Abstract
In recent years, the need to develop advanced information technology systems in the area of mechanical engineering has been growing continuously to deliver better product quality at reduced cost. Embedding the electronics and software with machines transform them into smart machines sophistically called mechatronic. These software-oriented machines collect big data using sensors and other electronics and share among other smart machines, which further helps them in controlling the manufacturing processes, decision-making, and even in maintenance. Machine-to-machine sharing of data involves the risk of data stealing or modification, which may further disrupt the working of manufacturing process and leads to poor quality product. For data security, block ciphers like advanced encryption standard are needed. Advanced encryption standard is an encryption algorithm which is widely used to provide security to sensitive information by organizations. The main core of advanced encryption standard is its non-liner component that is S-Box, which is also called substitution table. The S-Box provides confusion capabilities in algorithm. The point of interest for cryptanalysis and hackers is S-Box, which is fixed in case of advanced encryption standard. Cryptanalysis and hackers exploit this weakness of advanced encryption standard. Many researchers tried to modify S-Box using different techniques. In this article, we tried to create dynamic S-Boxes which are key-dependent and, at the same time, they are using dynamic irreducible polynomial and affine constant.
Introduction
In mechanical engineering, innovation is coming from electronics and software in mechatronic products. Machines that used to be completely mechanical now have controls that are largely electronic and software driven. This means that the motors, pumps, valves, and all manner of other traditional components are now can be controlled by software and, at the same time, upgradable over Internet connection. These traditional machines are now transformed to mechatronic by increasing software proportion by machine automation and proportion of mechanics is decreasing in terms of value.
The machines need to communicate to collect data from various stages of production process for faster and smarter decision-making that can have deep impact on supply, manufacturing, and shipping. This machine-to-machine communication is a major focus of information technology in making advancements in mechanical engineering. Information technology opens up new opportunities for applications in mechanical engineering such as condition monitoring, remote maintenance, or decentral energy management.
Security and reliability will play curtail role in making these systems secure. So, here, in this article, we presented a modified encryption algorithm to encrypt data during machine communication. Here, we are introducing advanced encryption standard (AES) algorithm, which is already a well-known algorithm in data encryption. We have proposed a new dynamic S-Box algorithm, which further enhances the security of existing AES algorithm.
AES is a block cipher widely used for encryption and decryption of data. AES block cipher was adopted by the US government as standard in 2001. Joan and Vincent Rijmen developed AES block cipher.
AES uses block sizes of 128 bits for encryption at one time, which is fixed. AES has three variants in which variable key sizes for different rounds (10, 12, and 14) are used. AES uses 128 bit key size for 10-round variant, 1 192 bit key size for 12-round variant, 2 and 256 bit key size for 14-round variant. 3 All the calculations of AES block cipher are carried out in finite fields, that is, GF(28). To encrypt the 128 bit input block with 128 bit key, 10-rounds are used each round consists of four possessing steps except the last round which consists only three steps. For decryption, same rounds and steps are used, but in reverse order. Different steps which are used in each round are as follows:
The byte substitution transformation: byte substitution is a non-linear confusion process, which consists of multiplicative inverse in GF(28) and followed by an affine transformation.
The shift row transformation: shift row is a linear diffusion process, operating on individual rows in a 4 × 4 matrix. First row remains intact, one left shift is done in second row, two left shifts are done in third row, and three left shifts are done in fourth row of the matrix.
The mix column transformation: in mix column matrix, multiplication is done over GF(28). Multiplication of column vector is done with a fixed matrix, where all the bytes are treated as polynomials.
Add round key: in add round key, the bytes of state matrix and XORed with bytes of the round key.
AES S-Boxes
The design of S-Box should be such that it can resist to algebraic attacks like linear and differential cryptanalysis. S-Box is a non-liner layer in AES which provides confusion to the AES. S-Box must be invertible, which is used in decryption. S-Box is nothing but a permutation of 256 8-bit values. Each input byte in plain text is mapped or replaced with a corresponding new byte in S-Box. In AES, S-Box is generated using GF(28) (Galois Field) and irreducible polynomial

AES algorithm.
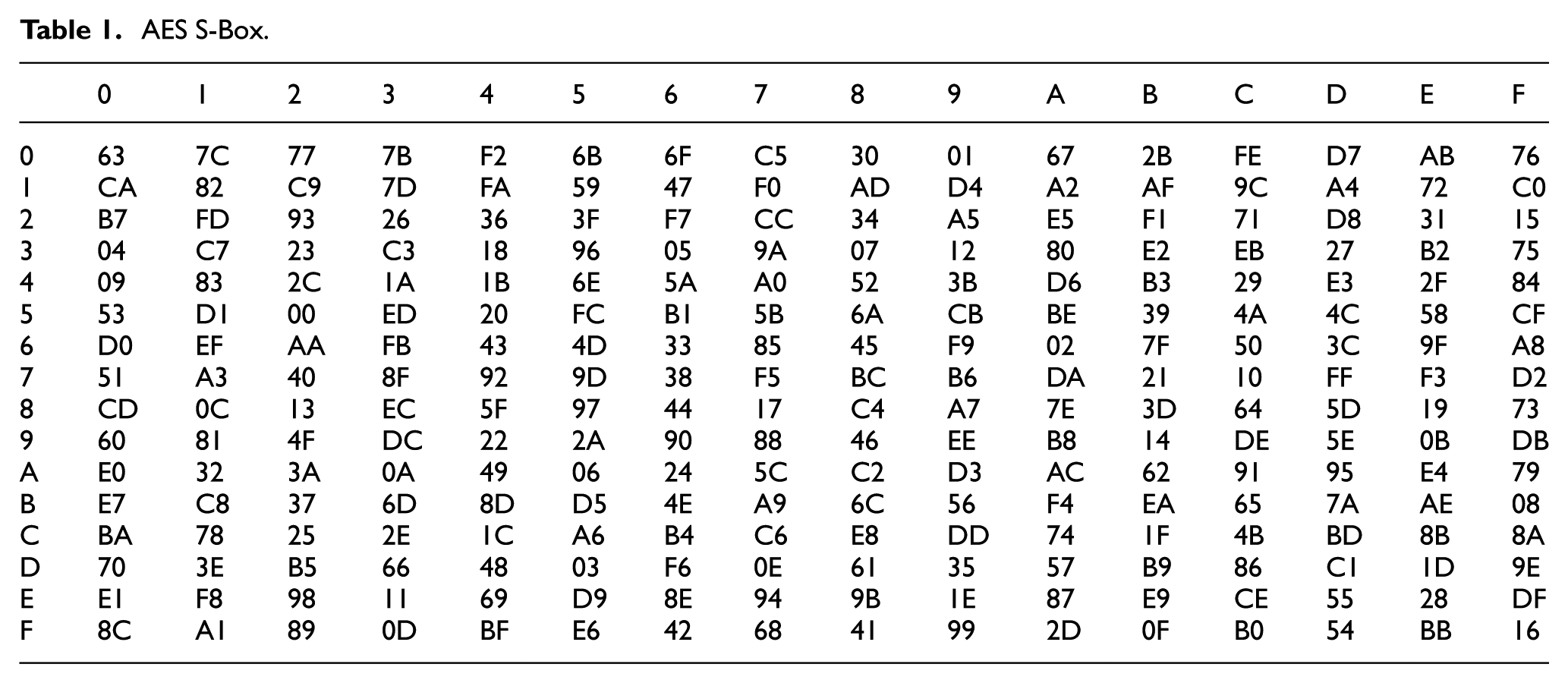
The S-Box and inverse S-Box generated by above affine transformation are represented in Tables 1 and 2, respectively. 3
AES S-Box.
Inverse AES S-Box.

Many researchers put their effort to make AES more secure by applying different techniques. In all these articles, we found that the authors used to make S-Boxes key-dependent using various techniques. GN Krishnamurthy and V Ramaswamy used AES-KDS block cipher, in which they used S-Box rotation on each round. They also used different stages to enhance the security. 5 K Kazys and K Jaunius 6 created key-dependent S-Boxes by making changes in key expansion routine of AES. Abd-ElGhafar et al. 7 used RC4 algorithm to generate S-Boxes key-dependent. J Cui et al. 8 increased the complexity and security of AES S-box by modifying the affine transformation. R Hosseinkhani and H Haj Seyyed Javadi 9 used AES S-Box to generate dynamic key-dependent S-Box. E Mohammed Mahmoud et al. used a technique in which PN Sequence Generator was used to generate perfect random sequence of bits. This approach use linear feedback shift register (LFSR) to generate key-dependent dynamic S-Boxes. 10 S Arrag et al. 11 proposed a new approach in which they used lookup S-Box table and key expansion algorithm to enhance the complexity of the S-Box. VL Hallappanavar et al. 12 used different irreducible polynomial to create new S-Box for AES. So, by taking motivation from existing work, in this article, we have presented a new technique to present dynamic S-Boxes which are not only key-dependent but also sensitive to other inputs like irreducible polynomial and affine constant. So, these three parameters generate highly dynamic S-Boxes which enhance security of algorithm from various algebraic attacks.
Proposed dynamic key-dependent S-Box algorithm
The proposed dynamic key-dependent S-Box algorithm is a permutation of existing AES S-Box. To make S-Box dynamic, existing AES S-Box and new generated S-Boxes are being used. The idea is that whenever a single bit of a key is complemented, then the algorithm will select an irreducible polynomial from 30 irreducible polynomials available, an affine constant from all affine values from 0 to 255 is being selected and a key EX-OR value is computed which is EX-OR value of all bytes of key. So, our S-Box values are dependent on these three parameters. Every time a key bit is complemented, then a different S-Box with permuted values will be generated, which adds complexity to the algorithm. Figure 2 presents the flowchart of proposed dynamic key-dependent S-Box algorithm.

Flowchart for proposed algorithm.
Algorithm to generate dynamic key-dependent S-Box
Inputs
Secret key
Initial AES S-Box
Irreducible polynomials
Outputs
Key-dependent dynamic S-Box
Key-dependent inverse dynamic S-Box
Case 1: round
Compute secret key value
Select irreducible polynomial
Select
Find
Apply affine transformation on all values of
Now make create S-box dependent on key value
Write new S-Box constants to DSBox:
Generate key-dependent inverse dynamic S-Box
Case 2: round
to
Compute secret round key value
Select irreducible polynomial
Select
Find
Apply affine transformation on all values of
Now create S-box for round
Write new S-Box constants to DSBox of round
Generate key-dependent inverse dynamic S-Box
Dynamic S-Box generation with single bit change in key
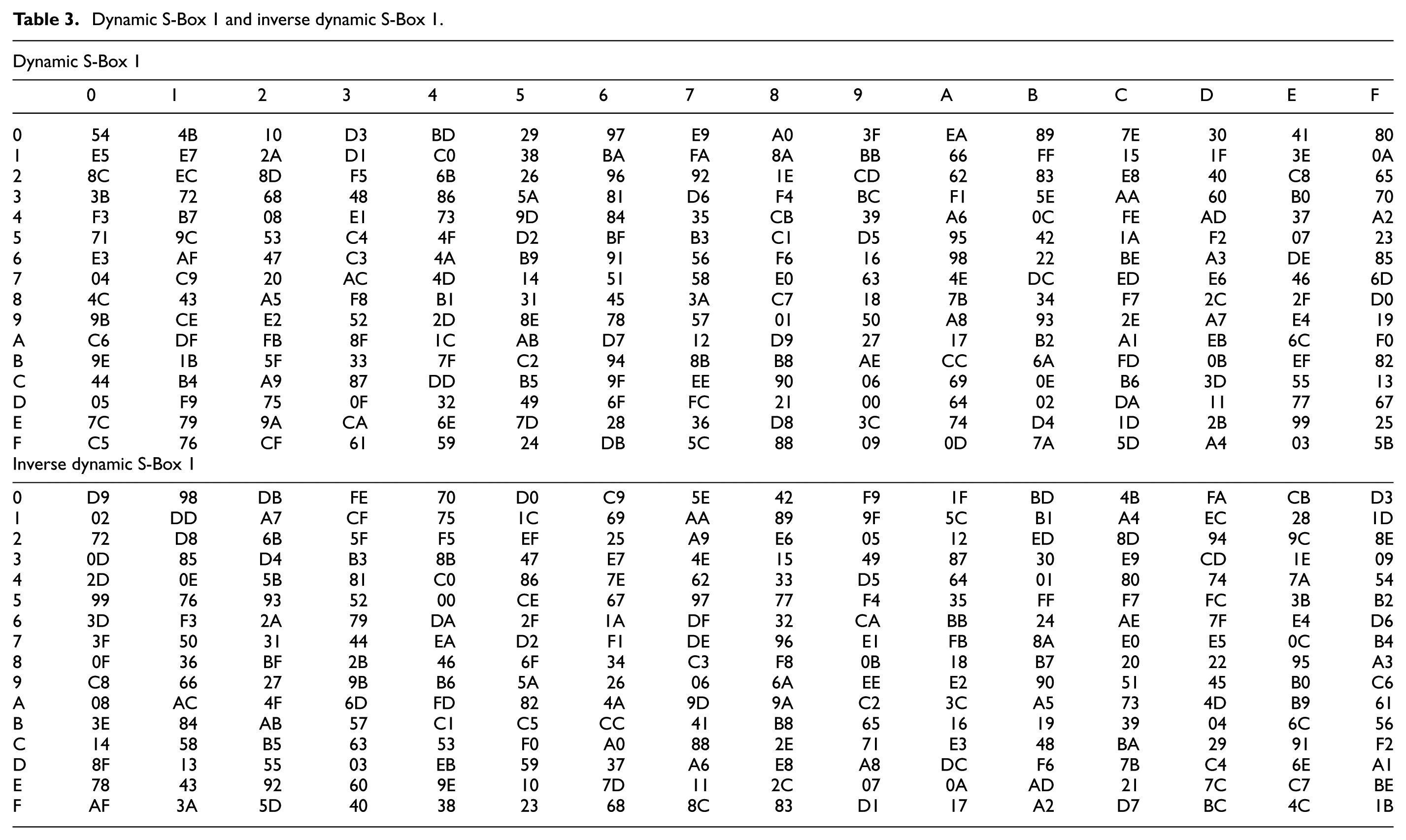
In this article, we have generated nine dynamic and dynamic inverse S-Boxes by just changing one bit in the key. Dynamic S-Box 1 and inverse S-Box 1 are generated in Table 3 with key 00E9C9F2A509D4E8A8BBB760A02AAB08. By just changing only one bit in the key other eight dynamic S-Boxes and inverse S-Boxes are created:
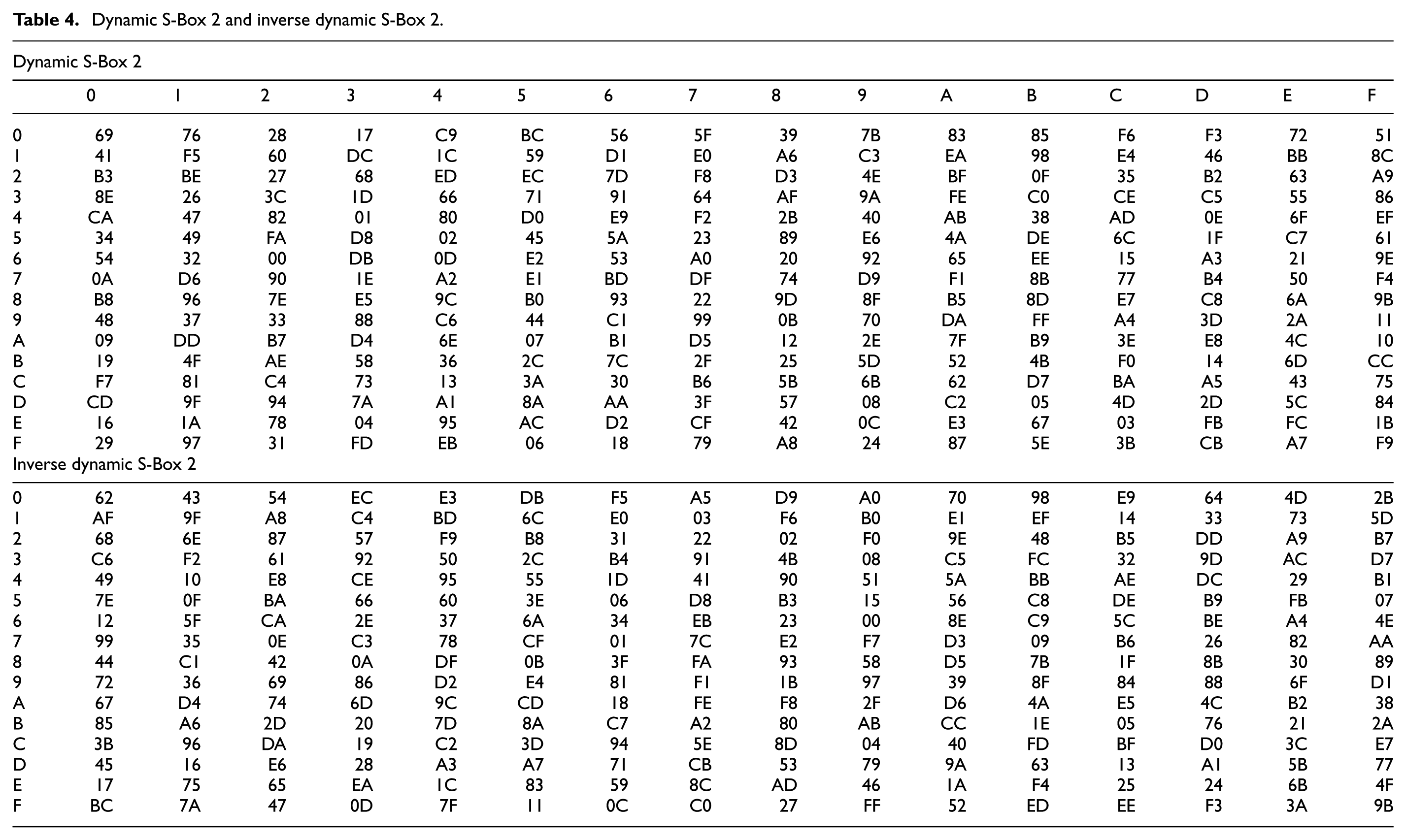
Dynamic S-Box 2 and inverse S-Box 2 are generated in Table 4 by changing just one bit in key from 00 to 80 using key 80E9C9F2A509D4E8ABBB760A02AAB08.
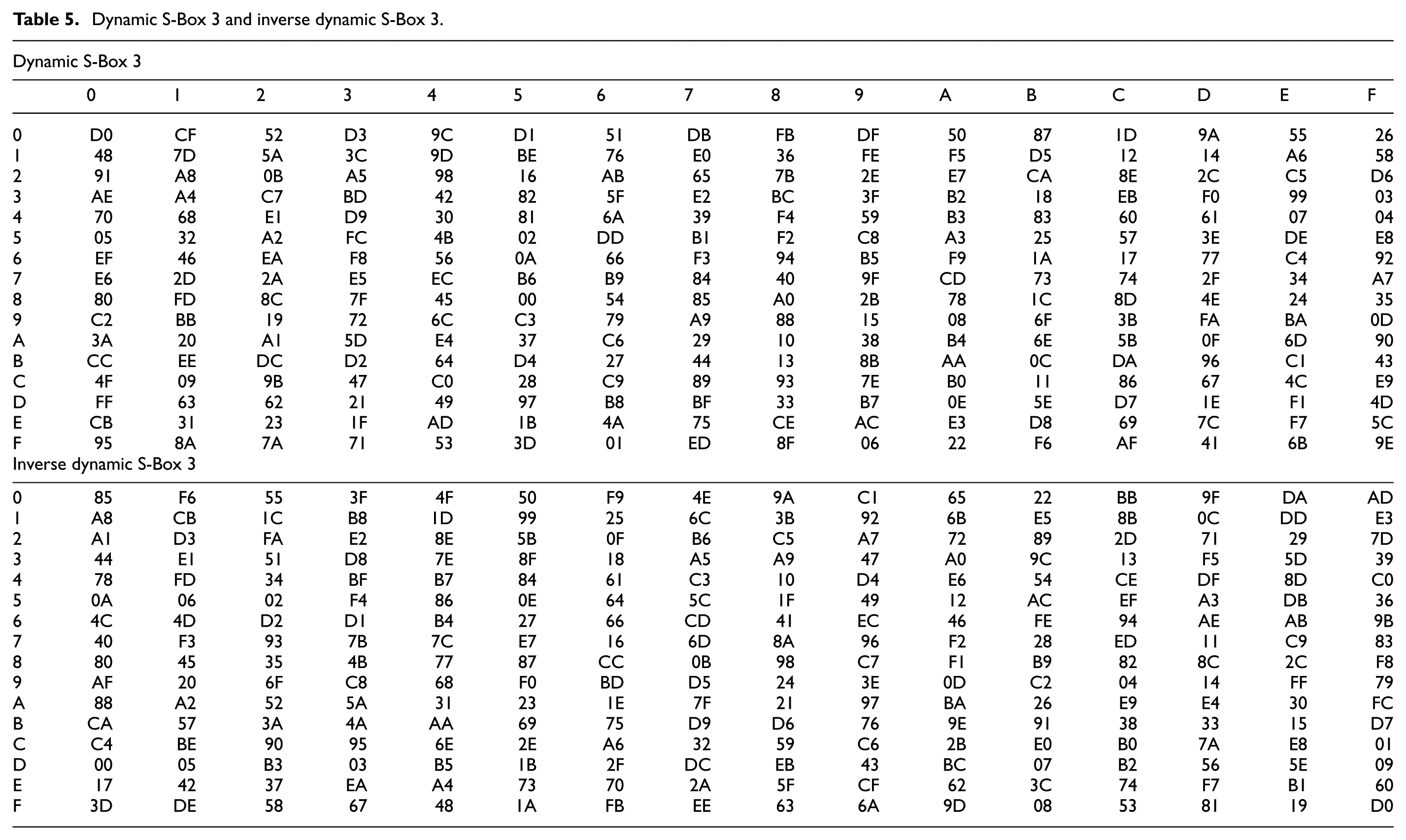
Dynamic S-Box 3 and Inverse S-Box 3 are generated in Table 5 by changing just one bit in key from 80 to 04 using key 40E9C9F2A509D4E8A8BBB760A02AAB08.
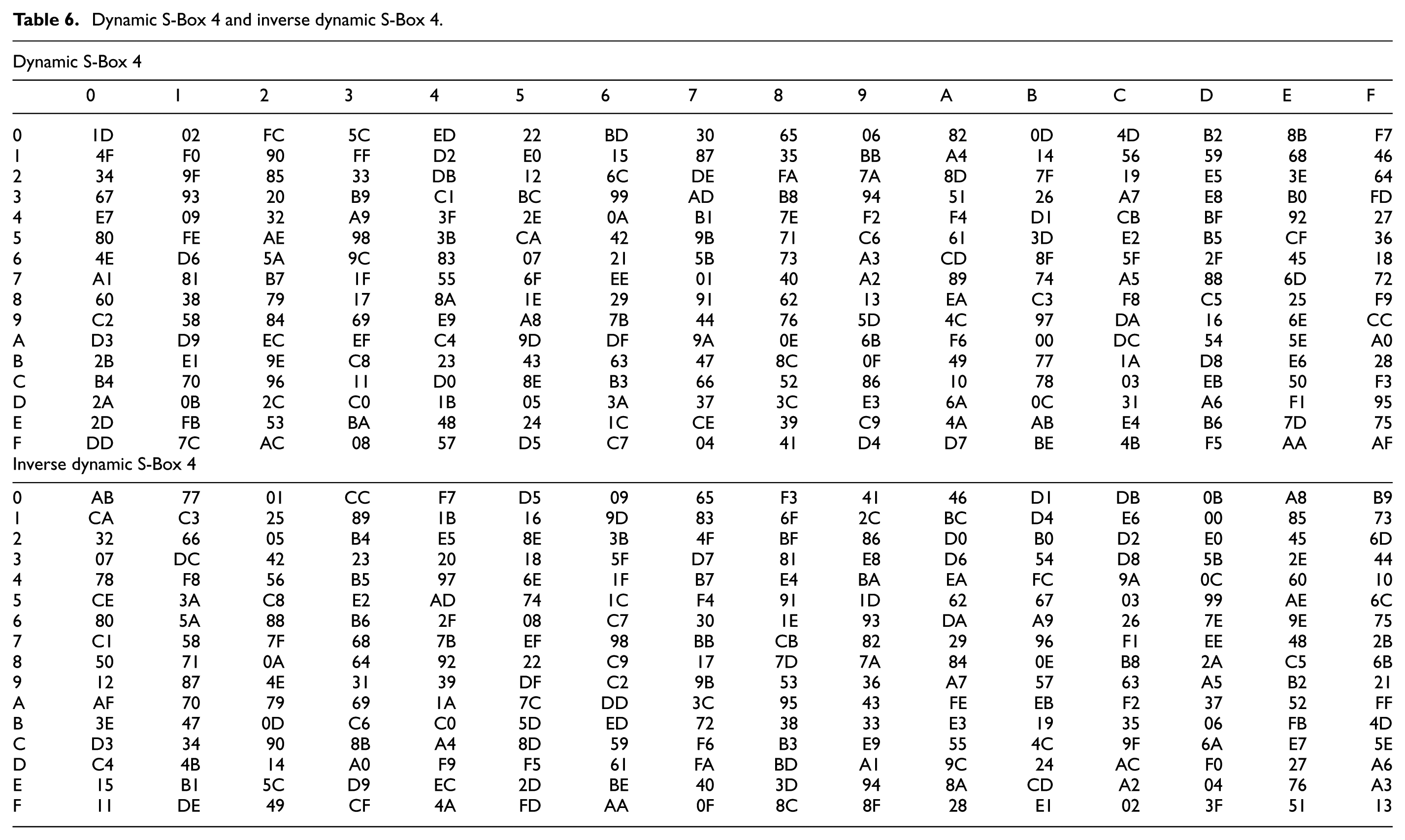
Dynamic S-Box 4 and Inverse S-Box 4 are generated in Table 6 by changing just one bit in key from 04 to 20 using key 20E9C9F2A509D4E8A8BBB760A02AAB08.
Dynamic S-Box 5 and Inverse S-Box 5 are generated in Table 7 by changing just one bit in key from 20 to 10 using key 10E9C9F2A509D4E8A8BBB760A02AAB08.
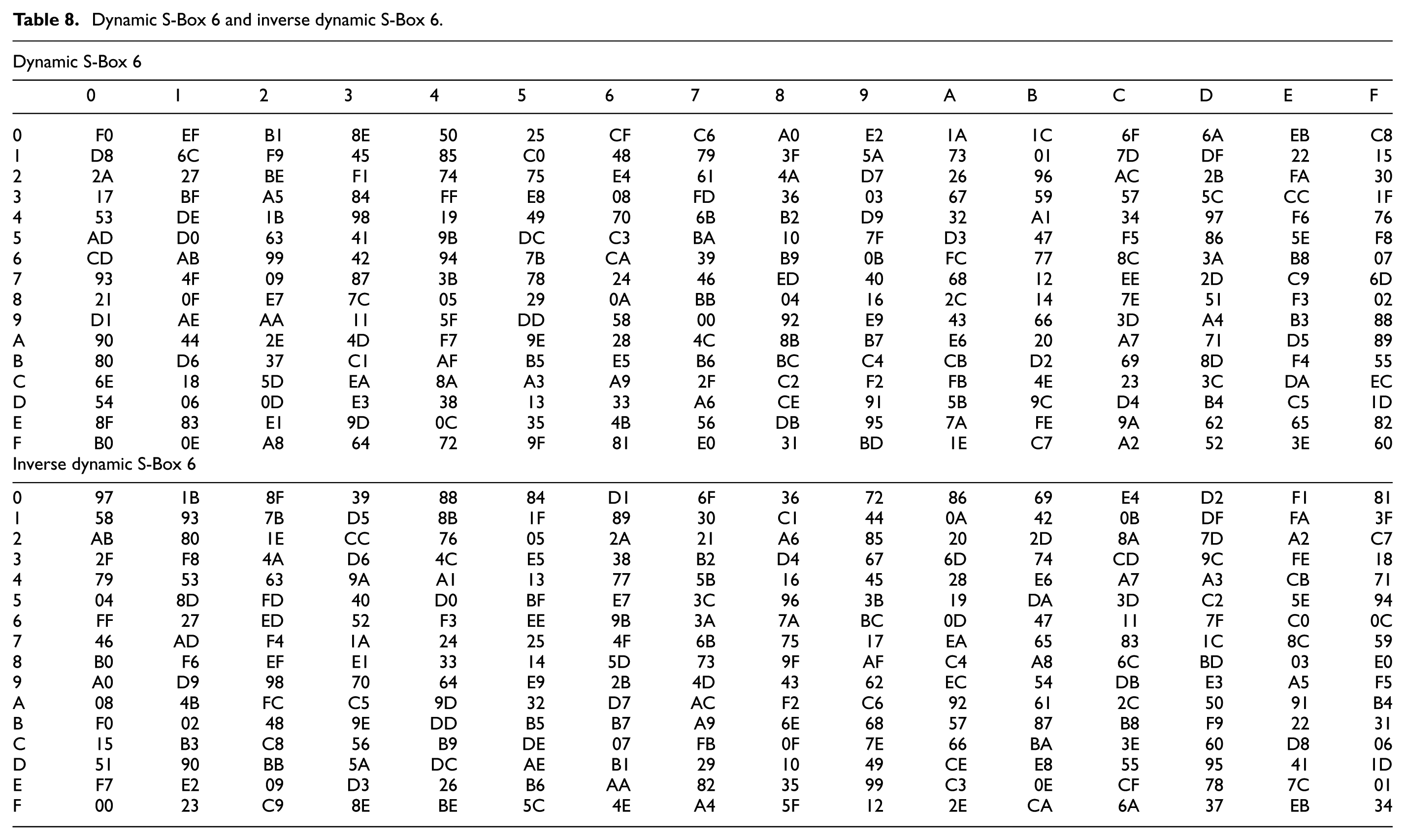
Dynamic S-Box 6 and Inverse S-Box 6 are generated in Table 8 by changing just one bit in key from 10 to 08 using key 08E9C9F2A509D4E8A8BBB760A02AAB08.
Dynamic S-Box 7 and Inverse S-Box 7 are generated in Table 9 by changing just one bit in key from 08 to 04 using key 04E9C9F2A509D4E8A8BBB760A02AAB08.
Dynamic S-Box 8 and Inverse S-Box 8 are generated in Table 10 by changing just one bit in key from 04 to 02 using key 02E9C9F2A509D4E8A8BBB760A02AAB08.
Dynamic S-Box 9 and Inverse S-Box 9 are generated in Table 11 by changing just one bit in key from 02 to 01 using key 01E9C9F2A509D4E8A8BBB760A02AAB08.
Dynamic S-Box 1 and inverse dynamic S-Box 1.
Dynamic S-Box 2 and inverse dynamic S-Box 2.
Dynamic S-Box 3 and inverse dynamic S-Box 3.
Dynamic S-Box 4 and inverse dynamic S-Box 4.
Dynamic S-Box 5 and inverse dynamic S-Box 5.

Dynamic S-Box 6 and inverse dynamic S-Box 6.
Dynamic S-Box 7 and inverse dynamic S-Box 7.

Dynamic S-Box 8 and inverse dynamic S-Box 8.

Dynamic S-Box 9 and inverse dynamic S-Box 9.

So, the algorithm is capable of generating 256! dynamic S-Boxes, which is equal to
Difference between elements of AES S-Box and dynamic S-Boxes after changing one bit of the key
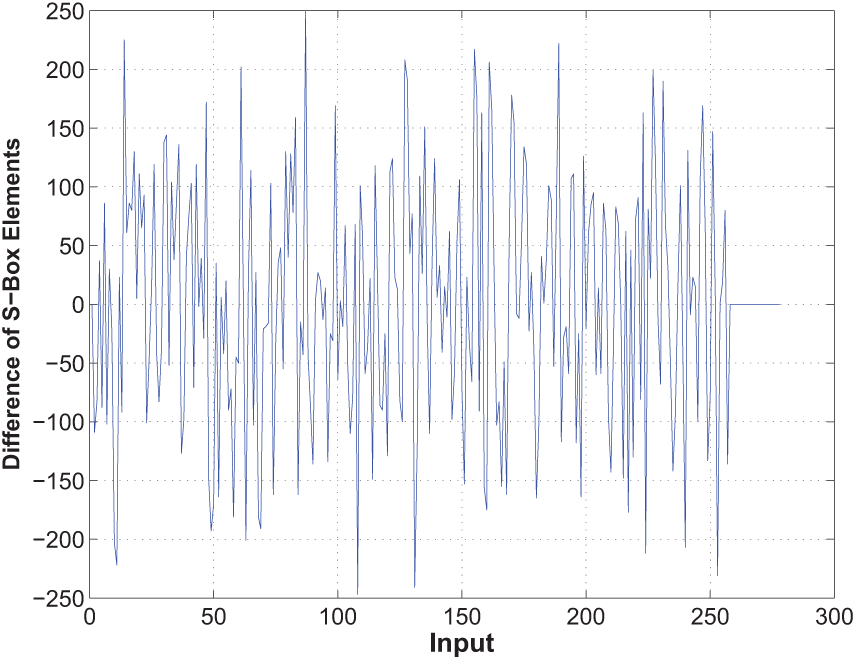
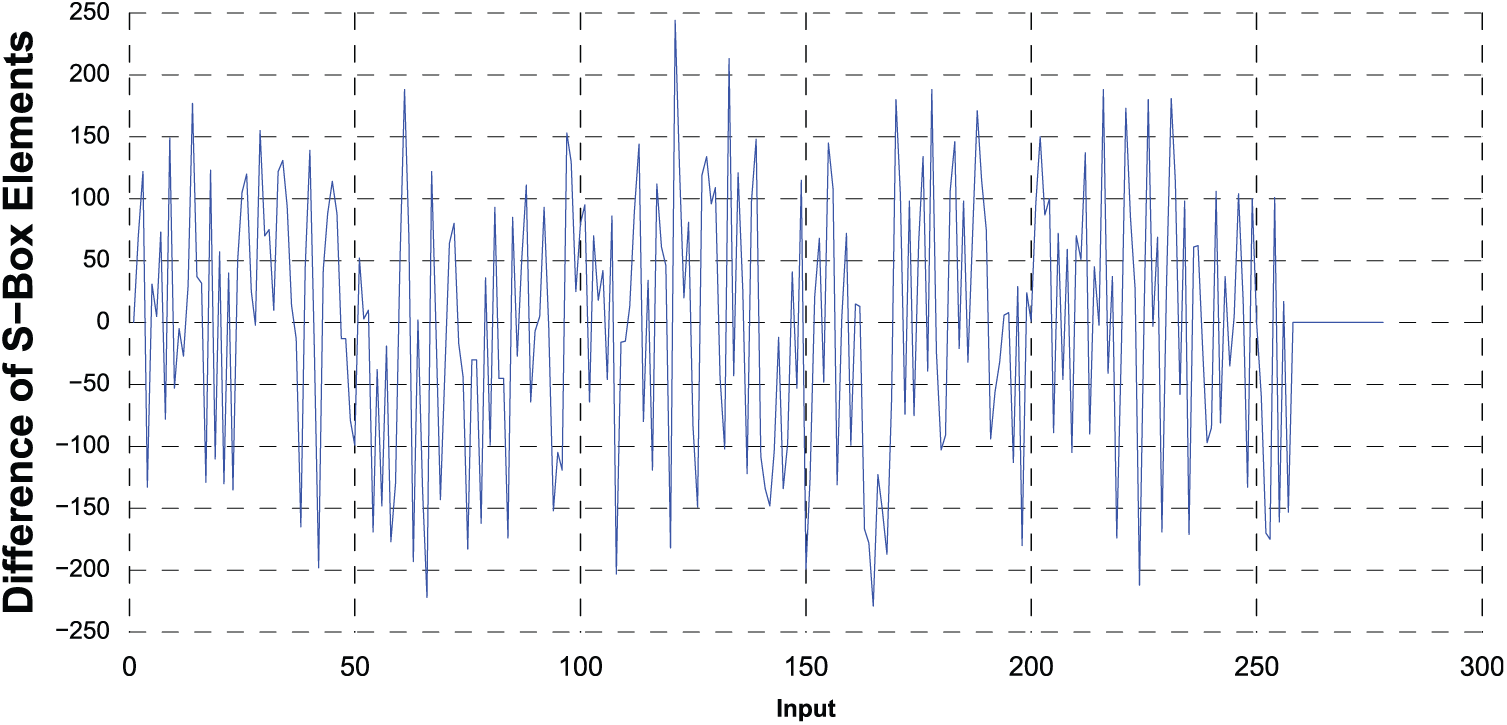
In this article, we have shown graphical representation of difference between elements of AES S-Box and all nine dynamic S-Boxes generated just by changing only one bit in key (Figures 3–11). Shows 100% difference in elements of AES S-Box and dynamic S-Box 1 by just changing one bit in key. Shows 99.6% difference in elements of AES S-Box and dynamic S-Box 2 by just changing one bit in key. Shows 99.6% difference in elements of AES S-Box and dynamic S-Box 3 by just changing one bit in key. Shows 99.6% difference in elements of AES S-Box and dynamic S-Box 4 by just changing one bit in key. Shows 100% difference in elements of AES S-Box and dynamic S-Box 5 by just changing one bit in key. Shows 100% difference in elements of AES S-Box and dynamic S-Box 6 by just changing one bit in key. Shows 99.6% difference in elements of AES S-Box and dynamic S-Box 7 by just changing one bit in key. Shows 100% difference in elements of AES S-Box and dynamic S-Box 8 by just changing one bit in key. Shows 99.2% difference in elements of AES S-Box and dynamic S-Box 9 by just changing one bit in key.






The aim or benefit of dynamic key-dependent S-Box algorithm is to increase the security of exiting AES by introducing different and dynamic S-box in each round of AES, which increases security against algebraic attacks. Earlier number of algebraic attacks designed to break AES. The algebraic attack analysis the algebraic structures of block cipher and with the combination of plain text and cipher text tried to find out the secrete key. As the S-Box in AES is fixed in all rounds of encryption process and the attackers or cryptanalysts analysis the linear and differential properties or AES S-Box and mounted attacks like linear cryptanalysis, Differential cryptanalysis, Boomerage Attacks, Interpolation attacks, Slide attack, Multiset attacks include round 4, 6, 7, 8, and 9 rounds, XL and XSL attacks. The new proposed algorithm makes all the attacks very difficult.
The cryptography has an important role in mechanical engineering sector. Mechanical engineering is all about automation. IT is playing an important role in machine automation by embedded software in machines, in other word, we can say that a machine is a device equipped with logic that takes the form of software and responds to the commands. These machines are used in all sectors like automobile industry, manufacturing industry, medical science, and film industry. A machine can interact with other machines or devices, which is called inter-machine communication. In inter-machine communication, the machines form a network in which the data are shared among machines or with other derives then there is a need of data security, where in the role of security algorithms like cryptography algorithms come. Cryptographic algorithms shuffle the bits and present data in a way that only authorized users can unshuffle them to obtain the original data. Cryptographic algorithms are based on mathematics to achieve such shuffling of bits.
Conclusion
We introduced algorithm which generates dynamic key-dependent S-Boxes with dynamic irreducible polynomial and affine constant. This algorithm is tested by complementing only one bit of key and it generates different S-Boxes with different values. Unlike AES S-Box which is fixed and can be prone to many algebraic attacks our algorithm is dynamic in nature which creates a secure block cipher. By applying this methodology total of 256! different S-Boxes are possible. Furthermore, we will analyze new generated dynamic S-Boxes on the basis of non-linearity, XOR profile, strict avalanche criteria (SAC), and bit independence criteria (BIC). In our algorithm, all polynomials worked well and gave desired result except one irreducible polynomial, that is, 1EF. So, in future work, we will do efforts to solve this problem.
Footnotes
Acknowledgements
All authors contributed equally to the manuscript. All authors read and approved the final manuscript.
Handling Editor: Yong Chen
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: The third author is very grateful to the Universiti Putra Malaysia for providing partial financial assistance in the form of Grant Putra 9543000.

