Abstract
Links between IPF and homicide concealment have been observed but not explained. We theorize IPF perpetrators use concealment to continue coercively controlling investigators, children, courts and finances post-IPF. We compare abuse in the relationship and surrounding IPF in five diverse cases. Facilitated by concealment, offenders use versatile, subtle and overt tactics to extend control post-IPF. They capitalize on opportunities for concealment and regaining control, sometimes without other benefits. Tactics are akin to those employed previously, aligning with the power and control wheel. Concealment allows offenders to dominate the death narrative and assists with remaining unaccountable.
Keywords
Introduction
Feminist research has consistently demonstrated a strong association between intimate partner femicide (IPF) and coercive and controlling behaviors by perpetrators (Johnson et al., 2019; Monckton Smith et al., 2017; Stark, 2009). Recently, links between IPF and offender attempts to conceal the homicide have emerged, indicating IPFs are not uncommonly masked as non-suspicious deaths such as suicides or accidents (Bitton & Dayan, 2019; Eke, 2007; Ferguson, 2021; Ferguson & Sutherland, 2018; McLachlan, 2023; Monckton Smith, 2019). Explanations for IPF offenders concealing homicides are limited and unspoken, seemingly based on assumptions of perpetrators avoiding accountability (Eke, 2007; Ferguson, 2021; Monckton Smith, 2019). Such explanations have a major limitation: most homicide offenders likely wish to avoid prosecution. The question remains then, why so many offenders perpetrating IPF attempt to conceal the femicide.
We draw on links between IPF and feminist theories of coercive control (CC) to fill this gap. Using collective case studies (Stake, 1995), we argue that within an IPF, concealment helps offenders maintain control over the victim, her proxies, the story of their relationship, their children, and his reputation and finances. CC in the relationship extends to the planning, perpetration, and post-IPF behavior of the offender, allowing them to punish the victim, regain control, and remain unaccountable. This makes concealed IPF an attractive alternative to separation for some abusers.
Intimate partner violence (IPV) and IPF scholars may view this theory as self-evident. Despite strong support in the IPF and detection avoidance (DA) literature, though, explanation for how CC is used during and after an IPF has been absent. To address this, we use the feminist scholarship on CC to argue that it continues after a female partner is murdered. Then, profiles of controlling IPV offenders as chronically manipulative and instrumental are compared to those of offenders who use DA, showing marked similarities. Next, control tactics used by offenders during their relationships are compared to those used surrounding a concealed IPF, with the power and control wheel as a framework; highlighting significant overlap in the behaviors observed. Finally, illustrative case studies drawn from the concealed IPF research are described, demonstrating the versatile ways that concealment allows CC to continue after a woman is murdered by her intimate partner.
A Continuing Need for Control
In 2007, feminist scholar Evan Stark conceptualized IPV as resulting from and reinforcing CC, where a person is entrapped by a pattern of abuse that establishes and maintains the dominance of one partner over another. Stark defined CC as “a strategic course of self-interested behavior designed to secure and expand gender-based privilege by establishing a regime of domination in personal life” (Stark, 2012, p. 21). As Stark’s framework gained momentum, other researchers advocated for individual-level factors as contributors. For example, Day and Bowen (2015) examined cognitive and developmental correlates of CC arguing expert IPV offenders have long histories of violence, entrenched attitudes, and deliberately use abuse tactics to control and avoid accountability. They argued these behaviors are grounded in core beliefs about abusive behavior, including justifications that it’s part of their personality, they are neither violent nor abusive, and abuse is their partner’s fault (Day & Bowen, 2015; see also Walker et al., 2014). This frames IPV as occurring “within a context of a far broader pattern of maladaptive controlling behavior” (Buzawa & Buzawa, 2013, p. 129), based on factors including attitudes towards women and violence, genetic loading for impulsivity, family of origin violence, peer delinquency, attachment style, impulsivity, and social skills (Day & Bowen, 2015; Holtzworth-Munroe & Stuart, 1994). Day and Bowen (2015, p. 67) explain: Exposure to IPV and coercion in childhood can lead to the development of beliefs about gender and patriarchy which translates into the desire for relationships involving power and control in adolescence. CC behaviors then become established (and elaborated), as the perpetrator learns how to most effectively use threats and intimidation to gain compliance. This is then reinforced and rationalized and provides the motivation to develop knowledge about how best to avoid detection.
In this model, the origins behind power and control are clear, as is the addition of consideration being made to DA. We argue that since the antecedents behind power and control are brought with the perpetrator and fixed (Day & Bowen, 2015), this desire is unlikely to end at the termination of the relationship, especially with expert perpetrators. Indeed, evidence suggests CC commonly continues for months or years post-separation (Anderson, 2005; Ornstein & Rickne, 2013).
The femicide literature adds IPF it is not an extension of IPV, but an extreme form of violence perpetrated by expert, CC abusers. Dobash and Dobash (2015) argue that IPF may itself be a tactic for offenders to regain a perceived loss of control over the victim. If expert IPV offenders continue CC after separation, and possibly use IPF to do so, it follows that controlling behavior may also continue post-IPF. Continued control would have to shift from dominating a living person to controlling their children and property, her memory, or possibly, perceptions surrounding her death.
Coercive Controlling Offenders vs. DA Offenders
Research on CC suggests offenders are chronically cold, calculating, and goal-directed in their abuse. For example, Spidel et al. (2007) note that some expert IPV perpetrators only engage in relationships so they have a person to control, and resources and power to use for their own benefit. Day and Bowen (2015) observe that CC abusers create and exploit opportunities to exert power using a combination of tactics. They use violence in a hostile manner that is manipulative, callous, and instrumental (Day & Bowen, 2015; Ross & Babcock, 2009). Use of the word “tactics” emphasizes these behaviors are deliberate and goal-directed, capitalizing on the victim’s vulnerabilities and the situation (Mankowski et al., 2002). Willis (1997) portrays expert IPV offenders as master manipulators, observing such skills are also used to avoid prosecution. Day and Bowen (2015) discuss “conviction evasion skills” (p. 66), used to control the legal system and cover up abuse. Monckton Smith et al.’s (2017) work describes perpetrators’ chronic manipulation of police and the family court to portray victims as unstable and untrustworthy. Since manipulative tactics are used within the relationship, to avoid prosecution, and to malign the victim to authorities, these skills might also be used to avoid detection for an IPF.
Characterizations of offenders in the research on DA/concealment in homicide are remarkably similar to those of CC abusers. While approaching the research from different perspectives, the parallel in profile suggests both bodies of work may be describing the same cohort of perpetrators, perhaps at different points in time or levels of expertise. For example, Eke (2007) studied concealed intimate partner homicides (IPH; mostly femicides), finding that DA offenders were more instrumental and deliberate in their offending than other IPH offenders. Eke’s (2007) concealers lacked remorse, guilt, or empathy, and were characterized as callous, conning, and manipulative. Direct links between concealed IPH and CC were also shown, with DA offenders more controlling of their victim than other murderers (Eke, 2007).
Eke (2007) also explains that “the manipulative behavior of these offenders may not be exclusive to murder, rather the [concealed] case of homicide might be an extension of their generally manipulative behavior” (p. 87). Other studies of concealed homicides report similar results: Ferguson (2019) found long histories of fraud and deception in offenders with police training; Ferguson and Sutherland's (2018) study of murders concealed as accidental falls found several cases involving offenders who tried to kill their victim previously or were suspected of killing other spouses; and Ferguson (2021) attributed DA/concealment to psychopathic-like tendencies, noting the “profile of DA offenders [is] chronically and deliberately conning and manipulative for the sake of personal, financial or emotional gain” (p. 83). Indeed, Ferguson (2021) commented on the alarming rate at which expert offenders successfully use these tactics, finding 25% successfully evaded arrest for their IPH in one sample. The picture emerging casts IPF concealers as persistently calculating and domineering; expert CC offenders. This profile suggests behaviors surrounding an IPF are likely to be employed intentionally for a perceived gain - the maintenance of control and “conviction evasion” (Day & Bowen, 2015, p. 66).
Similarities between CC abusers and homicide concealers support the contention that offenders use DA/concealment to continue their control post-IPF. Parallels in the tactics used to enact this control, both before and after an IPF, offer further evidence.
Coercive Controlling Tactics in Life vs. Death
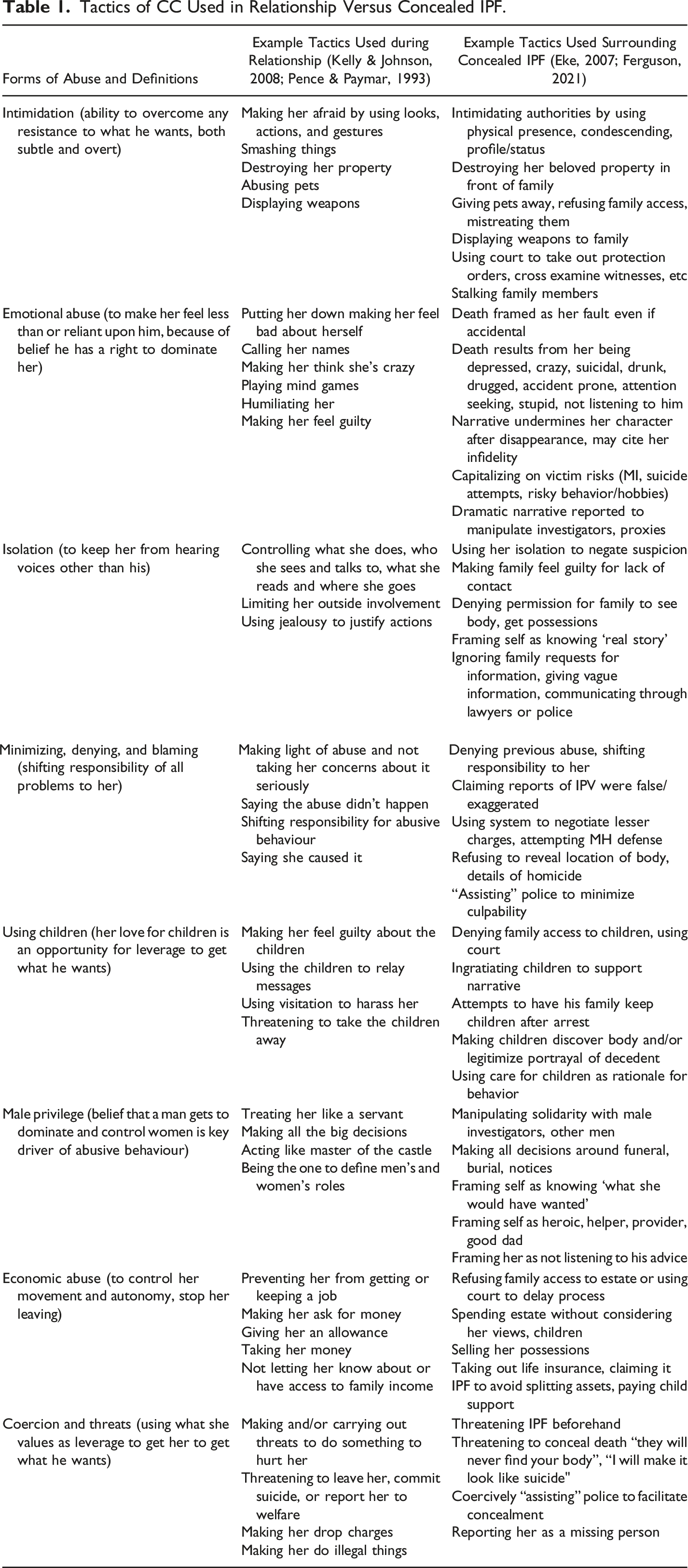
Tactics used to enact CC are individualized and variable. They may only appear abusive when viewed in context and can be difficult to define (Wangmann, 2021). The most universalist tactics have been framed against Pence and Paymar’s (1993) original feminist model of IPV, using the power and control wheel (Kelly & Johnson, 2008). The wheel depicts forms of power and control in each spoke, including intimidation; emotional abuse; isolation; minimizing, denying, and blaming; using children; using male privilege; economic abuse; and coercion and threats. The tactics under each form of abuse are used to achieve power and control, with sexual and physical violence (outside of the wheel) giving each behavior more influence (see Kelly & Johnson, 2008). Viewing IPV along a continuum and as intentional and goal-directed illustrates the system of abuse used in CC relationships, instilling fear to dominate and entrap a person.
Tactics of CC Used in Relationship Versus Concealed IPF.
To further unpack how concealment is used within IPFs to continue CC, a collective case study was used. With the power and control wheel as a framework, we: 1. Explored the subtle and overt forms of power and control used by IPF concealers 2. Compared tactics used during the relationship and surrounding a concealed IPF 3. Searched for themes across the cases
Method
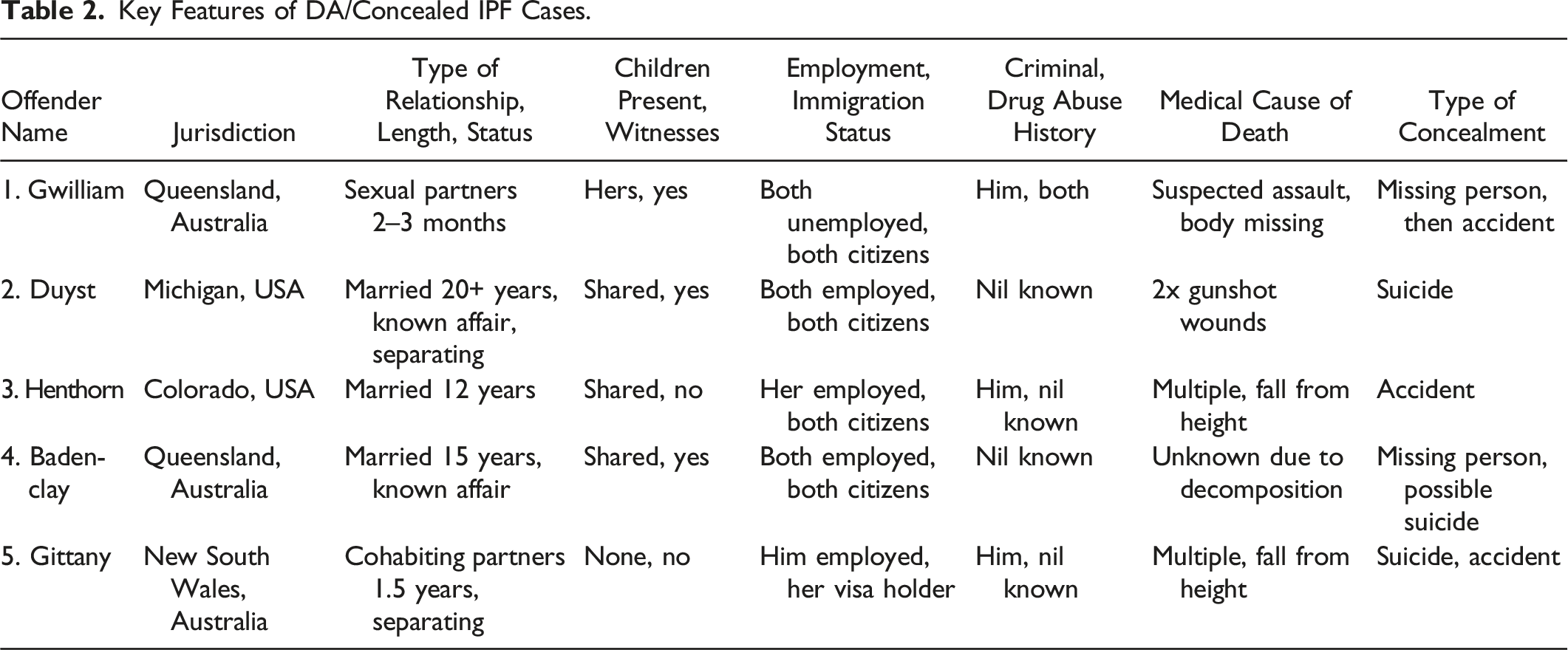
A collective case study of five solved concealed IPF cases was examined (Stake, 1995). Five cases have been used previously as an adequate sample for balancing the presentation of sufficient detail for a robust analysis with outlining the breadth of behaviors and contexts possible, within limited space (Orland-Barak & Hasin, 2010). Using five strategies we began purposive sampling of 74 possible cases from our previous research, aiming to represent multiple CC behaviors. The strategies involved first searching for cases where adequate information was available from a variety of sources (51 cases excluded). Second, for comparability in the sample we looked for cases with cisgender heterosexual couples. Because of an absence of detailed information, no cases were excluded based on this rule. Third, we selected cases to include a variety of demographic features of involved parties, including: jurisdiction, length, and type of intimate relationship (married, partnered, separating); presence of children; socioeconomic, employment and immigration status; criminal history and substance misuse (10 cases excluded). Fourth, we included cases with a variety of relationship dynamics, including: levels and types of previous abuse; reporting to authorities or others; and suspicions of abuse (3 cases excluded). Finally, we included cases with limited repetition in concealment tactics used, so that the widest range of potential behaviors could be presented. We included cases that differed from each other surrounding cause of death (falls, gunshots, unknown); concealment type (suicide, accidental death, missing person); presence of witnesses and other evidence; and tactics used (5 cases excluded). Though they do not show all possible variations, the resulting five cases present different types of relationships, multiple forms of abuse, and many different features of concealed-IPF.
We followed a case study approach to data collection, analysis, and interpretation. For each of the five cases, purposive searches for relevant documents were conducted between May and August 2022. Searches included examining legal databases for court records, sentencing remarks, and victim impact statements, coronial repositories and archives for reports and inquests, and media sources for emergency assistance recordings and triangulating information. Materials collected for each case differed but generally included multiple factual summaries from criminal trials, appeals, and civil or family court records. In one case a detailed a coronial inquest was available, and in three others entire books had been written. Media accounts were used sparingly to fill in gaps in official records (such as by indicating that there was an ongoing legal dispute) and to corroborate official data.
The cases were examined from multiple perspectives to identify abusive tactics in context. Using multiple data sources, we examined forms of power and control directed at different targets in different contexts, including investigators, children, proxies of the victim, the court, and the perpetrator’s reputation. The hermeneutic approach to triangulating these multiple perspectives resulted in a detailed unpacking of the offenders’ tactics.
Data analysis was conducted within and across cases, yielding new representations of each case as well as common themes across the collective. Data analysis proceeded in three stages as per Miles and Haberman (1984). First, summaries of each case were compiled, focusing on the overt forms of abuse evidenced in the relationship and then surrounding the concealed IPF. Stage two involved a within-case analysis to cross reference abuse seen pre-offense and surrounding the IPF, and vice versa. This process involved searching for subtleties in the data to compare tactics used across time, targets and in context. The third stage involved a cross-case thematic analysis to identify common themes.
Findings
Key Features of DA/Concealed IPF Cases.
Forms of Abuse pre and Post IPF.
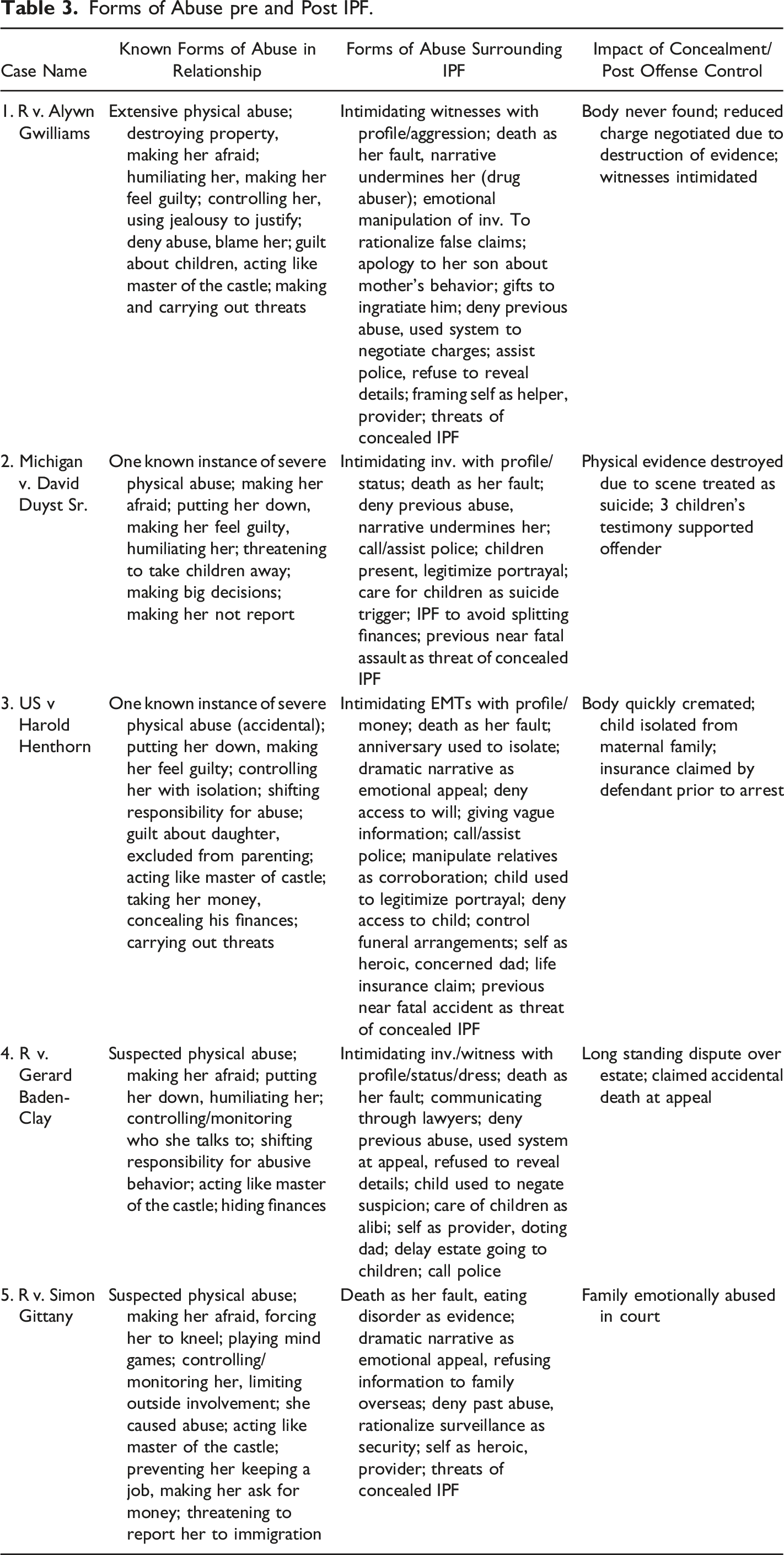
R v. Alwyn Gwilliams
Alwyn Gwilliams was physically violent, jealous, and controlling of his partner Dulcie Birt; he used intimidation, terror, threats, and destruction of property to dominate her. He had previously tied her to a tree; given her a black eye; punched her in the stomach; and threatened to kill her. In 2009, Birt was last seen by her son, before leaving in a car with Gwilliams. The couple was arguing, and he threatened to cut off her head. After her disappearance, Gwilliams destroyed evidence and physically intimidated female relatives into assisting him using tone and posturing. He texted Birt’s phone and went to her house to feign concern for her. He invoked misogynistic biases, maligning Birt as a promiscuous drug abuser, and casting himself as her protector and provider. He reported trying to help her get sober, giving her cash, and denied, minimized, or blamed her for his abuse. He ingratiated himself with Birt’s son, giving him food and money, and apologizing for Birt’s behavior. Six weeks later, Gwilliams admitted Birt died in a car accident (she was intoxicated and failed to wear a seatbelt) despite his attempts to save her, and he disposed of her body. He used concern for his disabled other partner as a rationale for his previous false statements. Extensive searches offered no corroboration for this accident scenario.
Before a Coronial Inquest, Gwilliams coerced witnesses using his reputation for violence, again influencing female family to assist. Gwilliams already being convicted and sentenced meant the truth could have no impact on his accountability for the murder. The inquest found Gwilliams assaulted Birt. He has never revealed the location of her remains.
Michigan v. David Duyst Sr
David Duyst Sr. was violent and abusive to his wife Sandra; he humiliated her by having a public affair with a co-worker at a family business, put her down and made her feel guilty for her frailties, controlled finances, and insisted Sandra submit to his authority.
In 2000 David murdered Sandra and reported a suicide; she had been depressed since being kicked in the head by a horse 2 years earlier. He politely stated “Ma’am my wife just tried to kill herself again. I think she did it this time”. David was helpful to police and passed two polygraph tests. He explained that since her head injury Sandra had gained weight and suffered memory loss; allegedly attempting suicide three times. The couples’ 13-year-old daughter corroborated this. David described threatening Sandra with losing her home and children. He used this conversation and her mental ill-health as triggers for her suicide. David framed a recorded voicemail from Sandra, insinuating her desire to separate by saying “you can go on without me” as evidence of her suicidality. He used his community involvement and status to disarm investigators and receive the benefit of the doubt. The children’s trauma was used to sidestep suspicion, implying no father would subject his children to that.
After her death, a note from Sandra was discovered indicating the horse accident was an assault by David. “If anything has happened to me, look first to David Duyst, Sr. He could be my killer. I would never commit suicide. He may have killed me.” (Duyst v. Rapelje, 2011, p. 21). This assault allowed him control of their business; prevented separation; and cast him as a hero. Sandra’s injuries were then capitalized upon to justify the suicide facade.
US v. Harold Henthorn
Harold Henthorn used control, isolation, and male privilege in his marriage to Dr Toni Henthorn. He controlled phone calls to Toni and dominated phone conversations with her family. He convinced Toni to move out of state, acted superior to her, cut her off, made all decisions, and used her faith to prevent divorce. He excluded her from parenting their daughter, put her down, and made her feel guilty. He shifted responsibility for his financial abuse and lied about his financial situation. The year before her death, he dropped a beam on her, nearly killing her in an alleged accident.
In 2012, Toni fell to her death while hiking with Harold. He described a treacherous climb down to her before calling 911, texting friends and her family, reporting her vital signs, and administering CPR. He demanded a helicopter evacuation, saying he would pay all associated costs and giving detailed information about his location. When rescuers arrived, Harold appeared upset and started giving Toni’s body chest compressions. Within days, and against her family’s request, Harold had Toni cremated. He stated this was her wish. He refused to tell her family if she had a will or produce it and refused to let her mother choose her final dress. Within 2 days, Harold attempted to claim one of three insurance policies.
Surrounding her death, Harold cast himself as heroic, employing a dramatic narrative to invoke sympathy from authorities, garner solidarity with her family, and prevent his version being questioned. He used their daughter to advance this narrative. Guardian ad litem noted the child’s insistence that Toni was stupid and clumsy. Harold used Toni’s family’s support as evidence of his innocence, while also criticizing their treatment of her (falsely stating they had not contacted her on her 50th birthday). He manipulated witnesses to support his version (including EMTs), and publicly condemned authorities who suspected him.
The Queen v. Gerard Baden-Clay
Gerard Baden-Clay was dominating in his marriage to Allison Baden-Clay. He had systematically isolated her and was controlling and emotionally abusive. He monitored conversations using a baby monitor, controlled finances and hid their financial position, deleted numbers from her phone, and blocked family numbers from calling.
Gerard murdered Allison in 2012, claiming he woke to find her gone. When she failed to return, after calling, texting, and searching for her (while preparing their three daughters for school), he reported her missing. His report was polite, formal, and twice referred to his parenting responsibilities. Police were immediately suspicious of Gerard due in part to apparent fingernail scratches on his face. He explained these were from shaving, and his eldest daughter indicated the same. Gerard used Allison’s absence on a school morning to subtly malign her as a mother while currying favor with authorities as a devoted father and husband. He wore a pressed suit on arrival of police, had tidied the house, and uncharacteristically served tea in China teacups. Gerard volunteered that he’d previously had an affair, but it was discovered this was ongoing, he’d given a deadline for leaving Allison, and he’d actively influenced what this woman told police. 11 days later, Allison’s body was discovered in a creek. He maintained that they had not argued or physically fought prior to her disappearance, that he could not have disposed of her body because he would not leave his children alone, and that suicide was likely. Gerard used Allison’s previous depression and her taking antidepressants as evidence supportive of suicide.
Framing Allison’s death as a suicide allowed Gerard to use several controlling tactics post-homicide. He self-initiated contact with police to establish his narrative and credibility. He used his parenting duties and daughter’s statement as leverage against suspicion, and his status to intimidate authorities. He denied or minimized all previous abuse and criticized Allison’s mental health. He portrayed himself as a pillar of the community, a provider, and a concerned father. His control continued to his appeal when he alleged Allison died accidentally but would not reveal the details.
R v. Simon Gittany
During their 1.5-year relationship, Simon Gittany was controlling and possessive of Lisa Harnum, depriving her of autonomy. He monitored her conduct openly and covertly, installing cameras inside their apartment and applications on her phone. Gittany threatened that if Harnum left, he would cancel her visa application and have her deported. He prevented her having a job, controlled all finances, and acted superior. He threatened she would be on the streets with nothing if she left him. A witness reported that Gittany had threatened to kill Harnum and make it look like a suicide. Harnum was seeing a counsellor and began giving belongings to a friend until she was able to separate. When Gittany became aware of this he threatened the counsellor and forced Harnum her to kneel in front of him and submit.
A few days later Harnum attempted to flee their apartment. She banged on the door of a neighbor, screaming for help. CCTV from outside the door showed Gittany grabbing her with a hand over her mouth and dragging her back. 69 seconds later, Gittany dropped Harnum from the balcony, killing her. He portrayed her death as either a suicide or an accident while she was attention-seeking. He used her eating disorder as evidence of mental ill-health. He reported a dramatic attempt to save her; with her slipping from his grasp. He refused to respond to Harnum’s mother begging for information. His first phone call was to an attorney, after which he refused to cooperate further with the investigation nor with the Harnum family.
Gittany invoked a hero narrative to juxtapose his own profile with Harnum’s and used grief to explain his DA behavior. This invoked sympathy, cast him as brave and traumatized, and made him more difficult for authorities to challenge for fear of being wrong. He blamed Harnum for past abuse, including insisting his surveillance was for security.
Thematic Analysis
The cross-case analysis revealed four themes illuminating how and why offenders use concealment to continue CC after an IPF, and unpacking the subtle, individualized forms this abuse takes in different contexts. The first theme uncovered that IPF concealers cultivate and capitalize on vulnerabilities in the victim and their situation to kill them and conceal the death as non-suspicious. Offenders plan how to exploit vulnerabilities, generally or specifically and across various periods. The strategies used are idiosyncratic, but the theme of planned, instrumental, and exploitative behaviors is clear. For example, Henthorn used an anniversary trip to lure Toni to a dangerous location despite she and her family’s misgivings after her first supposed accident. “Harold secretly worked with Toni’s coworkers to have her patient list cleared and then drafted a fake patient list to throw Toni off. That Friday, he arrived at her clinic and hid in an examination room, then surprised her with news of the trip.” (Fleeman, 2017, p. 25). Using colleagues to help with the surprise made it impossible for Toni to refuse. Harold then used the romance of their anniversary to assign blame to Toni for detouring from the main path, allegedly so they could share an intimate moment alone.
Gwilliams used Birt’s drug abuse and supposed relationships with other men to rationalize her disappearance after her murder. “Gwilliams said … that he loved her and would really miss her and hoped they found her alive. He said he had dropped Dulcie off at home at 10:30p.m. and had given her $300 because her boyfriend was sending threatening messages.” (Lock, 2014, p. 18). Birt’s homicide was spontaneously timed, but the behaviors used were planned and practiced. Threats to another partner mirrored Birt’s death: “[He] pointed to some bushland … and said ‘that’s where they’ll find you dead’” (Lock, 2014, p. 11). And an assault on a previous partner was markedly similar: “[Gwilliams’] victim was a woman with whom he had been in a relationship. The episode took place at a quarry at night. The attacks were described by the sentencing judge as involving “the utmost brutality” (The Queen v Gwilliams, 2013, p. 70). Gwilliams stripped this victim, beat and choked her, and put her head under the car wheel threatening to “finish her off” (Lock, 2014, p. 19). Such planning and use of victim vulnerability in concealed cases illustrates how offenders deliberately invoke concealment to avoid accountability and therefore maintain control.
The second theme identified is the consistency observed between abusive behaviors in the relationship and to conceal the IPF. All offenders used several of the same forms of abuse during the relationship as post-homicide, suggesting abuse tactics are fit to purpose in both contexts (Stark & Hester, 2019). Offenders conceal the homicide using versatile but practiced tactics, cementing CC perpetrators as goal-directed and deliberate, even after the victim’s death (Ross & Babcock, 2009; Spidel et al., 2007). For example, Gwilliams regularly used posturing and yelling to intimidate Birt. On the night of her death witnesses reported “he then yelled ‘how would you like me to cut your head off and let blood drip all over his doorstep’” (Lock, 2014, p. 9). The same tactics were used more subtly post-IPF to get witnesses to hide/destroy evidence and prevent them cooperating with police. “[Gwilliams’ sister] heard her brother yelling out to open the door. She did and he drove his utility in and yelled at her to shut it… Gwilliams had told her not to go to the police… She stated she had not been in contact with Gwilliams for years but [days before her testimony] a request had been made for her to be placed on his prison telephone list” (Lock, 2014, p. 13–4). This behavior created fear, capitalizing on her suspicions he was a murderer. The coroner remarked “a number of witnesses expressed concerns about their fears of possible retribution… I accept those fears are well founded” (Lock, 2014, p. 5). Gwilliams’ intimidation of others to conceal his behavior is plain pre and post-IPF, even while serving his sentence in prison.
While Sandra Duyst was alive, David blamed his threats of separation, and seeking sole custody of their children on her mental health. “He informed Sandra that he was going to file for divorce and that he had an excellent chance of gaining custody of the children” (Duyst v. Rapelje, 2011, p. 9). Her fear of these outcomes facilitated control. Post-IPF, he positioned her death as caused by her depression and used it to influence their children’s statements. After her murder he framed her letter as a false report and further evidence of her mental illness: “Defence counsel [explained Sandra] was attempting to frame her husband for her murder” (p. 22). Continuous repositioning of his abuse, including Sandra’s murder, as symptomatic of her mental illness was used to shift blame and avoid accountability in the hopes of maintaining control. This theme reinforces that IPF concealers continue using tactics that are well-practiced and likely to be successful at meeting their aims, post-homicide.
The third theme builds on the versatility described, relating to perpetrators controlling particular targets. Offenders often focused on one element to control post-IPF. This might be insurance or estates; custody of children; or how the victim is portrayed, including having her appear crazy or unreliable, to punish her proxies, or to save face. Each offender appeared focused on controlling certain targets, while the tactics used were broad and context specific.
Henthorn’s concealment of Toni’s murder appeared to focus on controlling their daughter, Haley. Post homicide and conviction he manipulated Haley, prevented access to Toni’s family, and fought their attempts to adopt her. Her guardian ad litem described the manipulation, stating he " [shrunk] her down to a puppet.” (Man sentenced to life, 2015, p. 7). Toni’s brother said, “after Toni’s death, the Defendant routinely proclaimed that Haley was doing ‘just fine’ … because the ‘real relationship’ was actually between Haley and him” he recalled Henthorn’s “selfish quest to hoard a child as a possession” (Family addresses judge, 2016, p. 5). The concealment facilitated these ongoing efforts to control, providing an alleged innocent rationale for Harold’s continuing abusive behavior.
Baden-Clay focused his control on finances, before and after his arrest. The day after Allison’s body was discovered, he made claim to her life insurance. He explained “Dad told me that I really had an obligation to the insurers to let them know, that was why I made the call” (Kos, 2017, p. 12). Doing so commenced litigation against the trust for his children which he did not capitulate for 5 years, after his conviction (Kohlbacher, 2017). Concealment of the homicide provided a convenient rationale for continued attempts to access these funds, and a much greater likelihood of success. Gerard’s attempts to control the only income available to his daughters is also notable as it belies his façade of a devoted father. Together these examples demonstrate how concealment facilitates what appears to be a key motivator for IPF concealers – control of particular targets like finances, children, or reputation.
The fourth theme involved the persistence of attempts to control after the IPF – sometimes long after the concealment was revealed. Upon recognizing they were suspected, offenders commonly changed their version to suit the evidence. This might involve now claiming that the victim died accidentally, and the offender only disposed of their body; or by reporting the victim died by suicide as opposed to accident. This pivot is not unexpected given the persistent need for control proposed in our theory and observed elsewhere. Maintenance of the façade and subsequent efforts to control sometimes occurred with no benefit to the perpetrator or even negative impacts, aligning with descriptions of CC as enduring (Anderson, 2005; Ornstein & Rickne, 2013). This is significant given the instrumentality seen in abuser profiles (Day & Bowen, 2015; Ross & Babcock, 2009; Spidel et al., 2007). For example, in a jurisdiction with “no body, no parole” laws, Gwilliams persisted in refusing to reveal the location of Birt’s remains, maintaining his accidental narrative, despite already pleading guilty and being sentenced.
Similarly, Baden-Clay proposed on appeal that he could have unintentionally caused Allison’s death. This new version contradicted his evidence at trial; “he denied that he had fought with his wife, killed her and disposed of her body” (The Queen v. Baden-Clay, 2016, p. 5). However, this new narrative led to his murder conviction first being set aside and replaced with manslaughter, then reinstated. Setting aside the murder conviction exemplifies the usefulness of these pivots by perpetrators. Even when new versions reveal the previous deception, concealers persist in attempts to limit their responsibility, often successfully maintaining some control over the process by doing so.
Gittany’s persistence in blaming Lisa Harnum for her own murder continued post-conviction, and to his detriment at sentencing. In open court Gittany stated the Harnum’s “might find some consolation in hearing [me] say that Lisa Harnum did not die as a result of being murdered” (R v. Gittany, 2014, p. 74). This shows Gittany’s continued attempts to control using the concealment, feigning sympathy but taking no responsibility and foreshadowing efforts to prolong litigation. This persistence was not viewed favourably by the sentencing judge, who observed “in the face of those remarks it is difficult to know where rehabilitation would begin. It appears to be an arid prospect” (R v. Gittany, 2014, p. 74). The persistence seen in this sample demonstrates the instrumentality of IPF concealers, continuing attempts to control despite only remote chances of success, and sometimes to their own detriment. Concealers appear either incapable of or simply unwilling to acknowledge the reality of their abuse and their failure in concealing it, rigidly continuing.
Discussion of Findings
IPFs commonly occur in relationships involving CC, when expert perpetrators perceive that their control over the victim is waning (Stark, 2009). IPF offenders then “change the project” (Dobash & Dobash, 2015, p.39), from controlling a living person, to punishing them for non-compliance. Our theory extends feminist theories of CC, adding that while punishing the victim, a concealed IPF allows perpetrators to maintain some form of control over her, the investigation of her death, her family, their relationship and children, and/or his reputation and finances. CC tactics used in the relationship extending to the planning, perpetration, and post-IPF behavior of the concealer provides evidence of continued attempts to control. A concealed IPF allows an offender to punish, control, and remain unaccountable - making it an attractive option for some. Such domination over what’s left of the relationship also explains the high levels of DA seen in IPF cases compared to other types of homicides (Eke, 2007; McLachlan, 2023), assuming most murderers want to avoid prosecution. Unlike other offenders, IPF concealers appear to be expert abusers who are highly motivated to regain control, goal-directed in their behavior and persistent.
The collective case studies illustrate that the same tactics used to coercively control women are also used surrounding concealed IPFs. The examples show that, like in many IPV cases, offenders use versatile power and control strategies in concealed IPFs, sometimes in subtle, context specific ways. They capitalize on the vulnerabilities of their victim and situation; using concealment to give abuse tactics more power. Some continue post-conviction and for no apparent gain other than maintaining control. The picture emerging is of expert abusers chronically and deliberately using concealment tactics that are practiced to facilitate control of targets most important to them. Each case illustrates the callousness and instrumentality involved in concealed IPF, offering critical insight into understanding this group of expert abusers.
Limitations
This study has some limitations. We note the conceptualization and measurement of CC is challenging, in both methods and definitions. Tactics of power and control are highly individualized behaviors, which may not seem abusive without contextual information held by the victim herself (Wangmann, 2021). Since the victim in these cases cannot provide this context, tactics of CC may be underestimated. Without a consistent definition of CC between, or within, countries (Stark & Hester, 2019), it was left to us to identify CC in each case. It was important to analyze each case not only for isolated instances of abuse, but for patterns of behaviors and their intent. While this does not rule out potential under-reporting of CC, it allows for a broader analysis of the tactics of abuse used both before and surrounding an IPF. We also note that local idiosyncrasies, structural forces, and intersectional axes of power were not the focus of our examination. This limits the discussion to the most macro or universalist abuse tactics, also potentially underestimating CC. Based on the method used, we simply cannot account for how location, legal processes and racial or ethnic dynamics restricts our assessment of CC or our identification of cases for inclusion in the sample.
Another limitation is our small number of solved cases. The five cases analyzed provide valuable, although limited, insight into how CC is extended beyond the murder of the victim. Though a larger sample of cases could provide more reliability in qualitative findings (Sandelowski, 1995), our results illustrate our proposed theory, offering a first step in an unexplored research space. Using a snapshot of cases, forms of abuse detected contribute to the limited understanding of how IPF perpetrators recover their control of the victim post-IPF. We note that subtleties may be missed when public documents are the sole data source. Police who first collect this data may not recognize certain behaviors are abusive, especially in absence of the victim’s voice. They also may not realize or record when a perpetrator is attempting to manipulate them. The same may be said of prosecutors, journalists, coroners, and witnesses. This limitation was mitigated by combining information collected from many sources including direct sources like emergency assistance calls, to provide a detailed picture of many of the control tactics perpetrated by our five offenders. While our method does not allow for statistical generalizability, it does enable theoretical advancement. We acknowledge the most adept offenders are not included here, as their concealment may never be revealed.
Implications
The argument that concealment of an IPF allows CC to extend beyond the homicide has several implications. Most notably, in preparation for a concealed IPF, perpetrators may leak signs of their plan, which may be used for prevention. Threatening homicide is a known risk factor for IPF (Stark, 2009), however we add that threatening a concealed IPF may be particularly important in predicting a perpetrator’s actions. Other behaviors like reporting mental health issues in the live victim (e.g., by saying she is suicidal) may reveal an offender’s intentions. Planning time together alone amidst a real or threatened separation might also be viewed suspiciously, as attempts to further isolate the victim and manipulate opportunities for non-suspicious death scenarios.
McPhedran et al. (2018) have suggested homicide-suicide is a unique type of IPF, however, when compared to the themes of the concealed IPFs in this study, some similarities emerge. Notably, both concealed IPF offenders and homicide-suicide offenders’ behaviors may be motivated by avoiding accountability or controlling the narrative post-femicide. The similarities between these types of IPF warrant further exploration. Both appear to represent significant trends that offer critical insight into the behavior and motivations of expert IPF offenders.
Other implications include addressing investigative challenges created by concealed IPFs, especially considering the manipulative personalities of offenders. Concealed IPFs are not often straightforward death investigations (Ferguson, 2021; Ferguson & McKinley, 2021). Perpetrators have a head start on investigators given their tendency to plan, foreshadow the innocent scenario, and manipulate witnesses convincingly. Training and resources for investigators are required to identify concealment and understand how offenders exploit opportunities to advance their narrative. Resources like protocols for practitioners investigating suspicious deaths of women are needed, to ensure that major inquiries begin early, documentation is secured, and evidence is collected before perpetrators may influence it. Outside of the death investigation, we note that work performed by death review teams could benefit from unpacking the critical insight provided by concealed IPF cases. Examining the behaviors associated with concealed IPFs in death review annual reports for example, allows for recommendations specific to concealment to be outlined for practitioners and policy makers. Dissemination of scholarship surrounding concealed IPFs is also necessary, to encourage practitioners to recognize these behaviors quickly and actively search for overt and subtle attempts at manipulation against themselves and others.
Finally, future empirical research is required to test our theory against a large set of solved IPF cases. Such research might focus on measuring common forms of power and control used in concealed IPF cases, and when or how they are likely to be successful. Not all IPF’s involve attempts at concealment, future research to clarify who uses it is a natural next step. Leakage by offenders when preparing for a concealed IPF is also a necessary area of study, to examine how these clues might be used in risk assessment or death investigations. This paper provides the starting point of such an approach, with the goal of revealing concealed IPFs and preventing the murder of women.
Footnotes
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
