Abstract
This article considers the load frequency control of multi-area power system-based multi-agent system method under false data injection attacks. The research can provide better solutions for multi-area power system load frequency control under false data injection attacks. First, an event-triggered mechanism is introduced to decide which data should be transmitted in the controller to save the limited network bandwidth. Besides, a model of cyberattacks is built using the Bernoulli random variables. Then, conditions are given for maintaining the system asymptotic stability under attack. Finally, simulations are performed to demonstrate the validity of the theory proposed in this article.
Introduction
Load frequency control (LFC) is the key to maintain the frequency stability of power systems. More recently, a large number of researchers published papers on LFC because of the security and stability of power systems.1–5 The multi-area power system is connected by the power systems of multiple regions. Besides, distributed cooperative control method based on multi-agent system (MAS) has been widely used in multi-area power system.6–9 MAS refers to a network system associated with a group of agents with functions of perception, communication, computation, and execution. 10 Singh et al. 8 presented an intelligent controller for LFC in “smart grid” environment which has been changed in communication topology via MAS technology. A two-level coordinated control frame based on MAS was proposed in Yang et al. 9 to improve the frequency control performance of the power system.
The control center and measurement center of LFC system are typical networked control system (NCS), and the communication between them adopts open communication network or special communication network. Actually, open communication networks rely on open communication channels to share large amounts of data, while special communication networks only allow specified data to be shared through channels. Compared with the latter, open communication network has the characteristics of more flexibility and practicality. However, open networks are vulnerable to malicious network attacks, which lead to security accidents in power systems. Therefore, it is necessary to study the LFC under malicious network attacks. From the target of attack, data integrity and availability are the main targets of attack. From the type of attack, attack can be divided into denial-of-service (DoS), deception attack, false data injection attack (FDIAs), random attack,
11
and so on. ShangGuan et al.
12
proposed a switched system model based on the LFC of multi-area power systems to reduce the adverse effects of DoS. In Wang et al.,
13
an
In order to avoid system failure caused by network congestion, event-triggered transmission scheme was often applied to NCS.17–25 The LFC for power systems with communication delays was studied in Wen et al.
20
where an event-triggered control method was used to reduce the amount of communications required. In Liu et al.,
21
the LFC for multi-area power systems under DoS attacks and deception attacks was solved by introducing an event-triggered mechanism and a switched system model. An adaptive condition for event-triggered scheme was given in Zhang et al.
22
for the multi-area uncertain power systems. The robust stability and stabilization of adaptive event-triggered LFC of multi-area power systems were investigated under a networked environment via sliding mode control in Lv et al.
23
Li et.al.
24
investigated dynamic event-triggered
The main contributions of this article are summarized as follows:
The important goal of LFC is to ensure the stability of frequency in the area, which is similar to the consensus based on MAS. Therefore, the consensus control based on MAS is used for the theoretical analysis of the LFC.
The event-triggered mechanism is introduced to lighten the load of network bandwidth, which not only reduced the update frequency of the controller, but also improved the security of information transmission. Furthermore, we proved that the proposed event-triggered mechanism does not have the Zeno phenomenon by deducing the lower bound of the time interval of any adjacent triggering moment.
In addition, most of the literatures20–24 mentioned above rarely take FDIAs into account. Therefore, the conditions for maintaining the system asymptotic stability under FDIAs are given to guarantee the safe and stability operation of the system.
The rest of this article is organized as follows. The models of the multi-area power systems, FDIAs, and event-triggered mechanism are introduced in section “Problem formulation.” In section “Main results,” the sufficient conditions of tolerable attack parameters are proposed and are further analyzed, which guarantees the asymptotic stability of the multi-area power systems. In section “Simulation example,” a simulation example is given to illustrate the effectiveness of the theory under the FDIAs.
Notions
In this article,
Problem formulation
This section gives the background of the problem which includes multi-area LFC power systems description, FDIAs model, and event-triggered transmission mechanism.
Multi-area LFC power system description
The multi-area LFC power systems of the


Dynamic model of the
Parameters in

Therefore, it can be induced to equation (2) based on Figure 1

The dynamic behavior of the power systems is achieved using the inverse Laplace transform with equation (2) based on 26

The
where

The purpose of this article is to design the proportional–integral (PI) controller applied in the LFC power systems, which can be expressed as

where
The control input of the multi-area LFC power systems can be rewritten as

where
False date inject attacks
For FDIAs, it destroys system stability by injecting false data into the system. As shown in Figure 2, the data are damaged by malicious FDIAs in the process of network transmission. The measurement output

FDI attack model.
Besides, we assume that the false signals

where
In this article, we assumed that the FDIAs occur randomly. Therefore, we use a Bernoulli random variable

where
Thus, the real measurements’ output

Combining equations (6) and (8), the control protocol under false data inject attack can be rewritten as

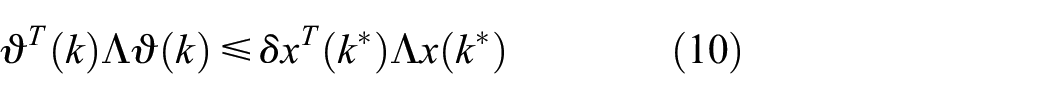
Assumption 1
To restrain the FDIAs, suppose that the following condition of attack energy function

where
Remark 1
Inspired by Pang et al. 28 and Sakthivel et al., 29 malicious attacks by attackers cannot inject false information unboundedly. It is reasonable to assume that the energy of attack signal is constrained. In addition, motivated by the works in Liu et al., 21 a probability-dependent false data inject model is adopted during the design of the reliable controller for the multi-area power systems.
Event-triggered mechanism
In this section, an event-triggered mechanism under LFC controller for multi-area power systems is given as
where
Remark 2
The non-periodic intermittent information transmission mode of event-triggered control can not only improve the security of information transmission to a certain extent, but also reduce the use of communication and computing resources, which can effectively improve the economy and practicability of LFC in multi-area power system.
Main results
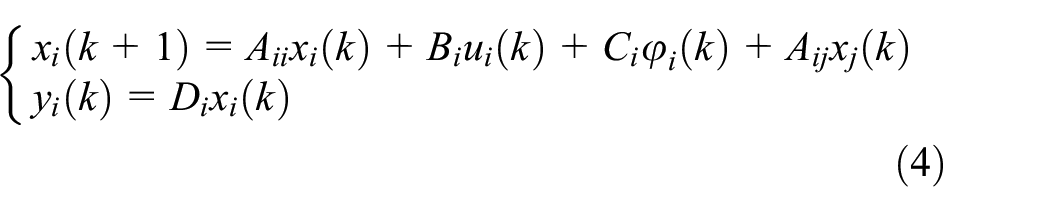
This part will analyzes the security consensus of the multi-area power system (4) under FDIAs and proves that the proposed event triggering condition (10) does not result in Zeno behavior.
By applying the Kronecker product, the multi-area power systems (4) can be transformed as following based on equation (9)

where
Stability of the multi-area power systems
Definition 1
The multi-area power system (11) is asymptotically stable,14,21 and
The multi-area power system (11) with
Under zero initial conditions, the inequality
Lemma 1
Suppose that there exist constant matrices

if and only if

Theorem 1
Under the FDIAs, the multi-area power systems (11) are asymptotically stable with the

and

where
Proof
Choose a Lyapunov function candidate for multi-area power systems (11) as follows

When
Then, calculate the difference of

It is clearly that

By employing Lemma 1 to equation (15), it can be concluded that

When
Then, calculate the difference of

It can be concluded that
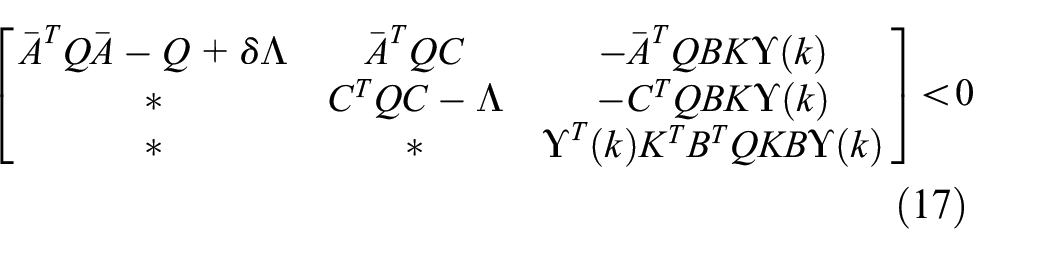
Define

Under zero initial conditions, we have

Combing equations (16) and (18), it can be obtained

According to equation (17),

Moreover, we need to guarantee that system (11) is asymptotically stability. According to equation (17), it follows that
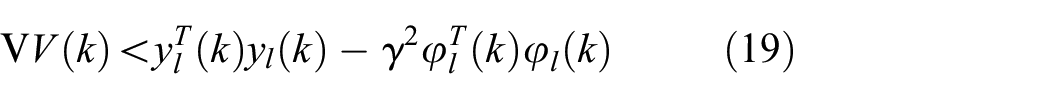
Summing up both sides of equation (19) with

so the asymptotic stability of system (11) is guaranteed.
The proof of Theorem 1 is completed.
Zeno phenomenon
Another problem that cannot be ignored for the event-triggered control algorithm is to prove that the algorithm will not appear Zeno phenomenon. Next, we will prove that the proposed event-triggered algorithm does not have the Zeno phenomenon by deducing the lower bound of the time interval of any adjacent triggering moment.
Definition 2
The Zeno phenomenon is presented if it takes an infinite number of triggers countless times in a finite amount of time. 30 In other words, the time interval is more than zero for any two adjacent events.
Theorem 2
For the event-triggered condition (10), there is a positive lower bound on the interval between two adjacent triggering event points.
Proof
According to the definition of

where
Integration from

Define

Define

Therefore, we can obtain

The proof of Theorem 2 is completed.
Simulation example
In this section, a three-area power system is employed to identify the effectiveness of our proposed event-triggered secure control strategy for LFC under FDIAs. The system parameters setting of the three-area power system (12) is shown in Table 2. The communication topology of the interconnected three-area power system is given in Figure 3 and each area adopts wired connection.
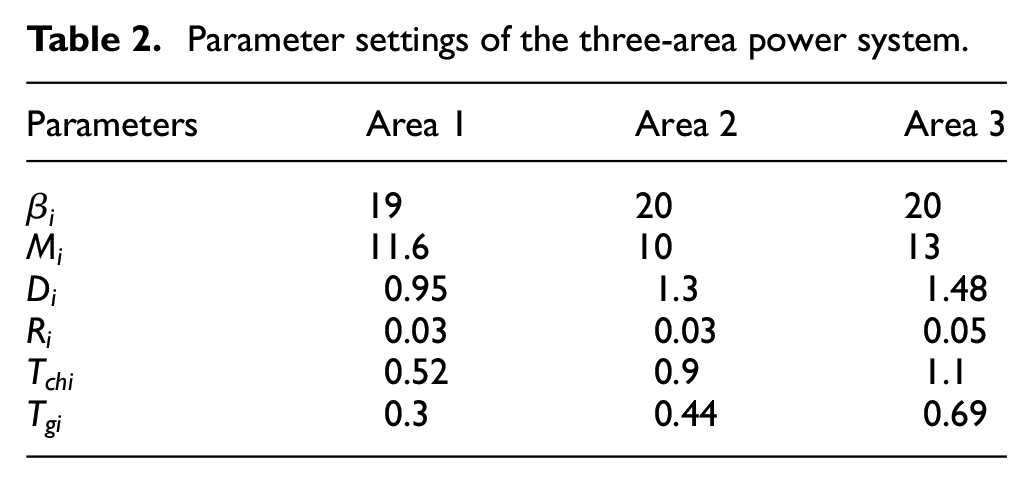
Parameter settings of the three-area power system.

The communication topology of the three-area power system.
In this simulation, we suppose that

The occurrence of false data injection attacks.
The simulation results are shown in Figure 5, which gives the frequency response of the conventional LFC in and our method. It can be seen from Figure 5(a) that the traditional LFC takes a long time to restore the stability of the system when multi-area power system is attacked by FDIA. However, it is unacceptable for power systems. Figure 5(b) perceives that the proposed method has improved the iteration speed, which meets the conditions of safe and stability operation of the power system.
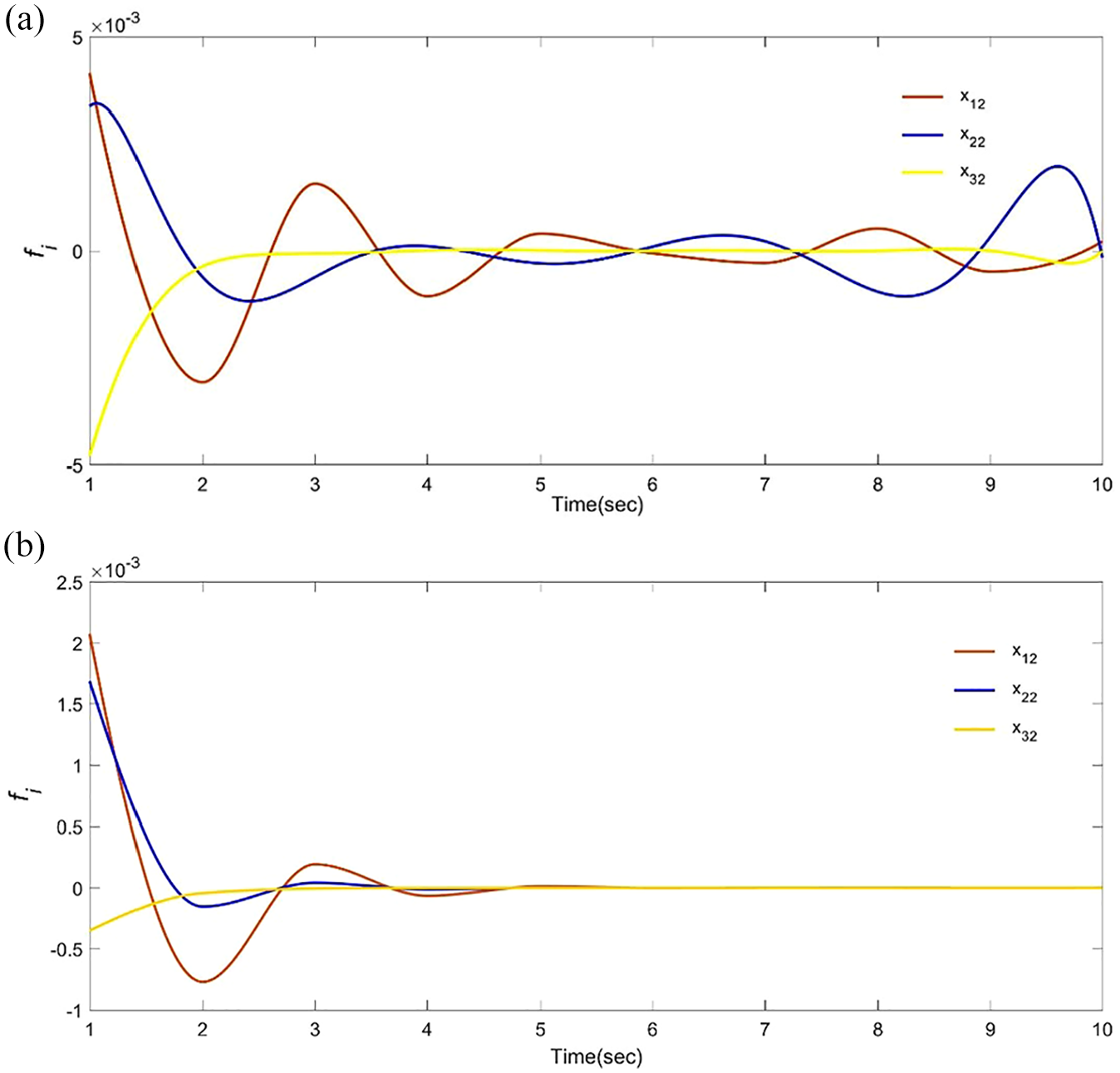
The frequency response under FDIAs. (a) LFC method proposed in Hu et al. 14 and (b) LFC method proposed in this article.
Figures 6 and 7 delineate the tie-line active power deviation and generator mechanical output deviation change of the three-area power system. It should be pointed out that system (11) maintaining recovery and synchronization of communication links under FDIAs.

The tie-line active power deviation changes of the multi-area power system.

The generator mechanical output deviation changes of the multi-area power system.
It is worth noting that the method proposed in this article does not consider the influence of time-delay on the system, but time-delay is inevitable for any engineering system. Therefore, we will continue to study the LFC with time-delay in multi-area power system under FDIAs in subsequent studies.
Conclusion
In summary, this article studies the LFC of multi-area power system based on MAS distributed control technology under FDIAs. The Bernoulli random variables are used to model the multi-regional power system affected by FDIAs. Then, an event-triggered mechanism is proposed to reduce the bandwidth of the network, and the asymptotic stability condition of multi-area power system is given. In addition, by deducing the lower bound of the time interval of any adjacent moment, it is proved that the event triggering mechanism proposed in this article does not have the Zeno phenomenon. According to this theorem, the simulation of specific cases is completed using LMI toolbox. The simulation results show that the proposed control algorithm can realize LFC security control of multi-area power system. Compared with other literature, the proposed algorithm has the advantages of faster and stronger robustness.
Footnotes
Handling Editor: Yanjiao Chen
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported in part by the West Light Foundation of the Chinese Academy of Science, in part by the Scientific and Technological Research Program of Chongqing Municipal Education Commission (KJZD-K201901504 and KJQN201901537), in part by the Humanities and Social Sciences Research of Ministry of Education (19YJCZH047), in part by the Research Foundation of The Natural Foundation of Chongqing City (cstc2021jcyj-msxmX0146), and in part by the National Innovation and Entrepreneurship Training Platform for College Students (202111551002).
