Abstract
Due to the broadcast nature of wireless channel, attacks against wireless sensor networks are much easier to carry out as compared to wired networks. Passive attacks such as eavesdropping and traffic analysis cannot be eliminated even if cryptographic technologies are used. Conventional frames are usually designed to include checksum, which facilitates to adversaries capturing correct frames for further attacks. In most wireless sensor networks, source address and destination address at data link layer are unprotected, which makes traffic analysis quite easy. In this paper, we argue that the long-hold design principles of data link layer protocols are unreasonable from the perspective of wireless security. A secure ARQ scheme for wireless sensor networks named Sec-ARQ is proposed. Without the help of preshared keys or complex authentication infrastructure, Sec-ARQ protects frame checksum and addresses by cumulated checksum. Cumulated checksum is unknown to adversaries because of unavoidable wireless transmission errors. As frame checksum is unavailable to adversaries, error frames caused by collision cannot be detected, rendering eavesdropping useless. Addresses protection provided by cumulated checksum disables traffic analysis attacks. Sec-ARQ can defend against passive attacks effectively. Simulation results prove that Sec-ARQ can improve wireless security with little performance sacrifice, which is more suitable for resource-constrained wireless sensor networks.
1. Introduction
With the technology advances in wireless communications, wireless networking has been experiencing an explosive growth recently. While wireless communications provide great flexibility and mobility, they often come at the expense of security [1]. This is because wireless communications rely on open and public transmission media that raise further security vulnerabilities in addition to the security threats found in regular wired networks. Attacks against wireless networks are much easier to carry out as compared to wired networks. Cryptographic technologies are widely used to provide data confidentiality and integration. However, passive attacks such as eavesdropping and traffic analysis can be successfully launched even if the frames are encrypted [2]. Passive attacks are usually followed by active attacks. And such passive attacks are fundamental for successful active attacks. Eliminating passive attacks can improve wireless security dramatically.
Eavesdropping attacks try to capture frames for the purpose of accessing secret of the payload. Frame payload at data link layer is usually encrypted to protect sensitive information. It is very difficult to take advantage of weakness of a modern encryption system. But the secret can be recovered by offline brute-force attacks, in which the adversaries search the key or password exhaustively. On the one hand, with the development of high performance computing technologies such as GPU technology and cloud-based computing technology, up to 130 million password combinations are run through in just 20 minutes [3–5]. On the other hand, current researches show that users are reluctant to user complex passwords that are usually difficult to remember [6]. Both situations make wireless networks vulnerable to brute-force attacks, which cannot be eliminated by adopting more complex encryption algorithms. Normally, eavesdropping is the foundation of brute-force attacks. The adversaries must capture frames from targeted communications pair first. And only based on correct frames from this pair can they launch success brute-force attacks. That is, two conditions must be satisfied for successful brute-force attacks. First, the adversaries must identify the communication pairs. And secondly, the adversaries must capture correct frames between the communication pair and discard corrupted ones. Unfortunately, the source address and destination address are known to adversaries because they are not protected in conventional wireless networks. And most wireless frames at data link layer include checksum, which facilitates adversaries to capture correct frame and drop corrupted ones based on checksum validation. The adversaries can capture correct frame between the communication pair easily [7, 8].
Different from eavesdropping, traffic analysis attacks try to deduce the context information by analysing the traffic pattern from eavesdropping on wireless communication [9, 10]. For instance, adversaries might gather information such as how many terminals in the network, address and physical location for each terminal, network topology and the traffic volume, and pattern of the network. Such information can be used to deduce key terminals in the network such as sink terminals in wireless sensor networks, mesh router in mesh networks, or access point in wireless LAN. The following active attacks can be launched targeting these key terminals. Most conventional wireless networks are designed to provide strong encryption to payload in data link layer frame, but the source and destination addresses are left unprotected, which makes traffic analysis quite easy.
In this paper, we argue that the long-hold design principle is unreasonable from the perspective of wireless security. As illustrated in Figure 1, only payload is encrypted in conventional data link layer frame design. Other fields are transmitted without any protections, which make passive attacks quite easy. To eliminate passive attacks, link layer information such as source address, destination address, and checksum must be prevented from being decoded except the intended receivers. Link layer information protection is an effective countermeasure to passive attacks. Firstly, checksum protection prevents adversaries from distinguishing corrupted frame from correct ones. As wireless channel is error prone, adversaries may capture error frames for future brute-force attacks. Based on such untrustworthy frames, the success probability of the brute-force attacks decreased dramatically, rendering eavesdropping useless. Secondly, without source address and destination address, the adversaries cannot deduce network information by traffic analysis. Moreover, addresses protection can further confuse eavesdropping because they cannot identify the communication pair by addresses any more.

DATA frame at conventional wireless network is prone to passive attacks.
To protect information at data link layer, a secure ARQ (Automatic Repeat Request) scheme named Sec-ARQ is proposed. Without adopting preshared keys or complex authentication infrastructure, Sec-ARQ protects data link layer information by cumulated checksum. Cumulated checksum is a result of all frames that have been transmitted successfully from the transmitter to receiver. It is shared by the communication pair only. The adversaries cannot access cumulated checksum because of the unavoidable wireless frame error. Cumulated checksum can defend passive attacks effectively. Firstly, the checksum transmitted in frame is protected by cumulated checksum. The adversaries cannot distinguish error frames from correct ones without checksum. It is impossible for adversaries to launch success brute-force attacks based on such error prone frames. Secondly, cumulated checksum changes each time a successful transmission finished, which is used to provide dynamic address. As dynamic address is a hash result of cumulated checksum, and cumulated checksum is only available to the sender and receiver, it is impossible for the adversaries to analyse the traffic of wireless networks.
2. Related Work
In order to resist passive attacks, several countermeasures have been proposed. Fake packet injection is the most widely used approach to confuse adversaries. In such approaches [11–13], terminals in the network transmit fake packets while they are idle. With the present fake traffic, the adversaries cannot deduce traffic pattern or locate key terminals of the target network. The main drawback of fake packet injection is that the injected traffic will undoubtedly decrease network throughput and increase power consumption, especially for resource-constrained wireless networks such as wireless sensor networks. ACS (Anonymous Communication Scheme) is proposed in [14], which adopts the keyed hash result of address and sequence number as addresses. As the sequence number is increased on successful transmission, the resulting address changes dynamically and is unknown to adversaries. Because all terminals in the network use dynamic and encrypted addresses, the adversary cannot deduce anything about the network. In ACS, one key is necessary for each pair of terminals. In a real wireless network, one terminal may be required to communicate with many neighbours, and many keys are required. How to maintain or distribute these keys is a difficult task.
Countermeasures against eavesdropping can be divided into two categories, the physical security and encryption. ACDM and iJam are two typical physical security schemes. ACDM (Algebraic Channel Decomposition Multiplexing) [15] tries to solve open channel problem through physical layer spread-spectrum precoding. In ACDM, the transmit code vectors are determined from the SVD (singular value decomposition) of the convolution matrix describing the channel between the transmitter and desired receiver. Since any potential transmitter-eavesdropper channel will have a different multipath structure, eavesdropper’ ability to detect and decode the transmissions can be severely reduced. Under iJam [16], the sender repeats its transmission two times. For each sample in these repeated transmissions, the receiver randomly jams either the sample in the original transmission or the corresponding sample in the repetition. Since the eavesdropper does not know which signal sample is jammed and which one is clean, it cannot correctly decode the data. Such approaches require more complex wireless hardware devices. A great deal of time and efforts are needed to develop such devices. And further, such schemes need total replacements of wireless devices that are widely used.
Encryption approaches try to fight against eavesdropping through data encryption, which is the most widely used in conventional wireless networks. Unfortunately, as mentioned above, such approaches are under the risk of brute-force attack. For example, the weak password of the most popular security scheme WPA2-PSK can be cracked in about 20 minutes by using GPU technology [17].
In this paper, the proposed Sec-ARQ tries to eliminate passive attacks at data link layer. As compared to physical security, Sec-ARQ requires no hardware modification, only minimal firmware updates are necessary, which is particularly suitable for widely deployed wireless devices. Cumulated checksum instead of key is used to protect addresses and checksum at data link layer, which is more flexible as compared to ACS. Sec-ARQ can be deemed as complimentary strategy to conventional encryption approach. That is, it can defend against weak password brute-force attacks targeted at conventional encryption schemes, rendering eavesdropping attack useless. Dynamic addresses provided by cumulated checksum can further effectively eliminate traffic analysis attacks and eavesdropping attacks.
3. Attack Model and Introduction of ARQ
Adversaries can be divided into two categories: passive and active. Passive adversaries eavesdrop on communications between terminals in the network. Active adversaries can forge frames with any addresses and any payload data. Although Sec-ARQ is the focus on defending against passive attack, the scheme itself must be resistant to any active attacks. Therefore, we assume that adversaries have both of the above capabilities: an adversary can capture all the communications in the network and forge frame with any data in the network.
Sec-ARQ works at data link layer. Data link layer services include framing, error control, and media access control (MAC). MAC services are responsible for coordinating multiple terminals to access the wireless channel, while error control services are used to deal with error in wireless channel. In this paper, the proposed security scheme is implemented by improving error control scheme, leaving MAC schemes untouched. ARQ is the most widely used error control scheme. Sec-ARQ is based on improvement of ARQ scheme. We give a brief introduction of ARQ first.
To simplify presentation, denote the transmitter with S and the receiver with R. As illustrated in Figure 2, fields in DATA frame include frame control, duration, source address, destination address, sequence number, payload, and CRC checksum. Frame control field is mainly used for framing, and duration field is used for media access, which is out the scope of this paper. We focus on the following fields of the frame. Source address and destination address are the address of S and R, respectively. Sequence number is used for identifying the frame, which is an increasing number with step one. Payload is the data from upper layers, which is usually encrypted. FCS is the checksum of this frame.

DATA frame at link layer.
ARQ at data link layer is quite simple and efficient. As illustrated in Figure 3, we denote payload with m and checksum with
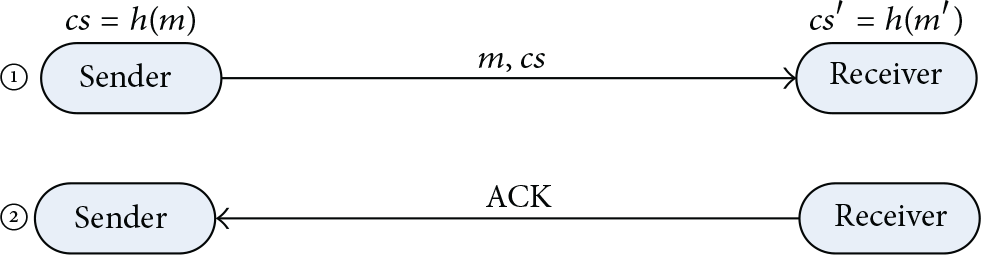
ARQ process at data link layer is efficient.

ACK frame for conventional wireless networks.
At data link layer, only payload is encrypted in conventional wireless networks, and addresses and checksum are transmitted without any protection, which is unreasonable from the perspective of wireless security. Due to the broadcast nature of wireless channel, adversaries can launch passive attacks easily. As to eavesdropping attacks, checksum in DATA frame facilitates adversaries to capture correct frames. Only based on correct frames can the following brute-force attack succeed. If the captured frames include error frames or even fake frames, the attack will be confused by such frames, which leads to failure of the following brute-force attacks. How to protect frame checksum and inject fake frame to confuse the adversaries is the first task of this paper. As to the traffic analysis attack, unprotected source address and destination address make traffic analysis quite easy. Therefore, how to protect these addresses without introducing complex authentication infrastructure is the second task of this paper.
It is commonly accepted that wireless channel are error prone; the packet error rate in wireless network is much higher than in wired domain. And further, because wireless channels are shared by many terminals, MAC schemes at link layer are very important, which coordinate terminals to share the channel efficiently. Unfortunately, the most used CSMA/CA based MAC schemes cannot eliminate hidden terminal in wireless network [18]. Frame collisions in wireless network are unavoidable with the presence of hidden terminals. For these reasons, the ARQ is widely used in wireless network to retransmit collided or error frames. But from another viewpoint, such instinct characteristic of wireless can be used for information protection. Because collisions and error frame are unavoidable for both the receiver and the adversaries, collisions at the adversaries can be used for security. The scheme proposed in this paper is based on this observation. It is based on conventional ARQ, we call it a secure ARQ (Sec-ARQ).
4. Description of Sec-ARQ
4.1. Basic Idea
As mentioned above, the checksum validation process of ARQ is executed by R. S calculates checksum of the frame and append it in DATA frame. R calculates another checksum of the received frame and compares it with the checksum in the frame. Such process is simple but has security flaw. This facilitates the adversaries to capture correct frames.
Now we redesign the checksum validation process as follows. Note that normal checksum function such as CRC is in fact a hash function. In this process, we use a keyed hash function, which takes another parameter key except the payload m. As illustrated in Figure 5, S calculates checksum

Basic idea of proposed ARQ.
Key extraction for S and R that is unknown to adversaries is based on the instinct characteristic of wireless networks. As we know, error frames and collisions are unavoidable at both R and the adversaries. Errors at R can be resolved by retransmission, but errors at the adversaries cannot be resolved. That is, S and R know exactly the frames that have already been transmitted. Error frames caused by collision or unreliable channel can be retransmitted by ARQ. But the adversaries may lose at least one frame with high probability, because they cannot request retransmission from S for error frames. This can be used to extract keys for checksum protection.
4.2. Checksum Protection
The details are illustrated in Figure 6. S maintains two variables, hsc and hsh. hsc is the cumulated checksum for S and hsh is called the hidden checksum for S. R maintains three variables, hrc, hrh, and hrt. hrc is the cumulated checksum for R. hrh is the hidden checksum for R. hrt is a temporary checksum. Sec-ARQ uses cumulated checksums hsc and hrc as the key. The hidden checksum hrh is the checksum that is actually transmitted in ACK frame. It is called a hidden checksum because it is protected by cumulated checksum.

Checksum protection in Sec-ARQ.
To illustrate how it works, we give an example. Supposing that hsc = hrc and a frame m is to be transmitted, S calculates the hidden checksum of mhsh using
In Sec-ARQ, cumulated checksum is used as a key to protect checksum of DATA frames. Cumulated checksum is the XORed result of all previous DATA frame checksum, and it is updated once new DATA frame is received successfully. As to the adversaries, they can trace the cumulated checksum just as R does. Since they cannot request retransmission from S, any error in the captured frame will make the cumulated checksum lost. Without cumulated checksum, the adversaries cannot validate the following frame any more. As compared to conventional approaches, benefits of cumulated checksum are twofold. Firstly, any terminals in the network can talk to any neighbour without key distribution protocol. This can greatly simplify the network design and improve performance of network. Secondly, cumulated checksum changes dynamically. It is impossible to access this key through brute-force attacks.
4.3. Defend Brute-Force Attacks against Cumulated Checksum
To identify a unique DATA frame, Sec-ARQ uses sequence number seq, which is included in DATA frame. R uses seq to determine whether this is a required frame. Assuming that previously received DATA frame is

Active attack protection.
Sec-ARQ adopts sequence number hashing to fight against such attacks. As hsc and hrc are known to be S and R, respectively, and adversary knows nothing about them, they can be used to protect sequence number against attacks. For this purpose, some modifications are necessary to DATA frame. A field name IV is appended to DATA frame. IV is a random vector to introduce computation complexity to adversaries. seq field of DATA frame is set to
4.4. Last Frame Problem in Sec-ARQ
Assuming that S sends a DATA frame to R, and no more frames are to be transmitted, the last frame problem occurs in Sec-ARQ. If S sends
4.5. Dynamic Addresses in Sec-ARQ
As mentioned above, anonymous address is an effective countermeasure to traffic analysis attacks. Conventional schemes such as ACS adopt preconfigured key to hide addresses. Sec-ARQ achieves anonymous address with the help of cumulated checksum. As cumulated checksum is a secret shared by S and R and is updated after each success transmission, it is ideal option for hidden address. We call them the dynamic addresses.
In wireless networks, each terminal has a unique MAC address. Neighbour discovery is usually achieved by beacon broadcasting, which includes MAC address of the transmitter. Therefore, S knows address of R before communication and so do R. Supposing MAC address of S is saddr, and the address of R is raddr, the dynamic address of them can be calculated as follows. Dynamic address of S is
In a typical wireless network that is composed of more than two terminals, there may be more than one terminal that send data to R. For each communication pair, R maintains one hrc and one seq. On receiving DATA frame, R must calculate a hash for each communication pair and compare it with .dest field in DATA frame. That is inefficient if R has many communications pairs and the networks are heavy loaded. Sec-ARQ overcomes such inefficiency by calculating the hash before DATA frame receiving. For example, if
The address in Sec-ARQ is a keyed hash result of address with cumulated checksum as key. Different from ACS, Sec-ARQ provides anonymous address through cumulated checksum. As cumulated checksum is updated on success transmission, the hashed results addresses are also changed, creating a dynamic address. With dynamic address, only R and S know the anticipated address of the next frame. To the adversaries, as hsc and hrc are unknown to them, they cannot trace the address of S and R. Without these addresses, it is impossible to deduce traffic pattern, network topology, or even how many terminals in the network, rendering traffic analysis attack impossible. Moreover, the adversaries cannot identify the communication pair with dynamic addresses, rendering eavesdropping and following brute-force even more difficult.
4.6. Formal Description of Sec-ARQ
See Algorithm 1.
Sender: On initialization: On have packet to be sent: Send DATA frame without checksum; Start a timer; On receive ACK frame: if if hsh = ACK.hrh then seq++; //next frame else Retransmit DATA end; end if; On timeout: Retransmit DATA Receiver: On initialization: On receive DATA if if DATA.seq = Send ACK with hrh; seq++; else if DATA.seq = Send ACK with hrh; end if; end if;
Algorithm 1
5. Performance Analysis and Evaluation
Because protocols at data link layer are low level protocol, efficiency is among the most important design considerations. Two different checksum functions are used in Sec-ARQ,
Sec-ARQ protects checksum by cumulated checksum, which is shared by the sender and receiver only. This is based on the facts that checksum is the only way to verify that the frame is correct. But someone may worry that the received signal strength may be used for another indication of frame error. Apparently, it is easy for adversaries to get received signal strength (RSS) for DATA frames. If packet error can be detected by RSS, Sec-ARQ will be bypassed, and the adversaries can drop error frames without checksum. As we know, the main reasons for frame error are weak signal and collisions [23]. First, the error frames introduced by collisions are irrelevant to RSS. Frames may be corrupted because of collision even if the RSS is pretty strong. And further, previous researches show that CSMA/CA based MAC protocols such as 802.11 cannot eliminate hidden terminal problem. Collisions introduced by hidden terminal problem are the main source for error frames in high densely deployed wireless network. Secondly, there are not established relations between RSS and error frame even if frame error is introduced by weak signals. Without checksum, the adversaries cannot confirm that the frame captured is error only by RSS. To validate the irrelevance between RSS and frame error, the first simulations is conducted.
Glomosim [24] is used for the simulations. As shown in Figure 8, two APs are deployed in the network, and 4 clients are associated with them, respectively. As WLAN are densely deployed, this is a simplified network. The build-in 802.11 of Glomosim is used for the simulation. Constant Bit Rate (CBR) model is used for the upper layer traffics. By adjusting the distance between APs, and APs to clients, several simulations are conducted. The results are shown in Figure 9.

Simulation topology.

Relation between signal strength and PER.
The simulations are configured for three payload sizes, which means different frame size. Short frame results in low packet error rate but cannot eliminate it. When the RSS is pretty strong (such as −40 dBm), the frame error rate remains not less than 2.1% because of collisions. We have conducted simulations with more nodes in the network, and the results reveal that more nodes in the network lead to greater frame collision rate. Simulation results show that error frame cannot be avoided even if the adversaries have very strong RSS.
Sec-ARQ is implemented in Glomosim. The adversaries lose information about the checksum if a single frame is corrupted. The time from the beginning of the transmission to the first error frame (we call loss sync time) is an important metric for Sec-ARQ. During loss sync time, the adversaries can trace checksum by checking DATA frame and ACK frame. That is, they can eavesdrop DATA from S and ACK frame from ACK. If no frame errors occur, they can validate DATA frame just like S do. Shorter loss sync time means less information lost. Simulations are conducted to measure loss sync time in the topology used in previous simulation, except that an adversary is included. The adversary is placed much closer to the AP to capture DATA frames from AP to its clients. The results are shown in Figure 10.

Mean time for first error frame.
Simulations results show loss sync time within 1.2 s irrespective of the frame size. Further analyses on the trace file of the simulation show that frame error are mainly introduced by collisions. As the adversary is placed much closer to the sender, there are less error frames introduced by weak signals. Note that Sec-ARQ is designed to protect conventional security schemes such as WPA2 from being brute-force attacked. Such brute-force attacks are based on key frames such as four-way handshakes for WPA2. Therefore, the transmitter can send information without key frames to protect information during loss sync time.
6. Conclusion
Sec-ARQ solves open channel problem at data link layer, which implies that no hardware modification is necessary. As wireless devices are widely used, this is particularly important. Sec-ARQ requires checksum calculation only, which is characterized by low computation complexity and easy implementation. Sec-ARQ cannot achieve wireless security alone; it is used to prevent other security schemes such as WPA2 from being brute-force attacked. Simulation results show that Sec-ARQ can improve wireless security by defending against passive attacks through cumulated checksum.
Footnotes
Competing Interests
The author declares that he has no competing interests.
