Abstract
The smart grid system enables bidirectional communication between end users and service providers, significantly enhancing service quality. One of its critical tasks is the monitoring and processing of abnormal transaction data. However, the openness and complexity of the network environment make the system vulnerable to a variety of attacks, such as internal data tampering and eavesdropping attacks. Consequently, the storage and communication security of abnormal transaction data pose significant challenges within the architecture and communication framework of the smart grid. To address these issues, this paper proposes a security protection scheme for abnormal transaction data in smart grid system. By employing a private blockchain network composed of consensus nodes, the scheme ensures the integrity and availability of abnormal transaction data. Additionally, the proposed authentication protocol facilitates secure communication among smart meters, consensus nodes, and servers within the blockchain-based smart grid system. Security analyses demonstrate that the proposed protocol effectively mitigates security threats while offering lower computational overhead compared to related protocols.
Introduction
With advancements in microelectronics, information technology, and communication technology, the traditional power grid has progressively transformed into a smart grid system. This evolution enables the seamless integration of energy flow and data management across the entire electricity transmission and distribution process, spanning from power plants to end users.1–3 The smart grid system facilitates centralized management of electricity generation, transmission, and consumption data, thereby enhancing operational efficiency, improving grid stability, and elevating service quality.4,5 For instance, sensors deployed within the grid collect real-time data on its operational status, while cloud servers process this data to monitor grid performance and evaluate potential security risks. This interconnected infrastructure underscores the critical role of data-driven insights in ensuring the resilience and reliability of the smart grid system.
The illegal use of electricity by end users poses a significant threat to the stable operation of smart grid systems. To address this issue, abnormal transaction data monitoring has become a widely adopted approach. Power management departments increasingly rely on information technology to enable real-time analysis and processing of abnormal transaction data, aiming to enhance the operational efficiency and reliability of smart power systems.
However, the continuous expansion in the number and diversity of end users has added complexity to abnormal transaction data management, introducing new challenges to the safe operation of the smart grid, such as data opacity and centralized control. 6 The centralized architecture of the smart grid, which relies heavily on third-party cloud servers, assumes the security of these servers. However, this assumption is often unrealistic, as it introduces security risks, including single points of failure, data loss, and data tampering.7,8 Blockchain, as a distributed and tamper-resistant architecture, offers a promising solution to these challenges by ensuring data integrity and availability in the smart grid system. This decentralized approach not only mitigates single-point attacks on consensus nodes by adversaries but also prevents insider threats from tampering with data.9,10
In blockchain-based smart grid systems, effective communication between cloud servers, consensus nodes, and end users is essential for sharing data.11,12 Given the openness and complexity of the network environment, it is critical to prevent adversaries from impersonating legitimate entities and to ensure the security of abnormal transaction data communication. 13 For instance, an adversary impersonating a smart meter to transmit false abnormal transaction data to consensus nodes could lead to inaccurate state estimations. Therefore, designing an authentication protocol is imperative to achieve secure communication among entities in a blockchain-based smart grid system.
Public key infrastructure is a widely used encryption technology that employs certificates issued by trusted certificate authorities to facilitate mutual authentication between cloud servers and users. 14 However, centralized authentication protocols face challenges in adapting to the distributed nature of blockchain architectures, as they incur high certificate management costs.15,16 Additionally, existing authentication protocols in smart grid systems often exhibit vulnerabilities, such as susceptibility to denial-of-service (DoS) attacks and replay attacks. 15 Furthermore, the smart grid's high real-time requirements, coupled with the limited computational and communication resources of end users’ smart meters, necessitate lightweight authentication protocols to minimize security risks arising from communication delays.
To address these challenges, this paper proposes a security protection scheme for abnormal transaction data in smart grid systems. The main contributions are as follows:
A blockchain-based smart grid system architecture has been designed to achieve data availability and integrity. The consensus node maintains a blockchain ledger that records abnormal transaction data collected by the smart meters. An efficient authentication protocol for blockchain-based smart grid system is proposed. The smart meters use lightweight XOR operation and hash function to achieve mutual authentication with consensus nodes and cloud server.
Related work
Recently, a growing number of authentication schemes for smart grid systems have been proposed to enhance their security and efficiency.
In 2019, Kumar et al. 17 introduced a lightweight authentication and key agreement scheme for smart metering infrastructure, aiming to secure communication between smart meters and the neighborhood area network. However, Yu et al. 18 identified that Kumar et al.'s scheme could not withstand session key disclosure attacks. To address this vulnerability, Yu et al. proposed a privacy-preserving lightweight authentication protocol that leverages pseudo-identities and secret parameters to achieve anonymity. Later, in 2021, Irshad et al. 19 revealed that Yu et al.'s protocol was susceptible to offline identity-guessing and DoS attacks. To mitigate these threats, they developed an improved authenticated key agreement scheme.
To strengthen communication security between smart meters and service providers, Srinivas et al. 20 introduced an anonymous signature-based authenticated key exchange scheme. This protocol demonstrated resilience against multiple attacks, including replay and impersonation attacks. In 2020, Aghapour et al. 21 proposed a broadcast authentication scheme utilizing a one-way hash function, coupled with a one-time pad system that negotiates a fresh key for each time interval. Subsequently, in 2021, Sureshkumar et al. 22 presented a mutually authenticated key establishment protocol for secure communication between smart meters and service providers. Similarly, Tanveer et al. 23 developed a robust access control protocol for IoT-enabled smart grids, supporting mutual authentication and session key agreement while addressing resource constraints.
Identity management serves as the cornerstone of authentication schemes. In 2022, Dehalwar et al. 24 proposed a blockchain-based self-sovereign identity and authentication technique to tackle identity leakage issues in smart grids. Xiang et al. 25 introduced an authentication key agreement scheme integrating the Paillier cryptosystem and zero-knowledge proofs to ensure the anonymity of authentication messages. In the same year, Chaudhry et al. 26 designed a privacy-preserving authentication scheme utilizing elliptic curve cryptography, providing resistance against impersonation and physical capture attacks.
In 2023, Li et al. 27 proposed a blockchain-based multi-domain authentication mechanism to secure power grid devices, employing blockchain to record device certificate hashes and reduce storage requirements. Similarly, Ayub et al. 28 presented a privacy-centric blockchain-based authentication solution to enhance consumer-centric security and ensure the integrity of demand response data in smart grids.
In 2023, Shahidinejad et al. 29 proposed a computationally efficient blockchain-based key management protocol, offering forward secrecy, conditional anonymity, and straightforward smart meter revocation. Concurrently, Pei et al. 30 developed a blockchain-based identity authentication and data aggregation scheme to facilitate secure, two-way communication between utility companies and electricity consumers. These advancements collectively enhance the robustness and security of smart grid authentication frameworks.
System model
In this section, we first propose the network model of blockchain-based smart grid system. Then, we describe the threat model used in proposed protocol.
Network model
In the proposed network model, we consider the four kinds of entities: sever, blockchain, grid gateway node, and end user, as shown in Figure 1.
Sever: It is a fully trusted entity in the authentication protocol, responsible for publishing system parameters and registering consensus nodes and end users. The server has strong computing capability, accepts data from the end users, processes and analyzes data, and sends the results to the consensus nodes.31,32 It also uses data collected by grid sensors to optimize the energy generation, transmission, and distribution processes and makes the final decision. Blockchain: In order to reduce the management overhead of data, this study adopts a private chain network composed of a large number of consensus nodes. Only nodes authorized by the server can join the blockchain to execute the consensus mechanism. The blockchain ledger maintained by the consensus node has the ability to prevent data from being tampered with and lost, and its main role is to record the data uploaded by the end users and the command data issued by the server. The certainty of data plays an important role in the stable operation of the smart grid system. Grid gateway node: It is an important component of the power transmission network that carries the power from the transmission system to the end users. It is also an information relay node with strong communication capability, responsible for the communication between the server and end users, and the communication between the consensus node and end users. It does nothing with the forwarded message. Its trust and security issues are not considered in this study. End user: Each end user is equipped with the smart meter with limited resources, which is responsible for monitoring electricity consumption and taking action against dangerous situations. Because the communication capability of the smart meter is weak, the data sent to the server and consensus node is forwarded by the gateway via the public channels. In addition, the design of authentication protocol should consider the characteristics of limited computing resources of smart meter and adopt lightweight encryption algorithm.

Network model of blockchain-based smart grid system.
Threat model
We utilize the widely used Dolev–Yao (DY) threat model to verify the security of the proposed protocol against various types of attacks.33,34 During the authentication phase, data is transmitted among entities via the public channels. Under the DY threat model, the adversaries can intercept, steal, modify, and replay transmitted messages. The extracted message is used by the adversaries to infer power grid privacy data or infer session key. Moreover, the adversaries can also impersonate legitimate smart meters and send forged data to server and consensus node.
Proposed authentication protocol
In this section, we propose an efficient authentication protocol for blockchain-based smart grid system, which includes initialization, registration, and authentication phase. The notations used in the proposed protocol are shown in Table 1.
Notation used in proposed protocol.

Initialization phase
The server chooses a random number as the master key
Registration phase
During the registration phase, the consensus node and smart meter are registered by the server and obtain the authentication parameters. These authentication parameters can be further used in the mutual authentication.
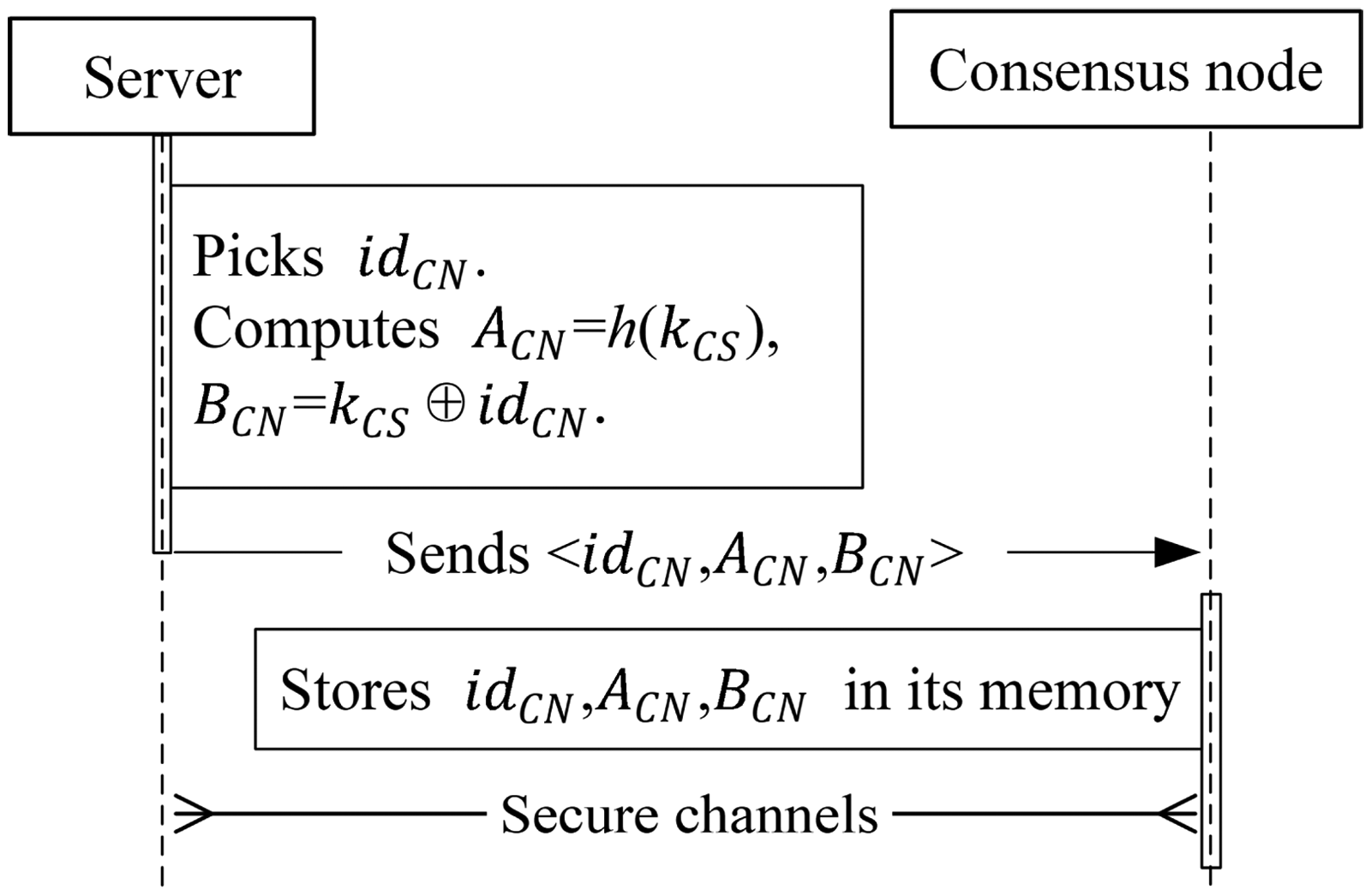
Consensus node registration process in the secure channels.

Smart meter registration process in the secure channels.
Authentication phase
1. The smart meter generates the authentication parameters. Initially, the smart meter picks the parameter
2. Upon receiving the parameters tuple <
Smart Meter and Consensus Node Generate Authentication Requests

3. On the receipt of the parameters tuple from the consensus node, the server checks the validity of the timestamps
If the condition satisfies, the server picks the parameter
Server Generates Session Key

4. Upon receiving
5. When
Smart Meter and Consensus Node Generate Session Key

Secure analysis
In this section, we introduce the security of proposed protocol against the hypothetical threat model and compare its security features with other related protocols.
Comparison of security features.

Security feature analysis
We discuss the security features of the protocol, including mutual authentication, session key agreement, anonymity, message integrity, resist eavesdropping attack, resist replay attack, resist offline password guessing, and resist impersonation attack.
Functionality comparison
Table 3 shows the comparison of security features between the proposed protocol and related protocols. Moghadam et al.'s 35 protocol only supports session key agreement and does not support mutual authentication among entities. In Zhang et al.'s 36 protocol and Mehta et al.'s 37 protocol, message integrity and timeliness verification mechanisms are not considered, so the protocol is also unable to resist impersonation attack. In addition, it can be seen that our proposed protocol has more security features and can resist a variety of well-known attacks.
This is a sample of a table title computation cost analysis of three protocols.

Performance evaluation
In this section, we evaluate the proposed protocol and compare it with related protocols35–37 from the perspectives of computation cost and communication overhead.
Computation cost
The proposed protocol is simulated based on Python program on the Ubuntu 18.04 workstation with Intel Core i7–10700 CPU @2.9 GHz and 8 GB memory. We use
In the authentication phase of the proposed protocol, the smart meter performs 16 XOR operations, one symmetric encryption, and five hash functions; the computation cost required for the smart meter is 16
There is less research on blockchain-based for smart power grid authentication protocols. This study only discusses the computation cost comparison of the smart meter and server. In Moghadam et al.'s 35 protocol, the smart meter performs two symmetric encryptions and nine hash functions, and the server performs two symmetric encryptions and eight hash functions. In Zhang et al.'s 36 protocol, the smart meter performs seven symmetric encryptions and one hash function, and the server performs three symmetric encryptions and nine hash functions. Table 3 lists the computation cost analysis between the proposed protocol and other two related protocols in the meter and server. In Mehta et al.'s 37 protocol, the smart meter performs two symmetric encryptions and two hash functions, and the server performs two symmetric encryptions and two hash functions.
The computation cost comparison results of the proposed protocol and related protocols are shown in Figures 4 and 5 respectively. It can be seen from the figure that the proposed protocol has the lowest computation cost of smart meter and server.

Computation cost comparison for smart meter.

Computation cost comparison for server.
Communication overhead
As per the Meng et al.'s 38 protocol, we assume that the size of a random number, the size of a time stamp, and the size of hash function output are 32 bytes, 4 bytes, and 32 bytes, respectively. The size of AES-128 symmetric decryption/ encryption algorithm is a multiple of 16 bytes.
In proposed scheme, the authentication parameters <
In Moghadam et al.'s
35
protocol, the smart meter sends the parameters <
In Zhang et al.'s
36
protocol, the smart meter sends the parameters <
In Mehta et al.'s
37
protocol, the smart meter sends the parameters <
Table 4 illustrates the communication overhead comparison between the proposed protocol and other related protocols. From this table, it is clear that our protocol has the lowest communication overhead.
Communication overhead comparison.

Conclusion
This paper proposes a security protection scheme for abnormal transaction data in smart grid system. By combining blockchain with the smart grid structure, the blockchain ledger maintained by consensus nodes ensures the integrity and availability of abnormal transaction data. In addition, the authentication protocol achieves communication security among entities in the power grid system. Finally, the security analysis and performance evaluation demonstrate that the proposed protocol provides strong security guarantees while achieving lower computational costs and communication overhead compared to related protocols.
Footnotes
Acknowledgement
This work was partially supported by the National Natural Science Foundation of China under Grants 62472168, 62072170, and 61976087, the Science and Technology Project of the Department of Communications of Hunan Provincial under Grant 202101, the Key Research and Development Program of Hunan Province under Grant 2022GK2015, and the Hunan Provincial Natural Science Foundation of China under Grants 2021JJ30141 and 2024JJ6066, and the Research Foundation of Education Bureau of Hunan Province of China under Grant 23B0288.
Author contributions
Conceptualization and writing original draft: Lijun Xiao and Dezhi Han. Editing: Xiangwei Meng and Meiguo Ke. Investigation and validation: Dacheng He.
Declaration of conflicting interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Ethical statement
I certify that this manuscript is original and has not been published and will not be submitted elsewhere for publication while being considered by editors. The study is not split up into several parts to increase the quantity of submissions and submitted to various journals or to one journal over time. No data have been fabricated or manipulated (including images) to support your conclusions. No data, text, or theories by others are presented as if they were our own. The submission has been received explicitly from all co-authors. And authors whose names appear on the submission have contributed sufficiently to the scientific work and therefore share collective responsibility and accountability for the results. This article does not contain any studies with human participants or animals performed by any of the authors.
Funding
The authors disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was partially supported by the National Natural Science Foundation of China under Grants 62472168, 62072170 and 61976087, the Science and Technology Project of the Department of Communications of Hunan Provincial under Grant 202101, the Key Research and Development Program of Hunan Province under Grant 2022GK2015, and the Hunan Provincial Natural Science Foundation of China under Grant 2021JJ30141.
Data Availability Statement
Data sharing not applicable to this article as no datasets were generated or analyzed during the current study.
Informed consent
Informed consent was obtained from all individual participants included in the study.
