Abstract
Covert Global Navigation Satellite System spoofer, called position deceptive tracking controller for unmanned aerial vehicle, is studied via analyzing the error characteristics in this article. Specifically, the following topics are discussed: (1) design the position deceptive tracking controller to make unmanned aerial vehicle deviate from the original path and follow up the spoofed new path point by point, and (2) analyze the related parameters by exploring the characteristics of the initial estimated state errors. Simulation results show the designed controller can realize the position offset of unmanned aerial vehicle unknowingly. What’s more, it can eliminate the initial state errors by selecting appropriate parameters.
Keywords
Introduction
On December 4, 2011, there was a big sensational military incident. An unmanned reconnaissance aircraft RQ-170 from the Central Intelligence Agency was captured by Iranian air forces in the eastern border area. 1 An Iranian engineer involved in cracking RQ-170 publicly explained the whole process. Their team first blocked the communication lines and cut off their contact with the ground control center. And then they interrupted the safety connection between RQ-170 and the satellites of Global Navigation Satellite System (GNSS) to force RQ-170 into the automatic navigation state. After these steps, they used unmanned aerial vehicle (UAV) spoofing technology to wrap the error message into seemingly reliably GNSS information, and eventually made UAV land to the designated location. The engineer insisted that the entire deception process had no need to crack the remote control and communication signal between UAV and the accusation center. 2
Likewise, similar event occurred again 1 year later. It is said that the Iranian Revolutionary Guard captured “Scan Eagle” in 2012, when this unmanned reconnaissance aircraft was patrolling the Persian Gulf waters, conducting reconnaissance and gathering intelligence. Afterward, Iranian military demonstrated the picture of capturing the drone. This event proved the feasibility of the interference method used in Iran once again. 3,4
Two vessels from the United States sailed into Iranian waters just few hours before US president Barack Obama delivered his final State of the Union speech in January 2016. 5 The Iranian military intercepted these vessels and captured 10 US sailors. No military official could explain why these vessels had strayed from their intended path. Without a clear explanation, it is speculated that Iran had sent deceptive GNSS signals to deviate the sailors into a scheduled path. 6
These events, that Iran captured American drones or vessels, are successful applications of deceptive spoofing technology in military affairs, which also had set off an upsurge of research on this field internationally. 7,8 As the navigation satellites are off the ground about 20,000–36,000 km, the power of their signals is very weak, which is usually lower than the noise 20 dB. Hence, GNSS signals are susceptible to malicious interference. GNSS spoofing attack has been taken regard as one of the most imminent threats to almost all cyber-physical system incorporated with the civilian GNSS signal. 9 –11
Regarding the civilian GNSS signals as the breakthrough point, many researchers have proposed a series of unmanned system deceptive schemes. Scholars at Cornell University began to conduct deception interference research for the purpose of trying to “deceive” GNSS receiver. 12 They firstly described how these researchers to place “fake” receivers near the targeted receiving device. And then they analyzed how the “fake” receivers to tamper and transmit the signals from the GNSS satellites. Eventually, they illustrated how the targeted receiving device to use the transmitted false signals. 13 A paper that described these results was presented at the American Association meeting held in Savannah, Georgia, on September 19, 2008. 13 Turin Polytechnic University built a simple deception test platform called “Limpet Spoofer.” It proved that the deception jamming technique could draw the receiver from the real signal to the false signal, with an anomaly of the receiver carrier ring and code loop in the total spoofing process. 14,15 The localization navigation team of University of Calgary published several papers on deceptive spoofing technology for GNSS systems. They mainly analyzed the types of deceptive jamming and established the model of the deceptive signals. 16,17
The compression assisted mode, that put the GNSS civil C/A code deceptive signals into the acquisition and tracking loop receiver, was applied in O’Hanlon et al. 18 The experimental results showed that the GNSS receiver could be successfully located at the scheduled position by reasonably controlling the frequency of the deceptive signal. The problem of the delay time about the GNSS deceptive signals was analyzed in Baziar et al. 19 It drew the conclusion that when the sum of the distance from the forwarded satellite to the transponder and the distance from the transponder to the real point is less than the distance from the forwarded satellite to the virtual point, no interference took effect on the receiver clock. Some scholars investigated the influence of the different factors on the performance of the receiver, such as the signal noise ratio, the carrier phase difference, and the code phase difference. 20 Furthermore, the capture probability of the forwarding spoofing interference toward GNSS receiver is studied in Ioannides et al. 21 Simulation results showed that the GNSS receiver spoofing had a higher acquisition probability if the forwarding spoofing only had a small forwarding gain.
The researches in the literature 12 –21 are mainly in the signal level which is aimed at putting the generated GNSS signals into the unmanned system. There is no theoretical discussion about generating which kind of GNSS signals to achieve targeted covert deception. Todd Humphreys, 8,22 –29 and his team in the University of Texas had done a lot of work. In their GNSS attack experiment, they set the UAV’s plant as double-integrator dynamics model. Besides, UAV typically employed Kalman filter to estimate their states, and proportional-derivative (PD) algorithm to generate the control commands. They further built the interconnection between the controller, plant, and estimator of the UAV and GNSS spoofer, so as to calculate the required counterfeit GNSS signals. After receiving the counterfeit GNSS signals, the positions, velocities, and times of GNSS receiver were influenced, and then the precise navigation was interfered. The computer processed these signals containing false geographic information and led to wrong navigation. 22 –24 In Shepard et al., 25 the US Department of Homeland Security tested the feasibility of the Todd Humphreys’ deceptive spoofers toward the civilian UAV at the White Sand Missile Range. This experiment achieved the same as the Iranian’s result. Todd Humphreys also succeeded in making a super yacht, named White Rose of Drachs (63 m long, worth 80 million dollar), deviate from its route without the captain’s consciousness. 26 –28,29 It proved that deceptive spoofing technology posed a threat to civilian and military GNSS location devices.
The researches on GNSS spoofing technology are highly confidential for any country. The public, authoritative, and theoretically valuable researches at present are provided by Todd Humphreys. However, it can be found that (1) many parameters are set with no rules in Todd Humphreys’ experiment, and (2) the deceptive tracking controller is too idealistic with no zero error, and there is no way to achieve in reality. In view of the above analysis, this article intends to focus on the design of the deceptive tracking controller and the select of the related spoofed parameters via analyzing the error characteristics.
The article is divided into five sections. The “Unmanned aircraft capture and control via GNSS spoofing” section presents a kind of covert GNSS spoofer, called position deceptive tracking controller. The “Analysis of spoofed parameters via error characteristics” section analyzes the characteristics of the initial state estimated errors that come from GNSS spoofer. Specifically, it deduces the convergence property of these initial errors by analyzing the exponential function of the system matrix. It also makes discussions about the related spoofed parameters. In the “Simulation and analysis” section, experimental results are presented in order to verify the correctness and effectiveness of the proposed theory. The “Conclusions” section concludes the work.
Unmanned aircraft capture and control via GNSS spoofing
The theory and practice of UAV capture and control via GNSS signal spoofing are analyzed and demonstrated by Todd Humphreys and his team. Their designed GNSS spoofer, called the position deceptive tracking controller, has two purposes. One is to force the UAV to far away from a prescribed original path
that state vector
The specific process of GNSS spoofing for UAV is given as follow: 1. GNSS spoofer observes the UAV’s position
where
2. The controller of GNSS spoofer builds a modified PD compensator
to generate
3. The UAV state estimator is Kalman filter that ingests GNSS counterfeit measurements
where
Due to the GNSS counterfeit measurements
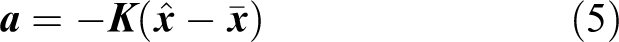
4. The controller of UAV also produces a PD compensator
where
As a result, this control commands make UAV mistake itself for tracking its prescribed original path
As a word, the interconnections between the controller, model, and estimator of the UAV and GNSS spoofer can be represented as a block diagram in Figure 1.
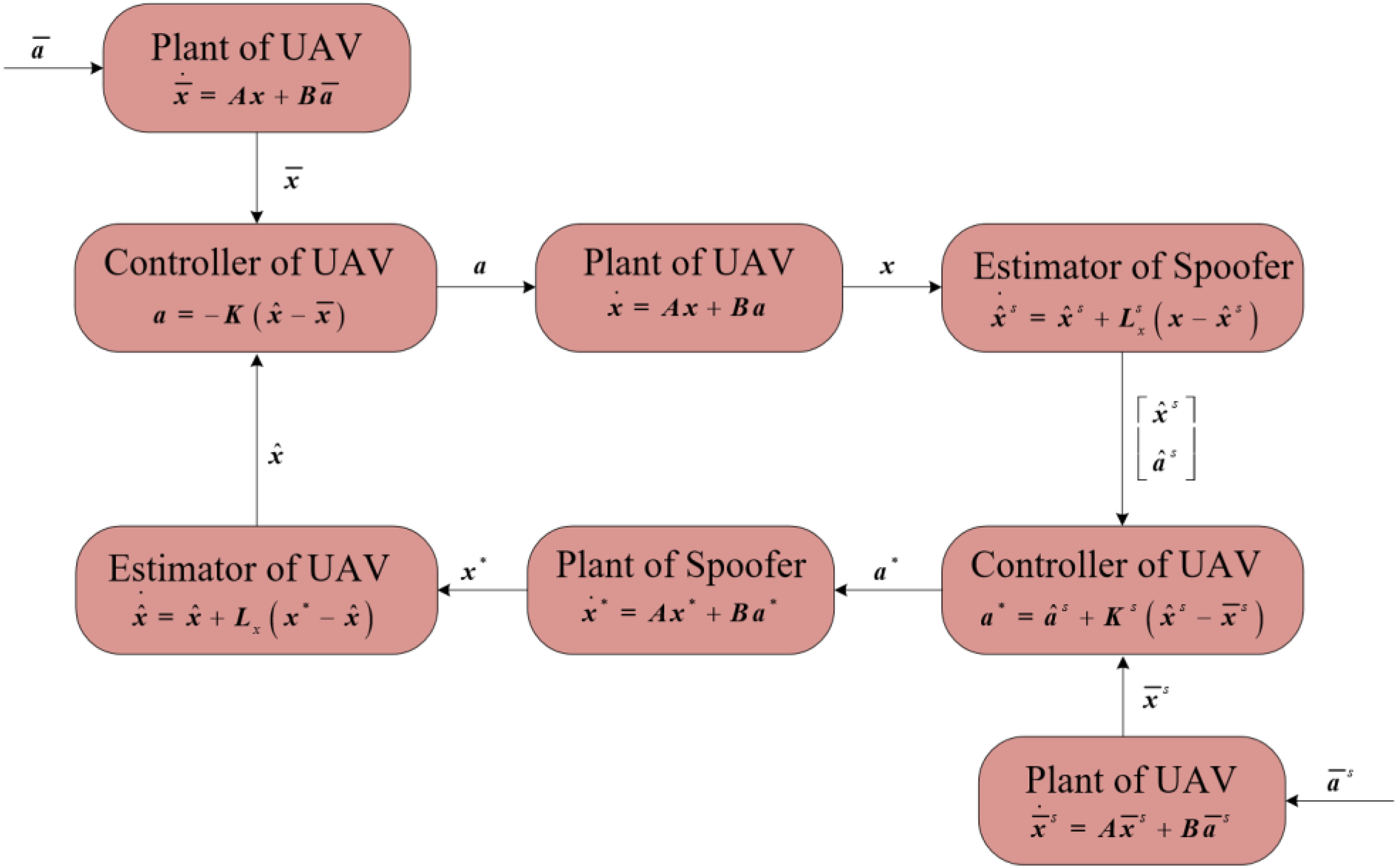
Block diagram of the coupled UAV and spoofer system showing the interconnections between the controller, plant, and estimator. UAV: unmanned aerial vehicle.
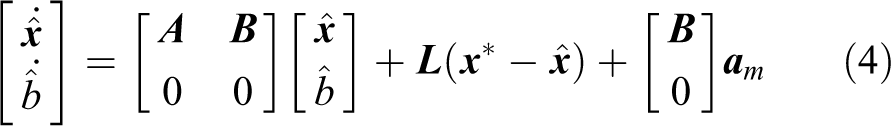
According to Figure 1, the dynamics of the position deceptive tracking controller can be given by
where
Analysis of spoofed parameters via error characteristics
Obtaining the UAV’s position
where
Influence mechanism analysis
Suppose that at the beginning of GNSS spoofing attack, there is an initial state error ξ in observing the UAV state by GNSS spoofer
where
Substitute equation (8) into equation (6), then
where
Subtract equation (6), then
which means that ξ, not only makes
Due to
the bias of
Meanwhile, the state estimator driven by UAV is
and the changes of
However, it is known from equation (6) that
Meaning that no matter how
Based on the above analysis, three conclusions can be drawn as follow: the existence of ξ makes the GNSS spoofing estimator directly generate the initial error disturbance of the existence of ξ causes bias to other state vectors of the position deceptive tracking controller system, such as the existence of ξ not affects the prescribed reference state vector
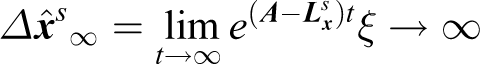
Error convergence of GNSS spoofing estimator
According to the kinematic analysis of the linear time-invariant system, 30 the solution of the state estimator of UAV driven by GNSS spoofer are obtained
then
Comparing equation (12) with equation (13), then
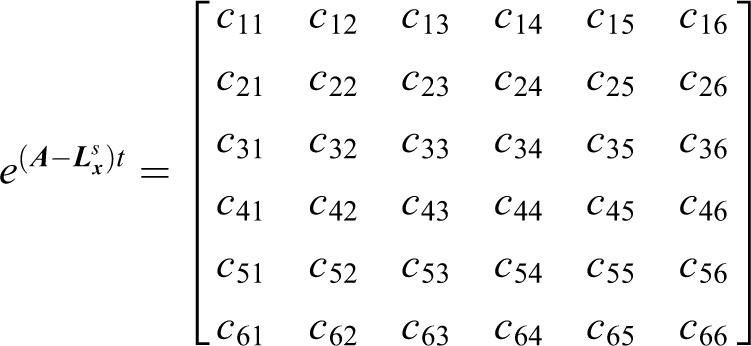
According to the multiplicity of the
For the first case, the eigenvalues of the matrix
And then it determines the transformation matrix
Substitute
where,
If
then
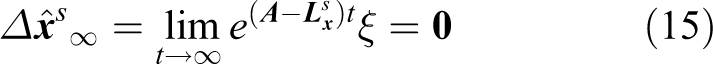
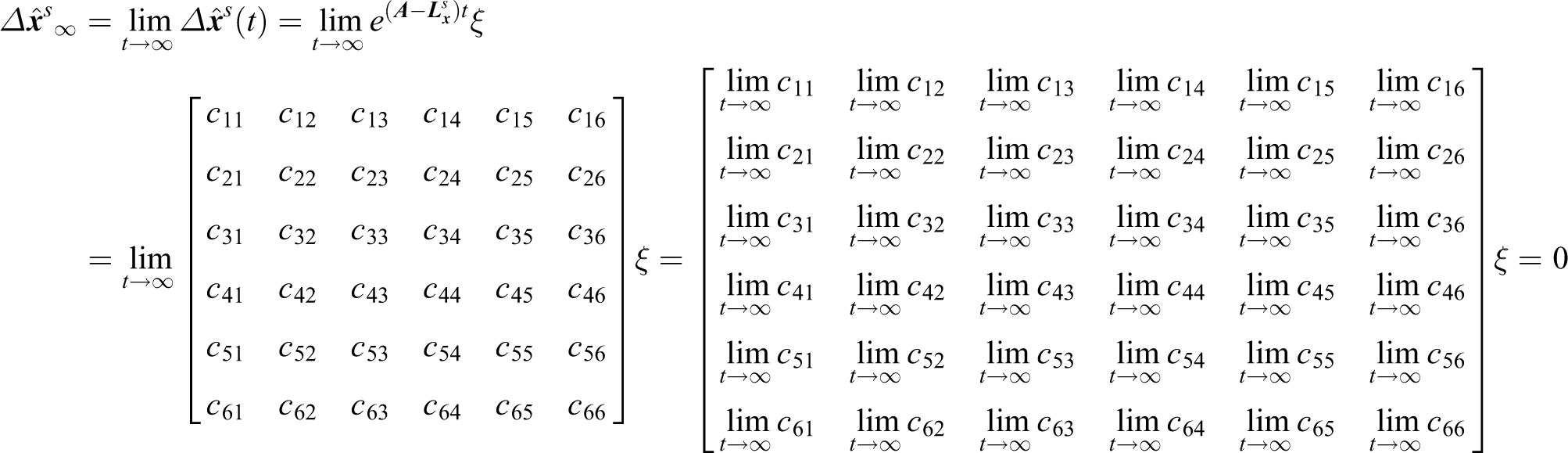
The limit value of each element in
Finally, the limit value of
named as
For the second case, the eigenvalues of
where
Then the arithmetic expression of
where
Due to
the limit value of
namely
Discussion on spoofer parameters
As a third part device independent of UAV, the position deceptive tracking controller estimates the UAV’s state with the initial state error ξ. It is not expected that the existence of this error affects the position deceptive offset on the UAV. In other word, the free trajectory of the initial state error ξ needs to end up at zero.
According to equations (15) and (16), the shape of the free trajectory of the initial state error ξ is uniquely determined by the matrix exponential function of
The matrix
where
where
In a word, the position deceptive tracking controller sets the reasonable parameters of
Meanwhile, the choice of
Simulation and analysis
In order to verify the correctness of the position deceptive tracking controller, and then analyze the influence of parameters setting on this designed controller, three simulation experiments are carried out in this paper. In the first experiment, Table 1 gives the relevant parameters of the position deceptive controller about calculating Ls.
Relevant parameters of the position deceptive tracking controller in the first experiment.

GNSS: Global Navigation Satellite System.
Then

which can make

and
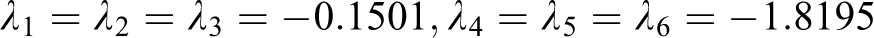
It shows that the parameters set in Table 1 are reasonable. The selection of

Set the prescribed acceleration and the reference spoofed acceleration as

where their corresponding trajectory is obtained by the second integral of the acceleration, like equation (1).
Figure 2 shows the results of the deceptive tracking controller for three-dimensional UAV, consisting of the real state path (red line), the new spoofed path (black line), the estimated state path (green line), and the original path (blue line). Although UAV deviates from the original path and tracks the new path, the estimated state that comes from UAV combined navigation filter output still follows the original path. The results show that utilizing the designed deceptive tracking controller can unconsciously make UAV deviate from the normal path with potentially spoofed GNSS signals, thus achieving UAV spoofing.

Results of the trajectory tracking control for three-dimensional UAV. UAV: unmanned aerial vehicle.
It is assumed that the initial estimated state errors driven by GNSS spoofer have constant errors, namely, position errors are 10 m and velocity errors are 1 m/s. Figure 3 shows the results of the deceptive tracking controller with initial estimated state errors that driven by GNSS spoofer, and Figure 4 gives the deviation curves of each state vectors. Comparing with Figure 2, the addition of initial state errors from GNSS spoofer do not affect the deceptive tracking controller. Meanwhile, due to the addition of smaller errors, the real path (red line) produces small amplitude oscillation at the beginning of GNSS spoofing on UAV. However, the selection of appropriate parameters, including

Results of the deceptive tracking control with initial estimated state errors by GNSS spoofer. GNSS: Global Navigation Satellite System.
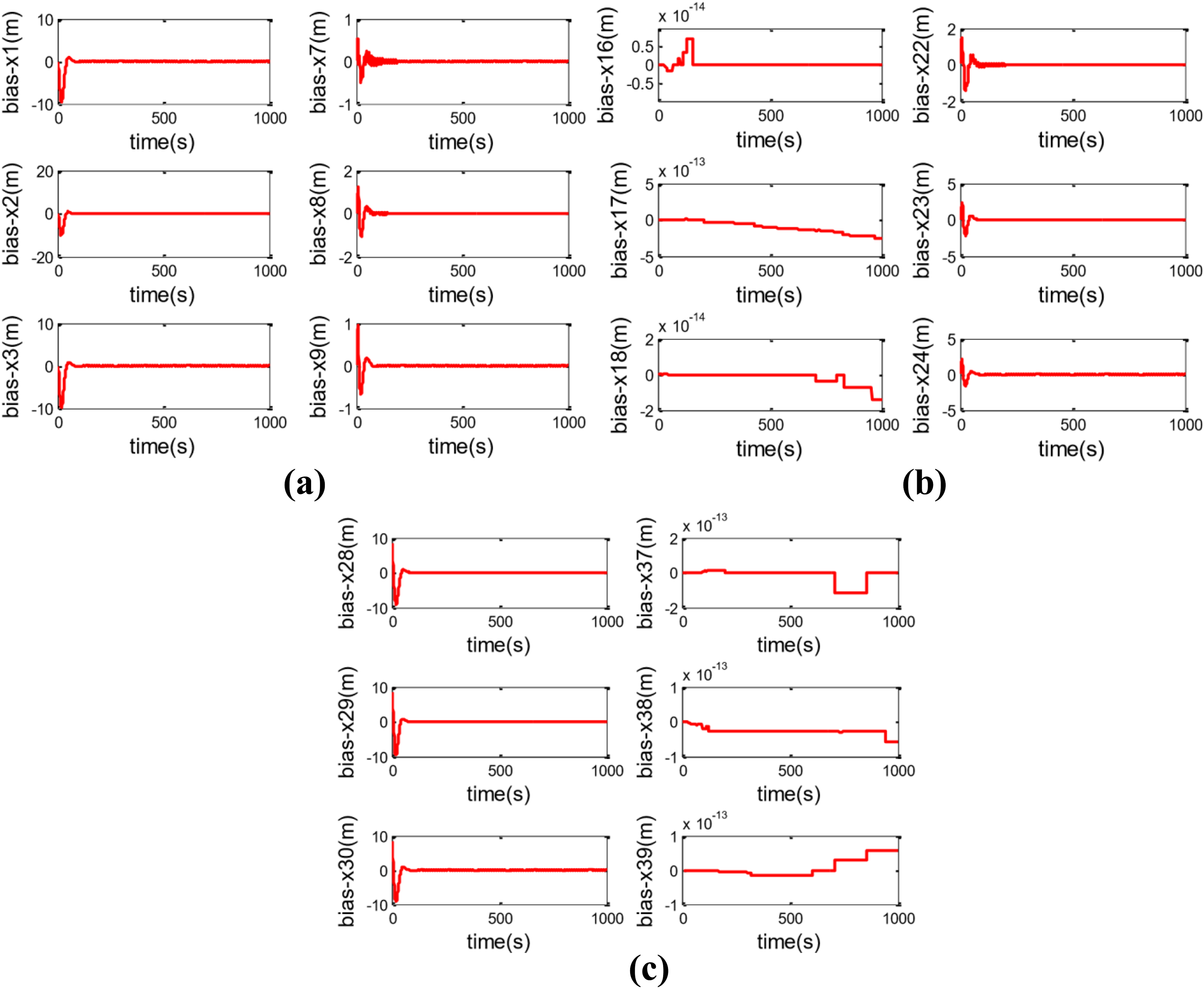
Deviation curves of each state vectors in UAV deceptive tracking control system with initial state errors by GNSS spoofer, where (1) x1∼x3-bias represent the real position bias in the direction of X, Y, Z; (2) x7∼x9-bias represent the estimated position bias by UAV in the direction of X, Y, Z; (3) x16∼x18-bias represent the original reference position bias in the direction of X, Y, Z; (4) x22∼x24-bias represent the spoofed GNSS position bias in the direction of X, Y, Z; (5) x28∼x30-bias represent the estimated position bias by GNSS spoofer in the direction of X, Y, Z; (6) x37∼x39-bias represent the spoofed reference position bias in the direction of X, Y, Z. Note that in Figure 4, it seems that not all the states will converge to 0. According to the conclusion analysis in the “Error convergence of GNSS spoofing estimator” section, it can be seen that the addition of the initial estimated state errors have no influence on the original path and the new spoofed path. It means that, the x16∼x18-bias and x37∼x39-bias are theoretically stable at zero. The curves of x16∼x18-bias and x37∼x39-bias in this figure fluctuate because the vertical coordinate is over amplified, that is, the order of magnitude of 10−13. UAV: unmanned aerial vehicle; GNSS: Global Navigation Satellite System.
The influence of improper parameters on the position deceptive controller is further analyzed. Firstly, the spoofer Kalman gain matrix
Relevant parameters of the position deceptive tracking controller in the second experiment.
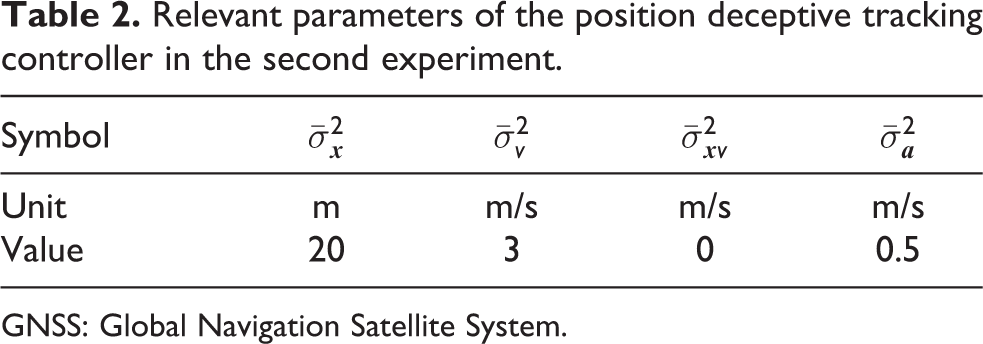
GNSS: Global Navigation Satellite System.
Then
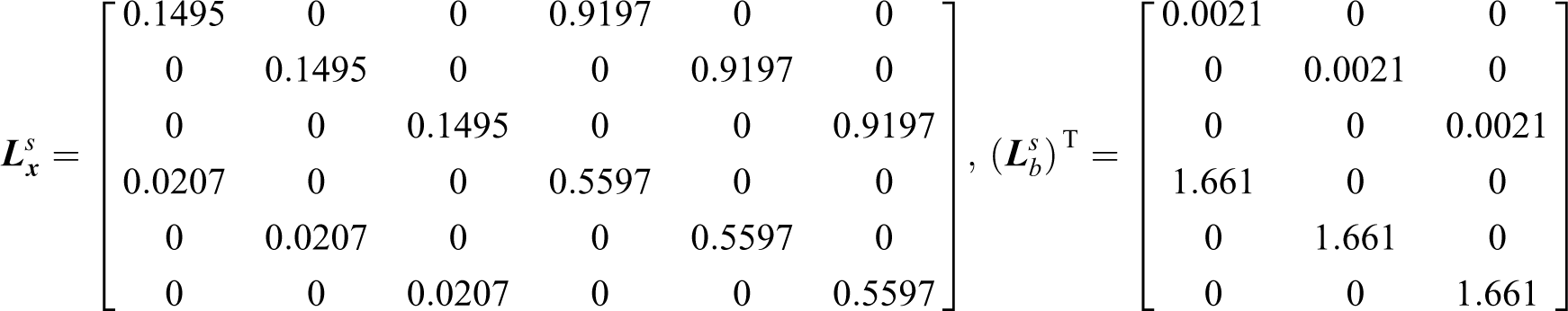
which can make
It shows that the parameters set in Table 2 are unreasonable. It means that the effect of the initial state estimated errors not disappear but diverge with time. The following simulation results in Figure 5 verify this theory.

Deviation curves of each state vectors in UAV deceptive tracking control system with initial state errors by GNSS spoofer, when the spoofer Kaman gain matrix is improper. The expression meanings of the horizontal and vertical coordinates are the same as those of Figure 4. UAV: unmanned aerial vehicle; GNSS: Global Navigation Satellite System.
Secondly, the spoofer control parameter

which can make the eigenvalues of
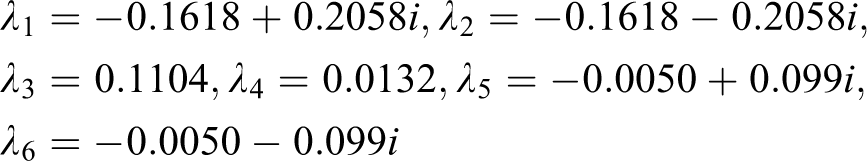
It can be seen that there are two eigenvalues of

Deviation curves of each state vectors in UAV deceptive tracking control system with initial state errors by GNSS spoofer, when the spoofer control parameters are improper. The expression meanings of the horizontal and vertical coordinates are the same as those of Figure 4. UAV: unmanned aerial vehicle; GNSS: Global Navigation Satellite System.
Conclusions
The focus of this article is to study the deceptive tracking controller and analyze the characteristics of the initial state errors to help GNSS spoofer select the spoofer parameters. Simulation results show that setting reasonable spoofer parameters can make the designed deceptive tracking controller achieve good spoof effect, meaning UAV deviate from its original path and follow up a new path. What is more, the existence of the initial state errors inevitably affected the deceptive tracking controller, but this effect will gradually weaken under the influence of the system matrix, thus eventually be eliminated. The performance of the initial state errors is reflected in the spoofing that UAV tracked the new spoofed path with deviations in the beginning and then almost matched the spoofed path over time, and ultimately be spoofed into a preset position and be captured. Conclusions are drawn that a small amount of the initial state errors by GNSS spoofer can be allowed in the practical application of this designed deceptive tracking controller.
Footnotes
Acknowledgement
The authors would like to thank all the editors and anonymous reviewers for improving this article.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was co-funded by the Hunan project on Science and Technology in China (no. 2017R3045) and the National Hey R&D Program of China (no. 2017YFC0601701).