Abstract
This work focuses on the calculation of state space for linear system of simple sequential processes with resources (LS3PR). The method, different from reachability graphs rendering high computational complexity, finds reachable markings by combinatorics. First, the set of invariant markings can be obtained by combinatorics if the influence of deadlocks is ignored. Unfortunately, some of reachable states in the set of invariant markings are proved to be spurious if deadlocks exist. Second, we find the spurious markings by computing a set of minimal spurious markings, which can be calculated by a proposed algorithm based on strict minimal siphons. The obtained spurious markings are proved to cover all the spurious markings of the LS3PR. Removing the spurious markings from the set of invariant markings, the left ones constitute the state space of the LS3PR. The detailed method is shaped to an algorithm. The effectiveness of the algorithm is proved by example calculation and analysis. Finally, we analyze the computational complexity of the proposed method compared with reachability graphs.
Introduction
Different kinds of products can be made in a flexible manufacturing system (FMS) by computer control based on the allocation of a limited number of shared resources. Due to the existence of competition for resources, deadlocks are always unavoidable. Petri nets, as a tool with powerful modeling and analysis abilities, are widely used in the deadlock prevention problems of resource allocation systems.1,2 Petri nets–based deadlock prevention uses an offline computation mechanism to impose constraints on a system to prevent the system from reaching deadlock states.
Almost without exception, the existing literatures try to evaluate the performance of liveness-enforcing supervisors in terms of behavioral permissiveness, computational complexity, and structural complexity. Reachability graph (RG) analysis is an important technique for deadlock control, based on which an optimal or nearly optimal supervisor with high behavioral permissiveness can always be obtained. Depending on the calculation of state space, the theory of regions can definitely find an optimal liveness-enforcing supervisor if it exists. 3 The theory of regions is used in previous studies4–6 for an S3PR 7 to obtain a suboptimal liveness-enforcing supervisor.
However, reachability analysis8–10 needs a reachable marking enumeration, which requires a large number of consumptions of resources. In some cases, the analysis may stop due to the exhausted memory. It is shown in the work by Lipton 11 that the complexity of the reachability problem of a Petri net is exponential. Currently, using the popular integrated net analyzer (INA) 12 to obtain the state space of a large Petri net model is difficult, even impossible. Large sets of reachable markings with shared data structures can be represented by binary decision diagrams (BDDs). Besides, BDDs can implement efficient manipulation on the sets of reachable markings. In order to overcome the state explosion problem, BDD is used by Chen et al. 13 to represent the state space. However, the method still requires a complete enumeration of reachable markings whose number increases exponentially with the size of a Petri net. Hence, state explosion problem is still a technique barrier of using RG analysis to prevent deadlocks in an FMS. Consequently, we figure out another way with relatively low computational complexity, different from RG, to handle state–space problem.
We tackle the problem in the previous work 14 for arbitrary marked graphs by finding the number of reachable markings in an algebraic way. And the subsequent work15,16 extends the research field from marked graphs to S3PR, where might exist deadlocks. It deals with an approximate calculation of the number of reachable markings of an S3PR to predict whether the number is beyond the upper limit of computing power.
Our previous works mainly focus on number estimation of reachable markings for deciding whether it is deserved to conduct an RG analysis. In this work, we place emphasis on the complete enumeration of reachable markings for a subclass of S3PR, called LS3PR. First, we find the set of invariant markings (IMs) of an LS3PR by combinatorics. Then, excluding all spurious markings from the set by finding a set of minimal spurious markings basing on strict minimal siphon (SMS), the left markings are the ones to be desired.
The article is organized as follows. Section “Preliminaries” presents the preliminaries used throughout this article. The detailed approach of computing the state space of an LS3PR is introduced and a well-known example of LS3PR is adopted to support the approach in section “Main approach.” We perform an analysis on computational complexity of the proposed method compared with RG in section “Computational complexity analysis and comparison.” Finally, the conclusion of the article is presented in section “Conclusion.”
Preliminaries
Petri nets
A Petri net is a four-tuple
M is used to denote a marking or state of a Petri net N, which is a mapping from P to
A transition
Let I be a minimal P-semiflow.
Let
Let X be a matrix where each column is a minimal P-semiflow of N and denote the set of IMs of
LS3PR
A class of Petri nets defined by Ezpeleta et al., 7 called LS3PR, is introduced in this subsection.
Definition 1
A simple sequential process, called S2P for short, is a Petri net
Definition 2
A system of simple sequential process with resources, called S3PR for short, is a Petri net
Let
Definition 3
A linear S3PR, called LS3PR for short, is an ordinary Petri net
N is strongly connected.
Property 1
Let
Any
Any resource
Definition 4
A Petri net
In this article, quasi-safe LS3PRs are the subclass of Petri nets we focus on enumerating the reachable markings.
Main approach
This section aims to elaborate on how to completely enumerate the reachable markings of an LS3PR. First, for clarity, we use a simple example to exhibit the rough calculation of reachable markings by the proposed method. Second, the set of IMs of an LS3PR, obtained in the case of ignoring deadlocks, can be calculated by combinatorics. In the following subsection, we exclude all spurious markings from the set and obtain the reachable markings of the LS3PR. Finally, we give an algorithm as well as a supporting example to shape the detailed approach.
A simple example
For the simple LS3PR in Figure 1, there are two P-invariants,

A simple LS3PR.
Invariant markings of the LS3PR in Figure 1.

We know that the markings in Table 1 are the reachable markings of the LS3PR if there exists no deadlock. Unfortunately, by reachability analysis,
Reachable markings of the LS3PR in Figure 1.

Thus, in this article, we place an emphasis on how to steer clear of RG to find the state space of an LS3PR.
IMs
In this study, first, we construct a state space of an LS3PR based on P-invariants. According to the definition of P-invariants, the space can be obtained by combinatorics. In this work, Pr-semiflow is used to denote a P-semiflow with resources.
Theorem 1
The number of combinations of placing m elements into n distinguishable containers is
Corollary 1
Let
By Corollary 1, we find the number of IMs of

A subnet of an LS3PR.
Markings in

Definition 5
Let
In this article, suppose that the tokens in any minimal Pr-semiflow of an LS3PR stay in the resources originally. If ignoring deadlocks, the reachable states of
Property 2
By the multiplication rule of combinatorics, the least upper bound of the reachable states of an LS3PR
Property 3
Let
By Property 2, the states in upper bound can be generated. Here is an example. There are two minimal Pr-semiflows in the LS3PR
States in

View
Reachable states of theory permissive of

Finally, considering idle places, by Property 3, we find the reachable states of theory permissive of
Reachable states of theory permissive of

Unreachable states exclusion
Without deadlocks, the tokens in the Pr-semiflows of an LS3PR can flow freely among the places in the support of the Pr-semiflow. The existence of deadlocks makes part of states unreachable. It is proved in the work by Ezpeleta et al. 7 that an SMS means at least a deadlock. Hence, we concentrate on an SMS-based method to determine the unreachable states from the upper bound.
Let
Definition 6
Let G be an m-configuration of an LS3PR and
Theorem 2
Let
Proof
We prove it by contradiction. If
Definition 7
Let G be an m-*configuration of an LS3PR
Property 4
Let
The net

(a) A subnet
As known to all, the unreachable states of an LS3PR are generated due to the existence of deadlocks. Precisely, deadlocks render part of states unreachable. By Property 4, we can find that the unreachable states of an LS3PR
Lemma 1
Let
Proof
An m-*configuration, as an independent part of N, and its reachable states are independent of that of other parts. If
Theorem 3
Algorithm 1 completely enumerates the MUS of the *configurations in an LS3PR

Proof
Without considering deadlocks, we can find a set of all the reachable states of theory permissive, denoted as
Definition 8
Let
State estimate algorithm and example
We shape the detailed approach of calculating the state space of an LS3PR
Here, the LS3PR

A typical example.
States in
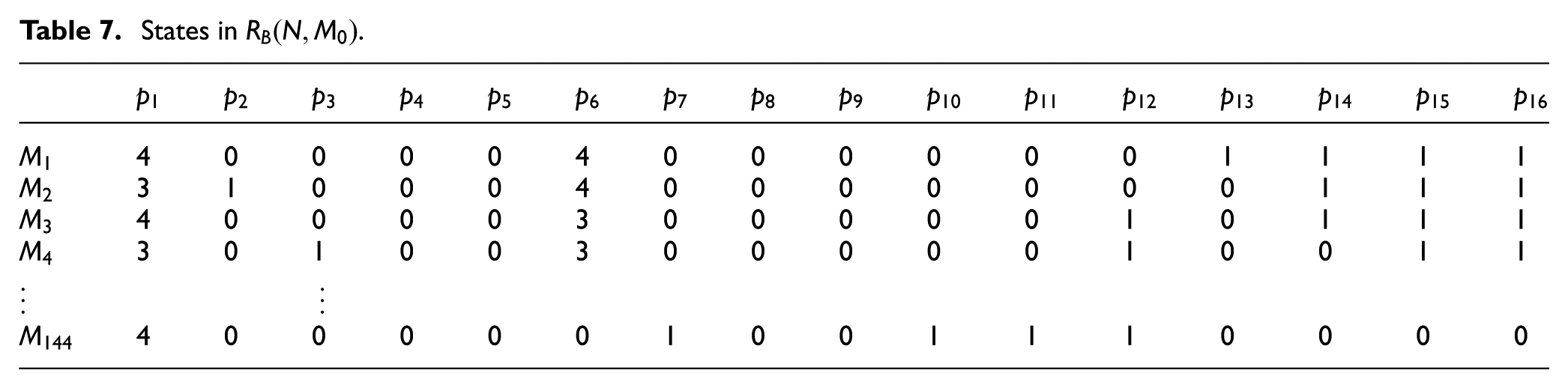
There are four SMSs,


Based on the SMSs, four *configurations are constructed by Definition 6 and shown as follows

By Theorem 2, we can find unreachable states of each *configuration. However, some of these states may be contained in the other *configurations that have less resources. Hence, it is necessary to find MUSs. By Definition 7, it is found that
MUS of *configurations.
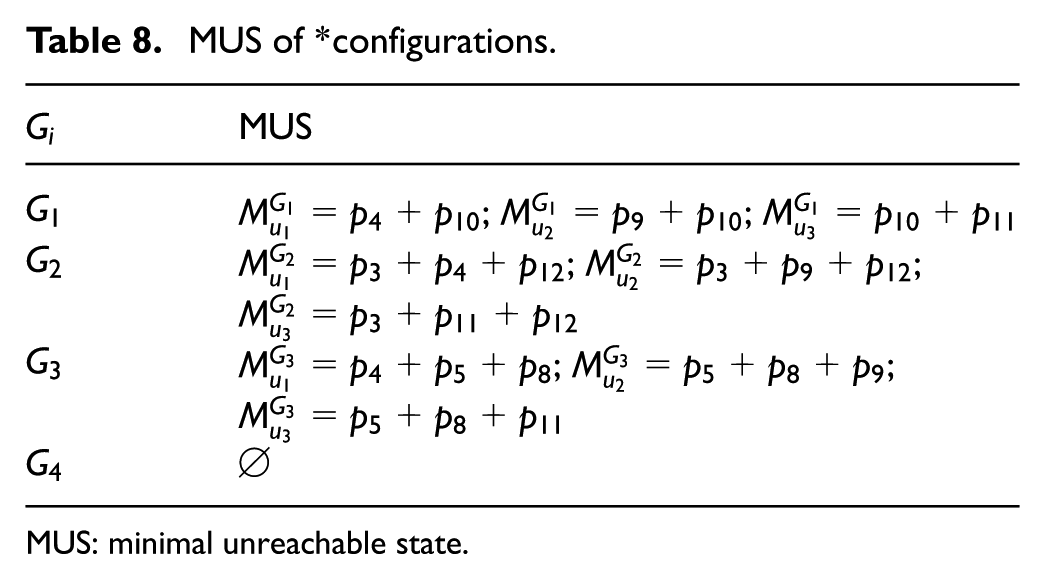
MUS: minimal unreachable state.
In the following, we need to compute the unreachable states of
States in

The rest unreachable states can be deduced by analogy. Finally, we find
Reachable states of

Computational complexity analysis and comparison
In this section, we compare the computational complexity of computing the state space of an LS3PR by the proposed method with that by RG. First, if RG is applied to find reachable states, supposing that k and t denote the number of reachable states and the number of transitions, respectively, for any state M in reachability set, one needs to compute subsequent states, which requires t steps. Thus, its computational amount is
Second, if we use the proposed method to compute reachable states, it is found that its computational complexity contains three parts. Supposing that there are m operation places and n resource places, computing the reachable states of theory permissive needs at most
Conclusion
This study presents a theory instead of RG to calculate the state space of an LS3PR. In deadlock prevention problems, we are committed to synthesizing optimal supervisors for plant nets. Hence, it is necessary to find all reachable states to synthesize an optimal or nearly optimal supervisor. The existing methods, such as RG, are difficult, even impossible, to find state space for a large net system due to its high computational complexity. This article pioneers the very first study to deal with a subclass of S3PR (LS3PR) by combinatorics. Excluding all unreachable states from the set of reachable states of theory permissive calculated by combinatorics, the left states are the reachable states of the considered LS3PR. Analysis shows its computational complexity is far lower than RG.
Footnotes
Academic Editor: Murat Uzam
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported in part by the National Natural Science Foundation of China under Grant No. 61673309, the Fundamental Research Funds for the Central Universities under Grant Nos. JB160401 and JBG160415, the Scientific Research Program Funded by Shaanxi Provincial Education Department under Grant No. 16JK1342, the National Natural Science Foundation of China under Grant No. 51607133, the Natural Science Basic Research Plan in Shaanxi Province of China under Grant No. 2016JQ5106, the Science and Technology Project of Shaanxi Province under Grant No. 2016GY-136, the Doctoral Research Startup Funds of Xi’an Polytechnic University under Grant No. BS1335, and the Innovation and Entrepreneurship Training Program of Xi’an Polytechnic University under Grant No. 2016125.
