Abstract
The current quality of system routing available in wireless sensor network mainly provides assurance for traffic flow, with little consideration on full use of network resource, like bandwidth. Aiming at solving these problems, this article proposes a quality of system routing method based on neighborhood interference detection and mitigation. First, the algorithm uses a sink node as root node to establish a minimum spanning tree for the network to obtain the depth of each node. Then, each node dynamically updates its interference degree by contiguous iterations during neighboring nodes communication. Finally, the interference degree, packet level, residual energy, and node depth are combined to establish a multipath route to enhance the network bandwidth and thus improve the quality of system. Experimental results show that the algorithm can not only effectively balance the network load but also reduce the network packet delay and improve the network throughput. It also has a good network lifetime; thus, it can effectively improve the quality of system of wireless sensor network.
Keywords
Introduction
Wireless sensor networks (WSNs) have a wide range of applications, which have quite different requirements. Even if data are the same, they may require different ways of processing and transmission in different applications,1,2 and remains a challenge due to heterogeneous traffic flows, dynamic network conditions, and resource-constrained nature of sensor nodes.3,4 For example, a fire monitoring WSN system, where temperature data are very important, requires an in-time response. Multimedia systems need to capture images, voice, video, and other information simultaneously, 5 whose transmission require a network with a higher quality of system (QoS), including not only the traditional QoS routing performance but also energy consumption, load balancing, network lifetime, and other QoS metrics, and so on.6–8
Multichannel methodology may be used for accomplishment of QoS requirements by making possible parallel communication, enhancing throughput/delivery ratio, reducing transmission delay and countering jamming attacks. 9 However, it involves too much software-definition in multi-radio, multichannel, and multi-hop networks, 10 leading to high-complexity in system. Channel model in realistic applications are still resources-limited and dependent on the wired infrastructure backbone, 11 and high-efficient bandwidth usage remains a challenge to this issue.
In this article, a method called neighborhood interference detection and mitigation (NIDM) is proposed to detect and mitigate inter- and intra-stream interference among neighborhood nodes, so that QoS for multiple media streams communication can be improved. Our proposed method also considers the balancing performance of networks, such as energy consumption, packet delay, network lifetime and so on, conducting a tradeoff consideration among multiple network parameters, for an optimal routing.
There are three steps in our algorithm. At first, we establish a minimum spanning tree for all nodes in the network. Second, each node updates its inter- and intra-stream interference level by contiguous iterations between neighbor nodes during packets sending and receiving process. Finally, we combine the node depth, interference level, and residual energy of neighboring nodes to select the appropriate path to sink node. Our proposed NIDM algorithm combines not only the delay caused by intra- and inter-stream interference, but also multiple quality of service (QoS) requirements, like different priority of traffic, the short routing, and so on. The simulation results show the effectiveness in QoS by our proposed method, such as transmission quality, reliability, and throughput, and network lifetime, compared with other up-to-date approaches.
The rest of this article is organized as follows: section “Related works” describes related works, section “Proposed schemes” presents the detail in NIDM algorithm, section “Simulation results and discussion” shows the simulation experiment results, and section “Conclusion” summarizes the study.
Related works
Requirements of QoS varied significantly in different network layers. For example, in network layer, the requirements were mainly related to: path latency, routing maintenance, congestion control, routing robustness, and energy efficiency.12,13 On the contrary, in data link layer, the requirements had been as: communication coverage, throughput, transmission reliability, and energy efficiency.14,15 Parts of them mentioned earlier were probably contradictory, leading to a soft QoS routing planning, to meet the specific service requirements at a probability level.16,17
Recent studies on the soft QoS were mainly based on multipath planning strategies.15,18–22
MN Bouatit et al. 19 presented a geographic multipath routing protocol (GMRP), based on control message between nodes, to achieve an optimal routing for multipath transmission, shortest path node-disjoint and bypass holes. However, too much data resources were involved in communication between nodes.
Xu et al. 20 proposed an energy-efficient clustering routing protocol based on a high-QoS node deployment with an inter-cluster routing mechanism (EECRP-HQSND-ICRM) for QoS planning. However, the method selected an optimal node based on its coverage rate, and quite possibly resulted in traffic unbalance among links.
J Zhang et al. 15 proposed a method called integrity and delay differentiated routing (IDDR), which constructed a virtual hybrid potential field to find the under-utilized paths in meeting the requirements on high data integrity and low delay. However, it could not satisfy both of two requirements mentioned above simultaneously.
Multiple paths could meet the QoS requirements, but they suffered from significant energy cost, and cross-interference on wireless channels, which in some degree impacted converse effects on QoS.
Alternatively, a single path planning, combined with multiple constraints seemed to be another way for QoS routing.16,23–29
H Mostafaei 23 modeled the problem as a multi-constrained optimal path problem and proposed a distributed learning automaton (DLA)-based algorithm to find the smallest number of nodes for the desired QoS requirements. Cheng et al. 24 defined an algorithm named as geographic opportunistic routing (GOR) for multi-constrained QoS provisioning in WSNs, which was formulated as a multi-objective multi-constraint optimization problem. Based on QoS-aware GOR (EQGOR) protocol for QoS provisioning in WSNs, the forwarding candidate set were selected in an efficient manner.
A virtual node schedule for supporting QoS in wireless sensor networks (VNSQW) was proposed by Wesam et al., 16 which provided a service for critical nodes that needed timely transmission of their packets, through the provision of additional time slots. Nevertheless, it brought with a scarification in term of additional power consumption.
GH Liu et al. 25 formulated a non-convex optimization problem to maximize the system throughput in multi-input multi-output (MIMO)-based wireless powered underground sensor network (WPUSN) with QoS assurance. However, detailed information on ever-changing channels would cause serious waste of resources by this method.
R Hamidouche et al. 26 presented a low energy-efficient hierarchical clustering and routing protocol based on genetic algorithm (LECR-GA), using energy-efficiently clustering and tradeoff transmission as proper chromosome variables and used them in the following GA operations.
Shu et al. 27 adopted a differentiated queuing services (DQS) scheme for maintaining data queues. Combined with flow control, routing, scheduling, and power control scheme, a Lyapunov optimization framework was proposed to increase network lifetime and scheduling fairness, in specified WSNs.
Manju et al. 29 presented a QoS-aware energy-efficient technique called improved-clustering-heuristic (ICH), which calculated a threshold (Th) on residual energy and gave priority to the node with residual energy more than the proposed Th. Based on this, cluster heads for the next round were selected.
Comparatively, the single path planning with multi-QoS constraints, with or without optimization, was an NP-complete problem on computational complexity, lacking of robust and self-adaptive solutions, compared with multipath schemes.
Accordingly, we had analyzed multipath QoS routing with both of the inter- and intra-stream interferences and evaluated the impact they might lead to. Then, we integrated three factors together to find an optimal routing and improved QoS provision of network. The advantages of our proposed algorithm were: (1) load balance, (2) reliability and fault tolerance, and (3) bandwidth availability.
Proposed schemes
Without loss of generality, we assume that:
WSN nodes are uniformly and randomly distributed on a two-dimensional plane with a radius R of the circular area and the sink node located at the center of this area.
All nodes, including the sink, are stationary.
Each node has the same wireless communication radius.
Each node can be used as a source node to generate packets and also as a relay to forward packets. The sink node does not send any packets.
Each sensor node has a limited cache, whereas the sink node has an unlimited one.
Service level of the packet is specified.
Topology establishment of the network
First, we initialize all nodes’ depth value to positive infinity.
Second, a route request packet (RREQ) is broadcast by the sink node, to invite other nodes across the network to join it. Suppose one node’s depth variable is L, and the number of hops of RREQ it receives is N, we could update its depth value L by comparison with N, as shown in Figure 1.

Depth updating flowchart.
When the RREQ has spread throughout the network, each node would have its own minimal depth value. Finally, topology based on minimum spanning tree for the network is established.
Neighboring interference detection
In this work, we define an interference-estimating metric for each node, to describe the impact of the shared link in neighboring nodes on network performance. There are mainly two kinds of interference: intra-stream interference and inter-stream interference, with two factors involved into consideration: (1) transmission rate and time of nodes in the stream, (2) transmission capability of nodes and the network, like caching, bandwidth, and so on. The following is the process of interference detection and estimation, where the initial interference value of each node is set to 1.
1. Neighboring nodes interference
Suppose there is a data stream X flowing in the network, each node of X sends out interference on its neighboring nodes, which is calculated as formula (1). Neighboring nodes then update their neighbor tables about the node of X with their new interference value
where Ineig represents the interference sent out by each node on its neighboring nodes. ρ is a control parameter, and 0 < ρ < 1. RX is the transmission rate of stream X, and NA is caching packets capability of node A, which is on the route of stream X.
2. Intra-stream interference
Suppose node B is also on the route of stream X, following node A in the next several hops. We use formula (2) to measure the intra-stream interference on node B, which is brought by the transmission of stream X
where α is another control parameter, taking the value 0.5 < α < 1, while k is the hop number from node A to B along the transferring path, and W is the bandwidth of channel.
3. Inter-stream interference
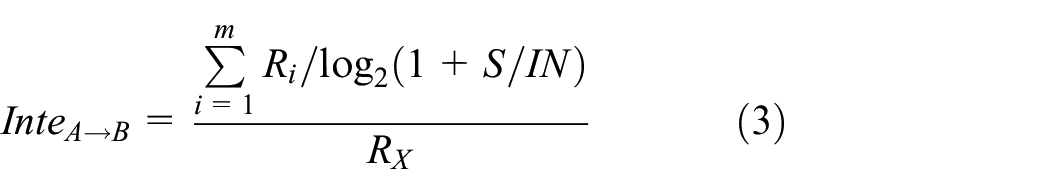
Suppose there are m links passing by node B at a given time, meaning that there is inter-stream interference imposed on node B while it is transferring stream X. According to Shannon Theorem, 30 network bandwidth is in relation to transmission rate RX and signal to interference and noise ratio S/IN. Then, we can estimate the interference on node B brought by other streams using formula (3)
where ratio InteA→B focuses on the bandwidth occupation ratio, which refers to the ratio of the bandwidth used by the total m links passing by node B, to the bandwidth used on node B for transferring stream X, If InteA→B = 0, the entire bandwidth will be available for link XA→B. When 0 < InteA→B < 1, it implies inter-stream interference existing on node B. Otherwise, InteA→B > 1 indicates that the channel is completely dominated by interference from neighboring links passing by node B, and there is no sufficient bandwidth for transferring stream X.
4. Combination of three interferences
Based on above analysis, a combining metric to reflect the influence of three kinds of interference on node B can be calculated, as shown in formula (4)
where y is the total number of neighboring nodes of node B, and
Procedure of NIDM
The process of NIDM algorithm is described as the following.
Setting up a topology for the network. The sink node sends an RREQ packet to establish minimum spanning tree, and minimal depth value in the tree is the minimal hop number for each node to the sink node. Descriptions in detail are as displayed in section “Topology establishment of the network.”
Calculating intra- and inter-stream interference of each node on its neighboring nodes, according to formulas (1) to (3). Then, combining three interference metrics together by formula (4). Details are shown in section “Neighboring interference detection.”
Selecting the appropriate next-hop from the candidate nodes list by a tradeoff consideration among interference degree, packet level, and residual energy of the nodes, as shown in formula (5)
where Poweri represents the residual energy of node i, Xprior is the priority level of the stream X, and depthi is the depth value of node i in the spanning tree. γ is another control parameter, and 0 < γ < 1.
To avoid a ring routing, the depth value of the selected next-hop node should not be greater than the current depth.
An example of NIDM process is described in Figure 2, including four stages, from Figure 2(a)–(d). Node D selects its routing according to metrNIDM obtained in formula (5).

Procedure of NIDM algorithm.
Figure 2(a) shows a multi-routing scheme for node D, which has two nodes C and E as its next-hop candidates. At the same time, three nodes A, F, and G are sending data to the sink node, whose stream are transferring along the path A→B→Sink, H→C→B→Sink, and G→E→F→Sink, respectively, as shown in Figure 2(b). According to formula (5), the metrNIDM value of node E is less than that of C, and then node D selects node E as its next-hop to establish a transferring path D→E→F→Sink, as shown in Figure 2(c). After three streams have finished their transmission, node D would re-select node C as its next-hop as shown in Figure 2(d).
In addition, consideration on dealing with burst traffic is also taken into account in this article. This often takes place in emergent affairs and requires an urgent data transmission. In this case, sudden interference to links and unbalanced load consumption might cause energy-hole occurrence in the network. Nodes are first grouped with their neighboring relations, and then we suppose that there is a burst traffic appearing on node 1, as shown in Figure 3.

Nodes clustering and intra-cluster collaboration.
The interference caused by burst traffic on node 1 is estimated by formula (1) to (4). If the accumulated interference on a node exceeds the pre-set threshold, like on node 2, other nodes within the cluster would come to forward the traffic to balance energy consumption on nodes.
Performance analysis
With our proposed algorithm, bandwidth utilization of the network is improved. Assuming a network with total throughput TN, the handling capacity of N nodes is c = {c1, c2,…, cN}, where
where Icom(j) is the combining interference value of node j, indicating that how node j gets involved in data transmission, including those originated from itself.
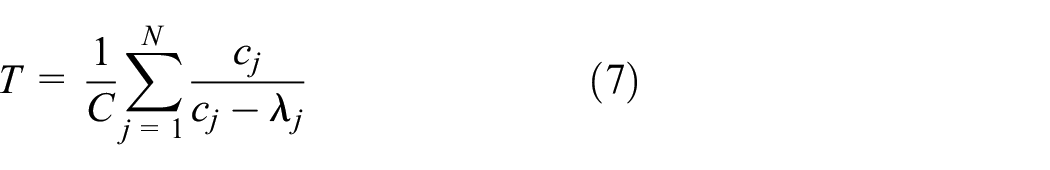
The average delaying time T of the network is as shown in formula (7)
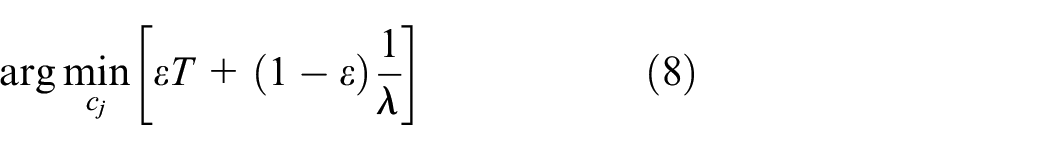
where C is the total caching capacity of network. Defining the problem as a multi-objective optimization, we can minimize T while maximizing λ, as described in formula (8)
where ε is a weighted factor for balancing the significance of T and λ.
Combining formula (7), Lagrangian function of the above problem is given by formula (9)
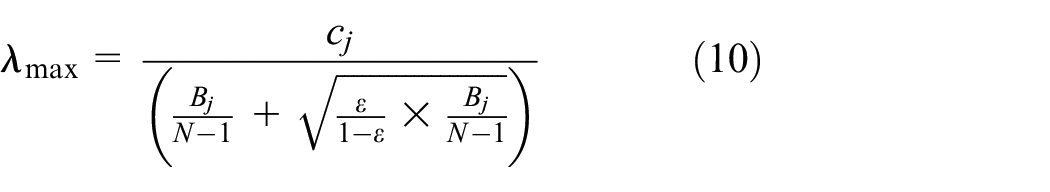
One solution to formula (9) is in formula (10)
where λ
where B* = arg min [B1, B2,…, BN] represents the minimal betweenness vector of N nodes. From formula (11), it can be seen that the maximal transmission rate λ
Accordingly, we can assign appropriately all tasks over the network to minimize B*aiming at enhancing the network’s bandwidth utilization and consequently improve its QoS.
Simulation results and discussion
In this work, we use the OPNET simulation platform to compare the network performance of the proposed NIDM algorithm with that of LECR-GA 26 and DQS 27 in terms of end-to-end (ETE) delay, throughput, packet loss rate, and network lifetime.
The topology of network is illustrated in Figure 4, and the number of nodes is 50, with No. 49 as the sink node.

Topology diagram of experiments.
There are seven data streams across the network, initiating from nodes with three-level different transmission rates 500 Kbps, 2 Mbps, and 7 Mbps, respectively. Node 41, 42, 45, and 46 are with 500 Kbps, and Nodes 47 and 48 are with 2 Mbps. The last one Node 37 sends packets with a rate 7 Mbps.
The parameters of the simulation environment are shown in Table 1.
Experimental parameters.

The results and analysis are as the following:
1. ETE delay
Figure 5 shows a comparison chart of the WSN transmission delay among three algorithms NIDM, LECR-GA, and DQS algorithms. In LECR-GA, we apply genetic algorithm for nodes clustering, where genes are used to represent the residual energy and the distance between nodes. In DQS, a tradeoff between time delay and transferring consumption is setup based on Lyapunov strategy.

Comparison results on ETE delay.
After a first sudden fluctuation, our proposed method becomes gradually less latency than other two algorithms, due to lower probability in packets retransmission caused by multiple interferences.
2. Network throughput
Figure 6 presents the throughput performance of network based on three algorithms, with that of our NIDM performs better than that of the other twos, showing that the best usage of bandwidth is done by our algorithm, through interference mitigation between neighboring streams.

Comparison results on network throughout.
The second better in Figure 6 is LECR-GA, taking number of neighbors into account during cluster heads selection, and balancing link loads. The last one is DQS, where quality of links is an insignificant factor during consideration.
3. Packets loss rate
Figure 7 shows results of packets loss rate by three algorithms mentioned above. In LECR-GA, residual energy and the distance between nodes have been optimized for nodes clustering, and in DQS, a differentiated queueing services is conducted. Our proposed algorithm can perform collision avoidance and achieve a low packet loss rate, while the effects of inter-flow interference are usually neglected in other two methods, leading to inaccurate bandwidth estimation.
4. Network lifetime

Comparison results on packets loss rate.
We define network lifetime as starting from the network’s operation to the death of the first node. With our metric
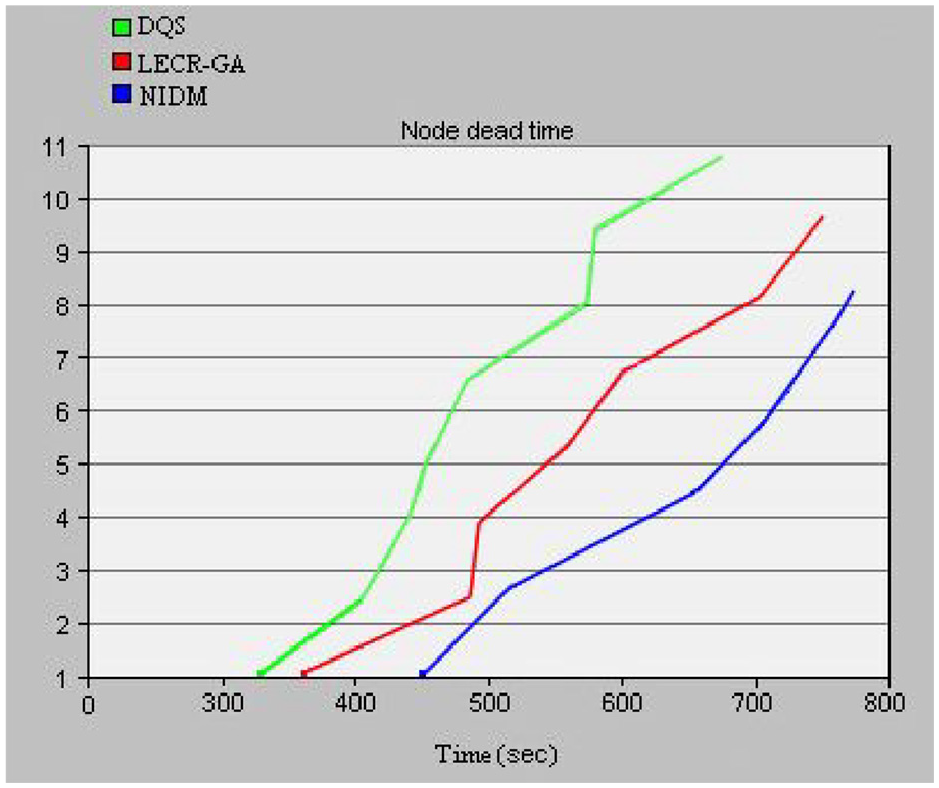
Comparison results on network lifetime.
Conclusion
Interference among neighboring links leads to inefficient utilization of network’s bandwidth. Through definition of interference metric of each node, we propose an algorithm to dynamically update link’s state for routing decision. It is in essence a real-time multiprocessing strategy, depending on the pre-determined minimum spanning tree, with links self-adaptive adjustment during transmission period.
Intra- and inter-stream interference detection can estimate the traffic condition of network. Combining it with nodes residual energy and service priority, our proposed algorithm can improve bandwidth deployment of the network. The experimental results show that this method can effectively improve the WSN throughput and lifetime, minimize end-to-end delays, and reduce packets loss rates. that is, the QoS of network.
Footnotes
Handling Editor: Peio Lopez Iturri
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was funded by Scientific Project of Guangdong Provincial Transport Department (No. Sci & Tec-2016-02-30).