Abstract
Adapting recent formal perspectives on shared interbrain activity in social communication, we explore a model of “East Asian” implication of an effect on an adversary, and take a general approach to degrading an opponent’s rate of cognition. These developments represent surprisingly routine application of the asymptotic limit theorems of information and control theories to organized conflict, modified by the necessity of making “adiabatic” approximations allowing the theorems to work sufficiently well. The resulting probability models provide a rigorous foundation for constructing statistical tools for the analysis of real-time, real-world data involving contention on “Clausewitz Landscapes” of fog, friction, and deadly adversarial intent.
… [E]ven rudimentary weapons can carry the day in the hands of motivated, patient humans who are prepared—and able—to make whatever progress is required. —Ankersen and Martin.
1
1. Introduction
East Asian—and current Russian—views on persistent conflict between polities differ significantly from the “Wehrmacht-ized” tactical preoccupation of many Western nations. Jullien
2
characterizes Chinese perspectives on strategy in these terms: For something to be realized in an effective fashion [in the Chinese view], it must come about as an effect. It is always through a process (which transforms the situation), not through a goal that leads (directly) to action, that one achieves an effect, a result … Any strategy thus seems, in the end, to come down to simply knowing how to implicate an effect, knowing how to tackle a situation upstream in such a way that the effect flows “naturally” from it …
Simplistically, the aim is to have fully boxed in one’s opponent well before open combat. That is, one gradually and imperceptibly imposes ultimately debilitating constraints on an adversary.
Bouwmeester, 3 in his Figure 6, contrasts the North Atlantic Treaty Organization’s (NATO) current policy of “Cumulative Destruction” with Russia’s “Systematic Disruption.” The essence of the contrast seems to lie in the very first row of that figure, “strength against strength” versus “strength (yours) against weakness (your opponent’s).”
As General George Armstrong Custer is reported to have put it at Little Big Horn, “Ride to the sound of the guns.”
Stalemate in Korea, defeat in Vietnam, catastrophe in Iraq, humiliation in Afghanistan. But by God, the United States is going to match China and Russia in hypersonic lifting vehicles …
And the Band Played On …
Or, if you prefer, Down Another Rabbit Hole …
Here, we will try to understand something of these dynamics, adapting recent formal results on shared interbrain activity in social communication. 4 That is, socially interacting higher animals—most particularly humans—have been found to share brain dynamics during certain social interactions. It is possible to view such sharing as the transmission of a message from one mind to another.
We will first examine an East Asian-style imprinting of a constraining “message” onto an opponent, and then extend the argument to constraining enemy cognition rate.
2. How to “implicate an effect”
Suppose we have developed a robust scalar index of dominance between two polities, call it
How does
A “dominant” partner transmits signals to a “subordinate” in the presence of noise, sending a sequence of signals
It is then possible to apply a rate distortion argument. The rate distortion theorem—for stationary, ergodic systems—states that there is a convex rate distortion function that determines the minimum channel capacity, written
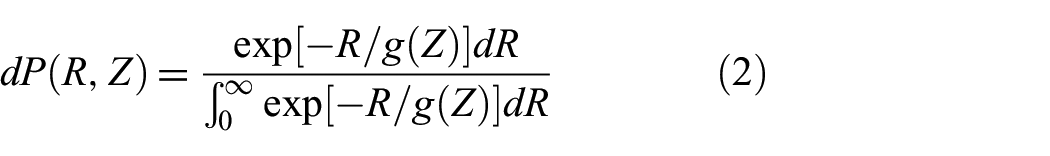
The “central trick” is to construct a Boltzmann pseudoprobability in the dominance measure
where the function
The “partition function” integral in the denominator of Equation (2) is simply
For a Gaussian channel using the squared distortion measure, the rate distortion function
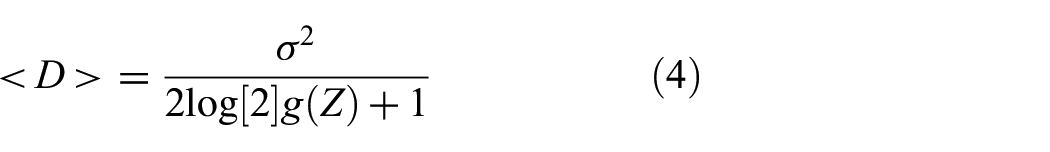
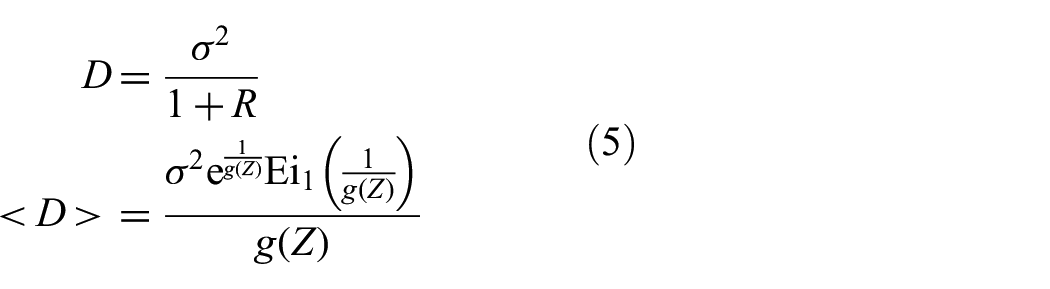
From these relations, using Equation (2), and after some manipulation, it is possible to calculate the “average average distortion”
For the so-called “natural channel”
where
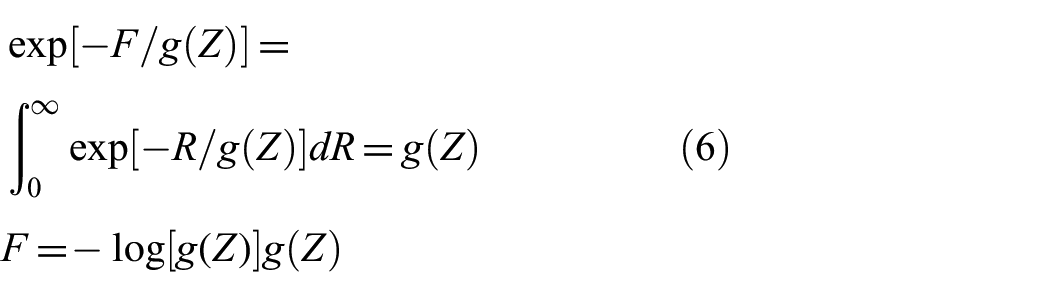
How do we find the “temperature” relation
Here, we take further formalism from statistical mechanics, using the “partition function”
It is then possible to define an “iterated entropy” in terms of
where
For the Gaussian channel, taking the Lambert W-function of order zero, and setting
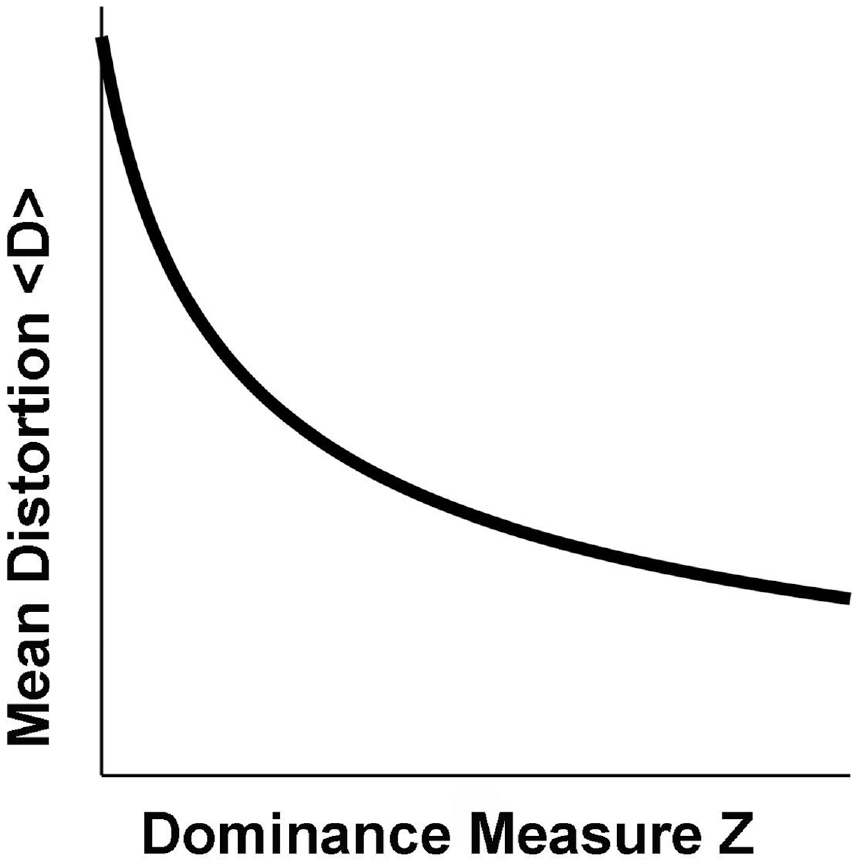
Mean distortion
For the “natural” channel, again with the W-function of order zero, and again taking
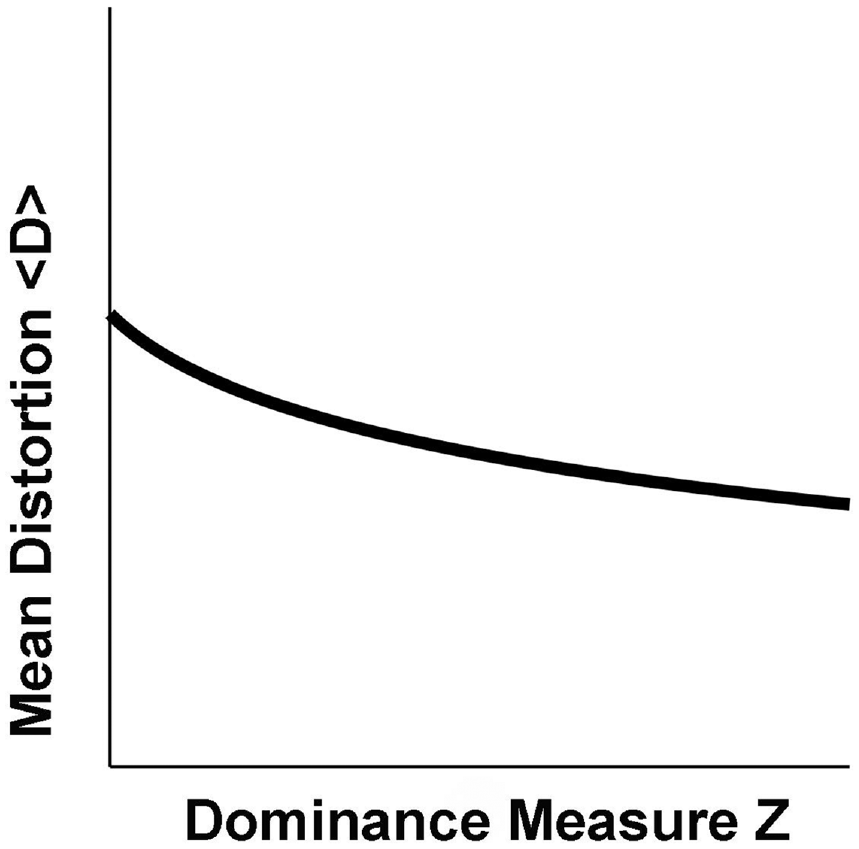
Mean distortion
Higher
Similar results will follow for all possible rate distortion functions that must be both convex in
Extension of the model to both nonergodic and nonstationary conditions more likely to mirror real-world conditions, or at least going beyond the nonequilibrium steady state assumption, requires further work.
The model can, in theory, be extended using the ergodic decomposition of a nonergodic process using the methods of Shields et al. 6
Otherwise, we are constrained to adiabatically, piecewise, stationary ergodic (APSE) systems that remain as close to ergodic and stationary as needed for the rate distortion theorem to work, much like the Born–Oppenheimer approximation of molecular physics in which rapid electron dynamics are assumed to quasi-equilibrate about much slower nuclear oscillations, allowing calculations using “simple” quantum mechanics models.
3. How to constrain an opponent’s cognition rate
Cognition during combat is not the kind of pre-conflict “transmitted correlation” studied above, and requires more general address, although degradation and deception remain standard tools at tactical, operational, and strategic scales.
A, perhaps the, central inference is by Atlan and Cohen: 8 that cognition, through active choice, demands reduction in uncertainty, implying the existence of information sources “dual” to any cognitive process. The argument is unambiguous and direct, and serves as the foundation to a comprehensive approach.
A first step is to view “information” as a resource matching the importance of personnel and such material agents and agencies as ammunition, armored vehicles, trucks, and fuel.
3.1. Information and other resources
Here, we must move beyond a “simple” measure of dominance between pre-conflict polities.
At least, three resource streams are required by any cognitive entity facing real-time, real-world challenges. The first is measured by the rate at which information can be transmitted between elements within the entity, determined as an information channel capacity, say
The third regards material resources available at a rate
These three rates may well—but not necessarily—interact, a matter characterized as a 3 by 3 matrix analogous to, but not the same as, a simple correlation matrix. We write this as
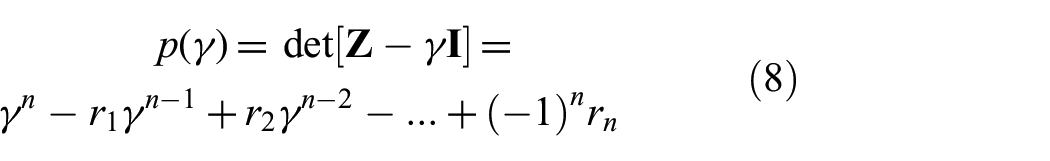
An
These scalar invariants make it possible to project the full matrix down onto a single scalar index
Clever scalarization, however, enables approximate reduction to a one-dimensional system.
Taking
3.2. Cognition and information
Only in the case that cross-sectional and longitudinal means are the same can information source uncertainty be expressed as a conventional Shannon “entropy.”5,10 Here, we only require that source uncertainties converge for sufficiently long paths, not that they fit some functional form. It is the values of those uncertainties that will be of concern so that we study “Adiabatically Piecewise Stationary” (APS) systems, in the sense of the Born–Oppenheimer approximation for molecular systems that assume nuclear motions are so slow in comparison with electron dynamics that they can be effectively separated, at least on appropriately chosen trajectory “pieces” that may characterize the various phase transitions available to such systems. Extension of this work to nonstationary circumstances remains to be done.
This approximation can be carried out via a fairly standard Morse function iteration. 11
The systems of interest here are composed of cognitive submodules that engage in crosstalk. At every scale and level of organization, all such submodules are constrained by both their own internals and developmental paths and by the persistent regularities of the embedding environment, including the cognitive intent of colleagues, in a broad sense, and the regularities of “grammar” and “syntax” imposed by the embedding social structure.
Furthermore, here are structured uncertainties imposed by the large deviations possible within that environment, again including the behaviors of adversaries who may be constrained by quite different developmental trajectories and “punctuated equilibrium” evolutionary transitions.
The Morse function construction assumes a number of interacting factors:
As Atlan and Cohen 8 argue, cognition requires choice that reduces uncertainty. Such reduction in uncertainty directly implies the existence of an information source “dual” to that cognition at each scale and level of organization. The argument is unambiguous and sufficiently compelling.
Cognitive physiological processes, like the immune and gene expression systems, are highly regulated, in the same sense that “the stream of consciousness” flows between cultural and social “riverbanks.” That is, a cognitive information source
Environments (in a large sense), also have sequences of very high and very low probability: night follows day, hot seasons follow cold, and so on.
“Large deviations,” following Champagnat et al. 12 and Dembo and Zeitouni, 13 also involve sets of high probability developmental pathways, often governed by “entropy” analog laws that imply the existence of yet one more information source.
Full system dynamics must then be characterized by a joint, nonergodic information source uncertainty
that is defined path-by-path and not represented as an “entropy” function.
10
Consequently, each path will have its own
The set
Again, we are projecting the spectrum of essential resources onto a scalar rate
The underlying equivalence classes of developmental or dynamic system paths used to define groupoid symmetries can be defined fully in terms of the magnitude of individual path source uncertainties,
Recall the central conundrum of the ergodic decomposition of nonergodic information sources. It is formally possible to express a nonergodic source as the composition of a sufficient number of ergodic sources, much as it is possible to reduce planetary orbits to a Fourier sum of circular epicycles, obscuring the basic dynamics. Hoyrup 14 discusses the problem further, finding that ergodic decompositions are not necessarily computable. Here, we need focus only on the values of the source uncertainties associated with dynamic paths.
3.3. Dynamics
The next step is to build an iterated “free energy” Morse function
11
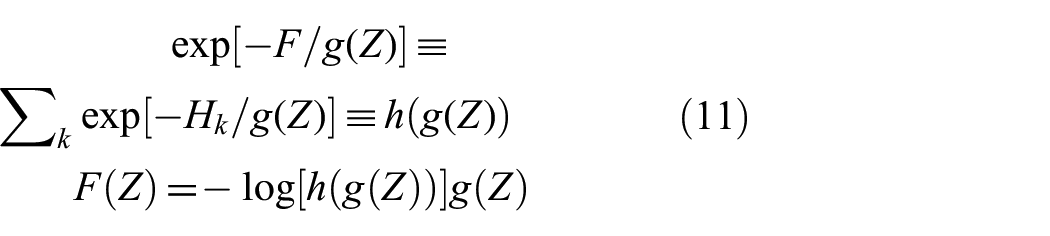
from a Boltzmann pseudoprobability, based on enumeration of high probability developmental pathways available to the system
where
The essential point is the ability to divide individual paths into two equivalence classes, a small set of high probability paths consonant with an underlying “grammar” and “syntax,” and a much larger set of vanishingly low probability, essentially a set of measure zero.
The temperature-analog characterizing the system, written as
We define the “iterated free energy” Morse function as
where the sum is over all possible high probability developmental paths of the system, again, those consistent with an underlying grammar and syntax. Again, system paths not consonant with grammar and syntax constitute a set of measure zero that is very much larger than the set of high probability paths.
Feynman 15 makes the direct argument that information itself is to be viewed as a form of free energy, using Bennett’s “ideal machine” that turns a message into work. Here, we again invoke an iterated—rather than a direct—free energy construction.
The disjunction described above—into high and low probability equivalence classes representing paths consonant with, or discordant from, underlying grammar and syntax—should be seen as the primary “groupoid phase transition” affecting cognitive systems.
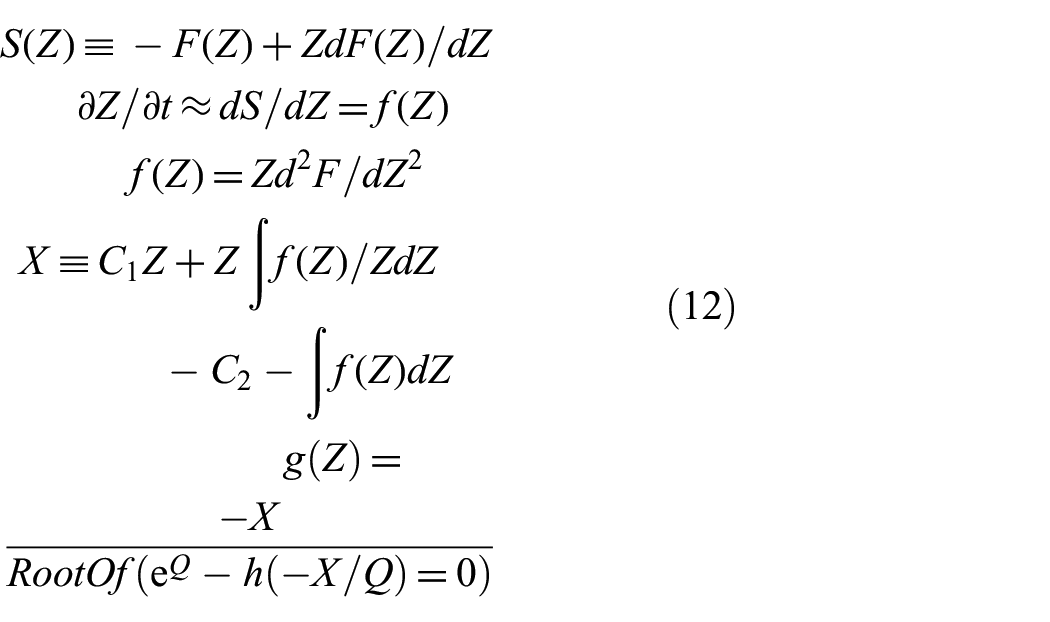
Dynamic equations follow from invoking a first-order Onsager approximation akin to that of nonequilibrium thermodynamics
7
in the gradient of an entropy measure constructed from the “iterated free energy”
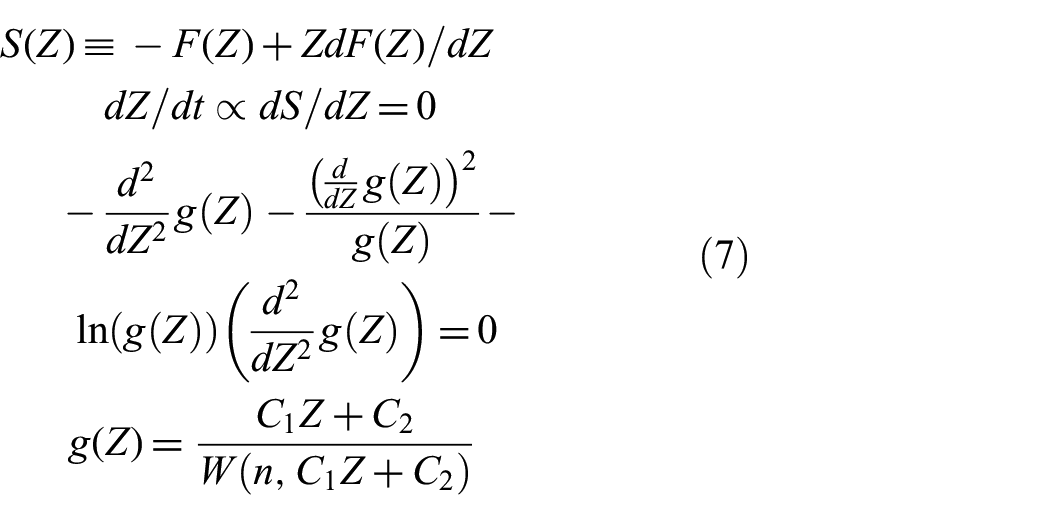
where the last relation follows from an expansion of the third part of Equation (12) using the second expression of Equation (11), and
Three important—and somewhat subtle—points:
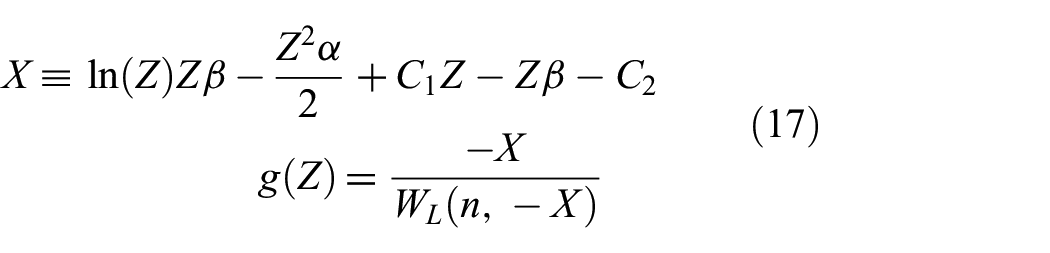
The “RootOf” construction actually generalizes the not-so-well-known Lambert W-function.19,20 This can be seen by letting
Information sources are not microreversible, that is, palindromes are highly improbable, e.g., “eht” has far lower probability than “the” in English. In consequence, there are no “Onsager Reciprocal Relations” in higher dimensional systems. The necessity of groupoid symmetries appears to be driven by this directed homotopy.
Typically, it is necessary to impose a delay in provision of
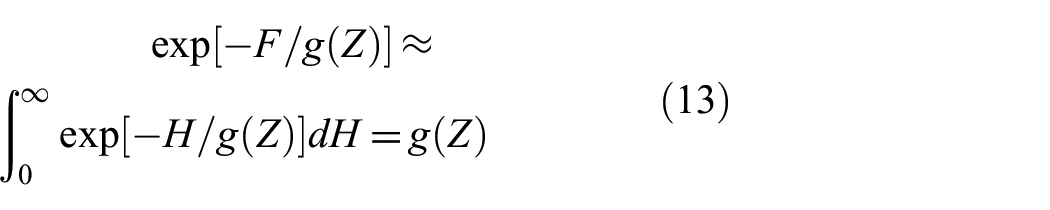
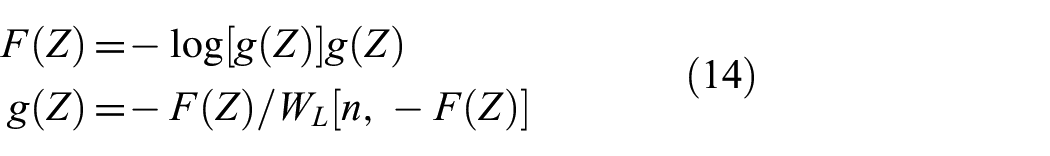
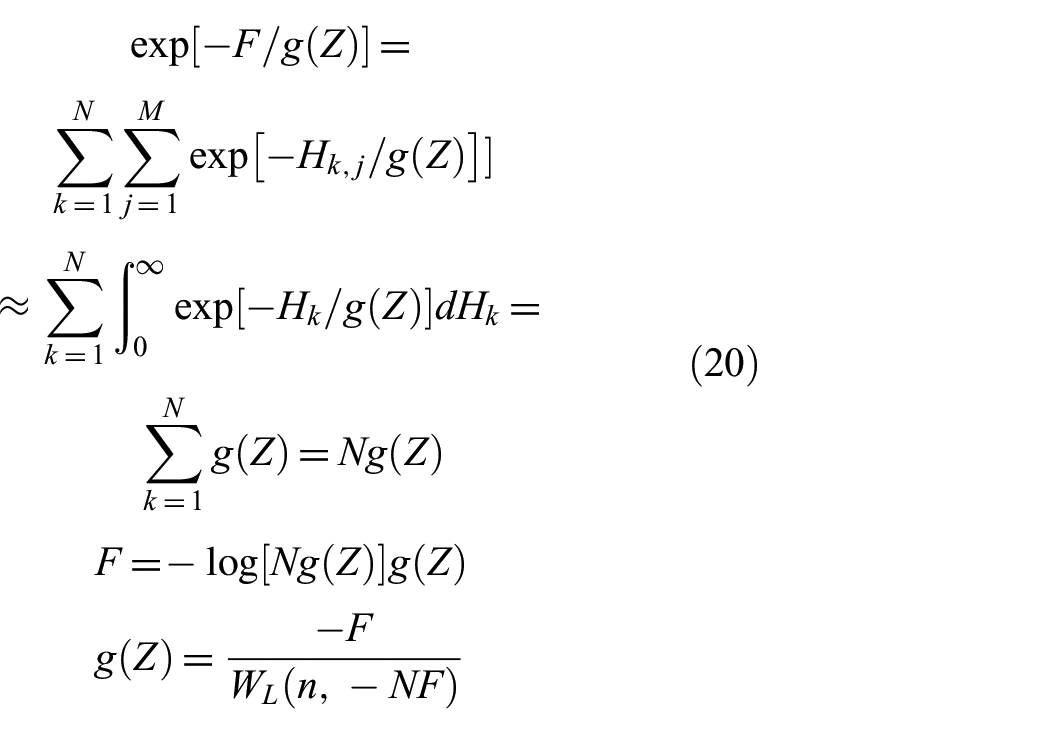
Suppose, in the first of Equation (12), it is possible to approximate the sum with an integral, so that
Again,
It is real-valued only for
In theory, specification of any two of the functions
3.4. Cognition rate
For phase transitions in physical systems, there is generally a minimum temperature for punctuated activation of the dynamics associated with given group structure—underlying symmetry changes associated with the transitions of ice to water to steam, and so on. For cognitive processes, following the arguments of Equation (5), there will be a minimum necessary value of
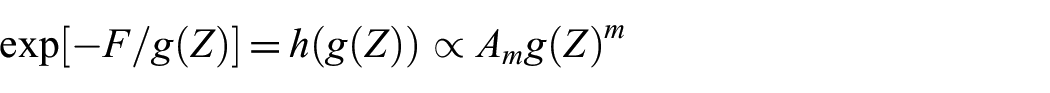
Taking a reaction rate perspective from chemical kinetics, 21 we can write an expression for the rate of cognition as
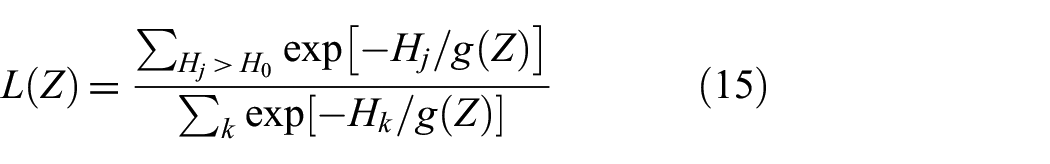
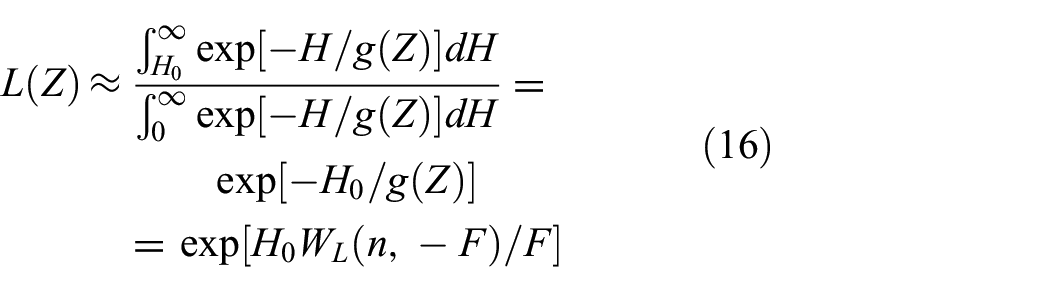
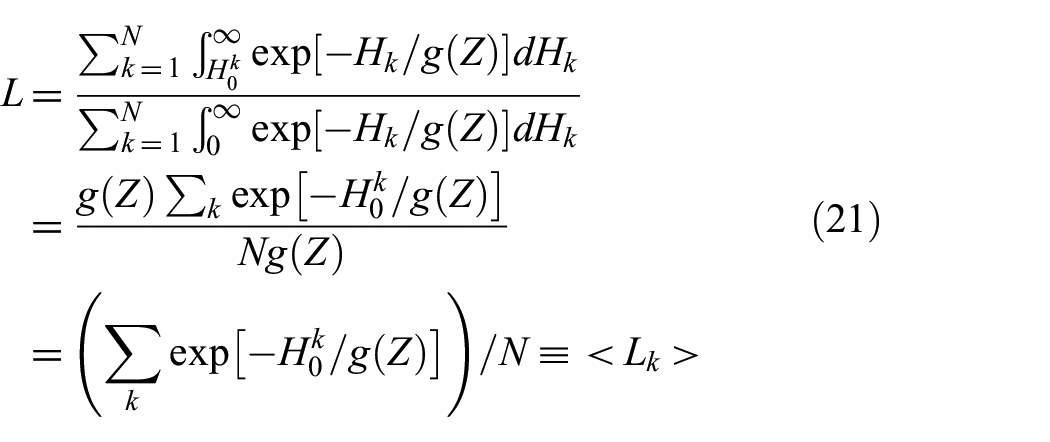
If the sums can be approximated as integrals, then the system’s rate of cognition at resource rate index
where
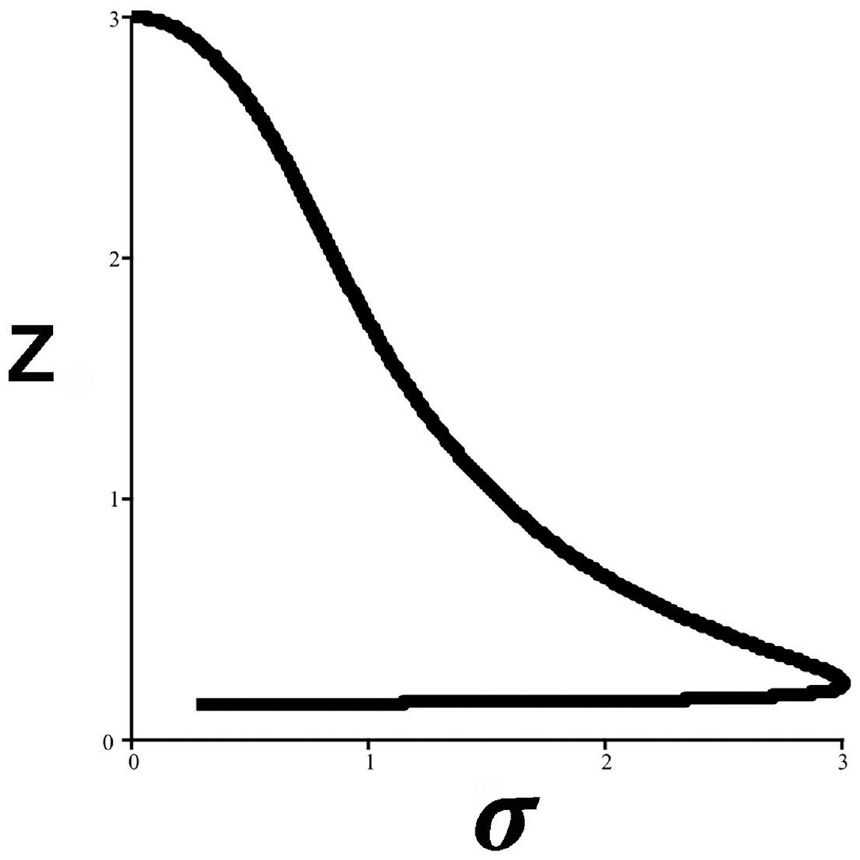
Figure 3 shows
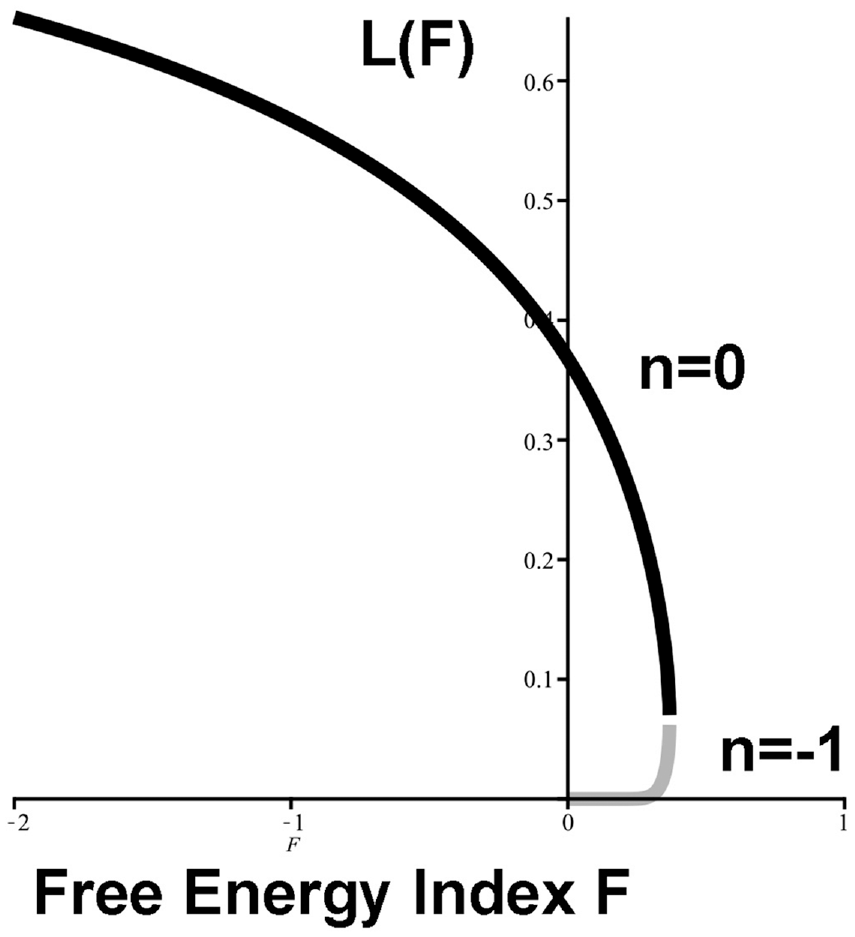
Rate of cognition from Equation (16) as a function of the iterated free energy measure
The Lambert W-function is only real-valued for orders
This development recovers what is essentially an analog to the data rate theorem from control theory,
22
in the sense that the requirement
3.5. An example 1: friction
We again approximate the sum in Equation (11) by an integral—so that,
with, again,
Similar results follow if
that is, if the function
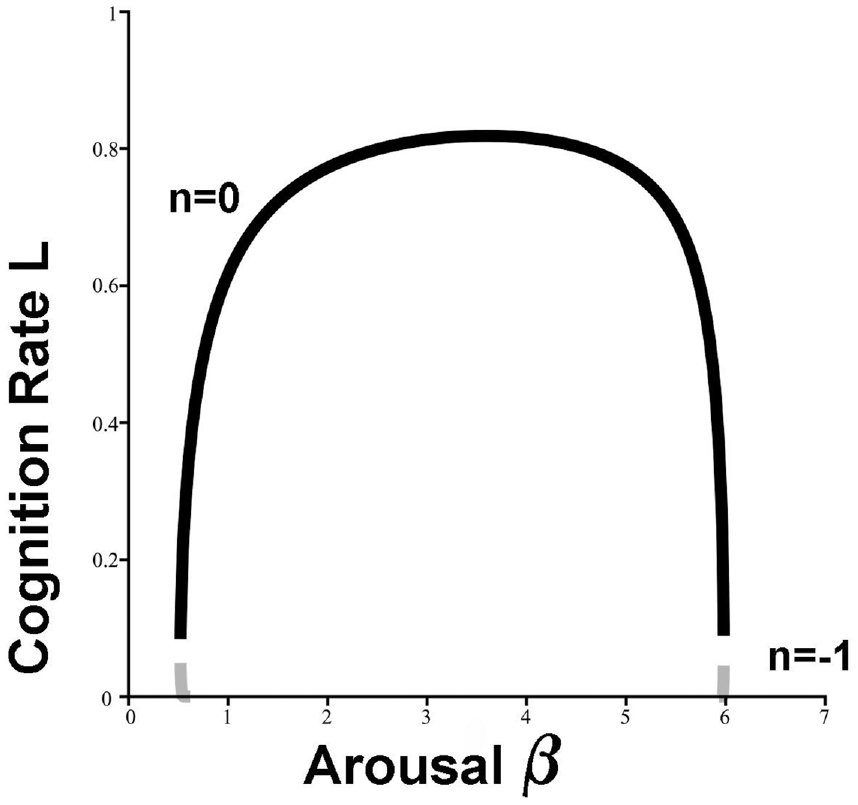
Classic “inverted-U” signal transduction for the cognition rate based on Equation (17), setting
3.6. An example 2: adding fog to friction
It is complicated—but not difficult—to incorporate stochastic effects into cognition rate dynamics based on Equation (17), via standard methods from the theory of stochastic differential equations. We take an example based on Figure 4, fixing
The approach is to apply the Ito Chain Rule
25
to the expression
where
Figure 5 shows the result, the solution equivalence class
Numerical solution equivalence class
Similar analyses to Figure 5 across increasing values of
4. Moving on . . .
4.1. Cooperation: multiple workspaces
The emergence of a generalized Lambert W-function in Equation (12), reducing to a “simple” W-function if
where, again, the Lambert W-function emerges.
This expression has punctuated onset of a giant component of linked nodes only for
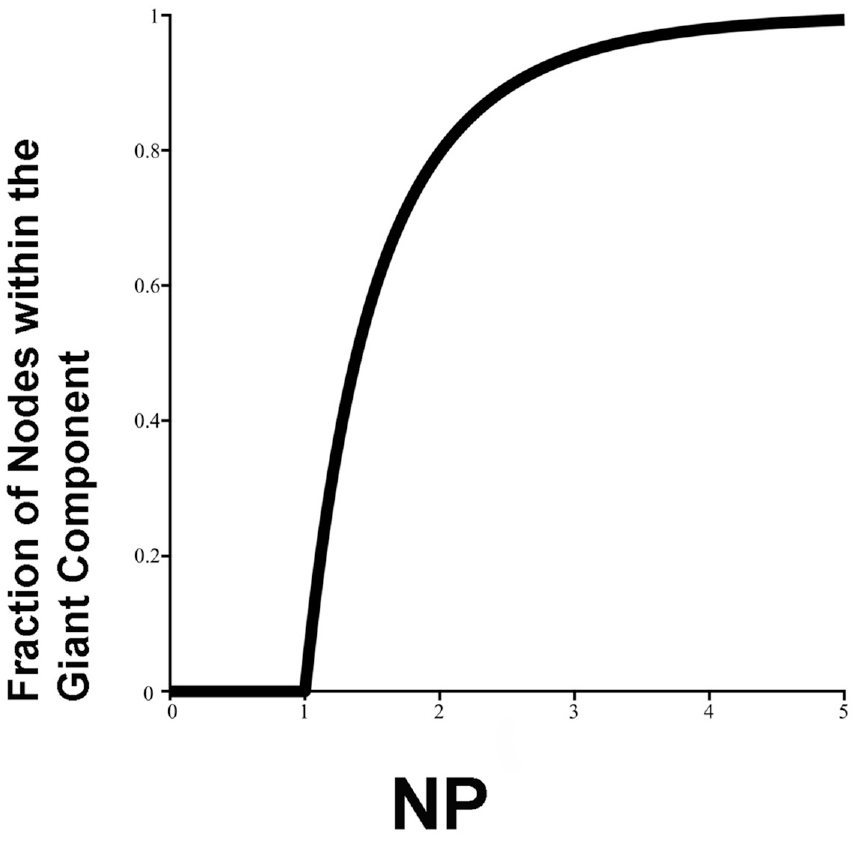
Within broadly “social” groupings, interacting cognitive submodules—individuals—can become linked into shifting, tunable, temporary, workgroup equivalence classes to address similarly rapidly shifting patterns of threat and opportunity. These might range from complicated but relatively slow multiple global workspace processes of gene expression and immune function to the rapid—hence necessarily stripped-down—single-workspace neural phenomena of higher animal consciousness. 29
More complicated approaches to such a phase transition—involving Kadanoff renormalizations of the Morse function free energy measure
By contrast here, while multiple workspaces are most simply invoked in terms of a simultaneous set of the
4.2. Network topology is important
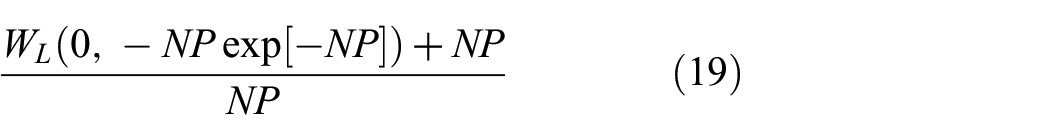
We can, indeed, calculate the cognition rate of a single “global workspace” as follows.
Suppose, we have
The sum over
The rate of cognition of the linked-node giant component can be expressed as
where, not entirely unexpectedly,
If we impose the approximation of Onsager nonequilibrium thermodynamics, i.e., defining
The appearance of
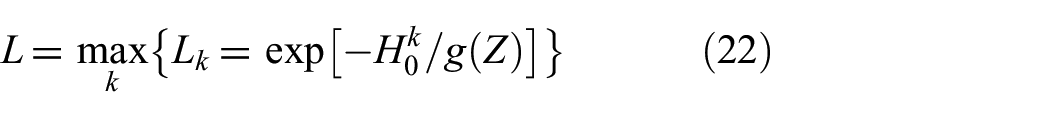
Such considerations lead to a fundamentally different picture that is not just possible, but often observed, i.e., a transmission model. Consider something like a colony of prairie dogs under predation by hawks. A “sentinel” pattern emerges, rather than the average system of Equation (21), through the “bottleneck” of a single, very highly optimized, “subcomponent” of the larger social structure. This involves a hypervigilant individual—or a small number of such appropriately dispersed—whose special danger signal or signals can be imposed rapidly across the entire population—postures, vocalizations, or both. Then
where max is the maximization across the set
Other network topologies are clearly possible. For example, in a rigidly hierarchical linear-chain business, military, or political setting,
The critical dependence of a system’s cognitive dynamics on its underlying “social topology” has profound implications for theories of the “extended conscious mind.”31,32 A particular expression of such matters involves failures of institutional cognition on wickedly hard problems. 33
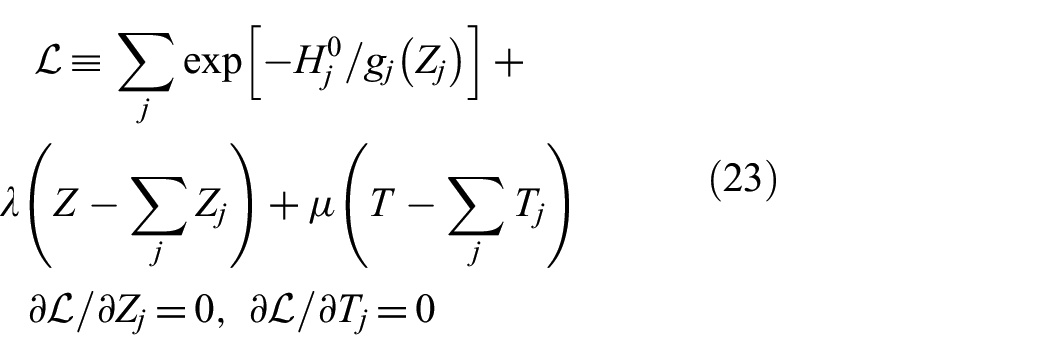
4.3. Time and resource constraints are important
Multiple workspaces, however, can also present a singular—and independent—problem of resource delivery, taking the scalar
If we assume an overall limit to available resources across a multiple workspace system
where we assume
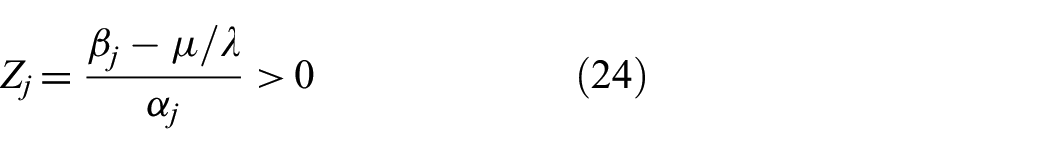
This leads, after some development, to a necessary expression for individual subsystem resource rates as
Cognitive dynamics—the rates of cognition driven by the rate of available resources
5. Further theoretical development
Following the arguments of Wallace, 36 the cognition models can be extended in a number of possible directions, much as is true for “ordinary” regression theory.
Perhaps, the simplest next step is to replace the relation
A next “simple” generalization might be replacing the scalar index
Likewise, it is possible to introduce discrete and distributed delays into the “frictional” relation
Further development could involve expanding the “Onsager approximation” in terms of a “generalized entropy”
As with regression equations much beyond
6. A remark on method
The approach to organized conflict taken here stands in some contrast to the avalanche of war studies initiated by Richardson, 38 work that emphasizes “universal” patterns in armed confrontation like power laws and such.39–43 Typically, as Lee et al. 40 describe, these and similar studies find that armed conflict data display features consistent with scaling and universal dynamics in both social and physical properties like fatalities and geographic extent, in particular conflict avalanches consisting of spatiotemporally proximate events that have been joined into clusters, implying that universality in conflict manifests in both local structure as well as in the statistics across many conflicts that span larger scales.
However, and paradoxically, almost exactly similar results follow from statistical analysis of literary texts. As Serrano et al.
44
put the matter, Our results show that key regularities of written text beyond Zipf’s law, namely burstiness, topicality and their interrelation, can be accounted for on the basis of two simple mechanisms, namely frequency ranking with dynamic reordering and memory across documents, and can be modeled with an essentially parameter-free algorithm. The rank based approach is in line with other recent models in which ranking has been used to explain the emergent topology of complex information, technological, and social networks … It is not the first time that a generative model for text has walked parallel paths with models of network growth. A remarkable example is the Yule–Simon model for text generation … that was later rediscovered in the context of citation analysis …, and has recently found broad popularity in the complex networks literature …
Such homologies should be a red flag, raising serious questions regarding the utility of these approaches for the fundamental strategic enterprise in which organized conflict is always embedded. One of the central themes of strategic thinking and planning is contained in the basic question “So What!.” 45
Such queries, including perhaps the one most often slighted—“Is This Prudent?”—are ignored at peril.
The perspective of this analysis is different in kind from these “universal” studies and begins with the classic Clausewitz Zweikampf, but moves somewhat beyond to view the central matter as an extended dialog between cognitive entities, a sort of duet in which each side is highly sensitive to the “song” of the other partner. Organized conflict is, after all, a joint—sometimes choral—performance.
Regularities in organized conflict—scaling laws, bursting patterns, and such—will emerge according to the “modes” of the musical traditions chosen by the performers. But central matters revolve around the content of the songs exchanged, and the skills of the singers.
Shakespeare is far more than the statistical regularities of his textural canon.
Clauset et al.,
39
following their analysis of power law regularities in public “terrorist event” data sets, are careful to raise the matter of context: … [A]lthough it may be tempting to draw an analogy between terrorism and natural disasters, many of which also follow power-law statistics, we caution against such an interpretation. Rather, a clear understanding of the political and socioeconomic factors that encourage terrorist activities and an appropriate set of policies that directly target these factors may fundamentally change the frequency-severity statistics in the future and break the statistical robustness of the patterns … observed to date.
Beware studying the grain of the paper on which a message is written without understanding the content and intent of the message. Indeed, as skilled practitioners from Sun Tzu on down constantly emphasize, decontextualizing the historical trajectories and cross-sectional imbalances channeling organized conflict is one of the surest roads to hell.
7. Discussion
Adapting formal perspectives on shared interbrain activity in social communication, 4 we have explored a model of “East Asian” implication of an effect on an adversary, and taken a more general approach to degrading an opponent’s rate of cognition. The development has been based on surprisingly routine application of the asymptotic limit theorems of information and control theories to organized conflict, modified by the necessity of making various “adiabatic” approximations so that the theorems work sufficiently well.
Extension of the approach to highly networked multiple “workspace” systems under time and resource constraints seems relatively straightforward, although critically dependent on the details of network topology.
The probability models explored here would seem to provide something of a rigorous foundation for building new statistical tools aimed at the analysis of real-time, real-world data on organized conflict at and across various scales and levels of organization. Proper use of such tools under the burdens of fog, friction, and adversarial intent, of course, would require its own skill set.
Indeed, as with all such quantitative studies of human conflict, failure to place the results within the embedding cultural, social, and historical contexts will engender failure of enterprise: “Know Your Enemy.”
Footnotes
Acknowledgements
The author thanks Dr D.N. Wallace for useful discussions and the reviewer for comments useful in revision.
Funding
This research received no specific grant from any funding agency in the public, commercial, or not-for-profit sectors.