Abstract
In this article, a new reversible data hiding scheme using pixel-value differencing in dual images is proposed. The proposed pixel-value differencing method can embed more secret data as the difference value of adjacent pixels is increased. In the proposed scheme, the cover image is divided into non-overlapping blocks and the maximum difference value is calculated to hide secret bits. On the sender side, the length of embeddable secret data is calculated by using the maximum difference value and the log function, and the decimal secret data are embedded into the two stego-images after applying the ceil function and floor function. On the receiver side, the secret data extraction and the cover image restoration can be performed by using the correlation between two stego-images. After recovering the cover image from two stego-images, the secret data can be extracted using the maximum difference value and the log function. The experimental results show that the proposed scheme has a higher embedding capacity and the proposed scheme differs in embedding the secret data depending on the characteristics of the cover image with less distortion. Also, the proposed scheme maintains the degree of image distortion that cannot be perceived by the human visual system.
Introduction
Recently, most of important information is transmitted over the Internet using advanced computer performance and Internet technology. Internet is convenient for information exchange because of easy access and various conveniences. However, the Internet is an open space, so important information can be deceived and altered by malicious attackers. Therefore, many data hiding schemes that can transmit information securely over the Internet have been proposed. In general, a data hiding scheme generates the stego-image by embedding the secret data into a cover image. Many data hiding schemes have been proposed based on least significant bits (LSB) replacement and pixel-value differencing (PVD) in irreversible data hiding methods.1–5 The LSB scheme embeds or extracts the secret data in the lower bit region in each pixel or pixel group that is based on the fact that it is very difficult to be detected by the human visual system even if the lower bits of a pixel change. The LSB-based schemes uniformly embed the secret data as same quantity into all pixels of a cover image. However, there are edge and smooth areas in an image and it means that different amount of secret bits can be embedded on edge and smooth areas. It is based on the fact that the alteration of edge areas cannot be distinguished well, but the alteration of smooth areas can be distinguished easily in human visual system. In other words, an edge area can be hidden more secret data than a smooth area. The PVD was first proposed by Wu and Tsai to distinguish edge and smooth areas. In the PVD method, two pixels are located in an edge area if the difference value between the two consecutive pixels is large, then more secret data can be hidden depending on the range table. On the other hand, if the difference value between the two consecutive pixels is small, less secret data can be hidden since the two pixels are located in a smooth area. Data hiding schemes using PVD method are proposed continuously.6–8 Although the PVD method can embed more secret data and guarantee high imperceptibility, the cover image cannot be restored because the original image is damaged after extracting the secret data from the stego-image. It could cause serious problems in the military and medical fields that are sensitive to the distortion of the original image, so reversible data hiding schemes have been proposed to overcome restoring the cover image.9–12 The reversible data hiding scheme can extract the secret data from the stego-image and restore the original cover image perfectly without loss of cover image. In general, reversible data hiding schemes generate a single stego-image by embedding secret data into a single cover image, but recently, dual image–based reversible data hiding schemes have been proposed that generate two stego-images after embedding secret data into a cover image. Dual image–based reversible data hiding scheme was first proposed by Chang et al. 13 in 2007. This scheme embeds and extracts secret data based on the quinary notation and improves the extraction function of exploiting modification direction (EMD) scheme 14 to increase the embedding capacity. A modulus function is designed, and two stego-pixel values are defined according to the value of the quinary secret data. In 2009, Lee et al. proposed a dual image–based reversible data hiding scheme using four directions based on the central point. 15 This scheme uses the relationship between two images to determine if secret data can be embedded in the second image. In the embedding process, two stego-pixel values are determined according to the combination of two binary secret bits. Qin et al. proposed a scheme for performing different embedding processes on two images, 16 where the EMD scheme was applied to the first image and three rules based on the first image to embed the secret data was used to the second image. In this scheme, the distortion of the second stego-image is larger than the first stego-image. In 2015, Lu et al. proposed a dual image–based reversible data hiding scheme to reduce loss of original image by applying center folding strategy (CFS) method. 17 The CFS method reduces the distortion of the image by adjusting the range of secret data. In this scheme, secret data are embedded by using the ceil function and the floor function to generate two stego-images. In 2017, Yao et al. 18 proposed a dual image–based reversible data hiding scheme using the selection strategy of shiftable pixels’ coordinates to improve the Lu et al.’s scheme. Yao et al. used the diagram to improve the scheme of Lu et al., and the selection strategy of the shiftable pixels’ coordinates was used to increase the embedding capacity. In this scheme, secret data are classified into even and odd numbers, and different embedding methods are applied. In 2019, Shastri and Thanikaiselvan proposed a scheme to improve the image quality of Yao et al.’s scheme. The CFS method, shiftable pixel coordinate selection strategy method, and lookup table were used to improve the image quality. 19 In this article, we propose a dual image–based reversible data hiding scheme using the PVD method. The proposed scheme divides a cover image into sub-block and uses the maximum difference value in each sub-block to decide the length of embeddable secret data. Therefore, the proposed scheme can embed more secret data when the difference value of pixel values is larger in each sub-block.
The rest of the article is organized as follows. The PVD method and dual image–based reversible data hiding schemes are described in the “Related works” section. In the “The proposed scheme” section, the proposed embedding scheme is described and extracting and restoring scheme is explained in detail. The experimental results are explained and analyzed to demonstrate the superiority of the proposed scheme. The “Conclusion and discussion” section concludes the article.
Related works
PVD
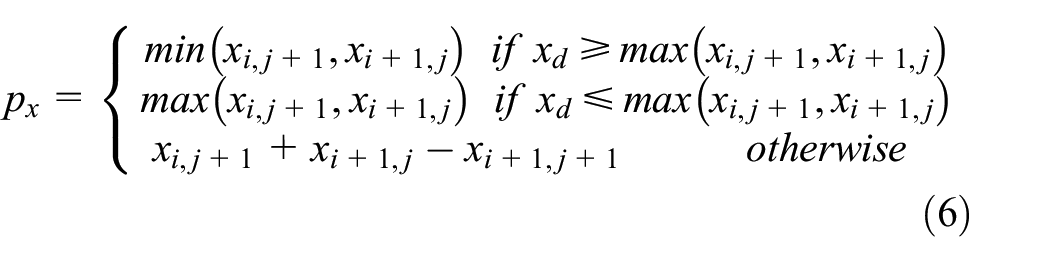
Wu and Tsai proposed a PVD scheme that adjusts the size of secret data that can be embedded according to the difference between two neighboring pixels. In the grayscale cover image, two consecutive pixels are used as one block. The image is divided by blocking. When the pixels of each block are denoted by

If a value obtained by converting

When the new difference value is

Suppose that two consecutive pixels in a grayscale stego-image are denoted by

Zhang et al.’s scheme
In 2019, Zhang et al. proposed reversible data hiding scheme using histogram shifting for high embedding capacity. This scheme used additive homomorphic encryption and block permutation for image encryption and consists of encryption, secret data embedding, secret data extraction, and image restoration phase.
The encryption phase consists of additive homomorphic encryption and Block permutation. The cover image is divided into non-overlapped blocks, and a key stream

Then, block permutation is performed to enhance security. Block permutation uses the Logistic chaotic function to generate a key sequence and performs block permutation based on this key sequence to create a fully encrypted image
The secret data embedding step consists of a prediction step, a histogram expansion, and a shifting step. In the prediction phase, three sets are used. In the case of set 0, the predicted value is calculated using MED. When
In case of set 1, the predicted value

The case of set 2 is similar to set 1. The

After the prediction error value

The prediction error

If the secret data are
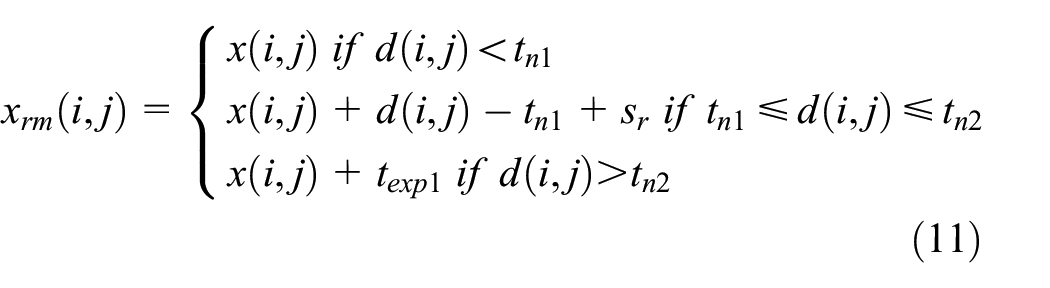
To generate a stego-image, a similar process is performed for histogram left expansion and shifting.
Lu et al.’s scheme
Lu et al.’s scheme used CFS method to reduce image distortion in embedding of secret data. Lu et al.’s scheme selects

In order to generate two stego-images, the

When a pixel value of the cover image is defined as

Yao et al.’s scheme
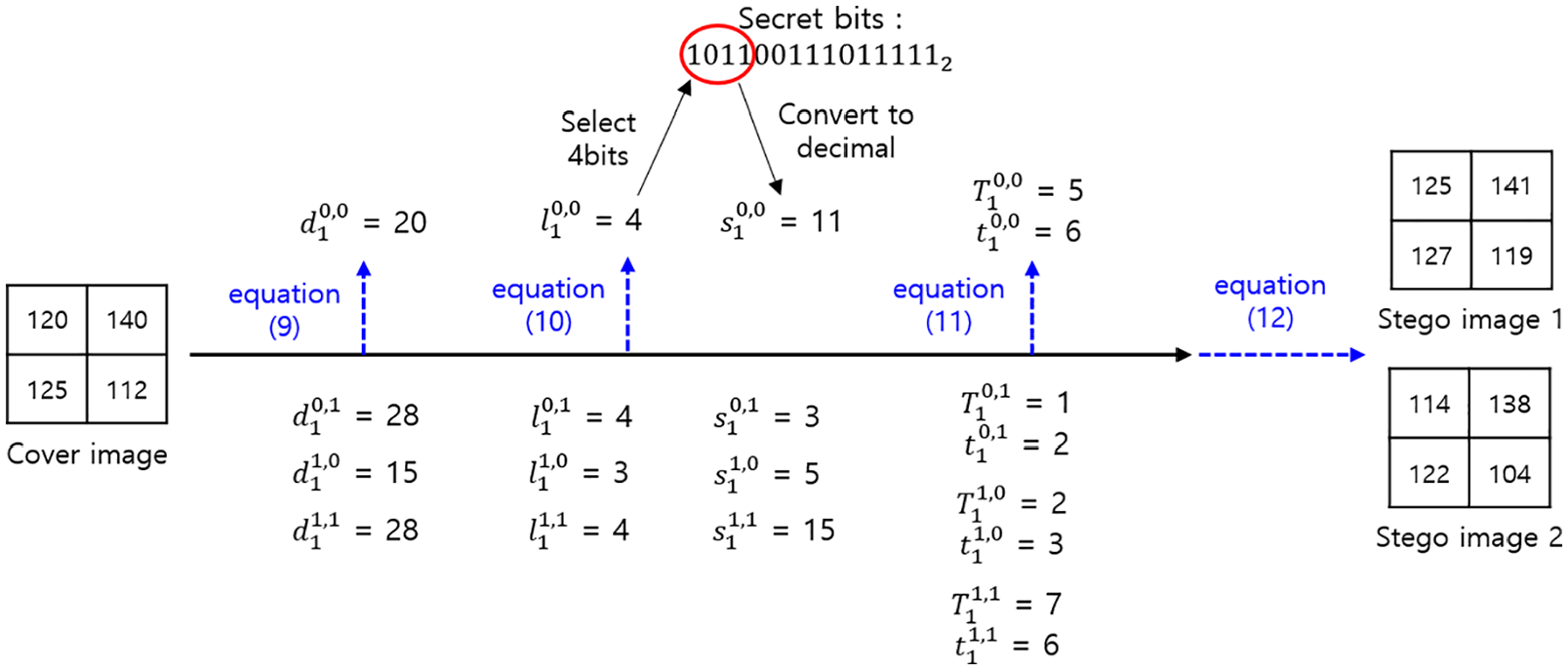
In 2017, Yao et al. improved Lu et al.’s scheme by using selection strategy of shiftable pixel coordinates. Yao et al. improved the embedding capacity of secret data by improving Lu et al.’s scheme as shown in Figure 1, where Figure 1 shows a diagram of the embedding of secret data for both schemes. As shown in Figure 1, Yao et al.’s scheme increased the embedding capacity since the number of cases of embedding is larger than that of Lu et al.’s scheme. If the number of bits of the binary secret data that can be embedded is

Comparison of (a) Lu et al.’s scheme and (b) Yao et al.’s scheme.
If
Case 1:

Case 2:
Shastri and Thanikaiselvan’s scheme
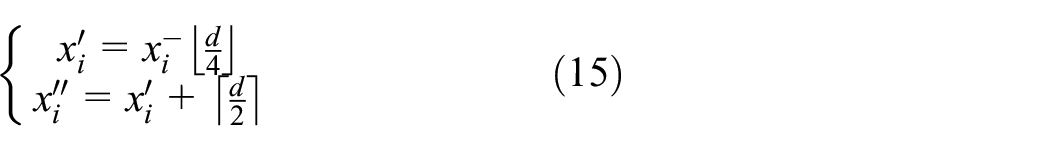
In 2019, Shastri and Thanikaiselvan proposed a scheme to improve the quality of the image while maintaining the amount of secret data capacity in Yao et al.’s scheme. This scheme uses the CFS method and the shiftable pixel coordinate selection strategy method and creates a lookup table to improve the
Trinary mapping.
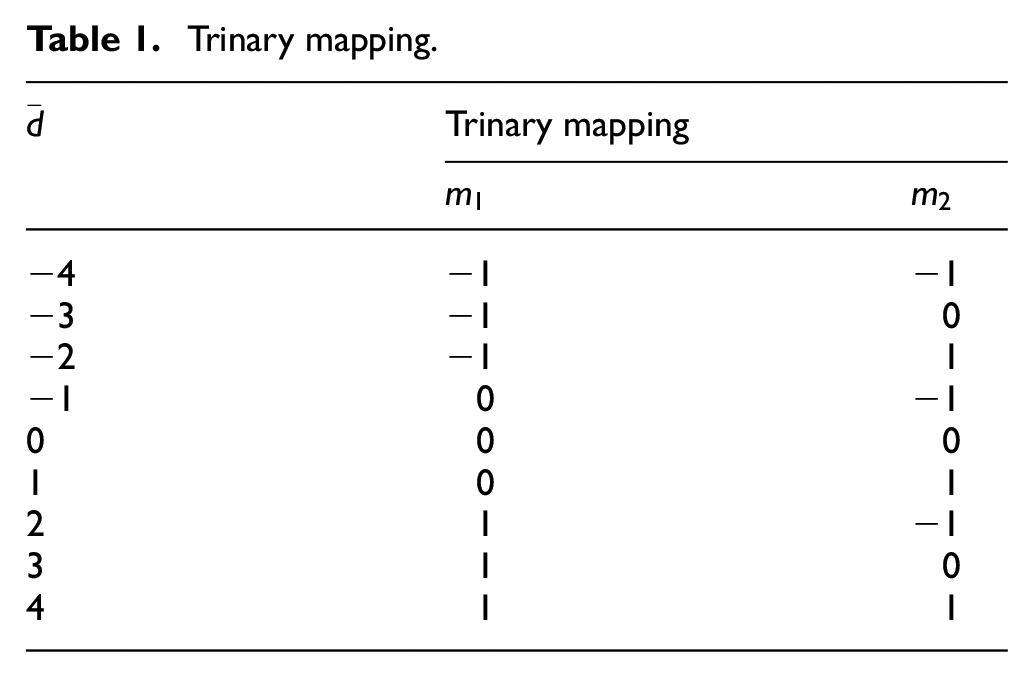
Initial shifts are calculated using equation (16).
Case 1:

Case 2:

The final shifts
Case 1:
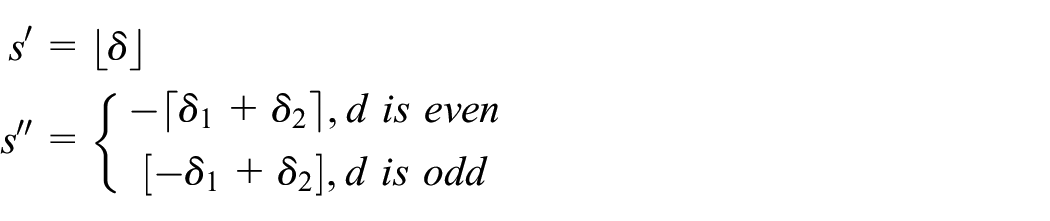
Case 2:
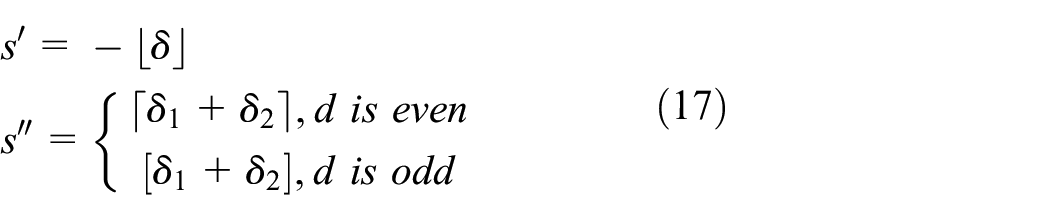
The created lookup table, Table 2, is as follows.
Lookup table.
Equation (18) is used to generate two stego-image pixels

The proposed scheme
The proposed scheme uses PVD method to dual image–based reversible data hiding scheme for high embedding capacity. The cover image divides into sub-blocks with non-overlapping and the maximum difference value is calculated between the pixels in each sub-block. The maximum difference value and log function are used to determine the number of embedding secret bits. The binary secret bits that can be embedded into each pixel are converted into decimal secret data. The decimal secret data are embedded by using the floor function and ceil function into the cover image to generate two stego-images. In the extraction process, the two stego-images are divided into non-overlapping blocks. The cover image is recovered using the average value of the pixel values of the two stego-images. The maximum difference value is calculated within each block of the cover image, and secret data are extracted using the maximum difference value and the log function. In this section, we describe a new dual image–based reversible data hiding scheme that embeds secret data according to the difference value of the pixels in the block for high embedding capacity.
Embedding algorithm
The detailed embedding algorithm is as follows. Each pixel in the block calculates the difference value with the other pixels in the block and embeds the decimal secret data based on the maximum difference value.
Input: A cover image with width
Output: The two stego-images of




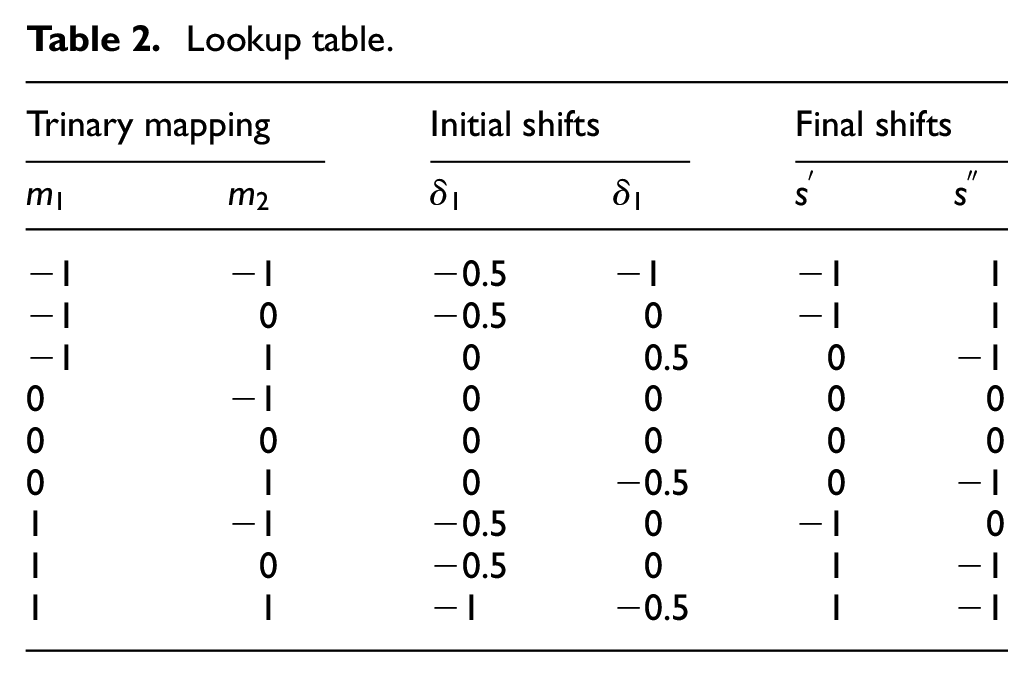
An example of the embedding algorithm is as follows. The cover image is divided into 2×2 size blocks. The first block is
Embedding example.
Extraction and recovering algorithm
The detailed extraction algorithm is as follows. In the recovering process, the cover image is restored by using the average value between the two stego-images. The secret data are extracted using the maximum difference value among the pixels in the restored cover image.
Input: The two stego-images of
Output: A cover image with width

An example of the extraction and recovering algorithm is as follows. The stego-image is divided into 2×2 size blocks. In the first block, the cover pixels

Extraction and recovering example.
Experiment results and analysis
The reversible data hiding scheme measures the image quality and embedding capacity to evaluate the performance of the proposed algorithm. The embedding capacity of the secret data means the amount of secret data that can be inserted into a cover image. The visual image quality means the degree of distortion of the stego-image. The

When the pixels of the cover image are

In the proposed method, two 512×512-sized stego-images are generated using a cover image of 512×512 sizes as shown in Figures 4–6. In 2002, Wang and Bovik 20 proposed a method to measure the quality index of images using correlation loss, luminance distortion, and contrast distortion


Cover images: (a) Lena, (b) Peppers, (c) Baboon, (d) Boat, (e) Barbara, (f) Airport, (g) Elaine, (h) Man and woman, (i) Crowd, (j) Tank, (k) Bridge, and (l) Truck.

First stego-images: (a) Lena (39.1330 dB), (b) Peppers (39.1375 dB), (c) Baboon (31.1448 dB), (d) Boat (36.6100 dB), (e) Barbara (33.4702 dB), (f) Airport (34.5950 dB), (g) Elaine (39.1330 dB), (h) Man and woman (36.1232 dB), (i) Crowd (37.0450 dB), (j) Tank (39.4645 dB), (k) Bridge (33.1101 dB), and (l) Truck (39.6765 dB).

Second stego-images: (a) Lena (38.2845 dB), (b) Peppers (38.2407 dB), (c) Baboon (30.7269 dB), (d) Boat (35.9289 dB), (e) Barbara (32.9912 dB), (f) Airport (34.0230 dB), (g) Elaine (37.9787 dB), (h) Man and woman (35.5408 dB), (i) Crowd (36.3602 dB), (j) Tank (38.4224 dB), (k) Bridge (32.6074 dB), and (l) Truck (38.6272 dB).
Each element of the equation is given in equations (29)–(31)



The exponent is defined as the combination of loss of correlation, luminance distortion, and contrast distortion, and is redefined as equation (32)

Visual image quality
The first stego-images with
Table 3 compares the
Comparison of

Comparison of

Embedding capacity
The maximum embedding capacity of the proposed scheme and other schemes is compared in Table 5. The average embedding capacity of the proposed scheme is at least about 100,000 bits higher than Lu et al.’s scheme and Yao et al.’s scheme on average. And, the average embedding capacity of the proposed scheme is at least about 600,000 bits higher than Shastri and Thanikaiselvan’s scheme on average. Shastri and Thanikaiselvan’s scheme aims to improve the image quality when the embedding capacity is not large, so the maximum embedding capacity is low. As a result, the proposed scheme can embed more secret data than other schemes while maintaining the degree of image distortion that cannot be detected by the human visual system. Figure 7 compares the maximum embedding capacity using a histogram. The histogram shows that the proposed scheme has higher embedding capacity than other schemes in most images. And, the embedding capacity of secret data is almost constant in other schemes. However, the proposed scheme can embed the secret data up to 1,800,000 bits depending on the characteristics of the image. In the case of Baboon image and Bridge image, the embedding capacity of secret data is high because of the large difference between adjacent pixels.
Comparison of maximum embedding capacity.
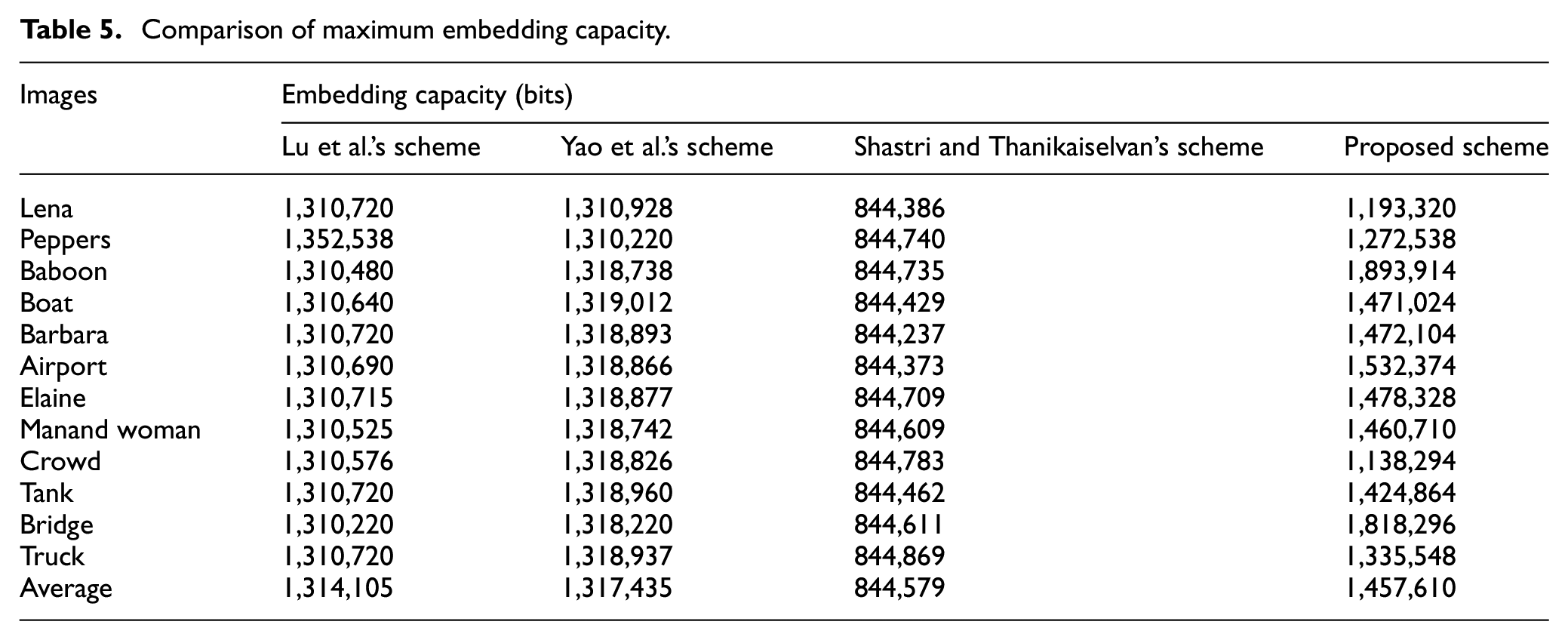

Comparison of embedding capacity of the proposed scheme and other schemes.
Quality index
Figure 8 shows the quality index values for each cover image. The quality index measures the loss of correlation, luminance distortion, and contrast distortion between the cover image and the stego-image. The proposed scheme maintains a similar quality index to Lu et al.’s scheme, Yao et al.’s scheme, and Shastri and Thanikaiselvan’s scheme. Therefore, the proposed scheme has a higher embedding capacity than other schemes, and the image quality is similar to other schemes.

Comparison of the quality index about four images.
PSNR and embedding capacity
Figure 9 shows

Comparison of embedding capacity and
Conclusion and discussion
In this article, a dual image–based reversible data hiding scheme using PVD has been proposed. The cover image was divided into blocks of size
Footnotes
Acknowledgements
We thank the anonymous reviewers for their valuable suggestions that improved the clarity of this article.
Handling Editor: Ru Zhang
Author contributions
All authors discussed the contents of the manuscript and contributed to its preparation. P.-H.K. conducted all experiments and wrote the manuscript. K.-W.R. designed and conducted the literature review. K.-H.J. proposed the concept of algorithm and wrote the manuscript.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research was supported by Basic Science Research Program through the National Research Foundation of Korea (NRF) funded by the Ministry of Education (NRF-2018R1D1A1A09081842) and Korea Research Fellowship Program through the NRF funded by the Ministry of Science and ICT (2019H1D3A1A01101687).
