Abstract
Toward the goal of high security and efficiency for data collection in wireless sensor network, this article proposed an adaptable secure compressive sensing–based data collection scheme for distributed wireless sensor network. It adopted public key cryptography technology to solve the key distribution problem, and compressive sensing over finite fields to reduce the communication cost of data collection. Under hardness of decisional learning with errors problem on lattice, it can ensure indistinguishability against chosen ciphertext attack (IND-CCA1) security scheme for collected data on the extranet and indistinguishability against chosen plaintext attack security for data during the process of distributed collection on the intranet. Owing to the similar linear structure for lattices and compressive sensing, data encryption collection can be all in the form of efficient linear operations, and internode data aggregation can be in the form of addition operation.
Keywords
Introduction
Background
Wireless sensor networks (WSN) is considered as a bridge between human society and physical world. It is deployed for collectively monitoring and disseminating information about various interesting phenomena. In a large-scale network, data transmissions are usually fulfilled through multi-hop routing from individual sensor nodes to the sink node, which causes a lot of redundant transmissions. Therefore, it increases the cost of network communication. The basic data collection scheme in WSN is shown in Figure 1. 1

Basic data collection scheme in WSN.
For
Remarkably, nodes that are closed to the sink will transmit more data and consume more energy than those outside the network. The out-off-balance energy consumption has a substantial impact on network lifetime.
Compressive sensing (CS) is a novel sensing paradigm that goes against the common wisdom in data collection. 2 Compared with the traditional theory, CS theory shows that one can recover sparse data from far fewer measurements or samples and thus reduce the data collection cost and prolong the lifetime of WSN.
CS-based data collection is now wildly used in WSN for data compression and linear structure. It can be depicted in Figure 2. 1
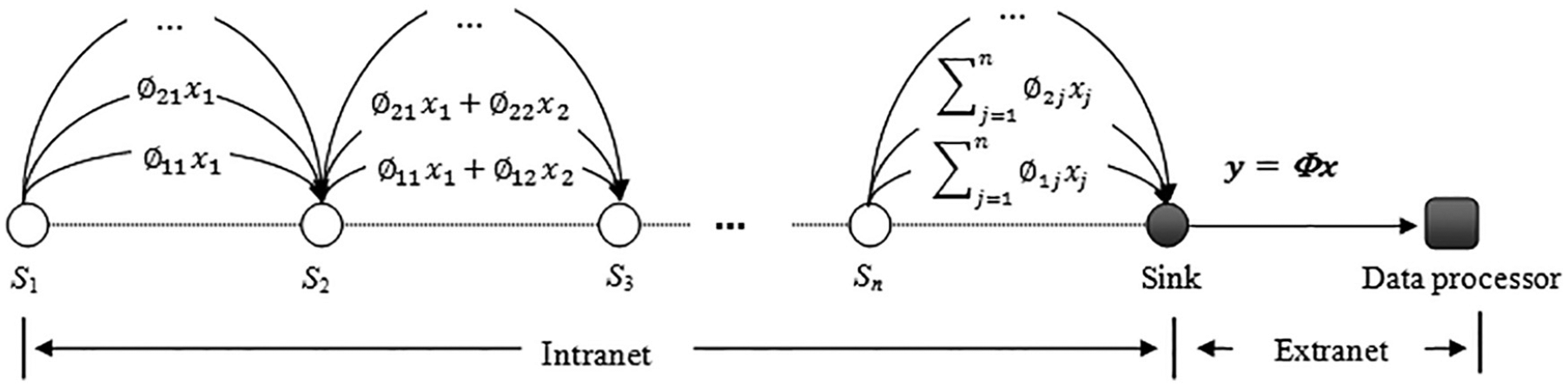
CS-based data collection schemes in WSN.
More concretely, let

In intranet of WSN, for
At present, WSN is widely used in many fields. In addition to energy issue, the necessity for security of data in transit becomes very crucial factor. Although CS-based data collection scheme can reduce the data collection cost and prolong the lifetime of WSN, 3 it does not consider the existence of adversaries in the network and therefore cannot protect the security of data. Thus, to construct a secure CS-based data collection scheme for WSN is a very significant work.
Previous works
To solve security challenges for CS-based data collection scheme, a feasible method is to let measurement matrix be a symmetric key, which is just known by both encrypted and decrypted parties. This ideal was formally studied in RB08, 4 who regarded an original signal to be sampled as plaintext and its random measurements as ciphertext. We called it as compressed sensing symmetric encryption (CSSE). In their security model, only the encoding result is accessible to the adversary (both the measurement matrix and signal cannot be accessed to the adversary), which means their conclusion is based on a ciphertext-only attack model. By employing a random Gaussian sensing matrix updated at every time encryption, BBM14 5 and BBM16 6 showed that the cryptosystem with the one-time sensing (OTS) random Gaussian matrix could be perfectly secure. The basic idea of the above scheme is to ensure the security of the system by using “one-time pad,” but it costs too much to update the key each time. From the practical point of view, YYN17b 7 employed a secret bipolar key-stream and a public unitary matrix, which could generate and renew the key-stream at each encryption in a fast and efficient manner. They demonstrated that the entries of the sensing matrix were asymptotically Gaussian distribution if the plaintext length is sufficiently large, and this cryptosystem could achieve the security of indistinguishability against chosen plaintext attack (IND-CPA) if each plaintext had constant energy. Previous security analyses of CS are based on the OTS hypothesis (i.e. the secret key/measurement matrix is used only once). CM18 8 studied a CS-based asymptotically Gaussian one-time sensing (AG-OTS) cryptosystem for secure wireless communications. HXC14 9 pointed out the CSSE was not secure enough without OTS assumption. However, due to the complex deployment environment of WSN, CS-based data collection schemes still face security threats, poor efficiency and impracticality.
In typical CS-based data collection scheme of WSN as Figure 2, the data collection, encoding, and aggregation are processed at each node in a distributed model, while the data recovery is accomplished at the sink independently according to measurement results received from other nodes. The sink shares the measurement matrix with each sensing node, respectively. To achieve OTS, the measurement matrix (secret key) should be stored in each node and synchronously updated in each measurement cycle. This may face several challenges. First, it enormously increases the cost of communication. Note that the size of the measurement matrix (
To improve security and practicality of CSSE-based data collection schemes in WSN, PSK18 3 present a secure data collection scheme based on compressive sensing (SeDC) by introducing an additive homomorphism encryption mechanism to enhance data confidentiality. In SeDC, the intermediate nodes can aggregate data directly in the ciphertext domain without decrypting the received data, which means the private key is not necessary to be stored at the intermediate nodes, thus the security is guaranteed.
More specifically, SeDC used a homomorphic encryption function HE to encrypt the

SeDC in PSK18.
Although by combining public key cryptography with compressed sensing, PSK18 solved the key distribution and storage problem of CSSE-based data collection schemes in WSN, there are still some imperfections in terms of efficiency and security.
First, homomorphism encryption function HE usually requires plaintext space to be a finite set, but
Second, intranet networks are usually more trustworthy than extranets, IND-CPA security would be sufficient in practice to preserve confidentiality for data on the internal network, but it needs higher security for data on the extranets, especially for some military data. PSK18 just achieves IND-CPA security both for inside attackers and for outside attackers. When data are transmitted to data processors through an external network, it is necessary to re-encrypt the data using a higher secure encryption scheme, for example, an encryption scheme with indistinguishability against chosen-ciphertext attack (IND-CCA1 or IND-CCA2) security.
Third, the expansion of ciphertext and computational efficiency are contradictory in homomorphism encryption. Additive homomorphism schemes 10 with low expansion usually contain large number of time-consuming exponents or bilinear pairings operation and cannot resist quantum attack.
From the aspect of computational efficiency and quantum attack resistant, lattice-based homomorphic encryption may be a good choice. Although lattice-based encryptions usually have large ciphertext expansion, compressed sensing can greatly compress the data for very sparse data. It can compensate for data expansion of lattice cryptography.
Linear structure of lattice-based cryptography is very similar to CS and has been recognized for its many attractive properties, such as strong provable security guarantees and apparent resistance to quantum attacks, flexibility for realizing powerful tools and high asymptotic efficiency (usually requiring only linear operations on small integers).
LHY18 11 solves the problem of combining CS with a lattice-based homomorphic public key cryptography by using CS in finite field and constructed an instantiated data collection scheme based on lattice. But LHY18 still can only protect IND-CPA security for data on the extranets.
Our contributions
In this work, we construct a CS-based data collection scheme that can resistant quantum attack and preserve IND-CCA1 security scheme for data on external and IND-CPA security on intranet. By combining an IND-CCA1 secure public key encryption scheme in MP12 12 with CS, we first constructed a CS-based public key encryption scheme (remarkably, we just take CS as a black box, which makes the application of our scheme more general) and proved IND-CCA1 security under hardness of learning with errors (LWE) problem on lattice. Then using some tips, we show how to use this new scheme to secure data collection on distributed WSN. We adopted the method in PSK18 to solve the key distribution problem in WSN with public key and also use CS in finite field as shown in LHY18 to solve the problem of combination of public key and CS. Since lattices and CS have similar linear structures, we use some tips to achieve ciphertext additivity of our new scheme. Furthermore, we proved that the piecewise ciphertext of each node can preserve IND-CPA security of the data on intranet networks; thus, each node completes the secure data collection during the transmission process.
Preliminaries
Notation
We denote the set of real numbers by
Over a finite or countable domain
For any basis
Sub-Gaussian distributions and lattices
Definition 1
For any

The subscripts
Definition 2
For

As above, we may omit the parameters
If for

We say the random variable
Notice that the
Definition 3
For any
Lemma 1
For a lattice
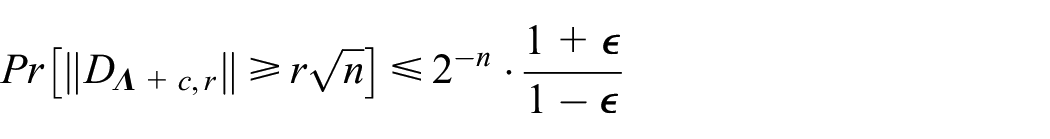
When
Lemma 2
For a lattice
Theorem 1
For any positive integer
Proof
For
Decisional LWE problem
For
The decisional
The hardness of decisional
Trapdoor for lattices and algorithms for inverting LWE
MP12 12 defined a new trapdoor, given a method of inverse LWE, and established some of important properties as follow.
Definition 4
Let
For our construction, we define an algorithm
Definition 5
Efficient algorithm
Pick
Output
Statistical instantiation
For any parameter
For example, let
Algorithm 2 in MP12 shows an efficient algorithm
MP12 also gave a detail construction of
Compressed sensing over finite field
Let
Sparse representation of signals
Set signal
Selection of measure matrix
If signal

where for
DM09
16
pointed out that a necessary condition for the successful recovery of all
In our scheme, we just consider the condition with
Definition 6
Let
Reconstruction of signals
Reconstruction of signals can be described as to reconstruct signals
Definition 7
Let
CS-based public key encryption and security definition
The CS-based Public Key Encryption (CSPKE) is defined as follows:
Definition 8
A CS-based public key encryption scheme is quadruples of algorithms (
Moreover, a further fundamental property is required: correctness. We want that, for any pair of public and secret keys generated by
Our CSPKE is IND-CCA1 secure for outside attackers and IND-CPA secure for inside attackers in distributed application. Next, we define IND-CCA1 security of CSPKE and IND-CPA security of CSPKE-D (we use CSPKE-D to express the scheme of CSPKE for distributed application) according to NYP 20 as follows.
Definition 9
IND-CCA1 security is defined by the interaction experiment between challenger C and attacker A.
Challenger C runs
When A makes a sequence of decryption query to C, for each decryption query, A submits a ciphertext
A chooses two signals
C randomly selects bits
A outputs
The advantage of attacker A to attack the above encryption algorithm is defined as

The CSPKE Algorithm is IND-CCA secure if for all probabilistic polynomial time (PPT) adversaries the advantage
Definition 10
IND-CPA security is defined by the interaction experiment between challenger C and attacker A.
Challenger C runs
A chooses two signals
C randomly selects bits
A outputs
The advantage of attacker A to attack the above encryption algorithm is defined as

The CSPKE-D scheme is IND-CPA secure if for all PPT adversaries the advantage
Compressed sensing public key encryption scheme based on LWE
The concrete scheme
We give some exemplary asymptotic bounds for a number of parameters involved in our scheme. In the following, we used
Let
For prime power
The error rate in LWE is express by
We need a special collection in the ring
For measure matrix
Runs algorithm
For parameters
Outputs public key
Chooses a nonzero
Chooses a vector
Computes
Outputs the ciphertext
Let
If
If
Let
Runs the algorithm
Analyses
Correctness
Theorem 2
The above scheme has only
Proof
Let
For arbitrary

Specially, for large enough
IND-CCA1 security
We will prove the security of above-described scheme.
Theorem 3
The above CSPKE scheme is IND-CCA1 secure assuming the hardness of decision-
Proof
Let
For signal
The encryption scheme in MP12 is IND-CCA1 secure assuming the hardness of decision-
A CS-based adaptable secure data collection scheme for WSN
Now, we show how to use CSPKE to implement a CS-based data collection scheme for distributed WSN that is IND-CPA secure for inside attackers and IND-CCA1 secure for outside attackers.
Although CSPKE scheme itself does not have additive homomorphic property, if we fix the first partial ciphertext
The main steps are summarized as follows:
Setup
The system first initializes the network, and for parameter
Encryption measurement and in-network aggregation
Let
Finally, the sink received encrypted measurement value
Let
The detailed process is shown as Figure 4.
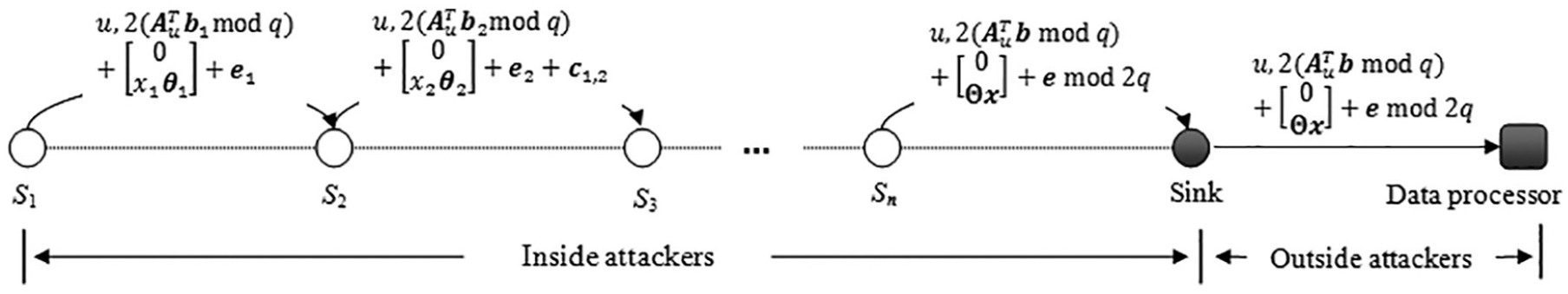
CS-based IND-CCA1 secure data collection scheme in WSN.
3. Data recovery
The data processor runs algorithm
Security analysis
As can be seen from the above description, the collected data
CSPKE scheme itself does not have additive homomorphic property. In order to implement a distributed data collection, we share the first partial ciphertext
Theorem 4
Our above CSPKE-D scheme is IND-CPA secure for inside attackers assuming the hardness of decision-
Proof
For inside adversaries, the first partial ciphertext
For the distinguisher, we are given
Prepare the public key
The simulator runs the key generation algorithm
For a gadget matrix
Outputs public key
Prepare the challenge ciphertext
When the adversary chooses
By Theorem 3.1 of Pei10
21
we can transform its samples
As we see from the adversary’s view, when the input to the simulator comes from an LWE distribution
Efficiency analysis
Considering from the computational efficiency, our above scheme just involved simple some linear operations, which are very efficiency on computation. It is worth noting that we take CS as a black box, thus the method used measurement sparse matrix for CS in PSK18 can also be used in our scheme to further improve computation efficiency. Next, we mainly analyze the communication efficiency.
Our scheme can be described as a public key encryption scheme to CS. In detail, original data
For a more intuitive description, we follow give a theoretical traffic comparison of related schemes in Table 1.
Comparison of related schemes.

CS: compressive sensing; IND-CPA: indistinguishability against chosen plaintext attack; IND-CCA1: indistinguishability against chosen ciphertext attack.
In Table 1, we assume that the lengths of input signal to these schemes are all n bits, and we use “Ciphertext” to represent the corresponding lengths of the outputs (theoretical traffic). For the line of ciphertext expansion, it means the ratio of outputs to inputs. Assuming that the outputs of CS scheme (who is the basis of PSK18, LHY18 and our CSPKE-D) are
Next, we analyze theoretical communication load of our above scheme in comparison with related schemes in detail.
Compared with the original CS scheme, the increased communication load of our scheme mainly comes from ciphertext expansion. According to MP12, we have
In order to facilitate the comparisons, from the aspect of quantum attack resistant and computational efficiency, we assume the homomorphic encryption scheme used in PSK18 is a lattice-based homomorphic encryption.
Furthermore, LHY18 can be seen as a concrete scheme of PSK18 by using a specific lattice-based additive homomorphism encryption scheme. Thus, PSK18 and LHY18 have a similar ciphertext expansion from the perspective of quantum attack resistant. As can be seen from Table 1, The ciphertext expansion of our scheme is only a little larger than that of LHY18 (note that |ℜ| is much smaller than
In terms of security, the size of
However, CS data compression rate is proportional to data sparsity. For
Conclusion
The security issues of data collection in WSN have attracted great attention from academics and industry. In this article, we mainly focused on the security among data collection and transmission process and proposed an IND-CCA1 for extranet and IND-CPA for intranet secure CS-based data collection scheme. The security of our scheme is based on the hardness of decisional LWE problem, to which there is no known effective quantum algorithm. In terms of computational efficiency, our scheme only contains simple linear operation, so it has high computational efficiency. In terms of communication efficiency, although CSPKE-D algorithm brings a little of data expansion, CS realized a good communication cost compensation by data compression, which makes our scheme practical in WSN.
Footnotes
Handling Editor: Weizhi Meng
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by National Natural Science Foundation of China (Grant Nos 61572521, U1636114, 61772550), National Key R&D Program of China (Grant No. 2017YFB0802000), National Cryptography Development Fund of China (Grant No. MMJJ20170112), Innovative Research Team in Engineering University of PAP (KYTD201805), State Key Laboratory of Information Security (2017-MS-18).
