Abstract
Routing protocol for low-power and lossy networks is a routing solution specifically developed for wireless sensor networks, which does not quickly rebuild topology of mobile networks. In this article, we propose a mechanism based on mobility entropy and integrate it into the corona RPL (CoRPL) mechanism, which is an extension of the IPv6 routing protocol for low-power and lossy networks (RPL). We extensively evaluated our proposal with a simulator for Internet of Things and wireless sensor networks. The mobility entropy-based mechanism, called CoRPL+E, considers the displacement of nodes as a deciding factor to define the links through which nodes communicate. Simulation results show that the proposed mechanism, when compared to CoRPL mechanism, is effective in reducing packet loss and latency in simulated mobile routing protocol for low-power and lossy networks. From the simulation results, one can see that the CoRPL+E proposal mechanism provides a packet loss reduction rate of up to 50% and delays reduction by up to 25% when compared to CoRPL mechanism.
Keywords
Introduction
Wireless sensor networks (WSNs)1–4 occupy several environments such as residences, offices, and factories, and perform an important role in integrating smart objects to the Internet of Things (IoT). 5
Motivating research in the area of IoT and WSNs forecasts point to the existence of about 50 billion devices connected to IoT in 2020, 6 which includes everyday objects such as mobile devices, cars, and also parts, products, and industrial machines. Opportunities also exist for the development of new applications, especially those involving mobility, in areas such as smart cities, robotics, e-health, and sports activities monitoring.
An example scenario that encourages research in WSNs is related to 5G networks that will be used as backhaul interface for WSNs. In 5G networks, small communication cells (SCCs) will coexist with the macro-cells in order to increase the quality of communication in the coverage area, increase the transmission rate, and reduce the communication delay. 7 In this scenario, base stations (BSs) of SCs may be used to offer Internet access to WSNs’ gateways, also called IoT border routers in IoT terminology. In this scenario, the IoT border routers can employ dedicated hardware or even be smart phones equipped with different technologies to communicate with sensors in the environment and to offer new smart applications.8–10 From this perspective, it is seen in Ahamed and Faruque 11 that 5G networks will play an important role in services of remote monitoring and real-time control of devices that support machine-to-machine (M2M) and IoT communication such as connected cars, mobile robots, sensors installed in the industry, public infrastructure, and smart homes. 8
The limitations of devices that compose the WSNs and IoT devices impact the routing protocol used by the wireless nodes. For this reason, specific protocols are required for this type of network.
Due to this, the IETF (Internet Engineering Task Force) developed the specifications of the routing protocol for low-power and lossy networks (RPL), designed to route data in low-power and lossy networks (LLNs).
RPL was initially developed to work on static network scenarios, since it dramatically reduces link maintenance when it assumes that the network has reached a permanent state.
In order to promote mobility support, some research in the literature12–25 suggests adaptations to the RPL protocol. Among these researches, we noticed the development of solutions that have the following characteristics: (1) are designed for scenarios with few wireless mobile nodes (MNs),12,13,16,17,19,21,24 (2) focus on the development of localization mechanisms that depend on a large number of fixed reference wireless nodes,12,14,17–19,21,23,24 (3) use scenarios where MNs have fixed or low dynamic movement trajectories (e.g. line, grid, square),12,14,16–18,23,24 and (4) are designed to improve downlink traffic 24 or to improve communications in scenarios with mobile root nodes and static wireless nodes.13,18
Among the works of the literature, we identified the CoRPL proposal
25
as being the one with the greatest relation to our research and that shows better performance. CoRPL proposes the division of the network into circular sub-areas called Coronas, with radius equal to the maximum transmission range of the wireless nodes—these areas being identified by a Corona ID (
In this article, we propose a mechanism residing in the MNs of an RPL network that extends the CoRPL mechanism. 25 In our proposal, we used the Corona ID, the mobility entropy, and the expected transmission count (ETX) metric in order to select among the next-hop MNs, which will be the PP node for an MN. The use of the mobility entropy in the proposed mechanism had the objective of selecting the PP node with the least movement instability among the possible next-hop PP nodes. The proposed mechanism was tested using the Cooja simulator, 26 in scenario of dozens of MNs moving with dynamic trajectory. RPL is currently considered the most important routing protocol in the IoT scenario, having the need to operate in applications with dynamic movement of several types of smart objects such as wearable gadgets, mobile robots, and unmanned air vehicles (UAVs). 27 In the simulated dynamic motion scenarios, the results showed positive aspects of the proposed idea: lower packet loss rate and lower average delay of packets transmitted in uplink toward the root nodes of an RPL network.
In order to present the subjects discussed, the article is divided into the following sections. The “Related work” section explains the RPL protocol and the concept of mobility entropy. The “Theoretical background” section discusses related works. The “CORPL+E architecture” section explains the architecture of the proposal CoRPL+E. The “Performance evaluation” section shows the results obtained. The “Conclusion” section presents conclusions and future works.
Related work
Lee et al.’s 12 study adjusts RPL parameters to improve performance of RPL in Vehicular Ad Hoc Network (VANET) scenarios. The adjustments made consist of (1) increasing the transmission frequency of probes used to determine the ETX metric, (2) ignoring the trickle timer used to periodically send DIO (DODAG Information Object) messages, and (3) ignoring the Delay-DAO (Destination Advertisement Object) timer used for DAO message transmission. As a result of the adjustments, the packet loss rate was reduced. However, the timer settings were executed statically for scenarios with few MNs moving in fixed trajectories. Therefore, the work does not evaluate or propose solutions for scenarios with dynamic mobility or with greater node density.
Safdar et al. 13 propose adapting the RPL to create a hybrid protocol, both reactive and proactive, but for the scenario with multiple mobile root nodes (mobile roots (MRs)), not considering the mobility of MNs. In addition, the proposal was not evaluated experimentally or in simulations.
In Korbi et al., 14 the authors present the Mobility-Enhanced RPL (ME-RPL), in which wireless nodes are classified as SNs (static nodes) and MNs. In ME-RPL, an SN is prioritized as the parent node. Next, the lowest ranking node is prioritized, and finally, if there is a tie, the objective function (OF) rules apply. Another change is the dynamic and more frequent delivery of DIS (DODAG (Destination-Oriented Directed Acyclic Graph) Informational Solicitation). Simulation results comparing RPL and ME-RPL demonstrate a reduction in packet loss and better route stability for the latter. However, the simulations were performed with a small amount of MNs in relation to the total number of nodes. In mobile networks, most nodes are in motion to impair the ME-RPL model.
The proposal of Hong and Choi 15 extends the RPL protocol to create the DMR (DAG (Destination Acyclic Graph)-based Multipath Routing for mobile sensor networks) protocol. The model uses rank as a metric in DIO messages to build the DODAG and to create alternate routes whenever possible using sibling nodes. The authors present performance simulation results of the proposed model, but the proposal is compared with networks that employ the AODV (On-demand Distance Vector), 28 and AOMDV (On-demand Multipath Distance Vector routing in ad hoc networks), 29 routing metrics. These two metrics were not designed for LLNs.
In Fotouhi et al., 16 the authors integrate a handoff mechanism for RPL aiming to handle long latencies, high packet losses, and high overhead. The mechanism uses RPL control messages, such as beacons, and adds four timers that help notice degradation of links. Simulation results show that the mechanism reduces packet loss and handoff time but results in a large overload in networks with high transmission rates, and the handoff process is less responsive in low traffic networks. Moreover, the authors evaluated their proposal in scenarios with only one MN that uses several SNs as reference to execute handoff between them.
The Kalman Positioning RPL (KP-RPL) 17 divides the routing into hierarchical levels and employs the conventional RPL protocol between SNs and geographic routing between MNs and SNs. Thus, the authors use an approach that is not normally employed in RPL networks.
Tahir et al. 18 adapt the RPL to scenarios with multiple mobile root nodes, not considering the mobility of MNs. The proposal is evaluated using mobility with semi-static behavior, which compromises performance evaluation.
EKF-MRPL (Enhanced Kalman Filter–Mobile RPL) 19 provides connectivity without interruptions to MNs while it is executing handover between parent SNs. However, the EKF-MRPL is able to determine the correct positioning of the MN, not aiming to propose an OF, and therefore was evaluated in a scenario composed of 25 reference SNs and 01 single MN limited to leaf node of the network.
Kharrufa et al. 20 propose D-RPL (Dynamic RPL) that implements a trickle timer called reverse which determines the transmission period of DIS messages. The authors use the MRHOF (minimum rank with hysteresis objective function) implemented in the Contiki operating system, 30 along with the ETX, energy, and Link Quality Indicators (LQI) metrics to propose their OF. However, Kharrufa et al. 20 do not clarify how the metrics were combined in its proposed D-RPL.
Sanshi and Jaidhar 21 propose the ERPL (Enhanced RPL) protocol that updates the PP of an MN when such MN moves away from its current PP. The proposal does not allow MNs to transmit DIO messages and thus become PP nodes. Note that making it impossible for MNs to become PPs can cause a network with many MNs to become disconnected.
In Wang et al., 22 the authors propose monitoring the received signal strength indicator (RSSI) of DIO messages received by an MN to update its rank. Some flaws in the proposed algorithm are evident, since it is possible for an MN to increase its rank value when it moves toward its PP.
Fotouhi et al. 23 propose an interoperability framework between SNs and MNs, so an MN can execute handoff of PP node. However, the proposal, despite assuming the positional science of all nodes, is highly dependent on SNs for its correct operation and therefore is tested in a grid scenario with 13 reference SNs and only one MN moving with deterministic trajectory defined between the lines of the grid.
Carels et al. 24 propose a mechanism to reduce connectivity loss and packet loss in downlink transmission; however, this does not improve performance for uplink traffic.
The CoRPL
25
divides the network into circular areas, called coronas with radius equal to the maximum node transmission range, being identified by a Corona ID
Table 1 shows that most of the works intend to improve the RPL performance but focus on the localization systems and, therefore, are highly dependent on static wireless reference nodes or low dynamic trajectories.12,14,16,17,18,19,21,23 Some aim to improve the performance of RPL for downlink traffic, 24 others13,18 aim to improve the RPL in the scenario of mobile root nodes. Works like ours appear in previous works.20,22,25 The drawbacks of such approaches are that Kharrufa et al. 20 do not explain how the metrics are combined in their D-RPL proposal and 22 focus on updating the rank of MNs and not on the proposal of a new OF. The results of the Wang et al. 22 show that, even in simulations with low packet transmission rates (e.g. 1 pkts/min), their proposal obtains packet delivery rate of up to 63% when the amount of MNs is equal to 60. In a similar situation, Gaddour et al. 25 show superiority obtaining a packet delivery rate of 67%, even when the packet transmission rate is much higher, with a value of 30 pkts/min. Compared to Gaddour et al., 25 our proposal improves the OF of the cited article, since we use the mobility entropy as one of the criteria to select the best PP for an MN. Due to this, our proposal obtains better results in terms of packet loss rate and average packet delay, when varying packet’s transmission rate, number of MNs, node’s velocity, and number of root nodes, as shown in the next section.
Articles that address mobility.

MN: mobile node; MR: mobile root; SN: static node; RPL: routing protocol for low-power and lossy networks; OF: objective function; MRHOF: minimum rank with hysteresis objective function; PP: preferred parent; DAO: Destination Advertisement Object; RSSI: received signal indicator; ETX: expected transmission count; LQI: link quality indicators.
Theoretical background
RPL protocol
RPL is an IPv6 protocol (Internet Protocol version 6) that builds a DODAG 32 to target the root node of the network. Each node maintains a table of neighbors containing possible parent nodes to reach the root node. One of the parent nodes is defined as preferred parent. The RPL defines the following ICMP-v6 19 route discovery messages: DIO, DIS, and DAO. DIO messages start from the root node and are propagated by the other DODAG nodes. Each network node uses a timer called trickle 33 that establishes the frequency of transmission of DIO messages to verify connectivity with nearby nodes. When a node verifies that there are differences between its neighborhood table and the network around it, the trickle timer increases the frequency of DIO messages and, when there are no inconsistencies, the trickle drastically reduces the transmission of DIO messages. DIO messages report DODAG characteristics such as the OF in use. The OF 34 informs the routing metrics used to give weight to the links. The rank value is a metric that indicates the position of a node, in number of hops, relative to the root node. 35 DIS messages are transmitted by nodes wishing to connect to DODAG. DAO messages propagate DODAG information from the network nodes toward the root node. 36
The proposed mechanism in this article is an extension of the original RPL protocol and the CoRPL extension. Thus, the proposal herein preserves RPL protocol messages such as DIO, DIS, and DAO. As in Gaddour et al., 25 the root node transmits DIO messages periodically, so that network topology changes are perceived more quickly.
Mobility entropy
Entropy is defined as the degree of disorder in a system. 37 This article uses the concept of entropy to create a mechanism that selects more stable links.
The entropy

In equation (1),


In equation (4),

In this article, we use the mobility entropy as a criterion used by a network node to determine its PP node. PP candidates with the mobility entropy closer to 1 are prioritized, as is presented in the following section.
CORPL+E architecture
In this article, we propose the CoRPL+E mechanism which is an extension of the CoRPL mechanism proposed in Gaddour et al.
25
For the implementation of CoRPL+E, all the available functionalities of CoRPL
25
were attached to Contiki. According to Figure 1, the proposal of Gaddour et al.
25
divides the network around the root node into concentric circular areas, with range given by the largest transmission radius of a wireless node, called Corona. As observed in example given in Figure 1, in the original CoRPL, if node

Criteria and example of PP selection in CoRPL + E proposal. Each MN uses as criteria for PP selection, the metrics Corona ID, mobility entropy, and the link quality metric.
The value of the mobility entropy is achieved through equation (1) and the result has a value from 0 to 1. The closer to 1, the more stable the link is.
We use Figure 1 and Table 2 to explain the idea of applying the Corona ID, the mobility entropy, and the quality metric of the link as criteria for PP node selection. This assumes that node
Neighbors’ table example.
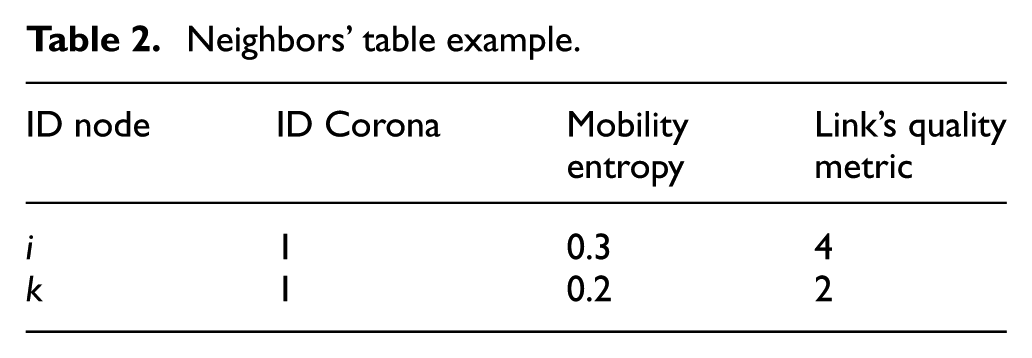
The node
Mobility entropy applied to CoRPL
In Algorithm 1, we can see the CoRPL+E mechanism that resides in each MN (variable

Choice of routes using CoRPL+E mechanism
Next, we show an example of the mobility entropy calculation for three nodes



Applying the Pythagoras theorem



Applying equation (4) as relative speed


Applying equation (2)


Finally, the entropy between the nodes is calculated applying equation (1)


From these calculations, we conclude that the most stable link is between nodes
Determination of nodes positioning in the CoRPL+E mechanism
To determine the velocity vector of the MNs, it was necessary to implement a mechanism, shown in Figure 2, to determine the position of the MNs during the simulation. We used the BonnMotion tool,
38
which can generate random motion mobility scenarios by writing in a log, the

Architecture of the mechanism implemented in Cooja that determines the position
The CoRPL+E protocol
In the following two sections we present, respectively, the protocol already implemented in the CoRPL+E protocol, referring to modifications in the DIS and DAO messages. In the following section, we present the proposed implementation of part of the CoRPL+E protocol, related to the location of the MNs in the network, to be used for the determination of the entropy of mobility.
Messages implemented in the current CoRPL+E protocol
To implement the CoRPL+E mechanism, we extend the Cooja simulator with an approach similar to Gaddour et al. 25 For this, we modify the DIS and DIO messages as shown in Figures 3 and 4.
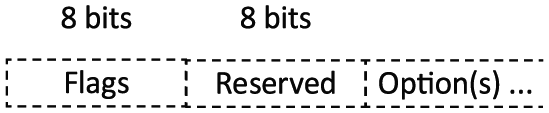
DIS messages of CoRPL + E and CoRPL. The binary values 1 and 2 in the two most significant bits of the flags field were used to identify DIS messages from CoRPL and CoRPL + E, respectively.

DIO message of the CoRPL + E and CoRPL protocols. We used the two most significant bits of the field flags with binary values 1 and 2 to represent the transmission of messages of CoRPL and CoRPL + E, respectively. The reserved field was used to transmit the value of
Figure 3 shows the structure of a DIS message that has the function of making probe of nearby DODAGs and requesting DIO messages. The first field is reserved for the use of flags, is not used, and has 8 bits of length. 41 We used this field so that an MN can identify the DIS messages used in CoRPL (02 most significant bits with 01 binary values) or CoRPL+E (02 most significant bits with 10 binary values). Using some bits from the flags field to differentiate types of DIS messages allows MNs that implement only the RPL protocol to coexist with MNs that implement CoRPL or CoRPL+E mechanisms. This is because nodes that do not use CoRPL+E or CoRPL ignore the flags field so they can use the default OF of RPL. However, in this article, we use the flags field, as commented above, to execute individual simulations of the CoRPL and CoRPL+E mechanisms. In the implementation of this article, as in Gaddour et al., 25 upon receiving a DIS message from a neighbor, the DODAG root broadcasts DIO messages immediately without any waiting time.
Figure 4 shows the structure of a DIO message used in the RPL protocol so that an MN can select its PP, discover, and select parameters of an RPL instance that is defined as one or more DODAGs that use the same OF. 41
In the RPL protocol, the flags field present in DIO and DAO messages is reserved, unused, and has an 8-bit size. In the implementation of this article, we used the values 01 and 10 binary, in the 2 most significant bits, to represent messages of the CoRPL and CoRPL+E mechanisms, respectively. As in Gaddour et al.,
25
we used the 3 most significant bits of the 8-bit reserved field to represent the Corona ID (
Proposed distributed protocol for MN localization
In the CoRPL+E mechanism, we use metrics
As presented in the “Determination of nodes positioning in the CoRPL+E mechanism” section, in this article we employ a centralized simulation scheme, with a position vector that contains the position of all MNs in the simulation, in order that each MN determines the position of the candidate nodes to be its PP.
In this section, we discuss a proposed distributed protocol to allow MNs to exchange information of their positioning with each other and thus MNs can determine the speed vector of the candidates to be their PPs.
According to RFC 6550, 41 the DAG Metric Container (DMC) field may be present as an option field in DIO or DAO messages. In Figure 5, we introduce the DMC field that has up to 255 bytes of total length. The DMC field has the subfields type, option length, and metric data, which in this order carry the value 0 × 02 stating that the DMC field carries a metric, the total size of the DMC field, and, finally, the content and coding of the metric transported.

Format of the DAG Metric Container (DMC) option field that can load metrics (e.g. metrics that result in a sum or product) or recorded metrics of each link in a route.
The DMC option may appear more than once in the same DIO or DAO message, for example, to accommodate a Metric Data field longer than 255 bytes. The DMC option field can contain several aggregated metrics (e.g. ETX metric), or recorded metrics, the latter being used when each node adds a sub-object reflecting the local value of a metric in a path.
In this sense, we suggest that the DMC field of DIO and DAO messages is carried as recorded metric; the
In the following section, we discuss about existing positioning methods, listing the most relevant ones for implementing a proposal of distributed localization protocol to be used in conjunction with the CoRPL+E mechanism.
Discussion about positioning methods
The CoRPL+E is a routing mechanism that requires the location of the MNs in order to determine the mobility entropy of them. To locate unknown positioning MNs (called unknown nodes), special anchor nodes are required to be aware of their positions through the use of an absolute location system (e.g. GPS), relative location system, or because they have been placed in known coordinates. The unknown nodes use the anchor nodes, along with algorithms in order to determine their own locations. 43
According to Halder and Ghosal, 42 localization algorithms can be classified into distributed, centralized, iterative, mobility assisted, and statistical. In the next paragraphs, we describe and compare these algorithms qualitatively.
In distributed algorithms, the unknown nodes are located through the exchange of messages with neighboring anchor nodes that can be more than a hop away. In the distributed system, the smaller the number of anchor nodes, the greater the need for the localization algorithm to use spatial information exchanged between the unknown nodes themselves, which makes the location inaccurate. Thus, this type of algorithm has the disadvantage of having a large density of anchor nodes to promote the location. However, using wireless sensors with new physical layer patterns such as IEEE 802.15.4g (Smart Grid Standards for Operation in Sub-1 GHz Bands) can reduce the number of anchor nodes used as references for locating other MNs. In this sense, it is reported in Oh et al. 44 that the IEEE 802.15.4g physical layer when using bandwidths ranging from megahertz to kilohertz can transmit at distances ranging from tens of meters to up to 20 km. Increased communication distance makes it possible for MNs to locate themselves over long distances with few reference anchor nodes in the network.
In the centralized algorithms, the unknown nodes participate in a network where there is exchange of messages between the wireless nodes and the root node, the latter node determining the location of the other wireless nodes. The centralized algorithms have the advantage of acuricity and disadvantage as they are expensive in terms of message exchange, making these algorithms have scalability problems, especially in mobile networks. By using physical layer patterns with higher transmission range (e.g. IEEE 802.15.4g), it is possible to employ the centralized approach in mobile WSNs. In this sense, MNs would communicate with anchor nodes and these, having greater battery capacity, would execute algorithms to determine the location of MNs. However, for this to be possible, it is necessary to use special anchor nodes with greater processing power to run the centralized location algorithm and consequently batteries with greater energy levels.
Iterative algorithms apply the centralized approach using clusters formed by wireless nodes, creating sub-areas of location. Iterative algorithms are used by distributed algorithms to refine the initially determined location. For this, the iterative algorithms add more spatial information and distance measures between the nodes. We comment that the CoRPL+E mechanism uses the concept of Coronas, areas determined by the greater transmission range of the wireless nodes. We have seen that although RPL networks work in the DODAG structure, it is possible to create virtual cluster structures within the areas of each Corona. We add that iterative algorithms can be considered an option for distributed implementation of a localization system for the CoRPL+E mechanism in order to reduce the overhead of the centralized algorithms and the number of anchor nodes required for the distributed algorithms.
The mobility-assisted algorithms use mobile anchor nodes, equipped with GPS, that move along with the other MNs and use beacons to periodically emit their location to the unknown nodes. We realize that this type of architecture offers great benefits since mobile anchor wireless nodes can be nodes that have lower energy restriction (e.g. mobile robots), when compared with the other MNs in the network. In addition, we noticed that the localization process of MNs can be improved by moving the mobile anchor nodes in paths that facilitate the process of locating the unknown nodes. As commented, the CoRPL+E mechanism uses Coronas to divide the area of the network into sub-areas. As the MNs of the network have mobility, the sub-areas of the Coronas also are mobile. In this sense, one can use the mobility of the moving anchor nodes to move them strategically next to the area of each Corona, providing coverage of the location beacons for the largest possible number of MNs. We add that mobile anchor nodes can be represented by robots with few energy constraints and that can easily carry GPS devices to determine their own locations. We conclude that the mobility-assisted algorithms are an option for the implementation of a localization system for CoRPL+E mechanism.
Statistical methods use signal signatures, measured at points where previous signal measurements were performed. The signatures infer the location by exploring the relationship between distances and characteristics measured in the signals for a particular measurement point. These algorithms can work with the presence of noise and uncertainties of signal measurements. We note that statistical methods can be used mainly to detect the position of a node when it passes in points of the space in which previously signal measurements have already been made. Thus, there is a previous stored signature for that particular measurement point. In order to make it possible to identify the signature of the signals, it is necessary to have static wireless nodes in known positions that can be used as reference by the unknown nodes. We realized that this approach may require a large amount of static wireless reference nodes to provide signal signatures for all points in the space through which the MNs of the network can move. However, we also have noticed that SNs with greater communication range can transmit location beacons at a much greater distance when using, for example, the IEEE 802.15.4g physical layer. For this situation, it is noteworthy the feasibility of using statistical methods to provide localization.
Threats and preventions to RPL-based protocols
Security is one of the challenges to be addressed in IoT, with secure packet routing being a critical issue. In the context of RPL, hereafter we make a brief list of threats and preventive actions related to denial-of-service attack, black hole and gray hole attack, sinkhole attack, identity-based attacks, and wormhole attacks. 45
One type of threat to wireless networks, including those based on the RPL protocol, is the black hole and gray hole attack, the latter also called selective forwarding attack. 46 In this attack, the malicious node drops all or a portion of the packets it would forward. In this selective forwarding attack, for example, an attacker can forward all RPL control messages and discard all data packets. For the black hole and gray hole attack, Raza et al. 47 performed measurements of the amount of transmitted DIO messages, packet loss rate, and delay of packets in order to identify the attackers. The authors of the article proposed that a wireless node informs its neighboring nodes after detecting the malicious behavior, in order that the attacking node is placed in a blacklist.
Another type of threat is the sinkhole attack where the malicious node informs its neighbors that has a low rank value, in other words, that is near to the root node of the DODAG. In the case of the CoRPL and CoRPL+E protocols, the attacker could report a low Corona ID value. With this, the attacker’s neighboring nodes would choose the malicious node as PP. Finally, the malicious node upon receiving packets transmitted by neighboring nodes would discard such packets. To address this problem, Perrey et al. 48 proposed using hash chains to sign the DIO messages used to carry the rank information. In this approach, the receiving node of the DIO message is able to authenticate the message, verifying whether any node in the path has announced a false rank value. A similar approach can be employed in CoRPL+E to protect the protocol from the sinkhole threat.
One more type of threat to RPL-based networks is the identity-based attack. In this type of attack, a malicious node forges the identity of another MN in order to control and attack the network. One variant of the identity attack is the Sybil attack where an attacker forges several virtual copies of a single physical node. 49 CoRPL+E uses node positioning to perform routing. Thus, in CoRPL+E, it is possible to implement a mechanism to mitigate identity attacks by verifying the identity of the node that must be present only in a single position in the network.
In the wormhole attack, malicious nodes modify routing tables, creating a tunnel to deviate traffic from one location to another. With this attack, it is possible, for example, that attackers deviate traffic destined for the root nodes and then carry out the sinkhole attack concomitantly. CoRPL+E uses geographic information to determine the routing entropy. This geographic information when present in the routing tables and used in conjunction with traffic information can be used to identify this type of attack, as done in Wallgren et al. 46
Among the possible threats are denial of service attacks. For example, RPL-based protocol packets carry information such as the 1-bit O and R flags. The first flag indicates whether a packet is transmitted in downlink (value 1) or uplink (value 0) and the flag R indicates error in the rank of the transmitter or receiver nodes. An attacking wireless node may generate a loop, if upon receiving a packet, for example in uplink, set the O flag to 1 to indicate downlink and then forward the packet in the uplink direction. 50 In RPL, if the receiver node detects the loop, it will set the rank error R flag to 1 and then make a drop of the packet. These flag changes performed maliciously and at high frequency cause a reset of the trickle timer, resulting in a denial of service attack, due to the large number of control messages on the network. To work around this problem, RFC 6553 51 proposes limiting the amount of resets of the trickle timer to 20. When reaching this threshold, the inconsistent packets are discarded, without resetting the trickle timer. Taking this possibility into account, Mayzaud et al. 50 dynamically adjust the threshold of inconsistencies that cause reset in the trickle timer. In the proposal of Mayzaud et al. 50 the threshold is reduced proportionately to the aggressiveness of the attack and increases slowly when the attack is stopped. This approach is effective in reducing this type of denial of service attack and can therefore be used in networks based on the RPL protocol, including CoRPL+E.
Performance evaluation
The performance evaluation of the CoRPL+E proposal was performed by comparing the results of packet loss rate and average delay through simulation experiments, with variations of transmission rates, MN speed, and number of root nodes. The mobility model used is the Random Waypoint Mobility Model,
52
whose operation consists of choosing a random position for which the MN moves with random speed. The velocity is defined within the interval
Parameters used in simulation.

MNs: mobile nodes; UDP: user datagram protocol.
Evaluation scenarios
Table 3 presents the simulation parameters.
25
In each round of simulation, each MN originates packets destined to the root nodes, according to the transmission rate specified in Table 3. The simulations were performed in scenarios with 1, 2 or 3 root nodes. In the scenario with 01 root node, this was positioned at the point (250
In the simulations, we aim to answer the following research questions. Is it possible to use the CoRPL+E mechanism to reduce, in relation to the CoRPL mechanism, the packet loss rate and average delay of the packets transmitted from the MNs to the root nodes of an RPL network? Is it possible to reduce packet loss and the average packet delay in networks with MNs that transmit packets with different rates, move at different speeds, and even in scenarios where there are different amounts of root nodes in the network?
Results
The results were generated using the average of 100 simulation values with a confidence interval of 95%.
Figure 6 shows the results of packet loss with varying transmission rates of the nodes for CoRPL and the CoRPL+E proposal.

Packet loss rate obtained by fixing nodes’ velocity and with variation of nodes’ packet transmission rate: (a) CoRPL and (b) CoRPL + E.
Figure 6 shows the results of packet loss with variation of the node’s transmission rate for CoRPL and proposed CoRPL+E when we used 03 root nodes. The results demonstrate a decrease in the packet loss rate as the number of nodes increases. This behavior is expected because the larger the number of nodes in the same area, the smaller the distance between them, which results in better link quality. With this, nodes have more route choices. Comparing the graphs in Figure 6(a) and (b), one can see that the CoRPL+E proposal obtains lower packet loss rate values for 13 out of the 18 average values presented. The percentage of packet loss rate reduction in favor of CoRPL+E reached 27.45%, when the number of nodes is 100 and when the transmission rate of packets has a value of 10 pkts/min.
Table 4 shows numerically the packet loss rate values of the CoRPL and CoRPL+E mechanisms exposed in Figure 6. In addition, Table 4 presents
The

The
Figure 7 shows that, for both CoRPL and CoRPL+E, the average delay decreases as the number of nodes increases. Figure 7(a) and (b) shows an average delay reduction of up to 1.6 s in favor of the CoRPL+E proposal when the transmission rate is 30 pkts/min and when the number of nodes is equal to 80. The best results in favor of CoRPL+E are shown in Figures 6 and 7, since MNs tend to establish and maintain established routes for longer times before a route repair is needed in our proposal.

Packet’s average delay with fixed nodes’ velocity and variation of the packet transmission rate: (a) CoRPL and (b) CoRPL+E.
In Table 5, we verify that the results of average packet delay obtained with the CoRPL+E mechanism and presented in Figure 7 are, with the exception of one result that is in a cell painted in gray, lower than those obtained with the use of the CoRPL mechanism. For the result with exception, it cannot be affirmed that the average values obtained through the use of the mechanisms CoRPL and CoRPL+E differ at the level of significance of 0.05.
The
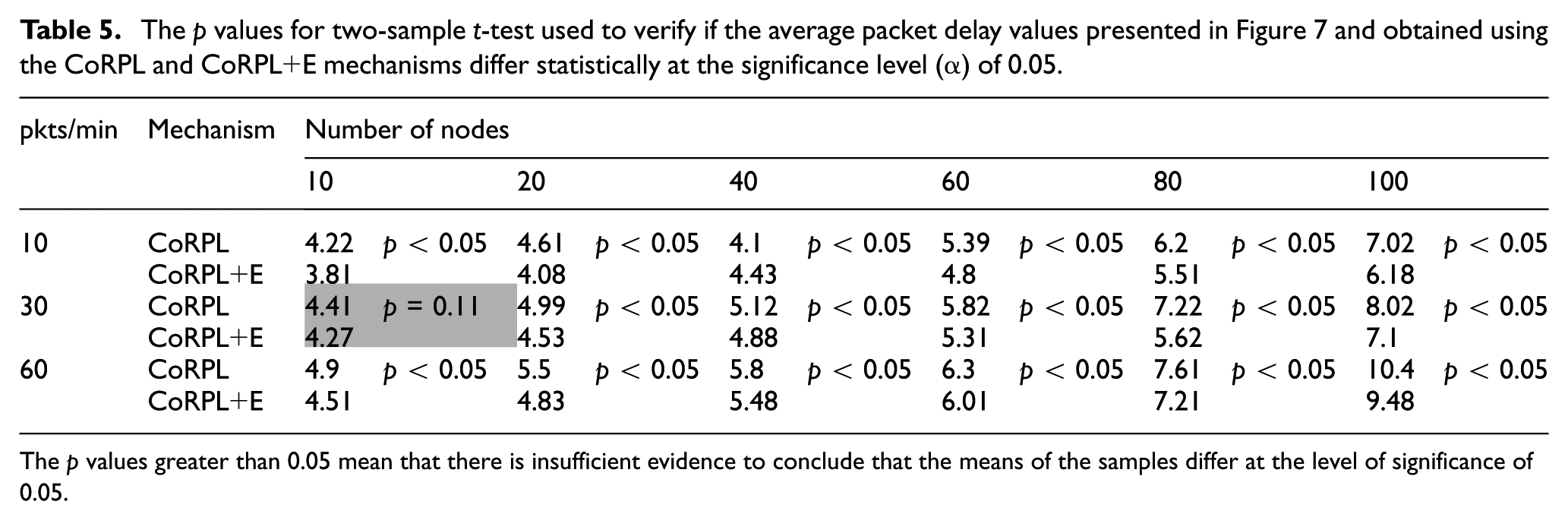
The
In Figure 8, we observe that as the velocity of nodes increases, the packet loss rate also increases for both CoRPL and CoRPL+E, since there is a greater number of link breaks between MNs and their PPs. Comparing Figure 8(a) and (b), we observe a reduction in the packet loss rate when using the CoRPL+E proposal. The reduction is around 50% when the nodes’ velocity has a value of

Packet loss rate obtained with variation of node’s velocity and fixing the packet transmission rate: (a) CoRPL and (b) CoRPL+E.
In Table 6, we show numerically the packet loss rate results of Figure 8. In the table, we find that the CoRPL+E mechanism, when compared to the CoRPL mechanism, obtained in most cases, lowers packet loss rate values. In 19 of the 24 average packet loss rate results presented in the table, the CoRPL+E mechanism obtained better results, with 95% confidence level.
The
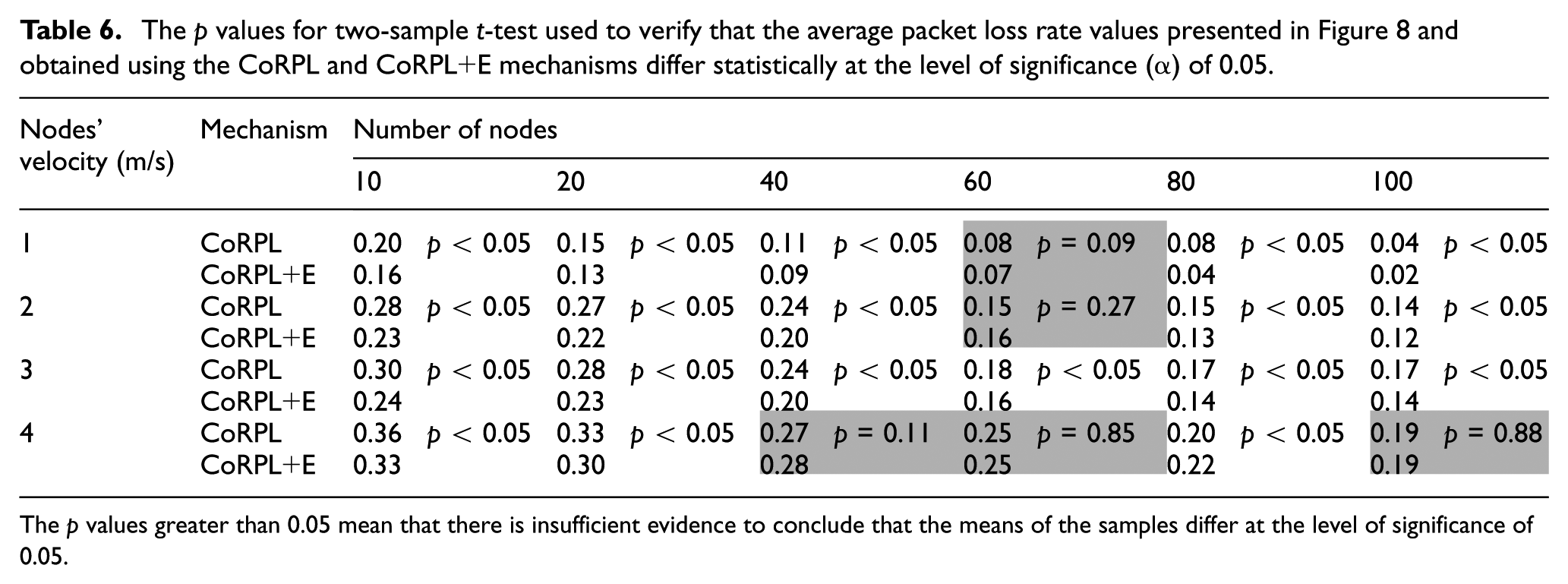
The
Figure 9 shows that the higher the velocity and the greater the number of nodes, the greater packets’ average delay is transmitted to the root node. This result occurs because as the node density increases, the distance between the nodes decreases and, consequently, the length of the links between the nodes decreases. With this, a packet goes through more hops when traveling from an MN to the root node, and both the CoRPL and CoRPL+E mechanisms do not consider the delay in determining routes. Figure 9 shows the average delay gains for CoRPL+E compared to CoRPL, for all number of nodes and all simulated nodes’ velocity values. For simulations with 100 nodes and nodes’ velocities of
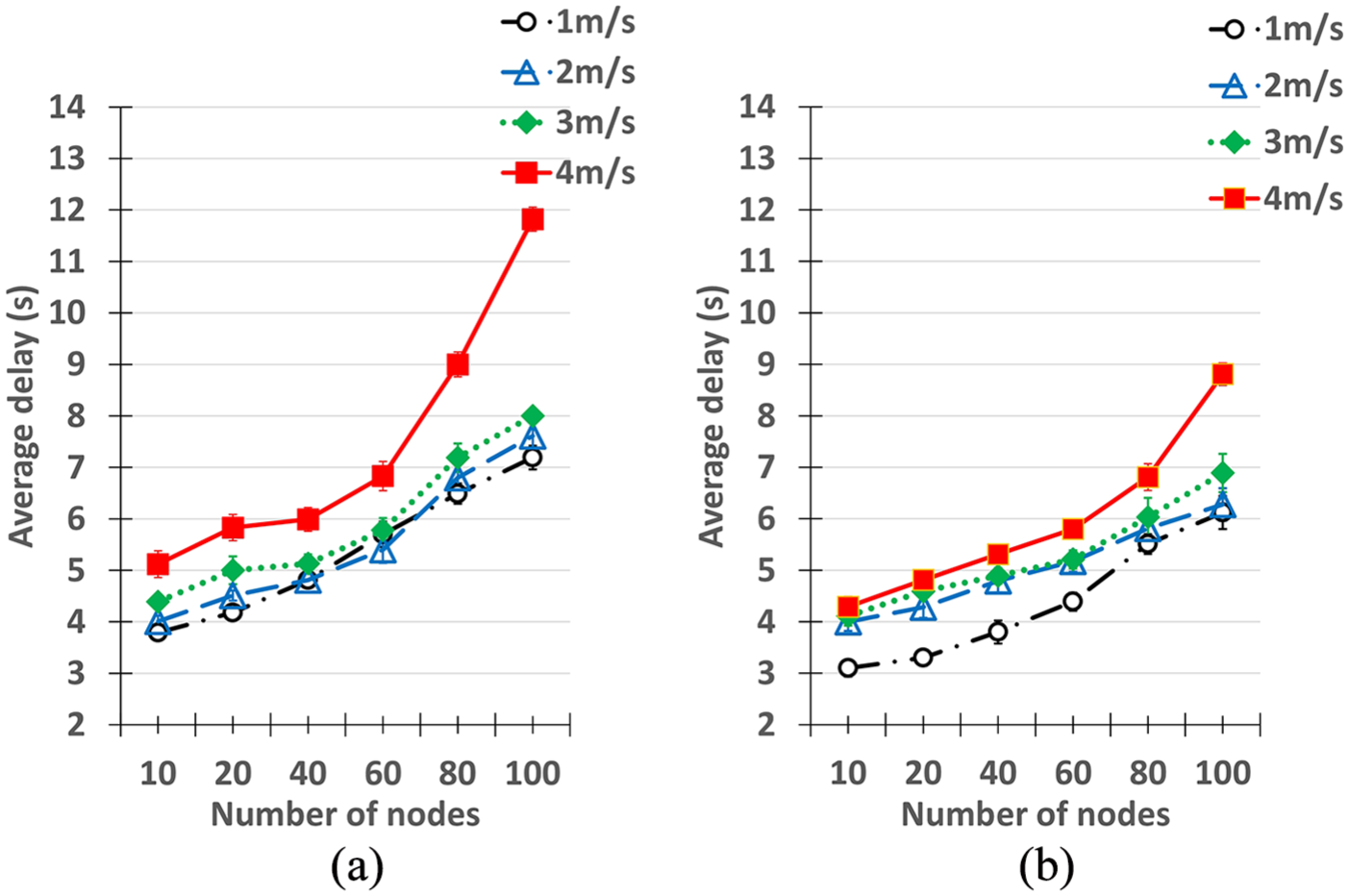
Average delay with variation of nodes’ velocity and with fixed packet transmission rate: (a) CoRPL and (b) CoRPL + E.
In Table 7, we present average packet delay values, shown in Figure 9. In this table, we see numerically that the CoRPL+E mechanism obtains lower average delay results when compared to the CoRPL mechanism in 21 of 24 of the values presented in Table 7. For three test cases, the results obtained when using the CoRPL and CoRPL+E mechanisms are similar and, therefore, it cannot be stated with 95% confidence level that the CoRPL+E mechanism got lower results than those obtained with the CoRPL mechanism, and vice versa.
The

The
In Figures 10 and 11, we vary the number of root nodes in the network by measuring the packet loss rate and average delay transmitted by the MNs when they are moving at a speed of

Packet loss rate with variation in the number of root nodes and fixed packet transmission rate and MNs’ speed: (a) CoRPL and (b) CoRPL+E.

Average packets’ delay with variation in the number of root nodes and fixed packet transmission rate and MNs’ speed: (a) CoRPL and (b) CoRPL+E.
Tables 8 and 9 present, respectively, the results of average packet loss rate and average packet delay presented in Figures 10 and 11. In addition, we present the results of
The

The
The

The
In Table 8, we see that the CoRPL+E mechanism obtained smaller values of average packet loss rate, with 95% confidence level, when compared with the CoRPL mechanism in 15 of 18 simulated test cases. In Table 9, we see that the CoRPL+E mechanism obtained smaller average packet delay values, with 95% confidence level, when compared to the CoRPL mechanism in 14 of 18 simulated test cases.
Conclusion
In this article, we propose the CoRPL+E mechanism that integrates mobility entropy into the CoRPL extension to reduce packet loss rate and average packets’ delay in simulated RPL networks that have MNs.
More specifically, the proposed mechanism includes an OF that uses Corona ID, mobility entropy, and link quality metric as criteria for an MN to select the PP of MNs. The use of mobility entropy as a criterion allows for the selection of more stable links with more lasting connections between an MN and its PP. This reduces the use of RPL repair mechanisms, thus reducing the packet loss rate and packet delay in the network.
The proposal was extensively evaluated using the Cooja simulator for WSNs. The results of the simulations of our CoRPL+E proposal were compared to the results obtained using the CoRPL mechanism, and the mechanism proposed in this article presented better performance.
For future studies, we suggest developing a protocol that uses iterative multilateration 40 for MNs to determine their positions, using a small number of MNs that are equipped with GPS system as a reference. 39 This mechanism can act alongside the OF that uses the mobility entropy to choose the best routes in the network.
In addition, we intend to validate the CoRPL+E proposal by testing its performance in real networks using the Contiki operating system and compatible sensors.
Footnotes
Handling Editor: Pascal Lorenz
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research was funded by SIDIA Institute of Science and Technology, by Coordenação de Aperfeiçoamento de Pessoal de Nível Superior (CAPES), by Fundação de Amparo à Pesquisa do Estado do Amazonas (FAPEAM)—support programs (Programa Primeiros Projetos (PPP) and Programa de Tecnologia da Informação na Amazônia (PROTI)-Amazônia-Mobilidade), by Câmara Técnica de Reconstrução e Recuperação de Infraestrutura (CT-INFRA) of Ministério da Ciȇncia, Tecnologia, Inovações e Comunicações(MCTI)/Conselho Nacional de Desenvolvimento Científico e Tecnológico (CNPq), and by Secretaria de Estado de Ciȇncia, Tecnologia e Inovação - Amazonas (SECTI-AM) and Government of Amazon State, Brazil.
