Abstract
With the rapid booming of intelligent traffic system, vehicular ad hoc networks have attracted wide attention from both academic and industry. However, security is the main obstacle for the wide deployment of vehicular ad hoc networks. Vehicular ad hoc networks security has two critical issues: access authentication and privacy preservation. How to ensure privacy preservation and improve the efficiency of authentication has become the urgent needs. However, the existing access authentication schemes for vehicular ad hoc networks with different flaws cannot maintain the balance between security and efficiency. Thus, an anonymous access authentication scheme for vehicular ad hoc networks under edge computing based on ID-based short group signature mechanism is proposed in this article to improve the efficiency and anonymity of access authentication. Multiple pseudonyms are presented to preserve the privacy of vehicle node. Besides, a new method is designed to identify and revoke malicious vehicles in the evaluation manner. The core protocols of the proposed scheme are proved to be secure by SVO logic. According to the computation cost and transmission overhead analysis, we indicate that our scheme owns better performance. Moreover, in this article, we combine vehicular ad hoc networks with edge computing together to provide a new clue for the development of mobile edge computing.
Keywords
Introduction
The increasing requirement for improving security and privacy for user has brought wide interest on anonymous access authentication for vehicular ad hoc networks (VANETs). The VANETs, a type of wireless mesh network (WMN 1 ), are designed for car interconnection communication under roadside infrastructures. 2 The rapid advances in intelligent vehicles and cloud computing technologies in recent years motivate researchers to investigate a new concept of edge computing. 3 As a new paradigm, edge computing works between the cloud and the terminal nodes, which enables to take full advantage of cloud computing, thereby providing vehicles with powerful computing resources and useful services.4,5 Different from cloud computing in the data center, edge computing can furthest promote the computing capabilities of terminal. In VANETs, the high mobility of vehicles and massive data from data center make the real-time communication hard under the common cloud computing environment.6,7 Edge computing can move the large amount of calculating pressure from the vehicle terminal to the roadside infrastructure (edge computing node),8,9 which is thus considered to be an ideal solution to the computational-cost process in VANETs during access authentication. However, few solutions are focused on the combination of access authentication with edge computing in VANETs. 10
VANETs can provide a lot of convenience for the vehicle user. For example, vehicles can share traffic information via VANETs to select better travel routes. If necessary, special vehicles, such as emergency vehicles, may even apply to control the traffic lights through VANETs to save more time for patients. In the future, massive data generated by vehicles accessed into VANETs require real-time processing to make decisions. In the future, as an essential part of intelligent transportation system (ITS), VANETs are becoming the focus of academia and industry. 11
Features and challenges of VANETs
As shown in Figure 1. VANETs contain three types of network entities: on-board unit (OBU), the intelligent module, which is loaded with integrated embedded systems, global positioning system (GPS), and the tamper-proof device (TPD). The roadside unit (RSU) is a roadside infrastructure, acts as the role of edge node, that can provide edge computing and access services for vehicles. The third-party trust authority (TA) is the central institution of the management for vehicles. VANETs communication is able to be divided into two modes that are vehicle-to-vehicle communication (V2V) and vehicle-to-infrastructure communication (V2I). The communication follows the dedicated short range communications (DSRCs 12 ) protocol.

The architecture of VANETs under edge computing.
VANETs have their unique features:
Vehicles own strong computing ability and rich storage capacity.
VANETs are more constant and stable than other ad hoc networks, due to the movements of the vehicles on the same direction are foreseeable.
However, the current technology of VANETs is still not mature enough and facing many security challenges such as access authentication, privacy preservation, traceability, unlinkability, and identification and revocation of malicious nodes.
In the aspect of security mechanisms for VANETs, access authentication and privacy preservation have been paid more and more attentions. How to construct concrete scheme of access authentication and privacy preservation has become a hotspot. 13
Related work
In previous years, some scholars have proposed a number of typical anonymous-certificates-based schemes14–16 for VANETs. There is no doubt that the utilization of certificates improves the efficiency of verification. However, with high overhead of certificate management as well as key distribution and management, all of the proposals are not suitable for deploying VANETs in a large scale. Furthermore, some schemes have a high requirement of OBU storage. Instead, several group-signature-based VANETs authentication schemes17–21 are proposed. Depending on group signature mechanisms, the authentication schemes may eradicate the high certificate management overhead and preserve the user privacy. In addition, each group member is able to sign the message to represent for the group. Thus, the adversary may not identify the signer according to the signed message. Nevertheless, once the number of vehicles increases dramatically, the packet loss rate is increased simultaneously. In recent years, ID-based cryptography (IBC) is put forward as a rising form of public key cryptography. 22 The most important ascendancy of IBC is that it streamlines the key management burden compared to traditional certificate-based public key systems. 23 A number of identity-based authentication solutions for VANETs are then put forward.24–30 But, there are still no mature solutions for VANETs to guarantee both security and high efficiency. In addition, the schemes have defects in preserving privacy and identifying and revoking malicious node. Moreover, few access authentication schemes combining edge computing with VANETs have been proposed.
Different from the above reported schemes, we have published an article 31 in IMIS 2017: an anonymous access authentication scheme (AAAS) for VANETs Based on identity-based short group signature (ISGS), 32 which could ensure efficient access authentication and strong privacy preservation. In this article, a novel AAAS for VANETs under edge computing based on ISGS mechanism is proposed, which could achieve efficient access authentication and formidable privacy preservation. Besides, in this article, we extend the paper 31 published in IMIS 2017 and combine access authentication with edge computing together with security proof as well as more comprehensive performance analysis. Specifically, the major contributions of this article are fivefold:
An AAAS for VANETs under edge computing is proposed, in which the usage of identity-based group signature and multiple pseudonyms can provide strong privacy preservation for users.
We design a new VANETs framework combining with edge computing, in which, RSUs play the role of edge computing nodes and the computation burden of OBUs is thus reduced.
We present a new identification and revocation approach of malicious node through evaluation mechanism.
The security analysis is carried out to indicate that our proposed scheme may meet the security and privacy needs in VANETs. In addition, the security proof of the fundamental protocols is presented through Syverson–Van Oorschot (SVO) logic.
Finally, the analysis of computation cost, transmission overhead, and serving ratio are performed to illustrate that our scheme performs better in both V2I and V2V authentication compared with previously proposed schemes for VANETs.
The rest of this article is arranged as given below. Section “Preliminaries” elaborates the related preliminaries. In section “The proposed anonymous authentication scheme,” we introduce the trust model, security requirements, and the details of the proposed access authentication scheme. The security proof of the fundamental protocols and formal security analysis are given out in section “Security proof and analysis.” In section “Performance analysis,” the comparisons of performance analysis are carried out. Finally, the conclusion is drawn in section “Conclusion.”
Preliminaries
We utilize CC signature mechanism for authentication between OBUs and RSUs, and ISGS mechanism for authentication among OBUs. The corresponding cryptography building blocks will be presented in this section.
Bilinear pairing
The bilinear pairing
In this scheme, elliptic curve–based mathematical hard problem in cryptography is also involved:
CC signature
CC signature mechanism,
32
a type of identity based signature (IBS) mechanism, which includes four algorithms
ISGS
The ISGS was proposed by Song et al., 33 which is based on bilinear pairing and designed to guarantee the privacy preservation of group members. The specific algorithm are as below:
Given a additive group Selects the random generator Generates
Assuming a new member GM calculates
For a given message Chooses a random number Computes
For a signature Computes: Checks the equation
The proposed anonymous authentication scheme
In this article, we extend the paper 31 to combine VANETs anonymous access authentication with edge computing and propose a novel AAAS for VANETs under edge computing (AAAS). In this section, we mainly introduce the detail of the proposed authentication scheme.
Trust model and assumptions
The general VANETs consist of three types of network entities: OBU, RSU (edge node), and TA.
The trust model of the proposed scheme is shown in Figure 2. TA is one-way trusted to both RSU and OBU. TA and RSU are connected through a secure wired channel, while RSU and OBU communicate over the wireless channel and distrust to each other. Amid OBUs, they correspond via ad hoc and do not trust each other. Suppose that the TA is entirely trusted and that only TA can modify the information in the TPD integrated on the OBU.

Trust model.
We assume that the adversary only has the common attack capabilities, such as impersonation, tampering, replay, and key-stealing attack.
Security requirements
As a public transportation network, VANETs face many security issues. In order to achieve the purpose of anonymous authentication, VANETs must meet the following security requirements:
The proposed scheme in this article try to meet the above requirements to be a complete solution.
AAAS
The AAAS proposed in this article is based ISGS to achieve the purpose of anonymous authentication. AAAS comprises five parts:
Notation and meaning.

OBU: on-board unit; RSU: roadside unit.
System initialization
During system initialization, TA generates and publishes the public parameters as below:
TA opts for two large primes
TA generates cyclic groups
TA randomly selects a generator
TA selects four hash functions
TA publishes the system public parameters
Registration
For the purpose of achieving mutual authentication, OBU and RSU should register to TA:
OBU sends TA calculates TA sends OBU stores
RSU sends the real identity TA generates the private key TA sends RSU saves
V2I authentication protocol
The V2I authentication protocol between OBU and RSU is executed when the mobile OBU moves to the wireless communication range of the accessed RSU. RSU is playing the role of edge node which owns richer computational power than OBU. During V2I authentication, we try to shift the large computational pressures from OBU to RSU to gain a better overall performance. As shown in Figure 3, the authentication protocol is composed of following steps:
RSU generates
RSU periodically broadcasts
When receiving {
OBU sends
After getting the message from OBU, RSU checks if
RSU sends
After getting
Hence, we can see that edge computing has the unique feature to reduce the calculating pressure of vehicle terminal to guarantee the users demand for real-time authentication.

V2I authentication protocol.
V2V authentication protocol
After V2I authentication, the accessed legal OBUs get their pseudonyms and group signing key pairs. Thus, OBUs may certificate each other for secure communication, which is known as V2V authentication. As shown in Figure 4, the V2V authentication (between
After getting {
After receiving

V2V authentication protocol.
Identification and revocation of malicious nodes
The identification and revocation of malicious nodes is a major challenge for VANETs. The process in this article is shown in Figure 5 below:
When a node
After receiving a
After getting a
After getting the real identity of
Finally, TA broadcasts

Identification and revocation of malicious node.
Security proof and analysis
Formal security analysis and proof of security for the proposed core protocols will be presented in this section. First, we will use SVO logic 35 to prove the security of the fundamental protocols. Then the further security analysis will be provided to prove that our scheme may satisfy the security requirements described in section “The proposed anonymous authentication scheme.”
Foundation of SVO logic
SVO logic is more intuitive, convenient, and practical than other logic analysis methods in the following aspects:
The axioms in SVO can be adjusted or extended easily to meet the security proof needs rather than Burrows–Abadi–Needham (BAN) 36 or other logical approaches.
SVO is detailed and legible, which helps to accurately express the actual meaning of the protocol, thus avoid the misunderstandings.
SVO is rigorous and reliable, and the semantics is clear.
SVO rules
SVO has two initial rules:
The separation rule
The necessity of rules
SVO axiom
For any subject
Believes: Ax1: Ax2:
Source association: Ax3: Ax4:
Key agreement: Ax5: Ax6:
Receiving: Ax7: Ax8: Ax9:
Seeing: Ax10: Ax11: Ax12:
Comprehending: Ax 13:
Saying: Ax14: Ax15:
Jurisdiction: Ax16:
Freshness: Ax17: Ax18:
Nonce-verification: Ax19:
Symmetric goodness of shared keys: Ax20:
SVO objectives
The following SVO objectives are given according to the security requirements of our scheme to prove the security of V2I and V2V protocols:
SVO objectives of V2I protocol:
SVO objectives of V2V protocol:
Security proof of the authentication protocols
Initial assumptions
In order to prove the security of V2I and V2V protocols, first, the assumptions are given below:
Assumptions of V2I protocol:
Assumptions of V2V protocol:
Security proof of V2I authentication protocol
From the assumptions, we can get:
S1: Obtain from P1, P2, P11, Ax1, Ax14, and
S2: Obtain from S1, P3, and Ax1.
S3: Obtain from P7, P9, and Ax7.
S4: Obtain from S2, S3, P2, Ax4, Ax14, and Nec.
S5: Obtain from P5, P7, Ax1, Ax9, and Ax17.
S6: Obtain from S4, S5, Ax1, Ax19, and Nec.
S7: Obtain from P8, Ax1, Ax1, Ax7, and Nec.
S8: Obtain from S2, S7, P4, P9, and Ax1.
S9: Obtain from S8, P4, Ax1, Ax5, and
S10: Obtain from P8, P6, Ax1, Ax10, Ax11, Ax12, and Nec.
S11: Obtained from the definitions of S9, S10, Ax1, and
S12: Obtain from S5, Ax18
S13: As defined by S3, S12, P10, Ax1, and Confirm
S14: Obtain from S7, S10, Ax1, Ax8, and
S15: Obtain from P10, S13, S14, and Ax13.
S16: Obtain from S14, S15, Ax19, and Nec.
The SVO object of
Security proof of V2V authentication protocol
From the assumptions, we can get:
S1: Obtain from P12, P13, P22, Ax1, Ax14, and
S2: Obtain from S1, P14, and Ax1.
S3: Obtain from P18, P20, and Ax7.
S4: Obtain from S2, S3, P13, Ax4, Ax14, and
S5: Obtain from P16, P18, Ax1, Ax9, and Ax17.
S6: Obtain from S4, S5, Ax1, Ax19, and
S7: Obtain from P19, Ax1, Ax1, Ax7, and
S8: Obtain from S2, S7, P15, P9 and Ax1.
S9: Obtain from S8, P15, Ax1, Ax5,
S10: Obtain from P19, P17, Ax1, Ax10, Ax11, Ax12, and
S11: Obtain from the definitions of S9, S10, Ax1, and
S12: Obtain from S5 and Ax18.
The SVO object of
Security analysis
We carry out the security analysis from the following aspects in terms of the security requirements:
From the above analysis, we can see that the proposed scheme (AAAS) can meet the security requirements described in section “The proposed anonymous authentication scheme.” Thus, the proposed AAAS is considered to be complete.
Performance analysis
The performance analysis of the proposed scheme (AAAS) is elaborated from three aspects: computation cost, transmission overhead, and serving ratio. Besides, the comparison analysis is presented among AAAS, CPAS, 30 ACPN, 27 and PACP. 37
Computation cost
Computation cost is the amount of computations made by related network entities during the V2I and V2V authentication procedure. With the deployment of edge computing, the computation cost on RSU side is not critical since RSU usually owes rich computation resource. Thus, in this section, we mainly give the comparison analysis of computation cost on vehicle side among different schemes. The main operations involved in the authentication of the schemes includes: bilinear pairing, hash-to-point, encryption, point addition, and point multiplication. Compared with the above operations, the cost of hash, point addition, and symmetric encryption can be neglected. In order to facilitate the expression, Table 2 presents the symbols and execution time (in milliseconds) for a curve with
Symbols and description.

RSA: Rivest–Shamir–Adleman.
During V2I authentication of AAAS, OBU verifies the CC signature by checking

In AAAS’ V2V authentication, OBU first generates the ISGS signature as

In V2I authentication of CPAS, OBU generates the digital signature as

While during the V2V authentication of CPAS, OBU generates the signature as
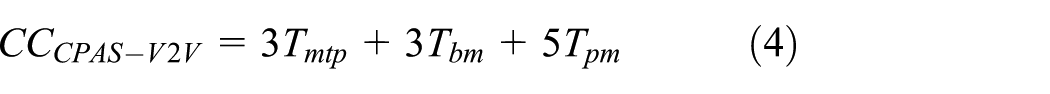
In the V2I authentication of ACPN, OBU generates a pseudonym as

During V2V authentication of ACPN, OBU generates the online signature as

During V2I authentication of PACP, OBU generates an IBS signature and verifies the signature from RSU. In addition, OBU executes the encryption and decryption operation as

In the V2V authentication of PACP, OBU do the same encryption and decryption operations as that in V2I authentication. Besides, OBU generates a Boneh–Lynn–Shacham (BLS) signature and verifies the BLS signature from RSU. To sign and verify a BLS signature, OBU executes 1 hash-to-point operations, 1 point multiplication operations, 1 hash-to-point operations, and 2 bilinear pairing operations. Therefore, we can get the computation cost of PACP in V2V authentication

To illustrate the better performance of the proposed AAAS scheme in the V2I and V2V authentication, we compare the computation cost of AAAS in V2I and V2V authentications with CPAS, ACPN, and PACP as shown in Table 3. According to the results, it is obviously that the AAAS scheme we proposed owes lower computation cost compared to the other three in V2I authentication. While during V2V authentication, the AAAS scheme has lower computation cost compared with CPAS, PACP, but slightly higher than ACPN. Furthermore, the total computation cost of the proposed AAAS scheme is lower than CPAS, ACPN, and PACP.
Computation cost analysis.

AAAS: anonymous access authentication scheme.
Transmission overhead
The transmission overhead is analyzed by the size of total messages transmitted during V2I and V2V authentication procedures. For ease of description, the following assumptions are given out in Table 4 with size of
AAAS: during V2I authentication, OBU receives

Assumptions.

OBU: on-board unit.
In the V2V authentication of AAAS,

CPAS: in V2I authentication, OBU receives

During V2V authentication of CPAS, OBU sends

ACPN: in V2I authentication, OBU receives

While during V2V authentication of ACPN, OBU sends

PACP: during V2I authentication of PACP, OBU sends

In the period of V2V authentication of PACP, OBU sends

Comparison with CPAS, ACPN, and PACP, the proposed AAAS scheme has the lower transmission overhead in both V2I and V2V authentication as shown in Table 5.
Transmission overhead analysis.

AAAS: anonymous access authentication scheme.
Serving ratio
During V2I authentication, RSU provides service for OBU. To weigh the capability of RSU providing service for OBU, we denote it as the serving ratio. In order to compare the serving ratio of RSU providing access service for vehicles of different schemes in the V2I communication, we give some symbols and parameters as shown in Table 6.
Notations of symbol.
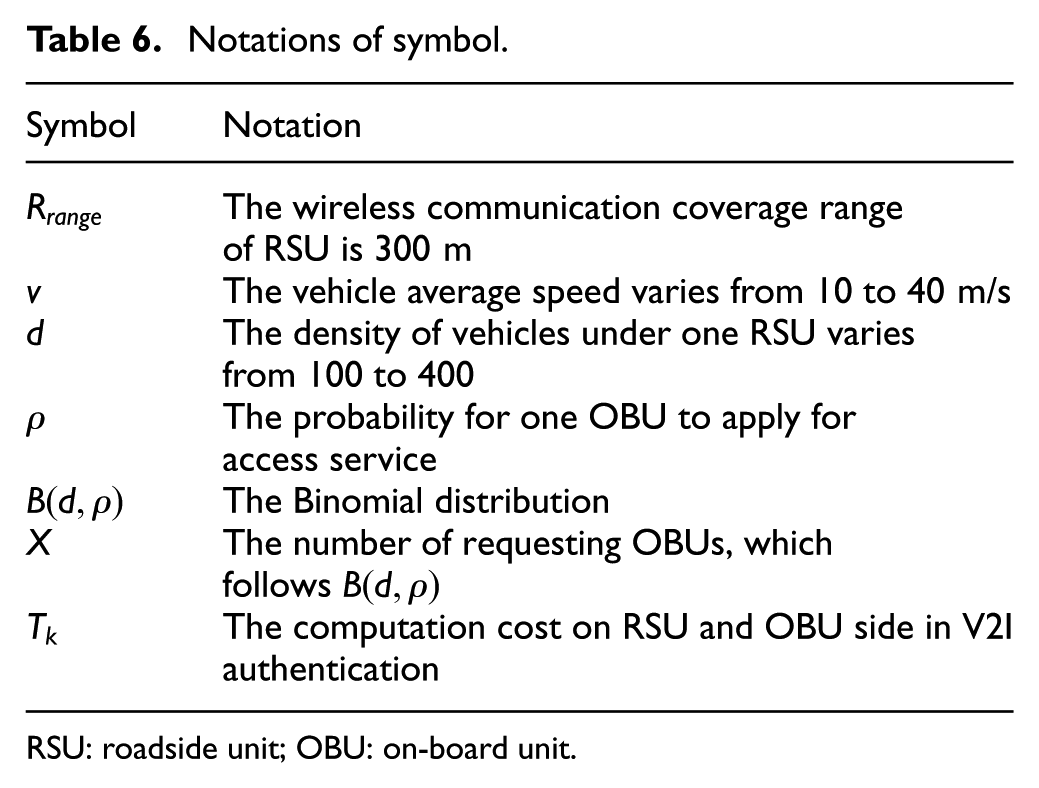
RSU: roadside unit; OBU: on-board unit.
We borrow the approach from 12 for the analysis of serving ratio below
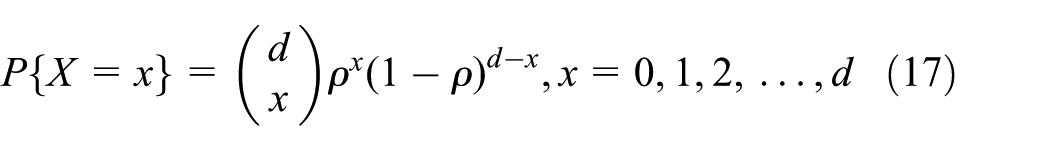

where

To weigh the capability of serving for OBU, we assume the maximal number of access services that the RSU can provide as

Thus, the number of completed access services denoted as

Therefore, the serving ratio
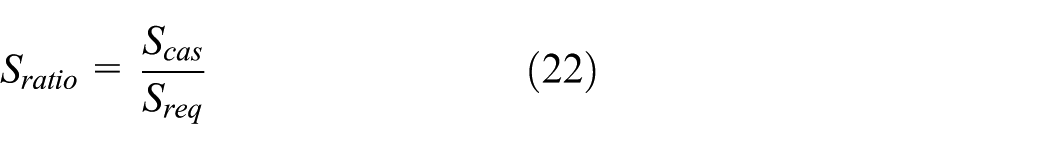
Then,

Based on the execution time results from section “Computation cost,” we analyze the serving ratio with different computation cost on RSU side:
Assume the low computation cost of the given schemes on RSU side as 19.612 ms, which is derived from Table 3



Assume that the high computation cost of given schemes on RSU side is 64.236 ms from Table 3



Finally, the comparison of serving ratio is given among the schemes as Figures 6 and 7. From the results, it is obvious to get that AAAS has better performance in serving ratio with the increasing vehicle speed and vehicle density. Besides, the serving ratio will be lower with increasing computation cost on RSU side. However, in the future, with the rapid development of edge computing, the computation on RSU side will have a sharp decline to improve serving ratio.

Serving ratio with low computation on RSU as 19.612 ms.

Serving ratio with high computation on RSU as 64.236 ms.
Conclusion
In this article, we combine the edge computing with VANETs and propose a novel AAAS for VANETs under edge computing that focus on preserving privacy and improving the access authentication efficiency. We adopt the ISGS mechanism to effectively protect the privacy of users in both V2I and V2V authentication procedures. The reputation mechanism is also introduced to identify and revoke malicious nodes. The security of the authentication protocols is proved by SVO logic. Compared with other typical schemes, the proposed scheme owns better performance.
However, the proposed scheme does not provide a fine solution to the preservation of user’s location privacy. In the future research, we will concentrate on this issue to pave the way for the wide deployment of VANETs. Besides, we will explore more efficient group signature mechanisms (such as IBV 38 ) and a new cryptography mechanism to improve the efficiency of anonymous authentication.
Footnotes
Handling Editor: Qiang Duan
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by National Natural Science Foundation of China under (grant number: 61402095). This work was, in part, supported by the Soonchunhyang University Research Fund.
