Abstract
This article focuses on intensifying in-vehicle biological wireless sensor networks for the persistence of monitoring the information on a precise vehicle. The wireless sensor networks will have enormous amount of nodules which are interrelated with each other. Therefore, these wireless sensor networks can be installed on a vehicle not only for monitoring perseverance but also for corroborating security with the support of a Global Positioning System expedient. In addition, the projected work focuses on reliable communiqué which is defined in terms of network reliability with discrepancy in reporting rate at each base station. To validate the efficiency of the proposed scheme, the simulation has been abetted using network simulator (NS2) and the outcomes indicate that when the sensors are installed, a robust system can be obtained with improved data transfer between the base stations. Moreover, a fortified in-vehicular sensor can be fixed in each vehicle with minimized path loss.
Introduction
In recent times, the sensor nodes have emerged in colossal fabrication due to their trivial extent, where the main exertion on deploying the nodes is (1) sensing in an innovative modus, (2) directing the information in an effectual way and (3) virtuous communication competences. These efficacious nodes will be dispersed in a spatial tactic in devoid of any wired intermediate (wireless communication is preferred).1,2 The foremost perseverance of sensor node is transmission of data to adjacent nodes, where the information will be finally conveyed to the base station. The role of base station is to accumulate the information, and this base station will act as a processor for controlling the interface. Furthermore, this base station will also function as a gateway for other adjoining complexes.3,4
The procedure of obtaining the information in a synchronized manner is also conceivable by deploying colossal expanse of sensor nodes. Moreover, these nodes can transfer the data over extensive expanses, and it also provides the advantage on supporting different applications which even includes irrigation, monitoring the traffic and environment and so on.5,6 An analogous feature for each sensor node is the multi-hop communication, where for each ad hoc network in wireless medium, the control cognisant routing protocols have been examined7–9 under different energy constraints in the framework of wireless sensor networks (WSNs). But the disadvantage of the methods listed in previous works7–9 is that the protocols will not be exploited in an effectual modus.
However, the applications of these WSNs and the requirements for each node will be distinct as these sensors will focus on numerous traits. 10 This tactical expansion will have several detriments on exploiting the WSN utterly which in turn will be inadequate by the energy constraint that is enacted by several sensors. Perhaps, this constraint will transpire only when sensing the environment and while processing the data in a wireless medium. It is well recognized that several applications or routing protocols that have been established on wired medium will have the advantage of providing better quality of service, but these protocols will be canned indecorous for applying in WSNs. In line with the above concern, a lot of protocols have been established for data routing in sensor networks.
The protocols thus suggested will make use of clusters for the perseverance of engendering effectual energy and the lifetime of the entire network can also be protracted. In correlation with the procedure listed above, the foremost effort of the cluster is to choose the cluster head (a precise node), where every node in the cluster will propel the information to the concerned cluster head. As a final point, the entire data will be conceded to the base station in two diverse techniques where in the first case, the cluster head will constantly be positioned nearby the base station unswervingly. In another case, there will be cluster heads located at the transitional station. Therefore, in order to assuage the delinquent of sensor nodes, dissimilar routing protocols have been examined.1–10
A unique tactic for accomplishing the combined chore on sensing is to use a trait based addressing for handling the task on data-centric routing, where the chief principle is allocating the tasks which is based on the imperative propagations that tends to instigate from other nodes in the entire network.8–10 These data-centric routing will have two different protocols (1) information via negotiation (IN) 11 and (2) directed diffusion, 12 where the IN protocol broadcasts the entire information to the neighbouring nodes if the nodes are concerned. While transmitting the data, the IN protocol will label the traditional data in a compacted size with the procedure of meta-data descriptors. But the directed diffusion will always use diverse kind of data-centric routing. 13
Related works
An effectual way on evading the valid routing protocol which is recognized on virtual routing circle has been inspected, 14 where the foremost standard relies on transmuting the arbitrary edifices that is tranquil on converting the edge nodes to a regular node by considering the mapping edge nodes to virtual nodes that transpires in a virtual circle. The reason behind electing the virtual circle is that it will avert avaricious advancing from deteriorating the proposed strategies. As a result, the control overhead and average length of routing paths can be utterly abridged. However, the edge network topology has been exploited for deciphering the routing void in geographic routing. Zhang et al. 14 have also emerged a new technique for void detection by establishing a path rendering the simulated harmonizes of the edge node.
An innovative procedure for segregating the network on large scale 15 has been explored whereas the purpose of exploring such method has the benefit on saving the energy effectively using cluster head and relay assortment schemes. In the projected process, the endowment has been provided for repeated clustering which consistently affords robust routing and hotspot solution. This tactical expansion will fragment the network on large scale into numerous concentric clusters and it can be perceived that a fan-shaped cluster subsists. In the conservatoire, the major intention relies on selecting the neighbourhood cluster head which is adjacent to the sink node. The tenacity of such assortment is to forward the data by organizing the cluster head in the form of chain. Then, during the last phase, the entire information will be directed till the sink node flinches to partition the system in two different stages. These stages can be categorized as low level and high level, where the clusters in low level will monitor in-cluster data collection and the clusters in high level will afford nine different low-level clusters for stirring the data transmission at inter level.
Conversely, for resolving two contradictory disputes, 16 an effective, secured and cost aware routing protocol has been inspected by exploiting two parameters (1) corresponding control of energy (2) random walking on apparent base. The initiators 16 observed that for a certain network topology, the consumption of energy is not allied to dispersal of vitality if it is uniform in extent. As a result, these consequences will condense the entire lifetime of the network. Therefore, an effectual scheme should be followed for enhancing the entire lifetime of the network, thus ensuring the distribution of information with security constraint. On the contrary, a protocol which has distinctive characteristics on gathering effectual information has been examined 17 where the optimization algorithm has been applied in two folds for the tenacity of detecting the ideal path with effective energy. Furthermore, if the approach is based on hybridization, then the quality of service and network lifetime will be enhanced with minimized bit error rate, delay and energy consumption.
The latter exertion is focussed on cluster-based procedures, where both upper and lower levels are deliberated with centralized and dispersed constellations. If the top-down approach is selected, then the priority will be given to upper-level cluster than the cluster at lower level. Consequently, with a fixed expanse of energy, the lifetime of the network will be exploited. Analogous towards 18 for selecting the upper level and lower level head, the integrated cluster and distributed clusters are used. To overcome the drawback of the aforesaid procedures17,18 a multi-hop routing with delay constraint has been inspected, 19 where this routing technique will select the cluster head for augmenting each nodule with the objective on minimizing both energy and delay from both transmitter and receiver. Despite the fact, the minimum itinerary for data diffusion will also be calculated. 19
Beforehand, for expending comprehensive data about a province, a region-based routing protocol has been recognized 20 for supporting point-to-point communications. From this type of protocols, the residence of the node can be easily deliberated. Also, this can be performed for static networks by exploiting the expanse feature, where the command for monitoring will be directed to intact expedient within a room of a particular building. Therefore, it is not that much significant to know which sensor has collected the data and the collected information will be used for determining the routing paths. Coupled with Zhao et al., 20 a social-based routing has also been established 21 with the objective on sinking the load of each node by regulating the flow of sending information, where the conveyance proportion can be minimized by modifying the device parameter.
Comparatively Zhao et al. 22 have elucidated the delinquent on diminishing the problem of energy routing with certain constraints which happens in a wireless multi-hop network. In this technique, the jammers will be fortified and will send the signal with a particular frequency that can be utilized by the nodes in the entire network. Nevertheless, this procedure can be applied in a sceptical mode due to the fact that the environment has to be dependent on restrained congestion. Recently, for exploiting path miscellany, an energy effective routing protocol which selects the power for transmission and forwarding is set optimally to make certain the connectivity of the entire network with dynamic workload sharing approach. But, the approach proposed in Haseeb et al. 23 and Chaabani et al. 24 is related to Lee and Kao 18 as the proposed method will use top-down approach for minimizing the energy consumption and path diversity. Even recent literatures25,26 have also been analysed for understanding different ways of installing multiple sensors using same hardware platform. Yeong et al. 25 have conducted experimental analysis using sensor fusion method under full automation process. In addition, the methods of improved reconstruction have also been examined as a survey model. 26 Both methods serve as an underlying platform for the development of projected method.
Research gap and motivation
Integration of intact system with vehicular wireless body sensor networks (WBSNs) is a challenging chore, and for overcoming the encounters such as reliability of the network, cluster rate and path loss, a lot of techniques have been offered.1–26 Also, there are few measures that are able to decipher these challenging errands. But all the procedures enumerated1–26 grieves from any one of the drawbacks. Therefore, the entire system thus needs an effective methodology for integrating the network with in-vehicular WBSNs, thus satisfying the consistency desires.
As an outcome for assimilating the vehicular biological WBSNs and for observing the entire network performance, an Energy Reliable (ER) routing protocol using cluster assortment procedures has been projected. In the proposed model, first, the Modified Chemical Reaction (MCR) algorithm is integrated for balanced clustering. Subsequently, the Adaptive Microscopic Swarming (AMS) algorithm has been smeared to compute the best optimal path with quick convergence rate among multiple paths.
Objectives
To the best of authors’ knowledge, there has been no preceding exertion on conjoining the vehicular biological WSNs with manifold objectives such as (1) minimizing the path loss, (2) deviation of reporting rates and (3) maximizing the network reliability in the presence of multiple signals. Therefore, the prime objective of the proposed exertion is to select presumptuous nodes, thus satisfying the aforementioned restraints by integrating the ER routing protocol using balanced clustering and by relating both MCR and AMS algorithms in two creases.
Problem formulation
Unlike other networks, the usage of WSNs in vehicle monitoring remnants is circumscribed as there is a prerequisite that the intact system in the vehicle needs to be sensibly explored. The persistence of this kind of exploration is to make sure about sustainable manoeuvre for the operation of WSNs. Therefore, for analysing the sensors in vehicle, the following major things need to be addressed:
To design a WSNs for adhesive in-vehicle atmosphere.
Incorporating these WSNs in the vehicles electrical system.
In the projected technique as shown in Figure 1, a Global Positioning System (GPS) will be integrated in the electrical system of the vehicle, where the information will be sent to the base station using the supporting technologies. The system can send the signals using 4G technologies instead of a Short Message Service (SMS). The reason behind using this kind of technology is that the reporting rate will be high when the network has been portioned into segments. The variation of reporting rate in each network can be given as
where

Enactment and design of smart vehicle monitoring with autonomous storing.
In each segregated network, the reporting rate should always be high in order to reduce the SMS-based technology. It is essential that the data for each vehicle should be conveyed at the beginning of every rotund. The subsequent equation ensures the exertion of the projected method at each round by also considering the length of the particular corpulent
where
When the sensors are installed in the vehicle, then there is a need that the data have to reach the base station within a short span of time. If the procedure ensues concomitantly, then reliable operation of the entire network can be accomplished. The network reliability can be analysed from the following equation
where Delay_E represents the total delay between instantaneous time generated and acknowledged. DL represents the limits on the chosen Delay_E.
In-vehicular WSNs, the information on real time should be collected even though the internal vehicular arrangement appears to be intricate. Furthermore, one of the critical factors in vehicular WSNs is the time variations of the information collected which is based on the received power. This kind of information transformation will be produced due to either large-scale or small-scale fading. If a fading occurs in large scale, then there is a need to monitor the path loss which can be given as
where l embodies the distance between transmitter and receiver, l0 is the reference distance, Pathloss (0) signifies the reference distance and w exemplifies the scattering parameter.
The reference distance (Pathloss (0)) can be calculated from equation (6)
The whole network enactment depends only on the path loss exponent and the distance between transmitted and received power. Moreover, the base station will receive numerous signals from many transmitters at same or different time. Therefore, there is a chance that signal interference will happen at the time of signal reception. So, in order to reduce this type of interferences, the base station should be designed in a particular way to make the entire system to operate in a user-friendly mode. It is conceivable to use the central limit theorem due to the presence of multipath constituents, where the signals can be separated by the Gaussian distribution as given be
where m symbolizes the received amplitude of the multipath signal, h exemplifies the peak amplitude and Bo represents the zero-order Bessel function.
The multipath signal constituent can also be epitomized as the relationship between deterministic signal power and variance of multipath signal which can be expressed in dB as
The type of conventional measurements will not accurately work in complex vehicular WSNs as there are huge numbers of electrical components connected inside the vehicle. Therefore, there is a need to evaluate the complete network data of the vehicle in addition to authentic allocations. Since three different sensors are used a back end transfer, process will be created for designing an intelligent algorithm with distributed storage system. The working model of multi-hop protocol with MCR and AMS is designed so that a sensor will be positioned in suitable places inside the vehicle. Therefore, the installed sensors will monitor corresponding parameter and it reports to the central station which is treated as a receiver in corresponding sub-interval areas. Thus, the distance can be defined using equation (9) as
where
Optimization algorithms
In the proposed method, multi-hop routing protocol is applied for avoiding duplication of same packets, and in addition for each period of time, the hop count will be reduced; therefore, at last count (0th count), entire packet will be discarded from the network. Moreover, if possible instead of using standard IP address to each packet, a sequence number will be provided for easy identification with application of selective flooding. An ER protocol for vehicular WSNs using optimal clustering and path selection techniques is combined with the MCR algorithm for balanced clustering. Generally, clustering consists of cluster formation and cluster head selection. Subsequently, the AMS algorithm is pooled to compute consistent routing by concerning both source and destination. In proposed method, there are four scenarios where to code each scenario, individual attention to each issue is required.
To simplify the complications and to ensure the individual attention of all cases, the algorithm is designed in two folds. The first algorithm which is called MCR will reduce the number of population, energy expenditure and collision rate of packets. Then, the aggregated data will be passed to AMS algorithm, where the fitness function will be calculated for providing precise values. Finally, all the values will be passed to the individual from the network server.
Balanced cluster incorporating MCR
The MCR is a nature stirred meta-heuristic algorithm which is based on populace, thus ensuing the principle of chemical reaction, where the procedure encrypts necessary data which will be arranged in the form of molecular elements. The necessity of incorporating the meta-heuristic algorithm is that it will explore the regions when there is a need for optimizing large number of decision variables with minimum number of reiterations.
For optimization, the MCR will attain the derivatives that are essential for making certain decisions. 26 The foremost intention behind choosing MCR algorithm is due to its ability on searching the local solution intensely. The performance of MCR can be greatly improved by making the step size to be adaptive. Furthermore, the retort of elements will monitor the arrangement of components which will be finally transmuted into products. In vehicular WSNs, there will be dissimilar intensities; therefore, the molecules with diverse energies will be transformed into produces, where only minimum energy is necessary for adaptation process. The process is followed by considering the decree on sustaining the energy using either distinct or multi-molecular reactions.
The search space is discovered in such a way by means of utilizing both manoeuvres such as combination and corrosion. The elucidations can be engendered by inter-molecular ineffective collision operators. The adaptive collision structure is pre-arranged in an exact mode for avoiding redundant computational interval. The computational time will become ineffective occasionally due to intersection of functionalities. Therefore, fitness value will elect the molecules relatively than following the environs manoeuvre which can be specified as follows
where
The clustering rate is a user-demarcated constriction which can be fixed during effecting, and it is generally selected empirically by users. The clustering rate can be given by a sigmoid function as follows
where NC embodies the number of iterations for manipulating the rate, and AVi denotes the maximum allowable rate for evaluating the functions.
The MCR technique is acquainting with selective strategies, where the fragments are selected randomly without affecting the convergence rate when compared with other techniques. 24
Segment procedure for elucidating MCR with balanced clustering
Step 1: initialize the parameters such as number of iterations (NC), populace size and step size Cluster_Rate (CR)
Step 2: create the Pop size for every element
where CPt and IPt are the current population and the initial population size, respectively.
Step 3: generate binary values (Bp) [0,1], if Bp < CR, an arbitrary fragment is selected.
Step 4: check for decomposition and trigger criteria.
Step 5: if the criteria are accurate stop, otherwise go to Step 2.
Gestalt of AMS
The AMS is commonly enthused by a cluster of rummaging comportment of bacteria. Predominantly, the AMS is inspired by a certain behaviour which is signified as chemo-taxis, where the procedure will identify the chemical gradients in the nutrients and by consuming these chemicals the bacteria inclines to move towards an explicit indicator. The forte behind AMS is that the algorithm will always make required arrangements for maximizing the energy consumption to solve the complications in real time. The AMS will always ensure the following four steps ensue in the specific order:
Chemo-taxis.
Crawling.
Reproduction.
Riddance diffusion.
In AMS, the bacteria will deter the elements in the environment and they can distinguish each chemical that they secrete. These bacteria will follow the principle of propulsion, where they move round the environs in a directed mode. If a specific cell interrelates, then the cells will swarm the food source, repel and sometimes both cells will ignore each other. This category of information dispensation technique will allow the bacterial cells to move around and collect the swarm for choosing the optimal solutions.
Enactment of AMS with MCR
The purpose of integrating AMS with MCR is to further speed up the convergence procedure within less number of iterations and also for enhancing the accuracy of entire network. The role of AMS is to fragment the field and the detachment will resolve the direction of swarm from choosing the best individual in field. This can avert the convergence from falling protracted, and in turn, it will also improve the precision of the network. Moreover, in AMS optimization algorithm, the precipitate convergence speed cannot be avoided even when it tends to search for optimal solutions during latter stage. The optimum solution can be found by expending the following
where posi symbolizes the locus of ith bacterium, Bk embodies the optimal solution established by the neighbouring solution, and Dk represents the swarming direction, where the molecules will lie in the range [−1, 1].
The AMS consists of microcells and the microbes, where they are allowed to freely move everywhere in search space. The microbes will make the entire network to move towards the global optima by consenting the plummeting components during last portion of the optimization process. The variations can be given as
where c1 and c2 denote the random numbers in binary form; r1y, r1z, r2y and r2z are the measurement quantities (constant); i and mi exemplify the current iteration and the maximum iteration that are permissible, respectively, and Dk2 designates the direction, where the elements lie within the range [−1, 1].
If the parameters are varied in a proper modus, then the optimum value can be enhanced, where a better convergence can be observed. The effective flow for smart vehicle monitoring system is given in Figure 2.

Effective flow of the projected system.
Step-by-step procedure for solving AMS with MCR
The following steps indicate the procedure to be followed when AMS is integrated with MCR:
Step 1: initialize parameters such as size of population, elements of the search space and swimming length that is necessary for accomplishment of optimal solutions.
Step 2: find the pre-eminent elucidation by the microcell on the intact field.
Step 3: eliminate the diffusion circle and generate the reproduction and chemo-tactic loop.
Step 4: compute the fitness function for each field.
Step 5: find the best solution by the entire microcell.
Step 6: if t < Chemo-tactic Step (CS) and if x < Reproduction Step (RS), go to Step 3.
Step 7: eliminate the bacterial elements.
Step 8: if y < dispersal stop. Otherwise go to Step 3.
Results and discussion
After several real-time tests, the proposed hardware setup has been established by installing corresponding sensors in all portions of vehicles that can able to provide corresponding information to each individual. The following sensors such as engine speed sensor which determines the crankshaft position, a small listening device which is termed as engine knock sensor that works with both trembling and wide-ranging positions, a regulate sensor that observes the amount of air flow inside the engine and a vehicle speed sensor which monitors the speed of wheel are connected with BeagleBoard which uses Node-Red online platform. Using the aforementioned setup, smart vehicles can be established and corresponding setup has been given in Table 1.
Hardware arrangement.

Network reliability
In the proposed method, a connection less service has been used, where there is no need of an additional circuit to deliver the packets and each packet can choose their own path for packet delivery. Therefore, in this case, dependability of the network through various paths should be established; hence, reliability has been deliberated as a major concern. All packets have been delivered directly to the base station by following different paths and check sum for each packet has been checked. The base station is having the capability to store and forward all packets to each individual user as data of every individual will be stored only in base station. After integrating three different sensors, reliability of each sensor per unit time in BeagleBoard has been observed and all real-time values are simulated and shown in Figure 3.

Consistency of network.
Figure 3 shows the comparison of network reliability with existing method, 25 but in previous case, the investigators have examined the same model using less number of sensors. From Figure 3, it can be seen that number of nodes has been considered from 1000 to 10,000, and reliability has been checked for every day for a period of gap between 8 and 9 h. After proper surveillance, it can be seen that the proposed method provides higher reliability when compared to existing method. For example, if 5000 nodes are considered, then reliability of existing method is 0.5 per unit time whereas for same number of nodes, the proposed method is high and constant reliability which is equal to 0.9 per unit time. Even if the number of nodes increases, then proposed method can able to provide constant reliability to the entire network.
Energy expenditure
Figure 4 explicates the total energy that is disbursed by each node that is connected to different sensors. Since the proposed method focuses on data communication and delivery, more amount of power is needed. Therefore, for knowing the amount of power that is consumed for data management, Figure 4 is plotted and all the real-time values are directly conducted and delivered to Node-Red module. The values that are observed from Node-Red are plotted in MATLAB for better understanding to users. From Figure 5, it can be seen that number of nodes are considered from 1000 to 10,000 and for each corresponding node, amount of energy has been simulated. For each nodal value, the proposed method consumes less amount of power when compared to existing method. 25 For example, if 5000 sensor nodes are present, then amount of power that is consumed by proposed method is 95 W, whereas for same number of nodes, existing method consumes 177 W which is much higher and amount of power is being wasted since more number of nodes remains in ideal condition.
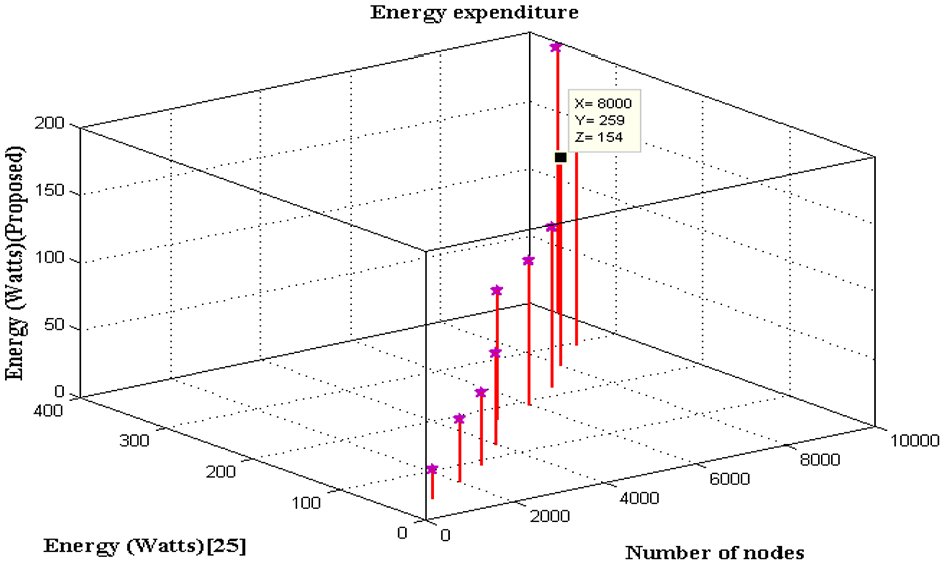
Energy expenditure.

Data rate of packets.
Throughput
In this scenario, throughput is evaluated using packet transmission technology which is sent for every second to the destination. It is apparent that data rate of the network should be higher, and in most cases, flow control technology has to be enabled for entire network. This type of flow control technique is used to avoid divergence between different packets since both transmitter and receiver should be in a position to send and receive packets in same data rate during bi-directional transmission. If there is high data rate, then packets will be successfully transmitted within short period of time and there is no need to provide random amount of waiting time to each user. The values of throughput for each packet are simulated and shown in Figure 5.
From Figure 5, it can be observed that data rate of packet delivery is much higher for proposed method. For example, if number of nodes reserved for each packet is 7000, then throughput of existing method is 1176 packets per second, whereas for same number of nodes, the proposed method provides higher throughput which is observed as 9239 packets per second. This proves that higher throughput can be achieved using three different sensors within a short period of time.
Network lifetime
Network lifetime determines the amount of time that each packet remains in the transmission media without being discarded. Since in the proposed method a hop method is used, separate sequence number will be provided for each data packet that is transmitted through base station. If hop count is decreased during each period of time in order to avoid duplication of data from other sources, it is necessary to determine the network lifetime of each sensor node. In case if a node fails to capture the entire data, then selective nodes can be chosen without reducing the high features of the network. The values of network lifetime are plotted in real time by observing the unpredictable values for a period of 7 days, and the simulated results are shown in Figure 6.

Network lifetime.
From Figure 6, it can be seen that same number of nodes has been considered from 1000 to 10,000, and for each node, packet lifetime is calculated. It can be observed in proposed method for each node, corresponding packets stay in the network for longer period. For example, if 7000 nodes are present, then packet lifetime in the network is observed to be 56 h, whereas with same number of nodes, existing method 25 can protect the packet for a period of 43 h. This proves that installed sensors in proposed method can able to store and forward more number of packets to destination when compared to existing method.
Performance analysis
In this section, performance analysis of proposed algorithm has been carried out using mobility model for defining the amount of control messages and time complexity for convergence analysis.
Mobility model
In the proposed method, mobility model is analysed using number of control messages which is present at both source and destination. For each metre, as packet authorizations are provided, the number of control messages should be decreased as soon hop count flinches. Figure 7 shows mobility model where the number of nodes is considered to be from 1000 to 10,000 and for each metre of node, both source and destination control messages are calculated. It can be observed that till 5000 nodes, the number of control messages for transmitter is very high, but once hop count has been started, the number of control messages has been reduced to great extent. The same case is applicable for receiver also, but in the initial stage itself, the packets at receiver have less number of control messages, and therefore, after the hop count, the number of control messages reached to 1. This type of mobility model provides standard synchronization between different packets from source to destination.

Mobility model of source and destination.
Time complexity
Since the system model is integrated with MCR and AMS, it is necessary to evaluate complexity of each packet transmitted during every interval of time. If the time complexity of proposed algorithm is lesser, then it can able to perform well in all circumstances in real-time situations. Figure 8 portrays complexity of packets that exists during certain interval of time where the numbers of nodes are considered as 1000–10,000. It can be observed that up to 4000 nodes, the time complexity varies extremely larger. Whereas, exactly when the number of nodes is 5000, the time period for transmission of each packet remains constant and is equal to 256 s. This simulation proves that time complexity of proposed model is much lower and convergence can be achieved in a firm way.

Time complexity of proposed algorithm.
Conclusion
Ensuing the innovative introduction of biological WSNs in vehicles, this exertion emphasizes on reliable inter-vehicular communication–based wireless sensors on the perception of storing the data in cloud. It is also conceivable that if the base stations are increased, then the congestion rate will be dwindled further. For providing better quality in terms of communication between transmitter and receiver, this technique regulates the reporting rate at a particular time period. Furthermore, to ease the design of networks, an energy efficient protocol has been integrated. The simulation results show that after integrating the proposed algorithm in two folds with cluster-based method, the convergence rate appears to be less significant when compared with existing methods. Future work will focus on designing a WSN with exertion on bandwidth estimate for augmenting the enactment of vehicular WSNs.
Footnotes
Acknowledgements
This research was funded by the Deanship of Scientific Research at Princess Nourah bint Abdulrahman University through the Fast-track Research Funding Program.
Handling Editor: Miguel Acevedo
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship and/or publication of this article: This research was funded by the Deanship of Scientific Research at Princess Nourah bint Abdulrahman University through the Fast-track Research Funding Program.