Abstract
Existing secure image acquisition works based on compressive sensing, viewing compressive sensing–based imaging system as a symmetric cryptosystem, can only achieve asymptotic spherical security denoting that the ciphertext only leaks information about the energy of plaintext. Thereby, compressive sensing–based secure image acquisition systems usually work in some scenarios of friendly attack, such as brute-force attack for the entire key space and ciphertext-only attack for the complete plaintext. In this article, a novel permutation–confusion strategy using chaos and compressive sensing is put forward to protect the privacy-crucial images from more threatening malicious attacks, including known-plaintext attack and chosen-plaintext attack. Security guarantee is provided by one-time random projection of compressive sensing, sample-level permutation, and bit-level substitution. It is noteworthy that double confidentiality is embedded in compressive sensing–based image acquisition process using the key-related measurement matrix and sparsifying basis and the randomicity is improved. Simulation experiments and security analyses suggest that the proposed framework can achieve a high-level security and the performance of image reconstruction can be distinctly improved.
Introduction
With the rapid development of multimedia technology, digital image has become an increasingly prevalent information carrier over the Internet. With the awakening of awareness that data are the treasure, personal privacy information contained in digital image is attracting more and more attention from malicious attackers. Image security is of great importance in both military and commercial fields. Fortunately, a large number of image-oriented privacy-preserving techniques are constantly emerging, for instance, image encryption, 1 image digital signature, 2 secret image sharing, and image information hiding. 3 Image encryption is the most straightforward way.
In essence, all kinds of image encryption techniques aim at achieving both diffusion and confusion effects, which were identified as the two essential properties of a secure cipher by Shannon. 4 Diffusion means the statistics redundancy of the plaintext is dissipated into the statistics of ciphertext, while confusion aims to break the connection between the ciphertext and the key. For an encryption algorithm with good diffusion, the ciphertext will change absolutely in a pseudo-random manner when even one bit in the plain domain is changed. Confusion makes it difficult for attackers to reveal the key, though they hold numerous plaintext–ciphertext pairs generated by the same key. One of the simplest methods to achieve both diffusion and confusion is a permutation–substitution network. 5 In general, permutation is to scramble the position of pixel or bit and substitution is to change pixel values in the field of image encryption.6–8
Expect for the above image encryption techniques, some pioneering works9,10 tried to embed confidentiality feature in the process of compressed sampling. Compressed sampling (also called compressive sensing, CS),11–13 a merging sampling theory, is able to sample and compress simultaneously without the limit of Shannon–Nyquist sampling theorem and exactly reconstructs the original signal from very few measurements (samples) as long as the measurement matrix obeys some energy-preserving conditions.14–16 When CS is regarded as a symmetric cipher, the original signal, the reconstructed signal, and the measurement matrix are considered as the plaintext, the ciphertext, and the key, respectively. Accordingly, sampling and reconstruction process denote encryption and decryption process, respectively. From this point of view, CS has the potential of integrating sampling, compression, and encryption in the only one physical layer at a minimal cost. CS-based cipher works under a simple fact that it is computationally infeasible to recover the plaintext from the intercepted ciphertext without the complete knowledge of the corresponding measurement matrix. To avoid transmitting a large-scale measurement matrix, chaotic systems were suggested to produce the measurement matrix and the initial parameters (seed values) controlling a chaotic sequence were viewed as the shared key between the encoder and the decoder.17,18 It should be noted that CS-based cryptosystem is generally required to work under one-time pad, that is, the same measurement matrix is used only once. For reusing the key of CS-based cipher, Zhang et al. 19 proposed a CS-based product cipher by embedding randomness in both measurement matrix and sparsifying basis. In view of the linearity of CS projection, CS-based cipher can achieve computational secrecy rather than information-theoretical secrecy. According to a latest research, 20 attackers could not reveal any valuable information but the energy about the original signal from the noise-like measurements when the measurement matrix consists of the independent and identically distributed (i.i.d.) Gaussian entries. In light of this observation, it was suggested that normalizing all measurements and regarding the normalized measurements as the ciphertext would get a perfect version of CS-based cipher. The fact that CS-based cipher can achieve the asymptotic spherical security was defined by Cambareri et al. 21
Recently, applying CS-based cipher to image encryption has attracted more and more attentions. Under the CS-based cipher model, CS-based imaging system can not only reduce the redundancy of image data but also provide some privacy-preserving properties to some extents. Chai et al. 22 combined CS and steganography to generate a visually secure image. Zhang et al. 23 proposed a scalable image encryption framework at different compression ratios, in which block CS works together with a Sobel edge detector and cascade chaotic maps. George and Pattathil 24 produced the measurement matrix by utilizing multiple chaotic maps. Moreover, they proposed a method of constructing a random measurement matrix based on the linear feedback shift register (LFSR). 25 Zhou et al. 26 created a key-dependent measurement matrix using the circulant matrices and controlling the original row vectors of the circulant matrices with logistic map. Besides, they considered the partial Hadamard matrix as the measurement matrix controlled by chaotic map and the acquired measurements are further scrambled. 27 Liu et al. 28 combined CS and chaos to compress, fuse, and encrypt images simultaneously, in which the random measurement matrix is constructed from a logistic sequence and the acquired measurements are further fused by an adaptive-weighted fusion rule. For the purpose of alleviating the burden of information and communication systems, Zhou et al. 27 proposed a simultaneous image encryption–compression scheme based on two-dimensional (2D) CS and hyperchaos.
In this article, we focus on how to design an image-oriented CS-based product cipher with the help of chaos. Considering that CS-based cipher is a lightweight cipher, we give a supplementary way to improve the security. Finally, a novel image sampling–compression–encryption framework is proposed for secure image acquisition, in which a high-level confidentiality is achieved through two approaches. One is that both the measurement matrix and sparsifying basis controlled by a same chaotic system are regarded as the shared secrets between the encoder and the decoder. Specifically, the elements of measurement matrix come from a chaotic sequence controlled by tent map, and the column vectors of a selected sparsifying basis are randomly permuted by leveraging the same tent map. Even having figured out either measurement matrix or sparsifying basis, attackers are still unable to reconstruct the original signal from CS measurements successfully. The other is that the captured data are further encrypted to breakout the linearity constraint of CS-based cipher by performing the sample-level permutation and the bit-level XOR, which are also manipulated by tent map. Obviously, diffusion and confusion effects can be easily achieved due to good pseudo randomness. In essence, the proposed imaging system is a two-layer cryptosystem consisting of CS-based cipher and chaos-based encryption.
The rest of this article is organized as follows. In section “Related works,” we briefly introduce some related knowledge about edge computing and CS-based cryptosystem and then point out some existing challenges in this field. In section “The proposed framework,” a double-secrecy encryption framework based on CS and chaos is proposed. Simulation experiments and analysis are given in section “Experimental results and security analyses.” Finally, conclusion is drawn in section “Conclusion.”
Related works
In this section, we introduce some fundamental knowledge about CS theory, chaos theory, and how to embed cryptographic feature in CS.
A brief review of CS
CS is an alternative to Shannon–Nyquist sampling when a signal is sparse or compressible. We denote a one-dimensional (1D) signal to be sampled as a column vector

where the column vector
In the CS framework, sampling and compression for a 1D signal

where

where
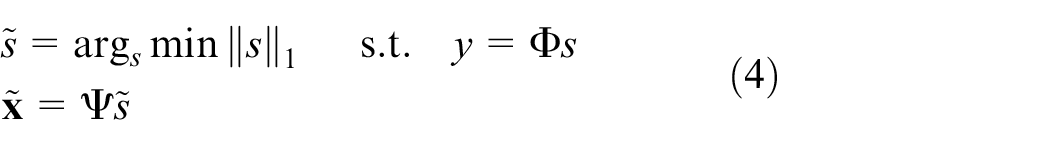
An important precondition is that measurement matrix
Definition 1
A matrix
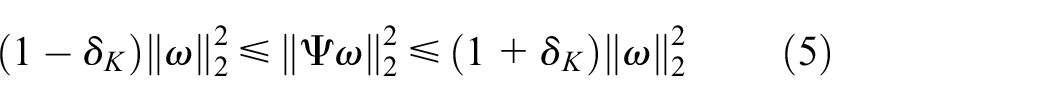
holds for any one
Chaotic encryption
In dynamical systems, chaos is extremely sensitive to initial conditions. Although the systems are deterministic, the sequences produced through iterating chaotic map show excellent pseudo randomness. Applying chaotic theory, the practice of cryptography has attracted much interest in the past 30 years, which utilizes the chaotic sequence to encrypt the plaintext. In view of its good randomness and large key space, thousands of chaotic encryption algorithms have been proposed, all of which take aim at a good diffusion–confusion effect by concealing the connection between ciphertext and plaintext as well as the used chaotic sequence. A common chaotic behavior is the tent map, which is defined as
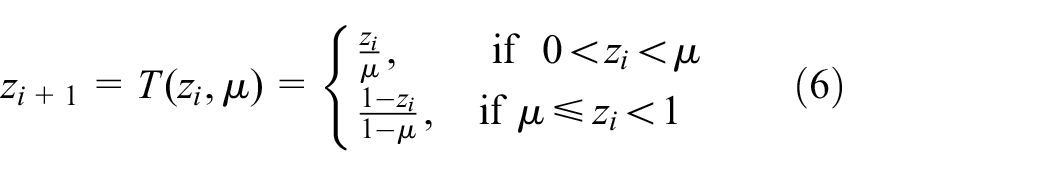
where
CS-based cipher
When viewed as a cryptosystem at the same time, CS-based information acquisition system can provide a certain level of confidentiality guarantee while compressively sampling. As shown in Figure 1, in the common framework of CS-based cipher, the original signal

CS-based cryptosystem framework.
To avoid transmitting the large-scale
To avoid updating the key of CS-based cipher frequently, Zhang et al.
19
provided a bi-level protected CS framework based on RIP-less theory,16,31 in which the measurement matrix is a key-controlled RIP matrix,
The proposed framework
In this section, a double-secrecy encryption approach based on CS and chaos and an additional chaotic encryption are introduced in detail. Moreover, a novel sampling–compression–encryption framework is proposed to realize secure compressed imaging.
Embedding double secrecy in one-timeprojection of CS
As mentioned previously, one-time random projection of CS can perform image sampling, compression, and encryption simultaneously. Almost all CS-based cryptosystems work under a common framework, in which one-time measurement matrix
Most of existing CS-based ciphers are based on the fact that the decoding process is doomed to failure when there is no information about
Definition 2
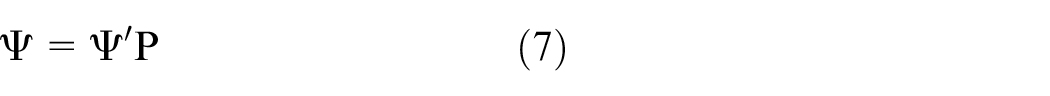
where
Obviously, random permutation matrix
Tent map has been proved to be suitable for constructing measurement matrix

where the scalar
It is not hard to come to a conclusion that transmitting the two keys,
Chaotic permutation–substitution encryption
As mentioned previously, CS-based cipher can only provide a computational guarantee of secrecy and the energy of the plaintext
Permutation is to scramble the position of CS measurements, which is done by putting them in a random order. A random index sequence
Therefore, a scrambled measurement vector

where
Substitution is further considered to change the statistical property. For a good confusion effect, substitution operation is done by performing the bitwise XOR operation between
The chaotic sequence
where the acquired
The proposed sampling–compression–encryption framework
The proposed CS-based double-secrecy cipher can provide a certain level of security guarantee, which can be implemented in the sense player of a low-cost information acquisition system. When there is a requirement for high confidentiality, some additional strong encryption methods need to be employed. Here, as shown in Figure 2, a sampling–compression–encryption framework is further proposed for secure image acquisition, whose security is guaranteed by the built-in CS-based cipher and the chaotic encryption.

The proposed framework.
Assume that the signal to be sampled is a gray image

where
When

Obviously, the whole sampling–compression–encryption process
Experimental results and security analyses
In this section, several simulations are implemented by MATLAB 2016b in Window 7 to demonstrate the high security of the proposed framework. A standard
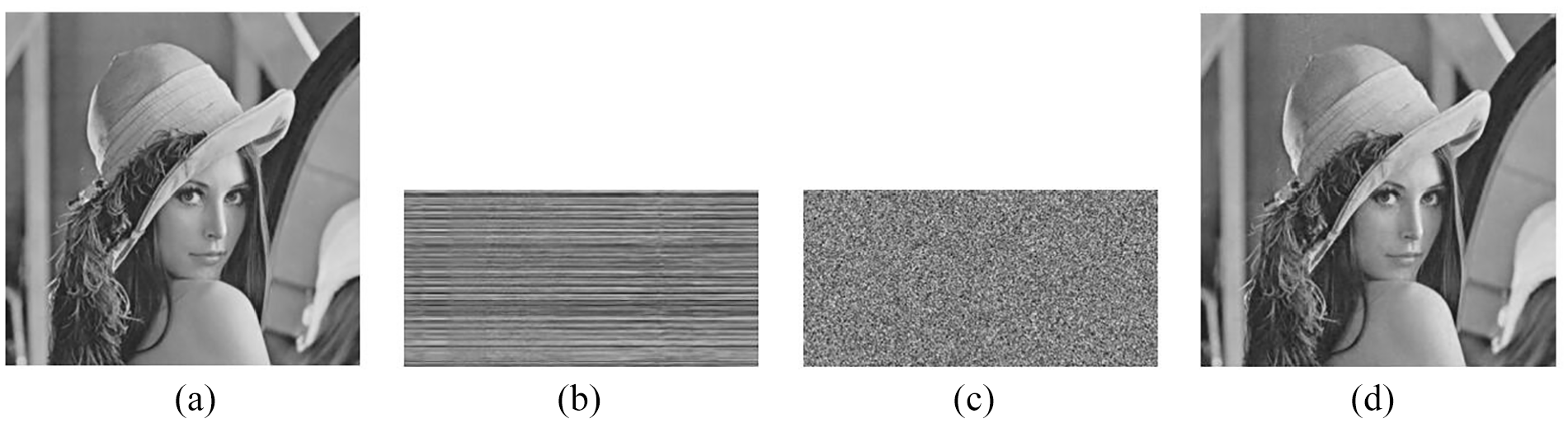
(a) The original image, (b) the CS-based encrypted image, (c) the finally encrypted image, and (d) the decrypted image (PSNR = 32.56).
Histogram analysis
In the field of image processing, the histogram of an image normally refers to a histogram of the pixel values. The histogram of image is an important statistical characteristic, which is usually considered as an approximation of the density function. Generally speaking, an ideal image encryption algorithm has the ability to realize that the encrypted image would not reveal any statistical feature of the original image.
The histogram of the original image, the encrypted image, and the decrypted image are shown in Figure 4. Obviously, the pixel values of the finally encrypted image well distribute in the interval [0, 255], which stands for an excellent encrypted result. However, the pixel values of the CS-based encrypted image approximately follow Guassian distribution, which is not accidental, resulting from a fact that CS measurements follows sub-Guassian distribution. It can be therefore said that the proposed privacy-preserving framework can conceal the statistical characteristic of the plaintext well.

The histograms of different images: (a) the original image, (b) the CS-based encrypted image, and (c) the finally encrypted image.
Correlation analysis
After encryption process is performed, an obvious space correlation for the neighboring pixels in a natural image always appears, which is a kind of meaningful information in some privacy-preserving scenarios. Hence, it is very crucial for an image encryption algorithm to avoid leaking the correlation. There is a mathematical definition of the correlation coefficient,

where
In our experiments, 2000 pairs of adjacent pixels are selected randomly from the original image, the CS-based encrypted image, and the finally encrypted image in the horizontal, vertical, and diagonal directions. As shown in Table 1, any two adjacent pixels in the original images are tightly correlated with each other but the correlation coefficients of the finally encrypted image are close to 0 in all directions. A more intuitive experimental result is shown in Figure 5. In general, CS-based encryption does well in only the vertical and diagonal directions but does not work in the horizontal direction. And the correlation is completely broken up after chaotic encryption is performed.
Correlation coefficients.

CS: compressive sensing.

Correlations between two adjacent pixels selected from different images in the different directions. The original image, CS-based encrypted image, and finally encrypted image in the (a) horizontal direction, (b) vertical direction, and (c) diagonal direction.
Key sensitivity analysis
In the proposed encryption framework, four chaotic sequences related with four keys
In our experiments, a seemingly tiny change 10−15 takes place in every key, and then these changed key are used to recover the original image. Note that only one key is changed in every experiment. As shown in Figure 6(a)–(c), the decrypted images can not reveal any meaningful information once one key is false. Figure 6(d) denotes that the decryption (reconstruction) algorithm cannot work completely after the bitwise XOR operation is performed. Here, we emphasize a conclusion that the proposed image encryption scheme can not only flexibly meet the different levels of security requirement but also be considered as a multi-party management system by distributing the four keys to several authorized individuals.

The decrypted image using a false key: (a)
Attack analysis
Brute-force attack
Brute-force attack means that an attacker tries to guess the possible keys and uses them for decryption. In the proposed framework, a chaotic system is used to perform CS-based sampling–compression–encryption, sample-level permutation, and bit-level substitution operations. The above key-sensitivity test intuitively demonstrates that the whole key space is large enough to make brute-force attack infeasible, which is therefore said to be computational secrecy.
Ciphertext-only attack
Ciphertext-only attack (COA) means that an attacker tries to get some valuable information about the plaintext only from the ciphertext. The security of the proposed framework depends on two kinds of privacy-preserving operations, including CS-based encryption and chaotic permutation–substitution encryption. In view of the linearity of CS projection, an interesting security feature of the CS-based cryptosystem under COA is the asymptotic spherical secrecy, meaning that any two different plaintexts with the same power keep approximately indistinguishable from their ciphertext. Such a property is attributed to the energy-preserving guarantee of RIP. In the proposed framework, the chaos-based bitwise XOR operation (substitution) can break the energy-preserving property such that attackers would not reveal any valuable information through COA.
KPA and CPA
As for the standalone CS-based cryptosystem, at least
Comparison
In this part, the superiority of the proposed framework is demonstrated by comparing it with some existing works. First, we present some potential attack types in this field, including attack type I: brute-force attack to the whole key space or guess at possible measurement matrices, attack type II: reveal the energy information of plaintext by COA, and attack type III: calculate the used measurement matrix by KPA or CPA. Then, we analyzed their resistance to the above attack types. Finally, their security levels are given in Table 2. CS-based sampling–compression–encryption framework, in which single 18 or multiple 24 chaotic map(s) is used to construct measurement matrix, is a lightweight cipher. The bi-level protected CS framework 19 is a prominent work but still could not get rid of the linear relationship between plaintext and ciphertext. In Zhou et al. 26 and Liu et al., 28 some additional privacy-preserving methods are integrated with CS-based cipher to enhance the confidentiality, but their confusion–diffusion effects are still not outstanding. In the proposed framework, not only is CS-based cipher embedded with double secrecy but also sample-level permutation and bit-level substitution (XOR operation) are used to guarantee a great confusion–diffusion effect.
Comparison between the proposed framework and some existing works.

Conclusion
In this article, it is pointed out that CS-based image acquisition systems have the potential to perform sampling, compression, and encryption simultaneously. Besides, how to design the CS-based cipher is deeply studied from two feasible view points, that is, the key-dependent measurement matrix and the key-related sparsifying basis. Moreover, we employ a chaotic system to realize a CS-based cipher with double confidentiality. Considering that CS measurements cannot provide an adequate guarantee of confidentiality, an intrinsic weakness of CS-based cipher, an additional encryption approach based on chaos, and diffusion–confusion mechanism have been proposed. Combining the CS-based double-secrecy cipher with the permutation–substitution encryption, we proposed a novel sampling–compression–encryption framework for secure image acquisition. Based on the simulation experiments and analyses, it is therefore said that the proposed framework achieves a high-level security.
Footnotes
Handling Editor: Leo Zhang
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the Chongqing Research Program of Basic Research and Frontier Technology (Grant No. cstc2017jcyjBX0008), the Chongqing Postgraduate Education Reform Project (Grant No. yjg183018), and the Chongqing University Postgraduate Education Reform Project (Grant No. cquyjg18219).
