Abstract
The Internet of Things provides visions of innovative services and domain-specific applications. With the development of Internet of Things services, various structural data need to be transferred over the Internet. However, protecting structural information that contains sensitive data has raised concerns against Internet of Things services. For a publish/subscribe scenario consisting of sensors, fog nodes, and subscribers, we propose a model that (1) expands the present XML Encryption standard for data with string and numeric types implemented in the sensors, (2) efficiently and discreetly filters matched streaming data and performs summation in the fog nodes, and (3) decrypts the filtered and aggregated data in the subscribers without revealing privacy data. The experimental results of the performance on fog node implemented by PC or Raspberry Pi show that the proposed model can rapidly process multiple encrypted XML streams generated by sensors in a parallel manner without revealing privacy data to subscribers. Therefore, the proposed model is a solution to the fog computing applications in which the privacy preservation of sensor data is of great concern.
Introduction
With advancements in information technology, many objects with embedded electronics are connected through the Internet. This connectivity generates the basic idea of the Internet of Things (IoT). Through the use of IoT technologies, unknown phenomena can be identified early. For example, anomalous heartbeats can be detected using wearable devices that monitor a person’s heart rate; an agriculture company can predict crop productivity using long-term data on humidity, temperature, and images of growing crops.
To expedite procedures for domain-specific analysis, cloud computing has been widely used in the IoT. Cloud computing services result in high network latency for users and involve high economic costs of computing resources for immediate services. By contrast, fog computing plays a critical role between users and cloud servers because of its low latency, widespread geographical distribution, mobility, low economic costs, and real-time processing.1,2 Fog computing offers some services close to users or connected devices that collect data such as billable services and simple analytics. 3 In smart grids, fog computing has been shown to improve efficiency of energy consumption in houses and buildings.4,5 A smart grid usually consists of smart meters, concentrators, and meter data management systems (MDMS). The smart meters collect private data, for example, power consumption, household ID, and other private information, and transmit them to the concentrators. Concentrators can act as fog nodes, which perform necessary data aggregation and then send the aggregated results to subscribers for visualization or advanced analytics. In smart city, smart street lights can serve as fog nodes to interact locally with sensors and detect presence of pedestrians and bikers, and measure the distance and speed of approaching vehicles and send warning signals to approaching vehicles. 6
In this article, we discuss the following system-related and privacy concerns of IoT technologies: (1) the prevention of privacy leakage, (2) a mechanism by which devices transmit comprehensive data specifically related to structural information, and (3) the efficient and secure processing of data in fog computing.
First, privacy leakage may be caused by malware, software vulnerabilities, and man-in-the-middle attacks. 4 We may assume that the fog nodes are semi-trusted and can honestly execute lightweight computational services such as aggregations. For aggregations in fog nodes, general encryption methods such as the Advanced Encryption Standard (AES) 7 and RSA (Ron Rivest, Adi Shamir and Leonard Adleman) are unsuitable because sensitive information may be captured by malware when the fog nodes decrypt the encrypted data. Second, XML technologies, such as Extensible Messaging and Presence Protocol (XMPP), are widely used in the IoT to transmit structural information. 8 For secure communication, RSA or AES is used in XML Encryption, as recommended by the World Wide Web Consortium (W3C). 9 Because of legislative concerns about data collection, 10 client privacy should be protected. However, decryption should be performed for aggregation. Private data may be accessed by attackers after decryption. Third, streaming processing technologies enable efficient data processing. XML filtering has been introduced to process XML streams. However, XML filtering focuses on processing a single stream, but rarely processes multiple streams.11–15 Computational ability can be enhanced if these filters concurrently process multiple streams.
To solve the aforementioned problems, we propose a computational model that (1) provides an XML encryption algorithm (XEA) that expands existing XML Encryption in sensor nodes and (2) efficiently and securely filters multiple encrypted XML streams that matched the queries of subscribers and performs aggregation operations without decryption in the fog node. The major contributions of this article are as follows: (1) we propose a model for encrypting XML documents by expanding the current XML Encryption standard, (2) we provide an approach that enables multicore processing of multiple XML streams, (3) we propose secure aggregation for encrypted XML streams without any decryption to support secure aggregation, and (4) we detail experiments in which three XML filtering and two aggregation methods were used on both devices of PC and Raspberry Pi.
The remainder of this article is organized as follows. Preliminary knowledge is introduced in section “Preliminary knowledge.” Related work is discussed in section “Related work,” and our proposed model is described in section “The proposed model.” Performance and security analysis are discussed in section “Performance and security analysis.” Section “Experiments” explains the experimental results and, finally, section “Conclusion” offers the conclusion of this study.
Preliminary knowledge
XML data model and tree pattern query
To represent XML documents in this article, we used the data model from parts of the XPath query model (XDM), 16 which is a tree-like representation model for XML. For example, a source XML document is presented in Figure 1(a) and the corresponding XML data model is presented in Figure 1(b). In Figure 1(b), the tree nodes without rectangles or the prefix “@” are the elements of the source XML document; the attributes of elements are denoted by the prefix “@” and the values consisting of element contexts and attribute contents are enclosed in rectangles. For each element node, its depth means the number of edges following from the root node to it. For instance, the nodes with element name c have depth of 2. We assumed that the values in the XML document were composed of string and numeric types. To easily explain our proposed method, we assumed that several string-type values and only one numeric value were present in the XML document.
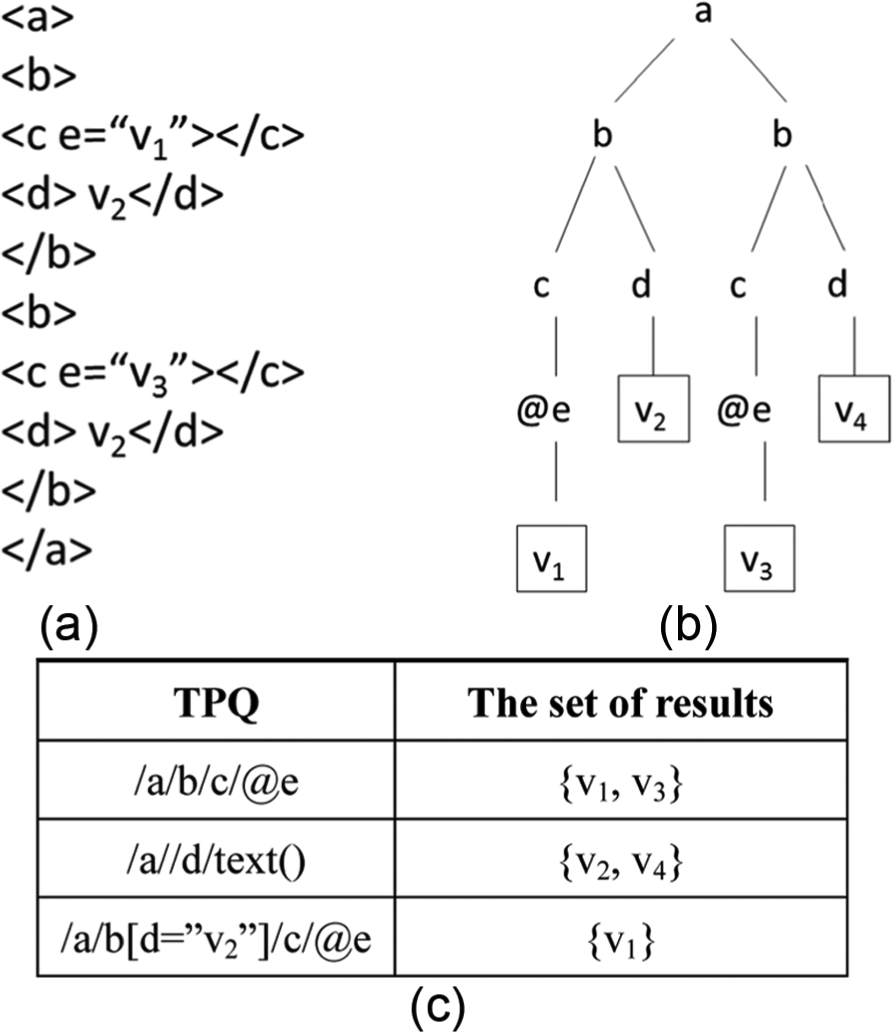
A simple XML document and its TPQ: (a) source structure of XML, (b) XML data model, and (c) examples of TPQ.
For queries in XDM, tree pattern query (TPQ) was used, as shown in Figure 1(c). The TPQ/a/b/c/@e is for determining the values of attribute e, which has ancestor elements following the order of a, b, and c. The “/” denotes the parent–child relationship. The other TPQ/a//d/text() is for determining the text of element d, which has an ancestor element a. The “//” denotes the ancestor–descendent relationship. In particular, the TPQ/a/b[d = ”v2”]/c/@e represents a twig query. It selects the path/a/b such that the element b has a child element d of value v2 and another child element c. Then, it returns the value of attribute e of the element c.
XML streams
An XML document can be transferred in a byte stream manner. In other words, the XML document will be sequentially transferred byte by byte from the beginning to the end to the Internet. In this study, we assumed that a sensor node generates a single XML stream. Each XML stream consists of timestamped XML documents with each XML document representing the sensed data of a sensor at the time specified by the timestamp. To embed a timestamp in an XML document, we placed a simple element called
Related work
IoT technology and security
An IoT platform may consist of components such as sensor nodes, fog nodes, and cloud computing nodes. The capabilities of various components in IoT application platforms such as communication protocols, services, and computation were widely discussed in Al-Fuqaha et al. 8 In some applications of smart city, Jayaraman et al. 17 proposed context-aware real-time data analytics platform called CARDAP to enable the dynamic integration of application-specific analytics for fulfilling the needs of crowd-sensing applications, such as monitoring citizen activities. Giordano et al. 18 designed the Rainbow platform for monitoring, managing, and controlling IoT devices remotely. They built a multi-agent system operating on the top of Rainbow to create smart services. To build a data mining system over the IoT, F Chen et al. 19 suggested five layers comprising IoT devices, integration of raw data, data gathering, data processing, and data mining services. They also mentioned adding a vertical layer for security and privacy. To format messages in instant messaging, XMPP was introduced by the Internet Engineering Task Force. Laine and Säilä 20 evaluated the performance of XMPP over HTML5 WebSocket and proved that XMPP was an efficient solution for real-time communication. Bendel et al. 21 proposed an XMPP-based service model for the IoT, which enabled nearly real-time processing and dynamically deployable services. Although these platforms exist,17–19 Bendel et al. 21 proposed solutions for data analytics on IoT platforms, where security concerns have not been discussed.
To enhance data secrecy, the Transport Layer Security (TLS) protocol 22 is used in developing IoT applications for communication security. 8
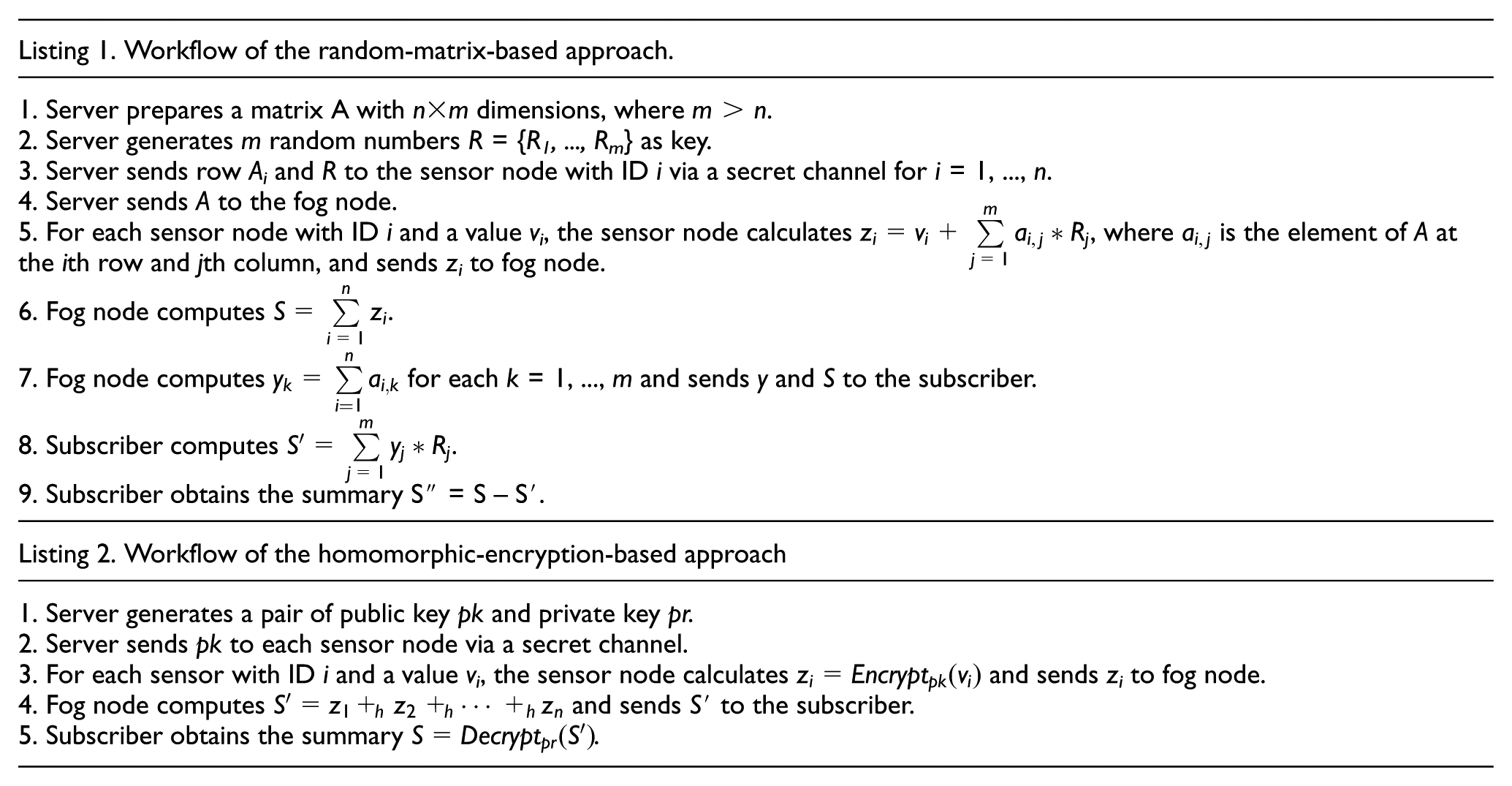
Wang et al. 23 discussed the differences between fog computing and cloud computing in terms of security issues. They further introduced the solution to prevent illegal access by monitoring the attack pattern and prompting SMS alerts to users. Stojmenovic and Wen 6 presented the man-in-the-middle attack by replacing the fake fog node and successfully hijacking the victim’s video communication. If a malware or a backdoor is on the computing nodes of smart grid, the attacker may use the malware or backdoor to steal the decrypted data while performing aggregation services. A solution to this problem is developing a secure mathematical operation for encrypted data. Because homomorphic encryption enables mathematic operations to operate on encrypted data, it is frequently used to preserve privacy in various applications. Jiang et al. 24 used a random-matrix-based approach and homomorphic encryption approach with the Paillier system 25 to discreetly calculate the similarities between documents. For smart grids, Garcia and Jacobs 26 proposed an approach that combines the Paillier additive homomorphic encryption and additive secret sharing. This approach can aggregate user energy consumption. However, it must periodically use shared random numbers in meters. A drawback of Paillier-based systems is the requirement to perform partial homomorphic encryption. Paillier-based systems claim to add two encrypted values and multiply the target value with one plain value. Gentry and Halevi 27 proposed a fully homomorphic encryption; however, its implementation yielded slow performance. Selection of partial or complete encryption depends on the type of application used. Considering the execution efficiency, we selected the approach described in Paillier 25 as our homomorphic encryption system.
XML filtering and querying on encrypted XML documents
XML filtering is used to remove unnecessary information, and it can capture the required data for further computation. YFilter, an XML filtering system, uses a novel nondeterministic finite automata approach to combine multiple XPaths for filtering on a single XML stream. 12 However, YFilter does not support position or twig queries. To support twig queries, EFilter was proposed, 28 which efficiently processes twig queries by utilizing QLinkedList. XMLDog 29 proposed an event-based approach to efficiently sniff and process XML documents, and this approach can be used to process XML streams. The Saxon processor 30 provides a utility for querying and filtering either XML documents or streams. However, these filtering systems can process only a single XML stream. 31
To encrypt XML documents, XML Encryption 9 is recommended by W3C. As mentioned in section “Introduction,” decryption should be performed when a content-based analysis is required. Therefore, performing queries securely on encrypted XML documents is very challenging. Brinkman et al. 32 used a relational database to store the structural information of XML documents. In their search protocol for pattern queries, the Data Encryption Standard was used, which has been considered insecure. 33 Wang and Lakshmanan 34 proposed a group approach for encrypting the selected blocks of an XML document with user security constraints. This approach supported range and twig queries on encrypted XML documents. However, the group approach may be unsuitable for users who cannot decide which part contains sensitive data. Attackers can obtain information from other non-encrypted blocks of the XML document. To support range queries without revealing the structural information, Cao et al. 35 proposed an encoding vector to hide the XML queries and implemented numeric value encryption based on asymmetric scalar-product preserving encryption. 36 The approach proposed by Cao et al. 35 is closely related to the approach proposed in our study, but their method supports only range queries, and the XML encoding technology is not compatible with present XML filtering tools. In summary, these approaches32,34,35 support only range queries but not aggregation operations.
The proposed model
To process multiple encrypted XML streams, filter the corresponding contents based on query patterns, and perform aggregation operations on encrypted content, we propose a model consisting of encryption for XML stream modules, XML filtering modules, and aggregation modules. Encryption for XML stream module enables the encryption of the XML document and generation of XML streams. The XML filtering module can filter the required information according to the given tree pattern queries. The aggregation module performs the aggregation operations on the basis of the encrypted contents filtered by the filtering module. The system architecture of the proposed model is presented in Figure 2. The system includes a third-party server, multiple sensor nodes, a fog node, and several subscribers. The sensor nodes discussed in this article have stronger computational abilities than typical sensor nodes. Platforms such as Raspberry Pi can act as sensor nodes.
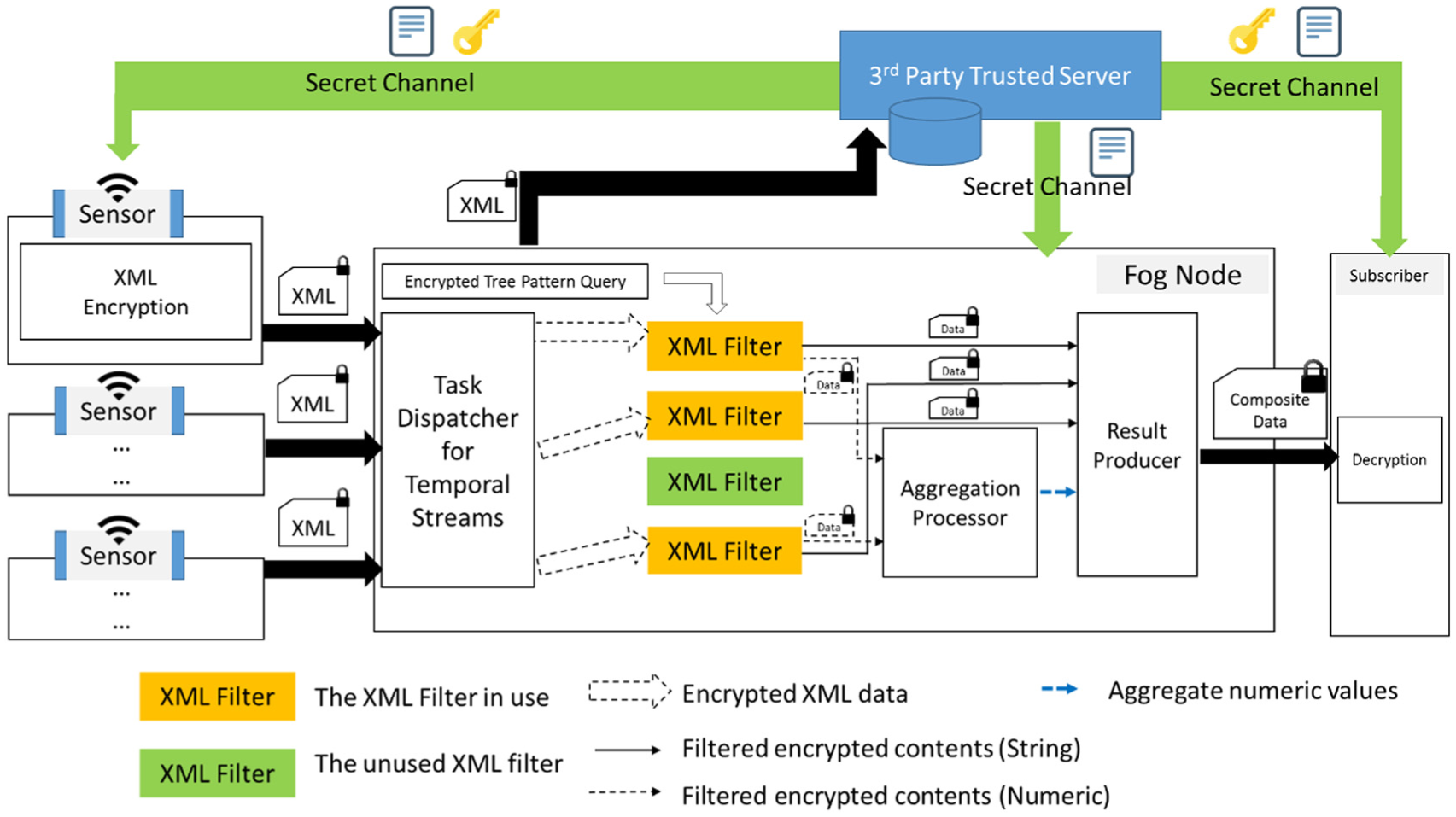
System architecture.
Third-party server
For simplicity, we refer to third-party servers as “servers” hereafter. Servers deploy public or secret keys and common parameters of selected encryption algorithms to sensors and subscribers. They have full access to the fog nodes to control which data should be passed to subscribers. Moreover, servers can store a large amount of sensitive data. Users who deploy sensors in their household or industrial area can access the server to observe the data collected from their sensors. The subscribers have access to the server and can request permission to obtain data according to the agreement among the users, third-party servers, and subscribers. After the request for acquiring and aggregating data is confirmed, the server encrypts the related query patterns for the subscribers and installs the patterns into the fog nodes and the keys and parameters to provide decryption operations to the subscribers in a secure manner. Subsequently, the subscribers receive the encrypted and filtered data from the fog nodes and decrypt the data using the keys and parameters provided by the server.
Sensor node
Sensor nodes generate encrypted XML documents using the proposed encryption algorithm. The sensor nodes must obtain secret keys, common parameters, and encryption functions from the server via a secret channel and execute the algorithm to encrypt the contents and attributes for the indicated XML elements and then generate the encrypted XML documents. The secret channel between the sensor node and server can be established using standard encrypted communication protocols such as Secure Shell or Secure Socket Layer (SSL).
For compatibility, the output format of our XEA is an extended version of the XML Encryption standard. The detailed design of the encryption in the sensor node is introduced in section “XEA.” Each sensor node transfers the encrypted XML streams to the fog node.
Fog node
The role of the fog node is to process the encrypted temporal XML streams from a group of specific sensor nodes. A fog node consists of five main components: (1)
Subscriber
To decrypt the encrypted data sent from the fog node, the decryption module must be installed in subscriber nodes. This module can decrypt data using the corresponding decryption algorithm according to the uniform resource identifiers (URIs) specified by the sensor node. We detail the decryption in section “Decryption by subscriber.”
XEA
For security and efficiency, the sensor nodes always generate encrypted XML documents and transfer the XML streams. The XEA is used to encrypt the raw data of XML documents. To conform to present standards, we adopted XML Encryption version 1.1 37 as the XEA output.
We assumed that any XEA contains an XML schema, which is shared by the server and sensor nodes. The XEA procedure is described as follows:
XEA fetches the preliminary settings from the server, including the hash functions, encryption keys, and common parameters. To protect the information from leakage, the encryption keys are protected and shared only with the server, subscribers, and sensor nodes.
XEA fetches presenting values and encrypts them according to their data types:
XEA follows the specification of XML Encryption and generates XML streams according to the given XML schema. The encrypted values should be placed into the
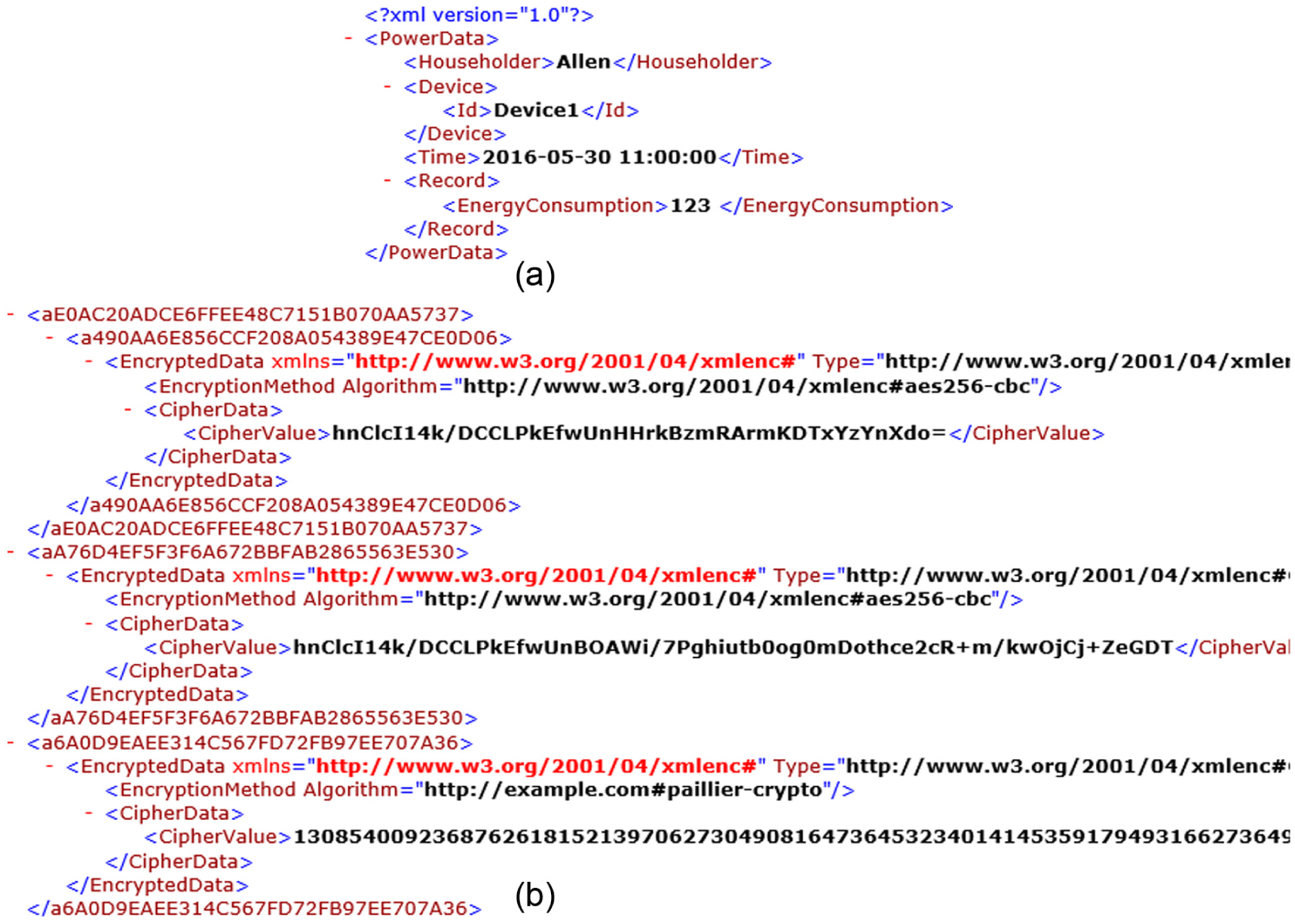
Example of XML Encryption for power metering data: (a) records of power consumption and (b) snapshot of an encrypted XML document.
ETPQ
To prevent the revelation of TPQ metadata to the fog node, encrypting the TPQs in the server is reasonable. We termed such encrypted TPQs as ETPQs. ETPQs are used to filter the values according to their type, which is required by the server for it to perform further operations. ETPQ consists of the following: (1)
Example 1
In Table 1, elements a, b, c, d, and e are hashed into ae87, b810, dp02, and ed70. The original TPQs /a/b/c/@e and /a//d/text() can be easily transformed into/ae87/b810/@ed70 and/ae87//dp02/text(), respectively.
Example of ETPQ.

TPQ: tree pattern query; ETPQ: encrypted tree pattern query.
Task dispatcher and XML filter
The task dispatcher was designed to execute a sequence of dispatching jobs including receiving multiple incoming streams, constructing a task for filtering the streams, and assigning the corresponding tasks for the filtering data. The pseudocode of the task dispatcher is shown in algorithm 1, where a thread pool consisting of XML filters given by ETPQs is prepared in line 1. The algorithm continuously listens to the incoming XML streams in lines 2–13. In lines 3–11, once an XML stream is received, a task for this stream is created and an available XML filter is sought to process the task. The task is placed into the queue of the thread pool if no XML filter is available.

For a given ETPQ, the XML filter performs the following:
Prepare the mapping table for ETPQ. The table entry is indexed by the ETPQ’s TPQ.
Read the given XML stream.
Push each value of the XPath matching ETPQ into the entry indexed by the matched ETPQ in the mapping tables. If the value’s corresponding URI of the attribute
After the filter processes the XML stream, execute the mapping table’s entries as follows. (a)
Aggregation processor
To aggregate the encrypted numeric values without decryption, we propose two approaches: random-matrix-based and homomorphic-encryption-based approaches for the aggregation processor. According to the results from the XML filters (the encrypted values and corresponding URI of

Decryption by subscriber
When the subscriber receives the set of outputs

Performance and security analysis
In this section, we analyze the time complexity of fog node, and security and privacy schemes of the proposed model in sections “Time complexity of fog node” and “Security analysis,” respectively.
Time complexity of fog node
To analyze the overall time complexity of a fog node, we calculate the time complexities of task dispatcher, XML filters, and aggregation processor. Assume that we have N streams and M concurrent XML filters. Assume these N streams contain K numeric values in total. We calculate the time complexity for processing each stream and then calculate the overall time complexity for processing N streams. We also assume that the time complexity for XML filter to process an XML document with E XML elements is O(E) and the time complexity of aggregating two encrypted values is constant, that is, O(1). Therefore, the time complexities for processing N streams are calculated below.
For task dispatcher, its execution is simple and assume it takes O(1) for each stream; therefore, O(N) in total. For concurrent XML filters, because the XML filters are running in concurrent manner, the overall complexity is O(N × E/M).
For aggregation processor, given K numeric values, it performs O(K) aggregations. The time complexities of encryption approaches based on random matrix and homomorphic encryption are described in Jiang et al. 24 Their time complexities seem to be the same but the actual execution time of homomorphic encryption is slower than that of using random-matrix-based approach.
Based on the above time complexities, the overall time complexity for processing
Security analysis
The main purpose of the proposed scheme is to provide a secure and privacy-preserving mechanism for fog computing. We assumed the fog node to be semi-trustable, that is, it was assumed to do the data aggregation operations without decryption honestly.
We consider two attack models. First, attackers may attempt to decrypt the encrypted sensor readings from the data communications between fog nodes and sensor nodes or between fog nodes and subscribers. Second, attackers aim to decrypt the encrypted sensor readings in the fog node. Both attack models address the problem of decrypting encrypted data consisting of encrypted strings and numeric data.
In the proposed model, the string-type data are encrypted using AES-256, and the encryption keys are transmitted to the sensor nodes and subscribers using the standard SSL protocol. The time complexity of breaking AES-256 using biclique method is 2254.4, 38 which can be considered as a very difficult problem for attackers.
Second, numeric data can be encrypted using two approaches. If numeric data are encrypted using the random-matrix-based approach, the numeric values are masked by
To further improve the security of the scheme, the server should periodically change the settings of the encryption system (i.e. the random numbers in the random-matrix-based approach or the public and private keys in the homomorphic-encryption-based approach).
Experiments
Experimental setup
To evaluate our proposed approach, the implementation of fog node is based on either PC or Raspberry Pi platforms. The PC environment was based on an Intel E3-1200 quad-core system with 4-GB memory and a 1-Gbps LAN, operated on Ubuntu 14.04 LTS with Linux kernel 3.19. The Raspberry Pi platform consists of a 1.2-GHz 64-bit quad-core ARMv8 CPU, a 10/100 Ethernet network card, and 802.11n wireless network; it operates on Raspbian OS with Linux kernel 4.4.9. We used Java to implement all algorithms on the fog node. The network environment was built on an Ethernet 100-Mbps LAN. Because deploying numerous sensors is difficult, we prepared a standalone PC to simulate the environment of several sensors.
In these experiments, we regard a smart meter with non-intrusive load-monitoring capability as a powerful sensor, which can simultaneously monitor and read the power consumption readings of 10 electric devices. The actual number of electric devices monitored by the smart meter depends on the interface design of the smart meter. The smart meter reads the readings of 10 devices and then generates encrypted XML document every second. The data format for each reading in XML document is described in Figure 3(a), which includes three string-type elements (householder ID, smart meter ID, and timestamp of the read operation) and one numeric-type element representing the reading of an electric device. Since each XML document contains data for 10 electric devices, it has 40 elements in total. The data size of the encrypted XML document is about 38 KB in average.
The worst case for fog node to process an XML document is to filter all of the contents of elements and perform necessary aggregation for readings. Therefore, we prepare 40 ETPQs for retrieving the contents of elements for 10 electric devices in an XML document. We evaluated the performance of the fog node by comparing the experiments of combinations of three XML filters (i.e. XMLDog, Saxon, and YFilter) on random-matrix-based and homomorphic-encryption-based approaches. We compared the performances by varying the number of concurrent XML filters (1, 5, 10, 15, and 20).
We compared the performance of concurrent processing of multiple XML streams by simulating 100, 300, and 500 sensor nodes. Given that
Experimental results
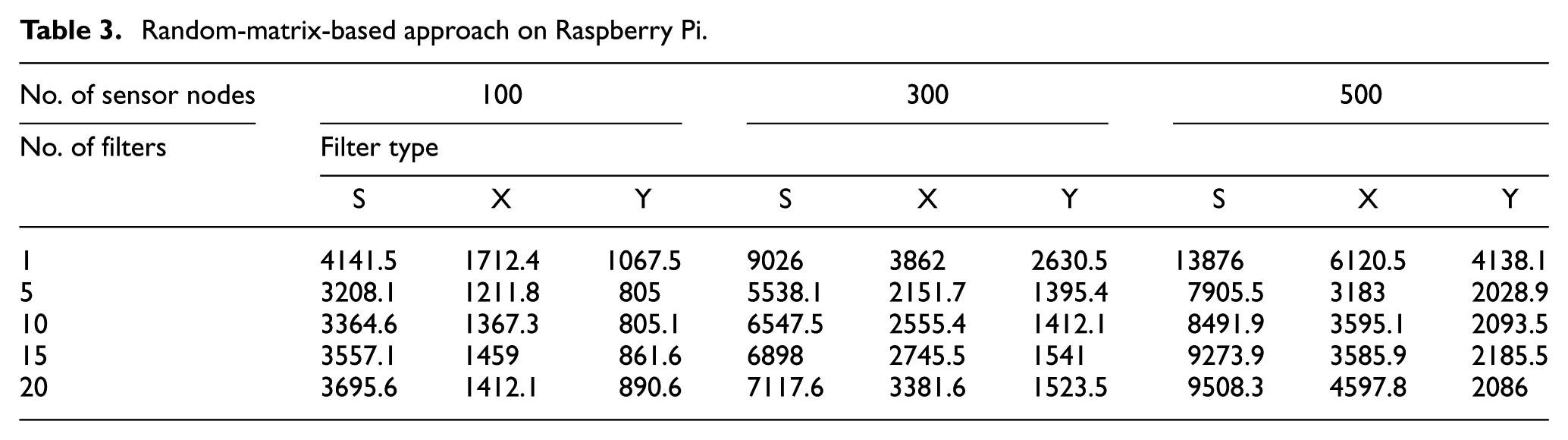
We evaluated the performance of the combinations of XML filters and the cryptosystem, the results of which are shown in Tables 2–5. The labels S, X, and Y in these tables represent Saxon, XMLDog, and YFilter, respectively. Run time is measured in milliseconds.
Random-matrix-based approach on PC.

Random-matrix-based approach on Raspberry Pi.
Homomorphic-encryption-based approach on PC.

Homomorphic-encryption-based approach on Raspberry Pi.

The evaluation of the random-matrix-based approach on the PC platform revealed that the performance of Saxon was lower than that of XMLDog and YFilter (Table 2) because, compared with XMLDog and YFilter, Saxon must initiate a higher number of running objects and create a complex data model to perform filtering. YFilter outperformed XMLDog in many cases because YFilter does not need to construct complex data objects and it has fewer event calls than XMLDog. The similar experiment on IoT device—Raspberry Pi (Table 3)—shows that the run time is longer than that of PC because of the limited computational abilities on Raspberry Pi. In Tables 2 and 3, the results indicate that with larger number of streams, the processing time is longer, but execution time can be reduced by properly increasing the number of concurrent filters. This situation actually coincides with our time complexity analysis.
The performance of the homomorphic-encryption-based approach was evaluated for PC (Table 4) and the IoT device (Table 5). The performance relationship between these filters remained unchanged. However, the run times were longer than those of the random-matrix-based approach because heavy product operations are executed in homomorphic encryption. In Table 4, although the filters benefit from increasing the number of concurrent XML filters, the overheads increase with the number of concurrent XML filters (≥5) because of resource competition. Similar results were observed in the homomorphic encryption on Raspberry Pi (Table 5). However, the performance was lower than that on PC. This can be attributed to the poor computational ability on Raspberry Pi. All three XML filters serving for 500 sensors cannot be accomplished within 2800 ms because of the poor performance. We also compare the approaches using AES-256, which is a built-in java library, for PC and Raspberry Pi. This AES-based implementation does not support aggregation with encryption. We perform the aggregation operations after decrypting the filtered numeric values. Then, the aggregated values are encrypted and sent to result producer. The corresponding results are shown in Tables 6 and 7, respectively. In most cases of running AES-256, the performance is worse than that of using homomorphic encryption. But the approach based only on AES-256 encryption should decrypt the sensor reading data for aggregation. It may have privacy leak if the malwares are put in the fog nodes. The proposed approaches using either random matrix or homomorphic encryption can provide privacy protection because no decryption is involved for aggregation.
AES-256 approach on PC.

AES-256 approach on Raspberry Pi.

To overcome the computation challenge on Raspberry Pi, we propose the following solutions: (1) select lightweight encryption functions when the incoming data are not very sensitive, (2) use native programs (despite the virtual-machine-embedded solution, using a native program can directly accelerate processing), and (3) collaborative execution (use several homogeneous or heterogeneous devices and compose them as an alliance to execute filters and aggregations in a map-reduce manner). These solutions may enable enhancing the performance.
Conclusion
In this article, we propose a model that (1) provides an XEA by expanding the XML Encryption standard 7 in sensor nodes, and (2) efficiently and securely filters multiple encrypted XML streams and performs aggregation operations without decryption in the fog node. We performed experiments on PC environments and IoT devices. Our experimental results show that although Raspberry Pi supports lower computing power than PC, its run time is satisfactory. However, because the computation resources of Raspberry Pi are limited, using too many concurrent XML filters easily results in resource competition. Nevertheless, efficiency is obtained by appropriately increasing the number of concurrent XML filters, particularly for consuming multiple XML streams.
The solution we proposed can not only be applied to the scenario of XML data exchange for publish/subscribe service but also provide a secure method for data protection and privacy-preserving. For IoT applications, JavaScript Simple Object Notation (JSON) has been a popular format, and JSON Web Encryption (JWE), 39 which utilizes standard cryptographic algorithms, is a proposed standard for encrypting JSON data. However, JWE requires the base64url encoding. To adjust our system for the JSON data, we can add a streaming decoder for base64url and use appropriate JWE filter modules in this system.
Our future study will address the following issues: (1) implement a collaborative computation model for several IoT devices, (2) support more aggregation operations, and (3) implement the proposed model on IoT communication protocols and compare their performance.
Footnotes
Acknowledgements
The authors thank the Institute of Information Science, Academia Sinica, Taiwan, for their support to this research while Dr I-En Liao was a visiting scholar during the period from 1 October 2016 to 31 December 2016.
Academic Editor: Davide Brunelli
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research was partially supported by the Ministry of Science and Technology, Taiwan, under the grant number MOST 103-2221-E-005052-MY2 and by the Taiwan Information Security Center at NCHU (TWISC@NCHU), Ministry of Science and Technology, Taiwan, under the grant numbers MOST 105-2221-E-005-070 and MOST 105-2218-E-001-001.
