Abstract
Except the network attacks, the industrial networked devices in Internet of things are also threatened by intellectual property infringement. Watermarking technique is a prevalent way to avoid this threat. Previous work on authenticating a watermark in industrial intellectual properties easily discloses sensitive information of real embedded watermarks. In this case, the evidence of identifying the ownership of industrial intellectual property may be attacked by the illegal verifiers. Although several watermark detection techniques can address the disclosure of sensitive information in detection procedure, the efficiency of detection is relatively low. Besides, it may yield large communication overhead of multiple authentication rounds. Motivated by the needs of robustness and efficiency, this work proposed a zero-knowledge approach to authenticate ownership of field-programmable gate array intellectual property design in industrial environment, named NIWAS. The prover can convince the verifier that he knows a secret in the suspected intellectual property design via only one interaction. Real locations of watermarks are concealed through location obfuscation. With the received authentication package from the prover, the verifier cannot obtain other useful information about the watermarks. The experiments show that NIWAS achieves high efficiency and robustness of watermark detection.
Keywords
Introduction
The advancement of Internet of Things (IoT) leads to an exponential growth of the number of connected hardware devices. Cisco and Intel predict the hardware devices will exceed 50 billion in 2020. 1 The threats and challenges in security of hardware and embedded systems attract widespread attentions. The white paper on IoT security involves three main areas, including industrial control, intelligent vehicle, and smart home. Here, the data of US Department of Homeland Security shows that the fundamental equipment and industry environment are prime targets of network attacks. The attacks on industrial environment increase by 20%. The applications of IoT in industry make the factories become more intelligent, greatly driving the revolution of the global manufacturing. The traditional embedded system combines with industrial cloud platform, realizing a networked, intelligent, and digital industrial factory. The efficiency and transparency are greatly promoted in this way. However, the industrial system and networked devices are vulnerable to attacks from outside network, causing serious consequences.
Besides, the accessible devices in industrial IoT are also threatened by intellectual property (IP) infringement or reverse engineering. So, the security should be considered at the design level to avoid network attacks and threats (e.g. IP theft, reverse engineering, tampering, or clone). A device in IoT without enough security easily causes IP theft of a design after suffering from attacks. In 2012, the share price of AMSC fell by 40% in 1 day and evaporated 84% within 5 months due to the lack of security mechanism in wind turbine algorithm. 2 The occurrence of the security events may cause great threats to national security or economical loss. So, it is inevitable to protect the security of accessible networked devices. IP-reuse technology is prevalent in designing an integrated chip. 3 It brings lots of convenience in shortening design cycle, lowering design risk, and accelerating the time to market. But, it also allows the illegal users to realize attacks in a chip. The protection of IPs against infringement and illegal distribution becomes a challenging task in hardware security. 4 Owning to its satisfactory performance of low cost, field-programmable gate array (FPGA) is increasingly popular in designing IP cores. The design is transformed into the bitfile and finally downloaded into an FPGA device. So, the security issues of this kind of designs (bitfile cores) are more critical.5,6 Generally, there are encryption technique and watermarking technique to address the security issues. The former depends on the credibility of a certain encryption algorithm. If the algorithm is cracked, the bitfile core will lose the secure protection. The latter deters illegal infringement of bitfile core by embedding identification information into a design imperceptibly. The presence of this information will be used as an evidence to identify the original ownership of hardware IPs.
Most of traditional IP watermarking methods are symmetrical. Namely, the secret key in watermark detection is the same with that in watermark embedding.7,8 In copyright authentication, the IP owner should use the secret key to extract watermarks in the design and prove the ownership. Once the watermark or the embedding key is leaked to a potential attacker, he can destroy or remove the watermark to defeat the intention of proving IP ownership. Thus, they can sell an illegal copy of design or add a fake watermark into the design. The authentication of watermark in this kind of techniques usually requires the participation of a neutral and trustable third party. So, the authentication process involves three parties: the prover, the verifier, and the third party. During the authentication, some sensitive information about the watermark (like watermarked locations) may be leaked to the verifier or the third party. The credibility of both the two parties cannot be ensured completely. Hence, it is a prime issue to achieve a trustable and secure authentication without the participation of the third party in watermarking techniques First, no useful information is leaked to the verifier because it directly determines the security of inserted watermarks in a design. Second, the detection procedure should have higher efficiency with lower overhead. It ensures a satisfiable authentication performance.
This work is organized as follows. Section “Related work” evaluates previous techniques. In section “The NIWAS protocol,” we give an overview of the proposed NIWAS. The procedure of IP watermark authentication is illustrated in detail. An overall analysis on NIWAS is introduced in section “Protocol analysis.” Section “Experimental results” evaluates the performance of the proposed NIWAS by conducting experiments on benchmarks. Finally, we summarize this work.
Related work
In IP watermarking techniques for industrial FPGA design, the ownership information of IP owner is usually inserted as configuration bitstring into lookup tables (LUTs) determined by a random location sequence.9,10 The inserted watermarks are verified from the bitfile. A signature is embedded within the memory structures or the combinational logics of the system by technique. 11 A watermark detection module is inserted into the design, causing large hardware overhead. The logic is easily to be removed as well. The watermarking technique 12 embeds watermarks into the unused LUTs of the used slice. The watermarks can be detected at the power supply pins of the FPGA using an oscilloscope and quantized into the original ownership information. In Schmid et al., 13 the watermarked LUTs are then converted to LUT-based RAMs or shift registers to avoid deletion due to optimization. The watermarks are detected from bitfile of FPGA design when the infringement occurs, as shown in Figure 1. The signature will be transformed into appropriate watermark fragments after encryption. Suitable positions (as a key) are selected in the design for watermark embedding. The watermark fragments are then inserted into the design in specific forms. In detection, the selected positions (key) in watermark embedding will be used to find the watermark fragments in the watermarked design. The watermarks are combined orderly to reconfigure the original signature with the key. Watermark authentications in these techniques are not effective and robust since it may leak useful information about watermarks. Besides, most of the above techniques require the participation of a trustable third party, which poses more risks on the watermarks.

Traditional IP watermark verification.
Zero-knowledge proof (ZKP) is a promising approach to overcome this security issue in watermark detection. An army of ZKP-based authentication techniques are reported in proving ownership of multi-media data. 14 ZKP protocol proves the presence of watermark in a certain design without leaking any useful information about the watermark. There are two types of ZKP protocols, namely, interactive and non-interactive.15,16 Interactive ZKP protocol consists of specific number of authentication rounds, as shown in Figure 2. A typical round involves a challenge depending on the random number or the outcomes of fair coin tosses by the verifier and a response by the prover. If the prover knows the secret, he can answer all challenges correctly. The authentication requires N rounds until the verifier accepts or rejects the proof of the prover. The condition depends on whether the prover gives successful response to all challenges of the verifier.

Interaction of zero-knowledge proof protocol.
On this basis, Verify_ZKP technique
17
proposed to authenticate a watermarked IP design publicly without the participation of the third party. The protocol reveals no sensitive information about watermark in detection. In Verify_ZKP, the prover proves he knows a secret in D with strong assumption that the verifier did not obtain a copy of D. Otherwise, authentication in Step 3(a) will not convince the verifier. (1)
In above cases, a massive exchange of messages to run a typical ZKP can be unfeasible due to possible connection failures during the protocol. To deal with this issue, the idea of non-interactive ZKP (NIZKP) has emerged in the related literature. 20 In a NIZKP, all the challenges of a typical ZKP are condensed into a single package sent in a few messages. This leads to the minimization of the time necessary for the exchange of messages. Non-interactive authentication is characterized by the requirement of fewer messages than interactive authentication. There is no need for two parties to communicate with each other in NIZKP, except sending one data set from the prover to the verifier.21–23 It can also be adapted to a required security level so that the greater the number of different challenges, the higher the security level of the verifier. 24 The efficiency of non-interactive is encouraging owning to no interaction with the verifier. It is also widely used in many fields of cryptography. This protocol motivates us to develop a non-interactive zero-knowledge watermark authentication protocol as a generic approach to authenticate ownership of FPGA bitfile design with high efficiency.
The NIWAS protocol
In this section, we aim to implement a watermark authentication protocol to detect watermarks in a bitfile core without leaking any clue to remove the watermarks. To achieve better efficiency, this protocol uses NIZKP in authentication. Intuitively, for a complete authentication, the number of interactions between the prover and the verifier is reduced to be only one. First, we give a brief overview of a robust watermarking algorithm 25 for the IP owner to watermark his or her copyrighted IP design. Then, the copies of watermarked design will be regarded as illegal IP cores and traded in market. Finally, the authentication protocol is activated if there is a dispute on the watermarked design or other cases that the IP owner wants to prove his ownership.
Watermark generation and embedding
The watermarking scheme can be defined by a tuple
The signature S is encoded and XORed with a pseudorandom sequence, yielding an initial binary watermark sequence
Non-interactive watermark authentication
Traditionally, ownership authentication is mainly implemented by extracting marks in locations in correspondence with the reserved private key P (namely, the embedding key
Protocol overview
The authentication protocol involves two parties without the participation of the third party. To be clear, the prover and the verifier are named as Alice and Bob, respectively. Alice aims to prove to Bob with trust that her watermarks W exist in the disputed bitfile core
In interactive zero-knowledge-based IP watermarking techniques, the challenge usually depends on coin tosses. The prover will reply the different challenges depending on different results of coin tosses. In order for the protocol technique to be fair and practical, the public sequence of queries
Step 1 (initial stage): the bitfile core can be abstracted as a matrix
Step 2: based on input value
Step 3(a): if
Step 3(b): if
Step 4: Alice repeats Step 2 and Step 3, until
Step 5: Bob verifies each response in

The non-interactive zero-knowledge proof protocol.
To be clear, the protocol requires only one interaction with Bob. As the common inputs Q can be generated as a hashed message to the design or randomly selected. Since Step 3(a) and Step 3(b) are independent, the prover deceives Bob in Q is unnecessary. So, any random sequence can be used as common inputs. For each
Protocol implementation
In non-interactive zero-knowledge-based FPGA watermark authentication protocol, a critical issue is to ensure the security of watermark positions during the authentication procedure. The security involves: (1) the malicious verifier cannot deduce the real watermark positions from the authenticated design and (2) the malicious verifier cannot distinguish the watermark content from the content of the authenticated design. So, position obfuscation and content encoding are necessary in authentication. Position obfuscation requests that the secret keys in different authentication rounds have low correlation. Chaos phenomenon is a deterministic and random process in a nonlinear dynamic system, which is non-periodical and sensitive to the initial value. The secret key generated by chaos system has good randomness and low correlation, rightly satisfying the requirements of position obfuscation in watermark authentication.
In this section, two chaotic sequences are generated by chaos system and used to control the position obfuscation. To achieve better security, a random obfuscation algorithm is proposed by separating the rows and columns in obfuscation. Besides, the secret keys of position obfuscation and content encoding are mutually correlated, making it difficult for the malicious to crack any one secret key and deduce the real watermark positions. The implementation of NIWAS is described as follows.
Generation of chaotic secret key
Logistic is a widely used chaos system in cryptography due to it is simple and easy to implement, which can be represented as equation (1)26,27
Here,
The mean value
By repeating multiple iterations with equation (1), the generated chaotic sequence is transformed into a binary sequence. The auto-correlation
Random obfuscation algorithm
The bitfile can be abstracted as a matrix
Step 1: a initial value
Step 2: the rows of
Step 3: the same subsequences are used to encode the elements in both matrixes with
Step 4: both the obfuscated matrixes will be restored using the stored indexes in I. The matrix with separated columns is denoted by
Step 5: after obfuscation, both the matrixes will be integrated into a matrix
Step 6: the Steps 1–4 are repeated for N times, and the final obfuscated matrix is generated.
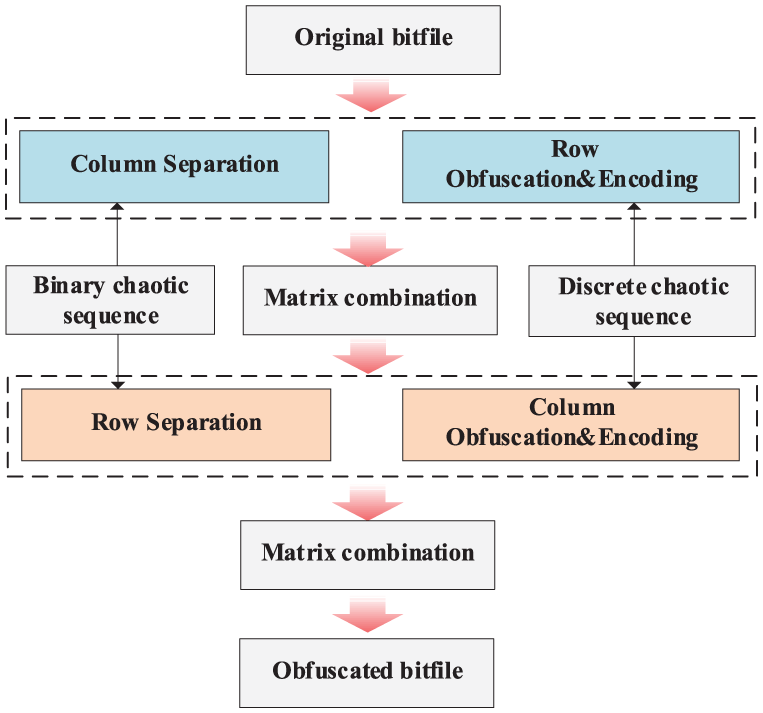
The flow of position obfuscation algorithm.
Protocol analysis
The proposed watermark authentication protocol only needs one interaction round to convince the verifier. It realizes high authentication efficiency and enables the verifier to check the ownership of the bitfile core offline. In this section, the property analysis is discussed, including completeness, soundness, and zero-knowledge property. Besides, the robustness of NIWAS is also analyzed.
Property analysis
As for ZKP, there are three central properties captured in the notions of completeness, soundness, and zero-knowledge. In what follows, we give a discussion about these properties.
Completeness
The prover can convince the verifier if the prover knows a witness testifying to the secret in an IP design. Here, we consider that the verifier has a watermarked copy of IP design
Soundness
A malicious prover Peggy cannot convince the verifier if the statement is false. In our technique, Peggy cannot pass both cases with high probability. For case (1), he may pretend to be legitimate IP owner by declaring a fake ownership with a copy of published IP design
Zero-knowledge
A malicious verifier learns nothing except that the statement is true. The queries depend on a public sequence
Robustness analysis
In this section, we analyze the robustness against several typical attacks, including tampering attack, removal attack, brute force attack, replay attack, and so on.
Tampering and removal attack
The zero-knowledge of the protocol will leak no sensitive information about real watermarks. In the mapped designs, the real watermark positions are obfuscated. So, an adversary has low probability to directly tamper target watermarked LUTs. But, it cannot avoid the watermarks being tampered by coincidence. If one or several watermarks are attacked, there are two mechanisms to restore the watermarks. (1) If the number of tampered bits does not exceed the correction ability of ECC, the watermark can be retrieved itself. Otherwise, the watermark will be dropped, and another reliable watermark will be chosen instead to ensure a successful authentication.
Brute force attack
The attackers tried to find the watermark positions using brute force. A real FPGA system includes many IP cores and the number of gates may be extremely large. The watermarks are embedded into the LUTs after series of processing. The number of watermarked positions can be ignored by comparing to the number of the complete design. The combinations to select several watermark positions from the design are almost countless. Moreover, the watermarks are implemented through configuration. The configuration data of watermarks is no different with that of the design. So, it is also hard to distinguish the watermarks.
Replay attack
It means that a vicious party can insert a forged signature into a watermarked IP design to declare a forged ownership. Since there are many unused LUTs in the watermarked design. If the attackers intentionally perform this type of attacks, one effective way is to register a timestamp of a watermarked design in a neutral authorized institution. So, the extracted watermarks which include this timestamp are legal. In this case, the forged watermarks cannot be used as legal evidence in authentication.
Experimental results
The proposed NIWAS is tested on benchmarks from IWLS2005 and ISCAS ‘89. First, the watermarks are prepared, and each benchmark is synthesized and implemented on smallest possible FPGA devices, yielding configuration bitstring. After that, the prepared watermarks are inserted into the design as in section “The NIWAS protocol.” Watermark authentication is implemented in java language on a machine with 2.59 GHz Intel® core™ i7 CPU and 8 GB memories.
The NIWAS is compared to the Verify_ZKP 17 and Blind_ZKP, 19 which are protocols of authenticate the copyright from the bitfile core. We embed 256-bit private watermark representing IP ownership into the benchmarks. In this section, the robustness and detection rate of NIWAS are evaluated.
Robustness evaluation
In this section, we aim to evaluate the robustness of generating a mapped design through location scrambling. Manhattan distance is used as a metric for evaluation. The distance between two points in a grid is based on a strictly horizontal and/or vertical path (i.e. along the grid lines), as opposed to the diagonal or “as the crow flies” distance. The Manhattan distance is the simple sum of the horizontal and vertical components, whereas the diagonal distance might be computed by applying the Pythagorean theorem. 29 Since the location scrambling is to exchange the positions of the elements in ℜ. If the Manhattan distance between the original location and the mapped location is larger, the performance of scrambling is better. However, another case cannot be ignored. As for an element in ℜ, if it has large Manhattan distance before and after location mapping and its neighboring elements also move to the same direction with large Manhattan distance. We cannot judge a good scrambling performance. So, Manhattan distance can be used as a good metric to evaluate the performance of location scrambling but should not be the only consideration. Here, the uniformity of location scrambling is also considered for a comprehensive evaluation.
In this experiment, we employ two metrics to evaluate the robustness of position obfuscation, the Manhattan distance and the uniformity. 30 Manhattan distance represents whether the elements are moving to the positions as far as possible. And, the uniformity denotes whether the elements are evenly distributed. Larger value of both metrics shows good robustness of position obfuscation.
Let
We assume a matrix
The uniformity degree of block B, namely,
Here,
Besides the Manhattan distance, we also calculate the uniformity to evaluate the scrambling effect. The matrix is divided into a set of blocks. If the elements are moved to other blocks evenly, the performance will be better. The uniformity degree and its mean in NIWAS are calculated using equations (9) and (10). The results are listed in Table 1. The first three columns, respectively, list the benchmarks, the number of LUTs in a marked design and the size of array in bitfile core.
Robustness evaluation of obfuscation.

LUT: lookup table.
In Table 1, the benchmarks occupy various resources of FPGA, ranging from 226 to 3034. The mean

Robustness of position obfuscation: (a) The evaluation of the mean manhatan distance and (b) The evaluation of the uniformity degree.
The comparison of position obfuscation is shown in Figure 5. Figure 5(a) shows the overall shift distance and Figure 5(b) shows the uniformity of obfuscation. NIWAS has larger value of the mean Manhattan distance than other two protocols. The protocols of Verify_ZKP and Blind_ZKP are based on configurable logic block (CLB) obfuscation, while our protocol directly obfuscates the LUTs. Due to the small granularity of obfuscation, a specific position moves farther in comparison, but requires more time for obfuscation. Besides, the curves in Figure 5(b) show the uniformity of NIWAS is larger than the other two protocols. By comparing to the protocols of Verify_ZKP and Blind_ZKP, the proposed NIWAS improves the uniformity by 35.2% and 25.9% at most. It directly relates with the chaos-based random obfuscation algorithm. Besides, we also evaluate the robustness of encoding in obfuscated design, as shown in Figure 6. The three protocols show stable curves of the number of flipped bits in the encoded design. However, the proposed NIWAS has slightly larger value than the other protocols, 16.1% and 13.5% at most. It may be related to the use of chaotic sequence in encoding.

Robustness comparison of bitstring encoding.
Watermark detection rate
The detection rate

Here,
In this experiment, the benchmark ethernet is chosen for evaluation. The bitfile is generated after embedding 128-bit watermarks. The results shown in Figure 7 are determined by 50 times of repeated experiments. Figure 7(a) shows the proposed NIWAS has better detection rate in a watermarked LUT when there are less impaired watermark bits. The ECC in each watermark has limited correction ability for bit flipping. But with the increase in the impaired watermark bits, three protocols show a similar descending curve. In Figure 7(b), NIWAS has higher detection rate

The comparison of detection rate: (a)
Conclusion
In this work, we have analyzed current ZKP-based IP watermark detection techniques and proposed a non-interactive watermark authentication technique to prove IP ownership without revealing any information to remove the watermark. It is a real-time watermark authentication technique owning to only one interaction with the verifier. The real watermark locations will not be leaked to the verifier due to the use of location obfuscation. Integrated with the proposed watermark embedding technique, the efficiency and robustness of watermark authentication are relatively enhanced. The proposed NIWAS compensates for the deficiency of most schemes that fail to consider public blind detection of watermarks. The experiments show that the proposed watermark embedding and authentication techniques are robust and efficient in proving ownership of FPGA bitfile cores. In the future, we will conduct further study on passive blind detection for secure authentication of IP ownership in IoT.
Footnotes
Handling Editor: Fei Yu
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the National Science Foundation of China (Grant Nos 61472130 and 61572188), the Research Project supported by Xiamen University of Technology (Grant Nos YKJ15019R and YSK15003R), Xiamen Science and Technology Foundation (Grant No. 3502Z20173035), the Open Research Fund of Hunan Provincial Key Laboratory of Network Investigational Technology (Grant No. 2017WLZC007), and the Open Research Fund of Fujian Key Laboratory of Automotive Electronics and Electric Drive (Grant No. ZDKA17001).