Abstract
This study examines ransomware crime through the lens of neutralisation theory, and explores techniques used by alleged offenders to justify their involvement in ransomware attacks. This work focuses on highly organised ransomware groups that not only conduct attacks but also operate as Ransomware-as-a-Service businesses. The interview data (
Introduction
Ransomware is one of the most significant cybercrime types in the world, affecting both public- and private-sector organisations (Europol, 2023). This form of crime involves encrypting someone's data and holding it hostage until they pay a ransom. Lately, organisations have improved backup practices, leading to tactical displacement: Lang et al. (2023) explain that hackers not only encrypt but also steal data.
Organised crime groups (or Ransomware-as-a-Service - RaaS) operators who not only conduct attacks but also sell the malware) that are believed to be behind some of these ransomware attacks (RTF, 2022) share characteristics with legitimate businesses. Their operations are complex and systematic with clearly defined roles and responsibilities (Matthijsse et al., 2023; Meland et al., 2020; O’Kane et al., 2018). Internal business processes include technical operations such as malware development, sales and spread (i.e., distributors who infect victims' devices) (Alwashali et al., 2021; Meland et al., 2020) as well as managerial operations, including hiring and firing internal and external personnel, providing training, and utilising marketing to increase brand reputation, which potentially motivated some of our interviewees to step out of hiding and speak about their activities. RaaS operators also outsource various services in order to obtain information about vulnerabilities, gain initial access to the victim's network, host a website with a rogue hosting provider, and launder criminal proceeds. RaaS operators may also use the services of darknet marketplaces to assist in malware sales (Meland et al., 2020). Using crime script analysis, Matthijsse et al. (2023) represented the complexity of ransomware operations by identifying eight scenes necessary for a ransomware ecosystem to exist: (1)
In this research, we examine narratives from individuals who claimed to be ransomware offenders through the lens of neutralisation theory. We believe our study makes three valuable contributions: (1) we approach this topic from a point rooted in social science, while most research on ransomware is focused on the technological aspects of the attack (Connolly et al., 2023), with the exception of several studies analysing ransomware from a social perspective, such as Connolly et al. (2020), Hoevel (2024), Matthisse et al. (2023), Meurs et al., 2022; (2) to the best of our knowledge, this is the first time this problem is analysed using neutralisation theory; and (3) the results add to the very limited body of knowledge on organised cybercrimes. Given that ransomware offenders tend to operate anonymously, interview data is limited (Maimon and Louderback, 2019).
In the initial phase of this work, we have used the original theory of neutralisation proposed by Sykes and Matza (1957). However, as data analysis proceeded, we realised that the five original neutralisation techniques were not sufficiently granular to represent all the arguments used by ransomware actors in detail. Accordingly, we considered ‘supplementary’ techniques that have been proposed subsequently (Brewer et al., 2020). Our preliminary findings suggested that alleged ransomware actors employ six techniques of neutralisation, including two original techniques –
Although the extant literature offers a considerable amount of supplementary techniques, they vary in terms of granularity, and many overlap with each other. Fritsche (2002: 485) argued that collectively these supplementary techniques ‘do not offer a theoretically sound taxonomy, nor an exhaustive list’, which can lead to inconsistent research findings (Maruna and Copes, 2005). Furthermore, Brewer et al. (2020) cautioned that the findings from existing cybercrime research must be interpreted carefully due to the aforementioned overlap, and they called for the adoption of methods that can clearly distinguish between the different neutralisation techniques. Kaptein and Van Helvoort (2019) recently proposed a new model. Using both deductive and inductive approaches, they searched for neutralisation techniques that have been identified in the academic and professional literature and organised them in a logical and systematic way. Leveraging their work, we endeavoured to identify and classify neutralisation techniques adopted by reported ransomware actors using their model. We found nine neutralisation techniques relevant to ransomware crime (i.e., three more than in our initial study). In addition, the granularity of the model allowed us to reveal distinct attributes for each technique. Such detailed findings provided us with a deeper understanding of the reasons invoked by offenders to commit ransomware crime.
Theoretical framework
Neutralisation theory
The theory of neutralisation, proposed by Sykes and Matza (1957: 666), suggests that individuals employ strategies that shield them ‘from self-blame and the blame of others after the act’. Neutralisation techniques help them rationalise engagement in wrongful behaviour, diminishing both the consequences of the actions and the burden of guilt. Hinduja (2007) surmised that this allows them to partake in rule-breaking activities without adopting a deviant identity and, thus, disregard societal norms. The five original techniques of neutralisation proposed by Sykes and Matza (1957) are
Kaptein and Von Helvoort (2019)'s model comprises four levels. The highest level specifies two broad categories:
Kaptein and Von Helvoort (2019: 1263) argue that these categories are exclusive and exhaustive. They note that the techniques are associated with different levels of responsibility. Denying deviant behaviour, for example, is safer than denying responsibility because one admits less guilt when using the former and has more neutralisation options available to them. Furthermore, when people deny deviant behaviour, it is safer to distort the facts rather than negate the norms because when the facts are changed and no norm is broken, there is no reason to neutralise someone's behaviour by negating the norm. However, when the facts cannot be changed, people acknowledge the facts but aim to modify the existing norm to excuse their behaviour. When deviant behaviour cannot be denied, however, it is safer to shift responsibility to circumstances before individuals admit the lack of self-control. Essentially, the model commences with neutralisations in which people distort the facts, asserting that no crime took place, and culminates with individuals acknowledging the occurrence of the crime and even the harm caused, all the while contending that they are mere humans and hence cannot be held responsible for their actions. With such granularity, the model was deemed highly appropriate to understand how offenders justify their involvement in ransomware attacks.
Method
Data
In selecting applicable participants, we focused on alleged members of ransomware groups that not only conduct ransomware attacks but also operate RaaS model by selling their variants to others. Interview data used in this study was collected by three media and four cyber intelligence organisations (Table 1 and Supplemental File A) and is openly available on the internet. Although the use of primary data would be preferable, arranging interviews with ransomware offenders is challenging due to the nature of their business (i.e., anonymity is the cornerstone of their operations). Working with secondary data, we could not validate the authenticity of some interviews; we relied on the reputation of the companies that published these interviews and claimed that these interviewees were ransomware offenders.
The data used in the study.
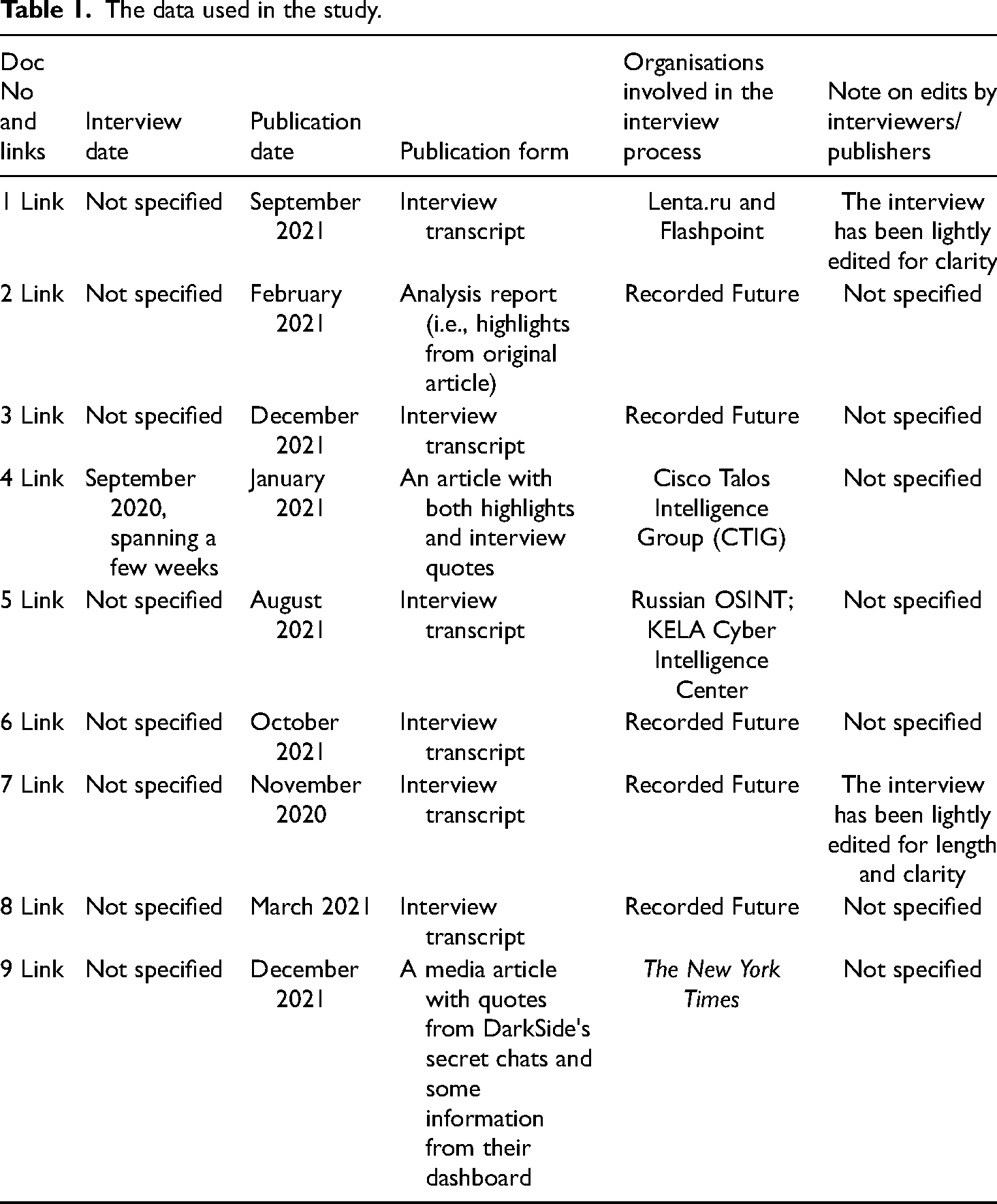
The search for interview data involved entering specific keywords (including ‘ransomware criminal interview’, ‘ransomware offender interview’ and ‘ransomware crime interview’) in the Google search engine. From the results, we selected nine documents (that fit our criteria) published between November 2020 and December 2021. These include six interview transcripts with reported offenders, two highlights from the interviews, and a report containing information from a ransomware group's dashboard and secret chats between group members. Published in English, these documents offer information about the motives and justifications of these offenders. Some interviews were conducted, translated and published by the same organisation, while others were conducted by one organisation and translated and published by another (Supplemental File A). Two documents contain a notice informing readers that an interview had undergone slight editing for clarity. To ensure results reproducibility, we provided links to the files in Table 1.
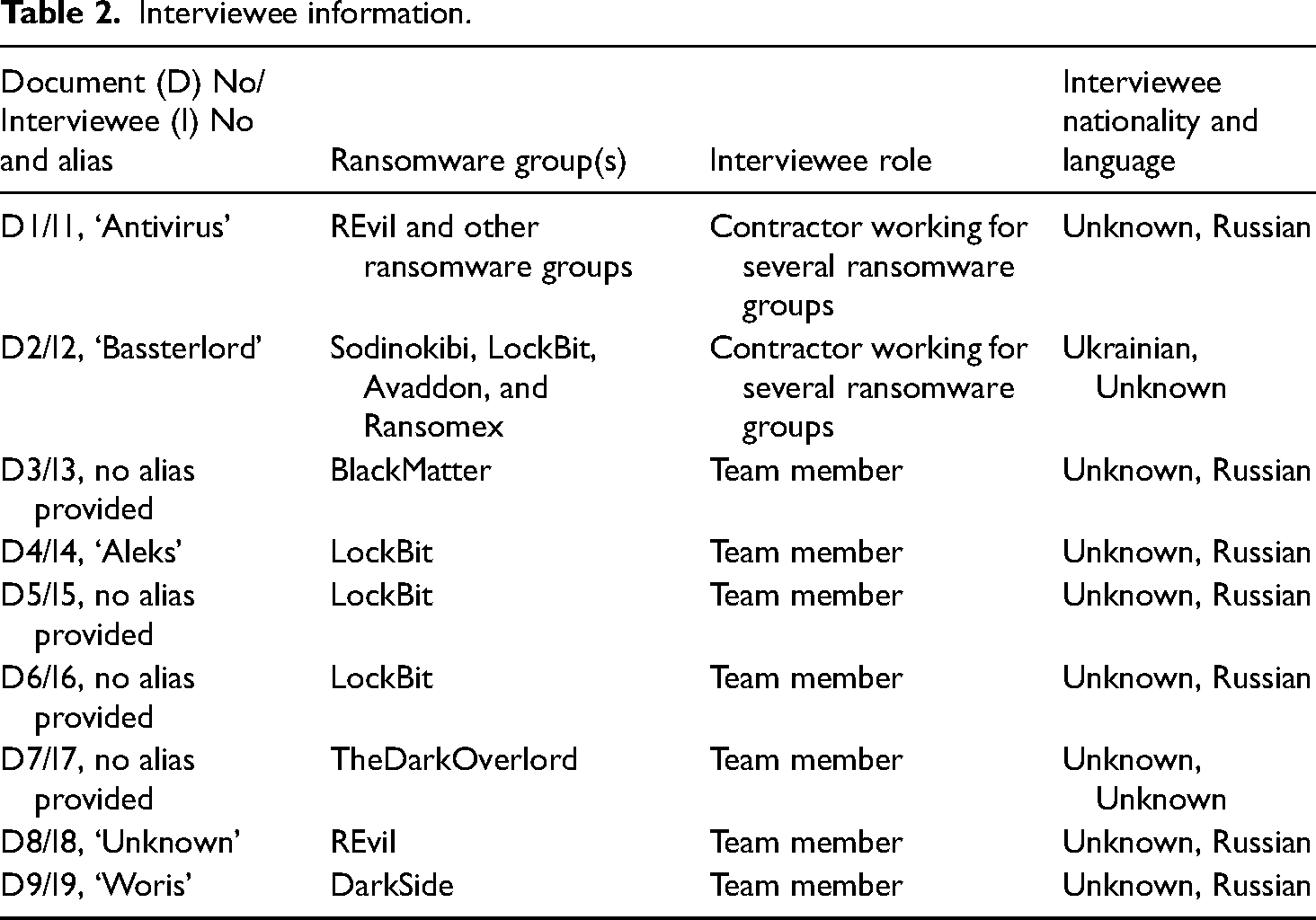
Table 2 contains demographic information about the interviewees (
Interviewee information.
Data analysis
Two researchers, referred to as R1 and R2, conducted the analysis in six phases (Figure 1). In Phase 1 (
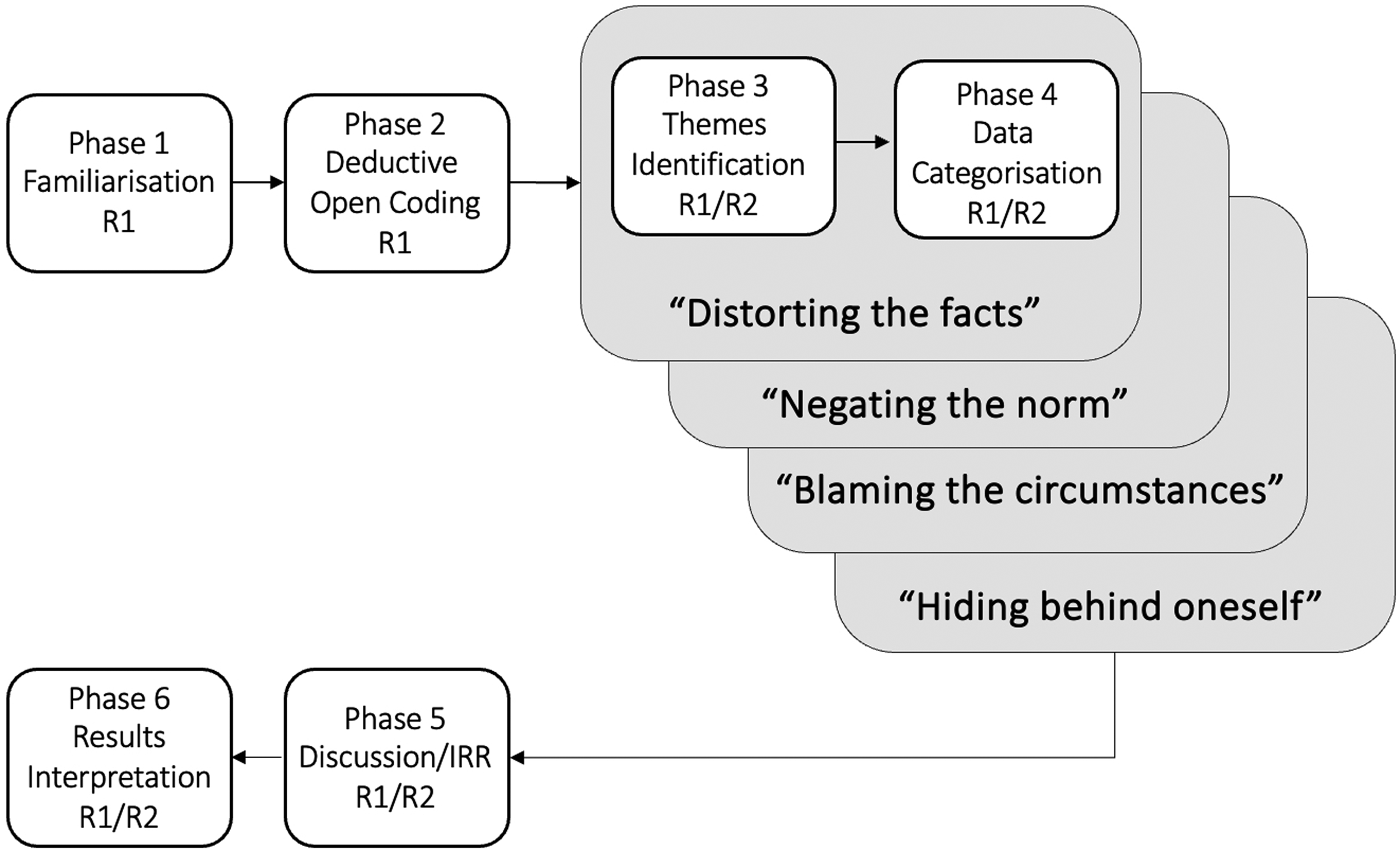
Data analysis.
As explained above, the neutralisation framework that guided our work consists of four sub-categories with three neutralisation techniques each. R1 and R2 independently ascertained if the 46 quotes matched the first sub-category (‘Distorting the fact’ in the
Findings
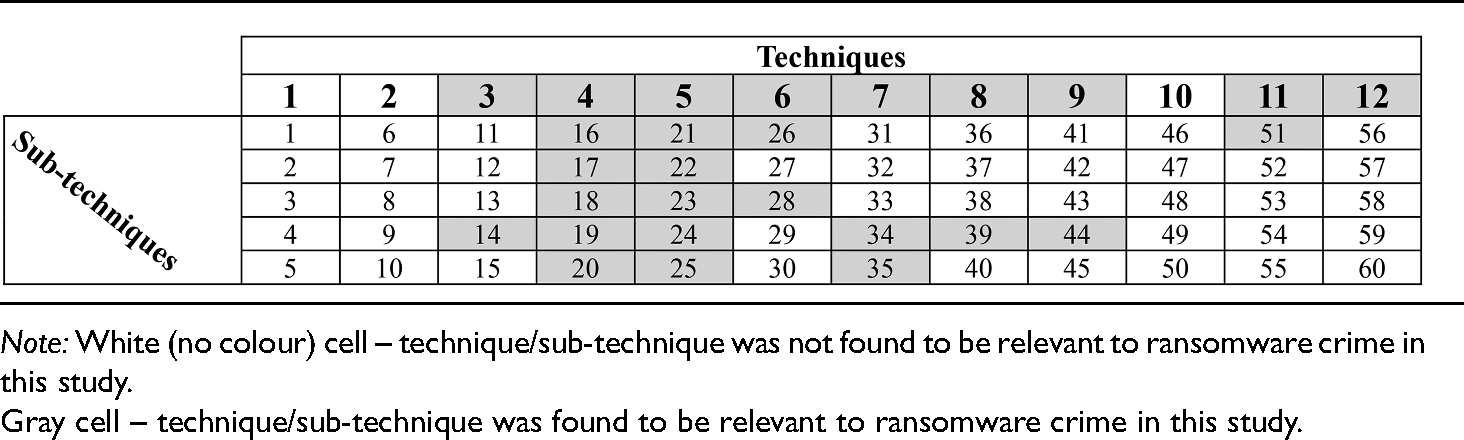
Nine neutralisation techniques and 19 sub-techniques were identified in the interviews (Table 3).
Neutralisation techniques and sub-techniques (greyscale version).
Distorting the facts
Kaptein and Von Helvoort (2019) explain that
Inventing new facts (Technique 3)
When inventing new facts, the alleged offenders created a new reality, so the violated norm no longer (fully) applies. Five interviewees (Quotes (Q): 5, 9, 13, 20, 22, 27, 28) invented facts about some aspects of their criminal activities (sub-technique 14: the invention of circumstances). Some, for instance, diminished the severity of the crime by asserting that ransom payments, however large, are inconsequential to the victims (Q: 9, 27, 22): The company always has the ability to pay funds and restore all its data. (Interviewee 3)
Others made general statements about companies' investments in cyber security, before suggesting that these attacks are the natural consequence of their poor decisions (Q: 20, 28). Interviewee 6 fantasised that all organisations have means to pay the ransom: There are no companies without money [that cannot pay a ransom]. (Interviewee 6)
Kaptein and Von Helvoort (2019) explain that when
Negating the norm
The second category of neutralisations where offenders deny their deviant actions is called
Reducing norms to facts (Technique 4)
Kaptein and Von Helvoort (2019) suggested that offenders may negate a norm by reducing it to facts (sub-technique 16: the reduction to facts) (Q: 2, 4, 19, 20, 22, 25, 28). One interviewee, for instance, stated that the world is built on financial gain and therefore there is no point in discussing whether ransomware is moral or not: The world is unfair to the weak, everything is built on financial gain. (Interviewee 1)
Kaptein and Von Helvoort (2019) argued that, in such scenarios, people simply assert that there are only facts, leaving no space for norms or normative judgements. Once facts are present, no interpretation of the situation is required. Maruna and Copes (2005: 227) noted that such neutralisations (e.g., ‘i.e. just the way the world works’) are more likely to be associated with persistent criminality. This has relevance in the context of ransomware since perpetrators commonly begin as hobbyists before engaging in minor cybercrimes, and eventually evolving into career criminals (Wall, 2021). Topalli (2006: 488) also found that offenders can argue that victimising is an unavoidable aspect of their life – ‘It is just the fact’. Since the situation is out of their control, the offender can avoid feeling guilty.
Alternatively, individuals can reduce norms by using labels (sub-technique 18: the reduction to labels). Once a crime is re-labelled, it can then be denied, for example, referring to ‘car theft’ as ‘joyride’ (Copes, 2003), and stealing in the workplace as ‘income adjusting’ (Shigihara, 2013). Interviewee 5 referred to victims as ‘business sharks’ or ‘capitalists’, suggesting that it is acceptable for them to target (other) ‘immoral’ organisations (Q: 19, 20): We prefer to attack those who are like us – ‘business sharks’. (Interviewee 5)
Another interviewee acknowledged wrongdoing but appeared to be apathetic to the societal norms and the opinions of others (sub-technique 17: the reduction to taste) (Q: 4).
Essentially, people acknowledge that there is morality (i.e., a set of norms) but it is subjective, which allows them to reject any form of accountability towards others and society at large. People commonly use these statements to justify deviant behaviour: ‘It is my own life’, and ‘It is none of your business’ (Kaptein and Von Helvoort, 2019: 1269). Eaton and Henry (1999) referred to this neutralisation as the claim of individuality, where people assert that they are unconcerned about the opinions of others regarding their behaviour.
When reducing norms to facts, interviewees also tend to blame another party by shifting the focus from their deviant inclinations to unethical propensities of potential victims (Interviewee 6) and justice system (Interviewee 5), which gives them the right to commit crime (sub-technique 19: the reduction to the immorality of accusers) (Q: 3, 20, 28).
Coined as
Alleged offenders also claim that a particular norm is invalid or irrelevant to them (sub-technique 20: the reduction to an invalid norm). Interviewee 6, for instance, used it to justify their involvement in ransomware activities (Q: 25).
In such instances, offenders actually acknowledge the existence of morality, but they assert their superiority above conventional norms. Kaptein and Von Helvoort (2019: 1269–1270) present the following examples: ‘We are above the law’, ‘Rules are meant for other people’ and ‘Ethics and laws are for lesser firms’.
Appealing to another norm (Technique 5)
When appealing to another norm, individuals acknowledge that the norm is violated, but they justify the violation by appealing to another more important norm (Q: 6, 7, 10, 11, 12, 20, 23, 24, 25, 28, 30, 31). Here, Interviewees 3, 4 and 5 (Q: 6, 11, 12, 24) were found to appeal to higher goals (sub-technique 21: the appeal to higher goals): We do not deny that business is destructive, but we look deeper. As a result of these problems, new technologies are developed and created. If everything was good everywhere, there would be no room for new development. (Interviewee 3)
Schönbach (1990) referred to this technique as
One interviewee explained that given the manner in which companies conduct business, it is unrealistic to anticipate outcomes different from what is currently happening to them (sub-technique 22: the appeal to others) (Q: 20, 28): There are cunning companies that do not want to spend money on protecting their network, pay salaries for good system administrators, and then [spend money] on ransom. (Interviewee 6)
Essentially, these offenders argue that the norm to be followed is determined by others – in this case by victims. If one does not invest in security, they cannot expect anything else but these attacks. In a sense, what others do (not do) is used for neutralisation. Prior literature referred to this technique as the
Interviewees 3 and 5 appealed to their right to benefits (sub-technique 23: the appeal to rights) (Q: 7, 10, 23): We love our job. The money is not the target ‒ the process is the important thing… The one of self-realisation. You should do the things that you can do the best because you need to realise your potential ‒ this is a basic necessity for every human. (Interviewee 5)
Kaptein and Von Helvoort (2019: 1270) explained that when using this neutralisation technique, individuals ‘hide behind moral and legal rights, by calling upon laws, rules, agreements, and promises’. For instance, Interviewee 5 claimed their right to self-realisation, while Interviewee 3 – to a right to proper material reward. Schönbach (1990) referred to this technique as the
Similarly, quotes 7, 10, 23, 25, 30 demonstrated that alleged offenders (Interviewees 3, 5, 6 and 7) appeal to self-interest, arguing that it is reasonable to give priority to their own needs (sub-technique 25: the appeal to self-interest or lack thereof): There is one life and we take everything from it. (Interviewee 3)
Barriga and Gibbs (1996) referred to this phenomenon as
Findings also demonstrate that Interviewee 8 hides behind good intentions (sub-technique 24: the appeal to good intentions). In one particular instance, an interviewee explained that they typically reduce the amount of the demanded ransom – a gesture of goodwill or, in the words of Kaptein and Von Helvoort (2019), a good intention (Q: 31).
In these situations, people acknowledge wrongdoing, but the good motives render the behaviour not deviant. For instance, Ferraro and Johnson (1983) studied relationships between abusive husbands and their wives. Results demonstrated that certain high causes, for example, religious commitments, justify the abuse.
Relativising the norm (Technique 6)
When offenders relativise a norm, they acknowledge that the norm was broken but mitigate the wrongfulness by comparing their actions with the actions of others. Essentially, individuals claim that their behaviour is not that bad (Kaptein and Von Helvoort, 2019).
Our findings suggest that reported ransomware offenders (Interviewees 3, 4, 5, 6, 8 and 9) use this neutralisation technique (Q: 8, 9, 16, 17, 18, 19, 21, 22, 26, 29, 31, 32). They claim, for example, that their aberrant actions are not as harmful as the actions of others (sub-technique 26: the relativisation by others). For instance, Interviewees 3, 4, 5, 6 and 9 shared that some ransomware gangs have no ethical considerations when they select their targets (Q: 8, 9, 16, 17, 18, 21, 26, 32): We have a negative attitude towards ransomware gangs that encrypt healthcare and educational institutions. (Interviewee 5) DarkSide was not completely without a moral compass. In a list of rules posted to the dashboard, the group said any attacks against educational, medical or government targets were forbidden. (
Fritsche (2002) refers to this technique as the
Interviewees 3, 4, 5, 6, 8 and 9 also claimed that the crimes they commit are not as serious as the crimes of others (sub-technique 28: the relativisation by seriousness). Attacking business sharks or capitalists appears to be ‘less or not bad at all’ (Kaptein and Von Helvoort, 2019: 1271) (Q: 8, 9, 16, 17, 18, 19, 21, 22, 26, 29, 31, 32). We are dealing with capitalists in the first place, which means they assess the risks, probable benefits, or losses from the deal. (Interviewee 5) Aleks states that he avoids targeting entities related to healthcare, labour unions and education. (Note: we were unable to verify such claims.) He criticised other ransomware offenders that do not share his ethical views, saying ‘Just because you are a criminal, does not mean you have to stop being a human being. If you are attacking hospitals during COVID-19, you are a [expletive]’. (Cisco Talos, Document 4)
Liddick (2013: 624) referred to this neutralisation technique as
Blaming the circumstances
The third category of neutralisation techniques,
Blaming the limited options (Technique 7)
When blaming the limited options, offenders reduce or remove alternative options and subsequently claim that their actions are necessary due to the lack of ‘real’ options. Kaptein and Von Helvoort (2019) elaborate that people believe that it is unrealistic for them to behave well, given the circumstances. Some of the interviewees claimed to be confronted with unrealistic options (sub-technique 34: the limitation to unrealistic options), leading them to rationalise their non-conformities. For instance, Interviewee 1 stated that money is of central importance to this world. Since not everyone can earn money legitimately, they are left with no other realistic option, but to conduct crime (Q: 2). Similarly, Interviewees 3, 6 and 7 argued that sufficient revenue could not be obtained from legitimate work (Q: 10, 25, 30): This [pentesting] could not bring a proper material reward. (Interviewee 3)
It [the earnings from ransomware activities] gave me confidence for the future, and also the ability to pay for a very expensive surgery required for my brother. (Interviewee 5)
In summary, interviewees excuse their criminal activities by believing in the absolute inevitability of conducting ransomware crime. Morris and Higgins (2009) found digital pirates excuse their behaviour on the basis that, if one cannot afford software for work or studies, it is acceptable to download it illegally. Minor (1981) referred to this technique as a
Blaming the limited role (Technique 8)
In addition to blaming the limited options, offenders argue that they had a limited role in the crime. Accepting that there were other options, they can claim to have less or no relationship to the deviant behaviour, thus diminishing their responsibility (Kaptein and Von Helvoort, 2019). Interviewee 5, for instance, shifted the responsibility for the attacks to the victims (sub-technique 39: the limitation to others being responsible): Companies do not want to spend money on protecting a corporate network and hiring highly paid specialists. (Interviewee 5)
Interviewee 6 shared a similar sentiment (Q: 28).
Similar to the previous point, Interviewee 8 explained that a ransom price negotiation is possible but only to a certain extent. The interviewee underlined that if the victim insists on further concessions, they will break the initial deal and demand full payment. The victims will have no one to blame but themselves in this case:
In studying youth anti-social behaviour, Barriga and Gibbs (1996) discovered that youth can deny their responsibility for anti-social behaviour by completely shifting responsibility to other parties. Bersoff (2001) found individuals tend to blame a company in order to reduce guilt. Similarly, our results suggest that ransomware offenders shift the responsibility for their wrongdoings to the victims.
Blaming the limited choice (Technique 9)
People can also blame the circumstances by claiming to have limited choices. Offenders do not deny their moral autonomy but emphasise that this is threatened by pressures and temptations that are difficult to resist. Therefore it is reasonable that ‘one succumbs to them’ (Kaptein and Von Helvoort, 2019: 1275). Interviewee 1, for instance, explained that such an opportunity to earn is too big to miss, especially in a country where professionals with comparable skills are not in demand (sub-technique 44: the limitation to overwhelming temptation): I am younger than you, but I have already earned for the rest of my life. Not millions, but enough to live in peace and never work. Here is a factor: how to quit a job that brings such earnings in a country where you are not much sought after? (Interviewee 1)
Kaptein and Von Helvoort (2019: 1276) elaborate that, in such instances, individuals refer to the existence of an irresistible opportunity, where one accepts that they have a choice to behave compliantly but choose not to; this choice is threatened by ‘extreme demands on their personal integrity’. Interviewee 1 used the fact that people with their skills are not sought after in their country to justify their choice to act maliciously. Research confirms that some criminals go as far as blaming something or someone for pushing them to commit the crime. For instance, Vasquez and Vieraitis (2016) reported that one of their study participants, a street tagger, explained that walls call their names and tell them to tag. Sexual predators frequently use this argument and accuse their victims of being seductive and provocative and therefore impossible for the perpetrators to resist (Scully and Marolla, 1984).
Hiding behind oneself
When using the final three neutralisation techniques, offenders reduce or completely deny responsibility by hiding behind themselves or simply their own limitations. They suggest that they are not perfect human beings and do not have full control over themselves. Maruna and Copes (2005) elaborated that guilt can be mitigated through the capability to attribute bad behaviour to another part of the self that has been separated from the real person. One can hide behind oneself by appealing to
Hiding behind imperfect capabilities (Technique 11)
Individuals can claim that they are fundamentally uncontrollable and, therefore, do not possess the capabilities to resist bad choices. Schönbach (1990) refers to this technique as
Kaptein and Von Helvoort (2019) stressed that people who hide behind imperfect capabilities believe that all or most human beings have insufficient and inadequate capabilities and therefore cannot be held accountable for their wrongdoing. Rhodes and Cusick (2002) reported that women excused themselves for having unprotected sex due to their incapacity to negotiate. People can also claim that while they possess the capabilities to behave well, they do not have the ability to self-restrain in some situations (Taylor, 1972).
Upon data analysis, we found another quote that fell under Technique 11: I am against romanticising my work. Money is being stolen or extorted with my hands. But I am not ashamed of what I do. I sincerely try to find at least something bad in this and cannot. Probably my concepts of what is good and what is bad are somehow shifted. But in this case, they are shifted for many in this profession. (Interviewee 1)
Interviewee 1 is incapable of appreciating the societal norm. They know the norm but they (say that they) don't comprehend it. It was not clear to us if this relates to the technique ‘Hiding behind imperfect capabilities’.
Hiding behind imperfect intentions (Technique 12)
Finally, people can hide behind the lack of good intentions to excuse their behaviour. In such instances, individuals admit being ill-affected or unwilling to behave compliantly. Offenders understand what good behaviour is, but they are unwilling to act accordingly (sub-technique 57: the hiding behind imperfect preferences). For instance, Interviewee 7 is unwilling to take a white hat job as this would be a waste of their life:
Marshal (2017) explained that, when using this technique, individuals follow their desires and emotions despite the consequences – ‘the heart wants what the heart wants’. Interviewee 7 unmistakeably puts high emphasis on their priority without considering the potential repercussions of ransomware attacks. Similarly, Interviewee 6 shared that their primary focus is on achieving a higher quality of life, which they would not be able to afford on a salary. Accordingly, it is acceptable to continue with their trade: We are not planning to introduce restrictions [i.e., limit ransomware activities]. We only live once. Restrictions are created for people who want to live on a salary. (Interviewee 6)
Interviewees 6 and 7 engage in crime because they simply want to. Kaptein and Von Helvoort (2019) argued that this is the most unsafe neutralisation technique because an individual acknowledges that they misbehave willingly, which makes it close to confession. Copes (2003) interviewed 40 tow car thieves and discovered that they commonly use this neutralisation technique.
Discussion
To our knowledge, this study is the first to explore neutralisation techniques used by alleged ransomware offenders. The findings should be considered with the following limitations. The first one is the use of secondary data, and that the interviewees are potentially not representative of the wider group of ransomware actors, or that they were not genuine in their answers. Additionally, there is limited information on the reliability of transcripts (i.e., two documents mentioned light edits for clarity, see Table 1). We cannot be completely sure that no further edits took place or that the translation to English was perfect (Supplemental File A). The second limitation is the small dataset size (
Implications for research and theory
Although the interviewees tended to use neutralisations, the results suggest that most of them still commit to the dominant normative system (e.g., laws, values, norms, etc.) and therefore care about their self-image. Research shows that offenders often struggle with a negative perception of their identity (Durkin and Bryant, 1999) and therefore manage their self-image through cognitive manipulations. Our results demonstrate that some interviewees admit that their activities are destructive and even insist they are ‘against romanticising their work’. However, they emphasise that these actions lead to positive outcomes, including driving the development of new technologies and educating companies about cyber security. Although admitting that they commit offences, some of the interviewees refer to themselves as ‘human beings’ who spare organisations such as hospitals, labour unions, educational establishments, etc. Such statements are potentially an attempt to influence public opinion about them or hackers more generally and change the negative perception of their identity. Rather than regarding themselves solely as ‘criminals’, some of the interviewees conceptualise themselves as ‘criminals with good intentions’.
In this research, we used Kaptein and Von Helvoort (2019) model due to its comprehensiveness and granularity. In our previous research, we found six techniques relevant to ransomware, indicating that reported offenders invent facts about victims; blame victims for being attacked; appeal to higher goals, their rights and self-interest; and diminish the effects of crimes by comparing them to the actions of others (Connolly et al., 2023). All these excuses fall under the category of
Next, our research suggests that ransomware offenders use at least nine neutralisation techniques to excuse their behaviour. We have not found any support for the three techniques in the model (i.e.,
The second technique,
Kaptein and Von Helvoort (2019) explained that people selectively deny relevant facts, consciously pretending that nothing harm was inflicted. Von Hippel and Trivers (2011) argued that individuals engage in this self-deception by rehearsing lies in their minds until they depict a different truth. While we are unsure if the interviewees selectively denied facts, we found some evidence that they invented new facts about ransomware crimes they claimed to commit (Technique 3). This suggests that perpetrators might reduce guilt by distorting the facts about those.
We also did not find any evidence to support Technique 10. This discovery corroborates the notion that reported ransomware offenders, especially those interviewed, are not feigning ignorance about the deviant nature of their behaviour. Instead, they are conscious of the deviance inherent in their conduct. However, due to limited data we cannot confirm with confidence this finding.
Another interesting discovery is that interviewees tend to deny the wickedness of their actions (i.e., there is no problem at all because there is no deviant behaviour) more commonly than the responsibility (i.e., there is deviant behaviour but one is not responsible for it) (Kaptein and Von Helvoort, 2019). We made this inference because
Conclusion
This article investigated neutralisation techniques used by studying individuals, who allegedly have taken part in ransomware criminal activities. Based on data from nine interviews, we found evidence of nine neutralisation techniques: denying wrongdoing through the invention of new facts or by negating societal norms. If the criminal behaviour could not be nullified, interviewees tended to deny responsibility by blaming the circumstances or their personal limitations.
The data used in this study makes this work unique and valuable for two reasons. Primary data on ransomware offenders is not easy to collect and secondary – not available in abundance in the public domain since these offenders are rarely arrested, tend to operate anonymously and rarely communicate about their activities. Furthermore, the data was collected from reported offenders who had not been apprehended. As such, the data is possibly more accurate and truthful than that collected from apprehended or convicted criminals whose accounts might be distorted by the prospect of a shorter prison sentence or more lenient treatment in prison (Pollock and Hashmall, 1991).
Supplemental Material
sj-docx-1-euc-10.1177_14773708251320464 - Supplemental material for Ransomware crime through the lens of neutralisation theory
Supplemental material, sj-docx-1-euc-10.1177_14773708251320464 for Ransomware crime through the lens of neutralisation theory by Lena Yuryna Connolly, Hervé Borrion and Budi Arief in European Journal of Criminology
Footnotes
Acknowledgements
The authors would like to express sincere gratitude to Zayed University for providing Research Incentive Fund (Grant No. R22014) to conduct this research.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research project is funded by the Research Incentive Fund (Grant No. R22014) provided by Zayed University.
Supplemental material
Supplemental material for this article is available online.
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
