Abstract
Secure and private communication has gained much focus on the international arena recently due to the ability of certain organizations to eavesdrop on private communication. This ability is further increased in the Internet of Medical Things scenario where medical images and private data are shared over insecure channels. This work is focused on a new and exciting question related to medical image steganography: is it possible to send hidden information through a cover medium, that is a medical image, without making any alteration to the cover medium in an effective manner? The proposed work has shown that it is possible to send hidden information through a medical image without making any alteration to the original medical image. This solves two problems at the same time. The first problem is that privacy and security approaches that depend on watermarking and steganography usually need some sort of modification to the medical images. The second is the knowledge that there is steganography taking place is completely hidden as no change is made to the medical image. Experiments have shown that the proposed approach under investigation demonstrates effective robustness against attacks like filtering, compression, and addition of noise.
Introduction
Since the beginning of the history of communication, there has been a need for means of secret communication. This need led to a variety of methods for secret and secure communication over the years. From the etching of messages on a messenger’s head to the usage of wax-covered wooden tablets to invisible ink, null ciphers, and Cardan Grille; 1 humans have employed several methods to achieve information security. Every method was an advancement toward better security and secrecy while trying to reduce the drawbacks of previously proposed approaches. But the advent of computers and the Internet changed everything. As a consequence, a novel class of information security techniques was invented and deployed.
Modern day information security techniques have various disciplines and applications ranging from secure data storage and copyright protection to secure communication. Nowadays, the field of information security has two subcategories: cryptography and information hiding techniques. Cryptography is a popular approach for secure communication and data security. Techniques under this category aim at the transformation of the information into an incomprehensible form based on secret keys, thus impeding the access of an adversary to the information. However, cryptography is not concerned with the fact that an adversary will have the ability to identify the existence of secret data even if no meaningful information can be extracted from the encrypted data. This leads to suspicion and has the potential of making secret communication ineffective if the adversary tries to corrupt the encrypted information.
On the contrary, information hiding solutions primarily concentrate on hiding the presence of secret data. Such techniques try to avoid the suspicion of the transfer of secret data. Information hiding solutions are subdivided into steganography and watermarking. Four primary metrics that are generally used to evaluate information hiding techniques are imperceptibility, robustness, capacity, and security. Steganography encompasses the techniques that try to hide secret information in a cover medium (text files, images, audio, video, or any kind of digital data); thus, it is a suitable candidate for secret communication. In steganography, the primary emphasis is on the imperceptibility, capacity, and security of the hidden data. Robustness is usually considered a secondary characteristic of a good steganography algorithm. However, robustness becomes a primary concern of medical images for the Internet of Medical Things (IoMT) and other applications involving medical images.2,3 Therefore, the robustness of a medical image steganography technique should be taken into account, as it is primarily used for secret communication.
With the advent of the digital information age and rapid penetration of Information Technology among the masses, problems such as counterfeit, piracy, and copyright violations have increased. Watermarking techniques were invented to have a digital signature in the data under consideration, such that a rightful owner may be able to prove his ownership if required. Watermarking provides protection against copyright violations and counterfeit issues by embedding a signature into the digital data with minimal distortion in the original cover. Contrary to steganography, in watermarking, the invisibility of the watermark is primarily not always necessary. As the signatures are usually small, high capacity is also not a primary requirement. The only essential characteristic for watermarking techniques is to be robust against removal and corruption. 4
The minimal distortion introduced by watermarking techniques into the original data is sometimes inadmissible in some highly sensitive applications like military and medical images. A new branch called zero-watermarking is employed to solve this problem in an effective manner. As the name suggests, these techniques avoid any distortion in the original data after watermarking. Instead, a secret key is generated based on relationships among the watermark and the cover image. 5
In order to prevent the use of steganography, steganalysis methods were developed to detect steganography techniques. Advancement in the development of steganalysis tools led to the detection of simple steganographic techniques, ultimately making the latter ineffective for practical usage. Steganalysis counteracted steganography—every time a steganography method was developed, sooner or later a new steganalysis method managed to detect it. Also, some steganography algorithms were vulnerable to image processing attacks. This weakness was exploited by researchers as these attacks partially or entirely damaged the cover image, which in turn damaged the hidden payload. As a result of these loopholes, simpler steganography algorithms were no longer reliable for information hiding.
Steganography researchers then shifted their focus toward more complex techniques such as transform domains and other adaptive techniques. Jpeg-Jsteg, 6 JK-PGS, 7 S-Tools, 8 IVS-Stego, 9 and so on were the tools developed. However, they had one or more of the following problems: low embedding rate, low robustness to visual attacks, high computational complexity, and increased detectability to modern steganalysis tools.10–12 This led to the need for the development of steganography algorithms that have better imperceptibility, undetectability, capacity, and robustness.
Nowadays, steganography and cryptography are used in conjunction, to achieve better data protection. In this dual-layer method, the payload is first encrypted and then hidden using steganography techniques. The adversary has to first identify the existence of information that is hidden, and remove all the hidden data—a difficult task—and then break the encryption algorithm to find the secret data.
The emphasis of the proposed solution is on steganography for medical images within the IoMT environment. In this digital age, steganography is achieved by manipulation and alteration of digital cover data in order to store the secret data or payload. These manipulations should be done so that the existence of secret information in the digital cover remains imperceptible. Least Significant Bit (LSB) modification of carrier data in the spatial domain is one of the simplest techniques to achieve digital steganography. Slightly complex forms of LSB steganography-based solutions apply this LSB modification technique in the transform domains to improve the invisibility of the algorithm.
The remainder of this article is arranged as follows: section “Related works” details the related works of image steganography followed by section “Zero-steganography for medical images” which illustrates the proposed zero-steganography approach for medical images. The results and discussion are presented in section “Results and discussion,” and the work is concluded in section “Conclusion.”
Related works
Steganography is made from the Greek word steganos which translates to covered or secret and the word graphy which translates to drawing or writing. In its simplest and earliest forms, steganography consisted of hidden writing on a paper using invisible ink. However, with advancements in technology and the introduction of computers, steganography is now better known in its high-tech variety involving secret data and cover data that are in digital form. The steganography model is shown in Figure 1.

Steganography model.
At the sender or transmission side, the embedding procedure embeds the secret data into the cover medium or image using the secret key and generates a modified image with secret data imperceptibly embedded in it. This modified form of the original cover image is known as a stego-image. This stego-image is shared through the potentially insecure channel. If someone is trying to eavesdrop on this secret communication, they would analyze the stego-image using steganalysis methods to find potential signs of steganography. In addition, noise or intentional attacks may corrupt the stego-image, and hence, the secret data embedded in it. On the receiver side, the extraction procedure uses the stego-image along with the secret key as inputs and reconstructs the secret data.
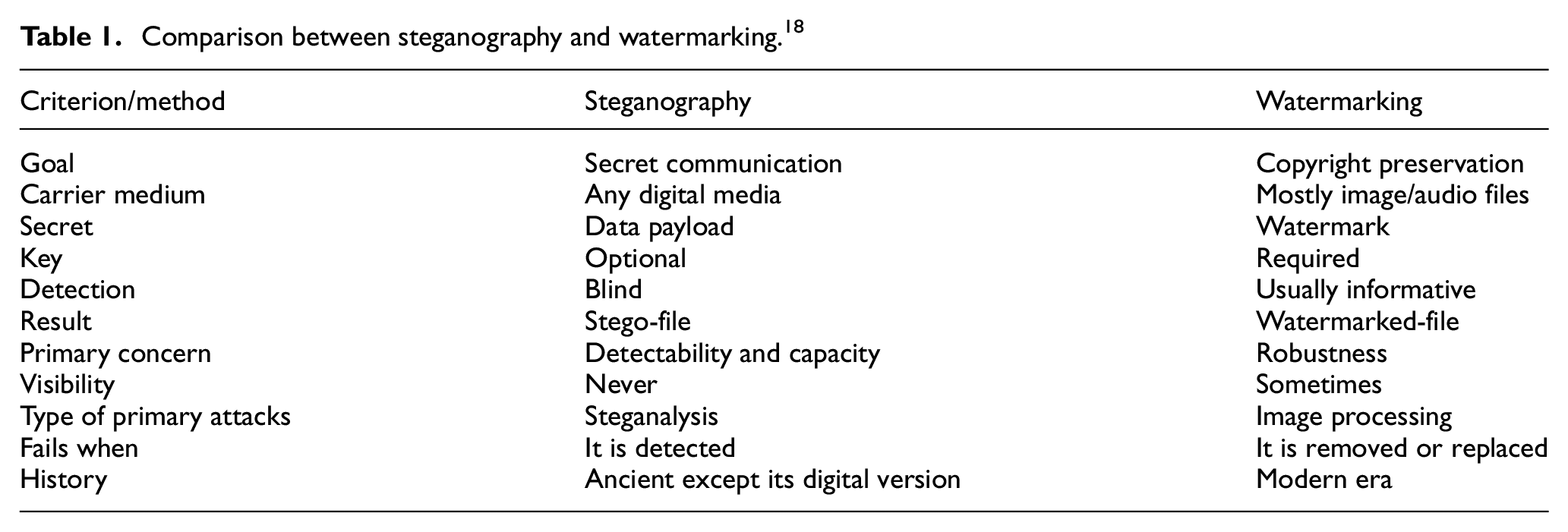
Steganography is an information hiding technique aimed at protecting secret data. Although usually associated with covert communication, steganography has found its way into several other applications as well. These applications include checksum embedding, 13 content protection, safe circulation of company’s secret data, in medical imaging to secure/conceal patient’s confidential data,14–17 and secret data storage. Steganography is closely related to another information hiding technique called watermarking. However, the difference between the two lies in the emphasis on robustness, capacity, and imperceptibility, among other things. Table 1 18 outlines the comparison between watermarking and steganography.
Comparison between steganography and watermarking. 18
A thorough history of the field of steganography is presented in the literature.19–21 Here, we would concentrate on more modern techniques of steganography. Digital steganography is a vast field encompassing several sub-fields. These sub-divisions are based on the category of cover data used in the steganographic process. This digital cover data could be in any form. The most common types of digital cover data used in steganography are as follows: images, video, audio, and three-dimensional (3D) graphic objects. However, out of these, digital images are frequently employed as the cover type and this sub-field of steganography is called digital image steganography. 18 Details of steganographic tools using other media can be found in Hayati et al. 22
Spatial domain steganography
Digital image steganography is the most widespread research area in the field of steganography and countless steganography algorithms have been presented by researchers in this field. These algorithms utilize spatial domain as well as transform domains for embedding secret data into the cover. An early method of digital image steganography was presented by Kurah and McHugh. 18 This method proposed embedding the payload or the secret data in the four LSBs of the image. Despite being a simple technique, LSB substitution method has had a significant impact on the field of steganography, and several algorithms that followed utilized this method in one form or another. However, the initial LSB substitution method had imperceptibility issues and was not robust against image processing attacks.
Another simplistic technique used for the purpose of steganography is to employ the End of File (EOF) tag in digital images. 18 The secret payload is added after the EOF tag so that if the image is viewed in an image viewer the user sees no change at all. However, if the image is opened in a notepad, the payload can be easily detected and read. Being a simplistic method, it can also be easily detected by the unusual increase in file size, in case the adversary has the original cover image. So, the payload is not secure at all.
Other techniques in spatial domain image steganography include color palette–based steganography using BMP and GIF image formats. These methods have weak robustness, and their effectiveness can be significantly reduced by image processing attacks.21,23–26 Histogram-based data hiding techniques such as the ones in Li et al. 27 and Tsai et al. 28 use the difference between adjacent pixels to implement steganography but these can be easily detected using the steganalysis method described in Cancelli et al. 29
Discrete cosine transform–based steganography
One of the most frequently used transform domains in image steganography is the discrete cosine transform (DCT) domain. As JPEG compression uses DCT as well, therefore naturally, most of the steganography techniques using DCT domain utilize JPEG images. A steganographic method that changes the quantization table (QT) used in JPEG lossy compression is presented in Li and Wang. 30 It is important to note that changing only one coefficient in a DCT block changes the pixel values of the whole block. 31 However, visible changes are not apparent in the cover image if the DCT coefficients are handled with care.
JSteg was one of the first algorithms that utilized JPEG images. It is robust against visual attacks, but JSteg leaves a statistical signature
21
that makes it vulnerable to steganalysis using
Discrete wavelet transform and discrete Fourier transform–based steganography
Several steganography algorithms have been proposed that use the discrete wavelet transform (DWT)35–38 which show that modifying data using wavelet transform provides good quality with high imperceptibility. The discrete Fourier transform (DFT), on the other hand, is not used frequently in steganography due to the round-off error introduced by the inverse discrete Fourier transform (IDFT). This round-off error corrupts the payload embedded in the cover image, even in the absence of any attacks.
Adaptive steganography
In addition to these steganography techniques, several adaptive steganography solutions have also been suggested by researchers. Adaptive steganography solutions are also identified as statistics-aware steganography embedding, masking, or model-based techniques.19,21, 39 These steganography techniques use statistical global features in order to determine the LSB/DCT coefficients in which changes are made.40,41 Model-based method (MB-1) 39 produces the stego-image built on a certain distribution model using the generalized Cauchy distribution and the resultant stego-image has minimal distortion. However, because of the absence of a perfect model, MB-1 is vulnerable to first-order statistics. 42 Chang at al. 43 propose a variant of LSB substitution method using adaptive techniques with high payload capacity.
Genetic algorithm–based steganography and 3D steganography
Genetic algorithm (GA)–based techniques for steganography have also been proposed by several works.44–46 However, the main problem with such algorithms is the time-complexity requirement. Recent works have also discussed 3D steganography.47,48 Such techniques hide the secret information in the payload in 3D models. Although they claim higher capacity, the time complexity and the lack of portability of 3D object compared to digital images can be an issue.
Zero-steganography for medical images
Spatial domain algorithms for image steganography are often prone to visual attacks and steganalysis methods. However, steganography techniques operating in DCT and DWT as well as adaptive steganography are less prone to attacks especially if the payload is small. This is because of the fact that the changes are made in the transform domain coefficients and the visual distortion, as a result, is minimum. However, such algorithms have low payload capacity compared to spatial domain algorithms. The main problem with GA-based steganography is the time complexity required to carry out such a technique. 3D steganography, on the other hand, is limited by the usage of 3D objects. Almost all of the conventional steganography algorithms can be detected by one steganalysis method or the other. Some algorithms are undetectable by steganalysis as long as the payload capacity is extremely small.
A relatively new and recent sub-field of steganography named zero-steganography has emerged. This sub-field proposes to carry out a steganographic process without making any changes to the cover image. Hence, the cover image and stego-image are the same and such algorithms are completely imperceptible. 49 Zero-steganography seems like a promising concept. This work is aimed at the exploration of the concept used by zero-steganography and to produce new algorithms that are not only imperceptible but also provide effective robustness. 50
The following provides the details of the procedures and techniques used in this work. First, the requirements of feature extraction methodologies are presented. Second, a brief discussion on chaos is provided and the reasons for its usage are presented. Then, the details of the algorithm and its results for robustness are given using a medical image data set.
Feature extraction
The feature extraction procedure basically extracts the features of the image that is used to embed the payload into the image. This payload can be the identity of the patient or the diagnosis for medical images. Several characteristic methods have been used by researchers in the field of image steganography. These methods directly impact the robustness and the capacity of the steganography algorithms. The goal of the proposed work is to present an effective zero-steganography algorithm that is robust to low-pass filtering, Additive White Gaussian Noise (AWGN), and JPEG compression.
The use of low-frequency components for the purpose of embedding the payload into the cover data is used for feature extraction because all of these attacks distort the high-frequency components of the image much more than the low-frequency components. This makes the low-frequency characteristics of the image a prime candidate for the association of the secret payload.
Chaos
A chaotic process is a deterministic process. It is found in dynamic, non-linear systems where it is primarily dependent on the system settings and initial parameters. Chaos is non-periodic in nature, it is a bounded process, and it is non-converging. 18
A chaotic map is basically a discrete-time dynamical system, expressed as 35

The resulting chaotic sequences

where the system setting parameter,
The chaotic logistic map used for the proposed zero-steganography approach has some useful properties. It has a simple form and sequences generated with different parameters are statistically uncorrelated. 12 The chance of getting to the correct parameters using simple brute force has a very low probability due to the reason that the bound contains infinite floating point numbers.
The goal here is to propose a zero-steganography technique that is more robust than the previously proposed techniques in zero-steganography. Generally, the approach is to evaluate each of the three key attributes and to achieve improvement in one or more of the three attributes without degrading the other. However, that is an ideal condition and in steganography, as in other fields, it is often a trade-off between the desired attributes.
The association procedure that actually creates a link or a relationship between the secret data to be hidden into the medical image and the medical image is probably the most important component of the zero-steganography system as it is responsible for the generation and size of the key and security of the payload. Figure 2 shows the basic block diagram of the steganographic process involved in the proposed algorithm. On the sender side, a feature extraction procedure is operated on the cover image. Then, the payload is converted to binary and indices for “1s” and “0s” are separated.
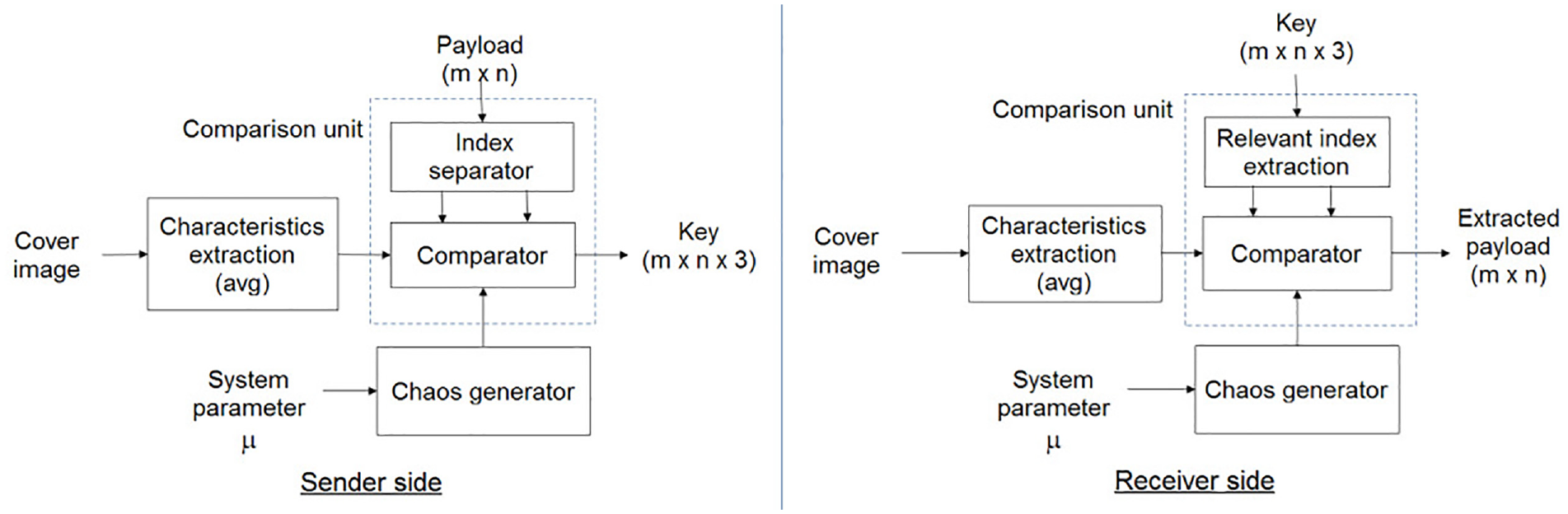
Proposed steganography process.
The comparator calculates the results for inequality expressions based on values of extracted features of the cover image
Conditions to be satisfied for embedding and extraction of a payload bit.
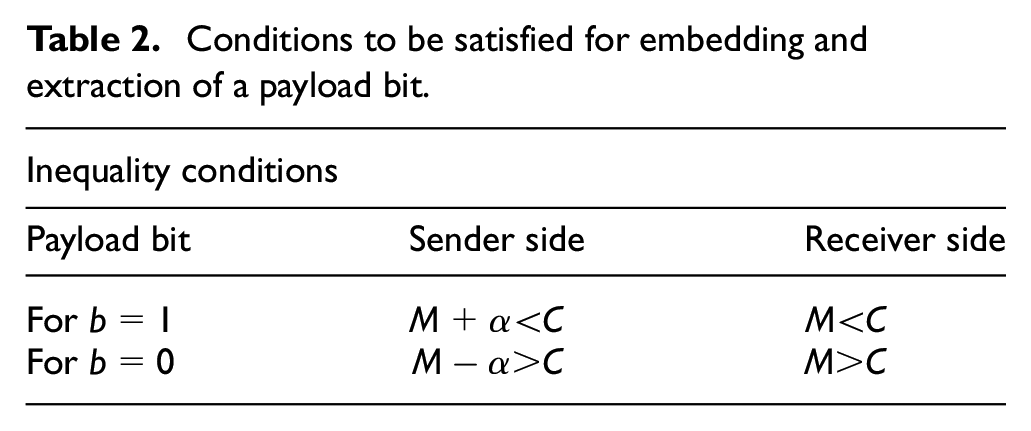
There is a tolerance margin,
Results and discussion
For the tests, a payload of
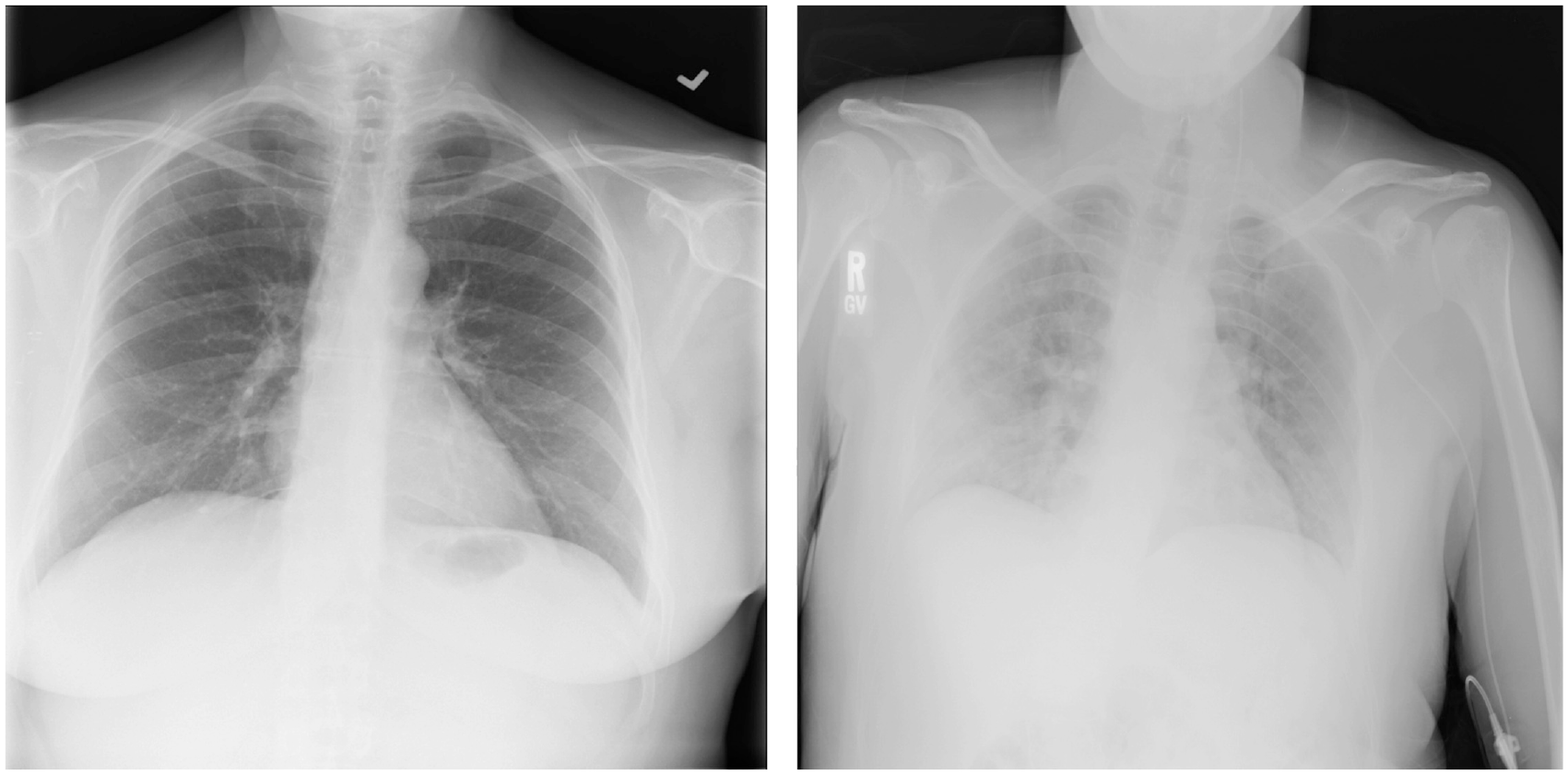
Samples from the National Institutes of Health (NIH)—Clinical Center chest X-ray data set.
The robustness of the algorithm was determined for three common attacks: (1) low-pass filtering, (2) AWGN addition, and (3) JPEG compression. The extraction method currently tested is averaging using an
Low-pass filtering
For the low-pass filtering attack, a filter size of
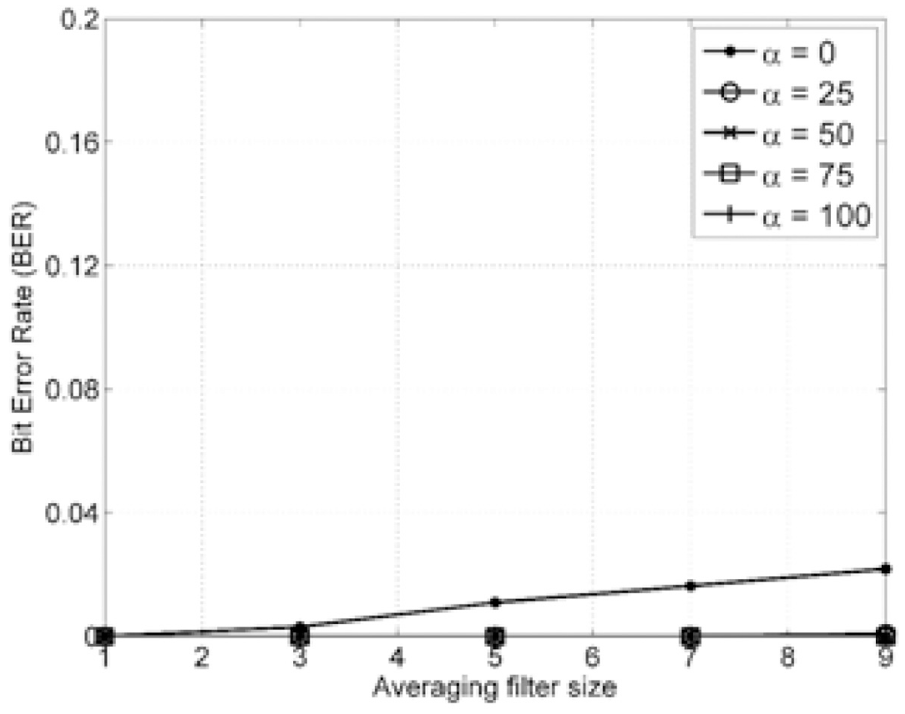
Performance against low-pass filtering attack.
AWGN attack
In case of AWGN attack, the proposed approach was tested for variance

Performance against AWGN attack.
JPEG compression
Robustness of the proposed algorithm was also evaluated against JPEG compression for quality

Performance against JPEG attack.
The results against JPEG compression, additive noise, and filtering attacks show that the proposed solution has several advantages compared to approaches that are based on traditional steganography, such as DCT-based steganography, spatial domain steganography, DWT and DFT–based steganography, and adaptive steganography. The main advantage is the robustness of the proposed solution against the applied attacks. The proposed solution is not only robust against the applied attacks but it is also completely imperceptible when compared with traditional steganography solutions. This gives the proposed approach a significant advantage when considering highly sensitive images such as medical images.
Conclusion
An effective zero-steganography algorithm for the protection of medical images in the rapidly evolving IoMT environment is proposed. The effectiveness of the proposed zero-steganography approach is validated through robustness against different attacks such as compression, additive noise, and filtering. The algorithm is capable of extracting the required information from severely degraded images. The algorithm ensures that the images are not altered through the information hiding process and are not vulnerable to intentional and unintentional attacks. This allows confidence to the disease evaluation experts that the images are protected when shared through the IoMT environment and no change has been made to the original image for the purpose of security. The proposed approach can be further enhanced and used for 3D medical images.
Footnotes
Handling Editor: Benny Lo
Declaration of conflicting interests
The author declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This project was funded by the National Plan for Science, Technology and Innovation (MAARIFAH), King Abdulaziz City for Science and Technology, Kingdom of Saudi Arabia, Award Number (13-INF2114-02).
