Abstract
Cluster-based wireless sensor networks have advantages of scalability and efficient communication. However, a major security risk to cluster heads is a malicious code injection attack through which an adversary can completely control a cluster network to deliver fake data and obtain private data. Memory attestation scheme is an effective mechanism for attesting the firmware integrity of an embedded device. Unfortunately, existing hardware-based remote attestation scheme relying on a trusted platform module incurs a considerable storage overhead to cluster heads. Therefore, this article proposes a lightweight hardware-based remote attestation scheme that comprises two remote attestation protocols. A lightweight hardware security module without executing any complicated cryptographic computation is employed and can substantially reduce the development cost and energy consumption compared with the trusted platform module. In the proposed scheme, a base station can attest each individual cluster head while all cluster nodes can simultaneously attest their cluster head in regular intervals. Performance analysis indicates that the storage requirement for cluster heads is independent of the number of attestation sessions. Furthermore, the computational cost of cluster nodes for the proposed scheme is comparable to that of the trusted platform module–based scheme. The proposed scheme is particularly suitable for long-term applications based on lightweight cluster heads.
Keywords
Introduction
Wireless sensor networks (WSNs) have been extensively employed in many mission-critical information systems 1 such as battlefield surveillance systems, healthcare monitoring systems, and advanced metering infrastructure. A WSN comprises a few base stations (or sinks) and a high number of sensor nodes for collection of environmental and physical data of a specific geographical area. Sensor nodes are generally constructed on the basis of the embedded devices with limited resources in computational power, memory capacity, and energy. The base stations have more computational capability and memory capacity compared with sensor nodes and deliver the sensed data to a backend management center for additional purposes.
A WSN is organized into several clusters for providing an energy-efficient deployment. 2 A low number of heterogeneous nodes serves as cluster heads. A cluster head is assigned to each cluster and aggregates the sensed data periodically provided by cluster nodes deployed in the same cluster. Furthermore, a cluster-based WSN has advantages of scalability and efficient communication. 3 In general, the cluster nodes are deployed in a human-unreachable geographical area, and the cluster head acts as a gateway to manage network packets in a cluster; however, the cluster head becomes an attractive target for an adversary intent on compromising a cluster. Injection of malicious codes4–6 into a cluster head enables the adversary to completely control the compromised cluster head, which then delivers the forged data to the base station, consequently compromising the security of the cluster-based WSN.
Remote attestation scheme is an effective mechanism that enables a verifier to remotely verify the firmware integrity of a prover. The prover convinces the verifier of its trustworthiness by providing an expected checksum of the program memory content. Software-based remote attestation schemes7–9 employ a software-only verification function used for generating the checksum and depend on exact elapsed time measurement. However, such schemes are suitable only for one-hop communication between the verifier and the prover. Hardware-based schemes10–12 rely on a trusted platform module (TPM) complying with the ISO/IEC 11889 standard. 13 TPM is a high-level hardware security module (HSM) consisting of several cryptographic components, such as asymmetric key cryptosystem, pseudorandom number generator, and one-way hash function. In a cluster-based WSN, each cluster head can be equipped with a TPM for the purpose of remote attestation. However, the TPM-based scheme 10 incurs a considerable storage overhead to the cluster heads because several hash values must be reserved.
This study focused on verifying the firmware integrity of a cluster head and considered the malicious codes residing in the program memory of a cluster head. Injecting malicious codes into the data memory engenders an unstable system state and restricts the behavior of the malicious codes because the data memory has limited capacity, reserved variables, and function stacks. 14 The security concerns addressed in this study were twofold:
Before delivering the sensed data, all cluster nodes must ensure the trustworthiness of their cluster head for preventing the sensed data from being captured. Therefore, a “bottom-up” remote attestation protocol is proposed for attesting the cluster heads in regular intervals (e.g. 10 min).
Assume that the cluster nodes detect the existence of a compromised cluster head; the abnormal event cannot be reported to the base stations through the compromised cluster head. Therefore, a “top-down” remote attestation protocol that enables the base station to attest each individual cluster head is presented.
This article proposes a lightweight hardware-based remote attestation scheme that comprises the aforementioned bottom-up and top-down remote attestation protocols. In the proposed scheme, each cluster head is equipped with a lightweight HSM acting as a remote agent appointed by the base station. Such a remote agent need not execute any complicated cryptographic computation and only depends on some storage of parameters as well as basic arithmetic and logic operations. The proposed remote agent can therefore reduce the development cost and energy consumption compared with the TPM-based one. The performance analysis indicates that the energy consumption by the cluster heads is very low while the storage requirement for the cluster heads is independent of the number of attestation sessions. Furthermore, the computational cost of the cluster nodes is comparable to that of the TPM-based scheme. 10 The proposed scheme is particularly suitable for long-term applications based on lightweight cluster heads.
The remainder of this article is organized as follows. Section “Review of TPM-based remote attestation scheme” briefly reviews the basics of trusted computing on the basis of TPM and the scheme of Krau
Review of TPM-based remote attestation scheme
Basics of trusted computing
The TPM is a cryptographic chip that is embedded on the motherboard of a primary platform and provides several security functionalities. Transitive trust is an integrity measurement process performed by the TPM. While the primary platform boots, the integrity measurement process is executed to measure each component in an order of booting sequence (e.g. BIOS ⇒ bootloader ⇒ operating system ⇒ applications). The measurement result (i.e. a 160-bit cryptographic digest) is then stored in a set of specialized platform configuration registers (PCRs) within the TPM. The TPM updates the measurement result by extending the current value stored in the PCR, that is, new PCR-stored value = H(current value ∥ measured result), where H(·) is a cryptographic hash function. Each time the primary platform reboots, all measurement results are reset. Therefore, occurrence of expected measurement results implies the trustworthiness of the primary platform.
The TPM provides a sealed storage technique, which encrypts or decrypts accordingly certain sensitive data associated with specific platform configurations. A sealing command uses the indices of several PCRs as inputs and involves a nonmigratable asymmetric key pair (e.g. RSA key pair) permanently stored in the TPM for encrypting or decrypting the sensitive data. Consider the following executed sealing command13,15
where
where
Review of the scheme of Krau
et al
Krau
PBAP
In the PBAP, each cluster head is equipped with a TPM, and all cluster nodes simultaneously attest their cluster head at each time point. The PBAP employs the one-way hash chain and sealed storage techniques. The one-way hash chain technique involves repeatedly executing a one-way hash function over a secret seed S. For example, if a one-way hash function (e.g. SHA-1) is iteratively applied n times to S, each hash value in the one-way hash chain is denoted by
Before the deployment of the cluster heads, each cluster head preloads a one-way hash chain, and all related hash values are encrypted through the sealed storage technique. When a cluster is deployed, each cluster node keeps the hash value
IAP
The IAP enables a base station (or a cluster node) to attest a cluster head and is designed on the basis of the challenge-response technique. Before the deployment of the cluster heads, the base station and each cluster head establish a unique symmetric key
Security assumptions and attack model of the cluster-based WSN
In a cluster-based WSN, the base station is assumed to be free from an adversary and communicates with the cluster heads through a multihop communication, whereas the cluster nodes communicate with their cluster head through a one-hop communication. Therefore, the communication between the cluster head and the cluster nodes is reliable. Each cluster is assumed to be deployed through a secure initialization phase within a reasonably short period. In the initialization phase, the cluster head and all cluster nodes establish a common symmetric key
A cluster head comprises two independent computing platforms: a primary platform and a lightweight HSM acting as a remote agent. The primary platform performs regular operations (e.g. data aggregation and command distribution) and can execute a one-way hash function and symmetric key cryptography (e.g. advanced encryption standard, AES). The remote agent is tamper-resistant and executes attestation-related operations. An external storage out of the primary platform can be used to store the sensed data. The access time of the external storage is practically longer than that of the memory inside the primary platform.
The adversary can remotely inject malicious codes into a fraction of cluster heads, and the compromised cluster heads can collude with each other as well as the adversary to eavesdrop, replay, and modify transmitted messages through wireless communication. The adversary is assumed to be aware of the exact program memory content of the cluster heads and completely controls the compromised cluster heads. Same as described in prior elapsed-time-measurement-oriented attestation schemes,7,17 the adversary cannot deploy any powerful computing device in the WSN because introducing such computing devices increases the possibility of being detected. However, a few fake cluster heads with comparable computing power as those genuine cluster heads can be deployed in the WSN. Physical attacks on cluster heads such as speeding up the clock rate, enlarging the memory capacity, or adding hardware components will substantially consume the energy of these cluster heads. So, the lifetime of these cluster heads will be reduced and accordingly the attacks might become less powerful. Therefore, based on the same assumption made in most recent literature of remote attestation,18,19 this study did not consider the physical attacks. Furthermore, a countermeasure to prevent the cluster nodes from being compromised did not be considered in this study because a potential attack can be achieved through a compromised cluster head (i.e. propagation of malicious codes through a compromised cluster head). A trusted cluster head can serve as a firewall to protect the cluster nodes against malicious code infection or as a verifier to attest each cluster node by employing existing software-based remote attestation schemes7,8 that are particularly suitable for one-hop communication in a cluster.
The proposed lightweight hardware-based remote attestation scheme
The proposed scheme depends on a lightweight HSM, which acts as a remote agent appointed by the base station. This section defines three security requirements of the remote agent used for providing a reliable integrity validation. In this study, we also propose a hierarchical key management mechanism to reduce the storage requirement of the remote agent. Table 1 lists the notations used in the remainder of this article.
Notations.

Integrity validation using the remote agent
Security requirements of the remote agent
The remote agent is tamper-resistant and is equipped with a processor and internal memory used for storing the firmware, temporary parameters, and critical sensitive parameters (CSPs). The security requirements of the remote agent are described as follows:
Access control. To prevent unauthorized access, any data stored in the remote agent cannot be read or modified without permission. In general, the access control mechanism can be implemented on the basis of an authentication scheme. Each remote agent preloads a unique authentication key ATK shared with the base station and then authenticates the requester depending on ATK when accessing stored data. Therefore, an entity with ATK is authorized to access the data stored inside the remote agent.
Built-in independent system clock. The remote agent has a built-in independent system clock, which is resistant to external tamper. When the integrity validation process is executed, the built-in independent system clock is used for measuring
CSPs. Before the deployment of the WSN, each remote agent preloads three CSPs for integrity validation purpose: (1) a unique CRP, (2) a unique MK, and (3)
The proposed integrity validation scheme
In this study, the trustworthiness of a
Before the deployment of the

where Chall, M[j],
When attesting a
Hierarchy of the working keys
Two symmetric keys, namely
In the initialization phase,
The proposed bottom-up remote attestation protocol
The bottom-up remote attestation protocol enables all
Step 1. When a certain period is reached, the
Step 2. An integrity proof
Step 3. Every
The proposed top-down remote attestation protocol
In general, the
Step 1. The
Step 2. The attested
Step 3. The
Security analysis
The security of the proposed scheme highly depends on the integrity validation process. If an infected
In a precomputation attack,
8
the adversary can precompute an expected checksum before compromising a target
The collusion attack
8
enables two (or several) compromised
In a code compression attack,
21
the adversary can compress the original firmware codes installed within a compromised
The random paddings deployed in the unused program memory space can protect the proposed integrity validation process from a malicious code hiding attack. In the demonstration of Castelluccia et al., 21 the malicious codes can be hidden by exploiting return-oriented programming technique. The malicious codes can store its copy in the external storage and remove itself from the unused program memory space. However, once the malicious codes reside in that memory space, the random paddings are overwritten and cannot be recovered. Such a corrupted memory state leads to an incorrect checksum.
In an on-off attack,
22
a compromised
The infected
Replay attack by capturing transmitted messages can be prevented in the proposed scheme because the one-time tokens (i.e. IPF and
In contrast to the IAP,
10
in the proposed top-down remote attestation protocol, the encrypted identifiers
Performance analysis
In this section, we first estimate the energy consumption by a
Analysis of energy consumption by cluster head
In this analysis, we have the following assumptions. Each
The analysis of power consumption focuses on the primary cryptographic computations executed on the
Cluster head storage analysis
The notations of the parameters used in the PBAP and IAP are defined as follows.
In the proposed scheme, the bit length of ATK, MK,
Cluster node computation analysis
In the proposed bottom-up attestation protocol, a
In the PBAP, a
Comparison between the proposed scheme and the TPM-based scheme.

TPM: trusted platform module.
Other related work of remote attestation schemes
Most existing remote attestation schemes focus on a distributed WSN and involve a verifier (a base station) and a prover (a sensor node). The proposed scheme particularly combines the advantages of these schemes. Table 3 presents a summary of the existing remote attestation schemes and proposed scheme in terms of design properties.
Summary of the existing schemes and the proposed scheme.
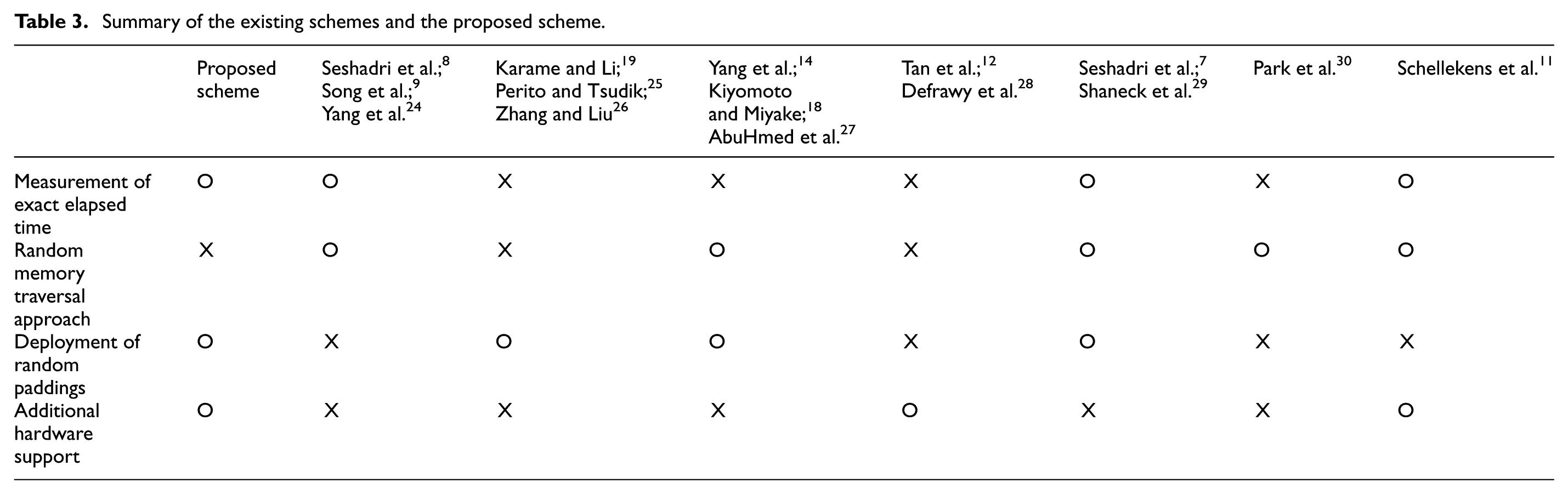
In the time-measurement-oriented software-based schemes,7,8,29 a correct checksum must reach the verifier in a timely manner. However, the measurement of exact elapsed time is susceptible to unpredictable transmission delay, particularly in multihop communication. While an improved time-measurement-oriented scheme has been proposed, 24 but unfortunately this scheme involves all nodes along the forward and the backward paths of attestation and incurs a high system complexity. Song et al. 9 proposed a one-way memory attestation scheme for addressing two man-in-the-middle attacks; however, such a scheme is vulnerable to an impersonation attack.
To protect the program memory and data memory from being corrupted, a segment of random paddings can be deployed in these memory spaces.19,25,26 The prover must provide an associated guarantee of completing the random padding process; otherwise, the prover will be concluded as a compromised one. A memory replication attack can be prevented by a copy-proof memory section. 30 The accessed memory outputs valid data only if the prover receives an indicator (i.e. flag = 1) from the verifier; otherwise, it outputs random data.
Yang et al. 14 employed the threshold secret sharing technique to design a distributed attestation scheme, in which the prover is attested through a collaboration of its neighbors. AbuHmed et al. 27 improved the block-based pseudorandom memory traversal approach 14 and proposed two remote attestation schemes without depending on the measurement of exact elapsed time. Kiyomoto and Miyake 18 proposed a lightweight distributed attestation scheme. In such a scheme, a compromised prover terminates itself to prevent the propagation of malicious codes after being detected.
Hardware-based remote attestation schemes usually employ a dedicated HSM (e.g. a TPM), which can be a tamper-resistant storage or an isolated environment. Both TPM-based schemes11,12 have been proposed for attesting the system integrity of a primary platform. Defrawy et al. 28 proposed SMART relying on a dedicated circuit used for providing access control to a secret key. Such a scheme attests a fraction of the program memory content determined by the verifier and employs a read-only memory-resident verification function used for checksum generation.
Conclusion
Ensuring the trustworthiness of the cluster heads provides reliable data aggregation for the cluster-based WSN, and the trusted cluster heads can act as a firewall to protect the cluster nodes from malicious code injection attacks. This article presents a bottom-up and a top-down remote attestation protocols relying on a lightweight HSM. The cluster head can be attested periodically by the underlying cluster nodes and by the base station as well. The performance analysis indicates that the required storage size of the cluster heads is independent of the number of attestation sessions. Furthermore, the energy consumption by cluster heads is very low. The proposed scheme is particularly suitable for long-term applications based on lightweight cluster heads.
Footnotes
Acknowledgements
The authors would like to thank Mr. Chia-Wei Shih for his valuable discussion on our preliminary work of the proposed scheme.
Academic Editor: Vicente Traver
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research was supported, in part, by the Ministry of Science and Technology of the Republic of China under contract MOST 104-2221-E-008-057-MY2.





