Abstract
This article presents an efficient integrated approach on designing a non-blocking supervisor for the most general classes of Petri nets, called G-systems that allow multiple resource acquisitions. This work mainly focuses on developing a deadlock prevention policy with a polynomial computational complexity. First, an extraction algorithm of liveness requirement constraints is presented according to the concept of resource partial orders. By considering the different resource requirements of various processes, monitors are added for the uncontrolled G-system on the basis of those precise linear inequality constraints. Afterward, we explore an iterative control policy by utilizing the traditional mathematical programming method, which can ensure the liveness of the resultant controlled system. Comparing with the existing deadlock control policies reported in the literature, the proposed method can achieve a non-blocking controlled G-system with simple structure and high computational efficiency. Finally, a benchmark G-system example is used to substantiate the efficiency of the new method.
Introduction
Nowadays, deadlocks can cause the part or the whole stoppage in highly automated manufacturing systems, even leading to catastrophic results. Over the last two decades, a great deal of research has been focused on solving deadlock problems in a flexible manufacturing systems (FMS), receiving an enormous attention from both academic and industrial communities.1–3 The family of Petri net formalisms is a good choice for a flexible manufacturing system environment and has proven to be very useful in the modeling, analysis, simulation, and control of an FMS.4–6
Deadlock solution methods under the frame of Petri nets can be divided into three major categories: deadlock detection and recovery, 7 deadlock avoidance,8–12 and deadlock prevention.13–22 The first strategy is an online mechanism, which permits the occurrence of deadlock. If a system enters into a deadlock state, a recovery mechanism must be executed by reallocating the resources such that the deadlock is resolved. Due to the requirement of a large amount of data, the first one is usually used under the instances where deadlock phenomenon is not serious. Deadlock avoidance mainly focuses on keeping the system away from deadlock states. When a resource is allocated to a process, an online control policy at each system state is used to make a correct decision such that the forthcoming state is safe. The main purpose of deadlock prevention is to control requests for resources to ensure that the resultant system can no longer reach deadlock states, which is usually achieved by adding monitors (control places) and directed arcs to its uncontrolled model. 23 By contrast, deadlock prevention for FMS is widely acknowledged as one of the most effective deadlock resolution, leading to a vast stock of results.24–28,29,30,31
The deadlock prevention policies on the basis of structural analysis are typical application of Petri net techniques. Especially, since most deadlock control policies are developed according to the relationship between liveness and siphons, 32 the siphon-based methods play a prominent role in the development of liveness-enforcing supervisors (LES).33–39,49 Unfortunately, a siphon-based control method always suffers from the issues of complicated structure and high computational complexity when designing a controller. To alleviate the problem of structural complexity, Li and Zhou40–42 pioneer the theory of elementary siphons, which provide a full-blown avenue for designing a structurally simple supervisor. However, the computational complexity of supervisor designed by elementary siphons theory remains high since the complete siphon enumeration cannot be avoided. The computational efforts for a supervisor based on elementary siphons are lowered by utilizing the traditional MIP (mixed integer programming)-based deadlock detection method. 33 Based on the MIP method, the iterative deadlock prevention policies are explored in our previous work 43,44 for generalized Petri nets. Those MIP-based approaches to a large extent reduce the computational cost to design an LES. However, it is not surprising that the solvent of MIP problem is still NP-hard in theory. Therefore, how to lower the computational complexity of supervisor has been an interesting and significant problem in both practice and theory.
In order to develop a computationally efficient deadlock control policy, a deadlock avoidance policy of polynomial complexity is proposed in Park. 45 Motivated by the seminar work in Park 45 and Zhao et al., 44 an extraction method of liveness control specifications is first expounded for the most general class of Petri nets in the literature, called G-systems. The proposed method aims to achieve the reasonable resource configuration among parallel execution and competing processes according to the liveness requirements. The main contribution of this algorithm lies in the fact that its computational complexity is polynomial and potentially redundant constraints are eliminated. By combining the concept of resource partial orders and MIP-based method, we propose an iterative method to design a non-blocking supervisor with precise monitors added at each iteration. A case study indicates that the proposed policy can usually generate a structurally compact supervisor with more permissive behavior.
The rest of the article is organized as follows. Section “LICs extraction method for G-systems” establishes a method of computing linear inequality constraints (LICs) for G-systems with respect to the concept of resource partial orders. Section “Deadlock control policy based on MIP method” develops an iterative control method for G-systems by combining the MIP-based deadlock detection method with the results provided in section “LICs extraction method for G-systems.” A typical G-system example is illustrated in section “The application of the proposed policy” to validate the results in sections “LICs extraction method for G-systems” and “Deadlock control policy based on MIP method,” and some comparison and discussion among different deadlock control policies for G-systems are made subsequently. While section “Conclusion” concludes the article and suggests some directions for future research. Some fundamental concepts of Petri nets and G-systems used throughout this article are listed in Appendices 1 and 2.
LICs extraction method for G-systems
This work considers deadlock problems for a class of manufacturing-oriented Petri nets, namely, G-systems first proposed in Barkaoui et al. 46 For more details, the preliminaries of Petri nets and the definitions of G-systems can refer to the previous work in Zhao and Hou. 47
First, this section presents an extraction algorithm of LICs under given resource partial orders for a G-system configuration. As known, a G-system net with concurrent processes may fall into permanent blocking since the circular wait of shared resources may occur among multiple processes. In order to eliminate deadlocks, it is necessary to prevent the occurrence of problematic states effectively. To achieve this, a deadlock avoidance policy in polynomial complexity is proposed in Park 45 for an S4PR in terms of resource requirement partial orders. Inspired by the method in Park, 45 we first extend this notion to G-systems that is a more general class of Petri nets than S4PR. After that, the redundant LICs are removed by the proposed algorithm, and the liveness of the controlled system would not be changed due to their removal. It means that a more compact structure of the resultant supervisor can be obtained by the proposed method.
Under different resource requirement partial orders, the supervisor should appropriately restrict the system resources allocation of various requested operations such that the presence of illegal states can be permanently prevented. The proposed method aims to design a non-blocking controlled system by properly supervising resources allocation among multiple concurrent processes. Consequently, the resulting controlled system is the synchronous synthesis of a G-system net model and its supervisor via shared transitions, which is defined as follows.
Definition 1
Let
Definition 2
Let
Let
Let r be a resource and
Let
Example
Taking the G-system net in Figure 1(a) as an example, we have

(a) A G-system
Definition 3
Let
A resource place in a net system is modeled with a singleton place whose token capacity represents the ability of processing raw parts concurrently.
Example
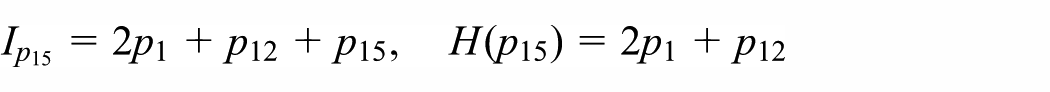
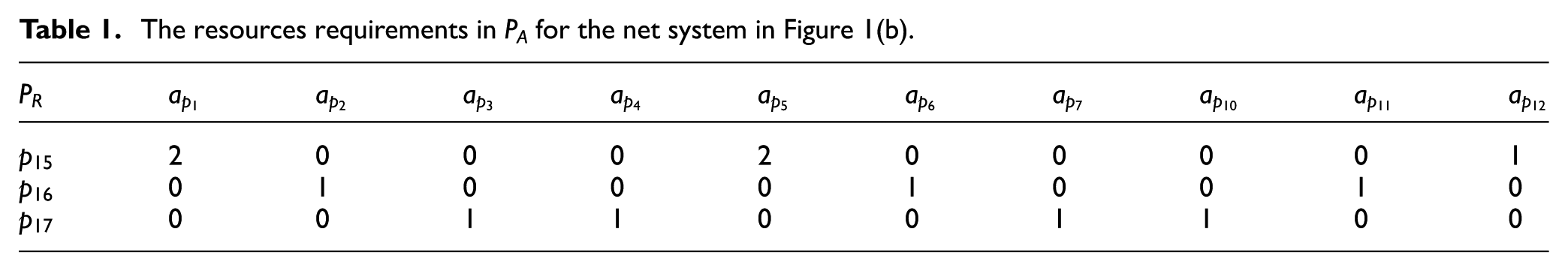
From the definition of a G-system, there are four minimal P-semiflows that can be computed in Figure 1(b) shown as below, which is associated with resource places
Definition 4
Let
Example
Take the net shown in Figure 1(b) as an example. For operation place
The resources requirements in PA for the net system in Figure 1(b).
By considering a G-system under different resource requirements, monitors should be added to the net system in order to prevent the controlled system entering into the forbidden markings, the policy under resource partial orders is presented as follows.
Definition 5
Let

and

Let
The neighborhood set

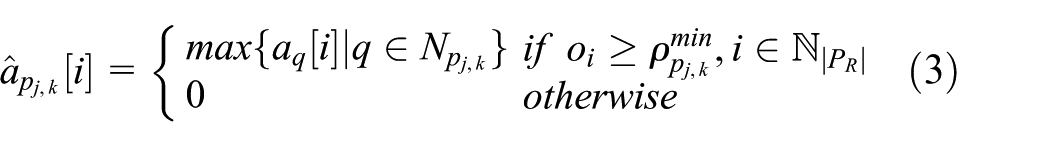
Definition 5 formalizes the liveness control specification of resources requirements, which can be expressed by a set of generalized mutual exclusion constraints (GMECs). The neighborhood set
Example
Consider the net shown in Figure 1(b) as an example and assume that the given resource partial order is
The computation of the neighborhood sets for the net system in Figure 1(b).

By utilizing Definition 5, the adjusted resource allocation requirements can be derived as shown in Table 3.
The adjusted resources requirements in

In order to prevent the system entering into deadlock states, another set of linear LICs should be computed according to the adjusted resource allocation requirements
Definition 6
Let
Example
From Definition 6, the following results are obtained for the net in Figure 1(b)
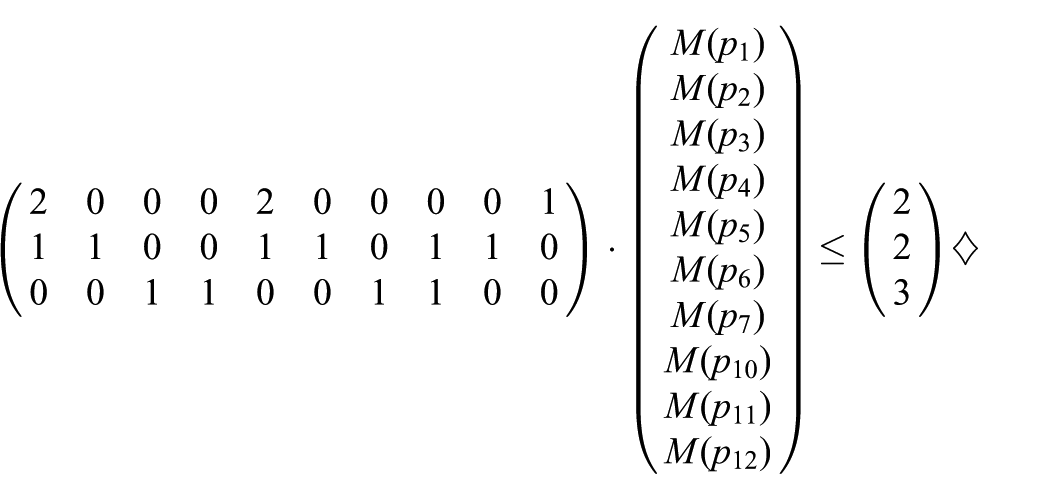

In Figure 1(b), when assuming that the places are ordered in the incidence matrix according to the sequence
Definition 7
Let
Definition 7 is widely used in the deadlock control and analysis area of Petri nets. Note that a live Petri net guarantees deadlock-freedom no matter what firing sequence is chosen but the converse is not true. Therefore, deadlock resolution methods mainly aim to obtain an LES for a Petri net model prone to deadlocks.
Definition 8
A G-system GS is well-formed if there exists an initial marking
Definition 9
A G-system
Remark 1
Note that the concepts of liveness and non-blockingness are totally different. The concept of non-blockingness is originally defined based on the theory of automata and formal language. Actually, in the frame of Petri nets, there is no standard definition of non-blockingness of deadlock control in the existing literature. In the article, Definition 9 first gives its formal definition for the most general class of Petri nets, called G-system. Note that the non-blockingness is an important property of a controlled G-system, which indicates that the system can always reach a final marking from any reachable state. In particular, the net structure of a G-system GS is different from that of other generalized Petri net classes. Since a G-task GT is circuit-free, that is, it is inadmissible to have loops in a G-task. As a result, a G-system GS is not strongly connected. To analyze the liveness of the given G-system, its corresponding augmented G-system
Proposition 1
Let
Proof
From Definition 5(2), the policy-imposed constraints on the system operations are expressed by the requirements that no resource is over-allocated with respect to the adjusted resource allocation represented by
After the liveness requirement constraints are established, the resource requirements of operations are then reallocated according to those constraints. Next, the precise LICs extraction algorithm is summarized as follows.

Remark 2
Based on the concept of resource partial orders, Algorithm 1 presents an extraction method of the precise LICs. Note that the key point of Algorithm 1 is to derive the adjusted resource requirements. According to the definition of partial orders, the priority of resources occupied or released by operation places may be different. Therefore, it is crucial to properly adjust the resource allocation when considering the certain resource partial orders. Furthermore, it is worth noting that some variables in Algorithm 1 can be derived by utilizing some domestically developed softwares, such as INA and MIPA, which are useful in shortening the computation time of LICs and supervisors synthesis.
Let
For more details, all original and adjusted resources requirements are represented by conjunction sets of GMECs,
Example
Taking the net in Figure 1(b) as an example, the LICs

Subsequently, the potential redundancy of those constraints can be further systematically removed by Algorithm 1 such that a structurally simple LES can be derived. For more details, we have
Theorem 1
Given a G-system
Proof
Give any G-system, LICs can be derived by Algorithm 1 in polynomial time, whose complexity is established from the following statements: (1)
Deadlock control policy based on MIP method
Although the liveness control specification is represented by a set of GMECs with respect to the ordering imposed on the resource set for any G-system net model, it is still a point solution to the underlying control problem. As is well known, deadlock occurs directly due to insufficiently marked siphons in generalized Petri nets. Thus, siphon-based control method requires the siphon enumeration, which is a task of nonpolynomial complexity as the number of net places increases. Fortunately, for the class of structurally bounded generalized net, the work in Chu and Xie 33 presents an additional sufficient condition of potential liveness that takes the convenient form of an MIP formulation of polynomial size with respect to the net elements shown as follows. It indicates that the aforementioned liveness sufficiency condition essentially provides an automatic correctness verification tool of deadlock control policy.
Definition 10
Let
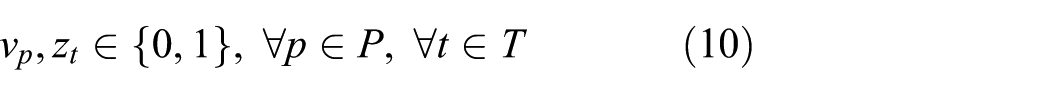
By considering the traditional linear programming method shown in Chu and Xie,
33
a siphon S in a structurally bounded net can be determined by solving an MIP problem based on two binary variables
Notation 1
Due to Notation 1, it is shown that any p with
Theorem 2
Let

where

s.t.




Proof
In order to understand the formulation of this theorem, notice that equations (6) and (9) imply that any fireable transition t at M has
Theorem 3
Let
Proof
If
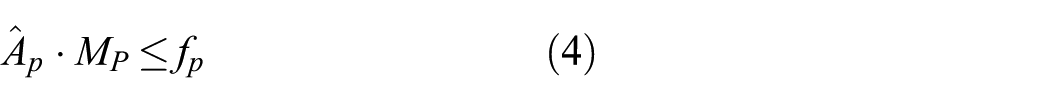
Given a bounded Petri net prone to deadlocks, the MIP-based method can provide an efficient and rapid deadlock detection approach to compute the deadly marked siphons. Next, monitors should be added to those insufficiently marked siphons such that the liveness of the controlled systems is ensured. In the frame of Petri nets, the LES consists of a set of monitors and a set of transitions, which is a subset of the set of transitions in the plant net model.
Definition 11
Let
Let
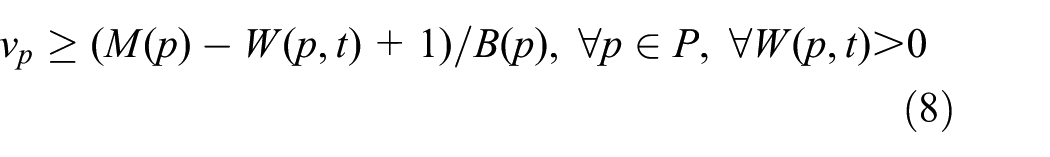
Additional monitors satisfy the following conditions: (a) (b) (c)if
Proposition 2
Let
Proof
Note that permanent blocking may occur in some operations if each process requires further continuation of shared resources currently held by some other processes. To avoid it, the proper resource allocation is needed under any given resource partial order. To achieve it, each additional monitor
The compound of a G-system model and its supervisor is called the controlled G-system, which is the synchronous synthesis net defined as follows.
Definition 12
Let
Corollary 1
Let
Next, we establish an iterative algorithm such that the non-blocking controlled system

Remark 3
By utilizing the MIP-based detection method, Algorithm 2 proposes an iterative policy for designing non-blocking controlled systems. Note that the MIP provides a highly computational efficiency throughout the iterations. Based on place-invariant (PI) control method, a monitor is added to enforce the controllability constraints derived by Algorithm 1 at each step. When the condition in Theorem 3 holds, the iterations would be completed. That is to say, the resultant net system would not generate the deadly marked siphons, which implies the resultant net system is non-blocking. Subsequently, the non-blocking controlled G-system
Example
Considering the net in Figure 1(b) as an example, a monitor
Proposition 3
Algorithm 2 always terminates and its termination gives a non-blocking controlled system
Proof
To properly allocate shared resources, the maximal resource requirements of job operations should be adjusted in terms of a given resource partial order. When an uncontrolled G-system
The computational complexity of the proposed algorithms is analyzed as follows.
Theorem 4
Let
Proof
From Algorithm 1, it is worth noting that the number of LICs set is no more than that of resource places, that is,
The application of the proposed policy
A G-system example
Take the augmented G-system in Figure 2 as an illustrative example. Obviously, the given G-system contains three processes






An augmented G-system
Afterwards, Table 4 lists the resource requirements of all operation places due to Definition 4.
The resource requirements in

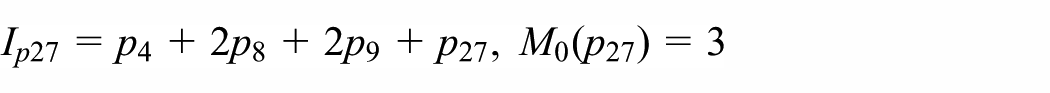
Consider all processes executed under the resource partial order
For job type
For job type
Accordingly, the adjusted resource requirements
The adjusted resource requirements in

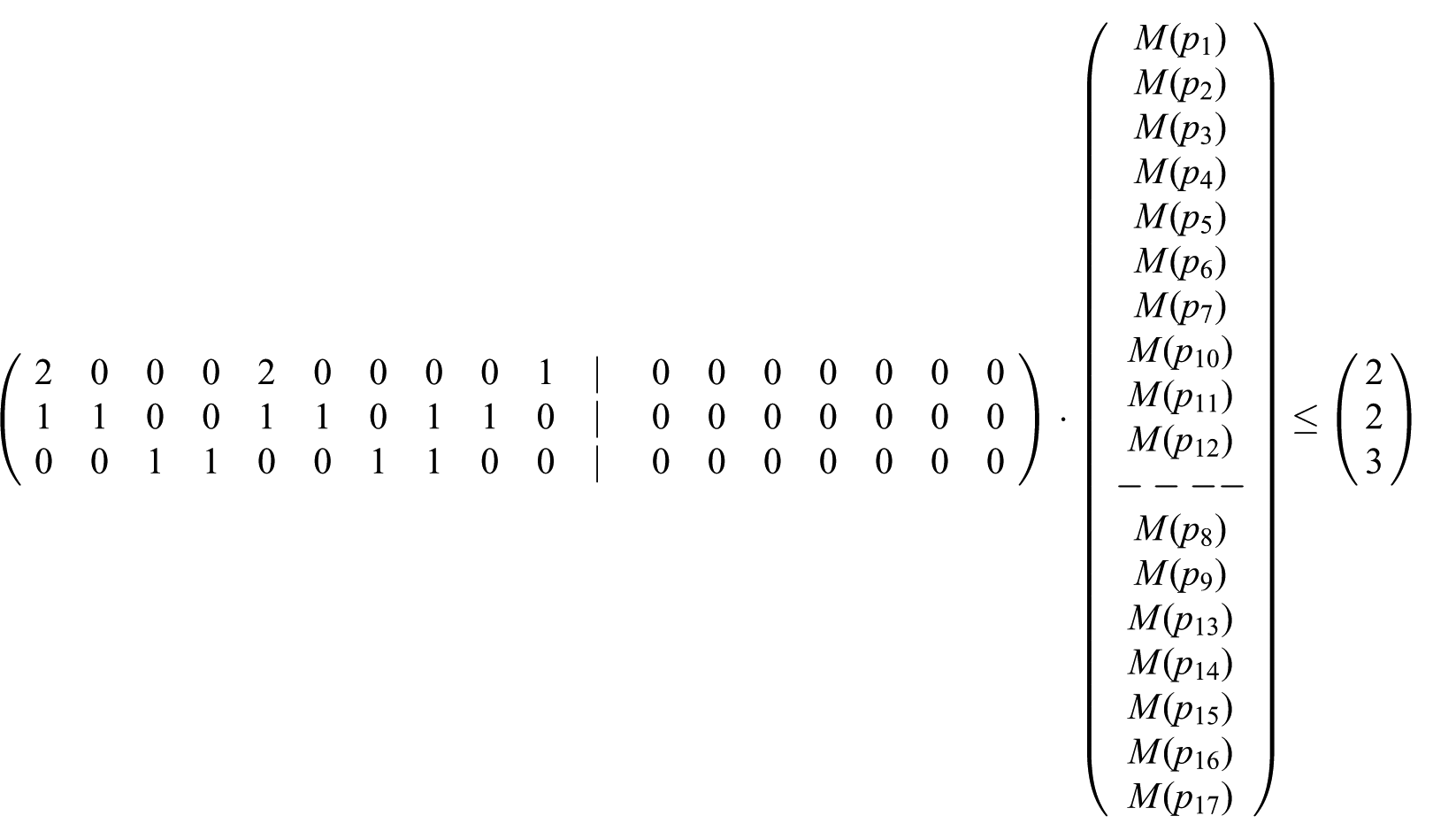
From Definition 5, the new set of LICs is computed and transformed into a matrix form as follows

Consequently, three precise control constraints of the liveness requirement are derived as follows
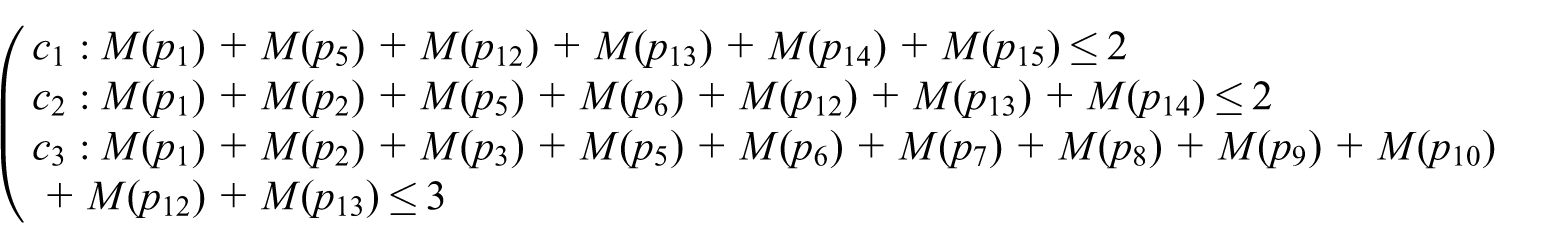
As previous results mentioned, each LIC is implemented by a monitor to ensure the liveness of the controlled system. To simplify the control constraints, Algorithm 2 is carried out further to design a structurally simple LES. As a result, it is shown that one monitor is only needed for the net model in Figure 2, whose related results are depicted in Table 6.
Monitors for the net model in Figure 2.

Comparison study
As is gradually recognized, the existing control policies developed by structural analysis technique are hard to achieve optimal performance in G-systems.41,42 In order to dissect deeply deadlock control methods in the literature, we review and compare the proposed method with those in Zhao and collegues41,47 through a typical G-system benchmark shown in Figure 2. It is easy to verify that the original net model has 123,595 reachable states. Among them, there are 123,060 legal markings.
From elementary siphon-based method in Li and Zhao,
41
the net system consists of 13 strict minimal siphons (SMSs), 5 of which are elementary ones. The resultant supervisor including five additional monitors is computed only for elementary siphons, namely
Similarly, the method proposed in Zhao and Hou 47 is then applied to the net in Figure 2. As a result, three monitors depicted in Table 8 can be computed. It can be verified that the controlled G-system in Zhao and Hou 47 has 123,060 legal markings, which indicates that the corresponding supervisor affords maximally permissive behavior for the original G-system.
As for the proposed method, one monitor
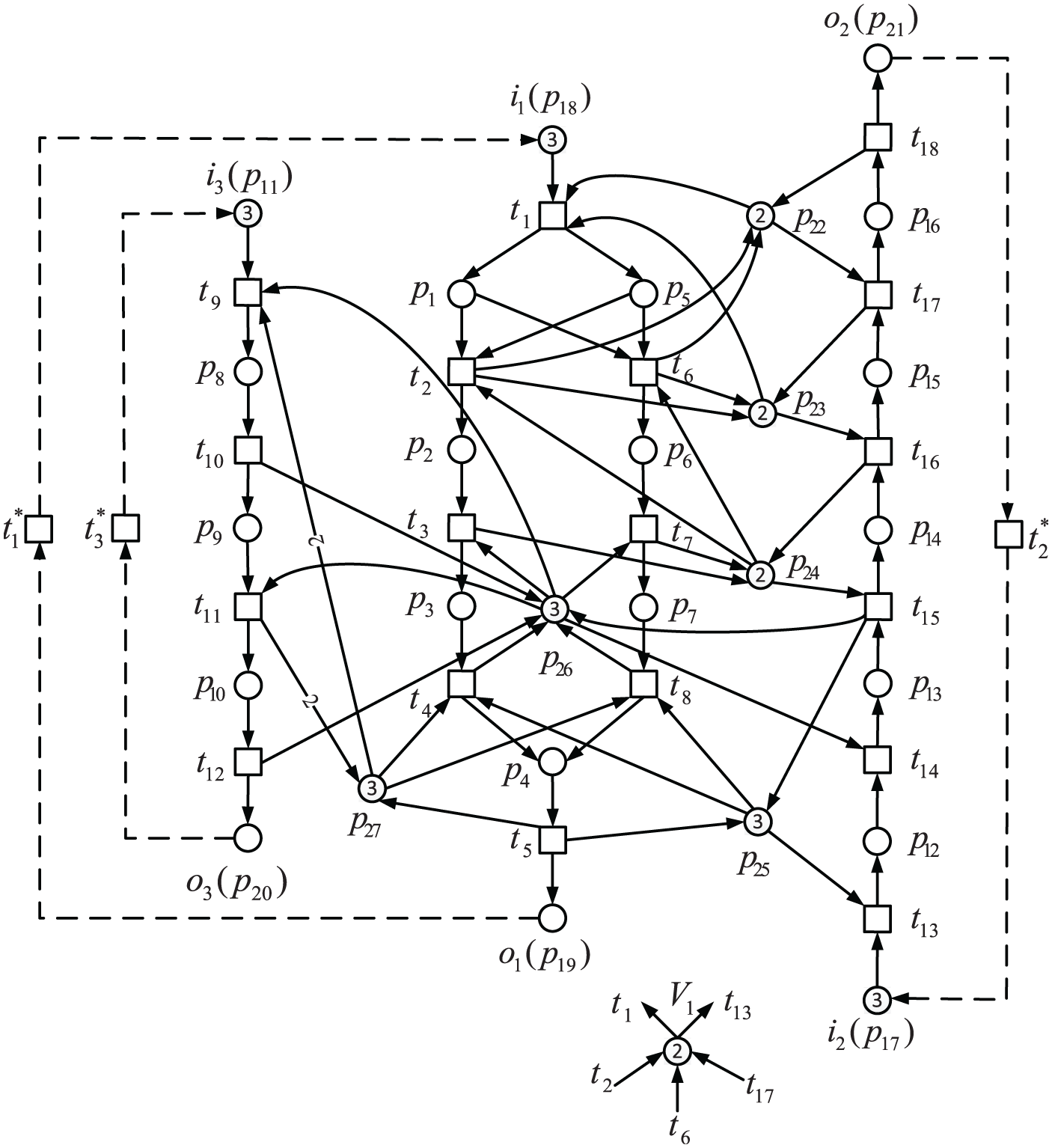
The controlled G-system net
Performance analysis and comparison of non-blocking supervisors.
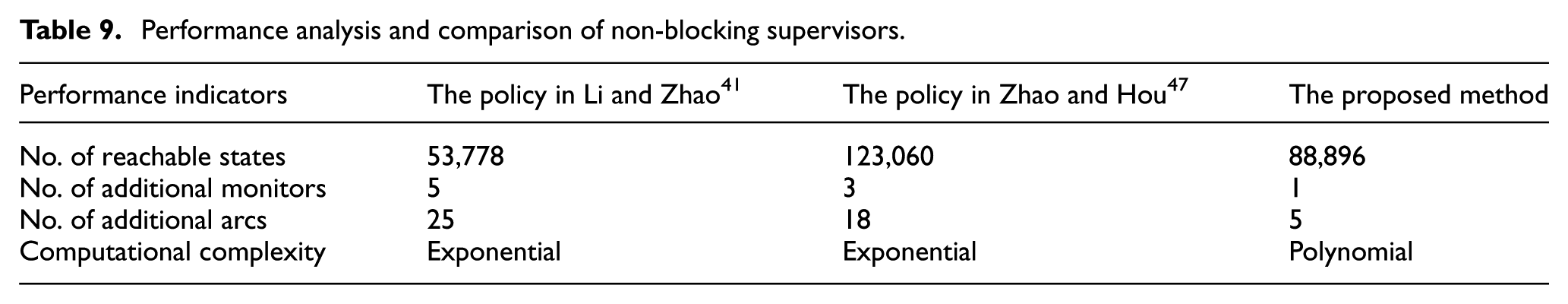
In conclusion, although the concept of elementary siphon can usually lead to structurally simple liveness-enforcing monitor-based supervisors, the number of monitors designed by the proposed method is less than those of Zhao and colleagues.41,47 Furthermore, the complete siphon enumeration-based methods would run into bottlenecks as the size of net model increases due to the problems of the computational complexity and behavioral permissiveness. By contrast, the method proposed in this article is more appropriate for large-scale systems.
Discussion
From the behavioral permissiveness point of view, the proposed deadlock prevention policy does not provide an optimal controlled system since it reduces the resource utilization to some extent, which indicates that some good states of the net model may be eliminated. On one hand, the behavioral permissiveness of the non-blocking supervisor depended on the selected resource partial orders. Based on the proposed method, the utilization of system resources may be limited due to different resource partial orders. Determining how to find an optimal resource partial ordering has been an interesting yet significant problem from view of the optimal trade-off between structural minimality and permissive behavioral maximality. On the other hand, since all output arcs of a monitor are led to the source transitions of the net system, which limits the number of workpieces being released into and processed by the system. Consequently, the proposed method is in general not optimal, from the behavioral permissiveness standpoint. Therefore, the key point of deriving a supervisor with the best behavioral permissiveness is to optimize the resource utilization and allocation. Furthermore, a designer always hopes to have a set of concise controllability constraints. To obtain a smaller set of monitors, the proposed method presents an MIP-iterative algorithm, which can remove redundant constraints such that the supervisor has more precise structure.
Taking the net in Figure 2 as an example, there are three precise inequality constraints, namely
Conclusion
Existing deadlock prevention policies developed by siphons control always face the issues of high computational complexity and structural complexity since siphons enumeration is computationally expensive or impossible if the structural size of a plant model is large. To improve the computational efficiency and structural simplification of supervisors design, this article proposes an MIP-based iterative deadlock prevention policy under resource allocation orders for the most general classes of Petri nets.
Since resource allocation of multiple processes directly affects the dynamic property of a net system, an efficient control method is developed by properly supervising system resource requirements. By utilizing the concept of resource partial order, a set of LICs is computed and designated as the liveness requirements conditions, from which the precise control constraints are extracted by a polynomial algorithm. After that, we establish an MIP-based iterative algorithm to derive a non-blocking supervisor for G-systems. Finally, a case study is shown to demonstrate the proposed policy and used to compare them with the state-of-the-art methods. Followed by the discussion in this article, how to derive the LICs of key resources to design an LES with better performance should be considered in the future.
Footnotes
Appendix 1
Appendix 2
Academic Editor: Tatsushi Nishi
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the National Natural Science Foundation of China under Grant Nos 61563045 and 61104110.