Abstract
Smart home environment comprises high-capacity and low-capacity sensors. These sensor nodes interact with daily activities of users and they communicate with each other to perform particular tasks. A set of instructions in insecure network during communication can result in a deadlock due to attack of adversary. Such deadlocks can be a severe risk for the security of user’s activities in smart home environment. Recent critical security attacks in smart home environment exposed that how communication channels turned low-capacity sensors into harmful attack for illegal activities which later lead to damage security and privacy. Therefore, a suitable framework is needed to overcome security pitfalls and to protect user’s activities by establishing secure key session between sensor nodes. This study has proposed new
Introduction
The popularity of smart home environment (SHE) has been increased in the last couple of years. SHE is basically a combination of low-power, low-cost, and sensor nodes which are installed over the specific region. The infrastructure of SHE could be heterogeneous which consists of different competences. 1 Our previous work in lab, 2 activity pattern knowledge mined from trajectories, described that automation is very important and possible when all the things are connected to each other virtually in SHE. Such types of SHE are combinations of appliance control system, smart energy system, multimedia system, light and flame control system, security and surveillance system, climate handling system, and home care system and these appliances take instructions from daily living activities (DLAs). 3 In several countries, many research projects have started to make the ideal SHE, for example, GENIO (next-generation home),4,5 SM4ALL (smart home for all), 6 and HOPE (a smart home for the old living people)7–9. Basically, smart homes combine with a large number of heterogeneous smart nodes and devices, such as smart light, actuator, smart surveillance digital camera, smart window shutter, thermostat, and many other types of devices which can be integrated, as shown in Figure 1. Design model of SHE is divided into four types of entities: (1) gateway, (2) nodes, (3) server, and (4) users. The sensor nodes are responsible to sense the users’ activities and forward these data to nearby local gateway. Then, local gateway is responsible to forward these data to server securely as shown in Figure 1. During our recent research in lab, we came to know that many security challenges (e.g. denial-of-service (DoS) threat, replay attack, masquerade attack, message forgery attack, and device-compromised attack) are existing in SHE due to the improper security level.10,11

Smart home environment.
Research contribution and motivation
In this article, we have assumed that SHE is a network of heterogeneous sensor nodes and these nodes sense the data from users’ activities and forward instructions to nearby devices like smart home local gateway (SHLG) so that users can access data and fulfill their objectives. SHLG works as a link between user and nodes. After sensing users’ activities, sensor nodes transmitted a message through insecure networks and adversary can insert, intercept, change, re-route, and delete the original communication message. Therefore, a number of security features such as message integrity, authentication, and protecting data of users’ activities are primary concerns of such type of network in SHE.
A secure seamless key session between the nodes involved is necessary to provide secure communication trajectory over insecure channel where authentication and anonymity are highly important. Many methods12,13 experienced to achieve authenticity of smart home nodes (SHNs) but oversaw other properties of security. Petroulakis et al. 14 and Burrough and Gill 15 discussed how poor security of networking protocol can be mistreated to handle the SMNs, so that it breaches the security of SHE. Most of the previous research works16,17 focused on authentication and none of them considered how to hide identity of SHNs. SHNs interact with daily activity pattern of users and then perform the tasks accordingly. If any device (e.g. surveillance camera and temperature control device) compromises with adversary, then it damages the security as well as privacy of users’ daily activity in SHE. Therefore, we preliminarily designed a secure distributed framework (SDF) suitable for SHE, basing upon on token authentication and seamless key session, for sensing the real-time data of sensor nodes and forward to nearby gateway and server after encryption, which resists the above-mentioned security attacks. Furthermore, the proposed scheme is better than the existing protocols as its uses distributed framework in order to keep the system secure and functional in case of any attack and by avoiding deadlock condition. Moreover, the proposed scheme uses activity recognition model to detect any kind of abnormal activity in SHE.
SDF proposed in this article meets the following facts:
The rest of the article is prepared as follows. In section “Review of related work,” we discuss the most recent research studies that are related to this research. Section “Design model, security properties, and threat assumptions” presents the structure of system design model and properties of security model. Section “Proposed SDF” presents the proposed SDF and all its notations. Section “Security verification and performance analysis of SDF” discusses experiments and results and verifies effective performance analysis of proposed SDF. In section “Conclusion,” we discuss the conclusions.
Review of related work
A few research studies have been published on security issues of SHE. These studies proposed schemes to protect communication from unknown attacks and threats. Previous research did not consider security issue regarding daily behavior activities’ recognition of users in smart home. Every scheme has its advantages and disadvantages. However, in this article, most recent research works are conferred.
Kumar et al. 17 claimed that the scheme is lightweight and established secure connection based on key-session process. During offline, secure key session is established after sharing a short authentication token to verify and legitimate smart nodes. However, schemes did not consider the anonymity to secure the identity of nodes and also did not provide activity recognition approach to distinguish abnormal activity. Kim et al. 3 suggested a process of seamless integration for heterogeneous nodes of smart home and access control. The proposed scheme described the open-service gateway initiative (OSGI) and also suggested a smart home for heterogeneous protocol in home area network (HAN). They described that access control model manages different user’s request along with authentication and authorization. In their architecture, the restful web services provided the remote access in SHE. However, this method did not provide solution for authentication of nodes during deployment time in smart home. Vaidya et al. 18 described a mechanism of smart energy for authenticity of devices in HAN. This scheme used the elliptic curve cryptography (ECC). For communication between two devices, a key session is established and then message is propagated over the channel. They claimed that their scheme is more effective and efficient. However, analysis of the security level of the scheme is not provided in detail. There is also not enough detail that how their scheme is more efficient than others.
Hoang and Pishva 19 described a new communication pattern to secure the appliances of smart home which is totally Tor based and the scheme uses public key approach for cryptography which is not suitable for resource-constraint devices. 19 Tor is used as an Internet browser by various users. This anonymous browser is operated only where surfing actions are performed. Moreover, authentication is not performed. Ayday and Rajagopal 20 observed that the existing technologies (e.g. ZigBee, Insteon, and Z-Wave) of HAN are suitable for security in smart home only up to a certain level. They proposed a new mechanism which is based on three different secure authentication mechanisms: (1) there should be authentication mechanism between gateway and smart meter, (2) there should be authentication between the HAN and smart appliances of smart grid, and (3) HAN and the transient devices should also have performed authentication. However, to perform the authentication process between two nodes, the scheme depends on the Internet service provider. The proposed scheme totally depends on the third part. In the work by Chen and Luo, 13 a secure smart household framework is proposed for appliances as a secure mechanism. The main focus of authors in this scheme called S2A is about usability, operation protection, and controlling the electricity prices of devices. S2A does not consider the fundamental properties of the security (i.e. confidentiality, authentication, and integrity of data). Moreover, the framework of S2A may not withstand the Dolev–Yao model which is a model of collaborative adversary. 21
Kumar et al. 22 proposed an anonymous secure framework (ASF). This scheme focused on anonymity, unlinkability, authentication, and integrity of devices in smart home. A key agreement and mutual authentication are required in this scheme which fulfills the cost of computation complexity. However, this scheme did not discuss about security in terms of DLA recognition pattern and how to make sure devices are faceless for security attacks at initial time to secure the DLAs. Another drawback of this scheme is that it stores on static devices. Li 23 proposed a scheme for smart home energy management system based on ECC. A key establishment protocol was designed and this scheme is based on two units: (1) a node and (2) security manager. A public and private key is distributed between entities through a trusted authority. However, operations of public key are not cheap for sensors because of time complexity. Moreover, security analysis is very limited.
Design model, security properties, and threat assumptions
Design model
SHNs play various key roles of security surveillance such as smoke detection alarm, temperature sensor, light control, flame detection, and home gateway 24 , as shown in Figure 2. In the work by Liang et al., 25 wireless channel has used HAN protocol (e.g. ZigBee) for communication of SHNs to SHLG. This type of communication pattern is named as SD-To-HG. 26 Basically, design model of SHE is a combination five major units which are shown in Figure 2.

Simple design model of SHE.
SHLG
SHNs are connected to SHLG and users collect information from SHLG. SHLG works as a router among users, SHNs, and server SSP (security service provider). Basically, SHLG communicates among different devices in smart home. It has the following functions: (1) it provides short-range wireless platform (e.g. 802.15.4) which facilitates connection within the internal SHNs and (2) works as a platform of communication to connect the outer world through Internet IPv4/IPv6. 27
SHNs
SHNs comprise
Security service provider/control system
The security service provider/control system (SSP/CS) provides various services to the SHNs and SHLG. It is a trusted server and it manages to assign the authentication services to SHLG. It also provides the secret key material to both SHNs and SHLG.
Internet (IPv4/IPv6)
It enables the smart home gateway to provide and operate the internal nodes with outer world through the connectivity of Internet (IPv4/IPv6).
Users
The end users can monitor and operate the internal functionality through the SHLG and its services. Users can also remotely or directly interact with appliances through internal short-range wireless channel.
Security properties
Internal design model of SHE consists of various heterogeneous nodes (LCS and HCS) and it requires various basic security properties. Security properties have been identified in recent research works24,25 that should be noticed in the internal networking of SHE. Our proposed SDF will cover these properties which are discussed as follows:
Assumptions
In this section, we describe some widely accepted important assumptions:
Secure service provider server (SSP) develops a safe environment with SHLG which senses activities of users and shares secret information to SHLG. Both SSP and SHLG have better memory in comparison with other devices in smart home, for instance, biometric detector sensor. Consider that both are temper proof and have good limitations of resources. SSPs have capacity to consider and store static and dynamic nodes, with attributes of key session.
SHLG and SSP are connected to each other through secure channel. Both have symmetric cryptographic method which is composed of encryption, decryption, and lightweight hash function. Asymmetric cryptographic method is not supported by low-capacity nodes in smart environment. 30 Therefore, low-capacity sensors are at higher risk of being attacked in SHE in comparison with HCS.
The scheme of Li et al. 30 is utilized to synchronize the clocks of all the nodes of smart home (i.e. SHNs and SHLG).
An adversary may eavesdrop between nodes which are involved over the insecure channel. It is also supposed that an adversary cannot interrupt the transmitted message in secure channel.
Threat model
We present threats and their widely accepted assumptions concerning threat and attack model as follows:
We follow the Dolev–Yao attack model, 21 where adversary is able to insert new message and spoof other identities or change message. Moreover, adversary might be able to get illegitimate data access to perform denial of service or service degradation. A complete protection against such types of attacks is integrally very challenging. However, the least requirement is the detection and protection mechanism which must be incorporated.
An adversary can delete, modify, re-route, and resend the eavesdropped data.
An adversary may legitimate device or vice versa.
Attacker can manipulate user’s activity pattern and can create abnormal activities resulting in damaging security of SHE.
Proposed SDF
This research is an extension and continuity of our previous research work.10,11 In this section, an SDF is proposed to protect the transmission in smart home architecture (SHA). SDF is based on key distributed session and mutual authentication phase to establish a secure trajectory. Proposed SDF is described in this section.
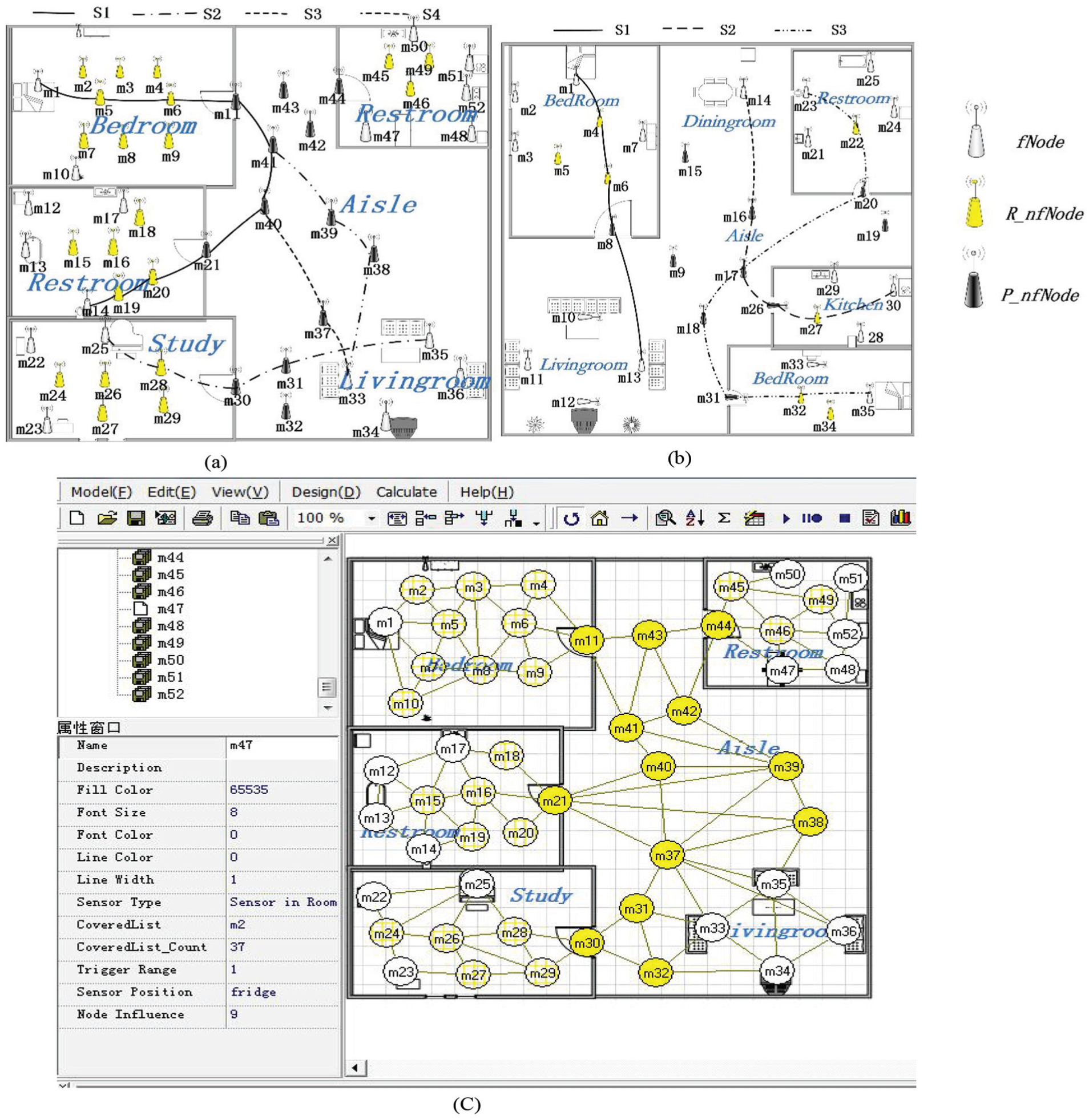
Notations, pre-deployment, and registration phase
In this section, all the notations, used in the SDF, are described in Table 1. Furthermore, in pre-deployment and registration setup of proposed SDF, network administrator is executed and run offline using setup server. Each regular sensor node, at the time of deployment, is pre-defined and labeled as
Notations and their description.
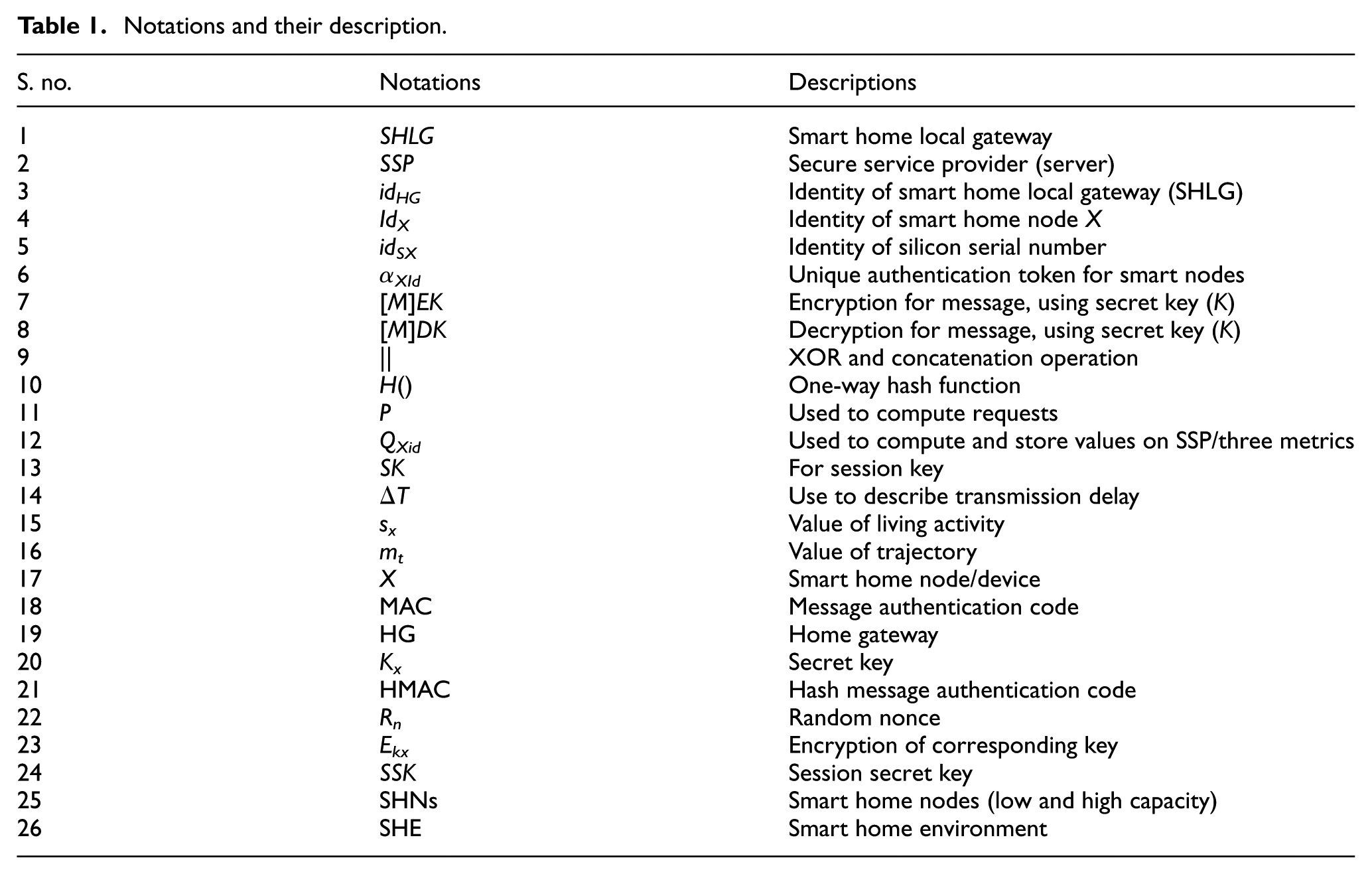
SCS
All SHNs should be configured and listed in SSP by a system administrator (SA) while staying offline. All devices acquired secret credentials from SSP and it computes the following key edifices as shown in Figure 3. In addition, SSP also stores the SHLG identity
Key-session steps of SDF for cryptic link setup: (a) scheme setup and (b) session key establishment for secure communication.
After this, SSP stores
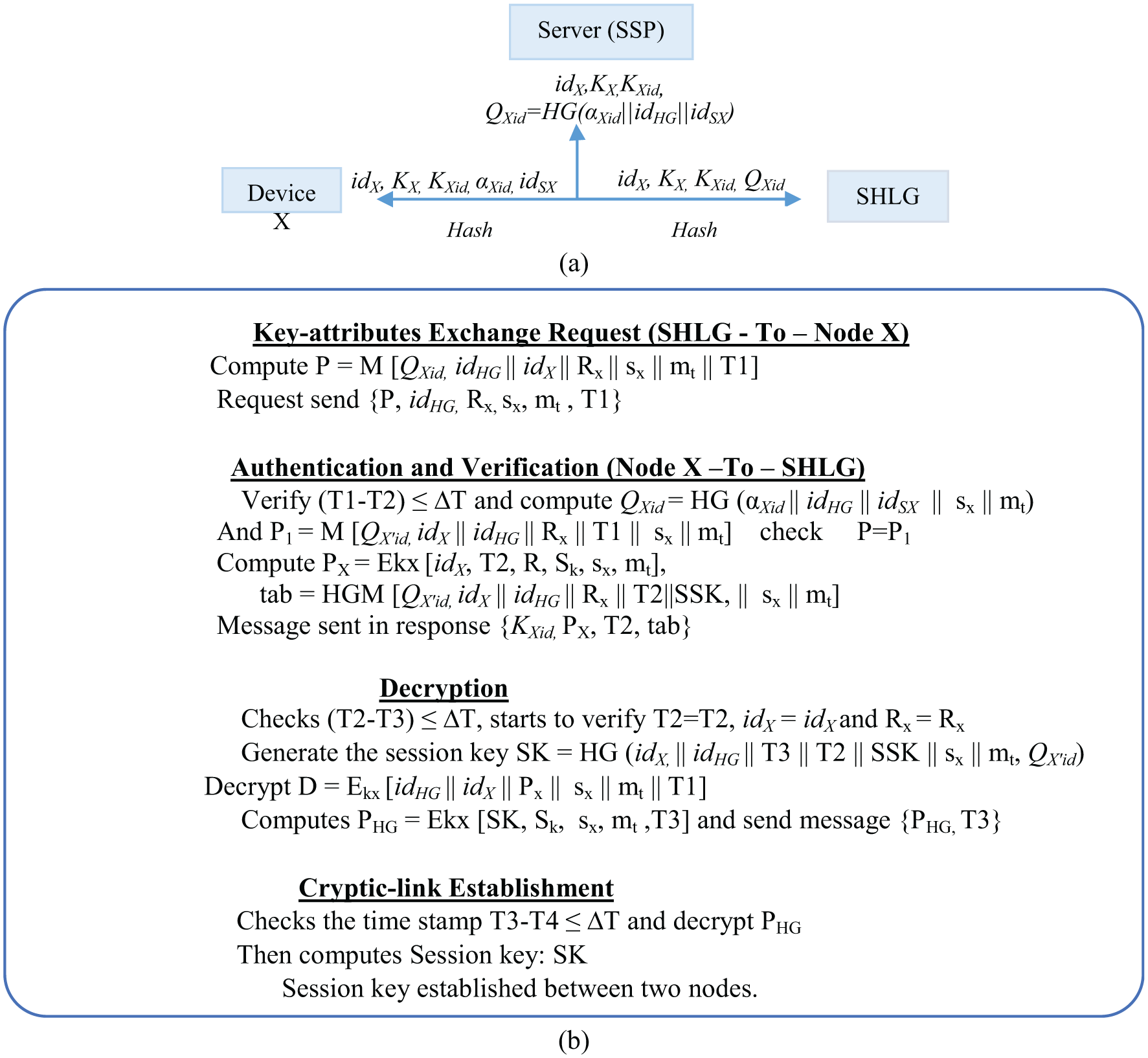
Time stamp frame of incorporated activities.
Terminologies and approaches which are used in our proposed SDF are discussed in the following sections.
Distributed approach
Distributed approach is used to keep trajectory functional during attacks in SHE by avoiding stalemate condition.
Definition
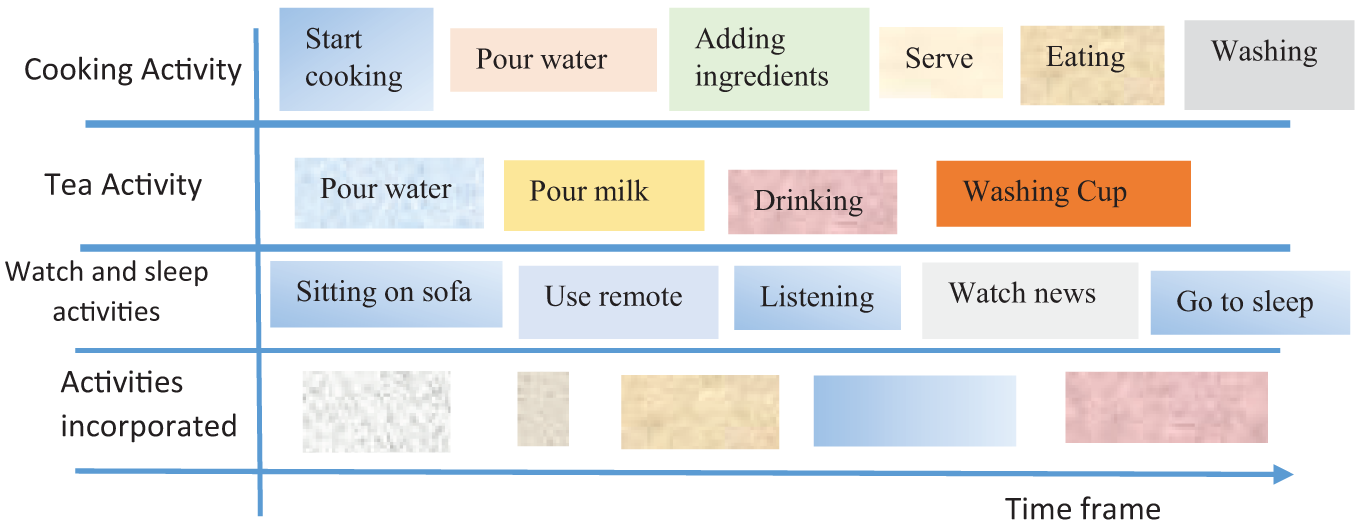
“Using distributed approach, each sensor performs encrypted process on their own end by utilizing key-session attributes of proposed scheme which is shared on trajectory by the service provider server unit to avoid deadlock condition as shown in Figure 5(c).” Actually, sensors of SHAs coordinate and detect the daily living behavior activities of individuals to perform various tasks. For example, if a person goes to kitchen for cooking breakfast, then the sensors of the kitchens become active to stimulate and send behavior activity to the main server. Each sensor device has its own capacity for computation process of appliances, which is basically support to distributed scheme, and interacts with each other to recognize a common task. To detect this kind of blockage which is created by abnormal activity/command, by keeping rest network functional, it is necessary to launch an SDF, which is based on seamless key-session process as mentioned above, and is demonstrated in Figure 3.
(a) Sensor devices and trajectories layout for encryption, (b) person’s behavior pattern layout of the new environment interaction with smart home’s nodes (LCS and HCS), and (c) distributed trajectories mode avoiding deadlock.
User’s activity recognition model
Activity recognition in SHE routinely detects person’s activities from the data captured by sensors. This is relevant and very near to most common applications such as human body motion–detecting sensors, surveillances, DLAs, healthcare, and temperature control. The time stamp frame of activities incorporated in smart architecture is shown in Figure 3. Here, we distinguish some definitions of DLAs of individuals:
Distributed activity key-session model and activity variation
In this section, we present activity model and activity variation concept which is used in our proposed SDF.
Activity key-session model
We describe the terminology which is used during work; set of sensor nodes is defined as

Definition of second pattern
“Sensors are assigned by unique keys
Activity variation
It is well known that same pattern of activities cannot be repeated at same real time. Therefore, small dissimilarities between these same activities are known as activity variation in our proposed SDF. Difference between trajectory variation

Security verification and performance analysis of SDF
In this section, we have described experimental setup in real SHE using widely recognized security analyzer tool–automated validation of Internet security protocols applications (AVISPA). 31 Then, we have discussed formal authentication of SDF in BAN (Burrows–Abadi–Needham) logic, informal, and performance analysis of SDF with other schemes. We have divided all these steps into four subsections which are discussed in the following sections.
Experimental setup using AVISPA tool
In this subsection, we implemented design model in real environment to make it easily understandable and performed same experiments in real environment to check the suitability of SDF as shown in Figure 6. Our real environment structure based on five basic parts is shown in Figure 2. This section comprises two parts: (1) brief detail about AVISPA and (2) simulation result.

Real smart home environment and physical setup in lab.
Brief detail about AVISPA
Automatic verification of Internet security protocol and application tool (AVISPA) is an automated application which validates and analyzes the security by Internet sensitive protocol whether it is safe or unsafe. AVISPA comprises four backends which are autonomously verified, namely, OFMC (i.e. on-the-fly model-checker), CL-AtSe (i.e. constraint-logic-based attack searcher), SATMC (i.e. sat-based model checker), and TA4SP (i.e. tree automata–based security protocol). The AVISPA tool utilizes high-level protocol language (HLPSL) and uses script of HLPSL as an input and translated it into intermediate format (IF) by utilizing the translator named HLPSL2IF. HLPSL contains important features (e.g. control flow pattern, data structure, cryptographic primitives, complex security properties, and alternative intruder models) which make HLPSL a well-appropriate industrial-scale protocol, as shown in Figure 7(a).

Authentication and confidentiality result: (a) steps of AVISPA analyzer tool structure, (b) SDF execution in AVISPA, and (c) authentication and confidentiality.
For additional details, we refer to the work by Vigano. 32 The attacker can play a role of a legitimate user in top-level global constants (i.e. environment role) with composition of one or more sessions. In AVISPA, 31 the attacker uses Dolev–Yao intruder model which is modeled through the channel. 21 Our proposed SDF has four basic steps and two basic roles. A configuration phase of nodes and key installation is similar to session role and environment role using Dolev-Yao model attack. Therefore, to perform the testing and authentication, we used the translator HLPSL2IF to transform the script of HLPSL into IF. In addition, four backends, CL-AtSe, OFMC, TA4SP, and SATMC, are integrated with scripts of AVISPA tool. These four backends translate the code of IF. Figure 7(c) reveals the results of confidentiality and authentication.
Simulation results
In this section, we describe simulation results of the proposed SDF. The results revealed that the proposed SDF clearly remained safe under Dolev–Yao attack model. In other words, it can be said that communication remained safe from Dolev–Yao model attack and the result is shown in Figure 8. This shows that all parameters remain secure enough between SHLG and node

Simulation result in AVISPA and safe-from-attack model of Dolev–Yao.
Formal verification proof based on BAN logic
This section discusses the formal analysis of the proposed SDF (e.g. established key session, authentication, and freshness) using Burrows–Abadi–Needham logic, 33 generally known as BAN logic.
{
Some basic postulates of the BAN logic are given as follows:
The message meaning rule:
Nonce verification rule:
The jurisdiction rule:
The freshness rule:
In case, if principal sees a formula, therefore, it also sees its parameter:
To verify an authenticity of protocol regarding its security, we followed the following steps:
The proposed SDF in the language of formal logic will be idealized.
The assumptions regarding the preliminary state of the proposed scheme will be identified.
The production and rules of the logic will be used to infer new predicates.
Logic will be used to determine the beliefs of entities about the proposed scheme.
In order to verify the proposed protocols secure, we perform the following logic verifications using BAN logic:
Now,
Informal analysis of security (properties)
This section focuses on the resilience compared to feasible attacks (e.g. device-compromised attack, denial of services, message forgery (including man-in-the-middle (MITM) attack), masquerade attack, known-key attack, and message replay) and recognition of abnormal DLAs. Dolev–Yao model is used to analyze the proposed SDF where an attacker can snoop message between node
Definition
Encrypted activity transfer is helpful in terms of transformation of activities from one another. To recognize the encrypted activity transfer process, the trajectory activity attributes consider to verify and also match the token authentication (
Trajectory set (
Key-pol’s attributes set (
Encrypted keys hold the attributes of the activity transfer process and trajectory process. Old and new encrypted activities’ key sessions have some similarities due to their abnormal functionality and condition. In order to explain the specific activity transfer, we have to take the daily activity routine of individual through sensors encrypted through key-session process of SDF. Therefore, through this process, communication upheld the secure trajectory among the devices of the SHA and shortly deployment is secured against attacks. Activity’s key updating and sharing process is shown in Figure 9, and results of activity recognition under various condition are shown in Figure 10.

Distributed trajectories updating and sharing mode for encrypted activities of key-session attributes: (a) time stamp synchronization, (b) sending encrypted key-pol attributes (

Result analysis of the proposed framework: (a) activity recognition under certain attacks, (b) activity recognition average, and (c) recognition of different types of DLAs.
Comparison analysis of activity recognition based on trajectory transfer and mining
To calculate more accurately, we evaluate the activity recognition result based on trajectory transfer and on activity recognition mining using various encrypted key-pol attributes shared between various sensors of bedrooms, kitchen, aisle, bathroom, and living room, as illustrated in Figure 5. To evaluate the activity recognition under uncertain attack, experiment is executed four times and results showed value of attacks 1 to 8, whereas encrypted activity recognition remained secured and performed the normal activity, as shown in Figure 10(a). We also calculated the encrypted activity recognition during 1 to 8 attacks based on mining. Results revealed that security of encrypted activity recognition remains high and also categorized into maximum activity recognition, minimum activity recognition, and average DLA recognition as shown in Figure 10(b).
Case: device-compromised attack and deadlock avoidance. Proof
This type of attack mostly happens during communication between devices in the smart home resulting in deadlock. When an unauthorized person (e.g. adversary (Tom)) attempts to access control on device (e.g. surveillance camera or door lock sensor) and any of the devices compromise with the attacker Tom, usually schemes terminate the system in case of such attacks resulting in deadlock. However, our proposed scheme will detect the cause of such attack and will prevent the deadlock condition by keeping the rest of the network functional using distributed framework. SDF secured the device from such attacks due to its unique value
Case: SDF secured against masquerades attack, denial of services, and message replay attack during adversary attempt. Proof
1.
2.
Case: SDF secured against message MITM attack. Proof
In this case, simulation results clearly ensure that proposed SDF secures against active and passive attacks including MITM attack. Here, we assume that adversary (e.g. Tom) may try MITM attack by modifying {
Case: SDF secured reciprocated authorization when adversary try illegal access. Proof
1.
Case: SDF secured key-session establishment and message confidentiality during attack. Proof
1.
2.
Case: SDF secured node identity faceless and upheld cryptic link when adversary tries to send fake identity. Proof
1.
Security properties comparison
In Figure 11, we have compared security feature of proposed protocol with some related existing schemes in terms of different security attacks. It is noticeable in Figure 11 that none of the protocols are completely safe from security flaws. The well-popular BAN logic authenticates the proposed SDF and verifies that SDF securely achieves session key agreement and mutual authentication. Furthermore, using AVISPA security tool, simulation results of SDF show that the protocol achieves the security properties and is secure against passive and active attacks including MITM attack.
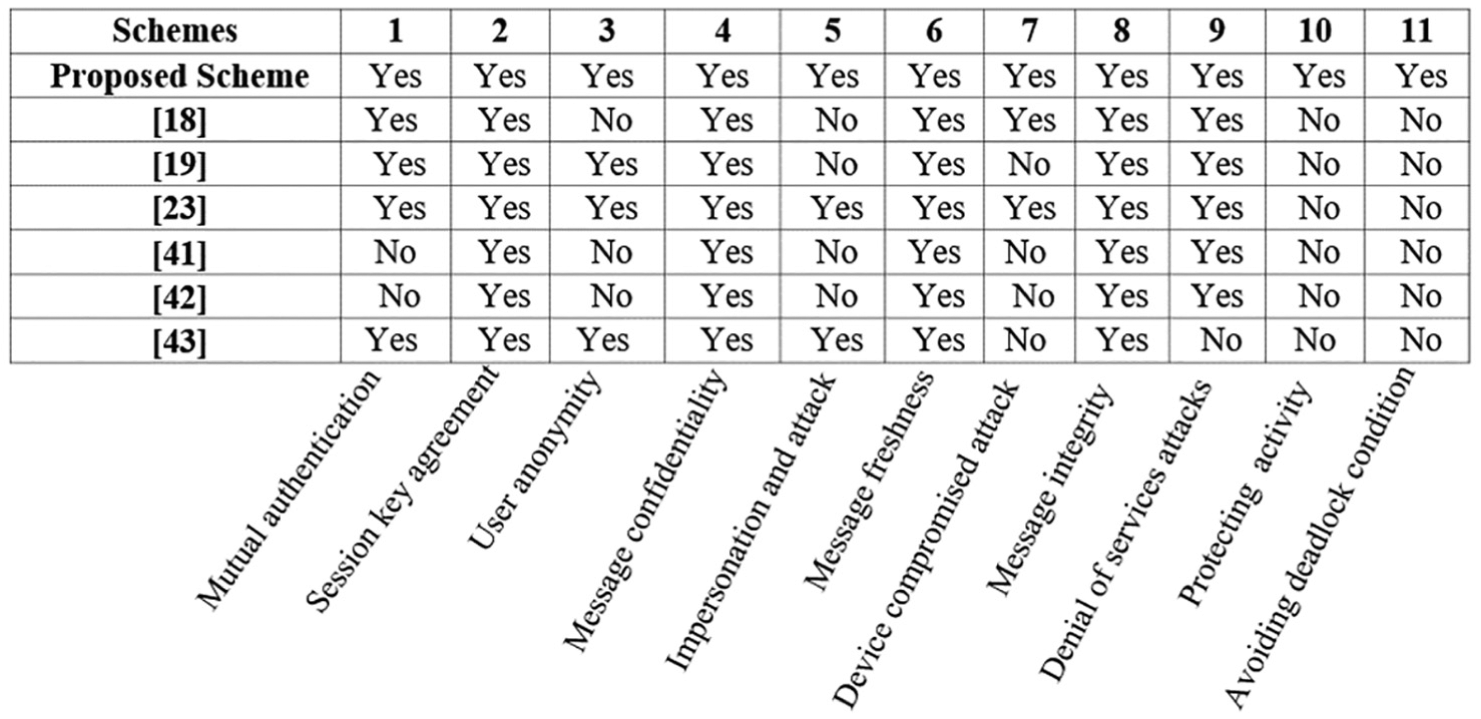
Security properties and features’ comparison of SDF with other related protocols.
Computational and communication cost analysis of SDF with other schemes
This section focus on performance analysis of proposed SDF and measured efficiency in the light of computation and communication costs in comparison with other schemes.17,18,22 This section comprises two subsections: (1) computation cost comparison and (2) communication cost comparison.
Computational cost comparison
We choose TelosB mote for experimental setup to implement the SDF as in the work by Kumar and colleagues.17,22 TinyOS version 2.x is used by TelosB mote to run and operate system; for more details, see TinyOS tutorials
36
and TelosB datasheet.
37
Advance Encryption Standard (AES) has considered current encryption standard which uses symmetric key algorithm and integrated in CC2420 radios.
38
We use cipher block chaining (e.g. CBC-MAC) to verify the authentication and integrity of message. A beacon frame is used by SHLG for synchronization of information and clock time which provide help to synchronize the SHNs and SHLG.
22
Clock synchronization is beyond the scope of this article; for more detailed experiment, we refer to previous works.17,19,39 The purposed SDF requires reasonable memory size to execute experiment in TelosB mote. SHNs are resource-hungry devices and we used computational and communication costs only for such devices. Figure 12(a) clearly displays the required size of memory (ROM and RAM) and time execution for TelosB mote. Hash, CBC-MAC, and AES required 39, 8, and 3.4 ms, respectively, for computation operation at node

Communication and memory size comparison of SDF with other schemes during execution: (a) communication cost comparison of SDF with other schemes and (b) computational cost comparison of SDF.
Comparison of computational cost with other schemes.

Communicational cost comparison
In order to calculate the communicational overhead of SDF, we consider total number of bits received and transmitted by device
Communication, storage overhead.

SDF: secure distributed framework.
Conclusion
SHE consists of heterogeneous devices and provides several services to the personages. These smart homes have various functions, for example, climate detection and control system, healthcare system, security system, and electricity control system. Individuals can enjoy these facilities in such smart environment through network-based smart devices and sensors. Faceless identity of devices during communication regarding security measurements is a critical challenge in smart home, where adversary and unauthorized individuals can recognize home devices to damage the DLA of users.
The SDF, proposed in this article, comprehends freshness of message actively via timestamp and uses user’s activity pattern to recognize the abnormal activity to secure the entire communication from attack. Furthermore, it covers the integrity and authentication of data by keeping identity of nodes faceless and establishes trustworthy session via cryptic link. SDF comprehends freshness of message actively via timestamp. In addition, analysis of SDF (in both AVISPA tool and real smart environment) demonstrated that proposed pattern is suitable to enhance the security level of SHE.
Footnotes
Acknowledgements
The authors are immensely grateful to Director, Mr Mazhar Waseem, for the language editing that greatly improved the manuscript.
Handling Editor: Weizhi Meng
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work is supported by the National Natural Science Foundation of China under grant no. 61672115 and Chongqing Social Undertakings and Livelihood Security Science and Technology Innovation Project Special Program (nos cstc2015jcyjBX0124 and cstc2017shmsA30003).
