Abstract
In the vehicular ad hoc network, moving vehicles can keep communicating with each other by entering or leaving the network at any time to establish a new connection. However, since many users transmit a substantial number of messages, it may cause reception delays and affect the entire system. A certificateless aggregate signature scheme can provide a signature compression that keeps the verification cost low. Therefore, it is beneficial for environments constrained by time, bandwidth, and storage, such as vehicular ad hoc network. In recent years, several certificateless aggregate signature schemes have been proposed. Unfortunately, some of them still have some security and privacy issues under specific existing attacks. This article offers an authentication scheme that can improve security, privacy, and efficiency. First, we apply the certificateless aggregate signature method to prevent the onboard unit devices from leaking sensitive information when sending messages. The scheme is proven to be secure against the Type-1
Keywords
Introduction
The vehicular ad hoc network (VANET) is derived from the concept of the mobile ad hoc network (MANET). 1 It has two communication methods: vehicle-to-vehicle (V2V) and vehicle-to-infrastructure (V2I) communications. All smart cars are equipped with onboard units (OBU), which can communicate with each other wirelessly through dedicated short-range communication (DSRC) protocol. 2 The device can alert the driver in emergencies (e.g. the vehicle is too close to the vehicle in the front) and issue a collision warning to avoid accidents. In V2I communication, a vehicle can communicate with a roadside unit (RSU) and make a service request. The combination of vehicles and a global positioning system (GPS) obtains road traffic conditions through the transmission of messages and plans a perfect driving route. 3 As a result, road congestion is reduced, and the driving experience is improved.
VANET’s infrastructure consists of three main components: OBU, RSU, and trusted authority (TA) (i.e. trace authority (TRA), and key generator center (KGC)). 4 For a legal member in the VANET environment, an OBU must be equipped to enable it as a network node and communicate with other legal devices. The OBU contains the user interface, DSRC communication media, GPS, a computing power processor, an event data recorder (EDR), sensors, storage devices, and tamper-proof devices (TPD). 5 RSU allows OBU to communicate with TRA. The RSU communicates with the OBU through open and insecure wireless network channels, while, on the other hand, it connects to the TRA through a secure channel. TRA is responsible for registering RSU and vehicle, generating pseudonyms for the vehicle, and in case of dispute, it can trace the vehicles’ real identity. Meanwhile, KGC is in charge of producing public system parameters and preloading them on RSUs and OBUs in the off-line/on-line mode. It also generates and distributes the partial private keys for RSUs and vehicles. The general topology of VANET is shown in Figure 1.

The topology of VANET.
Despite all the convincing features provided by VANET, it also has several challenges in its security and privacy.6,7 In VANET, V2V and V2I communications are taking place on the open wireless communication channel, which is naturally not secure. Therefore, the message must be acknowledged to ensure that it was sent by a legitimate device and withstand various attacks during the transmission. The transmitted message contains sensitive personal information and cannot be leaked. When a large number of OBU devices send messages to the other OBUs and RSU simultaneously, this large number of messages must be verified. This process will increase the verification time, resulting in a reception delay of other road traffic emergencies and essential messages. In addition, another issue that needs to be considered is the significant mobility of vehicles on the road. This condition makes VANETs’ topology rapidly shift, resulting in the connection between vehicles that can change at any time. If the excessive load can disable services for each device, then the VANET environment will be severely affected. Therefore, a robust and lightweight authentication mechanism is critically needed to satisfy the security, privacy, and efficiency of the information dissemination and verification processes in VANET.
In traditional public-key cryptography (PKC), each public key must generate a corresponding digital certificate.8,9 When a user wants to send a message to a receiver, they must first obtain the recipient’s public key and then use a certificate to validate the user’s identity. He or she then uses this public key to encrypt the message and send it to the recipient. Not only does this require certification management, but it also increases verification time. In 1984, Shamir 10 proposed a new concept called ID-based public-key cryptography (ID-PKC) to solve the above problems. The public key in ID-PKC consists of the user’s identity information, such as phone number and email address. Therefore, there is no need to generate a certificate, thereby solving the traditional PKC problem. 11 However, the private key corresponding to the public key is caused by a KGC. If the KGC is compromised, the attacker will obtain all the private keys. Thus, attackers can arbitrarily decrypt other people’s encrypted messages or forge signatures. This attack is called a key escrow problem.
To solve the key escrow problem in ID-PKC, in 2003, Al-Riyami and Paterson 12 introduced a new concept known as certificateless public key cryptography (CL-PKC). Although CL-PKC also requires a key generating center (KGC), it only generates part of the user’s private key, while the other part is generated by the user locally. As a result, key escrow is overcome, and CL-PKC does not need to create certificates. Furthermore, a scheme called aggregate signature can aggregate multiple signatures generated by different users for different messages into a single signature. This approach not only reduces the length of the signature but also improves verification efficiency. Therefore, based on CL-PKC and aggregate signature advantages, some scholars combined these two methods and proposed a certificateless aggregate signature (CLAS) scheme. This scheme will effectively improve the problem of verifying a large number of messages in VANET.
Related work
The idea of CLAS was first introduced by Castro and Dahab, 9 by combining the benefits of aggregate signatures and CL-PKC. Since then, many CLAS schemes have been proposed.9,13–33 From all of these methods, several scholars pay attention to specific applications on VANET.18,19,21,23–33
In 2015, Horng et al. 19 proposed a new CLAS scheme based on the certificateless signature scheme (CLS) method for V2I communication in VANET. They claimed that their approach could achieve conditional privacy protection, more efficient in the verification process. Moreover, a small amount of constant pair of calculations can resist forgery on adaptively selected message attacks in the random oracle model (ROM). However, in 2016, Li et al. 21 showed that Horng et al.’s 19 scheme is vulnerable to “malicious but passive” KGC attacks. In 2018, Cui et al. 24 proposed a pairing-free CLAS scheme that has an obvious advantage in efficiency over Horng et al.’s 19 scheme. However, Zhao et al., 28 Kamil and Ogundoyin, 26 and Li et al. 31 found out that Cui et al.’s 24 schemes cannot withstand a malicious KGC attack. Zhao et al. 28 also pointed out that Horng et al.’s 19 scheme cannot withstand users’ public-key replacement attack. Meanwhile, Ming and Shen 34 showed that Horng et al.’s 19 scheme could not provide authentication and message integrity and failed to resist common attacks such as replay, modification, impersonation, and man-in-the-middle (MITM) attacks. Kamil and Ogundoyin 26 proposed their full aggregation pairing-free CLAS scheme and made cryptanalysis to Cui et al.’s 24 scheme. However, Zhao et al. 28 found out that Kamil and Ogundoyin’s 26 scheme cannot resist Type-1 and Type-2 adversary attacks.
In the same year as Horng et al., 19 Malhi and Batra 18 also proposed their CLAS scheme. They aimed for a low computational cost approach that still maintained its security reliability. They demonstrated that theirs could withstand the unforgeability attack and have a low computational cost. So, they emphasized that their scheme is very suitable for VANET. However, Kumar and Sharma 23 found that Malhi and Batra’s 18 scheme is vulnerable to malicious KGC attacks. Meanwhile, Zhang et al. 35 also found out that Malhi and Batra’s 18 scheme cannot provide identity privacy-preserving.
In 2019, Zhong et al. 25 proposed a full aggregation CLAS scheme for VANET and claimed it has better efficiency than Malhi-Batra’s 18 scheme. However, Li et al., 31 Mei et al., 32 and Kamil and Ogundoyin 29 found out that Zhong et al.’s 25 scheme cannot withstand a malicious KGC attack. In the same year, Kumar et al. 27 proposed their CLAS scheme in VANET and claimed to be unforgeable against adaptive chosen-message attacks. In 2021, Mei et al. 32 proposed a full aggregation CLAS scheme in VANET that claimed more efficient than Kumar and Sharma’s 23 and Kumar et al.’s 27 schemes. Kamil and Ogundoyin 29 also proposed their full aggregation CLAS scheme in VANET and made cryptanalysis to Zhong et al.’s 25 scheme. They show if Zhong et al.’s 25 and Kumar et al.’s 27 schemes are vulnerable to the signature-forgery attack by a malicious KGC and forgery attack, respectively. Xu et al. 30 proposed their CLAS scheme in VANET that claimed unforgeable against adaptive chosen-message and identity attacks. Recently, Thumbur et al. 33 proposed the newest pairing-free CLAS scheme and compared it to the other CLAS schemes in VANET that employ computational Diffie-Hellman problem (CDHP) complexity assumption. The scheme results in apparent advantages in computation cost.
The other significant authentication schemes related to the CLAS mechanism in VANET are also published in recent years. Bouakkaz and Semchedine 36 recently introduced an efficient certificateless ring signature (BV-CLRS) with batch verification, a conditional privacy preservation authentication system for use in VANET that is based on traceable certificateless ring signatures. The scheme has significantly decreased computation and communication overhead due to the usage of batch verification. It also claimed to be secure against five types of adversaries. In 2020, Cui et al. 37 suggested a privacy-preserving data downloading scheme with edge computing in VANET. Their method allows the RSU to discover common data by recording encrypted requests sent from adjacent nodes while maintaining the download requests’ secrecy. Elliptic-curve cryptography (ECC), TESLA broadcast authentication, and additive homomorphic encryption algorithms are used to build the scheme. Very recently, Zhang et al. 38 proposed a Chinese remainder theorem (CRT)-based conditional privacy-preserving authentication (PA-CRT) protocol to establish secure communication between vehicles in VANET. The scheme eliminates the requirement for TPDs to hold long-term system secrets. The CRT in this scheme is also claimed to greatly reduce the computational complexity of the TA.
A comparative summary of existing state-of-art CLAS authentication schemes for VANET discussed above is presented in Table 1. In addition, the table elaborates the topology CLAS methods in VANETs, including the number of implemented algorithms (further discussion in Section “Preliminaries”), cryptanalysis improvements over other schemes, and the main contribution of security efficiency.
Literature survey.
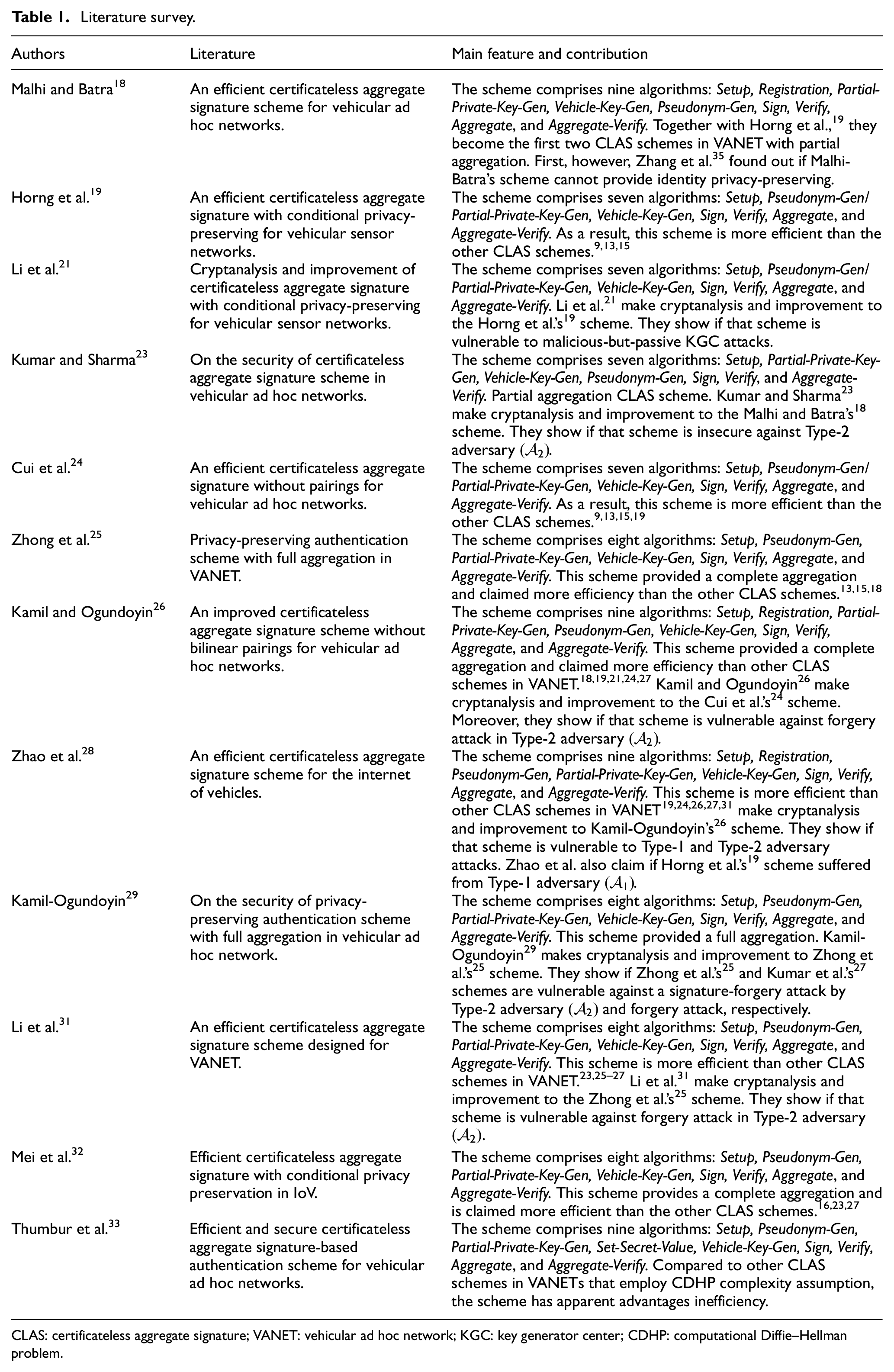
CLAS: certificateless aggregate signature; VANET: vehicular ad hoc network; KGC: key generator center; CDHP: computational Diffie–Hellman problem.
Our contributions
Our main contributions are summarized as follows:
We propose a new CLAS scheme that aims to make the computation cost a top priority and provide a secure and more effective CLAS scheme for V2V and V2I communications in VANET.
Our scheme provides a significant cost efficiency in the individual and aggregate verification, particularly compared to the other CDHP-based CLAS schemes.19,25,27,29,32
Our scheme realizes mutual authentication between vehicle and TRA to confirm that they are the corresponding legal entities.
Our scheme could provide pseudonymity, identity privacy-preserving, mutual authentication, message authentication, non-repudiation, traceability, unlinkability, and user location privacy. It also could withstand the Type-1 and Type-2 adversary attacks, replay attacks, MITM attacks, masquerade attacks, and impersonation attacks.
Organization
For a better understanding, the rest of this article is arranged as follows. In section “Preliminaries,” we provide preliminaries about the system model of CLAS, the concepts of bilinear maps, the complexity assumption we used, an outline of the CLAS scheme, security model, and other common security and privacy requirements in VANET. Then, the construction of our proposed scheme and its correctness is described in section “Our proposed CLAS scheme.” Next, section “Security proof and analysis” gives the security proof, analysis, and comparison toward other schemes, followed by the performance analysis in section “Performance analysis.” Finally, the conclusion is conveyed in section “Conclusion.”
Preliminaries
This section discusses the concept of bilinear maps, complexity assumptions, the outline of the CLAS scheme, security model, and other basic security and privacy requirements.
System model
As mentioned in section “Introduction,” in general, the topology of VANET is made up of three main components that are structured as the two-level architecture. In the CLAS scheme of VANET, we have an application server (AS) and TA (i.e. KGC and tracking authorities (TRA)) which make up the higher layer. Meanwhile, RSUs and OBUs cover the lower layer (see Figure 2). In the CLAS-VANET, AS is a trusted entity that serves as a traffic-related server for vehicles (traffic control and analysis center). It will collect traffic-related messages from the RSU and conduct additional traffic analysis. AS communicates with TA and RSU using a secure wired connection. In this scheme, RSU acts as the verifier of the signatures
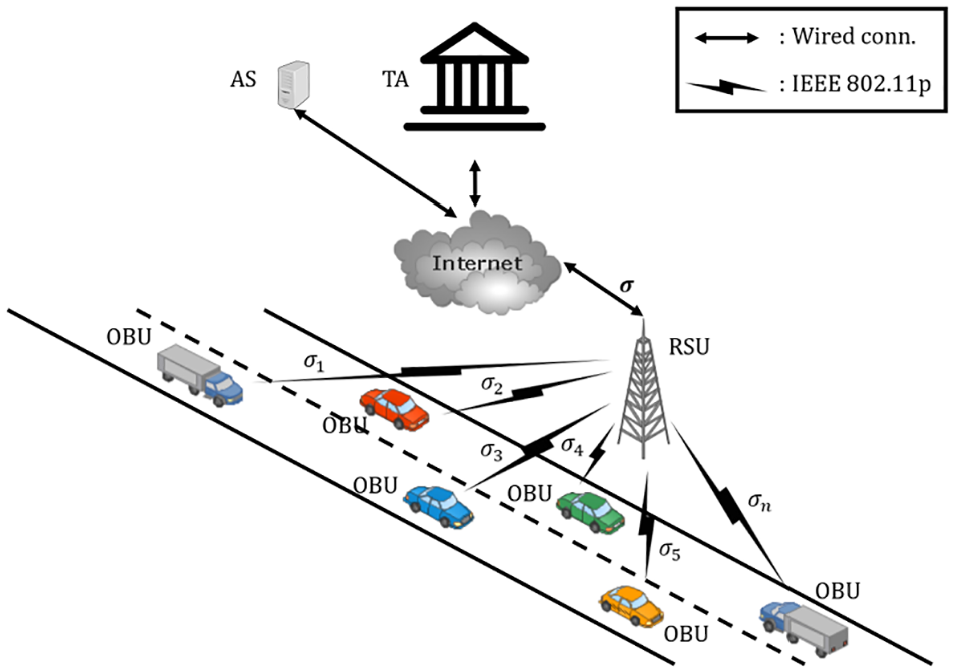
Aggregate signature in VANET.
The bilinear maps
The bilinear map
Complexity assumption
In CDHP,
Outline of CLAS scheme
Generally, a CLAS scheme includes eight following algorithms:
Security model
Depending on the behavior of adversary
Type-1 adversary
The Type-1 adversary
Type-2 adversary
The Type-2 adversary
A CLAS scheme is said to be existentially unforgeable against adaptive chosen-message and identity attacks by considering the following two games,
Game-1
The challenger
In this case,
The
Definition 1
If
Game-2
The challenger
In this case,
The
Definition 2
If
From
Other security and privacy requirements
As depicted in Figure 1, the V2V and V2I communication occur under an open wireless communication channel, so it is vulnerable to various attacks. To design a secure authentication mechanism, we define the security and privacy requirements that need to be met in VANET as follows.3,4,11,12,42
Pseudonimity
TRA can create a unique pseudo-identity from the vehicle’s real identity to protect the user’s privacy.
Identity privacy-preserving
Since the pseudonym covers the message’s sender’s identity, it would be anonymous, and only TRA can reveal their real identity.
Mutual authentication
Two parties can authenticate each other simultaneously to be assured and certain doing business exclusively with legitimate entities.
Message authentication
The receiver must be capable of differentiating the original message from the bogus message.
Non-repudiation
Messages’ senders cannot deny the information they have sent.
Traceability
TRA must be able to reveal the real identities of the pseudo-identities
Unlinkability
An adversary (vehicle or RSU) should not link two or more subsequent pseudonym messages of the same vehicle.
Replaying attack resistance
The networks could endure a passive data capture and subsequent retransmission to produce an unauthorized message by the adversaries.
MITM attack resistance
The networks could endure the eavesdropper to intercept a message and sometimes alter the intended message. Mutual authentication can prevent MITM attacks because both the sender and recipient verify each other before sending them.
Masquerade attack resistance
The networks could endure a fake identity that tries to gain unauthorized access to transmitted information through legitimate access identification.
Impersonation attack resistance
The networks could endure toward the attacker who tries to assume or impersonate the legitimate vehicles’ identity in VANET to generate the signature for any messages.
User location privacy
The networks could prevent other parties from learning the vehicle’s past, current, or next destination location.
Our proposed CLAS scheme
It is necessary to design an effective VANET authentication scheme in an environment where the communication channels are not protected. To enhance the security and improve message verification efficiency of V2V and V2I communication in VANET, we propose a CLS (
Notations of this article.

Construction
Our proposed nine-phase CLAS scheme is described as follows.
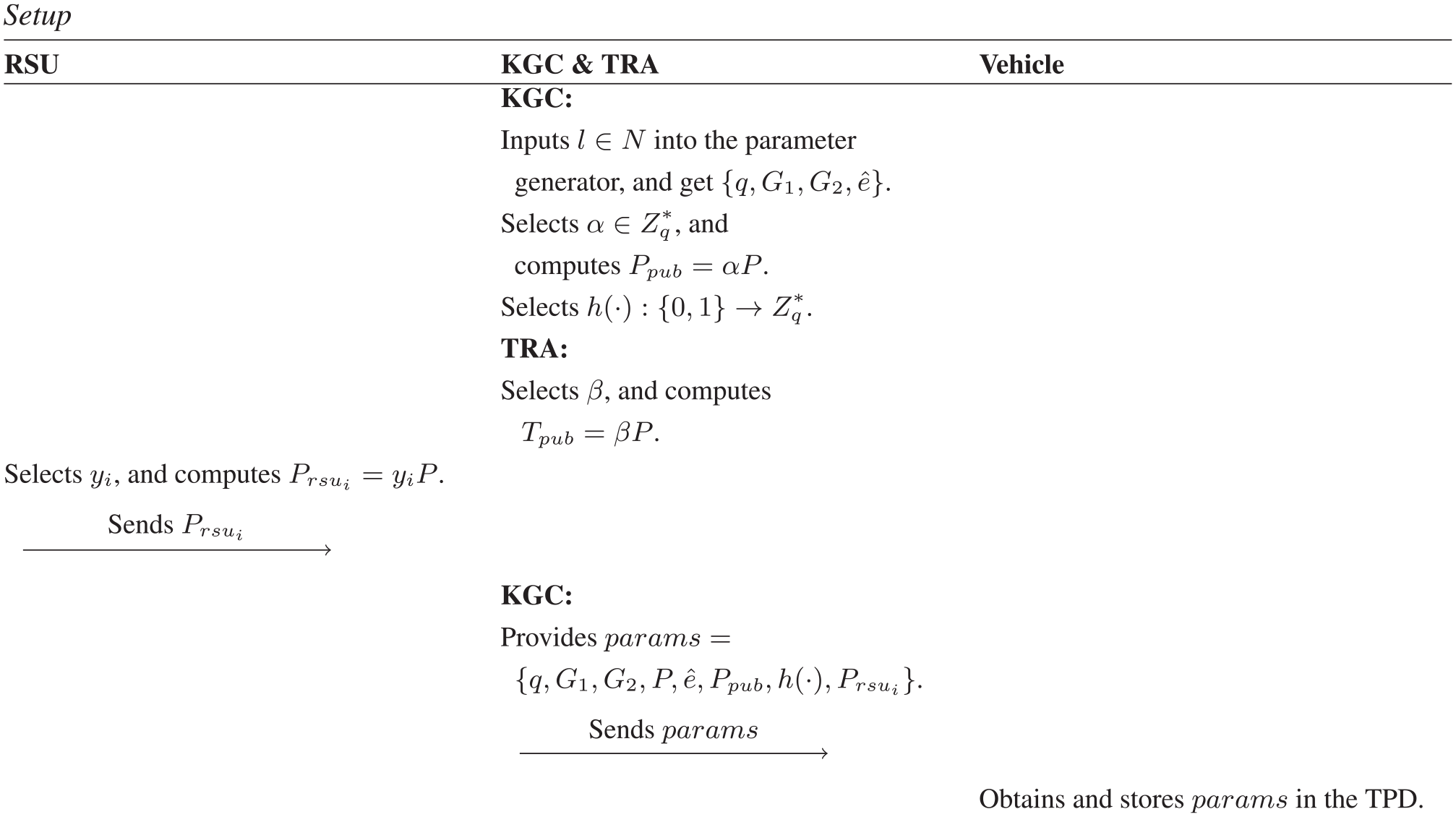
Setup
This phase aims to generate the system’s public parameters and the secret parameters of TRA and KGC. They are used for message encryption and signature generation. These parameters are used to generate a pseudo-identity of the device in the future and perform proper verification on the message’s signature. The KGC first selects a security parameter
Meanwhile, TRA selects a secret value
Registration
In this phase, every vehicle equipped with the OBU device needs to register itself to the TRA. So, in the case of dispute, the TRA can track the vehicle’s pseudo-identity and determine which vehicle owns that pseudo-identity. First, TRA chooses a hash function

Registration—Partial-Private-Key-Gen phases.
Partial-Private-Key-Gen
The KGC performs this phase to generate a partial private key
Vehicle-Key-Gen
When the vehicle needs to apply for a pseudo-identity to the TRA, first, it has to generate a private and public keys on its own. The vehicle selects a random number

After receiving (1), TRA then decrypts the message with its private key

Vehicle-Key-Gen—Pseudonym-Gen phases.
Pseudonym-Gen
After the mutual authentication process between TRA and vehicle is successful, the TRA will generate a pseudo-identity
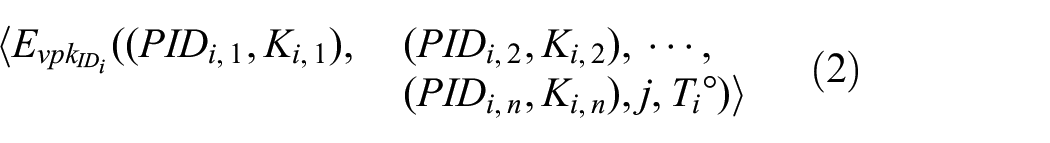
Message (2) is transmitted to the vehicle via RSU. After vehicle receives the message, it decrypts the message using its private key

and verifies whether
Sign
At this phase, when a vehicle wants to send a message or request, it needs to produce a valid certificateless signature. The receiver can verify the signature to determine whether to receive the message or not. The vehicle selects a random number

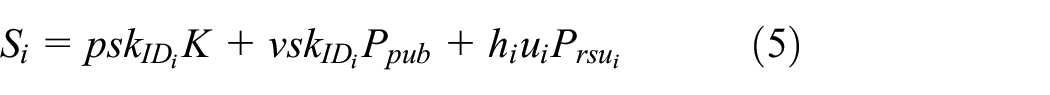
to generate a certificateless signature

Verify
At this phase, RSU acts as the verifier. It verifies whether a legitimate vehicle generated the signature and whether it has been tampered with during the transmission or not. When it senses the message transmitted by vehicles, the

If equation (6) holds, the certificateless signature is received. If the check fails, the message may have been tampered with and not accepted. The process of this phase is shown in Figure 6. To speed up the verification of frequently visited RSU, the proposed scheme pre-stores the parameter
Aggregate
RSU acts as an aggregator. On receiving

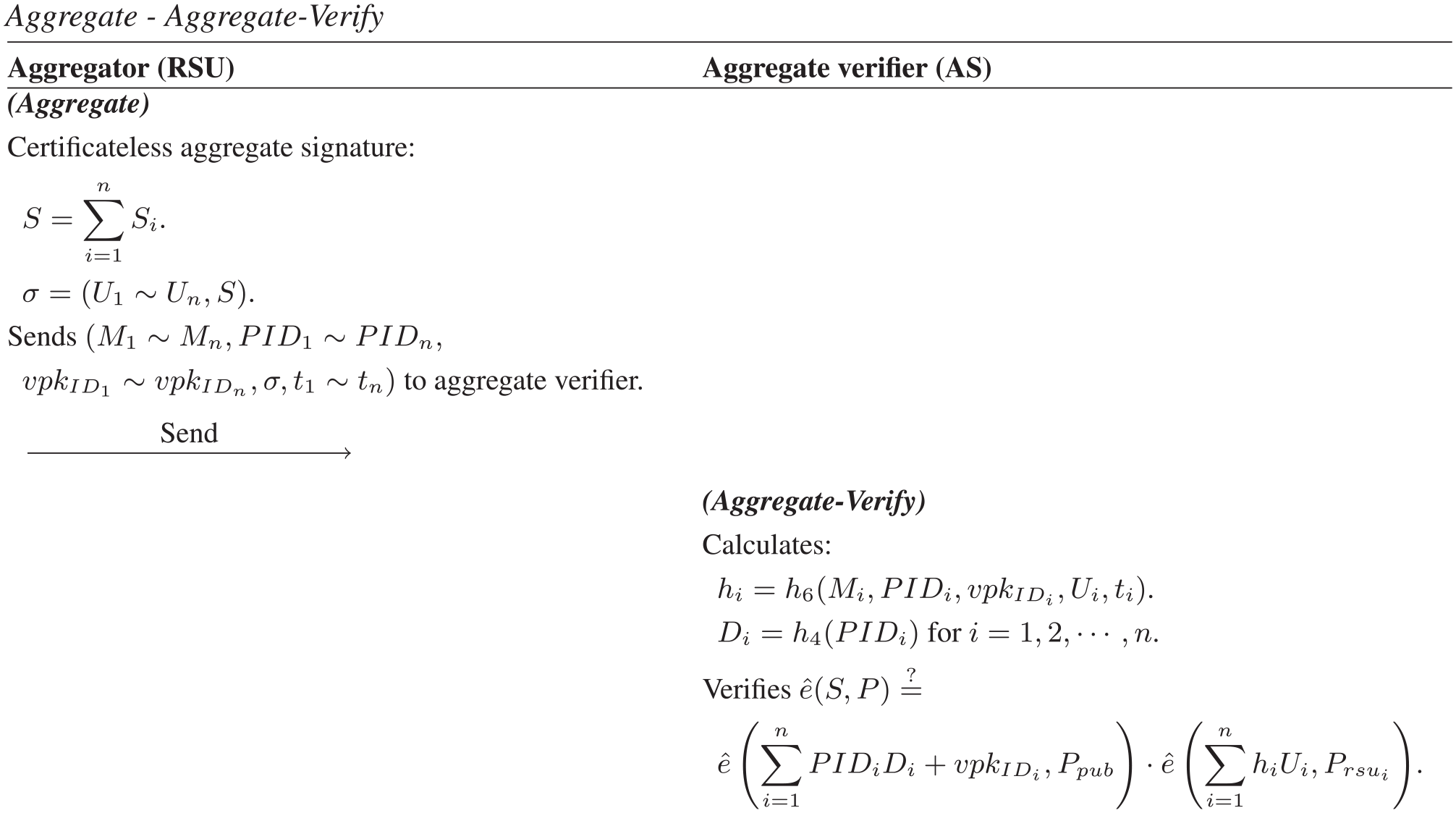
Aggregate—Aggregate-Verify phases.
Aggregate-verify
This phase is used to verify the legality of the aggregated signature by checking whether the legal device generates the signature and has not been tampered with during transmission. On receiving

If the verification fails, the message may have been tampered with and not accepted. If the verification hold, the CLAS is accepted. The process of this phase is shown in Figure 7.
When a vehicle’s density is high, such as at the intersection, the CLAS scheme enables many vehicle broadcast messages to verify and receive after aggregated. Thus, compared to verifying the signatures one by one, CLAS will increase verification efficiency.
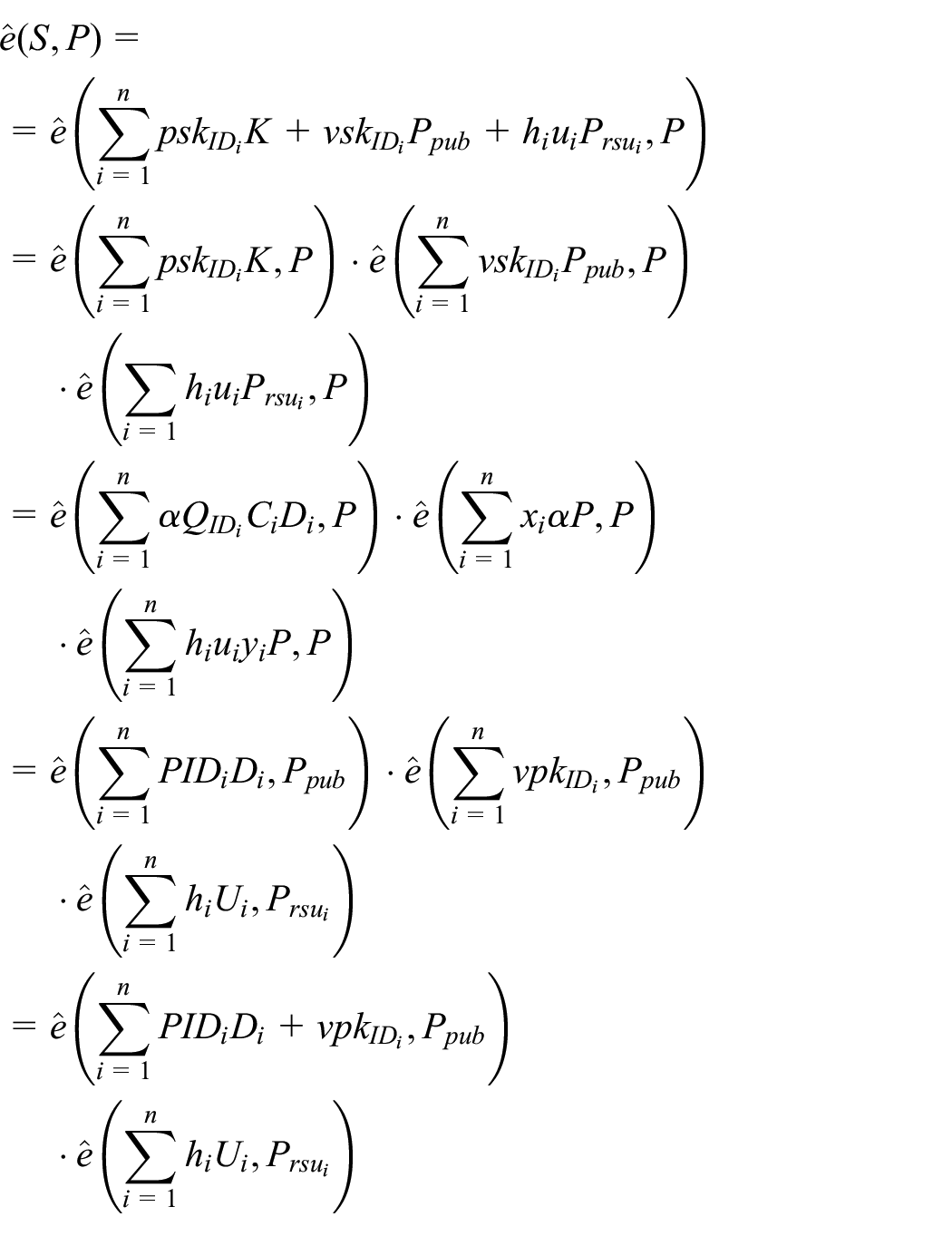
Correctness
Our proposed CLAS scheme is correct if and only if the

Security proof and analysis
In this section, we give the security proof of the proposed scheme against two types of adversaries
Comparison of the security and privacy.

V: The scheme is secure or supports feature; X: The scheme is insecure or does not support feature; M. Auth: Message authentication; Ano: Anonymity; Unlink: Unlinkability; Trace: Traceability; RAR: Resistance to replaying attack; IAR: Impersonation attack resistance.
Security proof
As mentioned in
Theorem 1
Our proposed CLAS scheme is existentially unforgeable against
Proof
We can prove the unforgeability of our CLAS scheme against
If

If
By using Forking lemma,
10
after replaying

Therefore, with
There are three events that required for
When all the above events happen, the probability of

For adequately large
Theorem 2
Our proposed CLAS scheme is existentially unforgeable against
Proof
Because the Type-2 secure proof is comparable to the Type-1 secure proof, the proof process is omitted.
Analysis of security requirements
Because V2V and V2I communication is carried out under open wireless communication channels, VANET is vulnerable to various attacks. To design a secure authentication scheme, we define the security and privacy that need to be met in VANET.3,4,12,13,43 This section analyzes whether our scheme satisfies security and privacy and then illustrates what problems we solve.
Pseudonymity
In our proposed scheme, each OBU device in a vehicle must apply multiple pseudo-identities
Identity privacy preservation
In our method, the final message
Mutual authentication
Our proposed scheme uses signature encryption and
Message authentication
Each message created by the vehicle must be signed before being delivered to the nearest RSU, so that the RSU can verify that the message has not been falsified or modified by an attacker
Non-repudiation
In our method, each vehicle must register itself to the TRA to obtain the identity
Untraceability
In
Unlinkability
In our scheme, each virtual identity can only be used once. Each time the OBU sends a message, it uses a different
Resistance to replay attack
In order to resist replay attacks, vehicles need to be verified before applying for a
Resistance to MITM attack
In order to resist MITM attack, the vehicle is required to generate a legal signature
Resistance to masquerade attack
In our proposed CLAS scheme, each vehicle broadcasts the final message using it’s
Resistance to impersonation attack
To be able to impersonate a valid vehicle,
User location privacy
As mentioned in the
Security and privacy comparison
Lu et al. 44 distinguished the privacy-preserving authentication of VANET into five categories, including certificateless signature. Based on Lu et al.’s classification, we compared the security and privacy of our proposed scheme with the other existing CLAS schemes in VANET.
In Table 3, we compare the security of our proposed CLAS scheme with the other six CLAS schemes for VANET.18,19,23,25–27 For ease of description, let
Performance analysis
To provide a fair comparison, particularly in terms of computation and communication costs, we compare our proposed scheme with the existing CDHP-based CLAS schemes in VANET.18,25,27,29,32
Computation overhead
To equally assess the performance of our proposed scheme, we take the other CDHP-based CLAS schemes in VANET,18,25,27,29,32 which also employ bilinear maps in their
Table 4 shows the comparison of the computation cost between our scheme and the other schemes,18,25,27,29,32 in terms of
Comparison of the computation cost.


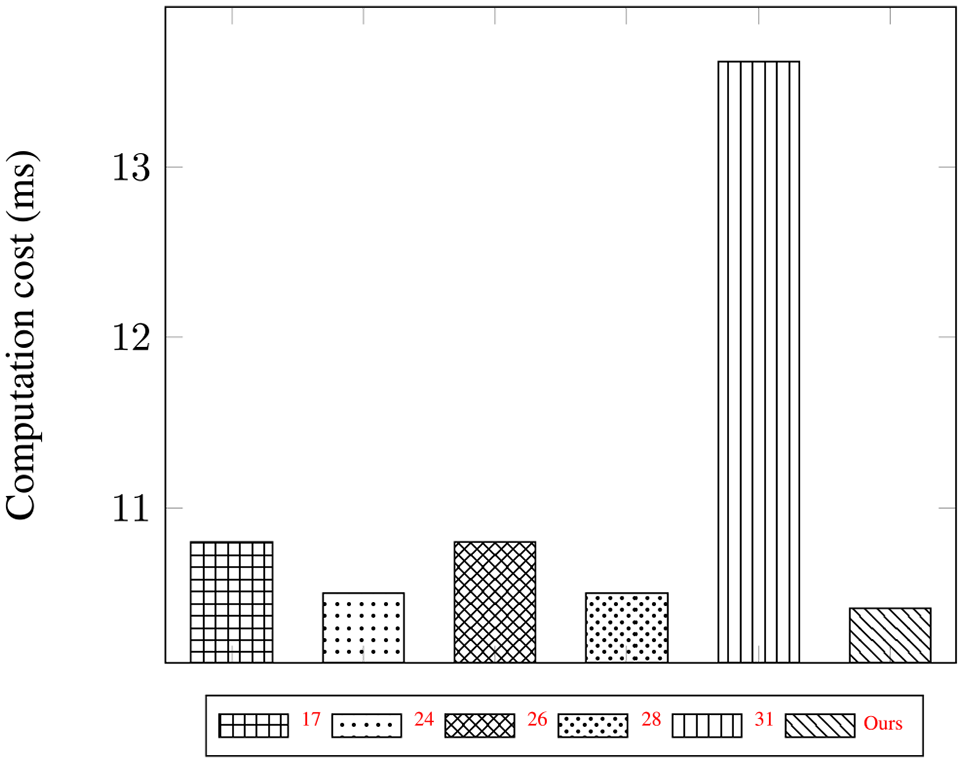

Aggregate-Verify cost.
From the
Communication overhead
Meanwhile, to evaluate the communication cost of one successful information exchanged in V2I or V2V communication, we follow the general parameters mentioned in most related schemes.26,34,47 We consider the length of a cyclic additive group
In Malhi and Batra’s
18
scheme, vehicle sends final message containing

Communication cost for a single message.
Comparison of the communication cost.

Conclusion
In this article, we proposed a CLAS scheme to improve security and privacy in VANET, with efficiency becoming the main spotlight. Our proposed scheme could solve the mentioned issues by satisfying all security and privacy requirements such as pseudonymity, message authentication, untraceability, unlinkability, privacy preservation, and resistance to some common attacks. According to an extensive performance study, our proposed scheme is substantially more efficient in terms of computation and communication costs than the existing reputable schemes. Hence, it is more suitable for both V2V and V2I communication in VANET.
Footnotes
Handling Editor: Yanjiao Chen
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research was partially supported by the Ministry of Science and Technology, Taiwan (ROC), under contract numbers MOST 109-2221-E-468-011-MY3 and MOST 110-2622-8-468-001-TM1.
