Abstract
The purpose of this systematic review is twofold: (1) to critically analyse relevant technology acceptance theories and identify the most suitable frameworks for understanding user behaviour and technology adoption in Library and Information Science (LIS) research, and (2) to explore the potential of UTAUT2 in qualitative research within the LIS context. Specifically, it answers the research question: How has UTAUT2 been applied in qualitative studies to understand user behaviour and technology adoption? To ensure a robust dataset, a systematic search was conducted across four major academic databases SCOPUS, Web of Science, LISTA and Google Scholar. The literature review provides a comprehensive overview of UTAUT2, offering qualitative insights and highlighting its applicability to LIS research. This is the first study to critically highlight technology acceptance theories, offering detailed criticisms that enhance LIS researchers’ understanding and ability to decide on appropriate technology adoption theories. The findings reveal that a substantial body of research employs UTAUT2 in qualitative contexts, underscoring its relevance and value. This study contributes to the theoretical discourse by clarifying the qualitative dimensions of UTAUT2 and providing valuable insights for researchers and students in LIS.
Keywords
Introduction
Theory is fundamental to advancing academic inquiry, as it provides structured frameworks for evaluating established knowledge, questioning assumptions, and refining research questions, methodologies, and interpretations (Leckie et al., 2010). Developed through systematic observation and testing, theory explains natural and empirical phenomena and encompasses facts, laws, predictions, and validated assumptions, as illustrated in rational choice theory, grounded theory, and critical race theory (Abend, 2008; Cherry, 2016; Hammersley, 1995). Despite its central role, selecting an appropriate theoretical framework often presents a significant challenge, which can hinder scholarly progress.
Theory assists researchers in identifying relevant variables, recognising confounding factors, interpreting results, and transforming findings into practical outcomes (Leckie et al., 2010; Wise & Shaffer, 2015). Within Library and Information Science (LIS), theoretical and empirical discourse has shaped both philosophical and practical orientations (Herold, 2001; Paisley, 1993). As an applied discipline, LIS addresses the lifecycle of documents and employs various techniques, procedures, and tools to manage and regulate information. Its empirical research supports service-oriented objectives such as education, preservation, and communication, while also contributing to foundational debates in the Philosophy of Information (Floridi, 2002).
LIS, as an applied form of the Philosophy of Information (PI), has the potential to contribute to the advancement of PI itself, rather than relying solely on pre-established philosophical foundations (Floridi, 2002). Applied disciplines, such as management, nursing, and public administration, are rooted in practical contexts, and LIS clearly aligns with this definition (Swanson & Chermack, 2013). However, LIS continues to face criticism for lacking a coherent set of explicit theories, a challenge that has sustained debate over its academic status and theoretical foundations (Hjørland, 2000).
This theoretical gap is not unique to LIS. In the field of Information Systems (IS), the absence of a substantial body of original, falsifiable theories has also been observed, with many models adapted from disciplines such as psychology, sociology, and management (Craig & Routledge, 1998). For example, Total Quality Management (TQM) is frequently applied in IS research despite not originating within the IS domain (Hjørland, 2000).
Nevertheless, LIS maintains a strong philosophical dimension, given the nature of its inquiries (Nitecki, 1997). It has been defined as the academic study of the creation, organisation, management, communication, and use of recorded information a scope that underpins professional practices such as librarianship, archiving, information retrieval, and records management (Bawden & Robinson, 2016). Theoretical perspectives, including critical theory, offer valuable insight into how broader societal changes such as the rise of data analytics are influencing LIS decision-making practice (Roy, 2024, 2025).
In this context, the present study critically examines technology acceptance theories applicable to LIS, assessing their strengths, limitations, and suitability for qualitative research. It focuses on models such as TAM2 and UTAUT, with particular attention to the potential of UTAUT2 to provide deeper insights into technology adoption in LIS environments. By doing so, the study contributes to ongoing discussions on LIS’s theoretical development, offering a qualitative perspective that complements the Philosophy of Information and strengthens the conceptual foundations of the discipline.
Problem Statement
Theoretical frameworks are essential for guiding research design, identifying key variables, and interpreting findings. In Library and Information Science (LIS), the absence of a well-defined theoretical foundation has been a topic of scholarly debate since the 1930s (Hjørland, 2000). While some argue that LIS lacks robust theoretical models, others highlight its potential as an applied discipline within the broader Philosophy of Information (Floridi, 2002).
Technology acceptance theories offer valuable insights into how individuals adopt and use technological innovations. However, many models used in LIS are adapted from other disciplines such as Psychology and Management rather than developed specifically for LIS contexts (Craig & Routledge, 1998). Among these, the Unified Theory of Acceptance and Use of Technology (UTAUT) and its extended version, UTAUT2, have gained prominence. Although UTAUT2 is widely used in quantitative studies, its application in qualitative LIS research remains limited.
This study addresses this gap by critically analysing technology acceptance theories, evaluating their relevance to LIS, and exploring the potential of UTAUT2 in qualitative research. By doing so, it aims to strengthen the theoretical foundation of LIS and enhance understanding of technology adoption within the discipline.
Research Question
The primary research question guiding this systematic review is:
Study Objectives
• •
Literature Review
This study looked at many other influential theories and models, such as TAM2 Venkatesh and Davis (2000) and UTAUT Venkatesh et al. (2003), that have been widely used in academic research on technology acceptance. Ovwasa (2019) investigated and generated the most cited influential theories and models in a technology acceptance study. Similarly, Alshammari and Rosli (2020) examined various technology acceptance models and theories to allow future researchers to embrace an appropriate model that aligns with their empirical investigations involving numerous technologies.
Influential Theories and Models in Technology Acceptance Research
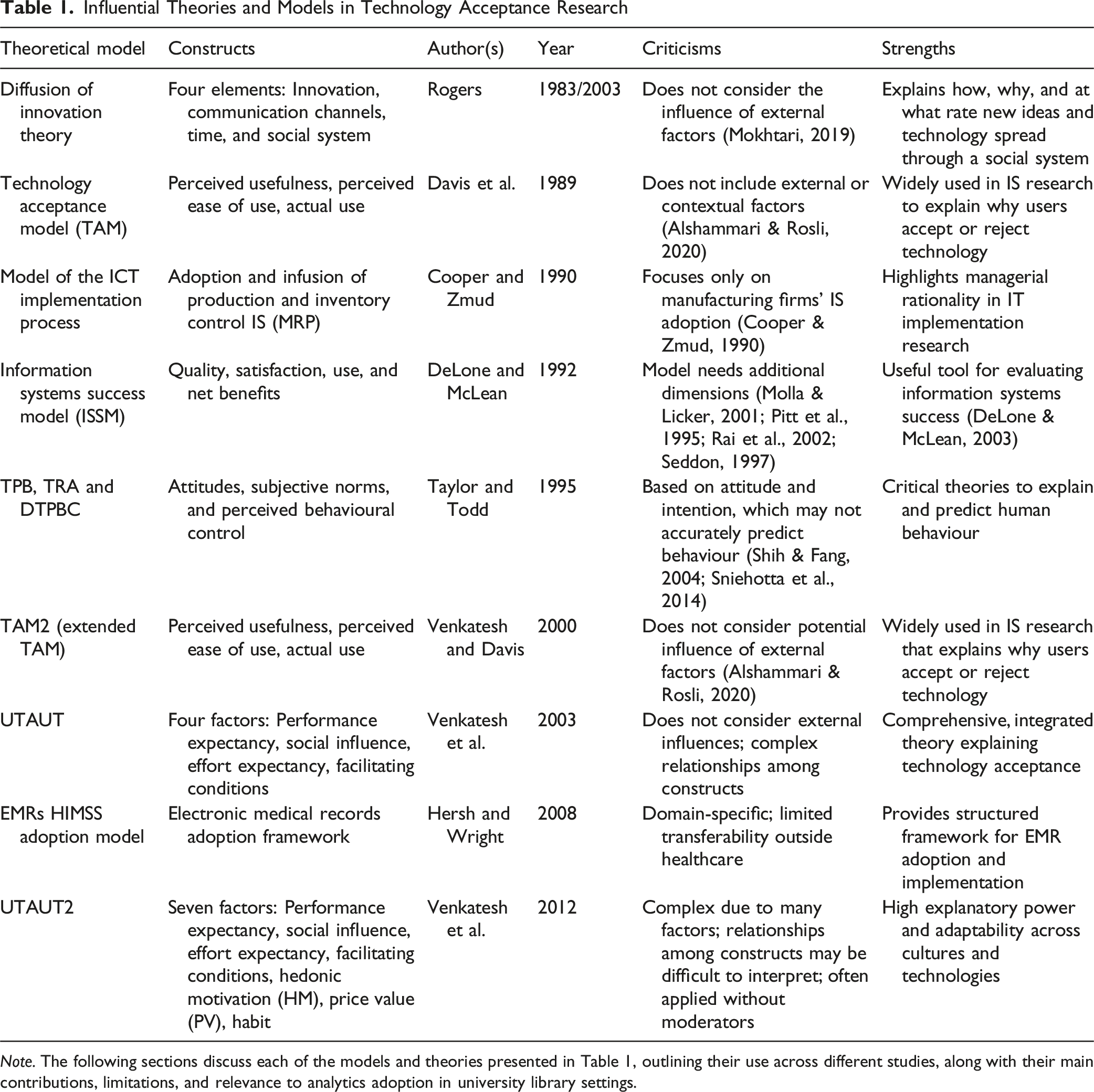
Note. The following sections discuss each of the models and theories presented in Table 1, outlining their use across different studies, along with their main contributions, limitations, and relevance to analytics adoption in university library settings.
Diffusion of Innovation Theory (DOIT)
The Diffusion of Innovation Theory (DOIT) is a theoretical framework used to explain how, why, and at what rate new ideas and technology spread through a social system (Rogers et al., 2014). The theory suggests that new ideas, products, and practices spread from one group or individual to another through communication, imitation, and adaptation. The rate of adoption and the success of innovations depend on several factors, such as the degree of perceived innovation, the degree of compatibility with existing practices and beliefs, the degree of complexity, and the degree of social influence (Kaminski, 2011; Rogers et al., 2014).
However, Bikhchandani et al. (1998), argue that this theory fails to capture the complexities of long-term adoption and the factors influencing innovation abandonment or persistency. Valente (2010) also argues that the theory fails to fully account for the social dynamics and complexities involved in the diffusion process. Another limitation of DOI is that it does not consider the influence of external factors. Studies such as Maruping et al. (2017) and Mokhtari (2019) identified external factors influencing individuals’ perceptions of using technologies. These factors included environmental, personal, technical, economic, and reliability. Roy et al. (2018) found that factors such as financial conditions and social trends can influence the adoption of new products and services and can be beyond the scope of the theory. Moreover, Rogers (2003) acknowledges this limitation and suggests the integration of other theoretical perspectives to address these factors.
Technology Acceptance Model (TAM)
The Technology Acceptance Model (TAM), a theory in the discipline of information systems created by Davis in 1989, offers a conceptual framework for understanding how individuals adopt and utilise technology. This theory focuses on technology acceptance and explains user behaviour across various emerging computing technologies, considering the user population. Davis et al. (1989) ‘s theory provides practical insights and supports theoretical and economic perspectives in this field. The Technology Acceptance Model (TAM) states that the perceived ease of use (PEU) of a technology has an impact on the perceived usefulness (PU) of that technology (Davis et al., 1989). In other words, if users find a specific technology to be easily usable, there is a greater likelihood that they will also see it as applicable. TAM argues that PEU and PU influence people’s attitudes towards technology use. When users perceive a particular technology as both easy to use and helpful, it leads to the development of a positive attitude towards using that technology. However, many researchers have broadly criticised TAM (Malatji et al., 2020). For example, Ang et al. (2015) and Shan and King (2015) noted that TAM could not underline behaviour to be quantified reliably in the observed study, owing to various subjective elements, such as values and norms of societies, individual characteristics and personality attributes. Alshammari and Rosli (2020) supported this statement. Further, they noted that utilising the Technology Acceptance Model (TAM) without any extensions is regarded as a general theory, and this theory may not offer a comprehensive explanation of users’ technology acceptance.
Model of the ICT Implementation Process
Cooper and Zmud (1990) examined the interaction of managerial tasks and the adoption and infusion of production and inventory control information systems (Material Requirements Planning: MRP). Using a sample of manufacturing firms, Cooper and Zmud (1990) found that the relationship between managerial tasks and information technology impacts the adoption. The findings suggest that rational decision models may be helpful when explaining adoption.
Cooper and Zmud’s (1990) study investigated the critical issues related to IT implementation processes and how to maximise the benefits of IT investments based on Rogers et al. (2014) Diffusion of Innovation Theory. Cooper and Zmud’s (1990) study’s primary contribution is the importance of positioning managerial rationality appropriately in IT implementation research.
However, the main limitation of the ICT Implementation Process Model provided by Cooper and Zmud (1990) is that the process focuses on adopting and infusing Production and Inventory Control Information Systems in manufacturing firms. Furthermore, the finding model focuses on how rational and political forces can be fruitful throughout the IT implementation stages (Cooper & Zmud, 1990).
Information Systems Success Model (ISSM)
The Information Systems Success Model (ISSM) is a theoretical framework developed by DeLone and McLean (1992) to evaluate the success of information systems (IS). Later, in 2002, DeLone and McLean published an updated version of the model, the D&M IS Success Model (DeLone & McLean, 2003).
This model was based on the premise that information system success depends on six dimensions: information quality, system quality, service quality, system use, user satisfaction, and net system benefits DeLone and McLean (2003). The model suggests that each of these dimensions is equally important for a system to be successful. The ISSM has been used extensively in information systems and is a valuable tool for evaluating the success of information systems (DeLone & McLean, 2003). The model has been used in various contexts, including healthcare, finance, education, and government.
Although many researchers tended to justify their empirical measurement of IS success by citing DeLone and McLean (1992), many criticised the model after the first information system success model was published (Zaineldeen et al., 2020). For example, Molla and Licker (2001), Pitt et al. (1995), and Rai et al. (2002); Seddon (1997) stated that the model is insufficient and needs additional dimensions. According to Cerná (2014), reducing the risk of adopting information systems requires proactive measures to identify vulnerabilities. Weaknesses in implemented systems are often attributed to limitations within the organisation, such as a lack of skilled personnel, time, or financial resources (Cerná, 2014).
Theory of Planned Behaviour (TPB), Theory of Reasoned Action (TRA) and the Decomposed Theory of Plan Behaviour Comparison
The Theory of Planned Behaviour (TPB) is a cognitive theory of human behaviour developed by Ajzen (1985). This theory is an extension of the Theory of Reasoned Action (TRA), derived from the work of the social psychologist (Ajzen, 1985). The TPB proposes that behavioural intentions, a function of attitudes, subjective norms and perceived behavioural control, are the immediate determinants of behaviour (Ajzen, 1991; Madden et al., 1992).
The dissimilarity between these two theories is that the theory of planned behaviour has added perceived behavioural control as the determinant of behavioural intention that affects perceived behavioural control. Both theories assume that humans are rational and systematically use the information available to make decisions (Chang, 1998; Madden et al., 1992).
The Decomposed Theory of Planned Behaviour (DTPB) is an extension of the TPB that examines the structure of its components in more detail (Taylor & Todd, 1995). The theory looks at the components of attitude, subjective norms, and perceived behavioural control in terms of their antecedents and consequences.
According to Taylor and Todd (1995), the Decomposed Theory of Plan Behaviour (DTPB) examines the relationships between behaviour, intentions, attitudes, and other factors to identify those most likely to predict behaviour. The Theory of Planned Behaviour (TPB), Theory of Reasoned Action (TRA) and Decomposed Theory of Planned Behaviour (DTPB) are critical theories used to explain and predict human behaviour (Shih & Fang, 2004). The TPB, TRA and DTPB are based on attitude and intention, which may not necessarily accurately predict behaviour (Sniehotta et al., 2014). While the TPB, TRA and DTPB effectively explain individual behaviour, they do not consider broader social and cultural contexts. For example, these theories do not consider the influence of family and peer groups on behaviour. A study by Conner and Armitage (1998) highlights the need to incorporate emotions into the TPB framework for a more comprehensive understanding of behaviour.
Technology Acceptance Model 2: (TAM2)
The Technology Acceptance Model (TAM2) was developed by (Venkatesh and Davis, 2000). TAM2 is an extension of the original Technology Acceptance Model (TAM) developed by (Davis, 1989). This model is widely used in information system research to explain why users accept or reject a particular technology. TAM2 has been used to understand user adoption of various technologies such as websites, mobile apps, and digital products (Fathema et al., 2015; Malatji et al., 2020; Nadri et al., 2018; Venkatesh and Davis, 2000). TAM2 attempts to explain users’ decision-making process when using or not using a particular technology.
However, studies such as Alshammari and Rosli (2020) stated that (TAM2) primarily focuses on the influence of users’ behavioural intention through the Perceived Usefulness (PU) construct. The model does not consider the potential influence of these external factors through the Perceived Ease of Use (PEU) construct, which may reveal additional existing relationships. The model also does not consider the influence of other factors, such as the influence of peers, on the user’s attitude towards technology (Venkatesh et al., 2003).
The Unified Theory of Acceptance and Use of Technology Theory (UTAUT)
The Unified Theory of Acceptance and Use of Technology Theory (UTAUT) model was developed by Venkatesh et al. (2003) to evaluate information systems and information technology use in institutions. UTAUT is based on the eight main theoretical models. These are: 1. The Personal Computer Usage Model, 2. Innovation Diffusion Theory, 3. Technology Acceptance Model, 4. Theory of Reasoned Action, 5. Combined TAM-PBT, 6. Theory of Planned Behaviour, 7. Social Cognitive Theory, and 8. Motivational Model. This is a comprehensive, integrated, and well-grounded theory that combines ideas from previous technology acceptance models such as the Technology Acceptance Model (TAM), Theory of Reasoned Action (TRA), and Theory of Planned Behaviour (TPB). UTAUT seeks to explain why users accept or reject technology by considering four main factors: performance expectancy, effort expectancy, social influence, and facilitating conditions. By focusing on these four factors, UTAUT provides a more comprehensive understanding of user acceptance and use of technology than existing models Venkatesh et al. (2003).
However, it has some limitations. First, UTAUT does not consider the external influences that may affect user acceptance of technology, such as organisational culture and market trends. Second, UTAUT assumes that all users will have the same motivation and satisfaction levels, which is not always the case. Alshammari and Rosli (2020) reviewed that UTAUT is not perfect for some applications, such as e-commerce, as it needs modification. It leads to low stinginess because of the complex relationships among constructs implied by different moderation effects. Another limitation of the model is that the relationships outlined in UTAUT may not always hold true when the model is applied in different settings. Thomas et al. (2013) found that there is not always a consensus or agreement on the nature of these relationships when UTAUT is employed in alternative contexts. Besides, the model does not consider the temporal dynamics of user acceptance and behaviour and does not consider the different stages of technology adoption.
Moreover, UTAUT is criticised for its low parsimony, primarily because of its intricate relationships among its constructs and various effects and moderations, as Venkatesh et al. (2013) suggested in their study. UTAUT also does not adequately address technology acceptance and the psychological and social aspects of behaviour. As a result, UTAUT is unable to address the impact of individual habit, which can significantly influence user acceptance of technology. While UTAUT successfully integrates eight prominent theories, it is not exempt from limitations and cannot fully address previous theories’ shortcomings. This indicates that despite its comprehensive nature, UTAUT still has certain limitations and may not provide a complete solution to understanding technology acceptance and usage.
An Extension Unified Theory of Acceptance and Use of Technology (UTAUT2)
Extension of Unified Theory of Acceptance and Use of Technology UTAUT2 is a theoretical framework for understanding and predicting users’ intentions and decisions to accept and use technology. It is an extension of the original UTAUT (Unified Theory of Acceptance and Use of Technology) model, which was proposed in 2003 by Venkatesh et al. (2003). UTAUT2 was created by Venkatesh et al. (2012) and is based on the original UTAUT model but with additional constructs and moderating variables. UTAUT2 comprises seven core factors (Performance expectancy, Effort expectancy, Social Influence, Facilitating conditions, Hedonic motivation, Price value, and Habit with a few moderating variables (Age, Gender, and Experience). These factors and variables are used to predict user acceptance and usage of a given technology and can be used to guide user experience design.
The initial UTAUT contains four main factors: performance expectancy, social influence, effort expectancy and facilitating conditions (Ayaz & Yanartaş, 2020; Kabanda & Brown, 2017; Sezer & Yilmaz, 2019; Venkatesh et al., 2003). Later, Venkatesh et al. (2012) integrated the baseline framework with three new constructs: hedonic motivation, price value and habit, which is the second generation of (UTAUT2), are antecedents of behavioural intention and use behaviour (Ain et al., 2016).
The UTAUT2 contains seven key elements of intention and use of technology (Vonjaturapat & Chaveesuk, 2013). These are (1) performance expectancy (PE), effort expectancy (EE), (3) social influence (SI), (4) facilitating conditions (FC), (5) hedonic motivation (HM), (6) price value (PV) and (7) and habit (HA). The model includes three intermediary determinants, gender, age, and experience, that indirectly affect intention or use, in addition to determining factors with direct effects to adopt technologies (Davis et al., 1989; Kabanda & Brown, 2017; Sezer & Yilmaz, 2019; Venkatesh et al., 2003).
Despite its widespread use, several researchers have identified some limitations to the model. UTAUT2 heavily relies on behavioural intention as the main predictor of technology adoption. Research such as Chuttur (2009) suggests that the relationship between intention and actual behaviour is not always strong, as individuals may have intentions that do not translate into actual usage. This overemphasis on intention may limit the model’s ability to predict and explain technology adoption behaviour accurately. Similarly, Venkatesh et al. (2012) stated that UTAUT2 does not include a comprehensive set of external variables that may influence technology acceptance. The model focuses on individual-level factors and fails to consider broader environmental factors, such as economic conditions, regulatory policies, and market competition. Neglecting these external variables may limit the model’s ability to provide a holistic understanding of technology adoption. Furthermore, UTAUT2 was developed based on studies conducted primarily in Western cultures, which may limit its generalisability to other cultural contexts. Venkatesh et al. (2012) mentioned that cultural and contextual differences can significantly influence technology acceptance and usage behaviours.
Table 1 summarises several technology adoption theories and models discussed in contexts like this study. For example, the Technology Adoption Model (TAM) (Davis, 1989), the Theory of Reasoned Action (TRA) (Montano et al., 2015), the Theory of Planned Behaviour (TPB) (Ajzen, 1991), and the Unified Theory of Acceptance and Use of Technology (UTAUT) (Venkatesh et al., 2003) have all been applied in technology adoption research. No new high-level unifying theory, such as string theory, is linked to adoption in analytics (Rose, 2016).
The question of which theories should be applied in technology adoption research is crucial, and the answer depends on the study’s scope and research questions. However, after thoroughly examining various technology acceptance theories, UTAUT2 emerges as a particularly suitable framework for investigating technology adoption and user behavioural studies.
UTAUT2’s comprehensive nature, incorporating constructs such as performance expectancy, effort expectancy, social influence, and facilitating conditions, makes it an ideal choice for understanding the complex factors influencing technology adoption. Additionally, its ability to explain user behavioural intentions and actual usage behaviour makes it a robust framework for technology adoption research.
While other theories, such as TAM, TPB, and TRA, may also be applicable in certain contexts, UTAUT2’s flexibility and adaptability make it a preferred choice for researchers seeking to explore the intricacies of technology adoption and user behaviour. Ultimately, selecting a theoretical framework should be guided by the research questions and objectives, and UTAUT2’s versatility makes it a valuable tool in the realm of technology adoption research.
Key Theory Evaluation Frameworks
A rigorous evaluation of theories is essential to ensure that the conceptual foundations of a study are both academically robust and practically relevant. In information systems (IS) research, several frameworks have been developed to guide scholars in selecting, refining, and justifying theoretical models. Among these, Weber’s (2012) and Wacker’s (1998) contributions offer structured approaches to theory evaluation that are widely cited across disciplines, including library and information science (LIS).
Weber (2012) emphasises the importance of assessing both the explanatory power and the relevance of IS theories. His framework proposes that a strong theory should account for a substantial proportion of the variance in the phenomena of interest, clearly articulate the relationships among constructs, and demonstrate relevance to practitioners and scholars alike. This structured approach underscores the need to evaluate not only how well a theory describes or predicts behaviour but also how effectively it informs action in complex organisational contexts such as LIS.
Similarly, Wacker (1998) provides research guidelines that delineate essential criteria for theory selection and development. He highlights four core attributes: internal consistency (the logical coherence among constructs and propositions), empirical testability (the ability to design studies that can falsify the theory), generalisability (applicability across settings), and parsimony (simplicity without sacrificing explanatory breadth). Together, these criteria help researchers judge whether a theory meets the threshold for rigorous academic inquiry and practical relevance.
Building on these seminal contributions, this study applies a multi-criteria approach to evaluating candidate theories of technology adoption. The frameworks provided by Weber (2012) and Wacker (1998) help ensure that the theories selected for analysis are not only methodologically sound but also aligned with the distinctive characteristics of LIS environments.
To determine which theory is most suitable, each candidate theory such as the Technology Acceptance Model (TAM), TAM2, the Unified Theory of Acceptance and Use of Technology (UTAUT), UTAUT2, and the Diffusion of Innovation (DOI) theory can be assessed against the following criteria: 1. Theoretical Fit o Relevance to LIS Context: Does the theory address the unique characteristics of LIS environments, including user diversity, institutional settings, and service orientation? o Conceptual Coverage: Does it include constructs meaningful for LIS, such as information literacy, system usability, trust, and collaboration? 2. Empirical Support o Evidence from LIS Studies: Has the theory been successfully applied in LIS research? What were the outcomes of these studies? o Predictive Power: How well does the theory explain or predict user behaviour in LIS settings? 3. Methodological Flexibility o Quantitative vs. Qualitative Use: Can the theory be adapted for qualitative research, especially in exploratory or interpretive LIS studies? o Operationalisability: Are the constructs and relationships clearly defined and measurable? 4. Practical Utility o Actionability: Does the theory generate insights that inform LIS practice, system design, or policy development? o Stakeholder Relevance: Is it useful for librarians, system developers, educators, and policymakers? 5. Theoretical Robustness o Generalisability: Can the theory be applied across different LIS contexts (e.g., academic libraries, public libraries, archives)? o Integration Potential: Can it be combined with other theories or frameworks (e.g., critical theory, participatory inquiry)?
In this study’s context, UTAUT2 is highly relevant, as its extended constructs hedonic motivation, price value, and habit offer deeper insights into user acceptance. This enriched perspective is particularly significant in modern library and information science settings, where varied user motivations and the ubiquity of digital services shape technology adoption. Furthermore, UTAUT2 has demonstrated adaptability to qualitative methods, such as thematic analysis and grounded theory, making it suitable for exploratory investigations. Evidence from prior LIS studies indicates that UTAUT2 has strong predictive performance in explaining technology adoption behaviours, especially in studies using interviews, focus groups, or case studies (Venkatesh et al., 2012).
By applying the criteria derived from Weber’s and Wacker’s frameworks, this research ensures that theory selection is both transparent and defensible. Such a systematic approach helps establish the explanatory adequacy and relevance of the chosen theoretical lens, strengthening the contribution of this study to both LIS scholarship and practice.
Research Methodology
The methodology employed in this study centred on a systematic literature review to explore the application of technology acceptance theoretical frameworks within the Library and Information Science (LIS) field. By combining a structured search strategy with rigorous filtering criteria, the study ensured the inclusion of high-quality, relevant studies.
Database Selection and Search Strategy
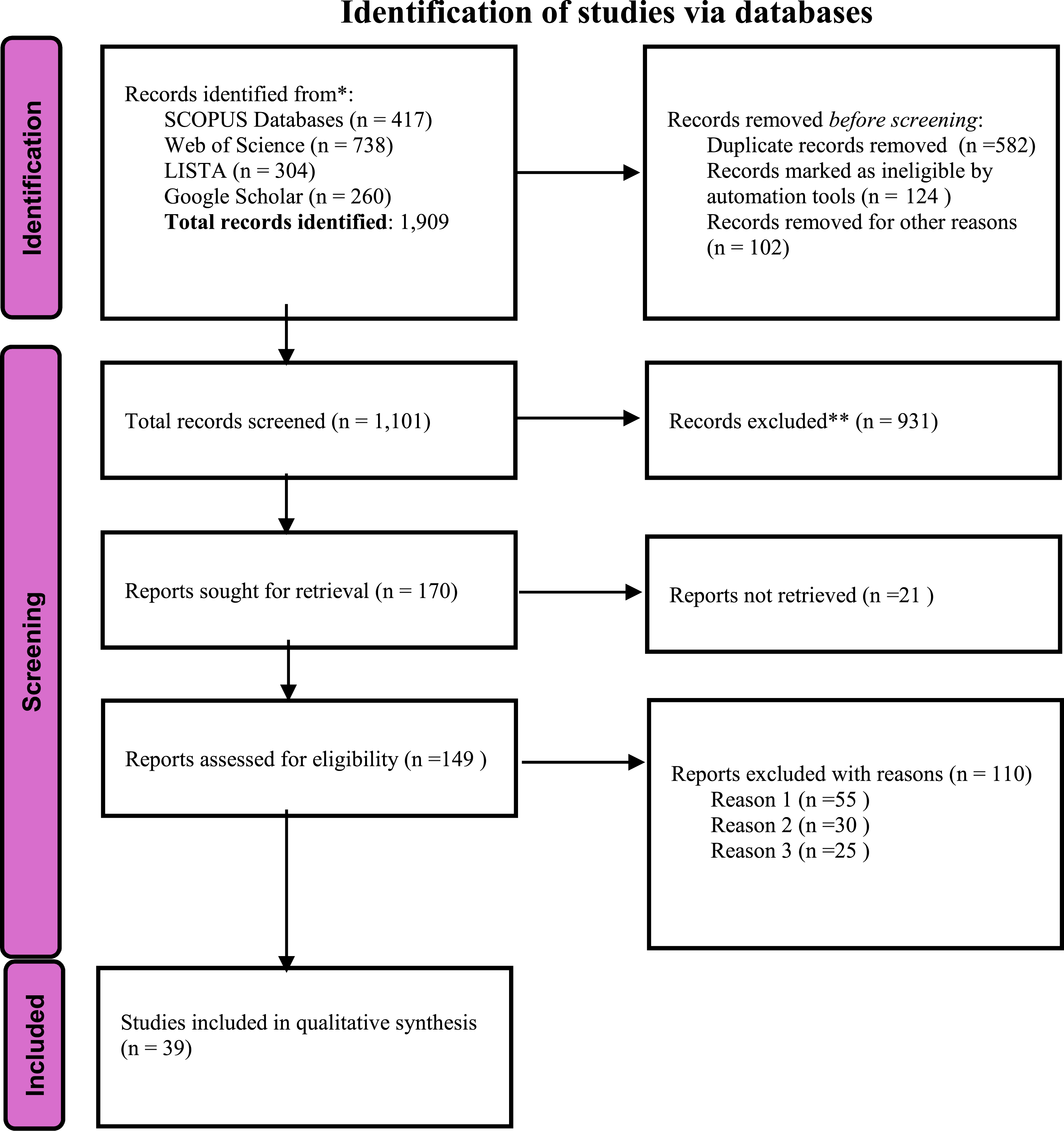
This study employed a systematic review methodology to explore the application of UTAUT and UTAUT2 models in qualitative research. The review followed the Preferred Reporting Items for Systematic Reviews and Meta-Analyses Protocol (PRISMA-P) guidelines to ensure transparency, replicability, and methodological rigour in identifying, screening, and selecting relevant literature.
The systematic literature review used four primary databases: SCOPUS, Web of Science, LISTA and Google Scholar. These databases were chosen due to their comprehensive indexing and prominence in facilitating access to scholarly research within LIS and related fields. The search strategy was adapted to align with each database’s unique features and functionalities, maximising the retrieval of pertinent studies.
SCOPUS, Web of Science, LISTA and Google Scholar
The same set of search keywords was applied across all four databases Scopus, Web of Science, LISTA, and Google Scholar to ensure consistency and comprehensive coverage. The common keywords used were “UTAUT”, “UTAUT2”, “Qualitative”, “Theory” and “Library and Information Science”. These terms were selected to focus the search on qualitative studies investigating technology acceptance within the Library and Information Science (LIS) domain. Logical operators (AND/OR) were used to connect and refine the search terms, with the following example representing the typical search string applied across all databases:
Database Searches: Dates, Coverage, and Keyword Strings
Database Searches: Dates, Coverage, and Keyword Strings

The following sections provide a detailed explanation of the search outcomes and screening process, outlining how the retrieved studies were evaluated, filtered, and selected for inclusion in the final analysis.
SCOPUS
The literature search was conducted on 24 October 2024 using the Scopus database, accessed through the university’s subscription platform, and covered publications from the past ten years (2015–2025). The targeted search generated 417 documents, which were exported to a CSV file for detailed analysis. A comprehensive review of abstracts and methodologies was then undertaken to exclude studies employing quantitative approaches, retaining only those that utilised qualitative research methods for inclusion in the study.
A comprehensive review of abstracts and methodologies was undertaken to apply detailed exclusion criteria. Studies were excluded if they: (a) employed purely quantitative research methods, (b) lacked a clear methodological description, (c) were not published in peer-reviewed journals, (d) were not written in English, (e) did not examine technology acceptance or adoption frameworks. Only studies meeting these criteria and employing qualitative research approaches were retained for inclusion in the review (Figures 1–3). Scopus Search and Refined Results Found 417 Documents by Subject Area 738 Publications Selected From the Web of Science Core Collection PRISMA-P Flow Diagram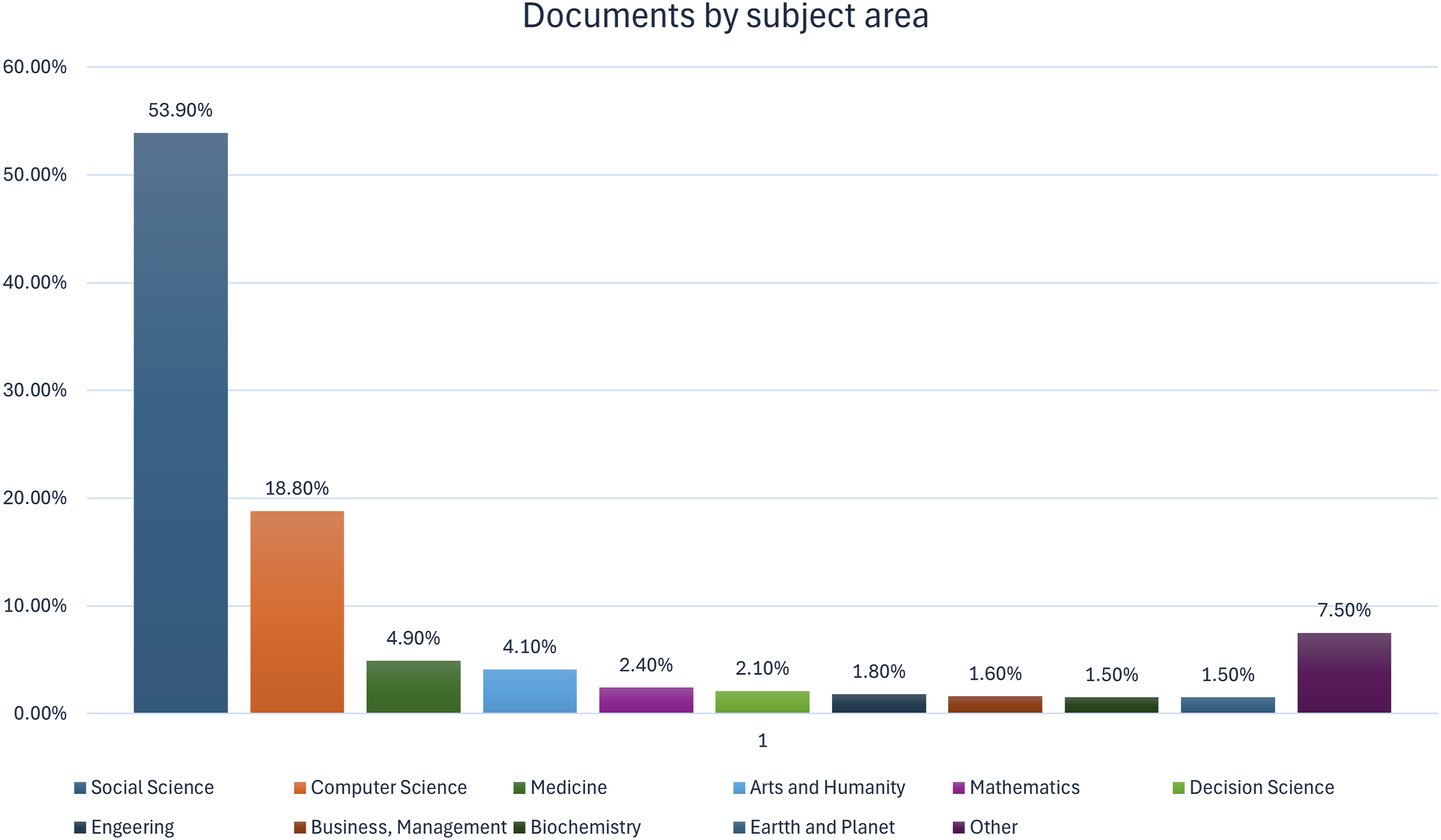

Web of Science
The literature search was conducted on 24 October 2024 using the Web of Science database, accessed through the university’s subscription platform. The search covered publications from the past ten years (2015–2025) and followed the same keyword strategy applied across all databases to ensure methodological consistency. The initial search in Web of Science identified 3,578 documents. Filters were applied to narrow the results to relevant subject areas, and specific exclusion criteria were implemented to remove studies that: (a) used quantitative methods only, (b) were not published in peer-reviewed journals, (c) were not written in English, or (d) did not focus on technology acceptance within the Library and Information Science (LIS) domain. After applying these criteria, 738 records were retained and exported into a CSV file for detailed review.
Library, Information Science & Technology Abstracts (LISTA)
The literature search was conducted on 15 July 2025 using the Library, Information Science & Technology Abstracts (LISTA) database, accessed through the university’s subscription platform. The search strategy was designed to capture peer-reviewed, academic journal articles published in the last ten years that focus on UTAUT or UTAUT2 models within qualitative research contexts.
The following Boolean search string was used within the title field (TI):
The search results were filtered using the following criteria: publications from the past ten years (2015–2025), limited to peer-reviewed academic journal articles. The linked full-text option was enabled to ensure accessibility, and the language filter was set to English.
Subject filters applied included topics such as data analysis software, social media, descriptive statistics, business communication, bibliometrics, bibliographic databases, behavioural research, academic libraries, technology, technological innovations, systematic reviews, social skill–context–anxiety, metadata, management information systems, information technology, information-seeking behaviour, data analytics, smartphones, data privacy, data analysis, libraries, empirical research, diffusion of innovations, qualitative research, factor analysis, information science, artificial intelligence, digital technology, decision-making, access to information, theory, and research methodology.
The search initially returned 304 articles, which were exported as a CSV file for further screening.
Google Scholar
The literature search was conducted on 7 October 2025 in the Google Scholar database, covering publications from the past ten years (2015–2025). An initial search retrieved 450 documents using the keywords “Technology Acceptance” AND (“UTAUT” OR “UTAUT2”) AND “Qualitative Research” AND (“Library and Information Science” OR “LIS”).
This revised search strategy ensured alignment with the other databases (Scopus, Web of Science, and LISTA) and clarified the study’s focus on the Library and Information Science (LIS) domain. This approach was harmonised across databases to maintain methodological consistency.
References retrieved from Google Scholar were exported as BibTeX files and integrated into Overleaf for reference management, writing, and organisation. Subsequently, the abstracts were thoroughly analysed, and specific inclusion and exclusion criteria were applied. Studies were excluded if they: (a) employed quantitative methods only, (b) were not peer-reviewed journal articles, (c) were not written in English, (d) did not address technology acceptance or adoption frameworks. Only studies that met these criteria and utilised qualitative research methods were retained for the final synthesis.
The following section provides a detailed explanation of the inclusion and exclusion criteria applied across all databases to ensure consistency and transparency in the study selection process.
Inclusion and Exclusion Criteria
To ensure a systematic and transparent selection process, this review considered studies published between 2015 and 2025, written in English, that investigated technology acceptance within a theoretical framework. Priority was given to research employing the Unified Theory of Acceptance and Use of Technology (UTAUT) or its extended version, UTAUT2, as the primary conceptual framework. Studies were also considered if they discussed theory development, theoretical application, or conceptual refinement relevant to technology adoption in library and information science contexts. Both qualitative studies and mixed methods works with substantial qualitative components were eligible, provided they offered meaningful theoretical insights. Accepted sources included peer-reviewed journal articles and all required full-text availability for analysis.
Studies were excluded if they fell outside the specified date range, were unrelated to technology acceptance or theory in the library and information science domain, or did not engage with UTAUT, UTAUT2, or comparable theoretical models. Opinion pieces, editorials, and non-scholarly works without empirical or theoretical contributions were excluded, as were duplicates, secondary citations of the same work, and publications not in English. Screening was conducted in two stages: initial title and abstract review to remove clearly irrelevant studies, followed by full-text screening to confirm alignment with the inclusion criteria. Any uncertainties during the screening process were resolved through careful review and reflection to maintain methodological consistency.
Inclusion and Exclusion Criteria
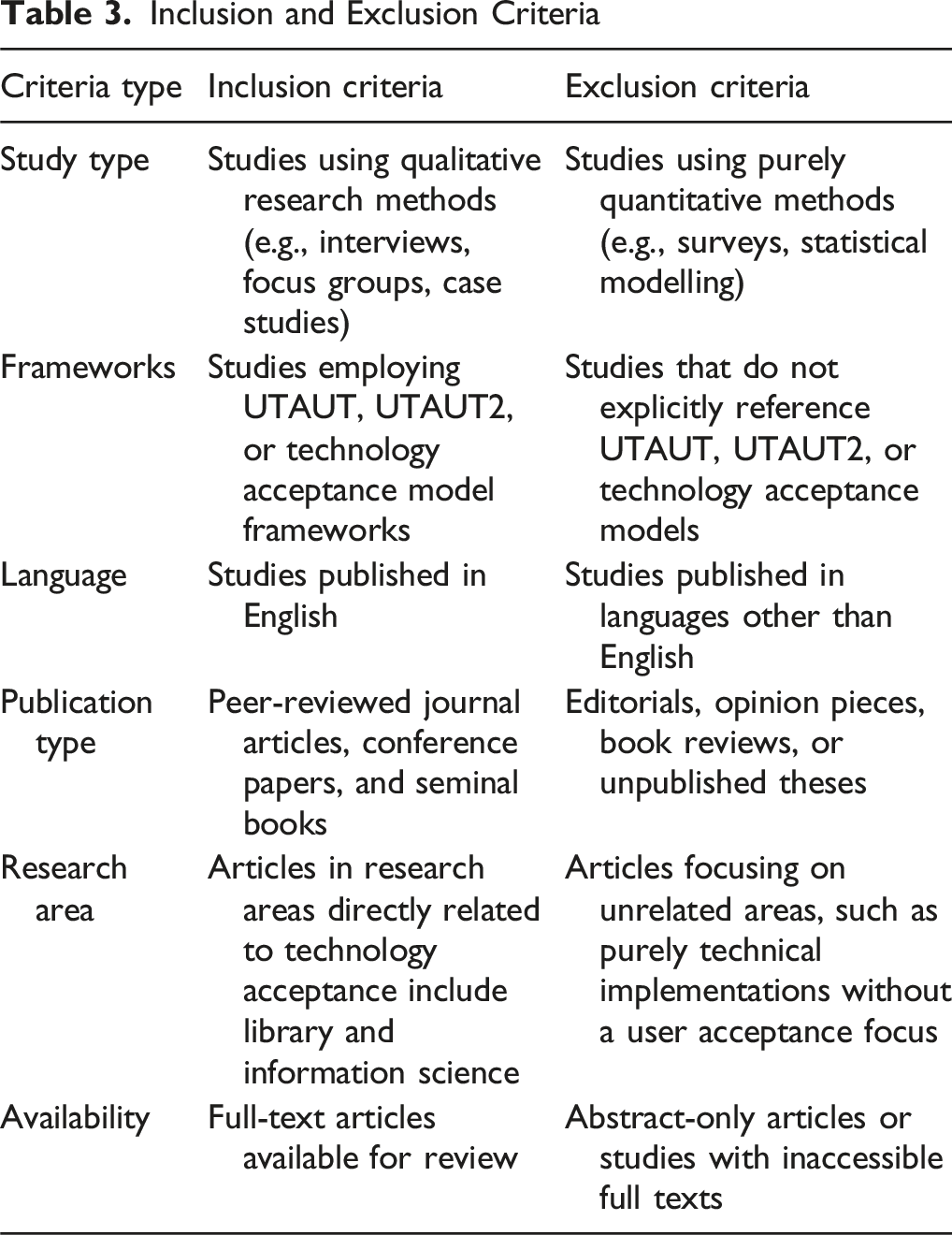
The screening process was conducted manually. Articles were first reviewed at the title and abstract level, followed by a full-text review when necessary. The inclusion criteria required that: • The study explicitly used UTAUT or UTAUT2 as a theoretical framework • The study employed a qualitative research design (e.g., interviews, case studies, focus groups)
Articles were excluded if they: (a) were based on quantitative research designs, (b) did not explicitly refer to the UTAUT or UTAUT2 frameworks, or (c) did not address aspects of technology behaviour, acceptance, or adoption.
Data Analysis
The PRISMA-P flow summary indicates that a total of 1,719 records were identified across four databases: Scopus (n = 417), Web of Science (n = 738), LISTA (n = 304), and Google Scholar (n = 450). After removing duplicate records (n = 582), records marked as ineligible by automation tools (n = 124), and records removed for other reasons (n = 102), a total of 1,101 records were screened. Of these, 931 records were excluded, and 170 reports were sought for retrieval. Twenty-one reports could not be retrieved, leaving 149 reports assessed for eligibility. Following assessment, 110 reports were excluded for the following reasons: Reason 1 (n = 55), Reason 2 (n = 30), and Reason 3 (n = 25). Finally, 39 studies were included in the qualitative synthesis.
A thematic synthesis approach was employed to analyse and integrate findings across the included studies, allowing for the identification of recurring patterns, themes, and theoretical insights. As the review focused on qualitative research, no statistical aggregation was conducted. The PRISMA-P (Preferred Reporting Items for Systematic Review and Meta-Analysis Protocols) framework guided the process of data extraction, organisation, and reporting.
This included documenting article metadata, theoretical constructs applied, research settings, methodological approaches, and key findings related to the application of UTAUT and UTAUT2 in Library and Information Science (LIS) research. The final dataset thus represents a focused body of literature offering thematic insights into how these frameworks have been applied within qualitative LIS studies.
Results
A substantial body of research has applied the Unified Theory of Acceptance and Use of Technology (UTAUT) and its extended version, UTAUT2, in qualitative contexts within the broader field of technology acceptance. Thematic analysis of the selected studies revealed three main groupings: (1) applications in health and well-being technologies, (2) applications in education and learning technologies, and (3) applications in other domains, including commerce, governance, and library services. Within these themes, the constructs of UTAUT2 performance expectancy, effort expectancy, social influence, facilitating conditions, hedonic motivation, price value, and habit were explored to varying degrees, often revealing context-specific influences on technology adoption.
Health and Well-Being Technologies
Several qualitative studies applied UTAUT2 to investigate technology adoption in health-related contexts. Thérouanne et al. (2023) examined the acceptability of telehealth, active video games, and mobile apps for bariatric surgery patients, identifying patient preference motives through the UTAUT2 lens. Schretzlmaier et al. (2022) explored mHealth adoption, finding that all exogenous UTAUT2 constructs were relevant predictors of acceptance in the health sector. Similarly, Woldeyohannes and Ngwenyama (2017) found that performance expectancy, effort expectancy, and habit were most influential in mHealth app adoption decisions. Dehghani (2016) focused on smartwatches and fitness wristbands, showing how human expectation and behaviour mediated technology adoption.
Education and Learning Technologies
A significant cluster of studies applied UTAUT/UTAUT2 to educational settings. Peng and Yang (2022) examined open educational resources (OER) adoption among Chinese college students, identifying perceived value, perceived risk, facilitating conditions, social influence, habit, and hedonic motivation as key influences. Kari et al. (2016) investigated the decision-making process for embedding self-tracking technologies, while Mokhtari (2019) examined Iranian learners’ use of mobile devices for assessment, linking adoption to motivation, self-efficacy, and academic performance. Tiba and Condy (2021) studied pre-service teachers’ readiness to integrate technology, highlighting factors that encouraged or inhibited adoption.
Commerce, Governance, and Library Services
In commercial contexts, Axcell and Ellis (2023) explored Gen Z attitudes towards branded mobile apps, revealing that privacy concerns significantly shaped adoption behaviour. Kazancoglu and Aydin (2018) applied UTAUT2 to omnichannel shopping, focusing on behavioural intentions and purchasing patterns. Maune (2021) investigated mobile applications for competitive intelligence, finding all UTAUT2 constructs significant, particularly ease of use, usefulness, enjoyment, and trust. Apfel and Herbes (2021) studied SMEs’ adoption of resource-efficient technologies, noting that high performance expectancy could diminish the importance of effort expectancy, while social influence had little impact. In governance, Alharbi et al. (2017) combined qualitative and quantitative approaches to examine e-government service adoption in Saudi Arabia, identifying interface quality, security, and legislation as major factors.
Within the library and information science domain, Roy (2024) applied UTAUT2 to understand factors influencing analytics adoption in Australian university libraries. All seven UTAUT2 constructs were found to be significant, alongside additional domain-specific factors such as the absence of analytics training in LIS curricula, algorithm literacy needs, and privacy concerns.
Cross-Cutting Insights
Across the thematic clusters, performance expectancy and facilitating conditions consistently emerged as strong drivers of technology adoption, while hedonic motivation and habit showed greater influence in personal and consumer-oriented technologies. Social influence appeared context-dependent, being prominent in education but less so in SME technology adoption. These findings demonstrate the adaptability of UTAUT2 in qualitative research and its capacity to reveal nuanced, context-specific determinants of technology acceptance.
Summary Results of UTAUT2 with Qualitative Studies
Summary of Studies That Used the UTAUT2 Model in Qualitative Studies

Many researchers, including Etemadi et al. (2020), Gupta et al. (2018), and Khechine and Augier (2019), suggest that extending pre-established technology adoption models is one of the leading solutions for researchers who aim to address various aspects of technology adoption that are complex. Thus, the researcher suggested an extension of UTAUT2, which was validated as an appropriate qualitative framework for examining the complex and diverse facets of technology adoption, allowing researchers to gain a more comprehensive understanding of this phenomenon.
Discussion
This discussion addresses the two primary objectives of the study: (1) To critically analyse relevant technology acceptance theories and identify the most suitable frameworks for understanding user behaviour and technology adoption, and (2) To explore the potential of UTAUT2 in qualitative research within the Library and Information Science (LIS) context.
Interpreting the Broader Application of Technology Acceptance Frameworks
The findings demonstrate that the Unified Theory of Acceptance and Use of Technology (UTAUT) and its extended version, UTAUT2, have been extensively applied across a range of qualitative research contexts, including health and well-being, education and learning, commerce, governance, and library services. The widespread application of these frameworks confirms their theoretical robustness and adaptability in understanding technology acceptance behaviour across different settings.
While the framework’s application varies across domains, the results show that performance expectancy and facilitating conditions consistently emerge as the strongest predictors of adoption in both professional and personal contexts. This reinforces the importance of users’ perceived usefulness of technology and the presence of supportive infrastructure in shaping behavioural intention.
Relevance and Transferability to the LIS Context
Although most studies identified were from outside LIS, particularly in health and education, their methodological approaches and thematic insights offer valuable parallels for library research. For instance, in health and well-being technologies, UTAUT2 was employed to examine user motivation, trust, and behavioural intention factors that can directly inform LIS studies investigating technology adoption by library professionals and users. Similarly, findings from educational technology studies such as the roles of self-efficacy, social influence, and hedonic motivation highlight transferable determinants relevant to understanding librarians’ and students’ engagement with digital tools, analytics platforms, and learning management systems.
The study by Roy (2024) specifically demonstrates how UTAUT2 can be successfully applied within university libraries to explore analytics adoption. It revealed that, alongside the seven core UTAUT2 constructs, contextual factors such as analytics training gaps, algorithmic literacy, and privacy concerns significantly influence technology acceptance. These findings confirm that the UTAUT2 framework not only fits the LIS context but can also be extended to capture emerging constructs unique to this domain.
Thematic Insights and Implications
The cross-cutting patterns across domains show that UTAUT2 effectively accommodates contextual nuances in qualitative research. The framework’s flexibility allows researchers to integrate new constructs such as trust, perceived risk, and ethical awareness without losing theoretical coherence. In the LIS context, this flexibility is particularly valuable, as library technologies increasingly intersect with data analytics, artificial intelligence, and digital privacy (Roy, 2025).
The discussion thus establishes that while UTAUT2 has proven explanatory power across various domains, its application in LIS provides additional insights into user perceptions of technological change, organisational readiness, and data-driven decision-making. The model’s holistic nature supports a deeper qualitative understanding of behavioural drivers among LIS professionals, enabling future research to develop tailored interventions for promoting innovation adoption in libraries.
Overall, the findings fulfil the study’s objectives by demonstrating that UTAUT2 is a theoretically sound and contextually adaptable framework for examining technology acceptance within the LIS field. While evidence from other domains reinforces its robustness, its emerging use in LIS research highlights its relevance for exploring evolving digital practices in libraries. Future research should continue applying and refining UTAUT2 in LIS to capture the interplay between human, technological, and organisational factors shaping technology adoption.
Conclusion
This review set out to critically analyse major technology acceptance theories and identify the most suitable framework for understanding user behaviour and technology adoption, with particular attention to the Library and Information Science (LIS) domain. Through a thematic synthesis of qualitative studies, the Unified Theory of Acceptance and Use of Technology (UTAUT) and its extended version, UTAUT2, emerged as the most comprehensive and adaptable frameworks for examining technology acceptance across diverse contexts. The findings confirm that UTAUT2 offers strong explanatory power in capturing the complex, multifaceted nature of technology adoption. Across health, education, and governance domains, the model’s constructs performance expectancy, effort expectancy, facilitating conditions, social influence, hedonic motivation, price value, and habit consistently explained variations in technology adoption behaviour. More importantly, these constructs also proved relevant within the LIS context, where evolving technologies such as analytics, artificial intelligence, and digital repositories demand deeper behavioural understanding.
The review demonstrates that the UTAUT2 framework can be effectively applied to qualitative LIS research, providing nuanced insights into how professionals and users engage with new technologies. This study contributes to both theory and practice by establishing UTAUT2 as a robust conceptual lens for exploring technology acceptance in libraries and related information environments. Future research should build upon these findings by conducting empirical LIS studies that adapt UTAUT2’s constructs to contemporary technological innovations, thereby strengthening theoretical understanding and supporting informed decision-making in library technology adoption and management.
Supplemental Material
Supplemental Material - Applying UTAUT2 in Qualitative Research: A Systematic Review
Supplemental Material for Applying UTAUT2 in Qualitative Research: A Systematic Review by Prodip Roy in International Journal of Qualitative Methods.
Footnotes
Funding
The author received no financial support for the research, authorship, and/or publication of this article.
Declaration of Conflicting Interests
The author declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Supplemental Material
Supplemental material for this article is available online.
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
