Abstract
With the current global food production capability, it is not difficult to anticipate that there will be a global food shortage when the world population grows beyond 10 billion by the end of the 21st century. Many projects are in motion to deal with this problem and some of them are considered to be quite feasible. Development and implementation of smart green houses and vertical farms are two major solutions for the expected crisis, but as other ICT-based systems, their security problems must be dealt with. Nevertheless, current network forensics is still unable to fully monitor and analyze computer network traffic to gather the evidences of malicious attacks or intrusions. Although major companies and government agencies have introduced various types of high-speed IDS into their networks, smaller firms or private organizations are unable to do so because of the cost involved. The lightweight IDS proposed in this study can be a suitable solution as this system can be operated with a common PC and peripherals. This system also underwent a test bed experiment and proved its efficiency. Jpcap library was used to capture transport packets which were then classified using typical communications protocols. The packet headers were subjected to analysis and the results were stored in database for later applications.
Keywords
Introduction
The early industrial automation systems that had used some type of information technology (IT) were relatively safe from external cyberattacks as they were independently constructed and separated from outside environments. Today, however, most of the industrial automation systems have become more sophisticated and complex; they need to be controlled and monitored by the systems within the manufacturing sites and other operation management system(s) from outside remotely. While the efficiency of such automation systems may have increased, the chance of cyberattacks from domestic and foreign organizations or hackers has increased so much that some of the control system research organizations in the Republic of Korea (ROK) have established a security guideline for them.
Although their guideline includes many useful measures to counteract possible attacks, its method requires a series of expensive equipment and subsystems which are quite unaffordable for small and medium-sized companies that operate or planning to operate smart green houses or vertical farms. The lightweight intrusion detection system (IDS) proposed in this study can be an adequate solution to the cost-related problems as this system model uses an open-source Jpcap library to capture transport packets, instead of developing any exclusive programs separately.
Related works
Security and denial-of-service attack
An effort to improve server stability has been continued at the government level because of recent proliferation of attack scenarios. Such effort, however, is mainly geared toward government institutions, which means that private organizations and individuals who construct small-scale networks are still vulnerable to these scenarios. The types of attack scenarios include DDoS (Distributed Denial of Service), DRDoS (Distributed Reflection Denial of Service), HttpTunnel, and MultiHop.1–3 In the case of DDoS attacks, for instance, Botnets scattered in networks initiate the attacks against the target servers simultaneously.
In addition, Botnets take various malicious behaviors such as DDoS attacks, leaking of personal information, spreading of malicious codes, and sending out large-scale spam mails. 3 Among them, DDoS attack is one that transmits enormous traffic volumes to the intended target servers using many distributed Botnets. It is characteristic of this attack that the servers being attacked cannot provide normal services or it will crash due to the system overload.
IP multimedia subsystem (IMS), which is a key technology for the provision of new services in an All-internet protocol (IP)-based fixed mobile convergence environment, is based on the session initiation protocol (SIP) signaling. As IMS is expected to be the major next-generation networking standard for both wired and wireless systems, the importance of SIP security will be increased. Also, as Dos attack has emerged as one of the greatest security threats recently, the importance of protecting major SIP components from it has been increased. Especially, since IMS’s Call Session Control Function (CSCF), which corresponds to the SIP proxy server, plays a key role in setting and controlling various multimedia sessions, the entire service could suffer a heavy blow when problems occur with CSCF. Conner and Nahrstedt 4 introduced the ringing-based denial-of-service (DoS) attack, which is a new type of DoS attack targeting SIP proxy server. This attack employs unique features of SIP and does not require heavy traffic generation to disrupt the service so that the attacker will have a great advantage.
J Shen et al. 5 introduced a different type of authentication protocol that does not require pairing for the certificateless cryptography used between personal digital assistant and its application provider (AP). This method adopted an elliptic curve cryptography algorithm that allows a low computation cost as well as a high-level of security.6,7
Smart home security and small information & communication technology service companies security
As the past concepts similar to the Smart Home, there were home automation in 1990s and IT homes in 2000s. They were the ones that integrated the communications and control technologies into the living space. The recent interpretation of the smart homes is based on the concept of energy savings or stabilizing the supply and demand of electric power. From a technology standpoint, they are the control systems in general. That is, the basic concept of the smart home system is having a home server (general-purpose controller), connected equipment/devices (appliances and systems), and a user interface (UI; input/display terminals) together to achieve communications, as shown in Figure 1.

Smart home security.
The equipment, devices, and systems in a smart home follow the purpose of application embedded into the system but their uses are not limited to a single purpose. For example, it will become a Home Energy Management System (HEMS) when instrumentation equipment and personal computer [PC(s)] are connected and a control system application is embedded, but it can also be changed into a security system by connecting the system sensors with smart phone(s) and embedding the application that sends the emails to the user informing the conditions of his or her home while he or she is out. 8 But the latter case usually involves the problem of cyber security.
Similar to smart homes, some of the information & communication technology (ICT) are integrated in smart green houses and vertical farms, and the cyber threats that often arise in the existing information and communications networks can also occur in the smart home environments. This could lead to a serious failure in the power grids, which are the essential national infrastructure, and cause unimaginable damages.8,9 Scott Borg, the head of U.S. Cyber Consequences Unit, claims that if one-third of the US’ Power Grids fails for a period of 3 months, the damages will be as great as the devastations that 40–50 hurricanes would cause. 10
If the smart home environments become common in the near future, they can easily become the targets of malicious attacks as the smart equipment and devices will be spread around every corner of the residential house allowing physical access. The attackers will be able to extract or leak personal information and manipulate the power usages by illegally occupying the network. Also, if one uses some of the low-security encryption algorithm module for his or her smart home equipment because of limited budgets or specification of equipment, the attacks through the vulnerabilities in the module will be much easier and the intrusion will advance into the entire network.
When the wireless communications technologies like ZigBee, Wi-Fi, or WCDMA are used, the “Sniffing” of transmitting/receiving data can be achieved easily so that information exposure becomes the major concern. In the wireless communications environments, for example, the default setting is often used as a security setting for the wireless access point (AP) so that the secondary cyberattacks can be expected. Moreover, since devices such as smart phones, PCs, Internet Protocol TVs, and others are connected in the smart home network to provide smart-services like real-time energy usage measurement or notification of power prices in each timeslot, the intrusions into the operation center will be possible.
Through the emerging growth of the Internet and technology, our modern life is becoming smarter and smarter every day due to continually and rapidly growing Internet technology. For example, a house installed with some kind of a communication network is being called a smart home. The residents of such a home are able to monitor, control or program almost all the household appliances such refrigerators, TVs, and security alarms using the network even when they are not in their homes, making them “smart.” By making the appliances smart, residents’ lives become easier and feel securer. Despite the positive effects the smart appliances or equipments offer, they are still vulnerable to many forms of cyberattacks which could bring serious consequences. Mantes et al. 11 had explained that there were six major elements pertaining to the security of smart homes-confidentiality, integrity, authentication, authorization, non-repudiation, and availability. Among these elements, the past DoS/DDoS attacks aimed the availability of the household smart equipment through a partial or a complete disruption of the installed communication system. For instance, Auriemma 12 and Nunes 13 claimed that there was an incident of DoS attack against the smart TV which had led to the interruption of normal service or operation of network-linked equipment. Thus, it is essential to establish a proper authentication procedure for the network system to prevent DoS or other types of cyberattack on the smart equipment 14 such that unauthorized service or operation by the infected smart objects. 15 Another grave scenario is the generation of botnets through vulnerable smart devices which could facilitate a more serious DDoS attack. As most of the smart devices have factory-set passwords, they can be easily turned into a zombie bot who will then assume the role of a secondary attacker. As mentioned earlier, the cyberattack carried out on 21 October 2016 had been carried out through smart equipment including security CCTV. 16 Being the biggest attack incident, it had become evident later that tens of millions of IP addresses were used in that attack originating from the infected smart equipment. 16 Although this type of attack is still effective, there is no perfect solution to prevent smart equipment becoming a malicious bot and increase the security of the smart home network system. Much more effort is required in this area by both the manufactures and the users. 17
Meanwhile, the Korean Communications Commission (KCC) provided a security consulting to 60 small ICT service companies in cooperation with the Korea Internet and Security Agency (KISA) on June to December 2012 and identified a total of 1157 vulnerabilities, including unnecessary exposure of information or administrator functions.18–24 This meant that each company had an average of 19 security-related vulnerabilities and it was urgent to initiate some measures for information protection. Many problems associated with the security of personal information (e.g. transmission of unencrypted data, weak account/password management policies) were found among the vulnerabilities as well.
As two major difficulties in performing security-related tasks, these small ICT service companies cited lack of security personnel (48.3%) and budgets (46%), requesting early and active government support in this matter. The situation has not changed much in the past 4 years and any rapid policy changes cannot be expected at the moment, especially for the small companies. For this reason, we believe a lighter security system will be needed for the future small businesses, and this can be in the form of small-scale smart green houses and vertical farms.
System goal and diagram
The small-scale IDS will be investigating the possibility of becoming a target of DDoS attacks or bots only for the client it is involved with, without considering other clients. Should the client become the target, the attacker’s IP address will be transmitted to the server to take a defensive action such as banning the relevant IP from re-entering client’s system. This IDS will also share the detection rules with server and synchronize (SYN) them to detect DDoS attacks. The small-scale IDS then transmits its detection information to a large-scale IDS who will let other clients to be aware of such information for individual protection. The large-scale IDS generally detects DDoS attacks in the internal network and the reason for dividing the IDS systems into two scales is to increase the reliability. In this regard, the small-scale IDS usually exhibits more thorough detection performance.
The administrator who runs the large-scale IDS with a UI based on the information from the small-scale IDS can grasp the situations within the internal network more intuitively so that he or she will be able to immediately issue a warning when the client acts as a DDoS bot. The large-scale IDS also informs the small-scale IDS of updates in DataBase (DB) rules and assumes the role of synchronization. In the study, it is made possible to test a DDoS attack scenario following the preceding study.25,26 First, there is a sever to be attacked within the network where a zombie computer which executes the attacking program exists. Such a virtual network should be constructed identical to an actual network where many number of computers are required. An IDS is implemented on the particular computer in the network. The IDS then extracts and notifies possible DDoS packets to the administrator after analyzing them. To accomplish these processes, DDoS attacks are classified by their types and the packets’ characteristics are identified for the database, as shown in Figure 2.

The packets’ characteristics are identified for the database.
A lightweight intrusion detection system
A lightweight intrusion detection system (LIDS) model has been designed to deal with cost problem mentioned earlier. This model can be operated with a standard PC(s) (Figure 3). Under the environment where the typical communications protocols such as user datagram protocol (UDP), transmission control protocol (TCP) are being used, the transport packets can be captured using an open-source Jpcap library and they are then stored in the system database for later analysis. This way, system load can be reduced when the algorithm applied in the model is in operation.

A lightweight intrusion detection system model.
The statistics compiled for 1000 databases are stored in the MySQL database and graphs are used to represent them. The performance of the model has been evaluated by performing several simulated attacks.
The system model largely undergoes two stages when detecting an intrusion event: adaptive stage and action stage, both of which were designed almost identical to the ones that have been designed in the preceding studies.25,26 The adaptive stage was rarely considered in other existing intrusion detection systems which had been designed to operate under a specific network environment exclusively. But the IDSs that have been designed to operate on the general-purpose systems need such a stage to adapt themselves to the different environments where network configuring elements such as buffers, service, ports, and the number of sockets are varied.
A server was constructed on a personal PC, and by assuming the system where two users use server pages through page refreshing, the packets were collected 100 times every 30 s to simulate the SYN flooding, which is known as one of the most common typical traffic attack methods (Figure 4). A lightweight among the collected packets, 430,820 packets were TCP packets and 3822 packets in these packets were SYN option packets (Figure 5).

A lightweight intrusion detection process.

Standard deviation of collected packets.
The SYN packets are a sort of TCP header option which is not directly involved in communication itself but has to do with the session connection prior to commencing a communication so that its numbers are relatively small. The standard deviation S is calculated as 28.47962 for the packet values collected from above preceding research equation.25,26 The normal distribution curve based on the values is shown in Figure 5. Although the curve did not display a perfect Gaussian-form curve due to non-uniformity in the data values, it was possible to recognize the packet-inflow patterns at specific times. The action stage which is to be achieved after recognizing the normal packet pattern is described in Figure 6.

The action stage achieved after recognition of the normal packet pattern.
The stage is largely divided into two threads. Thread 1’s role is as follows.
Thread 1
Loop
The packets flowing in and out of the system are captured in this looping phase using the Jpcap library. The packets capturing cycle, the number of maximum packets capturing, and the maximum packet size are defined for this process to avoid system loads resulting from constant capturing loops.
Filtering
In the filtering phase, only the data intended for analysis are filtered by discarding unnecessary packets from collected packets through looping phase. The data go through several filtering phases as water purification process. For instance, in order to extract a SYN packet, both Source and Destination IPs from the IP header are stored and then are checked whether the packet’s protocol is the same as the TCP protocol. The packets that do not follow the TCP protocol are discarded. Finally, the filtering process will be completed by discarding all the data except the packets conforming to the SYN option.
Insert (data)
In the “Insert” process, the “Data Clump” which only contains the necessary data is inserted in the database for analysis.
Here, the database acts as a “Shared Resource” because it will be difficult to gain access in the system having divided threads when the stack-type or list-type data are used. Also, the data are stored assuming the form of a database since there is a possibility of system degradation when direct memory input/output actions are taken in the system that collects packets repeatedly. Now, Thread 1 secures the data necessary for the analysis and keeps capturing remaining packets. In the main process, Thread 2 will be implemented before the next Loop begins, as described next.
Thread 2
Search
The primary object of Thread 2 is to draw out packets stored in the database. This is carried out independently from the main thread. These are stored as variables following the predefined packet options and numbers.
Decision
This is the phase in which the abnormality of each packet is checked using the characteristics of stored packet data. The data are actually analyzed and judged in this intrusion detection model. The possibility of intrusion can be determined using different methods depending on the types of attacks and the protocols which are not allowed to enter the port(s) in service, packets with forbidden options, and the packets largely exceeding the allowed numbers are subjected to judgment. The system loads have been minimized by the filtering phase in Thread 1.
Delete
The packet data clump(s) within the database should be cleared before commencing the next packet detection activity and completing all the filtering processes. This is the “Delete” phase. Without this process, the tens of millions of packets accessing a network system providing services to the clients have to be stored in the database without any restrictions. This is practically an unnecessary task and the data should be cleared at the end of every cycle. Thus, contrary to the Insert phase in Thread 1, the data can be cleared by transmitting a query which allows data initialization process.
System goal and attack environment
The modeled IDS has been tested for actual DDoS attacks at the test bed environment designed in the preceding study. The incidents of DDoS attacks studied in the preceding studies25,26 are represented in green while the same attacks used in this research are represented in blue (Table 1). Only simulated DDoS attacks were performed, as performing an actual DDoS scenario is not allowed by the authority even for an experimental purpose. Therefore, no one can anticipate the results from an actual attack. The program used for the LIDS has been implemented with Java to allow better communications capability and universality (i.e. operation on any platforms). Also, to achieve real-time operation, a structural logic that optimizes both execution and response times were emphasized in the program so that it can show the user the total volume of current traffic and the event of malicious attacks such as UDP, SYN and internet control message protocol (ICMP) flooding, both on a real-time basis. In the attack scenario, the network administrator or the monitoring staff can respond to a malicious attack remotely. Once the system recognizes a slight indication of an attack, the surveillance program is automatically activated and notifies the incident to a person in charge who will then take a defective measure to avoid or minimize damages. The DDoS attack incidents in the past few years are shown in Table 1. The experiments were conducted using the attack codes used in June 2013.
DDoS attack incidents in the ROK.

For the experiment, a total of 64 virtual PCs and 512 botnets were created by applying the virtualization technology on a private server (Samsung Smart Server) and eight PCs. Figure 7 shows attack experimental environment.

Attack environment.
Lightweight intrusion detection model for smart green house and vertical farm security was coded with Jpcap on the basis of Java and aimed to look at all the packets passing through user’s network interface card. It was constructed in such a way that the user can grasp network situation at a glance easily, check information regarding the control and other details, and give warnings using threshold value enabling easy detection of DDoS attack possibilities.
The ultimate objective of the system proposed in this article is to lower the entry barriers to the network analysis and management as well as provide a framework easily understandable to networks administrators who do not have adequate expert knowledge yet. Since the program has been constructed based on graphical user interface (GUI), the users unfamiliar with wireshark or other network analysis programs can easily approach it and the program will contribute to lowering of the entry barriers for the network security operation in small network/server management by individuals.
The other contribution of this research is that the program also focuses on preventing the errors which could have been avoided, in addition to protecting the user information. Without a proper monitoring/surveillance program or trained personnel, the system could miss out some of the malicious packets but the proposed system can capture these packets and display them on the monitor. The existing IDSs used a method where the intruder’s attacking signature can be identified by comparing it with the past records documented in their respective databases.
Performance evaluation
In order to compare the performance levels of IDSs or the anti-virus programs being used currently, the following commercial products have been tested by adding a new type of DDoS attack: Product A (Alyac by Eastsoft 27 ), Product B (Norton anti-virus by Symantec 28 ), Product C (Smart Defense by AhnLab 29 ), Product D (AD-Spider Dajaba by Digital on net 30 ), and Product E (Online vaccine v6 by nProtect31,32), as well as the proposed system.
The comparison results are shown in Table 2. All the systems except the proposed system could not recognize the unknown botnets at all or narrowly recognized them. This means that only Product B and E partially recognized and deleted the botnets but others just kept on going about checking the traffics. The proposed LIDS has shown a better performance by detecting the small number of dangerous packets, and considering its advantage in construction costs, it will be suitable for the security of smart green houses or the vertical farms owned by private farmers or small companies.
Comparative analysis with advanced research.

○: detection; △: partial detection;  : undetection.
: undetection.
Figure 8 shows the user interface which has a total of four domains. Domain A graphically shows the client currently connected to the main server. Here, the situations where a client is added or removed are checked on a real-time basis and the icon will be also added or removed accordingly. The icon of the client suspected of a DDoS attack will be indicated in red but otherwise in blue normally. The red icon will return to blue when the attack has been ended.

User interface of smart phone.
Meanwhile, the icon can be placed in any other places by dragging it with the mouse. When the icon is clicked, it will be indicated with a square box. In Domain B, the information of the server or the client clicked is displayed in a box which includes the ID of the device currently selected, the status of current DDoS attack, the number of devices being connected, and so on. In Domain C, the traffic information of the selected device is displayed which includes the packet number, starting/destination IP, captured time, SYN/RST flooding/ACK flooding Flag, and so on. Several functions are offered in this domain. First, the item can be arranged in either ascending or descending order by clicking the table item window. Second, the position of each item can be changed by dragging it with the mouse. Finally, by clicking the server, all the traffics will be shown while only the traffic directed to the client will be indicated when the client has been clicked. Domain D displays the TCP, UDP, ICMP, and other packets in real time with an interval graph and a pie chart. The former represents the packet volume of a time unit with a segment while the latter shows the proportion of the same volume in a total packet volume. This domain also displays the individual number of packets passed through by their types together with their individual percentages. When the server is clicked, all the packets will be displayed but only the graph of a specific traffic will be shown when a client has been selected. For the UI, some improvement has been made to utilize it with a Smart Phone (Figure 8).
With the reduced program size, this lightweight intrusion detection system can be used on the smart phones and its processing time will be faster as the program Java code has been optimized. Following results were obtained from the comparison of performance evaluations. First, as shown in Figure 9, the size of the Java program has been reduced from 267.7 Mb (preceding study 25 ) to 72.3 Mb by newly coding it with Java Android to replace the original program but still making it compatible. Also, a new UI has been developed for the smart phones so that it can support the system like the smart farm operation system. Based on these efforts, the system performance has been improved from 1.326 to 1.088 s in terms of processing time (Figure 10).
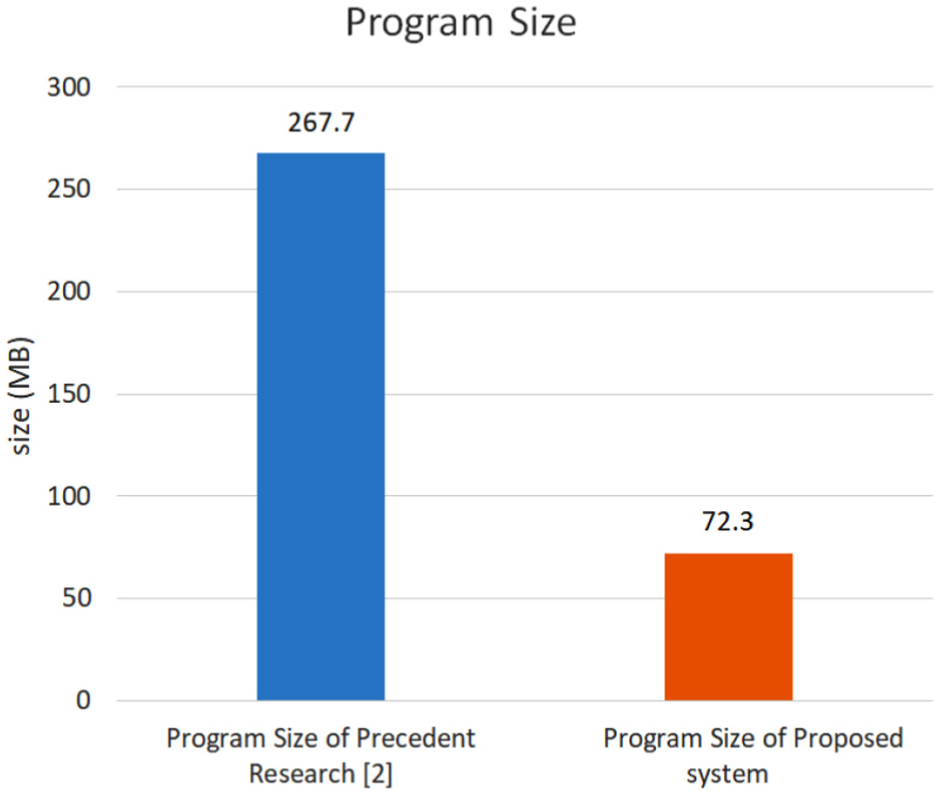
Program size.
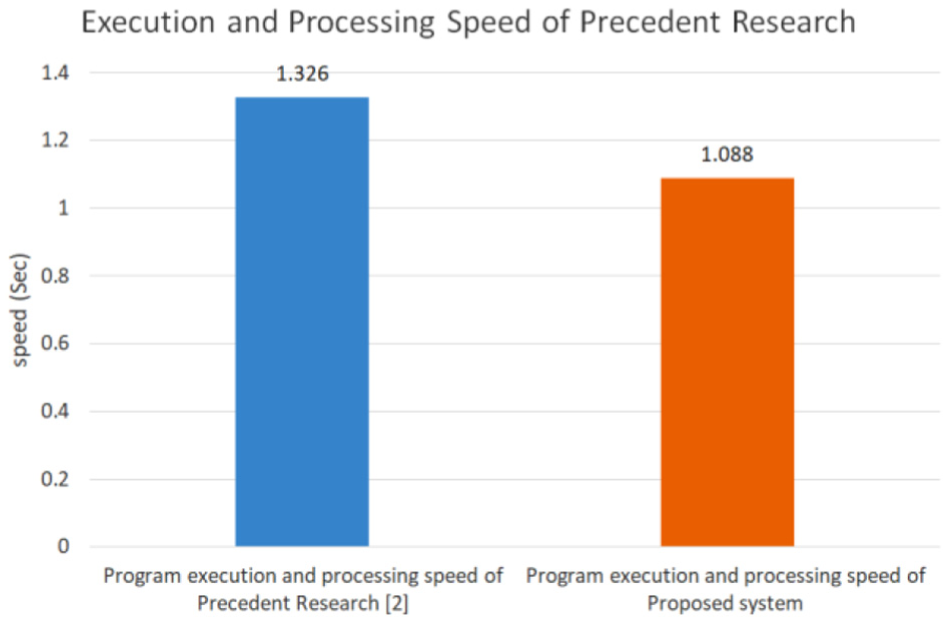
Program execution and processing speed.
The Green House and vertical farms adopt an independent small-scale network and it was difficult to attach an IDS system to each of them. I was motivated by this problem and implemented a graphic-based DDoS detection system for the shopping malls in the preceding research. 25 After optimizing the program and reducing its size, I was able to implement the IDS system suitable for the network-based systems smaller than the ones used at the shopping malls. For the performance analysis, the codes used for the experimental attacks were the codes used for the DDoS and other attacks carried out in the Republic of Korea in the past. Also, while the previous IDS system described in the preceding study 25 only allowed the detection with PC, the new system can be used with a Smart Phone.
Conclusion
Java language was used for the development of LIDS because of its adaptability and universality as a programming language. To compare the packet detection capability of each different product, the system that classifies the malicious botnets according to their behavioral characteristics was implemented. This system allows faster detection of harmful packets for analysis and removal than other commercialized IDSs. The malicious packets or codes were detected by analyzing the abnormalities in the data collected and stored in the databases and the attacking incidents were notified to the user. The system also performs a real-time traffic monitoring and detection with a method similar to the conventional method used by commercialized products, but it is optimized for the intrusion detection operations with smaller servers and affordable hardware.
While LIDS can be constructed with relatively lower costs, the disadvantage of this system is that the detection time for the DDoS attacks could be extended when such an attack is carried out simultaneously and independently. This problem may be solved by sharing the detection information such as attack rules, IPs, attack types, attacking stages, attacking times with other databases within separate servers so that the similar attacking incidents can be recognized by other servers using the same network. As hackers of intruders usually attack the network continuously rather than momentarily, the system can detect the attack easily when there is more than one abnormality detected. Also, the detection is still possible even when the small number of malicious packets has been detected. The authors have confirmed these abilities with the results obtained from the simulated DDoS attack scenario. In the future, authors plan to deploy this system in some smart green houses or vertical farms. Another tentative plan is to test the system in a smart building to seek further application possibility. The patent for this system will be filed after the test.
Footnotes
Acknowledgements
The first draft of this paper was presented Oral Session in 2017 APAIS 1st Special Issue International Workshop, 7–8 February 2017. The author grateful to two anonymous commentators who have contributed to the enhancement of the paper’s completeness with their valuable suggestions at the Workshop.
Handling Editor: Sabah Mohammed
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the National Research Foundation of Korea (NRF) grant funded by the Korea government (MSIT) (no. 2017R1C1B5077157).
