Abstract
In this article, based on wavelet reconstruction and fractal dimension, a medical image authentication method is implemented. According to the local and global methods, the regularity of the mutation structure in the carrier information is analyzed through a measurement defined in the medical image transformation domain. To eliminate the redundancy of the reconstructed data, the fractal dimension is used to reduce the attributes of the reconstructed wavelet coefficients. According to the singularity of the fractal dimension of the block information, the key features are extracted and the fractal feature is constructed as the authentication feature of the images. The experimental results show that the authentication scheme has good robustness against attacks, such as JPEG compression, multiplicative noise, salt and pepper noise, Gaussian noise, image rotation, scaling attack, sharpening, clipping attack, median filtering, contrast enhancement, and brightness enhancement.
Introduction
The rapid development of 5G technology makes tele-medicine and tele-consultation become a reality. The authentication of the authenticity, integrity, and validity of medical information in the process of tele-medicine has become a hot issue in current research. Medical information is different from other digital information. Any small changes in digital medical information may cause medical disputes. Therefore, no noise is added during the authentication process, and only using the inherent properties and internal characteristics of digital medical information to complete copyright authentication has become a feasible scheme for medical information authentication. Aiming at the security authentication problem of the E-health application environment, many experts and scholars have proposed a series of schemes.1–5 Ashima Anand combined discrete wavelet transform (DWT) and singular value decomposition (SVD) technology and gave a feasible scheme for the security authentication of patient data by embedding multi-level watermark into medical carrier image. 6 To realize the security authentication of medical information, Solihah Gull exploited the Huffman coding method to realize the reversible data hiding. 7 Babu completed the authentication of medical images using multiple digital signatures. 8
On the basis of summarizing the previous work, combining multi-scale wavelet transform and fractal dimension theory, a medical image authentication method based on wavelet reconstruction and fractal dimension is proposed. The novelty along with the contributions of this article is as follows:
This scheme makes full use of the inherent stability of the reconstructed information in the wavelet transform domain. Based on the fractal dimension of the block information, the scheme analyzes and studies the difference of the coarse degree of the block information and the structural characteristics of the data. The stable relationship of the roughness difference is used to construct the fractal features.
The quantified fractal features are used as the authentication information of the medical images. The authentication method combines the scale invariance of the fractal dimension and the advantages of multi-resolution analysis of wavelet decomposition.
There is no noise added in the authentication process. Through all kinds of conventional attack tests, the practicability of this method is verified.
Related technique
Wavelet
As an important mathematical tool, wavelet is widely used in many aspects of digital image processing due to its frequency decomposition, multi-resolution analysis, and other characteristics. The wavelet transform adopts the systematic method of local dependence on the whole, makes full use of the signal separation function of wavelet, and performs multi-scale refinement analysis of the signal through translation and expansion. The definition of wavelet transform is given below.
Set the function

where
The mother wavelet function

here,
With the change of the factors
For any function

here,
The factors
The corresponding discrete wavelet function

The discrete wavelet coefficients


Formula (5) is called discrete wavelet transform and
Wavelet transform has good time-frequency localization, scale transformation, and directivity. Meanwhile, wavelet transform is especially suitable for analyzing digital images with rich details, poor spatial correlation, and low redundancy. 9 In scale transformation, wavelet and fractal have a profound internal relationship.
Fractal
The concept of fractal was first introduced by Hausdorff in 1919 and then improved and developed by Mandelbrot in 1975. In fractal theory, fractal dimension can measure the singularity of signal and the ability of filling space which reflects the effectiveness of the space occupied by complex shapes. The fractal dimension is a measure of the irregularity of complex shapes and it can quantitatively describe the fractal characteristics of the structural region in a nonlinear system. Fractal dimension is a morphological characteristic parameter with constant signal scale which reflects the similarity of signals. It is an important structural feature of fractal signals. Using fractal dimension, we can quantitatively describe the relationship between data points and surrounding points, accurately describe the spatial characteristics of the signal, and observe the essential content of the signal from another angle. In this article, the stability of fractal dimension under different attack modes is tested. According to the working mode of E-health, the robustness of fractal dimension is deeply analyzed and studied. In this scheme, the fractal dimension is measured using the fractal Brownian random field model. 10
The authentication scheme
The authentication process is presented in this section. This section included two parts, one is the ownership construction and the other is the ownership verification.
Ownership construction phase
The low-frequency detail region of medical image is obtained by discrete wavelet transform, and the low-frequency approximate data are reconstructed by coefficient. The stable feature regions are found in the reconstructed data and then the fractal dimension of each block is analyzed and calculated. Analyze and normalize the fractal dimension to construct a feature matrix which is stored in the third-party certification center as authentication information. Figure 1 shows the process of copyright construction, and the detailed authentication process is as follows.

Ownership information construction phase.
Ownership verification phase
Figure 2 gives a schematic diagram of the copyright authentication process. The detailed implementation process is as follows:

Ownership information verification phase flow.
Analysis of experimental results
To compare the scheme of this article with the research work of other authors, six pairs of medical images are selected as the test objects. The size of the tested image is 512×512. The tested images all come from the public network platform https://peir.path.uab.edu/library/. The scheme of this article has been tested on all six types of medical images. Due to space limitations, only the test results of Adrenal images are given. Figure 3 shows the test examples of six kinds of medical images and also shows a secret copyright image. The size of the secret copyright image is 32×32.
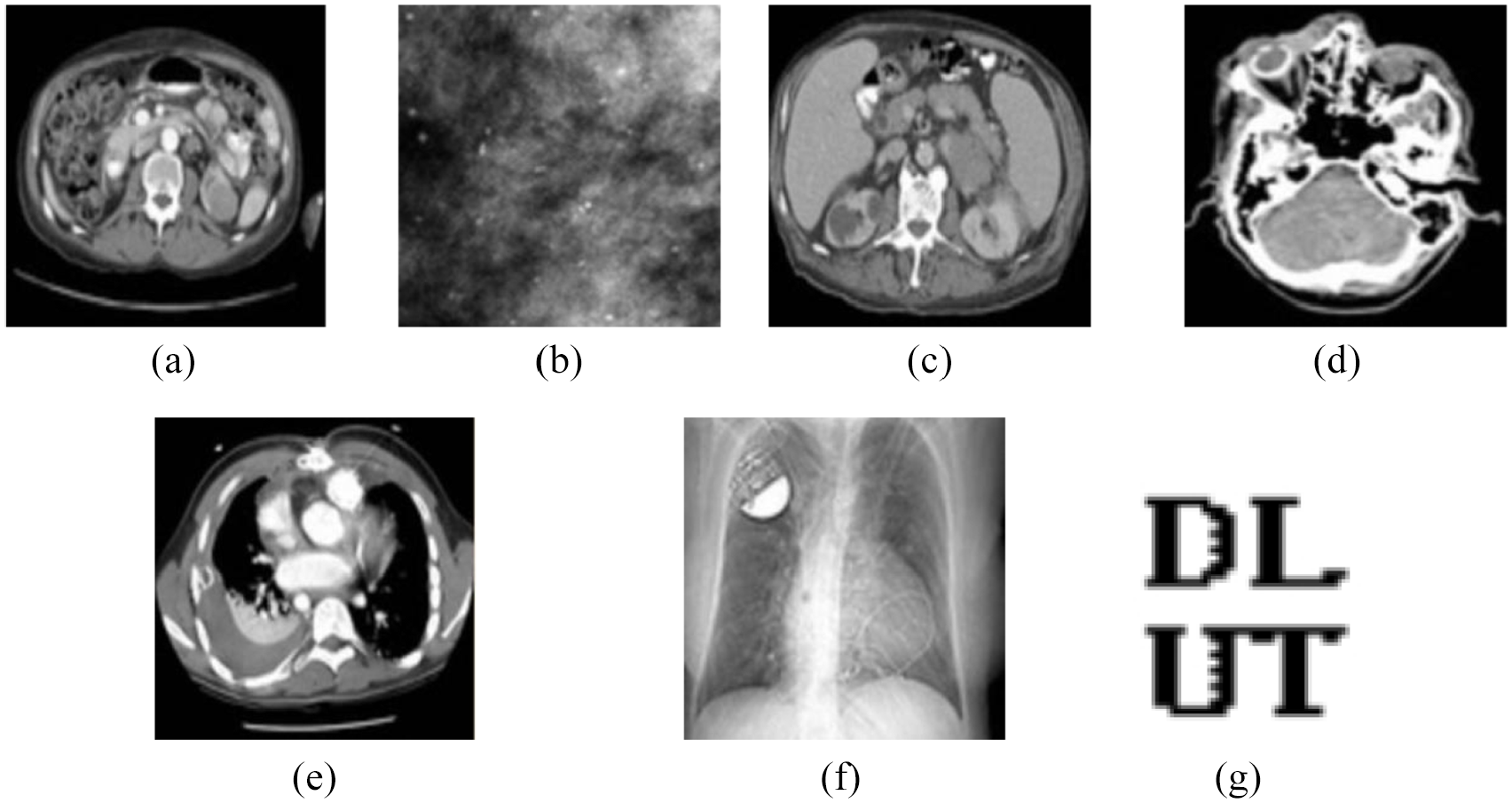
Tested images and secret copyright image: (a) abdomen, (b) breast, (c) adrenal, (d) head, (e) heart, (f) lung, and (g) secret copyright image.
To quantitatively characterize the robustness and effectiveness of the authentication method, the peak signal-to-noise ratio (


Correlation test of the carrier images
However, the features extracted from the images can express and describe the essential attributes of the carrier. Meanwhile, the authentication features extracted from different images should be independent of each other and not related to each other. To verify the independence of the proposed method, the authentication features of six test images are solved, respectively, and the correlation of the feature data is calculated and analyzed. Table 1 shows the correlation test results. It can be seen from Table 1 that the correlation coefficients of the features of different test images are mostly around 0.5 which shows that there are significant differences between the features extracted for different images.
Similarity test between different images.

Experimental results and analysis
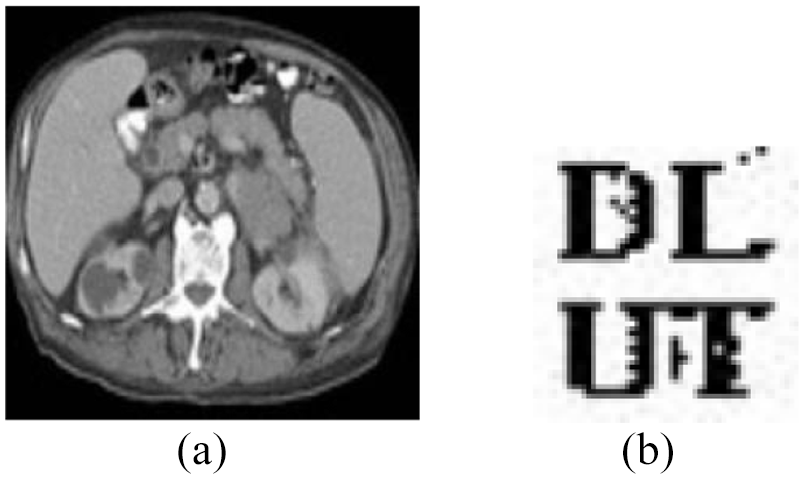
In the process of tele-medicine and tele-consultation, the transmitted medical images will be affected by a series of noises. Figures 4–14 show the robustness experiments of medical image Adrenal under the common attack modes. The attack types include image rotation (10°), scaling attack (reducing to 50%), sharpening, JPEG compression (compression factor 50%), salt and pepper noise (0.001), Gaussian noise (0.001), multiplicative noise (0.01), contrast enhancement, brightness enhancement, clipping attack (1/5), median filtering (7×7), and so on.

(a) JPEG compression attack PSNR = 43.1704. (b) Recovered secret copyright image from (a) (NC = 0.9941, SSIM = 0.9933).

(a) Salt and pepper noise attack PSNR = 34.4574. (b) Recovered secret copyright image from (a) (NC = 0.9971, SSIM = 0.9929).

(a) Gaussian noise attack PSNR = 31.9297. (b)Recovered secret copyright image from (a) (NC = 0.9893, SSIM = 0.9927).

(a) Rotation attack PSNR = 35.1048. (b) Recovered secret copyright image from (a) (NC = 0.9971, SSIM = 0.9927).

(a) Scaling attack PSNR = 48.6735. (b) Recovered secret copyright image from (a) (NC = 0.9971, SSIM = 0.9929).
(a) Sharpening attack PSNR = 36.1572. (b) Recovered secret copyright image from (a) (NC = 0.9834, SSIM = 0.9931).

(a) Multiplicative noise attack PSNR = 43.1704. (b) Recovered secret copyright image from (a) (NC = 0.9883, SSIM = 0.9926).

(a) Cropping attack PSNR = 17.9704. (b) Recovered secret copyright image from (a) (NC = 1, SSIM = 0.9928).

(a) Median filtering attack PSNR = 39.0042. (b) Recovered secret copyright image from (a) (NC = 0.9961, SSIM = 0.9929).

(a) Contrast enhancement attack PSNR = 32.5055. (b) Recovered secret copyright image from (a) (NC = 0.9785, SSIM = 0.9927).

(a) Brightness enhancement attack PSNR = 27.2279. (b)Recovered secret copyright image from (a) (NC = 0.9541, SSIM = 0.9931).
Medical information is different from other types of carrier information. Any subtle changes in medical images may cause special attention. From the simulation tests given in Figures 4–14, it can be seen that there are a variety of simulated attack methods that have caused major changes to the medical image. As shown in Figure 11, the test image is cut by 1/5 which causes a huge visual change. Its
Algorithm comparison tests
For different attack modes, Tables 2 and 3 show the comparison results between this method and other authentication methods. From the comparison results, it can be found that the method proposed in this article shows better robustness against common attack modes, such as noise, rotation, and cropping.
Comparison tests (1).

Comparison tests (2).

Conclusion
By measuring and analyzing the fractal dimension of medical image in wavelet reconstruction domain, the security authentication scheme of medical image is realized. The scheme does not add any noise. This method fully combines the multi-scale decomposition of wavelet transform and fractal singularity recognition. The inherent regularity of the hierarchical structure of the data is fully analyzed and mined. This method not only measures the anti-noise property of carrier features but also shows the stability of fractal features of carrier information under multi-scale and multi-resolution changes. A series of tests show that the authentication method is scale-invariant, rotation-invariant, and is robust to geometric deformation and noise of medical images. At the same time, the algorithm has good universality and can be extended to military images with higher security authentication level. The authentication method has good theoretical significance and popularization value.
Footnotes
Handling Editor: Benny Lo
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research was supported by the National Natural Science Foundation of China (Grant no. 61672124), the Password Theory Project of the 13th Five-Year Plan National Cryptography Development Fund (Grant no. MMJJ20170203), Liaoning Province Science and Technology Innovation Leading Talents Program Project (Grant no. XLYC1802013), Key R&D Projects of Liaoning Province (Grant no. 2019020105-JH2/103), the Youth Foundation of Xuzhou Institute of Technology (Grant no. XKY2017223), Xuzhou Science and Technology Plan Project (KC19197, KC17078, KC18011), Major Project of Natural Science Research of the Jiangsu Higher Education Institutions of China (18KJA520012), and Qinglan Project of Jiangsu Province under Grant 2018.
