Abstract
With the rapid development of industrial Internet of Things, the secure transmission of nodes in Internet of Things is easily attacked by malicious nodes at all times, thereby causing a great threat to network performance and security of industrial Internet of Things. To improve the security and success rate of data transmission in industrial Internet of Things environment, this work proposes a data transmission scheme based on the weighted security partition model by considering the requirements of a hostile industrial environment. The weighted security partition of the nodes determines the secret distribution model. On this basis, a secure authentication scheme for network transmission is proposed for industrial Internet of Things to prevent the data from being tampered by malicious industrial nodes. Authority access control is added to the authentication scheme. The network access authority of users is used to eliminate the access of malicious users. Finally, the simulation experiments and performance evaluation are conducted and compared with other secure transmission algorithms. Results show that, by comparing to low-energy adaptive clustering hierarchy and distributed data secure transmission, the transmission rate of the proposed algorithm has increased by 35% and 25%, and the lifetime has increased by 34.3% and 37.3%, respectively.
Keywords
Introduction
With the rapid development of industrial Internet of Things (IoT), the security of data transmission in industrial networks becomes increasingly important. IoT is a double-edged sword; it either provides convenience or causes numerous potential security risks. For example, the first case of malicious IoT attack occurred in 2014. The hacker was able to control more than 100,000 intelligent home appliances under IoT and construct a malicious botnet. About 750,000 phishing emails are sent to victims without precaution. IoT is an expansion of the Internet; thus, it faces the same security problems as the Internet. Although few IoT security events with large-scale and serious influence exist, the security situation of IoT has fundamental changes. The computational capability of embedded terminals is greatly improved, and the operating system is increasingly open. Hence, the security problems have worsened. The users are the service objects of IoT. If the security of user privacy cannot be ensured, then the practical application of IoT will be suspected. The foundation to ensure the security of user privacy should guarantee the completeness, correctness, and confidentiality of data and data transmission. IoT originates from the Internet. Hence, it faces many security problems. With its own features and limitation, security becomes increasingly intractable. 1
The expansion of IoT size has resulted in additional security risks. To avoid this issue, scholars2–6 have deeply analyzed the security problems in industrial IoT and proposed solutions to ensure the practical application of industrial IoT. The traditional mobile ad hoc network (MANET)7–9 depends on the infrastructure. However, the nodes in IoT use the store-carry-forward routing in communication. The issues of network division and time delay in traditional networks can be addressed in IoT. Therefore, IoT is suitable in hostile industrial environment without infrastructure.10,11 IoT only requires the calculation of the local information and selects the suitable next-hop node for forwarding the data to the destination node. Consequently, the industrial IoT is superior in a hostile environment. 12
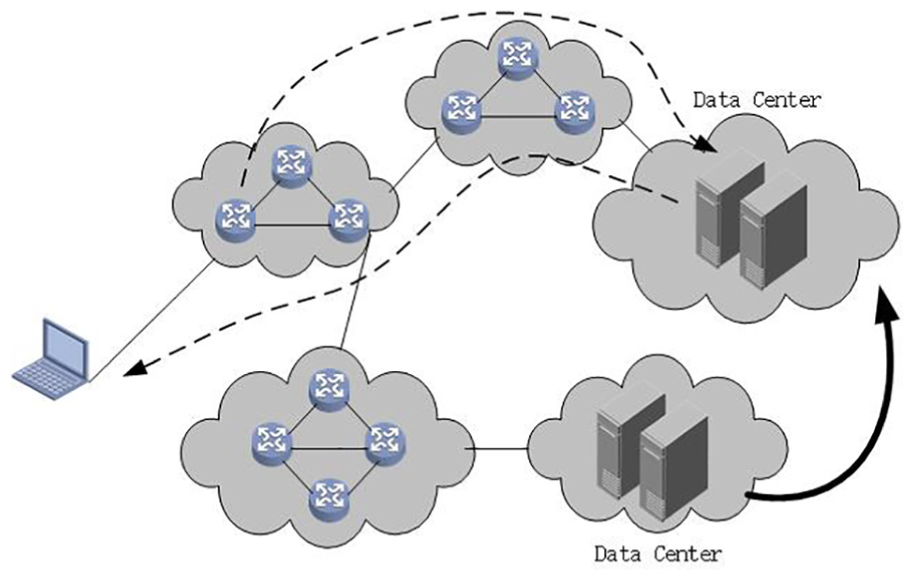
As shown in Figure 1, the industrial network environment is vulnerable to network attacks and threats from selfish and malicious nodes. Data forwarding in IoT depends on the mobility of nodes, and the identity of the nodes is not authenticated by any management institution. In the industrial environment without any security mechanism, the industrial nodes cannot judge the security of the next-hop node. Such a condition easily causes privacy leakage among industrial users. Moreover, the resource abuse of industrial nodes will cause IoT system crash. On this basis, researchers have introduced the encryption mechanism in IoT to ensure secure data transmission to the destination node. To guarantee the identity and legality of the industrial nodes and the authenticity and reliability of the message source, legal users can decrypt the message only with a key. Therefore, identifying the manner in which the encryption mechanism is used to avoid the influence of malicious node in industrial networks should be deeply researched in secure data transmission techniques.

The secure transmission flow in the industrial IoT.
In this work, we propose a data transmission method on the basis of the weighted security partition model to improve the security and success rate of data transmission in industrial IoT environment. The main contributions are listed as follows: (1) the weighted security partition of the nodes determines the secret distribution model; (2) a secure data transmission scheme is proposed to prevent the data from being tampered by malicious industrial nodes; (3) authority access control and network access authority of users are utilized to eliminate the access of malicious users.
Related work
In recent years, IoT techniques have been used extensively in the industry. Secure data transmission in industrial IoT has been attracting increasing attention. The secure protocol in the traditional network is not suitable in industrial IoT due to its differences. Therefore, routing protocols for industrial IoT must be designed. Substantial private user information exists in the routing protocols in industrial IoT. Once attacked, the attackers can pretend to be normal users and receive the transmitted data. This situation will cause considerable damage to the industrial network environment. Hence, researchers are also concerned with privacy protection in industrial IoT.
In industrial IoT, the source node should obtain the context attribute of the destination node before transmitting data. Substantial privacy information exists in the context, which should also be protected (e.g. the information of a node is sent to the next-hop sensor node after encryption). Mai and Azer 13 proposed the privacy leak problem based on the node context and infect forwarding. Identity encryption was used to solve this problem. The context of the nodes was substituted by a group of attribute values. The principle was that the relay node compared its context attribute with that in the destination node. The data were transmitted if both attribute values exceed a threshold. The relay node could not obtain other attribute information, thereby ensuring the privacy of the destination node. In Ramanathan et al., 14 a public encryption algorithm was proposed based on keyword search. The encryption algorithm could be used to set a threshold for the attribute of the node. The relay node could obtain the data when its context attributes satisfy the context attribute threshold of the destination node. The relay node could not obtain the attributes of the destination node when forwarding the data.
A content-based privacy protection algorithm was proposed in Burgess et al. 15 The routing table of a relay node was created based on the receiver. The relay node in the industrial network should encrypt the data, create the routing table, and query the encrypted routing information. The authors in Yao et al. 16 analyzed the privacy threats in the industrial network and proposed a solution to confuse the friend list of the sender. In this case, the attacker could not obtain the list and the original data.
Industrial IoT is different from the traditional wireless network. The industrial nodes are randomly distributed. Hence, no complete path exists between the source and destination nodes. 17 IoT has some features of a delay-tolerant network (DTN) because it originates from the DTN and the MANET. However, when the network is interrupted, the DTN regards it as a network fault, while IoT considers it normal and reconnects them using the node mobility. As a new self-organized network, the industrial IoT has a good prospect; however, many problems remain to be addressed.
Research on secure data transmission of IoT can be classified into several aspects. Conti et al.
18
proposed a common power control algorithm. All the nodes send data with the same power. COMPOW uses an agency at the network layer and compares the disperse power provided by the hardware. In this case, the minimum power to ensure the network connectivity will be found. Each node starts with the optimal power control and determines its own decision of transmission power. In this algorithm, the node degree is the number of neighboring nodes with a hop to the current node. The protocol based on the node degree initially sets the upper and floor requirement. The power of a node is dynamically adjusted to make its degree within the range of the requirement. In Song and Kotz,
19
all the nodes in the network used the maximum power to send data and form a topology graph
Data forwarding flow in IoT.
Region partition control scheme
Data transmission model
In order to verify the relationship between region partition and efficiency of data transmission in industrial IoT, a region classification of the nodes is the protocol. It can ensure the dynamic connectivity of the IoT topology structure. 30 To make the data transmission in industrial IoT reliable and stable, we assume that there are lots of industrial nodes, which can be covered by a circle in the factory. The industrial network is a static network with a high density. The base station is usually at a fixed position. So, it will not consider the fast mobility of the industrial nodes. In the initial state, we can divide the data transmission region.31–33
In the network transmission model of IoT, the coevolution is divided into three stages: subspace partition, selection of subspace adaption function, and subspace mutual collaboration. The neighboring region partition model is much important to keep the variety of population in coevolution. In this section, we assume that the industrial node selects the next-hop node in the forward neighboring region. A new secure transmission model based on neighboring region partition is proposed. The data transmission between regions is shown in Figure 3.
Given a security coefficient
The key generation center
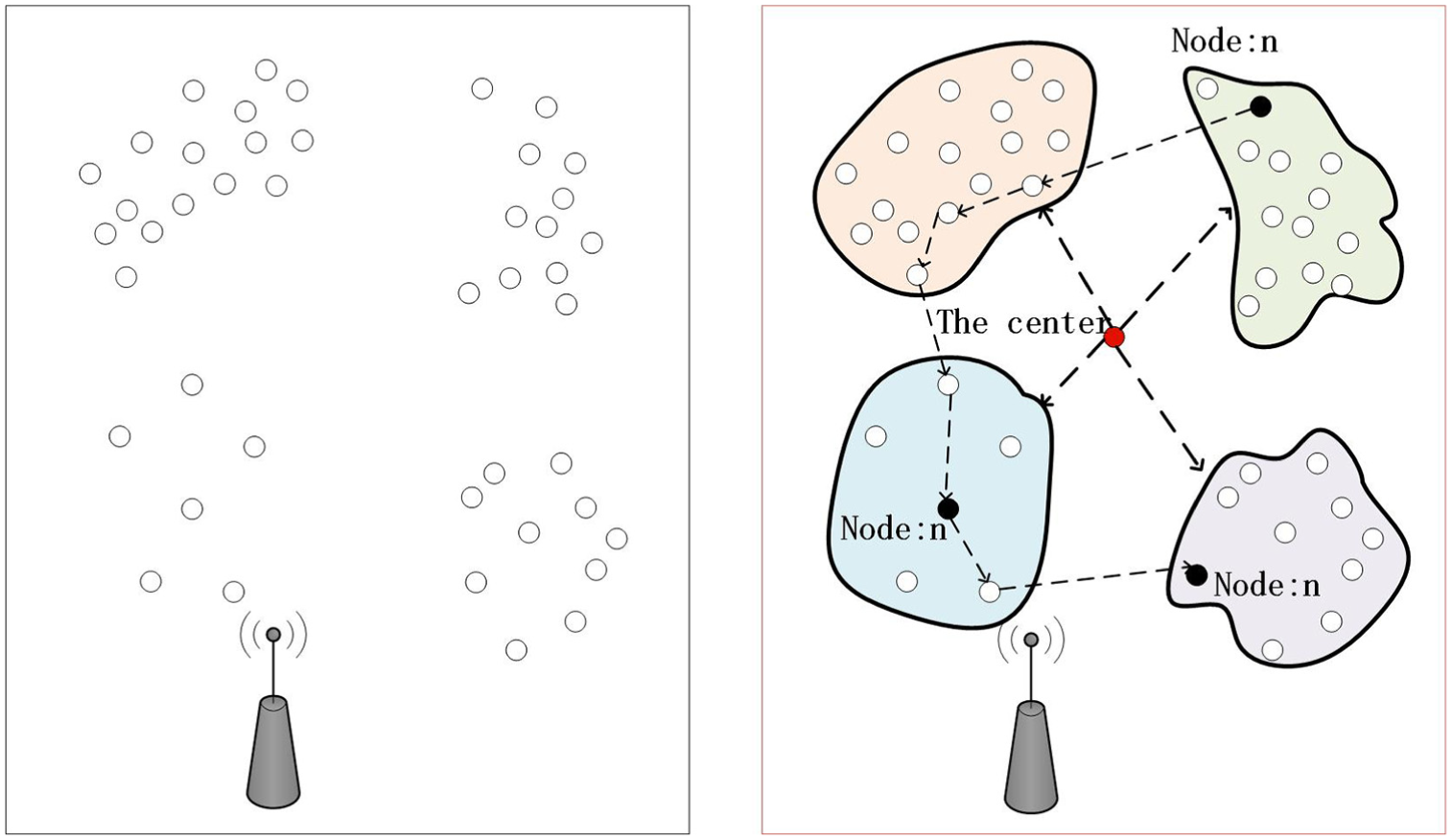
Data transmission between regions.
The security coefficient
Before data transmission, the identity of user


The private key generation model
Assume that the identity of a user is a bitstring with the length of

The encryption model
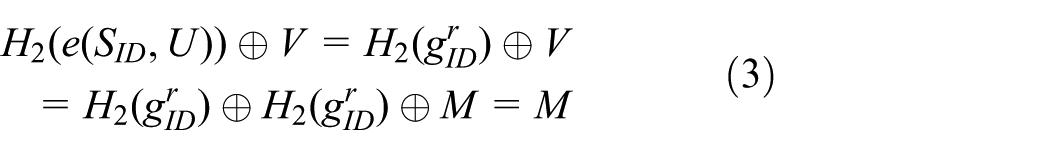
The message
The decryption model
The receiver uses the private key

Identity authentication protocol
This section will present a two-way anonymous identity authentication protocol. This protocol includes the initialization phase, registration phase, and the authentication and key update phase. All clients have unique identity.
Initialization phase
In this agreement,
Registration phase
Client registration
During client registration in
Server registration
During server registration in
Authentication and key update phase
At this stage, the client and server will authenticate the identity by using a bidirectional anonymous way, as illustrated in Figure 4.

Authentication and key update phase.
The implementation process is as follows:
The node partitioning algorithm in IoT
Weighted partition
After the industrial network is created, each sensor node in the factory will construct a reasonable communication region. As shown in Figure 5, the cluster head

The region partition of the nodes.
In this section, we use the concept of forward region and propose a new weight partition model based on the unit circle communication. As shown in Figure 6, the model divides the one-hop neighboring region of node
Two tangents are constructed from the sink node to the circle
Two line segments
The regions of


The region partition for industrial nodes.
According to the spatial distribution of node
After that, the region of the one-hop neighboring node
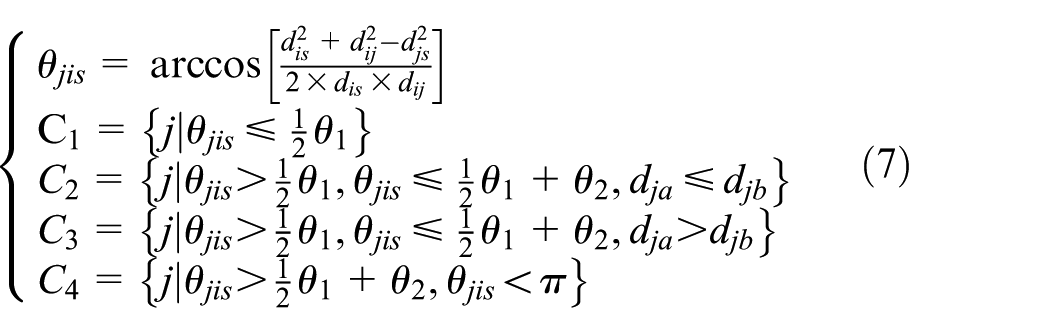
To find the optimal next hop of node
Node frequency control
When the number of nodes

The node weight is the number of nodes with the distance to a node
Secure partition of the weight region
The industrial IoT constitutes a reliable server and the industrial users. The reliable server is the center for key generation and does not have to be on-line all the time. The reliable server selects an attribute set for the users and generates a private key about the user identity for the user. The key will be sent to the user via a secure channel. The public key is generated by the initial module and exposed to all users. The reliable server is the only part trusted by all entities. All the weight partition nodes in the system are users including the sender and the receiver. Since malicious users may exist in IoT, the sender will encrypt the plain message before transmission. The message will be decrypted by the receiver. A large prime number

Here,

Here,
In this algorithm, the working time of the nodes in the wireless region is


In the data transmission scheme based on weighted partition,

Here,
The secret key generation center selects an attribute set
In the data transmission, the weighted partition function has the inputs of a message

In the secure data transmission scheme, the key generation center allocates a private key to the newly added user after the weight partition. The users can interact with each other without the participation of the third party. The secure authentication based on weight partition substitutes the password authentication in traditional encryption and prevents the malicious nodes from forwarding data. The security of data transmission is greatly enhanced.
In order to verify security, some regular attacks are simulated. The identity of attackers should be determined before attacks. An attacker
The experiments and performance comparison
Simulation parameters
In this experiment, the ONE simulator is used for simulation. The results are then shown by figures in MATLAB. The selfish node and malicious node will affect the normal operation of IoT. To verify the ability of the proposed DTSW against the malicious nodes, we conduct a series of experiments. Suppose that all the sensors are deployed within a square area of 4.5 km × 3.4 km. The ordinate of the sink node is (450M, 450M). The sink node is assumed to be inexhaustible. The detailed parameters are listed in Table 1.
Network simulation parameters.

Network lifetime
The performance evaluation metrics in industrial IoT include lifetime, network delay, and throughput. This work focuses on low energy consumption and prolonging the network lifetime. In this work, we select the following algorithms for comparison: low-energy adaptive clustering hierarchy (LEACH) 2 and distributed data secure transmission (DDST). 6 We adjust the parameters to make each algorithm run for the same period. In this case, the running rounds of the algorithm can be used to evaluate the running time and the overhead.
The number of surviving nodes can reflect the overall performance of the network. If the number of surviving nodes is less than a threshold, the network will be broken down.
The energy consumption is another metric to evaluate performance. Since the energy of the industrial sensor nodes is limited, it is important to prolong the network lifetime by saving the energy.
In this experiment, we evaluate the three algorithms under the same conditions. The external factors are the same except the algorithm principle. The experiments are conducted when the numbers of nodes in the network are 200, 400, 800, and 1600. The results are compared to those of DDST and LEACH, as shown in Figure 7.

The comparison of surviving nodes: (a) 200 nodes, (b) 400 nodes, (c) 800 nodes, and (d) 1600 nodes.
Figure 7 shows the surviving node in each round. The experiments are conducted under the same conditions.
Figure 7(a) shows the result when the number of sensor nodes is 200. In the 80th round, the surviving nodes of LEACH, DDST, and DTSW are, respectively, 162, 174, and 179. The DTSW algorithm increases the surviving nodes, respectively, by 10.5% and 2.9% in comparison with LEACH and DDST, respectively. In the 392nd round, the nodes in LEACH will be dead. In Figure 7(b), in the 200th round, the numbers of surviving nodes of LEACH, DDST, and DTSW are, respectively, 372, 355, and 392. The DTSW algorithm increases the surviving nodes, respectively, by 5.37% and 10.4% in comparison with LEACH and DDST. In the 992nd round, all the nodes of LEACH are dead but the there are some surviving nodes in DTSW. In Figure 7(c), in the 400th round, the surviving nodes of LEACH, DDST, and DTSW are, respectively, 684, 167, and 791. The DTSW algorithm increases the surviving nodes, respectively, by 15.6% and 78.9% in comparison with LEACH and DDST. In Figure 7(d), in the 1000-th round, the number of surviving nodes of LEACH is 984 and that of DTSW is 1322. The DTSW algorithm increases the surviving nodes, respectively, by 34.3% and 37.3% in comparison with LEACH and DDST.
We also evaluate the rate of energy consumption of the three algorithms, and the comparison results are shown in Figure 8. By comparing to DDST and LEACH, the proposed DTSW algorithm achieves the lowest energy consumption rate. Namely, DTSW has more remaining energy in each round than those of LEACH and DDST. So, DTSW is the most energy efficient.
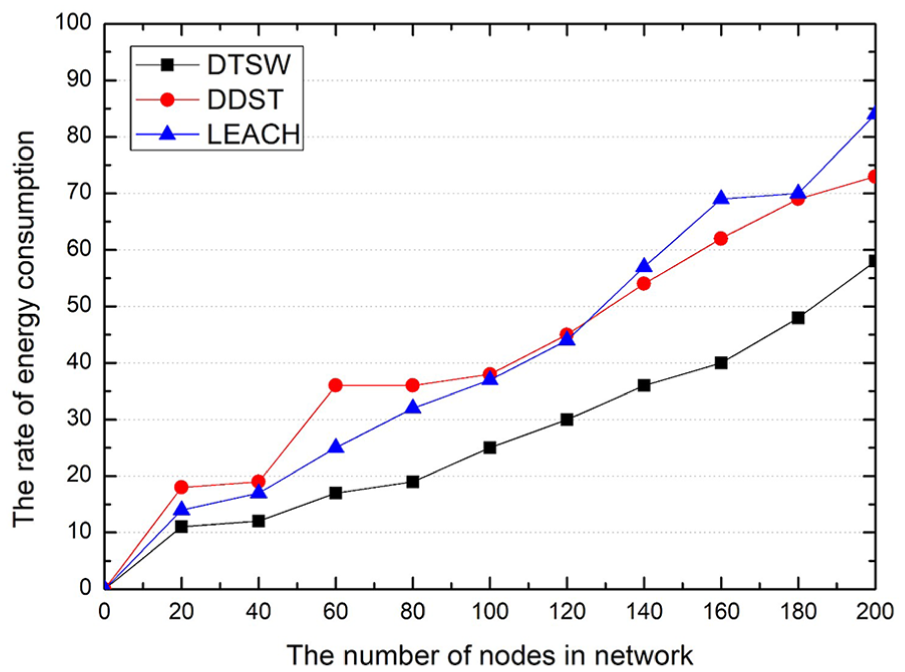
The comparison of remaining energy.
Network throughput
Network throughput is also evaluated and compared to those of DDST and LEACH. The results are shown in Figure 9. As shown in Figure 9, with the increase of the industrial nodes, the DTSW algorithm has better network throughput than the other algorithms. The weight partition model is used to control data transmission in the network. The above experimental results show that DTSW has good performance in terms of network lifetime and network throughput.
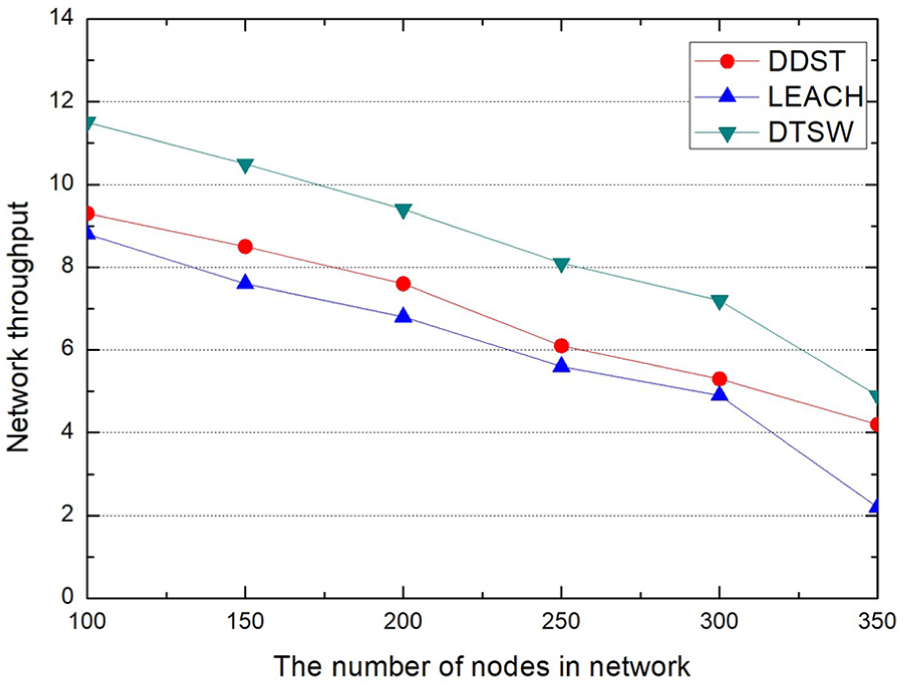
The comparison of network throughput.
Transmission rate
IoT uses the single-copy transmission. In the next hop selection, some selfish or malicious nodes are eliminated. In this case, the data transmission overhead is greatly reduced. In this evaluation, we set the number of selfish and malicious nodes at 40 and that of normal nodes is 160. With the increase of threats, the overall performance of the network decreases. The evaluation of the transmission success rate is shown in Figure 10. With the increase of simulation time, the network resources are gradually consumed. The transmission success rates of all the comparative algorithms show a downward trend. DDST has the highest transmission success rate when the network starts running. However, it has a sharp downward trend. DTSW shows a gentle curve. With the increase of simulation time, the transmission rate of DTSW is higher than those of the other comparative algorithms.

Comparison chart of data transmission rate when the number of selfish/malicious nodes is 40.
The evaluation of the average delay time is shown in Figure 11. DTSW is also compared to DDST and LEACH. In this figure, DTSW shows a short delay than DDST and LEACH. It demonstrates that the proposed DTSW also has good efficiency when there are some selfish and malicious nodes in the network.

Comparison chart of the average delay when the number of selfish/malicious nodes is 40.
Analysis
DTSW is a secure data transmission scheme for IoT that can solve the issue of slow extension speed of the nodes. It determines the transmission authority using the attributes of users. The attributes in the DTSW model can be divided into subjective (e.g. identity, role, age, and position), objective (e.g. accessed resource), and environmental (e.g. context environment) attributes. With the attributes of the users and the authority, the administrator only requires determining whether a user can access the network. The core factor of DTSW is attributes. The subject provides the IoT attributes and determines whether it can access the network. The authority is controlled by the attributes of the system. Hence, this condition is more suitable for a complex IoT environment and can improve the security of the network. Furthermore, DTSW has a good expression capability. The attributes of the users can be described from many aspects to satisfy the dynamic authority of access control. Table 2 presents the performance of data transmission and access control.
Advantages and disadvantages of different access control models.

LEACH: low-energy adaptive clustering hierarchy; DDST: distributed data secure transmission.
Conclusion
IoT has been extensively used in the industry due to its good features. This work analyzes the network feature of IoT and proposes data transmission based on weight partition. In this scheme, the region partition divides the uneven anisotropic network into several even isotropic networks. The proposed scheme can ensure communication quality and secure data transmission. The nodes with less communication time have a larger energy consumption weight than the ones with more communication time. In this case, the times to adjust the frequency will be less, thereby making the frequency close to the target value. It can reduce the response time, enhance the stability, and prolong the network lifetime. The experiments show that the proposed scheme has increased the network lifetime, communication traffic, and network capacity.
Although the proposed algorithm provides an effective solution for addressing the security issues in an anisotropic network, some aspects must be improved, such as optimizing network protocol to save energy consumption and designing a good routing protocol. The design of a secure transmission protocol in industrial IoT should be researched further in the future. In recent years, information privacy has become increasingly important in many fields, including IoT. In our future research, we will pay further attention to the protection of information privacy and avoiding data leakage. In this work, we realize initial studies on models with existing selfish and malicious nodes. In our future works, we will consider identity authentication between nodes and realize secure data transmission on the basis of the identity of the nodes.
Footnotes
Handling Editor: Fei Yu
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the National Science Foundation of China (Grant No. 61572188), Xiamen Science and Technology Foundation (Grant No. 3502Z20173035), Scientific Research Program of New Century Excellent Talents in Fujian Province University, Fujian Provincial Natural Science Foundation of China (Grant No. 2018J01570), the Young Teachers’ Education Scientific Research Project of Fujian Province (Grant No. JT180455), in part by the CERNET Innovation Project (Grant No. NGII20170411), the National Nature Science Foundation of Fujian Province (Grant No. 2018J01544), the Scientific Research Program of Outstanding Young Talents in Universities of Fujian Province, the Key Project of Natural Foundation for Young in Colleges of Fujian Province (Grant No. JZ160466), the National Nature Science Foundation of China (Grant No. 61871204), and the Natural Science Foundation of Fujian Province (Grant No. 2018J01544).
