approach, uses the task priority concept, Bayesian inference, and a hybrid multi-criteria decision-making approach based on the methods Analytical Hierarchical Process and Grey Technique for Order of Preference by Similarity to Ideal Solution. As a result, the proposed approach selects the best assignment plan for a resilient execution of the Inter-Organizational Workflow, in addition to delegates for each task-organization assignment if available.
Keywords
Introduction
With today’s technological advancements, organizations are able to utilize their information systems to integrate and extend their business processes across borders, enabling them to reach new markets and provide their goods and services to new clients. Moreover, the emergence of Enterprise Information Systems (EISs) — solutions that integrate various business processes and functions within an organization into a unified system 1 —, and Business Process Management (BPM) which represents a systematic approach to managing and optimizing an organization’s processes to achieve business goals. It encompasses the entire lifecycle of a process, from design and modeling to execution, monitoring, and continuous improvement. 2 Inter-organizational collaboration is made possible allowing enterprises to share their expertise and resources in order to achieve common goals. As a result, organizations and businesses across a range of industries are increasingly willing to work together and open to collaboration. Thus, organizations are looking for new reliable business partners globally. In order to achieve this collaboration, organizations have to connect their information systems and incorporate their business processes into an inter-organizational workflow (IOW). Further, the inter-organizational workflow has to meet collaboration specifications, management flexibility, and security requirements to ensure inter-organizational workflow resiliency. Accordingly, organizations use BPM tools for explicit representation and description of the coordination in their business processes. 2
Workflow Management Systems (WfMS) is a solution designed to facilitate the automation, coordination, and management of various business processes or workflows within an organization. It enables the design, execution, monitoring, and optimization of workflows to enhance efficiency, collaboration, and control of work processes.2,3 Further, WfMS are rapidly evolving and increasingly used in a variety of industries to automate and control business processes, which allows organizations to increase their workflows resiliency.3,4 Therefore, Organizations are able to extend their business process from an internal workflow level to a larger external inter-organizational workflow level. 1 Thus, they could thereby adapt to highly dynamic environments and abrupt changes, such as those that occur during epidemic crises. 5 Additionally, inter-organizational collaboration enables organizations to meet new market challenges, perform workflow re-engineering, complete workflow execution, lower production costs, and improve service quality.
However, the security risk remains the biggest challenge in collaborative environments with a dynamic management strategy and complex security policy for data/resource protection. Moreover, data breaches and cybersecurity threats are increasing every year with a high number of attacks recorded in 2020 during the COVID-19 pandemic. 6 Thus, a multitude of attacks against industries with a focus by cybercriminals on the healthcare industry given the huge amount of confidential patient data and human life factor in play.6,7 Therefore, the enforcement of the security policy and security constraints in IOW to ensure confidentiality, privacy, and data availability –especially in healthcare– is necessary. However, enforcing these constraints can result in a stalemate situation in which no user is authorized to execute the current workflow task, thus losing workflow resiliency. 8 Therefore, the tradeoff between ensuring IOW security and the termination of the IOW execution is a very challenging research problem.5,9
Regardless, of the proposed approaches in the literature for the workflow satisfiability problem (WSP) or the workflow resiliency problem, the majority of the research work provides solutions for a complete workflow execution with authorization policy and security constraints in intra-organizational workflows. 10 This gap is particularly pronounced in scenarios such as pandemics, where the need for agile and secure collaboration across different organizations is crucial. This observation forms the core problem statement of our research, emphasizing the need for approaches specifically tailored to inter-organizational workflows under dynamic conditions.11,12
Therefore, our proposed approach introduces an innovative algorithm to select the optimal task-organization assignment plan from a network of collaborating organizations in a shared Inter-Organizational Workflow (IOW). This approach is unique in its integration of the task priority concept, multi-criteria decision method (MCDM), and Bayesian inference, aiming to minimize the risk associated with the Workflow Satisfiability Problem while adhering to IOW security constraints and access control policies. Additionally, the proposed approach proposes an optimal selection of delegates for task-organization assignments as a mitigation to maintain workflow continuity. Furthermore, our research enhances decision-making in these environments by employing a Hybrid Multi-Criteria Decision-Making model that combines the Analytical Hierarchical Process (AHP) with the Grey TOPSIS Technique. This synthesis, along with the incorporation of task priorities and security criteria informed by Bayesian Inference, aligns closely with organizational objectives and security goals. Collectively, these elements constitute a comprehensive framework prioritizing security parameters in decision-making, thereby contributing a robust solution for resilient inter-organizational workflows execution.
The remainder of this paper is structured as follows: We first present the security and resiliency requirements of inter-organizational workflows. This is followed by a post-pandemic analysis of security issues for inter-organizational collaboration. Next, we review related works in the literature. Our approach is then presented, illustrated through a healthcare use case. Finally, the paper concludes with a brief summary and outlines future research directions.
Inter-organizational workflows security and resiliency requirements
Workflow management systems are very popular and largely used by organizations to achieve business objectives and improve their productivity. 11 Moreover, workflows play a central role in the strategies adopted to address global challenges allowing organizations to enhance the efficiency of their business processes. Furthermore, in the majority of data-driven research disciplines, scientific workflows are utilized to perform complex analyses on a multitude of distributed resources.12,13 Additionally, they allow collaboration between several partners to execute tasks in complex and dynamic environments using inter-organizational workflows. 10 However, to ensure organizations information systems security and data confidentiality, it is necessary to use security constraints and access control models to enforce the security policy. 14 However, the enforcement of the security policy affects the IOW resiliency and management flexibility.
Access control policies and security requirements
Many research papers in the literature proposed different access control models to describe security policies in the context of workflow systems.15–17 Besides traditional well-known access control models, there are many others developed recently to match advanced security requirements. 18 The majority of the proposed access control models are adaptations of the Role Based Access Control model (RBAC), 19 which allows users, tasks, role associations, and permissions to be modeled.
Access control is “…a process to determine who does what to what based on a policy”. 20 Access control helps to avoid data breaches and information leakage, more it also prevents data alteration by potentially malicious parties. 21 Thus, the access control model allows the enforcement of access rights, which are defined according to a specific authorization policy. 21 The most important security measure to consider in an organization’s workflow authorization system is Access Control.14,17 It ensures data security, protects resources and prevents unauthorized access by defined subjects to confidential information. 21
Moreover, access control models enable organizations to enforce other security concepts required for workflow systems security. They facilitate the definition of security policies and the formulation of security principles such as the Separation of Duties (SoD), which prevents users or organizations from being assigned conflicting duties (tasks with conflict of interest). 22 Also, the Binding of Duties (BoD) constraint, demands that the same user or organization must execute a specific set of tasks. 14 Furthermore, access control requirements like policies cohabitation, interoperability, and privacy are necessary for IOWs where the participating organizations (i.e., partners) are not necessarily known prior to the IOW execution. In addition, the dynamic aspect of the IOWs allows partners to join or leave the collaboration. 23 Thus, workflow administrators have to deal with the complex management in a business environment and the interactions between different organizations. 23 Therefore, selecting the most appropriate partners who meet the workflow specifications, security requirements, and access control policies is crucial to a successful and secure inter-organizational collaboration.5,23
Collaborators play a major role in the completion of the workflow execution. However, they represent a risk to workflow security and resiliency. For example, during the pandemic, remote working from home leveraged many security concerns for the organizations’ data. 24 Thus, the IOW system’s security highly depends on its partner’s security. Therefore, in order to prevent organizations from executing conflictual tasks or holding conflictual roles. Workflow administrators implement rigid security policies and enforce security constraints like entailment constraints (i.e., SoD, BoD), 4 to ensure secure workflow tasks execution in distributed organizations.25,26 Although, strict security enforcement may cause the workflow satisfiability problem and prevents workflow execution termination which is not tolerated in workflows that had a major impact on organizations in industries providing critical services such as healthcare, banking, etc. 5
Workflow satisfiability problem
In many circumstances, the execution of IOW depends on a number of parameters and environmental factors that are difficult to fulfill. Firstly, the workflow execution must meet workflow criteria and business objectives to ensure a timely termination of the workflow instance execution. 27 However, for security considerations, it is necessary to apply access control restrictions to prevent unauthorized access to workflow resources and ensure a safe and secure workflow execution, especially in dynamic environments during a crisis. 22 Therefore, because of the restrictive authorization policy, and security constraints some participating organizations may be designated unavailable for some tasks in the IOW.
Moreover, early IOW task assignments may cause collaborators to be unavailable for other task assignments in the IOW due to the conflict of interest. This workflow situation is known in the literature as the workflow satisfiability problem, an interesting problem in information security and access control systems that have been shown to be NP-hard.4,28 The basic form of a WSP instance is defined by a partially ordered set of tasks in a workflow instance that must be completed by users/organizations under particular authorizations and security constraints. 29 Thus, the WSP is a problem of finding an assignment of users to tasks so that all authorization constraints are satisfied.4,5,28 In other words, resolving WSP is to ask whether there is a valid plan of assignments where all authorizations and all constraints are satisfied. 27 As described in 30 a valid plan of assignments is a plan that is both authorized and eligible.
Furthermore, the authors in 31 distinguish between two forms of WSP. The classical form is in which we have to find authorized and eligible assignments of tasks to users (i.e., a plan) that satisfies all the constraints, but the availability of users/organizations is controlled (assuming they will be always available). The second form is where the availability of users/organizations is not controlled (at any moment they may become absent), thus we have to deal with uncertainty to ensure complete execution of the workflow with regard to the security policies.
In dynamic environments such as IOWs, where organizations’ availability as collaborators changes frequently, the WSP is known also as the workflow resiliency problem. 31 To understand this concept, a resilience system “is a system with an objective to survive and maintain function even during the course of disruptions, provided with a capability to predict and assess the damage of possible disruptions, and enhanced by the strong awareness of its ever-changing environment and knowledge of the past events, thereby utilizing resilient strategies for defense against the disruptions”.32–34 The workflow resiliency problem is an extended version of the WSP adding the assumption that organizations availability changes during the run-time of the workflow. Thus, workflows that are satisfiable at administration-time may become unsatisfiable during run-time.5,9,35 Therefore, a resilient workflow is considered satisfiable but vice versa does not hold. 31
Based on the user availability, the authors in, 4 defined three levels of resiliency. The first form is static resiliency where workflow users or organizations for IOW may be absent prior to the execution of the workflow instance. The second form is decremental resiliency where users/organizations may be absent before or during the workflow instance execution and they do not become available again. The third form is dynamic resiliency where users/organizations’ availability changes, thus they may be absent and become available again prior to or during the workflow execution. Moreover, checking static workflow resiliency for a given access control state is NP-hard, while decremental and dynamic resiliency are PSPACE-complete. 4
To optimize partner selection for collaboration as well as to ensure secure inter-organizational collaborations, IOW systems must be adaptable with efficient access control management.9,23 Furthermore, because collaborative environments are very dynamic, IOW systems must be designed with mechanisms to address the workflow resiliency problem. As a result, IOW systems can deal with unexpected shifts or even pandemics like COVID-19. Furthermore, they help organizations keep their operations running and ensure service continuity.
Post-pandemic analysis of the security issues for inter-organizational collaboration
Many healthcare providers (hospitals, clinics, insurance companies, etc.) struggle to have an accurate and timely transmission of medical records since people were often sent to the hospital with a packet of medical paper records which can easily be lost or misplaced in the emergency room. 36 Moreover, during the COVID-19 pandemic with all the restrictions to limit the possibility of viral transmission via fomites, medical records exchange was logistically problematic and time-consuming which complicated the situation even more. 36
A shift in organizations work model
The COVID-19 pandemic changed all aspects of life and business work ethics all over the world and caused a global quarantine with people in lockdown and millions of deaths. 37 As a consequence, a huge number of businesses did not survive the social and economic crisis. 24 Hence, the impact on individuals, organizations, and governments was expected to continue for a long time. 38
The crisis forced organizations to innovate and look for alternative strategic solutions as new business models adapted to crisis management and future big challenges, not only alternative solutions to struggle for survival waiting for the hard circumstances to change or the end of the pandemic. 39 Therefore, many organizations have managed the situation during the pandemic and switched their work model to make use of digital technologies, cloud computing platforms, and inter-organizational workflow systems for collaborations. A transformation that was important during the COVID-19 pandemic and impacted positively a wide range of industry stakeholders.1,40 Further, to cope with sudden changes in business work models, there was an increasing need for inter-organizational collaborations. 41 Organizations with implemented information systems were able to rapidly adapt to the new work model situation and allow their employees to work remotely and collaborate with other organizations to help in vaccine development, limit the spread of the virus, and elevate the health concerns of the public. 24
Furthermore, the use of collaboration management systems such as the IOW gives organizations a great solution for safe data sharing with flexible management of shared tasks, especially for the healthcare industry. 36 Since IOW helps to manage communication and exchanges between different collaborators by connecting their Electronic Health (e-Health) Systems (EHS). Thus IOW provides the flexibility and agility to respond to changing environments –like remote work during the pandemic-with an efficient and secure way for patient data exchange between different healthcare partners (collaborators), including hospitals, clinics, laboratories, nurses, doctors, lab. technicians, receptionists, emergency services and insurance companies.8,23,42 In healthcare the focus on collaboration is to improve relationships and trust between collaborating entities, further, it aims to ensure a continuity of care quality for the patient, especially during challenging circumstances like the COVID-19 pandemic. 36
As a result, collaborating organizations in various industries were able to continue operating and providing essential services (telehealth, online education, News updates, social connectivity, entertainment, etc.), which greatly aided decision-makers during pandemics and facilitated crisis management.24,40,41
Organizations security and privacy issues during the pandemic
The critical need for virtual work environments during the pandemic has pushed many organizations to respond quickly. Thus, organizations tried the digitalization of essential services and adopted remote working to ensure business continuity and service availability. Consequently, organizations implemented insufficient security measures for remote work, which cybercriminals can easily exploit outside the security protections provided by the organization’s internal infrastructure and information systems. 24
Furthermore, during the pandemic, cyber-threats have grown at a phenomenal rate, which challenged organizations’ new work model and security strategy to provide safe and reliable access to confidential data and resources, especially since personal data continues to be a lucrative target to hackers. 40 Despite the suffering people are living because of the pandemic; cybercriminals were taking advantage of the situation. Thus, threats escalated dramatically with an alarming high volume of COVID-19-themed scams, malware, and phishing emails exploiting the increasing reliance on information systems and electronic communication networks. 24
Every year IBM Security publishes a research report conducted by the Ponemon Institute on the cost of a data breach. In 2020 the year of the pandemic, some of the key findings of the research report on the impact of COVID-19 is that in response to the pandemic, 54% of organizations required remote work. Also, 76% of those organizations said that remote work increases the time to detect and contain a data breach, and 70% said it increases the cost of a possible data breach. 6 Furthermore, the annual report presented three primary categories of root causes of a data breach in 2020. Thus, 52% of incidents are from malicious attacks, 25% are caused by system glitches, and 23% are caused by human error.
As shown in Figure 1, data breaches root causes vary from one industry to the other. The highest percentage of malicious attacks affect technology, transportation, retail, and financial organizations. Whereas the highest percentage of data breaches caused by human error affect entertainment, education, pharmaceuticals, and healthcare.
6
Moreover, malicious attacks were the most expensive breach root cause, costing an average of $4.27 million, nearly $1 million more than system glitches or human error.
6
IBM security report for data breach root causes by industry.
6

The majority of these sectors are frequently targeted by cybercriminals for the high value of data and information shared in their systems. Since data and Information technology play a strategic role in industries characterized by high information intensity. Thus, the value of Information technology is very high for industries where data and information processing is required to efficiently and effectively manage their activities and business processes. 39 The authors in 39 presented a three-dimensional information intensity matrix that reflects the nature of the product/service associated with a level of information intensity for different industries.
As described in Figure 2, We can clearly see that Healthcare, Banking, and Media industries which figure in the sixth block of the matrix represent the industries with the highest level of information intensity of process and product/service, which make those industries essential in today’s world.
39
Also, it reflects the high amount of data circulating in their information system as they make use of technologies in their daily workflows. Thus, it confirms why those industries are highly targeted by cyberattacks as shown in Figure 1.
6
Industries information intensity matrix.
39

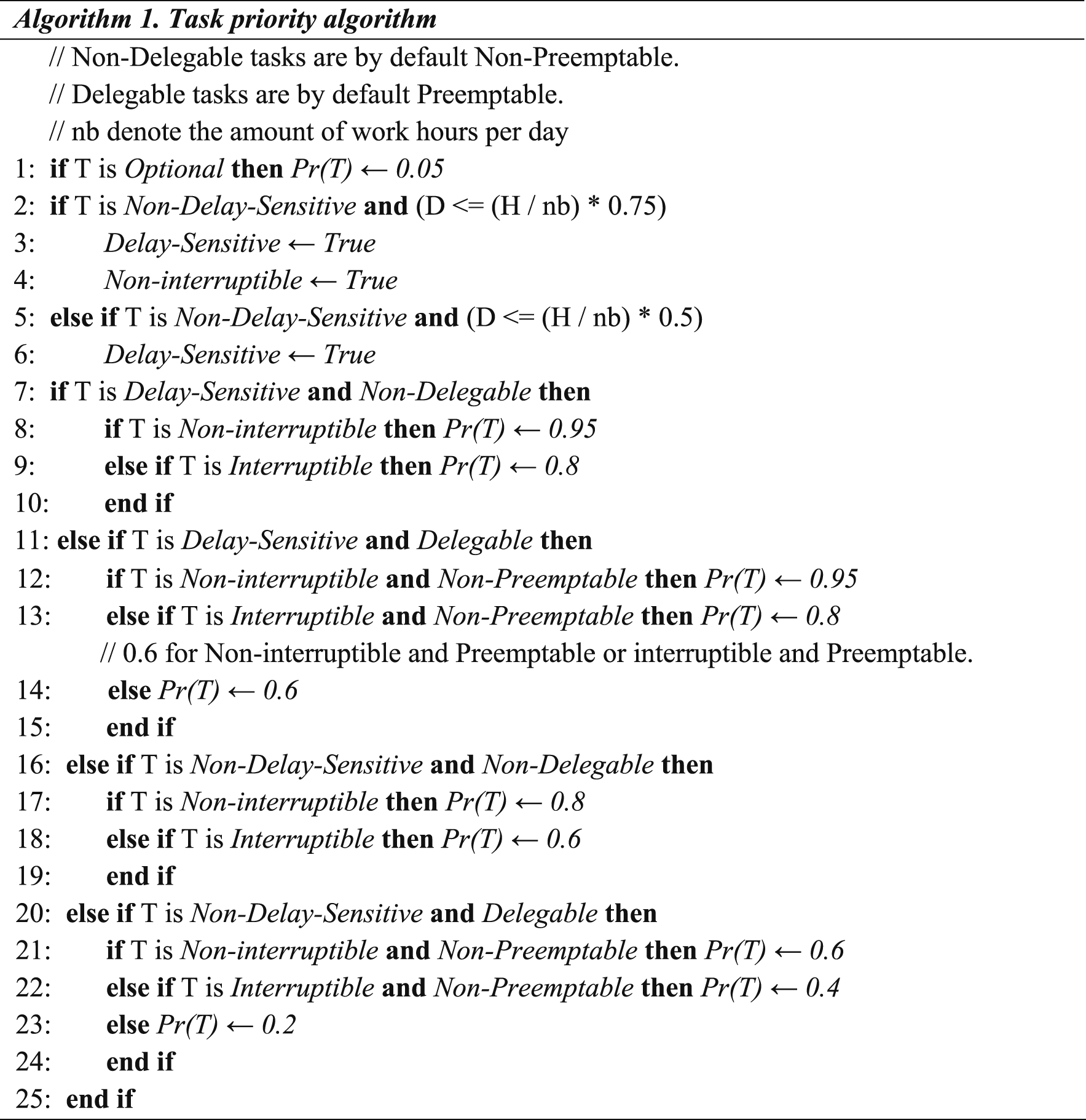
According to the IBM security cost of data breach report published in 2021,
7
the average cost of a data breach across all industries increased from $3.86 million in 2020 to $4.24 million in 2021. Moreover, the cost of Healthcare data breaches increased by 29.5% to an average of $9.3 million per incident, up from $7.13 million in 2020.
7
Thus, the healthcare data breach average percentage is roughly three times greater and twice as expensive as the worldwide industry average. Furthermore, the most common root causes of data breaches in 2021 were 20% for compromised credentials, 17% for Phishing attacks, 15% for cloud misconfiguration, and 4% for compromised business emails.
7
Additionally, the 2022 IBM report records a very high increase from last year of 12.7% in the average global cost of data breaches reaching $4.35 million.
43
Further, the top three industries affected in the 2022 report are healthcare, financial, and pharmaceuticals, each of these are part of critical infrastructure sectors as we presented earlier. Figure 3 shows the average overall cost of data breaches, with the healthcare industry recording a 9.4% increase over the previous year and the financial sector experiencing a 4.4% increase. While the average total cost decreased slightly in the pharmaceutical industry.
43
Top industries in the average total cost of a data breach - measured in US$ millions.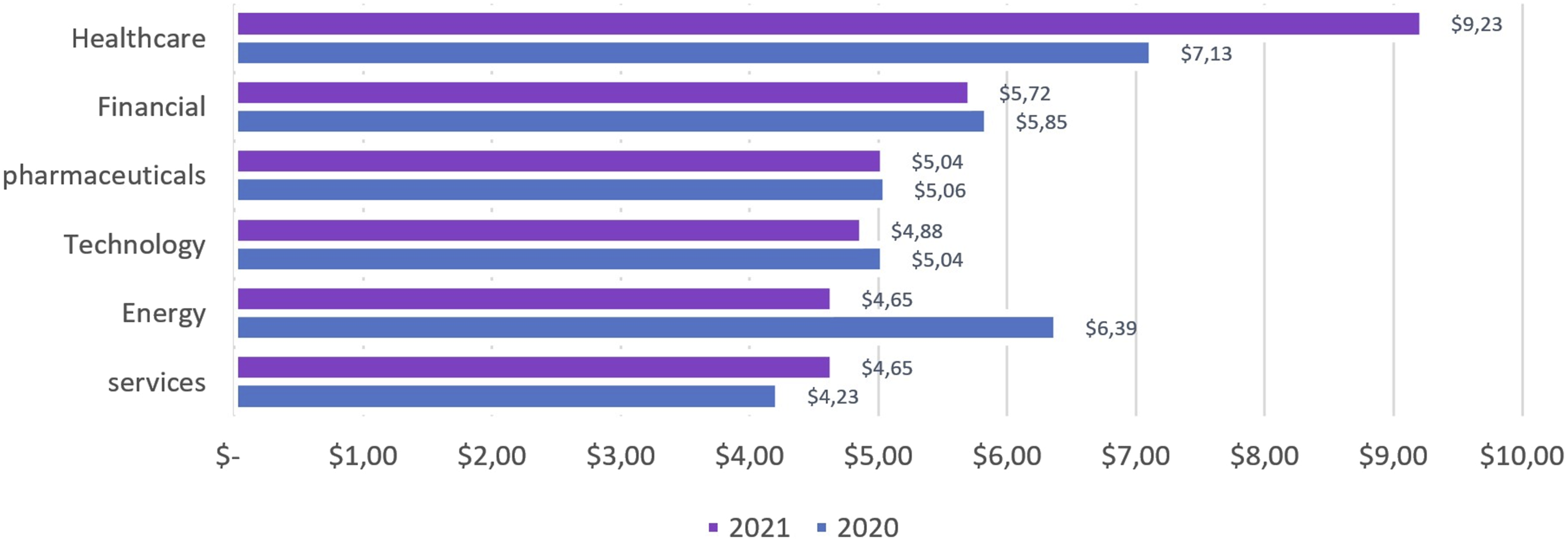
The top four initial attack vectors of data breaches identified in the 2022 report are the same as those identified in IBM’s 2021 report. The first most common attack vector reported is compromised credentials with 19% of breaches, and the second is phishing attacks accounted for 16% of breaches. More, the global average cost was calculated as $4.02 million with an increase to $4.99 million when remote work conditions were regarded as a cause triggering the data breach. 43
The presented statistics and the information matrix gives an insight into the impact of the pandemic on different industries’ business models. 39 For example, in many countries where healthcare systems are traditional, a large group of patients has been heavily affected. As healthcare workers were exhausted caring for COVID-19 patients, thus routine health services for ongoing care and long-term treatment such as specialized cancer consultations have been suspended. 44 On the other hand, healthcare organizations that are equipped with Electronic healthcare systems (EHS) or used Information and Communication Technologies have effectively addressed the challenges during the pandemic. Thanks to the features that ensure patient data availability and the possibility for resource sharing and access anywhere. 41 This helps the collaborating organizations to provide essential care efficiently and improves healthcare quality, treatment procedures, and reduces care cost and time. 45 Hence, healthcare organizations were able to redesign their care model enhancing communication and collaboration, redeploying staff, ensuring patients care continuity, and overcoming financial loss.41,45
Therefore, thinking about restructuring healthcare systems or any other industry with a high information intensity of processes and products/services to maintain functional business operations during crisis situations is very important. Regardless of the advantages, the openness of technology and services digitalization leverages the security and privacy concerns -such as access control, trust, authentication, data sharing and transmission, delegation, data confidentiality, and integrity, - especially in highly dynamic environments with all the sudden changes and environment variability as in crisis situation.1,40 As a result, during the COVID-19 epidemic, data sharing, and business collaborations become increasingly crucial and very challenging for several organizations. Therefore, the adoption of inter-organizational authorization systems and cloud-based platforms could help to enhance security and prevent data leakage, which encourages collaborations but these are not the only concerns. 40
The pandemic showed the necessity today for information systems and inter-organizational collaboration that allows enterprises to work with other partners sharing their expertise and resources to achieve common goals. Moreover, the pandemic proved for organizations the necessity to consider risk management and to have business continuity and incident response plans. Furthermore, enforcing access control authorization policy and security requirements to improve an organization’s security is a recommended practice. However, organizations must guarantee that their workflows are fully executed and met their business objectives according to the workflow specifications. Moreover, organizations have to manage security and workflow specifications to avoid the WSP, thus they avoid the violation of the access control authorizations to terminate the IOW execution.4,5,10 Thus, finding the balance between security, privacy, and workflow specification is vital for a successful secure resilient workflow for collaborating organizations. Therefore, organizations have to rethink their business models in order to capitalize on digitization toward a secure and flexible inter-organizational collaboration system adapted for dynamic environments and challenging circumstances.
Related works
Numerous authors in the literature have studied and experimented with various methods to solve the WSP. Among these approaches, we identified in the literature the Fixed parameter tractable (FPT), model checking, quantitative approaches, delegation mechanism, etc. 46
Wang and Li proposed an interesting work in, 4 in which they use parameterized complexity methods to evaluate the computational complexity of the WSP with multiple input parameters. The authors demonstrated the NP-completeness of the WSP and proved its FPT. Thus, efficient algorithms to solve WSP are conceivable when just inequality and equality relations (SOD/BOD) are considered. They also demonstrated that the usage of user-defined relations renders WSP non-FPT. 4 The authors developed an approach for executing an FPT reduction of the WSP to SAT in order to solve the WSP using the SAT solver. 4
Crampton et al. in, 28 enhanced Wang and Li’s findings by introducing counting constraints (a generalization of the cardinality constraints), and considering entailment constraints to represent other types of requirements. The authors demonstrated that counting constraints had no effect on the WSP’s fixed-parameter tractability. As a result, the WSP remains FPT for every constraint whose fulfillment is dependent on the action of a single user. 28 Therefore, Crampton et al. reduced WSP to a Max Weighted Partition problem, to ensure that WSP instance is FPT, allowing the development of an FPT algorithm to solve the WSP.
In 27 Cohen et al. used a constraint satisfaction problem (CSP) approach and the concept of plan-indistinguishability to create an algorithm that can handle a wide range of workflow constraints. As a result, the authors suggested a general method that incrementally builds executions, eliminating partial executions that can never match the criteria. Moreover, they demonstrated that the method could be improved for a wide range of user-independent constraints as well as unions of different constraint types. Furthermore, the authors showed that the algorithm is FPT for equivalent relation constraints and their union with user-independent constraints.
Karapetyan et al. in, 47 proposed a faster algorithm with only polynomial-space complexity. The presented FPT algorithm solves WSP with user-independent (UI) constraints exploiting two levels of decomposition and supported by heuristics. The Pattern Backtracking (PBT) algorithm handles the decomposition of WSP into two levels. The upper level corresponds to UI constraints where decisions can be encoded with a pattern. The space of the upper-level solutions has a size exponential in k not depending on n. While the lower level corresponds to user assignments where authorizations are user dependent, and thus cannot be handled with patterns. The lower level can be reduced to a bipartite matching problem which admits a polynomial-time algorithm. Thus, PBT has a running time exponential in k only. 47
Gutin et al.
48
explored the kernelization of the WSP for a variety of algorithms and showed that the algorithms in27,28 for solving the WSP for regular and user-independent constraints are most likely optimal. In addition, authors in
30
showed that algorithms to solve WSP in a running time of
Mace et al. introduce the concept of quantitative resiliency 49 and studied the resiliency problem quantitatively focusing on decremental and dynamic resiliency. 4 As a result, the workflow resiliency problem was reduced to that of solving a Markovian Decision Process (MDP). The authors developed metrics to evaluate the resiliency of a workflow, and the likelihood of workflow execution termination for a given security policy and user availability model. In, 50 Mace et al. enhanced the proposed approach to take into consideration workflow with choice and provide resiliency values for each execution path. Therefore, they define a metric -resiliency variance-for workflow failure analysis to help predict an appropriate mitigation strategy. 50
In 51 the authors defined the Bi-Objective WSP (BO-WSP), which helps in analyzing a variety of problems relating to workflow satisfiability. Thus, they have developed fixed-parameter tractable algorithms to solve BO-WSP, which means the possibility to solve many instances of BO-WSP with parameters that take values as it would be expected in practice like a larger number of users compared to the number of steps. 51 Moreover, inspired by the work of Mace et al. 49 the authors developed a new model for quantifying workflow resiliency based on probabilities associated with the unavailability or availability of users to expect the number of steps that will be executed for a given plan.
The author in 9 presented an approach that employs the delegation mechanism to improve the resiliency of workflow systems and uses the task priority concept to find appropriate delegatees. Moreover, the approach helps to decide which task instance to suspend if necessary in order to avoid the WSP at run-time. The delegatees are chosen based on their suitability but may lack competence, which is “the price to pay” for resiliency. 9 The delegation process takes place at the task level, thus it is not clear whether a workflow can still complete its execution while meeting security constraints.
In, 5 the authors presented an approach based on the workflow criticality metric to prevent the WSP. They have enhanced and redesigned the proposed approach and concepts in. 9 Thus, the new proposed approach aims to predict the workflow risk of failure before implementation. 5 Hence, tracking probable workflow execution failures during run-time will help workflow managers to design flexible and resilient workflows. 5 Further, the authors proposed an algorithm that combines workflow criticality, priority concepts, users’ availability, etc. 5 To bypass the WSP and search for a potential delegate that represents a low-security risk of execution failure for the critical task. 5
The authors in, 1 proposed RPMInter-Work, a multi-agent approach for planning task-role assignments in constrained inter-organizational workflow and security authorization limitations associated with task-role assignments. The proposed approach aims to define a valid role plan that ensures that each workflow task is performed by an authorized role and that this authorization does not block the execution of other workflow tasks. 1 The authors formulated their approach as a planning problem similar to a DisCSP which is solved using the DOC-SAT approach while respecting the privacy of the participating organization. 1 However, the approach presents some limits when the planning problem is over-constrained and there is no viable role plan that satisfies all of the required authorization restrictions. 1
Resilient assignment plan selection approach for IOWs
In this section, we describe our proposed approach to find the best plan of task-organization assignments for IOW complete execution that represent a low risk for WSP to occur. The proposed approach uses a task priority concept, 5 and a multi-criteria decision method (MCDM), 23 that combines AHP and Grey TOPSIS methods to rank collaborators for tasks suitability from a security perspective,.52–54 Moreover, we evaluate the risk of assignments for a critical task instance using Bayesian inference to select the best organization with a low risk of WSP for each task.55,56
Background and motivating example
We consider a workflow schema to define an inter-organizational as a tuple W (T, O, A, C). A workflow schema contains T the set of tasks in the workflow, and O the set of organizations in the partner network. Also, we have A (t) the authorization list for each task instance t where A = {A (t), t ∈ T}, and C the set of workflow constraints applied to tasks in W, thus we denote C (t, t’, c) for the constraint c to satisfy when assigning an organization to tasks t and t’.
As a running example, we consider the inter-organizational workflow in Figure 4 which is inspired by the healthcare environment for patient diagnosis and treatment. The considered IOW schema W (T, O, A, C) contains five tasks T = {T1, T2, T3, T4, T5}, and a set of collaborating organizations from the partner network O = {O1, O2, O3, O4, O5, O6} to execute tasks in T. Moreover, the inter-organizational workflow is an abstraction of a healthcare process presented in Figure 5 and which may involve different healthcare organizations (hospitals, clinics, laboratories, insurance companies, etc.). This process takes place as follows: - Starting from task T1 with the registration of a patient in a healthcare facility, either in a Hospital ER or Clinic care. Then proceed to patient examination. - After examination a patient diagnostic report is created, and a simultaneous signal is sent to start T2 for laboratory tests if needed and T4 to check the patient’s medical insurance. - After receiving the patient’s diagnostic and lab. test results, the execution of T3 starts. In T3 a doctor or medical specialist reviews the patient’s medical reports and creates a specialized medical report. - The final part of the process starts the execution of T5 to administer a treatment plan for the patient after receiving and reviewing the specialized medical report and the medical insurance decision. Inter-organizational workflow for patient diagnostic and treatment. Healthcare process for patient diagnostic and treatment.


Workflow tasks authorization lists.

The constraints C on tasks that have SoD constraint and should be assigned to two different organizations with non-conflictual roles are denoted C (t, t’, ≠) and constraints that have BoD constraints and should be assigned to the same organization are denoted C (t, t’, = ).
14
Thus, constraints C on tasks in our running example are as follows: - T1 (Hospital/Clinic) and T4 (Medical Insurance) constraint is C (t1, t4, ≠); - T3 (Medical Doctor/Specialist) and T5 (Treatment plan) constraint is C (t3, t5, = ); - T4 (Medical Insurance) and T5 (Treatment plan) constraint is C (t3, t5, ≠). - For T2 (Laboratory/Radiology Services) there is no constraint applied on it.
Task priority concept
In this section, we present a task priority algorithm, a concept defined in
5
and which evaluates task priority depending on task characteristics and task deadline. We define a workflow task as tuple
The workflow manager specifies the characteristics of each task in the workflow during administration-time. The task characteristics used to quantify the priority of a task are optional/obligatory, delay-sensitive/Non-delay-sensitive, delegable/non-delegable, interruptible/non-interruptible, and preemptable/non-preemptable. An optional task means that the task is by default interruptible, thus the task execution can be paused and resumed later. A delay-insensitive task is a task that has no time execution constraints. While a preemptable task is a task for which the user starting its execution can be replaced. Finally, a delegable task is a task with no confidentiality constraints that prevent its delegation.
Furthermore, with the exception of a task's delay sensitivity, most of the characteristics are unchangeable throughout workflow execution. Because it is a time restriction that indicates the execution time of a task and the remaining time before the deadline. As a result, a non-delay-sensitive task becomes delay-sensitive as it gets closer to its deadline.
Accordingly, the algorithm for task priority verifies task execution remaining time to its deadline and considers tasks with 50% to their deadline as delay-sensitive. While tasks with 75% to their deadline as delay-sensitive and non-preemptible. The following algorithm 1 we propose is an enhanced version of the task priority algorithm in 5 to identify task Pr(T) values.
The algorithm defines Pr(T) values in [0, 1] and it is designed to cover all the possible combinations of the task characteristics in T-Kind. Thus, the algorithm takes a set of tasks and their characteristics and returns task priority value for each task in a workflow schema W. In the first step of the assignment plan selection approach we apply the presented concept to the health care running example presented earlier.
Assignment plan selection approach
As presented earlier in this paper about the workflow satisfiability problem, executing inter-organizational workflows depend on different variables and conditions that may be hard to satisfy. Therefore, in many cases the workflow managers violate security constraints to complete the workflow execution, thus unavailable organizations are allowed to execute critical tasks in the workflow. The violation of security constraints to bypass WSP opens the system to a potential privacy violation and data breach. Since inter-organizational workflow enhances workflow resiliency throw a secure collaboration system which helps to provide high-quality services and products. However, it's necessary to have algorithms to help bypass the WSP by finding assignment plans that balance the trade-off between enforcing security constraints, workflow specifications and ensuring a complete successful workflow execution.
Therefore, the approach we propose uses the concept of task priority Pr(T) presented in
5
with some enhancements as presented earlier. In addition to an MCDM method presented in23,52 which we combine with a Bayesian inference approach. Figure 6 illustrates the flowchart of the proposed approach to select the best plan of collaborating organizations from the partner network to execute the IOW with the lowest risk possible that the WSP occurs. Inter-organizational workflow assignment plan selection approach.
Step 1: Ordering tasks using the priority concept
Figure 7 represents the first step in the approach described in Figure 6. This step of the approach uses the tasks priority concept to create an ordered set of tasks based on task priority values which reflect the risk of failure for each task based on its characteristics, and the security constraint applied to each task in the IOW. Thus, the first step of the approach provides an ordered set of tasks from the task with high priority to the lowest one in the IOW. The first step of the approach for task ranking using task the priority concept.
The task priority values Pr (T) of the Healthcare IOW running example.

To visualize the task’s priority and the impact of the security constraints applied to each task in the healthcare running example in Figure 4. We use a risk matrix that associates task priority to a level of risk (low, medium, important, high and critical) as illustrated in Figure 8. The risk matrix of the tasks in the workflow running example.
In Figure 8, the highest risk of failure is associated with task T5 with a high Pr(T5) = 0.8 and both SoD and BoD constraints. Also, task T3 has a high Pr(T3) = 0.8 and SoD constraint, thus they are ranked with high risk in the matrix. The task T2 represent the lowest risk since its Pr(T2) = 0.05 with no security constraints, while the tasks T4 and T1 represent a medium to important risk for the IOW execution.
Step 2: Bayesian inference on organizations’ availability
The second step presented in Figure 9, describes the Bayesian inference method which uses Bayes’ theorem in equation (1) to compute the organizations availability for each task given the security constraints applied on the task for the inter-organizational workflow execution. Therefore, to explain the second step of the approach we will generalize the concept of bias using our running example assuming that an organization with a bias of 0.5 will be available for the IOW execution half of the time. The second step of the approach for the Bayesian inference of organizations availability.


Accordingly, assuming that collaborating organizations for the IOW execution do not affect each other’s availability. Thus, we consider the organization's availability as a random variable that is independently and identically distributed (iid). Given these assumptions, the Binomial distribution is a good candidate to use in our model. Therefore, in a formal notation if X is a binomial random variable for organizations availability with parameters p and N, denoted 
Moreover, in relation to Bayes’ theorem, equation (4) represent a discrete distribution that returns the probability 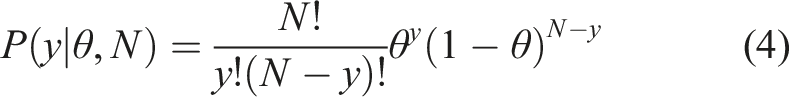
Furthermore, for the prior 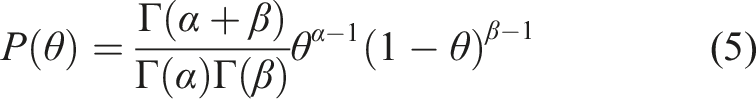
Finally, in our model in step 2, we have 
Thus, we simplify the expression in equation (6) and drop all the terms that do not depend on theta for practical concerns. The results will still be valid and we get: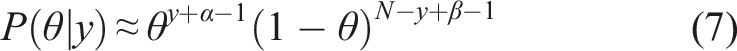
The posterior
We present the results of step 2 for the running example presented earlier. As we have described, to model our likelihood The impact of security constraints on organizations availability.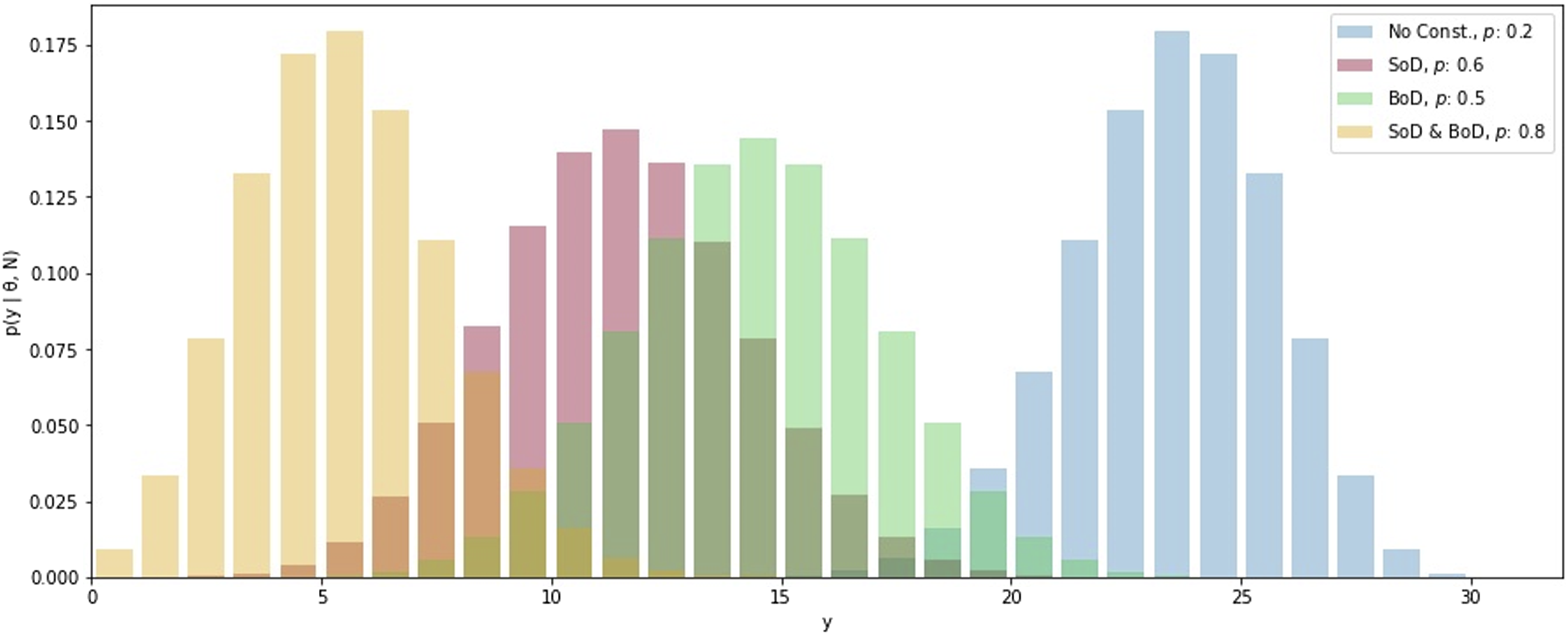
Further, we consider the Beta distribution for the prior The kernel density estimation and the sampled values for theta inference.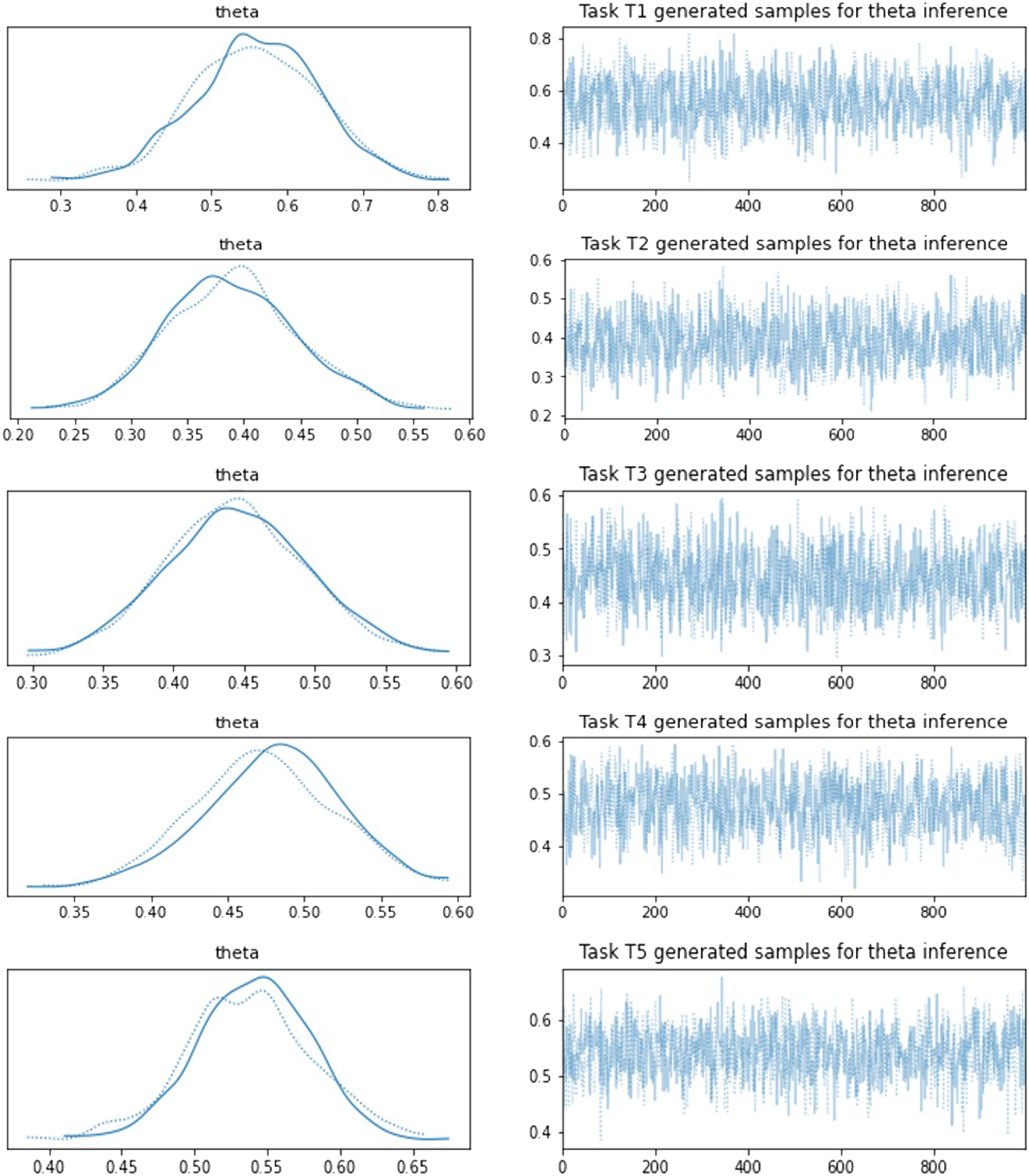
Therefore, to summarize the results of the Bayesian analysis performed in step 2 of the proposed approach, Figure 12 shows the posterior probability distribution for organizations unavailability for tasks T1 and T3 execution in the IOW. Moreover, Table 3 gives a detailed summary of all the tasks in the IOW running example. The posterior probability distribution of organizations unavailability for tasks T1 and T3. A detailed summary of step 2 results for the IOW running example.

Step 3: Ranking organizations using AHP and grey TOPSIS method
The third step of the approach presented in Figure 13 allows ranking authorized organizations for each task in the IOW based on the security constraints needed for secure collaboration between participating partners in the execution of a shared IOW. Thus, this step of the approach uses a hybrid Multi-Criteria Decision Method (MCDM) approach presented by the authors in.
23
The hybrid MCDM approach combines the Analytical Hierarchical Process method (AHP), with the Grey Technique for Order of Preference by Similarity to Ideal Solution (Grey TOPSIS).
52
The third step of the approach using AHP and grey TOPSIS for organization ranking.
The AHP method allows calculation weights for each criterion necessary to ensure secure collaboration between participating organizations in the execution of the shared IOW. Moreover, as described by the authors in, 23 the necessary security criteria for collaboration in the IOW are Cr1 = security level (SL), Cr2 = privacy compliance level (PCL), Cr3 = policy similarity level (PSL), Cr4 = trust and reputation level (RL), etc. Thus, the AHP method uses a pairwise comparison matrix of the security criteria required for partner (collaborators) selection for the IOW. Further, the pairwise comparison matrix is made by domain experts and workflow managers, to reflect the level of importance for each security criterion compared to the others.
Therefore, we consider the following pairwise comparison matrix A for our IOW running example presented in Figure 4 to compute the weights for the security criteria of organizations collaboration. Thus, for the matrix A of order n = 4 we calculate the product raised to the power of 1/n for the values in each row, then we normalize the result to get a vector of weights as follows:
Furthermore, to check the consistency of the judgment we calculate and check the consistency ratio
The second method in the hybrid MCDM in
23
is the Grey TOPSIS method which combines the grey theory and TOPSIS method, used to rank and classify the collaborating organization by required security criteria for collaboration. The Grey TOPSIS method uses grey numbers to deal with the uncertainty and incomplete information embedded in the security-based partner selection.
23
Thus, we denote a grey number as
The normalized grey decision matrix and AHP weights for T1 and T3.

The relative closeness value of the authorized organizations for T1 and T3 execution.

Step 4: IOW assignment plan with low risk of WSP and delegates suggestion
The fourth and final step of our proposed approach consists in combining the results from steps 2 and 3 as shown in Figure 14. Thus, we believe that the resulting IOW execution plan in step 4 of the proposed approach represents the best plan that balances secure collaboration and resilient inter-organizational workflow execution. The use of step 3 provides a ranking of the collaborating organizations in the partner network for each task T in the IOW that satisfies the necessary security criteria for collaboration as defined by domain experts and workflow managers. Further, step 2 of the approach performs a Bayesian inference about the probability of the organization’s availability for each task in the IOW given the security requirement needed to ensure a secure IOW execution. As a result, step 2 provides us with statistical information as shown in Table 3, which we use for a variety of analyses for the IOW. In our approach, we use the mean value of the organization’s availability for a given task in the IOW, with the relative closeness value calculated in step 3 to select the best secure and resilient plan of authorized collaborating organizations for the execution of the shared IOW. The fourth step of the approach to select the best execution plan for the IOW.
The relative closeness value for the authorized organizations for the tasks in the IOW.

The ranking values for selecting the best plan for the IOW execution.

Table 7 describes the calculated ranking value from step 4, which allows the selection of the best plan for the IOW execution. Thus, the organizations selection value for each task in our running example combines the results in Table 6 and the mean values presented in Table 3 calculated for each task in step 2.
Therefore, from the results of step 4 presented in Table 7, the tasks ranking using priority values from step 1 and the security constraints on tasks in our IOW running example. We rank organization increasingly using their corresponding values in Table 7 for each task, thus the first ranked organizations for each task is the best organization to execute that given task. Furthermore, the proposed approach provides the most suitable delegate if exists. Thus, the next ranked organization for each task is the most suitable organization for delegation in case of changing situations or organization unavailability for any intractable raison by our approach.
As a result, the proposed approach provides an assignment plan for the IOW tasks in the following order T5 > T3 > T1 > T4 > T2 reflecting task priority from step 1. Thus, the following task-organization assignment plan П = {O3, O4, O3, O5, O3} for the set of tasks T = {T1, T2, T3, T4, T5}, is the best IOW execution plan for our running example that ensures secure collaboration and resilient IOW execution. Further, for example the proposed approach gives {O1, O2} as a list of the most suitable delegates for task T3 execution in case O3 is unavailable.
Furthermore, in our running example the task T5 has BoD constraints with T3 and SoD constraints with T4. Also, the T3 task priority value is considered critical as shown in the risk matrix in Figure 8, thus our proposed approach considers the task T5 as the first task assignment to satisfy in order to override conflicting assignments. Moreover, given the security constraints on the IOW tasks we clearly see from the result of the approach that T5 has no available delegate in case O3 is selected in the assignment plan П for any other task. Thus, the workflow managers, can also use the proposed approach as a tool to anticipate future possible blocking situations and make possible changes in the IOW tasks authorization list, the workflow authorization policy, or redesign the IOW for better results.
Conclusion and future works
In this research paper, we introduced an innovative approach for selecting a task-organization assignment plan aimed at facilitating resilient and complete inter-organizational workflow (IOW) execution. Our method emphasizes adherence to collaborative specifications, authorization policies, and security constraints, ensuring that the chosen organizations within the partner network are both authorized and well equipped to execute their designated tasks without creating conflicts in the collaborative IOW. This strategy significantly reduces the risk of workflow satisfiability issues.
Our approach, underpinned by the concept of task priority, judiciously assigns tasks based on associated risks and security constraints. We incorporate Bayesian inference to estimate the availability of collaborating organizations for each task, given the security constraints, and fuse this result with a hybrid multi-criteria decision-making framework combining Analytic Hierarchy Process (AHP) and Grey Technique for Order Preference by Similarity to Ideal Solution (TOPSIS) methods. This integration produces a ranked list of organizations for each task, identifying the most suitable collaborators considering the security constraints. Additionally, it allows to select a secondary list of the most suitable delegates for each task-organization assignment.
The proposed framework offers managers a robust approach that allows enhancing collaborative workflow efficiency, particularly in environments where security and authorization are paramount. It provides a systematic way to evaluate and select partner organizations, thereby fostering more secure and efficient collaborative processes.
Despite its strengths, our approach is primarily based on Bayesian inference, which relies on approximating true probability distributions from available data. The accuracy of these approximations can vary, suggesting a need for more comprehensive data collection or the establishment of more informative priors for precise decision-making. Additionally, while the approach is suitable for sequential data analysis, it may face limitations in over-constrained IOWs lacking valid assignment plans that meet all security and policy requirements.
As a future direction, we aim to refine our model to overcome these limitations. Specifically, we plan to explore the integration of the Markov Decision Process (MDP) to further enhance the resilience and adaptability of IOWs under varying constraints. This exploration could potentially lead to more sophisticated and flexible models that cater to a broader range of IOW scenarios, thereby broadening the applicability and effectiveness of our proposed approach in enhancing the complex inter-organizational workflows resilience.
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.

