Abstract
The concept of public key encryption with equality test was introduced at CT-RSA 2010. It has been used in many fields, especially in cloud storage. However, the previous schemes do not provide an effective authorization mechanism. To fill this gap, Ma et al. presented a public key encryption with equality test supporting flexible authorization based on the bilinear pairings. Recently, Lin et al. presented a pairing-free scheme that employs quadratic curve to perform the equality tests, which can achieve a trade-off between computational cost and storage space. In this article, we show that the equality test can be better performed by using a straight line, rather than a quadratic curve. Moreover, we simplify the encryption algorithm, as well as reduce the ciphertext storage space.
Introduction
Searchable encryption (SE) scheme, presented in 2004 by Boneh et al., 1 allows the server to check whether some messages contain specific keyword without retrieving entire messages. Subsequently, scholastic community presented many improved schemes.2–8 In 2007, Bellare and ONeill 9 conceptualized deterministic encryption (DE) for public-key encryption schemes, in which the encryption algorithm is executed in a deterministic manner. Later, DE was uplifted by Bellare et al. 10 and Boldyreva and ONeill 11 But, DE could not gain immense appreciations due to its deterministic approach.
With the development of cloud computing and outsourcing, traditional encryption schemes cannot provide the solutions for many applications such as splitting of database. To handle the prescribed issue, Yang et al. 12 proposed the notion of public key encryption with equality test (PKEwET) at CT-RSA 2010. This effective mechanism allows anyone to check whether two ciphertexts contain the same message without decryption. Tang 13 intensified PKEwET with finegrained authorization (FG-PKEwET), which authorizes two users to a semi-trusted proxy, who can perform the equality test on their ciphertexts. Later, an extension of FG-PKEwET was also put forward by Tang. 14 Besides, in the same year, Tang 15 presented a new primitive called all-or-nothing PKEwET (AoN-PKEwET), which authorizes the specific users to perform a plaintext equality test from their ciphertexts. Another perspective in the form of identity-based encryption with equality test (IBEwET) was proposed by Ma 16 that combines the concepts of PKEwET and identity-based encryption.
The privacy of users is an essential context that necessitates to be considered while designing an applied protocol. Therefore, Ma et al. 17 strengthened the concept of PKEwET by introducing flexible authorization, which is termed as PKEwET-FA. In his scheme, the author implemented different authorization policies along with a corresponding trapdoor for each authorization to perform the test algorithm. For instance, as described in Ma et al., 17 suppose Alice is a ciphertext receiver, then four types of authorization with different granularity can be described as follows:
Type 1. User-level authorization: All ciphertexts of Alice can be compared with all ciphertexts of any other receiver.
Type 2. Ciphertext-level authorization: A specific ciphertext of Alice can be compared with a specific ciphertext of any other receiver.
Type 3. User-specific ciphertext-level authorization: A specific ciphertext of Alice can be only compared with a specific ciphertext of a specific receiver, for example, Bob, but could not be compared with any ciphertext of any receiver other than Bob.
Type 4. Ciphertext-to-user (or user-to-ciphertext) level authorization: A specific ciphertext of Alice can be compared with all ciphertexts of any other receiver (or vice versa).
Recently, Lin et al. 18 proposed a new PKEwET-FA scheme, in which the equality tests are performed without bilinear pairing. More precisely, the author utilized the message for generating a quadratic curve and then used Shamir’s secret sharing scheme to perform the equality test. Although it gets rid of the dependence on bilinear pairings, however, the computational cost of this scheme is high due to the involvement of quadratic curve.
Motivation and contribution
In this article, we improve the scheme presented in Lin et al. 18 by replacing the quadratic curve with the straight line to reduce the computational cost. Moreover, we improve the scheme by simplifying the encryption algorithm while reducing the computation of the modular exponentiation. Comparing with Lin et al., 18 our proposed scheme is more efficient in terms of the equality test as well as with respect to encryption and decryption. Furthermore, the storage space of ciphertexts is also smaller than that of Lin et al. 18 We compare the presented scheme with the previous work and the result shows that our scheme is more efficient and robust.
Organization
The rest of this article is organized as follows. In section “Preliminaries,” Shamir’s secret sharing scheme and the related security model are discussed. In section “The proposed scheme,” we present our scheme and four types of authorization and prove the validity of the proposed scheme. In section “Security,” we provide the security proof of presented scheme. In section “Performances analysis,” a detailed analysis of the presented scheme and comparisons with other schemes are presented. Finally, concluding remarks are given in section “Conclusion.”
Preliminaries
Definitions
Definition 1
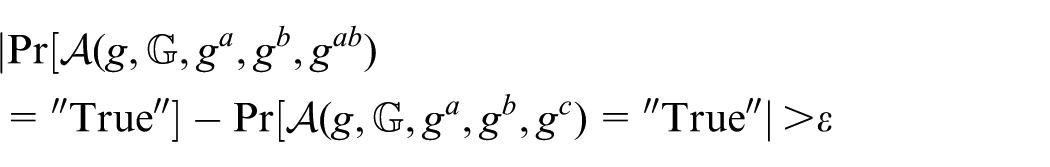
Decision Diffie-Hellman (DDH) Problem: Let
We say that the group
Definition 2 (Correctness)
If a
For any
For any ciphertexts Type 1 Authorization. Given
Type 2 Authorization. Given
Type-3 Authorization. Given
Type 4 Authorization. Given
For any ciphertexts Type 1 Authorization. Given
is negligible Type 2 Authorization. Given
is negligible Type 3 Authorization. Given
is negligible Type 4 Authorization. Given
is negligible.
Shamir’s secret sharing scheme
Shamir’s
Given t distinct points
Shamir’s scheme is defined for a secret
Security models
We recall the security models of PKEwET-FA defined in Ma et al.
17
It consists of six algorithms: Setup, KeyGen, Encrypt, Decrypt,
Two types of adversaries for the security of PKEwET-FA are described as follows:
Type I adversary. For Type-α (α = 1, 2, 3) authorization, with Type-α trapdoor information, the attacker cannot recover the plaintext from the challenge ciphertext.
Type II adversary. For Type-α (α = 1, 2, 3) authorization, without Type-α trapdoor information, the adversary cannot decide
First, we define one-way against chosen-ciphertext attack (OW-CCA) security for Type-α (α = 1, 2, 3) authorization against Type I adversary in PKEwET-FA as follows.
Game 1
Suppose that

The game between
Here,
and
The advantage of
Definition 3
For
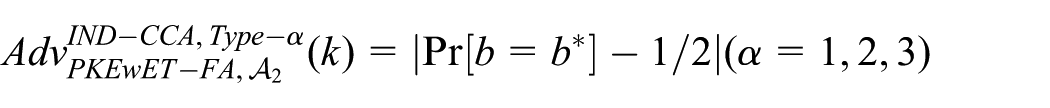
Next, we define the indistinguishable against chosen-ciphertext attacks (IND-CCA) security for Type-α (α = 1, 2, 3) authorization against Type II adversary in PKEwET-FA as follows.
Game 2
Suppose that

The game between
Here,
and
The advantage of
Definition 4
For
Notice
The aim of our scheme is to perform equality test for the messages corresponding to the ciphertexts of different users, which can be used in multi-user settings in a public key encryption.
The proposed scheme
Here, we describe our scheme in detail.
Let
Select hash functions:
The user’s key pair:
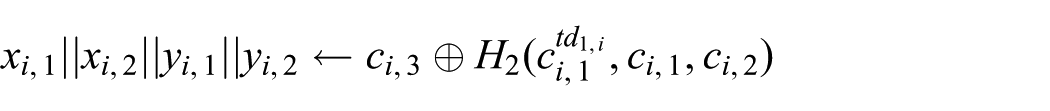
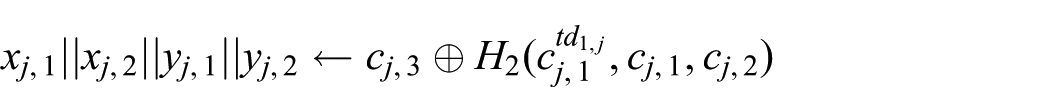
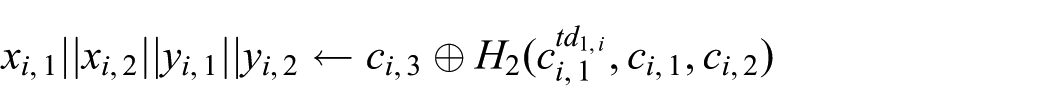
Use
Use two points
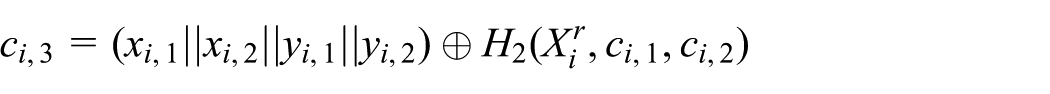
Choose
Choose a random number
Then, it uses M to create
Suppose
1. Type 1 Authorization • Auth1
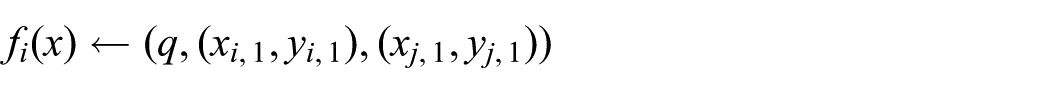
• Test1
Then, it outputs 1 if
2. Type 2 Authorization • Auth2
• Test2
Then, it outputs 1 if
3. Type 3 Authorization • Auth3
where • Test3
Then, it employs the Lagrange interpolation coefficients to compute
Finally, it tests whether or not
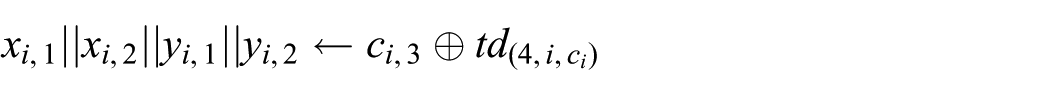
4. Type 4 Authorization • Auth4
Aut4
• Test4
Then, it outputs 1 if
Theorem 1
According to Definition 2, our proposed
Proof
Here, we prove that our scheme satisfies the three conditions, as defined in Definition 2:
1. It is not difficult to check that the first condition is satisfied.
2. Considering the second condition, for any
For any message
If
Type 1 Authorization: With
Therefore,
Type 2 Authorization: With
Therefore,
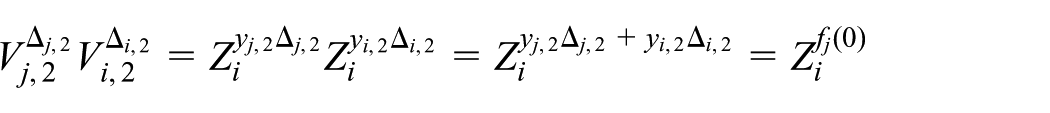
Type 3 Authorization: With
and
where
with
Therefore,
Type 4 Authorization: With
Therefore,
3. For the third condition, the following scenarios hold: Type 1 Authorization: If Type 2 Authorization: If Type 3 Authorization: If Type 4 Authorization: If
Security
Scheme security
In this section, we prove the security of our proposed scheme.
Theorem 2
Our proposed scheme is OW-CCA secure based on DDH assumption in the random oracle model for
Proof
Suppose
Let
Setup.
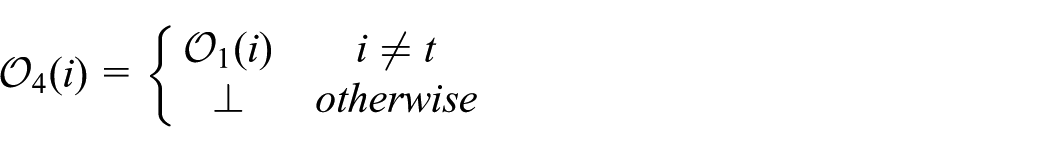
Phase 1.
If Otherwise, Decryption key queries retrieval (i): Decryption queries ( If Else If each tuple
Using Using the two points: Test whether Else, it Authorization queries ( For For For
where
Challenge. Once
Finally, it provides
4. Phase 2. During decryption key queries retrieval, During decryption queries process,
5. Guess.
Theorem 3
Our proposed scheme is IND-CCA secure based on DDH assumption in the random oracle model for
Proof
Suppose that
Let
Setup.
Phase 1.
If Otherwise, Decryption key queries retrieval (i): Decryption queries If Else If each tuple
Uses Constructs Tests whether Else, it Authorization queries ( In Type 1 authorization, with given i, In Type 2 authorization, given In Type 3 authorization, given
where
Challenge. Once
Finally, it provides
4. Phase 2. During decryption key queries retrieval, During decryption queries phase, For a In Type 1 authorization queries, In Type 2 authorization queries, In Type 3 authorization queries,
5. Guess.
When
Authorization security
In this section, we analyze the security of authorization.
In Type 4 authorization, the authorized party has
In Type 3 authorization, the authorized party has the followings
and
where
In Type 2 authorization, the authorized party has
Performances analysis
In this section, we discuss the efficiency of our scheme. According to the experimental results in previous studies,19–21 a bilinear pairing costs about five times than an exponentiation. Computational complexity in modular exponentiation is higher than in modular inverse. We provide an efficiency comparison with the papers by Ma et al. 17 and Lin et al. 18 in Table 1, the storage space comparison with Lin et al. 18 in Table 2, and a brief comparison with others in Table 3.
The comparison of computational complexity.

The comparison of storage space.
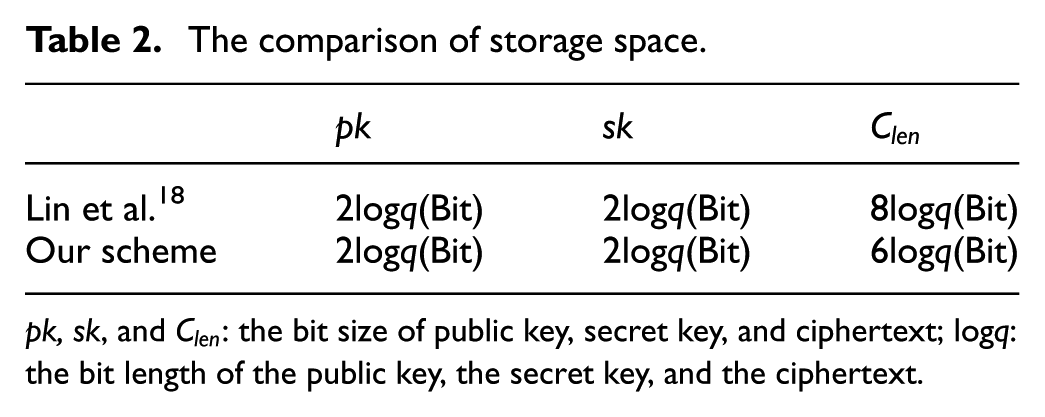
pk, sk, and
The comparison of computational complexity with others.
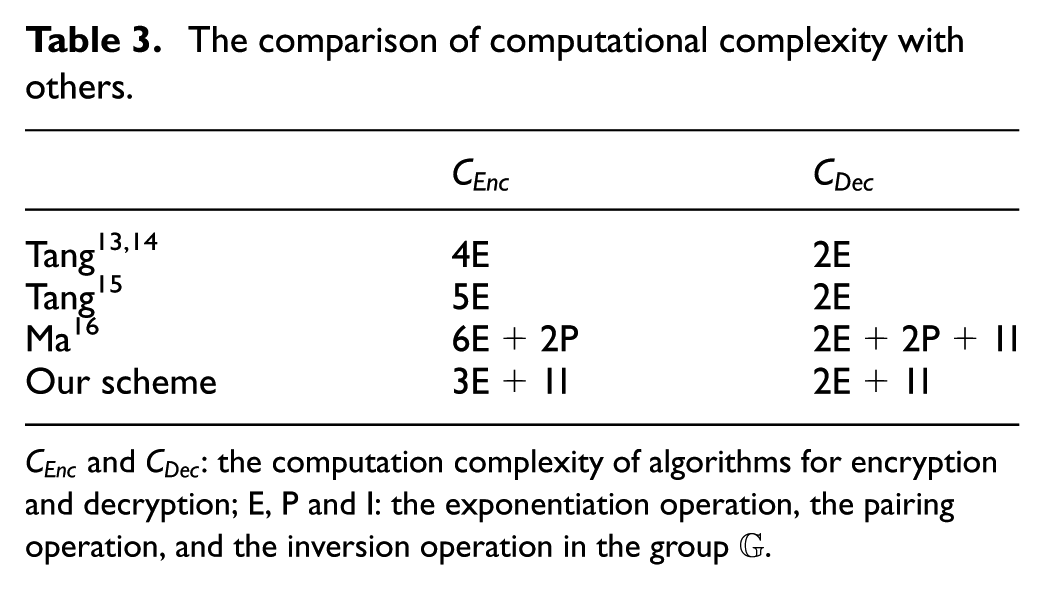
In Table 1, we compare the presented scheme with the scheme in Ma et al.
17
and Lin et al.
18
with respect to the computation complexity of Encrypt (CEnc), Decrypt (CDec) (from the second to the third columns), four types of Authorization (Auth) (from the fourth to the seventh columns) and four types of Test (from the 8th to the 11th columns). In Table 2, we compare the storage space with Lin et al.,
18
in terms of the sizes of pk, sk,
It is quite clear from the tables that our scheme requires smaller ciphertext storage compared to the previous study by Lin et al. 18 Computational cost is less when compared to the previous studies by Ma et al. 17 and Lin et al. 18 in case of Encrypt, Decrypt, four types of Authorizations, and four types of Tests. Thus, our presented scheme is more efficient. From Table 3, it can be observed that our scheme is more efficient than that of Tang13–15 in encryption.
As a whole, our scheme supports much more flexible authorization and is more efficient, compared to previous studies.12–14,17,18 Thus, we remark that our scheme is more practical for the age of big data.
Conclusion
In this article, we present an improved PKEwET-FA scheme. We prove that our scheme is more flexible and more practical comparing with previous works. For the Encrypt, Decrypt, and Test algorithms, we use a straight line instead of the quadratic curve. Finally, we conclude that the presented scheme achieves lower computational complexity and smaller storage space under the same level of security.
Footnotes
Academic editor: Shancang Li
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the National Natural Science Foundation of China (NSFC) (Nos. 61370194, 61502048).