Abstract
The transfer of dual-use technologies, which can be used for both civilian and military applications, has become a critical issue for national and international security. In response, the Strategic Trade Act 2010 (STA 2010) was enacted in Malaysia to regulate the export, transit, and transshipment of strategic items, including dual-use goods and technologies. However, despite its importance, researchers in Malaysia’s Higher Learning Institutions exhibit lack of awareness and understanding of the Act, potentially placing national security at risk through unintended breaches of export control regulations. This study aims to evaluate the knowledge and awareness of the STA 2010 among researchers in Malaysia, focusing specifically on their understanding of tangible and intangible technology transfers (ITT) and the associated risks of dual-use items. Questionnaires were distributed to a purposive sample of researchers, and the data were analyzed using the Rasch Measurement Model to assess levels of knowledge. The results indicate a significant knowledge gap among the research community, with most respondents demonstrating insufficient awareness of STA 2010 provisions, despite the Act being in place for over a decade. These findings highlight the urgent need for targeted educational programs and outreach initiatives to improve compliance and mitigate potential risks. Policymakers and key stakeholders must strengthen efforts to raise awareness and ensure researchers are adequately informed about the legal frameworks governing dual-use technology transfers, thus safeguarding both national and international security.
Keywords
Introduction
The current work highlights knowledge on dual-use technology (DUT), dual-use research (DUR), and dual-use research of concern (DURC) among researchers in Malaysian Higher Education Institutions, focusing on their meaning, nature, utility, benefits, capability, and potential for legitimate or illegitimate use.
Evaluating the knowledge and awareness of the Strategic Trade Act 2010 (STA 2010) among researchers in Malaysia has implications that extend beyond its borders due to the interconnected nature of global research, trade, and technology transfer. Malaysian researchers often collaborate internationally, and inadequate awareness of STA 2010 could lead to unintentional violations of export control laws, with potentially serious repercussions for global security. Malaysia’s compliance with international obligations, such as United Nations Security Council Resolution 1540, is critical in preventing the proliferation of dual-use technologies that could be misused for harmful purposes. The findings from this study offer insights that can inform global efforts to enhance regulatory compliance and secure technology transfer, making this study valuable to policymakers and institutions in other regions with similar challenges.
This study aligns with the journal’s objectives by addressing a critical intersection of governance, policy development, and security in the context of dual-use technologies. The journal often focuses on research that combines localized issues with broader international implications, and this paper achieves that by using Malaysia as a case study to explore challenges in dual-use research compliance. The findings not only identify gaps in STA 2010 awareness within Malaysia but also provide actionable recommendations applicable to other nations striving to balance innovation and national security. By contributing evidence-based insights and proposing targeted interventions, the study offers practical value to global debates on dual-use technology governance, aligning with the journal’s focus on bridging research with impactful policy outcomes.
The central research focus of this paper is to investigate why knowledge gaps about the STA 2010 persist among Malaysian researchers more than a decade after its implementation. Despite being a key legislative tool for regulating dual-use research and technology transfer, the Act remains insufficiently understood by those it directly impacts. This raises important questions about the effectiveness of existing awareness initiatives and regulatory outreach. The study seeks to identify demographic and institutional factors contributing to these knowledge deficiencies and explore how they can be addressed. The puzzle lies in understanding why, despite Malaysia’s commitments to international security frameworks, researchers continue to lack the necessary awareness to comply fully with STA 2010.
This study is particularly timely due to the increasing prevalence of international collaborations involving Malaysian researchers, which heighten the risks of dual-use technology transfer. Globally, case studies have demonstrated that universities and research institutions can be exploited by proliferators seeking access to sensitive technologies and knowledge. While Malaysia’s laboratories are not explicitly identified, the findings emphasize the importance of preventive measures to protect researchers and institutions from unknowingly contributing to such activities. Addressing these knowledge gaps is critical to ensuring compliance with international obligations and fostering a secure environment for innovation and technological advancement.
Policy and decision-makers could use such knowledge as technical input to develop relevant policies, intervention programs, and control measures. This article is organized into three main sections. Section 1 provides an overview of the Strategic Trade Act 2010 (STA 2010) and technology transfer modes. Section 2 outlines the data collection process. Section 3 discusses research data analysis outcomes, including respondents’ demographic attributes, knowledge of STA 2010, and technology transfer modes.
Significance of research
Malaysia serves as an ideal case study due to its strategic position as a growing hub for research and technology transfer in Southeast Asia, located at the crossroads of major international trade routes. The country’s prominence in global research networks, bolstered by international collaborations and the presence of foreign researchers, lecturers, and students from various regions and continents, underscores the complexity of managing dual-use technologies. These diverse academic interactions amplify the risks of unintentional technology transfer and necessitate robust governance measures.
The risks discussed in this paper, such as unintentional breaches of export control regulations or the misuse of dual-use technologies, are not unique to Malaysia. However, they reflect global challenges in balancing the need for innovation with national security priorities. As proliferators increasingly target universities and research institutions worldwide to gain access to sensitive technologies, Malaysia’s case highlights the urgency of implementing preventive measures. Although Malaysia’s laboratories are not directly implicated in these incidents, the growing internationalization of its academic sector makes the study especially timely.
By examining Malaysia’s implementation of the Strategic Trade Act 2010 (STA 2010) and addressing its gaps, this study contributes to broader debates on dual-use technology governance. It provides actionable insights for nations particularly in developing regions that are working to align their regulatory frameworks with global standards. Addressing knowledge gaps among researchers, particularly in a country with diverse academic stakeholders, ensures that institutions are equipped to safeguard both national and international security while fostering responsible innovation. Lessons drawn from Malaysia’s experience offer valuable guidance for other countries facing similar challenges in managing dual-use technologies within increasingly globalized research ecosystems.
Background of research
Technologies such as global positioning system (Isa et al., 2017; Saad et al., 2018; Zaideen et al., 2019), the internet (Abdul Majid et al., 2016; Badrul Hisham et al., 2019), fitness bands (Brown et al., 2021; Mohamad Noor et al., 2023), touch screens, digital cameras, and microwaves were initially developed for defense purposes. With technological advancements, these products have found daily use. However, concerns about the misuse of such technologies have led to the implementation of stringent regulations and international agreements to prevent their misuse. The United Nations Security Council Resolution 1540 (UNSC Resolution 1540), approved on April 28, 2004, is a significant measure to combat the proliferation of weapons of mass destruction (WMD) and ensure global security. This resolution requires states to adopt and enforce effective laws to prevent non-state actors from acquiring or using nuclear, chemical, or biological weapons. It also emphasizes the need for high export controls to prevent sensitive data and technology from falling into the wrong hands. Following this, the 2012 Seoul Nuclear Security Summit highlighted the importance of global efforts to prevent the trafficking of sensitive materials and technologies (Pomper and Dover, 2012).
In recent years, the geopolitical implications of intangible technology transfer (ITT) have become more pronounced, particularly in the context of global technological competition. The risk of sensitive technologies being transferred through intangible means, such as emails, cloud storage, or international academic collaborations, presents challenges for both national security and global stability. ITT is often used by malicious actors or states to acquire sensitive knowledge without physically importing restricted items. Given these risks, many countries, including those in Southeast Asia, have recognized the need for stringent regulations to control both tangible and intangible transfers of dual-use technologies and research to maintain national and international security (Badrul Hisham et al., 2024b; Mohamed Yusof et al., 2024; Rehman and Qazi, 2019). In this regard, Malaysia’s Strategic Trade Act 2010 (STA 2010) is a key piece of legislation aimed at regulating the export, transit, and transshipment of strategic items, including dual-use goods, technologies, and data.
STA 2010 aligns with international efforts to prevent the proliferation of WMD and ensure that sensitive technologies, including those transferred through intangible means, are not misused (Albright et al., 2010; Rehman and Qazi, 2019; Reynolds, 2021; Salisbury, 2018; Salisbury et al., 2018). Given the increasing collaboration between academia and international partners, it is crucial to understand the level of awareness and knowledge among researchers regarding dual-use technology, dual-use research, and dual-use research of concern (DURC). As global research becomes more interconnected and interdisciplinary, the risk of unintentional technology transfer through academic channels grows. The regulation of intangible technology transfer has become a significant issue, as research institutions are often unaware of the risks associated with the transmission of sensitive data or technology through seemingly innocuous activities like international conferences, collaborative research, or cloud-based storage solutions.
Despite the implementation of STA 2010, gaps in knowledge and awareness of this Act remain a significant challenge, especially in academic settings. The case of Dr. Thomas Butler, an infectious disease expert at Texas Tech University in the United States, is a striking example of the risks associated with dual-use research. In 2003, Dr. Butler was involved in a high-profile legal case after he destroyed vials of the plague-causing bacterium Yersinia pestis without proper documentation, leading to multiple charges and a federal investigation (Tanne, 2003, 2004). Although no malicious intent was involved, Dr. Butler’s case highlights how a lack of awareness and adherence to export control regulations, including intangible technology transfer provisions, can result in serious legal consequences.
While there have been no recorded cases involving Malaysian researchers violating STA 2010, the potential for such incidents is growing as Malaysia continues to participate in global research and technology development. Anecdotal evidence from discussions with local experts and stakeholders suggests that many academic institutions in Malaysia still face challenges in fully implementing compliance mechanisms for STA 2010, particularly in relation to intangible technology transfer and dual-use technologies. This lack of knowledge could lead to unintentional non-compliance, especially as Malaysian researchers collaborate with international counterparts on sensitive technologies that may fall under export control regulations. The absence of local cases should not imply that the risks are non-existent. The potential for violations, particularly through intangible technology transfer, grows as research networks expand and the transfer of technology becomes more digitized and less tangible.
This study aims to explore the level of knowledge and awareness among Malaysian researchers regarding STA 2010, with a particular focus on the risks posed by dual-use technology and export control laws, including intangible technology transfer. By identifying areas where further education and compliance efforts may be necessary, the study seeks to enhance the understanding of how the STA 2010 impacts academic research and to highlight the challenges posed by intangible technology transfer and dual-use research in the Malaysian context.
Dual-use technologies and national security
The management of dual-use technologies has become a critical aspect of national security in the 21st century, with increasing attention to how such technologies influence global stability, trade, and international cooperation. The strategic importance of dual-use technologies lies in their dual nature, which can serve both civilian and military purposes. These issues are making them central to debates on non-proliferation, technology transfer, and international stability. This study builds on and contributes to these discussions by focusing on the Malaysian context, providing insights into how a middle-power nation navigates these global challenges.
Strategic use of dual-use technologies
The strategic implications of dual-use technologies have been extensively analyzed. Meier emphasizes the tension between controlling sensitive technologies and promoting cooperation in international trade and research, arguing that effective governance requires a balance between these objectives (Meier, 2013). Similarly, Horowitz highlights how emerging military technologies, often rooted in dual-use advancements, shape international politics by shifting power dynamics and exacerbating security dilemmas (Horowitz, 2020). Sechser et al. (2021) explore how these technologies impact international stability, noting that they can both deter and provoke conflict depending on their management. This study contributes to these debates by examining how Malaysia, as a developing nation with growing research capabilities, addresses the risks associated with dual-use technologies. Malaysia’s efforts to implement the Strategic Trade Act 2010 (STA 2010) illustrate the challenges of aligning national policies with international frameworks, such as the United Nations Security Council Resolution 1540.
Emerging technologies and international cooperation
The broader implications of dual-use technologies for international cooperation are examined by Vaynman and Volpe (2023), who argue that technological advancements significantly influence states’ willingness to cooperate on non-proliferation and export controls. Their concept of “dual-use deception” highlights the strategies employed by states to navigate the dual-use dilemma, balancing the advancement of national interests with adherence to international commitments. This framework aligns with Malaysia’s efforts to reconcile its national security priorities with obligations under global non-proliferation regimes. By setting the Malaysian case within these broader discussions, this study illustrates how insights from Malaysia’s implementation of STA 2010 can contribute to global strategies for managing dual-use technologies. It emphasizes the importance of adopting tailored approaches that address the unique challenges faced by nations with emerging research ecosystems, thereby advancing both national and international security objectives.
Dual-use technologies in Southeast Asia
Regional studies, by Lieggi (2016) and Santoro and Baker (2016) have identified Southeast Asia as a critical region for non-proliferation efforts due to its strategic trade routes and increasing technological capabilities. Lieggi (2016) warned of the non-proliferation challenges posed by dual-use technologies in the region, highlighting gaps in regulatory enforcement and awareness among stakeholders. Santoro and Baker (2016) similarly emphasized the need for capacity-building initiatives to strengthen trade controls across Southeast Asia. Building on these insights, this study positions Malaysia as a relevant case study within the regional debate. As Abdul Kareem (2016) notes, Malaysia has made significant strides in implementing strategic trade controls through STA 2010, but challenges remain in raising awareness and ensuring compliance among researchers and institutions. By focusing on the knowledge gaps in Malaysia’s academic sector, this study adds a new dimension to the discussion, emphasizing the role of researchers as key stakeholders in dual-use governance.
Comparisons within the Asia-Pacific region
The Asia-Pacific Region presents a unique set of challenges and opportunities in managing dual-use technologies, making it a critical area for comparative analysis. Regional studies, such as those by Lieggi (2016), Santoro and Baker (2016), and Sanders (2024), have highlighted the complexities of non-proliferation efforts in Southeast Asia and beyond. Lieggi (2016) identified enforcement gaps and limited institutional capacity as persistent challenges in Southeast Asia, emphasizing the need for tailored strategies to manage dual-use technologies effectively. Similarly, Santoro and Baker (2016) underscored the importance of capacity-building initiatives to strengthen trade controls across the region, particularly given the rapid technological advancements and strategic trade routes that characterize Southeast Asia.
Australia, as discussed by Sanders, provides an instructive example of a robust export control regime in the Asia-Pacific. Australia’s defense export control framework prioritizes critical technologies and provides a model for integrating regulatory enforcement with innovation (Sanders, 2024). These insights remain particularly relevant for Malaysia, which continues to face similar challenges in balancing national security concerns with its aspirations as a regional research and trade hub. By positioning Malaysia within this regional context, the study emphasizes shared challenges and opportunities for improving dual-use technology governance.
Comparisons with the European Union (EU) and United Kingdom (UK)
The European Union (EU) and the United Kingdom (UK) have established comprehensive frameworks for controlling dual-use items. The EU’s Council Regulation (EC) No 428/2009 sets up a regime for the control of exports, transfer, brokering, and transit of dual-use items, defining them as goods, software, and technology that can be used for both civil and military purposes (US Instruments, 2022). Similarly, the UK’s Anti-Terrorism, Crime and Security Act 2001 includes provisions to prevent terrorists from gaining access to materials that could be used for harmful purposes (Parliament of the United Kingdom, 2001). Malaysia hosts international campuses of UK universities, such as the University of Nottingham Malaysia Campus and the University of Southampton Malaysia Campus. These institutions adopt governance and compliance practices from their parent universities, which align with EU and UK standards. As a result, these international collaborations indirectly shape Malaysia’s approach to research governance and dual-use compliance.
Comparisons with the United States
The United States serves as a pivotal model for dual-use governance, given its extensive experience and significant influence in biosecurity and export controls. Frameworks like the United States (National Science Advisory Board for Biosecurity (NSABB), 2012) provide guidance on biosecurity and dual-use research, addressing issues at the request of the United States government. Additionally, the Export Control and Related Border Security (EXBS) Program aims to prevent the proliferation of weapons of mass destruction and destabilizing accumulations of conventional weapons by assisting countries in establishing effective export control systems (U.S. Department of State, 2021).
Malaysia’s engagement in United States led initiatives, such as the EXBS program, underscores its commitment to aligning with international best practices in export control and border security (U.S. Department of State, 2021). These collaborative efforts highlight the relevance of United States frameworks as benchmarks for evaluating and enhancing Malaysia’s Strategic Trade Act 2010 (STA 2010), providing insights into potential areas for improvement (NSABB, 2012; U.S. Department of State, 2021).
Strategic Trade Act 2010 (STA 2010)
Global trade control for dual-use technology (DUT) and strategic items has been part of Malaysia’s international trade policy since 2010. The trade control policy is incorporated into different STA 2010 provisions. Enacted by the Malaysian government in 2010, STA 2010 is deemed significant for the country to engage in global trade and import-export businesses, prevent global terrorism, and maintain international security. The STA 2010 primarily aims to control the export, transshipment, transit, and brokering of strategic items, goods, and technologies (including arms and related materials) and activities that potentially facilitate WMDs design, development, production, and delivery for local, regional, and global trade security purposes. The novelty of this Act lies in six parts, which contain 57 sections and one schedule:-
1. Preliminary,
2. Appointment and powers of strategic trade collectors,
3. Control of strategic items, unlisted items, and restricted activities,
4. Permit and registration,
5. Enforcement, and
6. General.
In meeting new global trade demands and developments, this enactment primarily manages the local exportation and movement of strategic items. While promoting global trade, the STA 2010 imposes the death penalty to parties breaching its provisions. This Act carries a transboundary effect, which is more common in criminal and penal laws rather than commercial or trade regulations. The high mobility of people between countries, advancement of information and communications technology, digital technology and globalization facilitate the implicit transfer of tangible or intangible goods, which is a global conundrum (Badrul Hisham et al., 2024a; Ministry of Investment, Trade and Industry, 2011). Strategic trade acts of the world, including Malaysia to prevent non-states from accessing weak links in the global security chain to proliferate and procure sensitive WMD-driven technologies.
The STA 2010 is governed, managed, coordinated, and enforced by Strategic Trade Secretariat (STS), a department within the Ministry of Investment, Trade, and Industry (MITI) together with other partner licensing agencies namely, Atomic Energy Licensing Board (AELB), a department within Ministry of Science, Technology, and Innovation (MOSTI), Malaysian Communications and Multimedia Commission (MCMC), a department within Ministry of Communications and Digital, and Pharmaceutical Services Division, a department within Ministry of Health. These agencies assist STS in the licensing process, as defined by their laws, for strategic items and technologies with expertise and resources.
The Strategic Trade (Restricted End-Users and Prohibited End-Users) Order 2010 further supports the implementation of STA 2010 (Ministry of Investment, Trade and Industry, 2011) based on the requirements of United Nation Security Council Resolution 1540 – OP3 (d). In this vein, member and signatory countries are encouraged to implement control measures based on their domestic needs and capabilities in different sectors or industries. At the domestic level, academic institutions are highly encouraged to set up biosecurity and bioethics committees or carry out studies to counter the potential risk of bioterrorism. Researchers can be introduced to relevant principles on data dissemination, the risk of joint research, the ethics of uploading dual-use data when attending conferences, exchanging research findings, sharing the moral implications of biological discoveries, and biomedical advances and their applications (Brizee et al., 2019).
Subjects and contents of Strategic Trade Act 2010 (STA 2010)
The STA 2010 is only applicable to parties who export, tranship, brings-in-transit, and brokers strategic or unlisted items (sections 9 [1], 9 [2], and 9 [3]), such as traders, exporters, cargo agents, carriers, freight forwarders, feeders’ operators, and logistics or service providers (section 11; Parliament of Malaysia, 2015). Given the mandatory nature of STA 2010 provisions, relevant parties with direct involvement under this Act must meticulously observe all the stipulated requirements. This Act also applies to (i) transshipment, traders, exporters, cargo agents, carriers, freight forwarders, feeder operators, logistic or service providers engaged in export activities (sections 12 [a], 12 [b], and 12 [c]; (Parliament of Malaysia, 2017), (ii) individuals who act on their own volition, (iii) people who represent others, and (iv) those who act as an agent of another person, with direct involvement in item negotiation, purchase, financing, conveying, buying, selling and supply.
Strategic items and matters associated with their origins, movements, and final use fall under STA 2010. Based on the MITI website, over 1500 strategic items require export permits to date (Ministry of Investment, Trade and Industry, 2023b). Despite being definitive and holistic, the numbers can change depending on time and necessity. Organizations with products that can be used as WMDs must register the items with MITI effective from 1 July 2011. Companies with unregistered products that are used as a WMD would be held liable and penalized. As such, parties that handle strategic items must fulfill their legal obligations with due diligence. Researchers should examine empirical information and ascertain its relevance to the Strategic Items List. The transference of such information falls under the export control restrictions in STA 2010. The party involved must apply for a permit from relevant authorities to protect his involvement and legalize his trade.
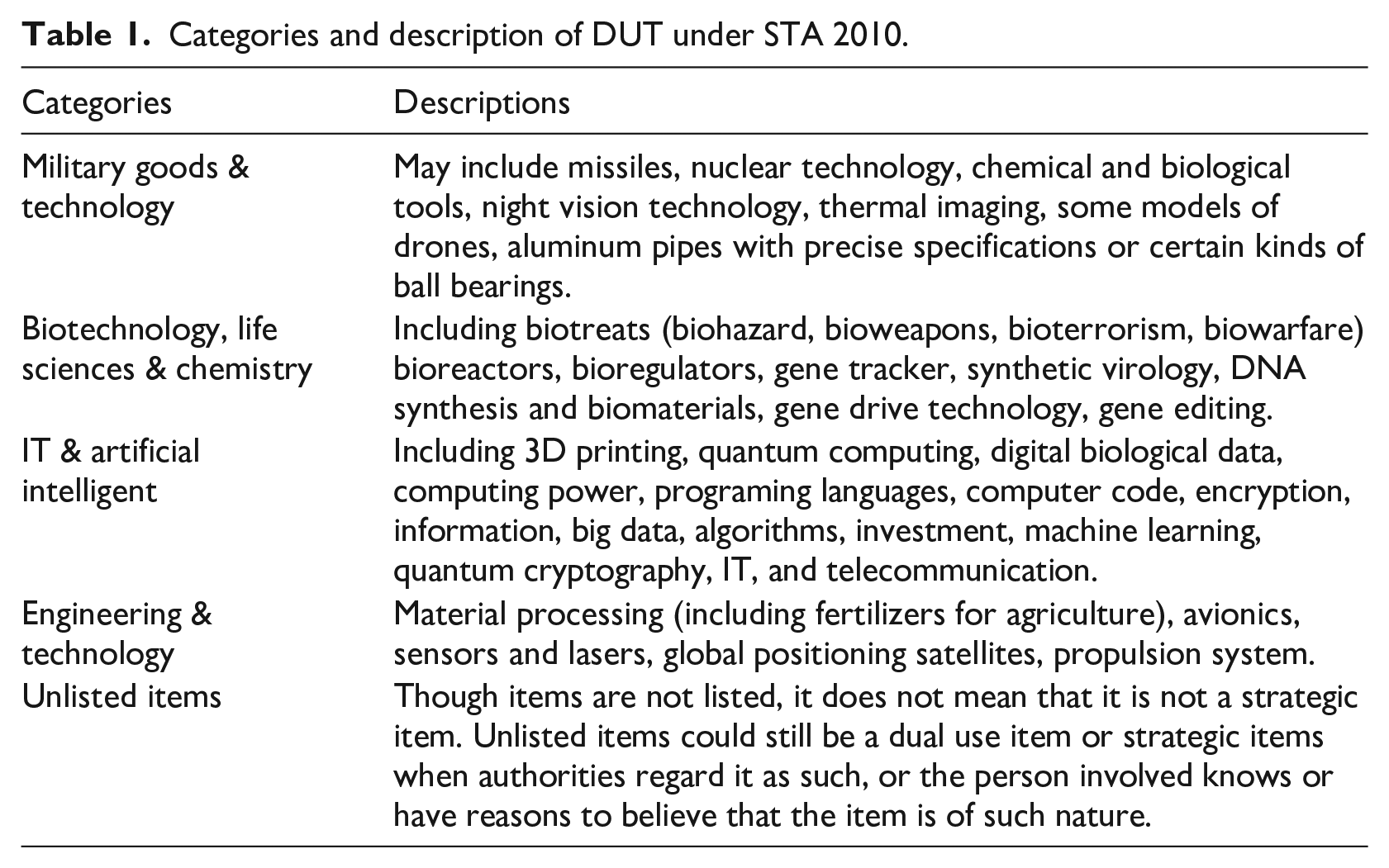
The STA 2010 clearly stipulate about dual use technology and its use. A dual use technology with potential use of being used to design, produce, or improve a weapon is considered a dual-use item. Despite not being its intended goal, the item could and is used to develop weapons. Judgments about risk and threat are contextual. In the context of technology, there are five categories of dual use technology under STA 2010 ranging from military goods and technology to goods and technologies for civil, commercial, and public daily use (see Table 1; Ministry of Investment, Trade and Industry, 2023b).
Categories and description of DUT under STA 2010.
Control mechanism
The STA 2010 imposes various permit and license types to govern the security and transparency of strategic items and dual use technology movements. In this regard, the chances of such items being exploited are significantly lowered. This scenario justifies the issuance of permits on a transactional basis, where one permit only applies to one transaction. The person involved must re-apply for a new export permit if purchasers, importers, or end-users make alternations that invalidate the issued permit. All parties are required to maintain export permits or broker registration documents.
The penalty clauses reflect the seriousness of the strategic item issues and STA 2010 stipulations. Under STA 2010, a person or entity violating the Act can be (i) penalized, (ii) imprisoned, or (iii) imprisoned and sentenced to death (Parliament of Malaysia, 2015). As such, one who engages in export, transshipment, transit, and the brokering of listed and unlisted strategic items must obtain a permit or broker registration certificate from relevant authorities. These transaction records and relevant documents must be retained for the stipulated period. Single-use permit, bulk permit, multiple-use permit, and special permit are the four permit types available under the Act. Although products not on the strategic items list are exempted from obtaining a permit, it is prudent to re-confirm this statement in compliance with the stringent laws of STA 2010. Following the stipulation of STA 2010, exporters who are informed by relevant bodies or those who know that unlisted items may be used for illicit activities must declare the items as unlisted.
Control mechanism
The STA 2010 imposes various permit and license types to govern the security and transparency of strategic items and dual use technology movements. In this regard, the chances of such items being exploited are significantly lowered. This scenario justifies the issuance of permits on a transactional basis, where one permit only applies to one transaction. The person involved must re-apply for a new export permit if purchasers, importers, or end-users make alternations that invalidate the issued permit. All parties are required to maintain export permits or broker registration documents.
The penalty clauses reflect the seriousness of the strategic item issues and STA 2010 stipulations. Under STA 2010, a person or entity violating the Act can be (i) penalized, (ii) imprisoned, or (iii) imprisoned and sentenced to death (Parliament of Malaysia, 2015). As such, one who engages in export, transshipment, transit, and the brokering of listed and unlisted strategic items must obtain a permit or broker registration certificate from relevant authorities. These transaction records and relevant documents must be retained for the stipulated period. Single-use permit, bulk permit, multiple-use permit, and special permit are the four permit types available under the Act. Although products not on the strategic items list are exempted from obtaining a permit, it is prudent to re-confirm this statement in compliance with the stringent laws of STA 2010. Following the stipulation of STA 2010, exporters who are informed by relevant bodies or those who know that unlisted items may be used for illicit activities must declare the items as unlisted.
Definition of terms
Malaysia enacts STA 2010 under Articles 25 and 48 of the United Nation Charter 1945 (United Nations, 1945a, 1945b) to discharge its global duties. Similarly, the country contributes to the global efforts in combating the exploitation of dual use technology, specifically items that can be used to design (i) nuclear, chemical, and biological weapons or their parts, (ii) WMDs, and (iii) their means of delivery. Researchers with a sound understanding of acceptable, adequate, and applicable definitions of terms and concepts can contextualize them to their study needs. The following paragraphs discuss the terms and concepts relevant to this study.
Strategic items
As prescribed and published in the Ministerial Order and Government Gazette, respectively, strategic items denote the goods and technology controlled under STA 2010 (Parliament of Malaysia, 2015). The list of items would reflect the items currently regulated under the global export control regimes and United Nation Security Council Resolution 1540. Currently, (i) nuclear materials, facilities, and equipment, (ii) special materials and associated equipment, (iii) materials processing, (iv) electronics, (v) computers, (vi) telecommunications and information security, (vii) sensors and lasers, (ix) navigation and avionics, (x) marine, (xi) aerospace and propulsion, and (xii) military items constitute strategic items.
Strategic items are divided into three categories, military, non-military list, and dual-use items, following the STA 2010 and strategic trade (strategic items) list 2023. Checking with the product manufacturer, importers, competitors, and controllers or regulators is a means of ascertaining whether an item is strategic or otherwise. A permit is legally required to handle, move, and transit a strategic item. Nevertheless, an unlisted item does not imply that it is not strategic. The item may fall under the category of unlisted items in certain scenarios.
Dual-use item (DUI)
The DUI, which constitutes data, knowledge, research, and technology, is not a novel phenomenon (Miller and Selgelid, 2007). Literally, the term “dual-use” stems from the integration of two root words: “dual” (Merriam-Webster Dictionary, 2025a) and “use” (Merriam-Webster Dictionary, 2025b). Dual implies more than one, while use denotes (product or service) usage and purpose. Overall, dual-use indicates the application of certain activities or entities in more than one way (Miller and Selgelid, 2007). Balmer and Martin (Balmer and Martin, 2008) attributed the duality of use and function to the combination of technical properties and intentions. The potential manipulation of dual-use knowledge, research, and technology for illicit activities may trigger ethical problems (Wessener, 1997). In the arms trade, some of these exploitations are impossible to trace following their use of household products, such as cleaning fluids (Alagha, 2011; Gosden and Gardener, 2005).
It is crucial to identify practical mechanisms that prevent the misuse of (i) dual-use knowledge, research, and technology or (ii) relevant data from proliferating and being manipulated for harmful reasons. In this study, dual-use item represents items that can be used for non-military and military purposes or in relation to weapon mass destruction or proliferation. Military items denote entities (including any part or component thereof) that are solely designed or modified for defense purposes and the technology necessary for military item development, production, or use. Summarily, dual use item includes the technology required to develop produce or use any dual-use items.
Dual-use knowledge (DUK), dual-use research (DUR), dual-use research of concern (DURC), and dual-use technology (DUT)
As extensions of knowledge, research, and technology, dual-use knowledge (DUK), dual-use research (DUR), dual-use research of concern (DURC), and dual-use technology (DUT) may reflect more than one use (Suk et al., 2011). The close association between knowledge, research technology, and technology advancement renders it possible to generate dual-use knowledge, dual-use research and dual-use technology (Suk et al., 2011). Essentially, dual-use technology and dual-use research share a long history of origin with several meanings (Merriam-Webster Dictionary, 2023a). Despite their interconnection, both elements reflect different attributes.
In this study, dual-use technology denotes a technology with (i) primary and targeted use and (ii) secondary, unintended, and untargeted use. The primary purpose or use reflects good intention and use, while its secondary counterpart is potentially malicious without its original intention. Both dual-use research and dual-use knowledge could produce valuable single-use or dual-use technology via processes, machines, or artifacts. The dual-use technology stems from research and knowledge, albeit with potential exposure to nefarious activities with serious consequences for public health or the environment (van Aken, 2006).
On academic grounds, discovering or creating dual-use artifacts or items is welcomed and valuable. Nevertheless, an artifact with a second use that does not relate to its primary purpose requires equal attention. Hence, the dual-use research of concern was conceptualized (Oltmann, 2015; Resnik et al., 2011). This label holds relevance amidst the high risk for the second use (Kuhlau et al., 2008). For example, ammonium nitrate is a common fertilizer that can also be used to make improvised bombs (Hess, 2013). Despite being mundane items, nails, ball bearings, timers, batteries, and mobile phones can also be used to improvise weapons. These items may not be new but would appear so when newly designed and used as weapons. Such an occurrence implies dual use (Forge, 2007; National Research Council, 2004; United States Government Policy for Institutional Oversight of Life Sciences Dual-use Research of Concern, 2014).
Under the United Nation Security Council Resolution 1540, dual-use technology is associated with the risk or actual multiplication and manipulation of dual-use data, technology, or knowledge that diverges from the intended use. Such use would propagate nuclear terrorism, the development of weapons capable of violating human rights, or the production of weapon mass destructions (Ministry of Investment, Trade and Industry, 2023a; United Nations, 2004). Given that the same scientific research that benefits mankind can equally cause harm, researchers are subjected to ethical dilemmas. As responsible citizens, researchers must choose their projects based on legal, moral, and ethical grounds.
Mode of transfer under STA 2010
Tangible technology transfer (TTT) and intangible technology transfer (ITT) represent two modes of transfer under STA 2010. Two variations of ITT risks associated with weapon mass destruction and proliferation are presented below: -
(i) Intangible knowledge transfer via technical assistance, consultancy, scientific meetings, discussions, exchanges, presentations, demonstrations, visual inspections, lectures and seminars, teaching, training, working knowledge, and education of foreign nationals.
(ii) Controlled technology or technical data transfer via intangible (electronic) means, such as email, fax, telephone, internet, and publications (Malaysian Communications and Multimedia Commission, 2014).
These activities are challenging but necessary to prevent unwarranted damages (Group C-TW and Ministry of Investment, Trade and Industry, 2021).
Situational analysis of dual-use technology in Malaysia
The STA 2010 has been implemented and enforced for almost 13 years (Abdul Karim et al., 2016; Abdul Majid et al., 2016; Balakrishnan, 2008; Tan et al., 2016; Yussof, 2010). Government officers in MITI (Ministry of Investment, Trade and Industry, 2010, 2019) or MCMC (Malaysian Communications and Multimedia Commission, 2014) have also conducted awareness and public engagements on the subject matter. Research and works conducted by Abdul Majid et al. (2016) and Tan et al. (2016) provided useful insights into dual-use technology and its implications. Notwithstanding, research on the implementation of STA 2010 or its impacts particularly on research communities remains lacking compared to outside Malaysia (Ma et al., 2022; Macnish and van der Ham, 2020; Steruska et al., 2019; Tran et al., 2011). This study demonstrated researchers’ knowledge level on STA 2010, technology transfers, strategic items, and dual-use technology and dual-use item.
Methodology
This section outlines the methodology used to assess the knowledge of research communities in Malaysia regarding strategic items, the Strategic Trade Act 2010 (STA 2010), dual-use technology, and dual-use items. Both primary and secondary data were employed to address the research questions, focusing on the “what,” “where,” “who,” and “when” of the study (De Vaus, 2001; Leedy and Ormrod, 2013; Mishra and Alok, 2017). The methodology was carefully designed to ensure replicability, validity, and the robustness of the results, while also maximizing their generalizability. The following provides a detailed description of the procedures used.
The primary aim of this study was to assess the knowledge levels of research communities in Malaysia regarding strategic items, STA 2010, dual-use technology, and dual-use items. Both secondary and primary data were crucial for addressing the research questions. Secondary data were collected through an extensive literature review, which helped lay the foundation for the study (Leedy and Ormrod, 2013). Primary data were gathered using questionnaires, featuring structured questions (De Leeuw, 2008; Kerlinger and Lee, 2000). These questionnaires were chosen due to their affordability, capacity to cover large samples (Creswell and Creswell, 2018), and ability to address multiple research questions within a short period (Denzin and Lincoln, 2005). The questions were standardized to ensure that all respondents were asked the same set of questions in a consistent manner, enhancing the reliability and comparability of the data.
Sample, sampling technique, and sample size
This study employed purposive sampling to select respondents from Malaysian universities and research institutes. Purposive sampling was chosen due to the specific focus on academicians and researchers involved in dual-use technology, ensuring the sample was relevant and reliable (Kirk, 2013). Criteria for inclusion were clearly defined to ensure that only participants with appropriate expertise were included. To ensure an adequate sample size, the study adhered to the recommendations of Memon et al. (2020) and Hair et al. (2019), which suggest a minimum of 100 respondents for studies employing simple models with fewer variables. Out of 164 distributed questionnaires, 153 valid responses were obtained, achieving a sample size sufficient to maintain confidence, validity, and generalizability in line with Hair et al.’s guidelines (Hair et al., 2019; Kirk, 2013). While purposive sampling can introduce bias, the selection process was meticulously documented to ensure transparency and enable replication.
A larger sample size typically results in more accurate and reliable data, with a smaller error margin leading to more credible generalizations (Neerchal et al., 2008). Given that quantitative research models with multiple variables often require larger datasets, the selected sample size was deemed adequate for this study (Grant and Booth, 2009; Sundaram et al., 2010). The respondents were selected using purposive sampling, ensuring representation from key academic disciplines and research institutions in Malaysia.
Data collection instruments
The primary data collection instrument was a 66-items structured questionnaires derived from empirical studies on knowledge, attitudes, and practices (KAP; Bano et al., 2013; Lee et al., 2021; Liao et al., 2022; Liu et al., 2020; Roelens et al., 2006; Timmermans and Cleeremans, 2015). This standardized questionnaire was developed to assess respondents’ knowledge of STA 2010, dual-use technology, and dual-use items. The KAP framework was chosen due to its ability to measure both knowledge and behavioral intent, making it highly suitable for assessing awareness and practice concerning strategic items (Launiala, 2009; Vandamme, 2009).
To enhance validity, the questionnaire was reviewed by experts in the field, and a pilot test was conducted to refine the instrument before full-scale data collection. The items were standardized to ensure consistency across all respondents, and close-ended questions were used to facilitate statistical analysis and improve response comparability (De Leeuw, 2008; Kerlinger and Lee, 2000). The questionnaire included general information about the study, its purpose, and a consent statement, ensuring ethical transparency.
Data collection procedure
The questionnaires were disseminated both electronically and in physical form to universities and research institutes across Malaysia to ensure comprehensive coverage of the target population. Respondents received a detailed cover letter outlining the research objectives and ethical considerations, and informed consent was obtained from all participants before their involvement in the study. To maximize efficiency, the questionnaires were designed to be self-administered, with clear instructions provided for completing and submitting responses (Denzin and Lincoln, 2005).
In addition to the online distribution, three enumerators were deployed to collect data in person, ensuring that universities across the entire country were adequately represented. The combination of online and offline data collection methods helped achieve a broader reach, enabling the study to gather data from a diverse range of institutions, disciplines, and geographical locations across Malaysia. This mixed approach ensured that participants from various academic and research environments were adequately represented, enhancing the inclusivity and comprehensiveness of the dataset. Additionally, it mitigated potential limitations of online-only data collection by providing all respondents, regardless of their access to technology, the opportunity to participate in the study.
Ethical considerations
All ethical guidelines were strictly followed to protect the participants’ confidentiality and anonymity. Each respondent’s identity was anonymized using unique codes, and access to the raw data was restricted to the research team only. Participation was voluntary, and respondents were fully informed about the study’s aims and their rights as participants. The data were stored securely, adhering to institutional and legal data protection guidelines, ensuring compliance with both national and institutional ethics standards. Details of the ethical considerations undertaken at each stage of the research process are illustrated in Figure 1.
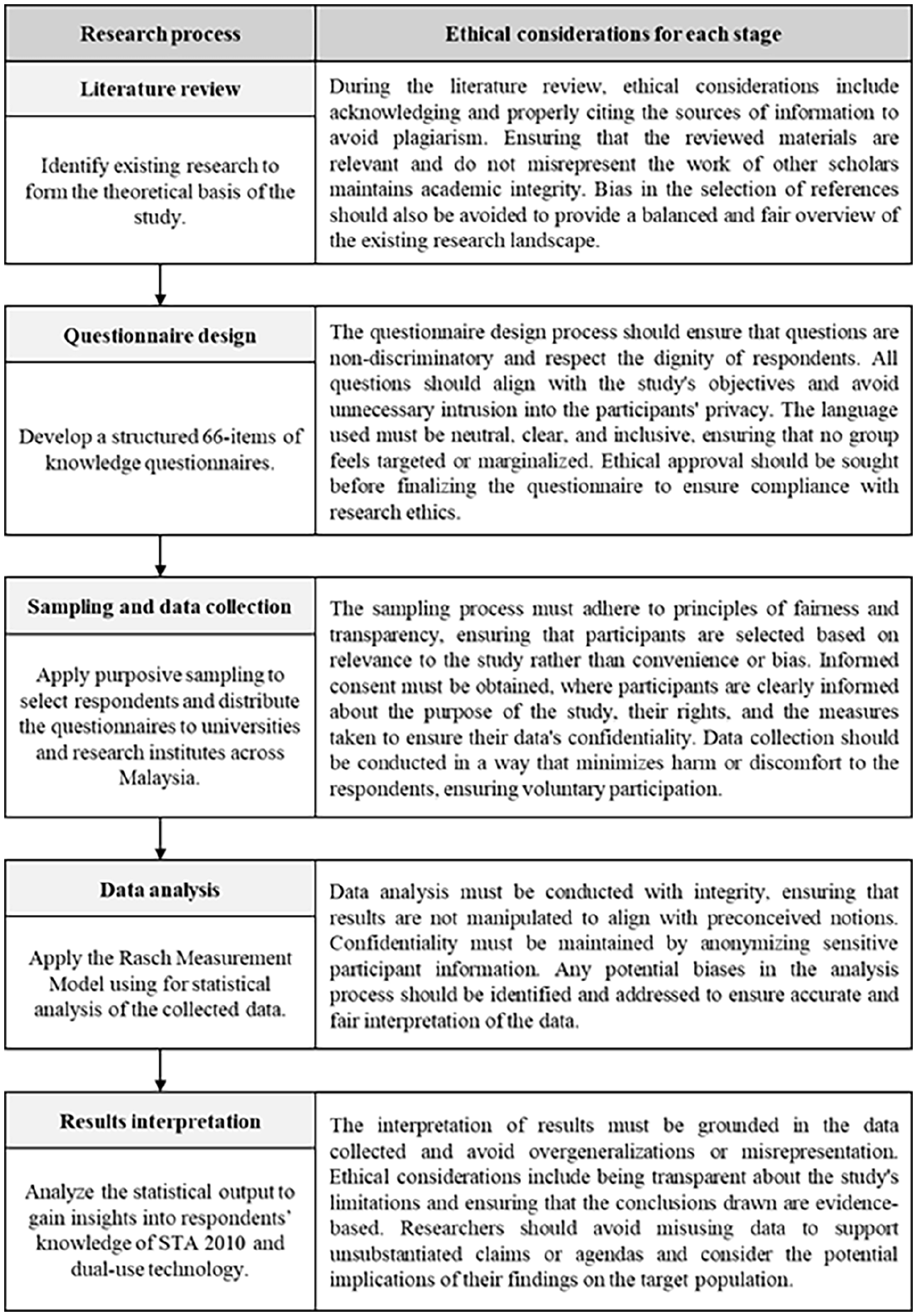
Research process flow diagram with integrated ethical considerations at each stage.
Statistical analysis
For data analysis, the Rasch Measurement Model was employed using Winstep software version 3.72.3 (Abdul Aziz et al., 2013; Adnan and Mohd Matore, 2019; Boone et al., 2014). The Rasch model was selected due to its ability to handle ordinal data and assess the reliability and validity of the measurement instrument. The model enables the estimation of item difficulties and respondent abilities on a single latent scale, which provides insights into the respondents’ knowledge levels regarding STA 2010 and dual-use technology. Additionally, fit statistics were generated to assess the appropriateness of the data for the Rasch model, and misfitting items were carefully examined.
Quantitative results were presented as means (M), percentages (%), and frequency analyses, providing a clear and comprehensive picture of the data distribution (Creswell and Creswell, 2018). The data were screened for missing responses, and appropriate handling procedures, such as pairwise deletion, were applied where necessary. To improve the replicability of the study, the equations used for the Rasch analysis (item reliability and person reliability indices, item fit, etc.) were documented, and all parameters were set according to standard practices in the field (Abdul Aziz et al., 2013; Adnan and Mohd Matore, 2019; Boone et al., 2014). Future researchers are encouraged to use the same software settings and data handling techniques to replicate or extend this study.
Process flow and model visualization
To enhance understanding and replicability, a process flow diagram detailing the key stages of the research process (literature review, questionnaire design, data collection, and statistical analysis) is illustrated in Figure 1. This visual representation outlines the flow of activities and highlights how different components of the study are interconnected.
Results
This section presents the main findings of the study. Section 3.1 covers the psychometric analysis of the instrument, including model fit, reliability, and construct validity. Section 3.2 outlines the data analysis process, while Section 3.3 describes the demographic profiles of respondents. Finally, Section 3.4 highlights key findings and observations, including general knowledge, knowledge levels on STA 2010, and the demographic impact on STA 2010 knowledge.
Psychometric analysis of the instrument
The respondents’ knowledge of strategic items, STA 2010, dual-use technology (DUT), and dual-use items (DUI) was measured using a structured questionnaire. The psychometric properties of the knowledge construct were assessed using the Rasch Measurement Model. This model was chosen because of its capacity to convert ordinal data from Likert-scale responses into interval-level measurements, offering a more precise understanding of the respondents’ knowledge levels. It also allows for the analysis of item fit and person reliability, which are crucial for ensuring that the instrument measures the intended constructs effectively.
Model fit and outlier removal
During the psychometric analysis, five outlier knowledge items were identified and subsequently removed to improve the model’s overall fit. This step was necessary to enhance the precision of the instrument, as items that do not align well with the underlying construct can introduce measurement error. However, it should be noted that the removal of these items slightly narrowed the scope of the knowledge construct. This is a limitation that should be considered when interpreting the results, as some aspects of knowledge may have been excluded due to their misalignment with the Rasch model requirements.
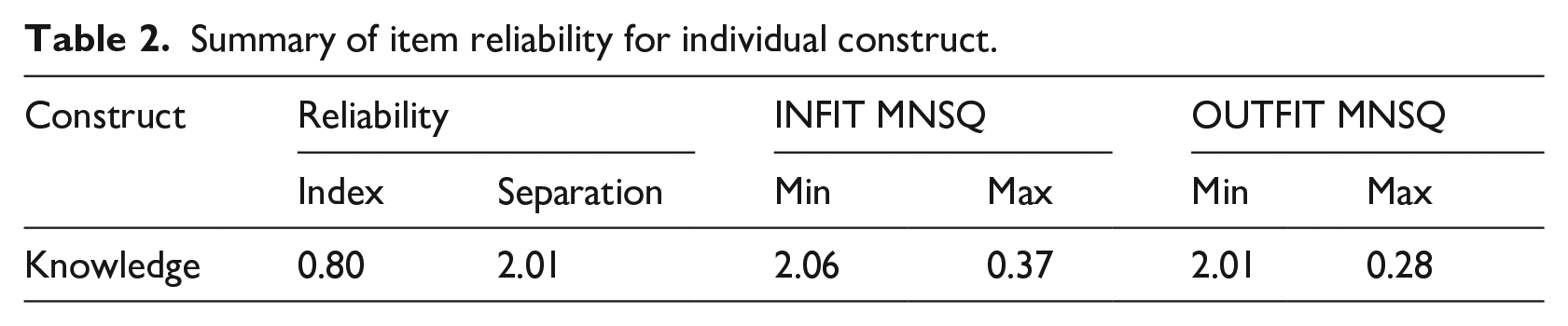
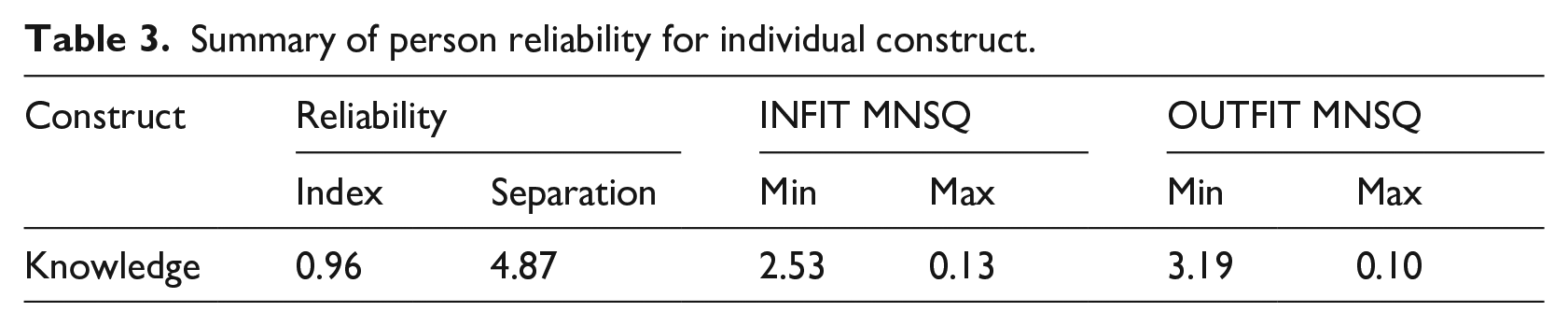
Item reliability and person reliability
The item reliability index was calculated at 0.80, with a separation index of 2.01 (Table 2). This indicates that the items in the questionnaire are reasonably well-differentiated, with a reliability level that exceeds the minimum acceptable threshold of 0.70. The person reliability index was found to be even higher, at 0.96, with a separation of 4.87 (Table 3). This suggests that the questionnaire reliably differentiates between respondents with varying levels of knowledge, reflecting strong psychometric properties. A separation index greater than 2.0 is typically considered sufficient for distinguishing between low and high performers, reinforcing the robustness of the questionnaire’s structure.
Summary of item reliability for individual construct.
Summary of person reliability for individual construct.
The infit and outfit mean-square (MNSQ) values further support the reliability of the instrument. For items, the infit MNSQ values ranged from 0.37 to 2.06, and the outfit MNSQ values ranged from 0.28 to 2.01. These values fall within the generally accepted range (0.5-1.5), indicating a good fit between the items and the construct. The few items with MNSQ values slightly outside this range were likely more difficult or misunderstood by respondents, suggesting areas for refinement in future iterations of the questionnaire.
Similarly, for persons, the infit MNSQ values ranged from 0.13 to 2.53, and the outfit MNSQ values ranged from 0.10 to 3.19. Although a few values exceed the upper limit of the ideal range, the overall distribution suggests that most respondents interacted with the questionnaire items in a meaningful way, further reinforcing the instrument’s reliability.
Construct validity
The construct validity of the instrument was also examined using Rasch-based principal component analysis. The raw variance explained by the measure was 47.2%, surpassing the minimum recommended threshold of 40% (Table 4). This indicates that nearly half of the variance in the data is explained by the underlying knowledge construct, suggesting a strong alignment between the questionnaire items and the concept of knowledge being measured.
Construct validity of the instrument.
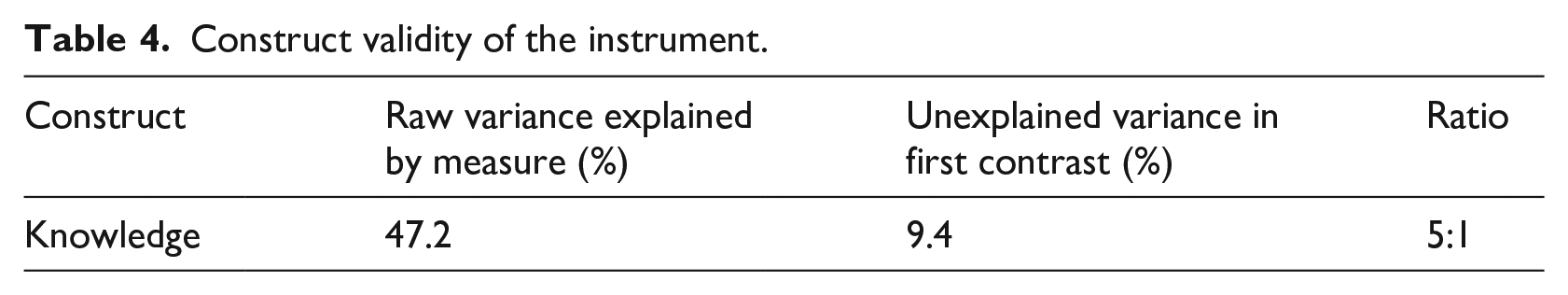
The unexplained variance in the first contrast was 9.4%, reflecting an acceptable level of error and supporting the idea that there is limited multidimensionality within the data. The ratio of explained to unexplained variance was approximately 5:1, further demonstrating the instrument’s construct validity. While there is always room for improvement in terms of reducing unexplained variance, these results provide strong evidence that the questionnaire effectively measures the intended knowledge domains.
Data analysis
The study data were analyzed using frequency, percentage, and mean. Some of the questionnaire items were phrased negatively, and by including both positive and negative items, the research aimed to prompt respondents to carefully consider their answers, reducing acquiescence and extreme response bias. Initially, a 5-point Likert scale was used, capturing varying levels of agreement from 1 (strongly disagree) to 5 (strongly agree). However, for the analysis of respondents’ knowledge about strategic items, the STA 2010, dual-use technologies and dual-use items, the scale was reduced to a 3-point format. Responses of “strongly disagree” and “disagree” were combined into a single category labeled “Little knowledge” to represent minimal familiarity, while the “No knowledge” category remained unchanged, capturing those with no awareness. Similarly, the “agree” and “strongly agree” responses were merged into “Some knowledge,” reflecting various degrees of partial or substantial knowledge. The re-categorization is tabulated in Table 5.
Re-categorization of scale.
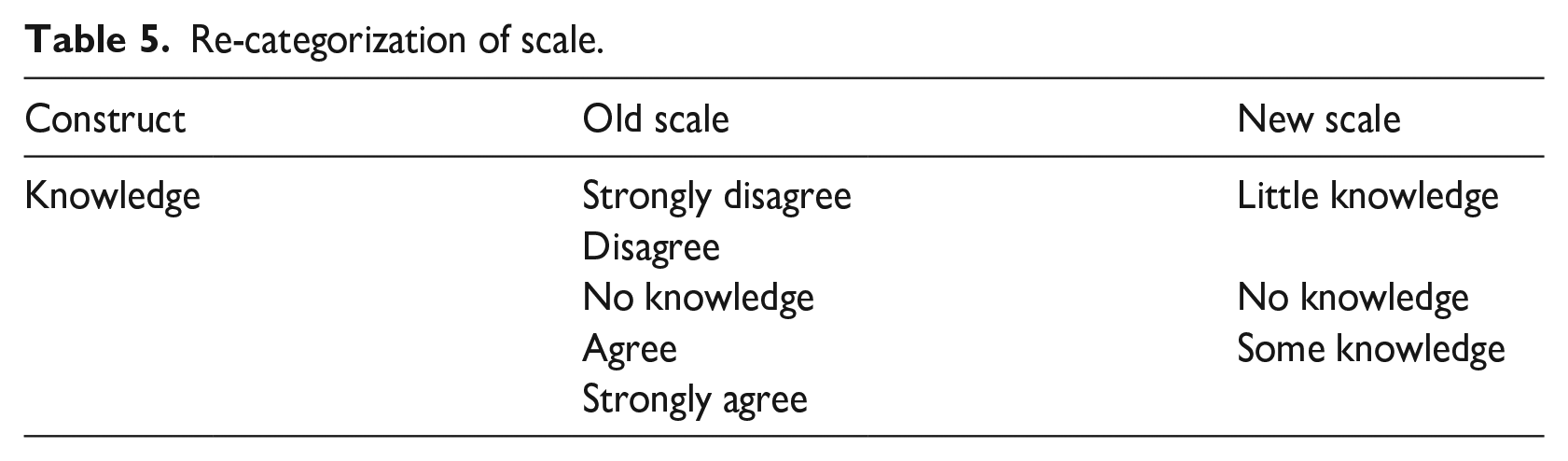
This re-categorization was in line with findings from similar studies that demonstrate the benefits of reducing scale points to enhance clarity, minimize response bias, and maintain data integrity. For instance, reducing a 5-point to a 3-point scale has been shown to improve structural validity and eliminate disordered response options without compromising reliability (Fang et al., 2011; Gabes et al., 2021). This method simplified the analysis, making distinctions between different levels of knowledge clearer and reducing potential biases such as extreme response bias.
Demography
The study collected data from respondents across a diverse range of universities in Malaysia, representing various institutional categories. The respondents’ sociodemographic factors, including age, institution category, niche, and professional positions, were gathered and analyzed as tabulated in Table 6. These factors provided valuable insights into the distribution of respondents across different age groups, institutional categories, research niches, and professional roles, contributing to a comprehensive understanding of the data.
Demographics data and analysis of respondents.
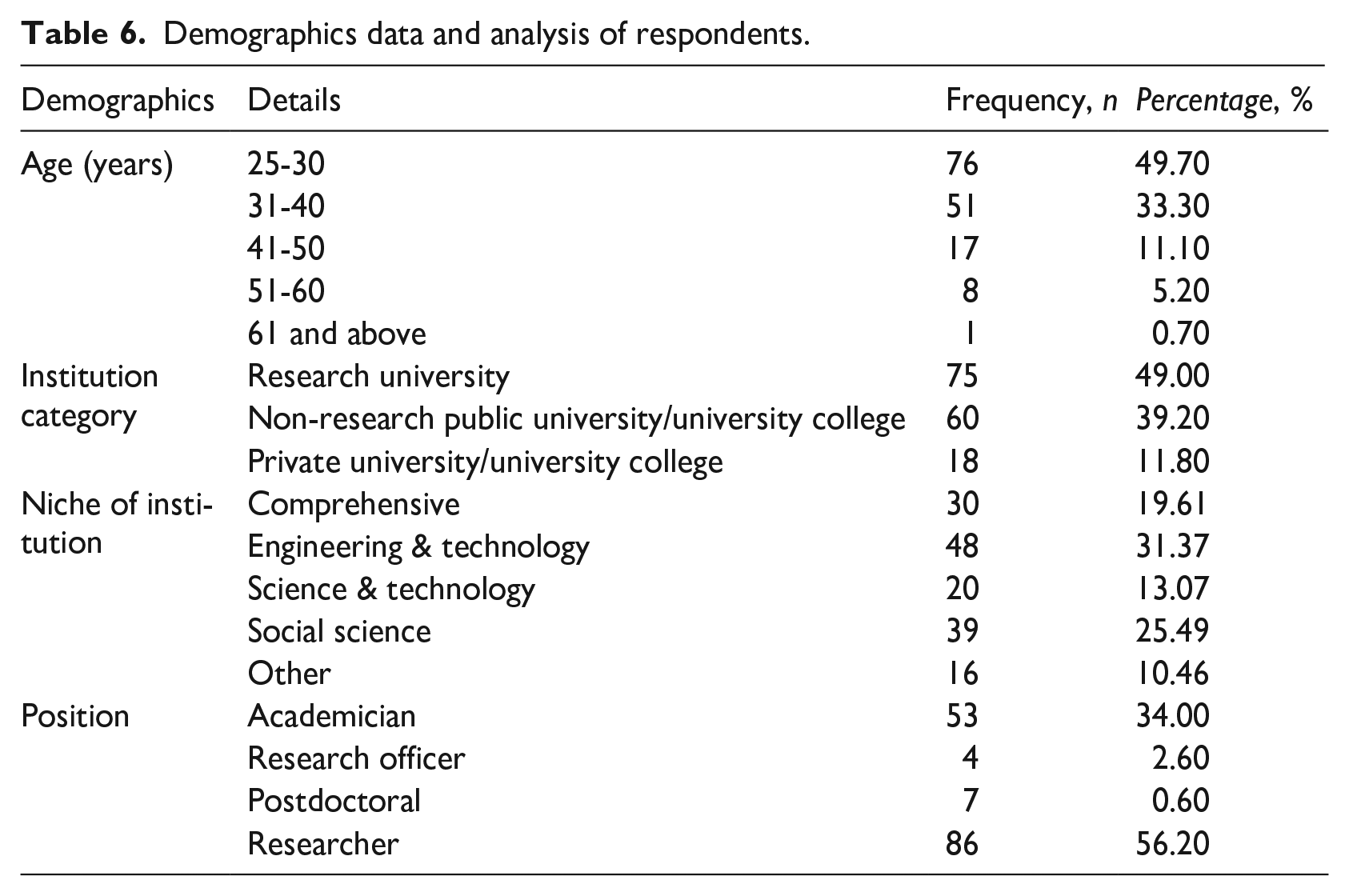
The universities involved in the study spanned three key categories: research university, non-research public university/university college, and private university/university college, ensuring a broad representation of academic staff involved in dual-use technologies and technology transfer. The participating universities were selected based on their research activities, particularly in fields relevant to the study’s focus. This selection provided a wide-ranging view of the awareness and engagement with dual-use technologies across these different categories of institutions, enabling a more thorough analysis of the collected data.
Findings and observations
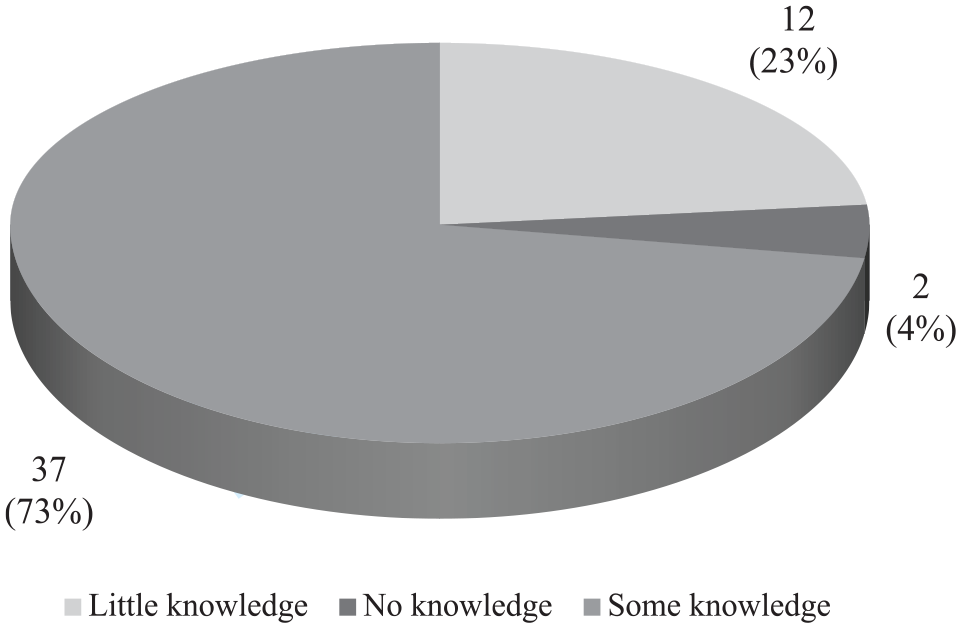
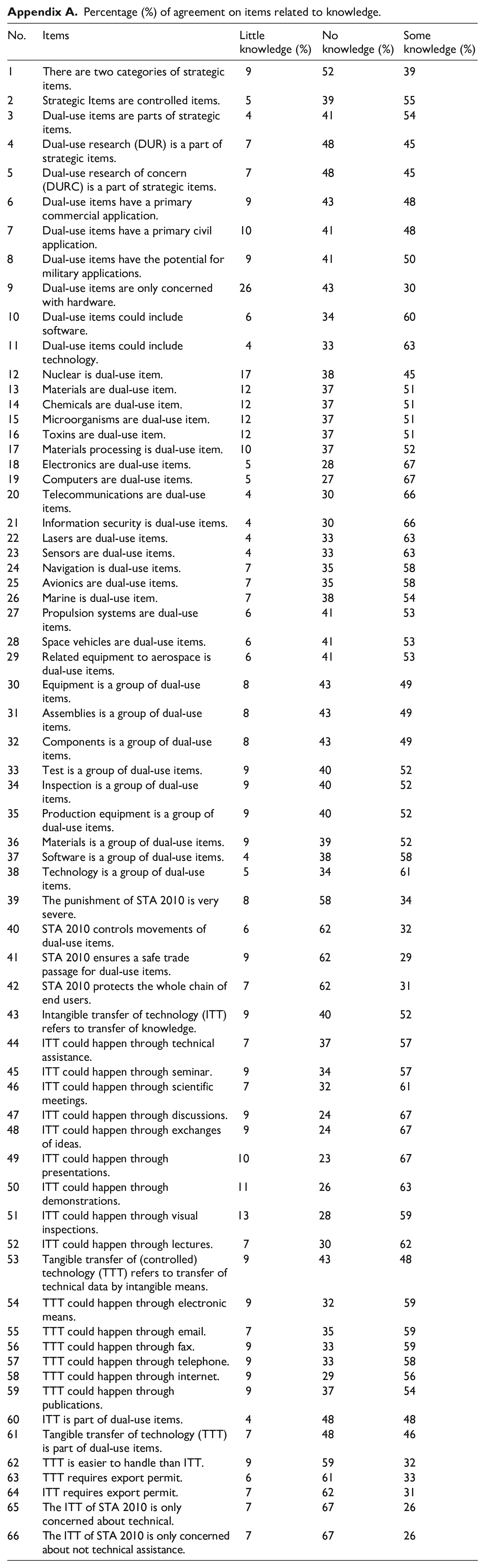
This study aimed to evaluate the knowledge levels of respondents regarding strategic items, the Strategic Trade Act 2010 (STA 2010), dual-use technologies, and dual-use items. The findings are summarized in Table 7 and Figure 2, which provide valuable insights into the participants’ understanding of these critical areas, as well as highlight key gaps that require attention.
Summary of knowledge levels on dual-use items, STA 2010, ITT, and TTT.
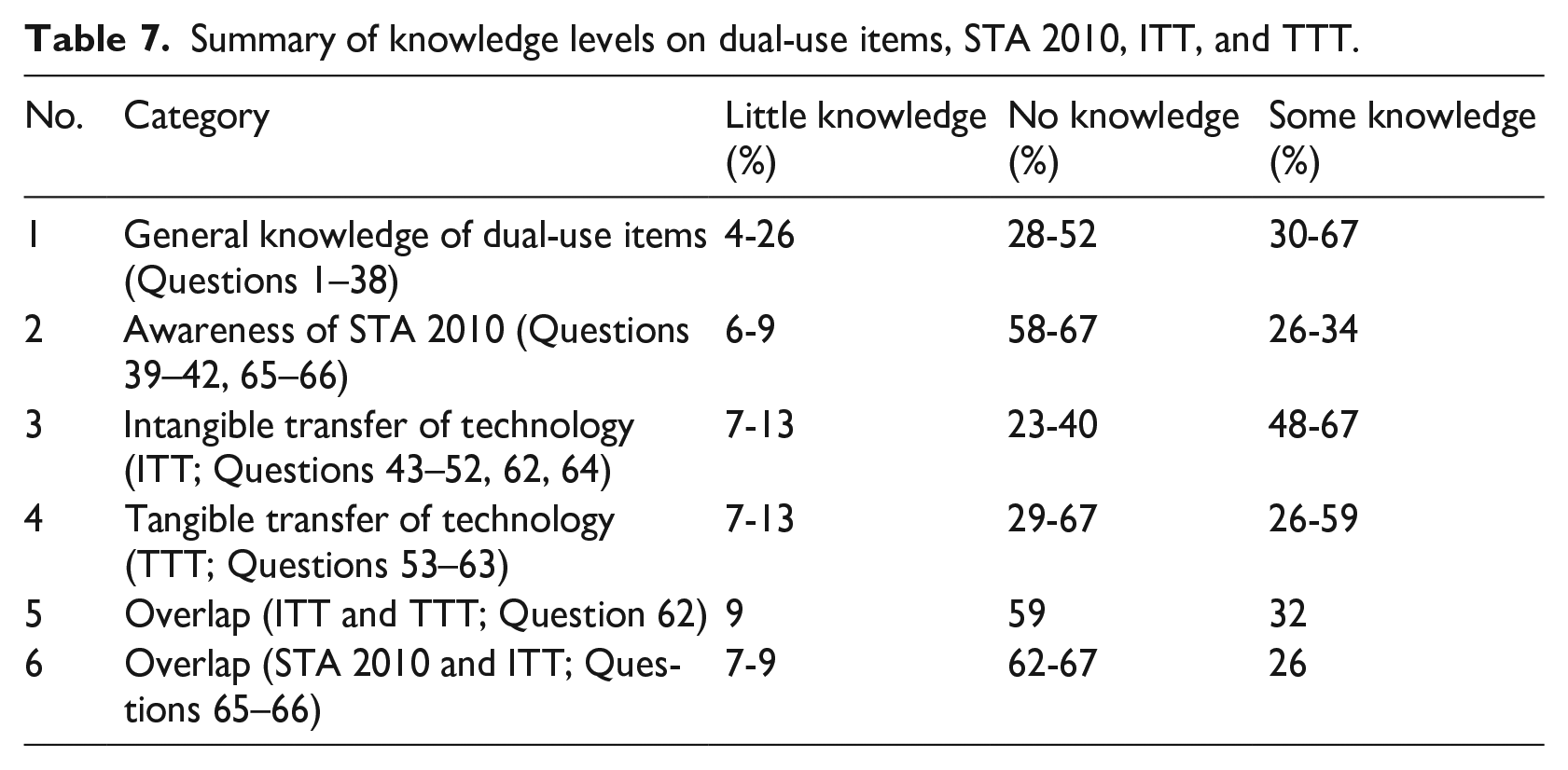
Knowledge on strategic items, STA 2010, dual-use items, intangible transfer of technology, and tangible transfer of technology.
General knowledge on strategic items, STA 2010, DUT, and DUI
As illustrated in Figure 2, most respondents (73%) indicated that they possessed some knowledge of strategic items, STA 2010, and dual-use technologies. A smaller portion (23%) reported little knowledge, while only 4% of respondents expressed no knowledge on these matters. The mean analysis (M = 3.86) suggests that the respondents generally possess a moderate level of understanding. This is indicative of a foundational awareness of the key topics; however, significant knowledge gaps persist areas, as detailed in Table 7.
Summary of knowledge levels on dual-use items, STA 2010, ITT, and TTT
Table 7 provides a detailed overview of the respondents’ knowledge levels across four key categories: dual-use items, STA 2010, intangible transfer of technology (ITT), and tangible transfer of technology (TTT). The table reveals varying levels of understanding across these categories, with notable deficiencies in knowledge concerning STA 2010 and the regulatory frameworks governing technology transfers. Complete details of the result are available in Appendix A.
Respondents demonstrated a moderate level of understanding regarding the general concept of dual-use items, as indicated by Table 7. Between 30% and 67% of participants reported “Some knowledge” of strategic items and their classifications. However, a significant proportion, 28%-52%, reported “No knowledge” of the specific applications of dual-use items, particularly in contexts related to military and civil uses (e.g. Items 5-6), indicating gaps in understanding their broader implications.
Knowledge of the Strategic Trade Act 2010 (STA 2010) was relatively limited. 58%-67% of respondents indicated “No knowledge” of STA 2010s key provisions, particularly in terms of its control over the movement of dual-use items and the regulatory requirements for technical data transfers (Items 26-29). Only 26%-34% of participants demonstrated “Some knowledge,” indicates that there is a substantial need for enhanced awareness and education on STA 2010 within the research and academic communities.
Understanding of the mechanisms involved in intangible transfer of technology (ITT) was varied between 48% and 67% of respondents indicated “Some knowledge” regarding the occurrence of ITT through presentations, discussions, and scientific meetings (Items 30-38). However, 23%-40% reported “No knowledge” of the legal and regulatory frameworks governing these transfers, particularly regarding technical assistance and seminars. This highlights a need for further clarification on how intangible transfers are managed under STA 2010.
Knowledge of tangible transfer of technology (TTT) was similarly varied. While 26%-59% of respondents demonstrated “Some knowledge” regarding the processes of TTT, such as the transfer of technical data through email, publications, or electronic means, a significant portion (29%-67%) reported “No knowledge” of the regulatory requirements for such transfers. This lack of understanding, especially concerning the need for export permits (Items 48-50), suggests that respondents may be unaware of key compliance requirements related to tangible transfers.
Question 51, which explored the overlap between STA 2010 and ITT, demonstrated that 67% of respondents reported “No knowledge” of how STA 2010 regulates intangible transfers of technology. Only 26% of participants showed “Some knowledge,” underscoring the need for targeted interventions to improve comprehension of the Act’s provisions in relation to ITT, especially within academic and research environments where such transfers are increasingly relevant.
The findings, as illustrated by Figure 2 and Table 7, indicate that while respondents possess a general awareness of strategic items and dual-use technologies, significant gaps in knowledge exist in relation to the STA 2010, IIT, and TTT. These gaps highlight the urgent need for comprehensive training and educational programs to improve understanding of dual-use regulations, particularly in academic settings where inadvertent involvement in dual-use technologies may occur. Efforts to raise awareness of the legal frameworks governing technology transfers will be crucial for ensuring compliance and safeguarding against potential risks associated with dual-use research.
Demographic impact on STA 2010 knowledge
The analysis of demographic data provides valuable insights into the varying levels of knowledge about STA 2010 among researchers in Malaysia. Age, institutional category, niche of the institution, and position all play a role in shaping respondents’ understanding of strategic trade regulations, dual-use items, and the intangible and tangible transfer of technology.
Looking at age groups, about half of the respondents (49.7%) fall within the 25-30-year-old range, with an additional 33.3% aged between 31 and 40 years. These younger cohorts may have limited exposure to export controls or dual-use technologies, contributing to the high percentage reporting “little knowledge” (73%) or “no knowledge” (4%). Limited access to capacity-building initiatives or institutional support for strategic trade compliance further compounds this generational knowledge gap. Addressing this issue would require targeted training programs, such as workshops and mentorship opportunities, designed specifically for early-career researchers.
Institutional affiliation also affects knowledge levels. Respondents from research universities, who make up the majority (49%), are likely to have better access to resources and support for STA compliance compared to those in non-research public universities (39.2%) or private universities (11.8%). However, even within research-intensive institutions, disparities persist, indicating the need for enhanced capacity-building efforts to ensure consistent knowledge dissemination. Tailored interventions like seminars and collaborative networks between research and non-research universities could help bridge these gaps.
The niche of academic institutions highlights additional challenges. While respondents from Engineering & Technology fields make up 31.37%, a significant portion also comes from Social Sciences (25.49%) and Comprehensive institutions (19.61%). Social Science researchers may struggle to relate STA 2010 concepts to their disciplines, leading to lower engagement and understanding. Incorporating STA 2010 topics into interdisciplinary research and curricula could facilitate broader knowledge transfer, ensuring greater awareness across academic fields.
Position also plays a significant role. Researchers, who constitute 56.2% of the sample, may have the most exposure to dual-use technologies but often lack specific training in STA 2010 compliance. Smaller groups, such as postdoctoral fellows (4.6%) and research officers (2.6%), may require customized training to address their unique roles in the research ecosystem. Academicians, who make up 34% of respondents, could benefit from workshops focused on integrating STA 2010 concepts into teaching and research supervision.
These findings underscore the importance of a multifaceted approach to improving STA 2010 knowledge among Malaysian researchers. Efforts should consider demographic factors like age, institutional type, niche, and position to design targeted interventions that effectively address specific knowledge gaps. Such initiatives would enhance compliance with STA 2010 and strengthen Malaysia’s role as a responsible participant in the global non-proliferation regime.
Discussion
The empirical outcomes on researchers’ knowledge level are both intriguing and concerning. Following previous studies, knowledge has been shown to have a direct effect on the risk level and the possibility of danger (KAP; Lee et al., 2021; Vandamme, 2009). World Health Organization has demonstrated that risk gradually decreases with an increase in knowledge, and this is reflected in the current study’s findings (World Health Organization, 2012). This study is the first of its kind to gather data specifically on Malaysian research communities’ responses to the challenges of dual-use technologies (DUT), dual-use research (DUR), and dual-use research of concern (DURC). The data reveals that researchers possess some knowledge, which marks a positive development, yet this knowledge remains insufficient when compared to international standards.
In contrast, countries European Union (EU; BAFA, 2023), United Kingdom (UK; McLeish and Nightingale, 2004), and United States (US; NSABB, 2012) have implemented more comprehensive regulatory frameworks and educational programs aimed at dual-use research. The EU, through Regulation 428/2009 (US Instruments, 2022), and the UK, with the Anti-terrorism, Crime and Security Act 2001 (Parliament of the United Kingdom, 2001), have established more stringent controls over dual-use items and research activities (McLeish and Nightingale, 2004). Similarly, the US’s biosecurity measures (van Aken, 2006), especially post-Patriot Act 2001, are more robust and supported by initiatives like the NSABB (2012). This comparison underscores the significant gap in knowledge and preparedness within Malaysian academia, highlighting the need for urgent improvements.
This small-scale data effectively fills a gap in the existing literature and provides valuable technical input for policymakers and decision-makers to enhance the current system. The need for academia, research communities, and stakeholders to upgrade their level of knowledge and improve attitudes toward DUT, DUR, and DURC is critical. STA 2010 aims to govern these areas, ensuring that research and development activities are carried out in a safe and secure environment. These issues should be examined in more detail by future researchers beyond the scope of this pilot study.
Limitation of this study
This study acknowledges several limitations, particularly regarding the reliance on self-reported data, which may introduce biases such as social desirability bias. Respondents might overestimate or underestimate their true knowledge, leading to a potential disconnect between their reported and actual working knowledge, especially given the sensitive nature of STA 2010 and dual-use technology regulations. Such biases pose challenges for the accuracy and interpretation of the findings (Boone et al., 2014). Future research should incorporate strategies like ensuring anonymity, using indirect questioning techniques, or triangulating self-reported data with objective assessments, such as direct knowledge tests, to mitigate these biases and provide a more comprehensive evaluation of respondents’ knowledge levels.
Furthermore, the study sample was limited to researchers from Malaysian Higher Education Institutes, which may restrict the generalizability of the findings to other sectors, such as industry or government agencies. The scope of this study was defined by the Ministry of Investment, Trade, and Industry (MITI), as academia typically does not engage directly in the import or export of strategic items. However, the increasing international collaborations among researchers may result in unintentional involvement in activities governed by STA 2010, underlining the need to improve awareness within academic circles.
Another limitation stems from the use of the Rasch Measurement Model. While it provided valuable insights into the psychometric properties of the instrument, the removal of five outlier items to improve model fit may have inadvertently narrowed the scope of the knowledge construct, potentially excluding valuable nuances. This could affect the comprehensiveness of the study. While the Rasch model mitigates some biases, it may also limit the breadth of the measurement tool if not properly accounted for (Scharl and Gnambs, 2024).
Recommendation for future studies
Future research should focus on determining specific areas where knowledge gaps exist regarding STA 2010 by conducting in-depth and stratified analyses of demographic and institutional data. Correlational studies are essential to explore relationships between variables such as age, institutional category, niche, and position, and their influence on STA 2010 knowledge levels. For instance, younger researchers may lack awareness due to limited professional exposure, while individuals in non-technical fields might struggle to connect STA 2010 principles to their disciplines. Sector-specific assessments could delve deeper into how knowledge levels vary across research areas such as engineering, social sciences, and comprehensive institutions to identify disciplines that require specialized interventions. Long-term studies could track changes in knowledge levels over time, evaluating the impact of capacity-building initiatives, training programs, and policy dissemination efforts. Perception and awareness surveys can help uncover misconceptions or knowledge gaps among researchers, while focus group discussions may provide qualitative insights into barriers faced by specific demographic groups, such as early-career researchers or those in private universities.
To address these gaps, targeted solutions must be developed. Age-specific training programs should be designed for early-career researchers aged 25-30 and 31-40, focusing on fundamental concepts of dual-use technologies and practical aspects of STA 2010 compliance. Discipline-specific modules should integrate STA 2010 related topics into academic curricula, particularly in non-technical fields such as social sciences, fostering interdisciplinary understanding, institutional capacity-building initiatives should promote collaboration between research universities and non-research or private universities, creating knowledge-sharing networks that include joint training programs, resource sharing, and collaborative workshops. Customized training sessions tailored to different roles such as practical compliance measures for researchers, STA 2010 integration in teaching for academicians, and advanced compliance training for postdoctoral fellows and research officers can ensure role-specific expertise. Online learning platforms offering webinars, e-learning modules, and video tutorials could provide continuous access to STA 2010 knowledge, particularly for researchers in remote or under-resourced institutions. National-level awareness campaigns, including outreach events, interactive workshops, and competitions, could further promote understanding of STA 2010, its goals, and its implications. Implementing these recommendations would bridge knowledge gaps, enhance compliance with STA 2010, and strengthen Malaysia’s role in global non-proliferation and export control initiatives.
Insights from the European Union, United Kingdom, and United States for Malaysia’s context
The decision to compare Malaysia with the European Union, United Kingdom and United States is driven by practical connections and shared priorities. The EU and UK indirectly influence Malaysia’s research governance through international campuses such as the University of Nottingham Malaysia (University of Nottingham, 2024) and the University of Southampton Malaysia (University of Southampton, 2024). These institutions adopt compliance practices aligned with their parent universities, serving as benchmarks for aligning Malaysian research governance with global standards. This comparative analysis underscores areas where Malaysia can draw lessons from these frameworks to enhance the implementation of its Strategic Trade Act 2010.
Similarly, Malaysia’s strong trade and research ties with the United States highlight the importance of comparisons with the US. Collaborative initiatives, such as the Export Control and Related Border Security Program (EXBS), demonstrate Malaysia’s commitment to aligning with international standards (U.S. Department of State, 2021). By evaluating Malaysia’s progress against these established systems, gaps and opportunities can be identified to strengthen its regulatory framework. These comparisons provide actionable insights for policymakers aiming to balance compliance with innovation in managing dual-use technologies.
Conclusion
The study aimed to assess the knowledge level of Malaysian academia regarding dual-use technologies and export control requirements, and it has successfully gathered initial data indicating that researchers possess some knowledge of the subject matter. However, the study reveals that this knowledge is insufficient when compared to global counterparts, particularly those in the European Union (BAFA, 2023), United Kingdom (McLeish and Nightingale, 2004), and United States of America (NSABB, 2012). This conclusion is based on data showing knowledge gaps that align with previous research, which found that inadequate knowledge increases risks in dual-use research (National Research Council (US) Committee on Assessing Fundamental Attitudes of Life Scientists as a Basis for Biosecurity Education, 2009; World Health Organization, 2012).
While the study provides a positive indication that some awareness exists, the current level of understanding among local researchers is not enough to fully mitigate the risks associated with DUT, DUR, and DURC. This place researchers and their institutions at potential legal and ethical risk, particularly in relation to STA 2010, which seeks to prevent the unintentional transfer of sensitive technologies. However, it is also essential to note that completely halting the dissemination of dual-use research, out of fear of legal consequences, would contradict the objectives of STA 2010 and UNSC Resolution 1540. These frameworks encourage responsible knowledge sharing to ensure continued social and technological progress.
The findings highlight an urgent need for more comprehensive education and training within the academic and research communities. The data serves as a crucial foundation for further research and policy enhancements aimed at creating a more secure and informed environment for dual-use research. Future studies should focus on identifying specific areas where knowledge deficiencies exist and provide targeted solutions to address these gaps.
Footnotes
Appendix
Percentage (%) of agreement on items related to knowledge.
| No. | Items | Little knowledge (%) | No knowledge (%) | Some knowledge (%) |
|---|---|---|---|---|
| 1 | There are two categories of strategic items. | 9 | 52 | 39 |
| 2 | Strategic Items are controlled items. | 5 | 39 | 55 |
| 3 | Dual-use items are parts of strategic items. | 4 | 41 | 54 |
| 4 | Dual-use research (DUR) is a part of strategic items. | 7 | 48 | 45 |
| 5 | Dual-use research of concern (DURC) is a part of strategic items. | 7 | 48 | 45 |
| 6 | Dual-use items have a primary commercial application. | 9 | 43 | 48 |
| 7 | Dual-use items have a primary civil application. | 10 | 41 | 48 |
| 8 | Dual-use items have the potential for military applications. | 9 | 41 | 50 |
| 9 | Dual-use items are only concerned with hardware. | 26 | 43 | 30 |
| 10 | Dual-use items could include software. | 6 | 34 | 60 |
| 11 | Dual-use items could include technology. | 4 | 33 | 63 |
| 12 | Nuclear is dual-use item. | 17 | 38 | 45 |
| 13 | Materials are dual-use item. | 12 | 37 | 51 |
| 14 | Chemicals are dual-use item. | 12 | 37 | 51 |
| 15 | Microorganisms are dual-use item. | 12 | 37 | 51 |
| 16 | Toxins are dual-use item. | 12 | 37 | 51 |
| 17 | Materials processing is dual-use item. | 10 | 37 | 52 |
| 18 | Electronics are dual-use items. | 5 | 28 | 67 |
| 19 | Computers are dual-use items. | 5 | 27 | 67 |
| 20 | Telecommunications are dual-use items. | 4 | 30 | 66 |
| 21 | Information security is dual-use items. | 4 | 30 | 66 |
| 22 | Lasers are dual-use items. | 4 | 33 | 63 |
| 23 | Sensors are dual-use items. | 4 | 33 | 63 |
| 24 | Navigation is dual-use items. | 7 | 35 | 58 |
| 25 | Avionics are dual-use items. | 7 | 35 | 58 |
| 26 | Marine is dual-use item. | 7 | 38 | 54 |
| 27 | Propulsion systems are dual-use items. | 6 | 41 | 53 |
| 28 | Space vehicles are dual-use items. | 6 | 41 | 53 |
| 29 | Related equipment to aerospace is dual-use items. | 6 | 41 | 53 |
| 30 | Equipment is a group of dual-use items. | 8 | 43 | 49 |
| 31 | Assemblies is a group of dual-use items. | 8 | 43 | 49 |
| 32 | Components is a group of dual-use items. | 8 | 43 | 49 |
| 33 | Test is a group of dual-use items. | 9 | 40 | 52 |
| 34 | Inspection is a group of dual-use items. | 9 | 40 | 52 |
| 35 | Production equipment is a group of dual-use items. | 9 | 40 | 52 |
| 36 | Materials is a group of dual-use items. | 9 | 39 | 52 |
| 37 | Software is a group of dual-use items. | 4 | 38 | 58 |
| 38 | Technology is a group of dual-use items. | 5 | 34 | 61 |
| 39 | The punishment of STA 2010 is very severe. | 8 | 58 | 34 |
| 40 | STA 2010 controls movements of dual-use items. | 6 | 62 | 32 |
| 41 | STA 2010 ensures a safe trade passage for dual-use items. | 9 | 62 | 29 |
| 42 | STA 2010 protects the whole chain of end users. | 7 | 62 | 31 |
| 43 | Intangible transfer of technology (ITT) refers to transfer of knowledge. | 9 | 40 | 52 |
| 44 | ITT could happen through technical assistance. | 7 | 37 | 57 |
| 45 | ITT could happen through seminar. | 9 | 34 | 57 |
| 46 | ITT could happen through scientific meetings. | 7 | 32 | 61 |
| 47 | ITT could happen through discussions. | 9 | 24 | 67 |
| 48 | ITT could happen through exchanges of ideas. | 9 | 24 | 67 |
| 49 | ITT could happen through presentations. | 10 | 23 | 67 |
| 50 | ITT could happen through demonstrations. | 11 | 26 | 63 |
| 51 | ITT could happen through visual inspections. | 13 | 28 | 59 |
| 52 | ITT could happen through lectures. | 7 | 30 | 62 |
| 53 | Tangible transfer of (controlled) technology (TTT) refers to transfer of technical data by intangible means. | 9 | 43 | 48 |
| 54 | TTT could happen through electronic means. | 9 | 32 | 59 |
| 55 | TTT could happen through email. | 7 | 35 | 59 |
| 56 | TTT could happen through fax. | 9 | 33 | 59 |
| 57 | TTT could happen through telephone. | 9 | 33 | 58 |
| 58 | TTT could happen through internet. | 9 | 29 | 56 |
| 59 | TTT could happen through publications. | 9 | 37 | 54 |
| 60 | ITT is part of dual-use items. | 4 | 48 | 48 |
| 61 | Tangible transfer of technology (TTT) is part of dual-use items. | 7 | 48 | 46 |
| 62 | TTT is easier to handle than ITT. | 9 | 59 | 32 |
| 63 | TTT requires export permit. | 6 | 61 | 33 |
| 64 | ITT requires export permit. | 7 | 62 | 31 |
| 65 | The ITT of STA 2010 is only concerned about technical. | 7 | 67 | 26 |
| 66 | The ITT of STA 2010 is only concerned about not technical assistance. | 7 | 67 | 26 |
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work is funded by the Universiti Teknologi Malaysia through Professional Development Research University [Q.K130000.21A2.07E01, 2023]. The data collection process for this study was funded by CRDF Global [202109-68099, R.K130000.7656.4C636, 2022]. The research team also received assistance and approval from the Strategic Trade Secretariat (STS) of the Ministry of Investment, Trade, and Industry (MITI), Malaysia to collaborate with the ongoing research project.
