Abstract
In this article, we investigate the physical layer security problem in relay wireless sensor networks with simultaneous wireless information and power transfer. Specifically, by considering the energy receiver which may act as potential eavesdropper and assuming that only imperfect channel state information can be attained, we propose a joint robust beamforming and artificial noise scheme. We formulate the relay power minimization problem under both the secrecy rate constraint and the energy harvesting constraints, which is non-convex and hard to tackle. By studying the hidden convexity of the problem, we propose an iterative algorithm combining semi-definite relaxation and a gradient-based method. In addition, a suboptimal rank-one reconstruction method is presented. Simulation results show that the proposed robust scheme achieves better performance than other schemes.
Keywords
Introduction
Wireless sensor network (WSN) is envisioned as one of the most important research areas with numerous applications such as vehicular tracking, environmental monitoring, 1 and other fields. 2 A WSN is typically composed of energy-constrained, cost-constrained, and lightweight computing sensor nodes, which can perform sensing, simple computations, and short-range wireless communications. 3
Energy harvesting (EH) is considered as one of the effective approaches for improving the energy efficiency of WSN since in many WSN applications, the lifetime of network is limited due to the constraints in energy resources. 4 EH-enabled sensors can harvest energy from either radio frequency (RF) signals or ambient energy sources which enable them to operate continuously. 5 Simultaneous wireless information and power transfer (SWIPT) is a promising EH technique to solve the energy scarcity problem in energy-constrained wireless system such as WSN. 6
However, the secure transmission has been recognized as an important issue for WSN due to the broadcast characteristics of wireless channel and the security requirement of the sensing information. 7 To address the issue, the physical layer security (PLS) technique, 8 which exploits the characteristics of wireless channels such as fading to fulfill secure communication, has been proved to be an effective way to improve security in WSN 9 as well as SWIPT system.10–12 Specifically, Curiac 9 investigated the utility of directional antennas to improve security in WSN, while Xing et al., 10 Liu et al., 11 and Shi et al. 12 investigated the secrecy SWIPT scheme for single-input single-output (SISO) channel, multiple-input single-output (MISO) channel, and multiple-input multiple-output (MIMO) channel, respectively. Among these literatures, beamforming (BF) and artificial noise (AN) are two key techniques to improve security and enhance EH. 13
One of the most important problems in PLS is the acquirement of the channel state information (CSI). The robust design has been widely applied to handle the CSI’s uncertainties.14–20 Specifically, Feng et al., 14 Chu et al., 15 and Zhang et al. 16 investigated the robust secrecy rate maximization (SRM) problems for an MISO SWIPT system without AN, with AN, and with a friendly jammer, respectively. Khandaker and Wong 17 investigated the robust power minimization and the robust SRM problem in MISO SWIPT by considering that the EH receiver may be potential eavesdropper (Eve), while Wang and Wang 18 investigated the robust SRM problem in MIMO wiretap channels. Recently, Chu et al. 19 and Zhang et al. 20 investigated the robust secrecy design for MISO SWIPT system by considering that all receivers have EH constraints.
Relaying is considered as a popular approach to extend network coverage and provide spatial degrees of freedom (DoF), which is beneficial to PLS 21 and SWIPT; 22 thus, several literatures investigated the secure SWIPT in relay system.23–27 Specifically, Li et al. 23 investigated the SRM problem in multi-antenna amplify-and-forward (AF) relay SWIPT system subject to the EH constraints, while Li et al. 24 considered unavailable Eve’s CSI and proposed a suboptimal null space–based BF and AN scheme in two-way AF SWIPT relay networks. Zhang et al. 25 proposed a joint design of the signal BF and AN at the source and the BF at the relay to maximize the secrecy rate, while Xing et al. 26 proposed a novel harvest-and-jamming method, where the friendly jammer used the harvested energy to confuse the Eve. Recently, Feng et al. 27 proposed a joint BF and energy signal scheme for providing both secure communication and energy transfer in AF relay networks.
Relay node can make the WSN transmission more reliable to satisfy the strict requirements in industrial applications. 28 Recently, relay WSN has aroused great attentions.29–35 Specifically, Dong et al. 29 investigated the diversity performance of high-altitude platform (HAP)-based relay WSN, while Dong et al. 30 investigated the energy-efficient transmission for remote WSN, where an integrated architecture based on HAP was proposed. Djenouri and Bagaa 31 investigated the relay node deployment for sustainable WSN with EH constraint. For the issue of PLS in relay WSN, Liau et al. 32 proposed a two-path successive relaying scheme to improve the security, while Gong et al. 33 utilized joint BF and AN to further improve the secrecy performance. For more complicated network structure, Zhang et al. 34 investigated the PLS scheme for orthogonal frequency division multiple access (OFDMA)-based two-way relay WSN, while Deng et al. 35 proposed a PLS scheme for three-tier WSN using decode-and-forward (DF) relay.
Motivated by these works, in this article, we investigate the PLS for SWIPT in relay WSN. Specifically, we investigate the BF and AN design to minimize the relay transmit power based on the following settings: (1) one multi-antenna relay forward the information from the source to the information sensor node, denoted as information receiver (IR), in the presence of multiple energy sensor nodes, denoted as energy receivers (ERs), which may be potential Eve; (2) relay employs BF and AN to improve security and enhance energy transfer simultaneously; (3) relay has perfect CSI of the IR, but imperfect CSI of the ERs and the ERs colluding to eavesdrop the confidential information.
Our main contributions can be summarized as follows: first, we propose a framework for secrecy SWIPT in AF relay WSN with different service requirements at different wireless sensor nodes which gives rise to new BF and AN task. Second, the power minimization problem subject to the non-convex secrecy rate constraint is hard to handle directly. Our gradient-based algorithm solves this problem efficiently and can be applied to similar scenarios. Third, by analyzing the Karush–Kuhn–Tucker (KKT) optimality conditions, we discuss the structure of the obtained BF matrix and propose a suboptimal rank-one reconstruction algorithm when the rank of the matrix is higher than one. To the best of our knowledge, such a joint robust design for secure SWIPT in AF relay WSN has not been investigated in related literatures.
One of the most relevant works is Li et al.’s study, 21 in which the authors investigated the robust secrecy scheme in multi-antenna relay networks, but the main differences of our article are summarized as follows: first, Li et al. 21 did not consider SWIPT, while our article considers the combination of PLS and SWIPT; thus, the BF and AN in our system have dual functions, for example, enhance the received signals at the IR and the ERs while degrade the received signals at the Eves simultaneously. Second, Li et al. 21 considered the SRM problem, while our article investigates the power minimization problem; although the one-dimensional search method in the work by Li et al. 21 can solve our problem with some necessary modifications, we propose a more efficient gradient-based algorithm by analyzing the hidden convexity of the power minimization problem. Third, the algorithm in the work by Li et al. 21 can always obtain a rank-one optimal BF matrix, while in the case of SWIPT, the structure of the obtained matrix is more complicated and we cannot always attain a rank-one BF matrix, so we propose an effective way to obtain a suboptimal solution when we obtain a high-rank solution.
The rest of this article is organized as follows. A system model description and problem statement is given in section “System model and problem statement.” Section “Joint robust BF and AN design for equation (8)” considers the joint robust BF and AN design problem, wherein a gradient-based optimization approach is established. Simulation results are illustrated in section “Simulation result.” Section “Conclusion” concludes the article.
Notation
Throughout the article, we use the upper case boldface letters for matrices and lower case boldface letters for vectors. The superscripts
System model and problem statement
We consider a relay WSN system for SWIPT as shown in Figure 1, in which a transmitter transmits information and wireless energy to a cluster of sensor nodes simultaneously with the help of one multi-antenna AF relay. One of these sensor nodes is IR, while the other sensor nodes are ERs. The relay is equipped with

System model for secure AF relay WSN with SWIPT.
In the first phase, the transmitter broadcasts its information

where
In the second phase, the relay employs the BF matrix

The received signals at the IR and the
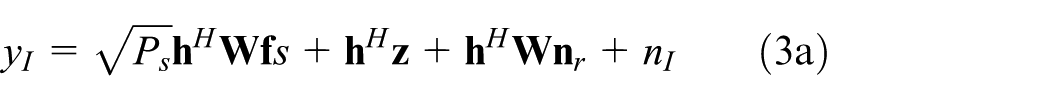
where
In this article, we consider the worst-case secrecy design. Specifically, we assume that all these single antenna ERs perform joint processing to eavesdrop the confidential information; thus, they can be seen as a virtual multi-antenna ER17,27 and the relay only has imperfect ER’s CSI. We use the deterministic spherical model26,27 to characterize the CSI uncertainties such that

where
Thus, the information rates at the IR and the colluding ERs are given, respectively, by


where

and the scaling factor 1/2 is due to the half-duplex operation of relay (See Feng et al. 27 for more details).
However, by neglecting the noise power, the harvest energy of the

where
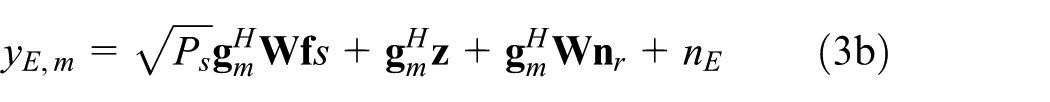
Our problem of interest is to design the BF matrix



where
Joint robust BF and AN design for equation (8)
Equivalent reformulation of equation (8)
We start by reformulating equation (8) into

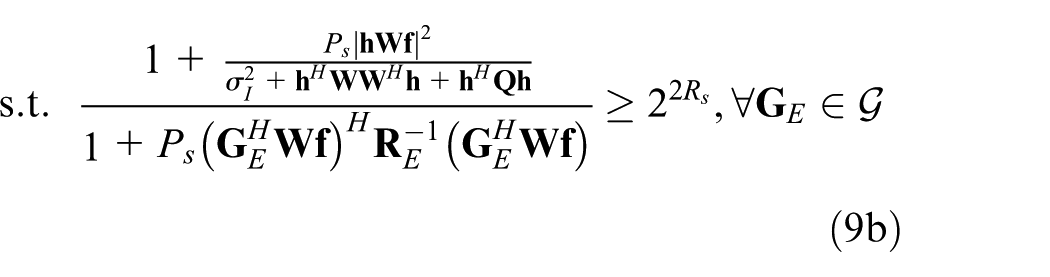
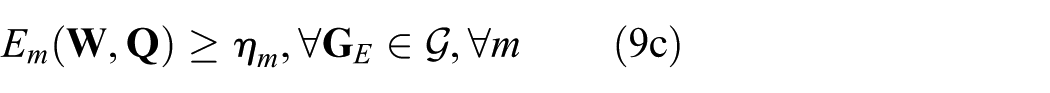
Then, by introducing an auxiliary variable




which can be re-organized as




The equivalence of equations (8) and (11) can be shortly demonstrated as follows. Let
Notably, the objective and constraints in equation (11) are highly non-convex; thus, it is hard to obtain the solution directly. In the following, we first solve it for fixed
Optimization of the SDR of equation (11) for fixed
Let us denote
Proposition 1
The SDR reformation of equation (11) can be defined as
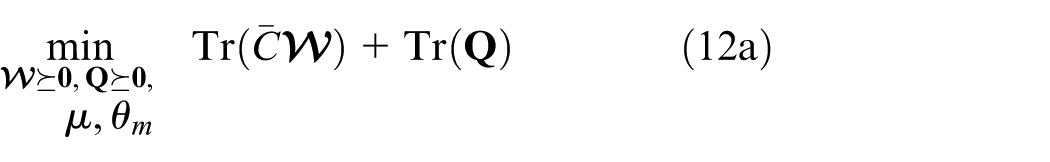



where

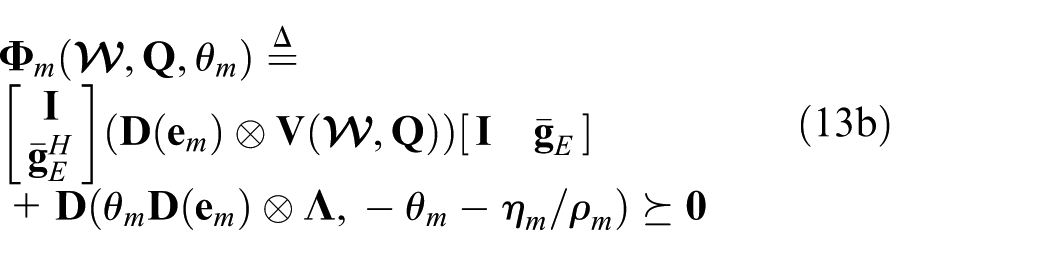
and
In addition,


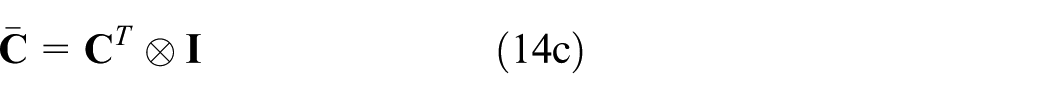


with
The main advantage of equation (12) is that for fixed
Proposition 2
The optimal solution

where
According to equation (15), if

while



Optimization over
In the above subsection, we have converted equation (11) to the SDR (equation (12)) for fixed
Next, we focus on finding the optimal
Proposition 3
Proof
The Lagrangian of equation (12) is
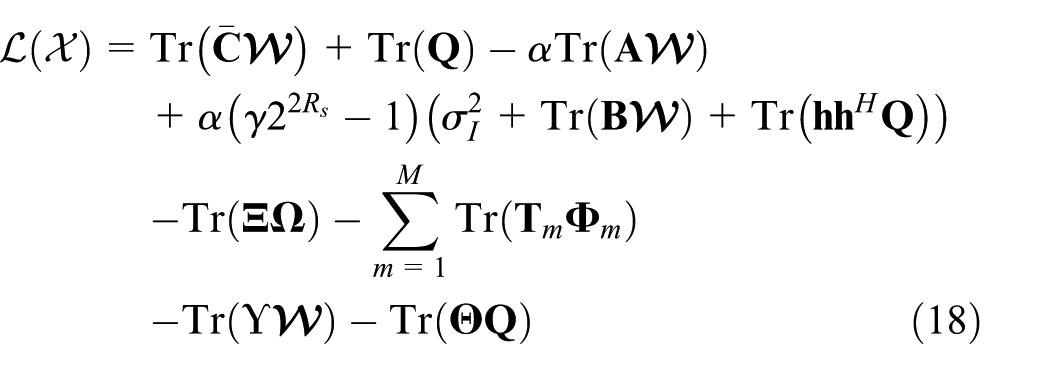
where
The dual problem can be written as



Based on the operation of matrix differential
37
and using the fact


where
Similarly, we attain the following relationships

where

Due to the strong duality between the primary problem (12) and the dual problem (19), the objective value of equation (19) is also
Proposition 3 shows that any local search algorithm can find the global optimal value of
The derivative of
The overall iterative algorithm to solve equation (11) is given in Algorithm 1. (The initial value of

Simulation result
In this section, we evaluate the performance of our scheme through Monte Carlo simulations. The following parameters
To highlight the superiority of our proposed scheme, we compare our algorithm with several other methods: (1) robust BF and AN with one-dimensional search; (2) BF with null space AN, which is a modified version of the null space AN method in the work by Li et al.,
24
for example, the AN is transmitted in the null space of the
The relay power versus the secrecy rate RS
Figure 2 illustrates the relay transmit power of these schemes versus the secrecy rate
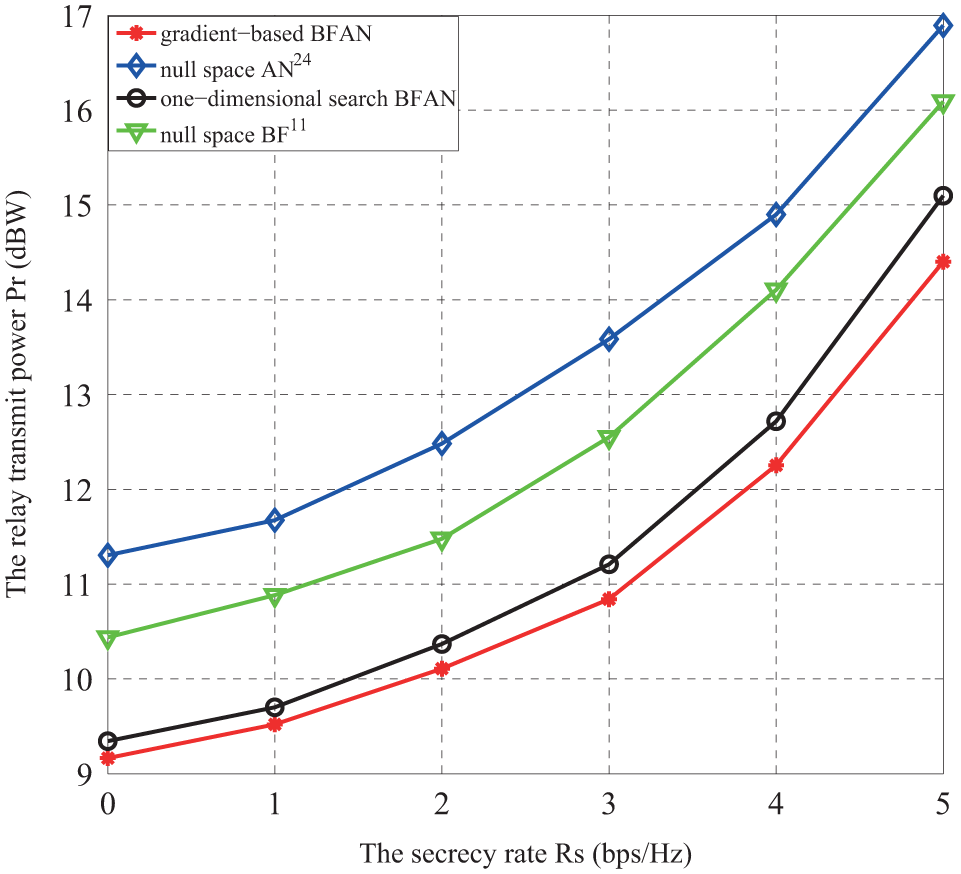
The relay power versus the worst-case secrecy rate.
The relay power versus the ERs’ CSI uncertainty level
Figure 3 shows the relay transmit power of these schemes versus the ERs’ CSI uncertainty level

The relay power versus the ERs’ CSI uncertainty level.
The relay power versus the EH threshold
Figure 4 investigates the relay transmit power of these schemes versus the EH threshold
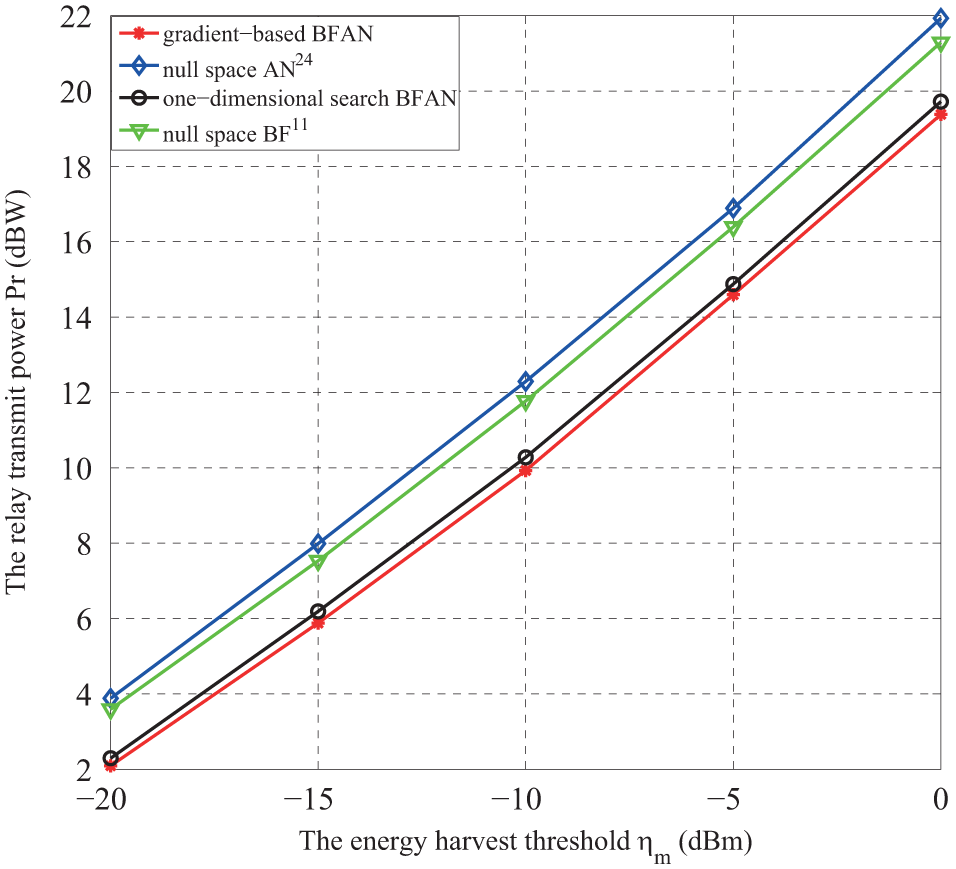
The relay power versus the EH threshold.
The relay power versus the number of relay antennas Nr
Figure 5 plots the relay power consumption of these schemes versus the number of relay antennas

The relay power versus the number of relay antennas.
The relay power versus the number of ERs M
Figure 6 depicts the relay transmit power of these schemes versus the number of ERs

The relay power versus the number of ERs.
The secrecy rate and EH performance versus the relay power Pr
Finally, Figures 7 and 8 depict the secrecy rate performance and the EH performance with relay transmit power, respectively. In both of the examples, we use the one-dimensional search method in the works by Li et al. 21 and Feng et al. 27 with several necessary modifications, and the joint design is labeled as “robust BFAN.” From Figures 7 and 8, we can find the joint design achieves higher secrecy rate and EH performance than the null space BF and null space AN design, which further demonstrates the superiority of the joint robust BF and AN design.

The secrecy rate versus the relay power.
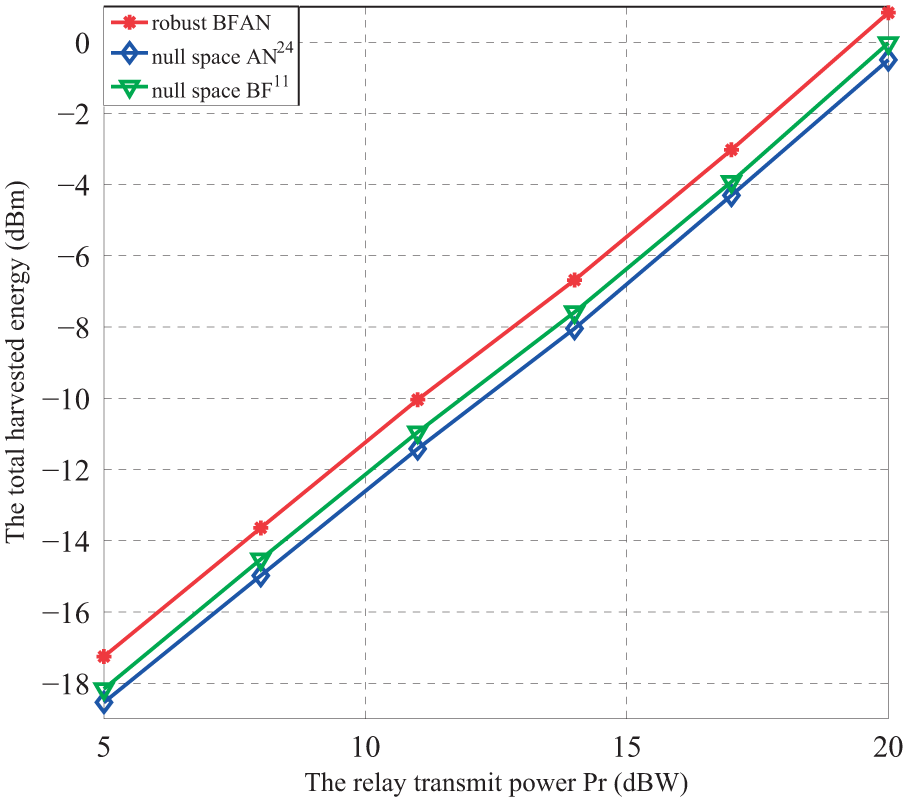
The total harvested energy versus the relay power.
Conclusion
In this article, we investigated a joint robust BF and AN scheme for secure SWIPT in AF relay WSN. Specifically, we formulated the robust relay power minimization problem subject to both secrecy rate and EH constraints. To obtain the optimal BF matrix and AN covariance, an iterative algorithm combining gradient-based method and SDR has been proposed to find the optimal solution by analyzing its convexity. In addition, a suboptimal rank-one reconstruction algorithm was presented. Simulation results demonstrated the effectiveness of the proposed design.
Footnotes
Appendix 1
Acknowledgements
The authors thank the anonymous reviewers for their helpful comments and suggestions.
Academic Editor: Bo Liu
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the Jiangsu Provincial Natural Science Foundation of China under grant no. BK20141069.
