Abstract
The relative glut of data on cybercriminal forums has led to a growing understanding of the functioning of these virtual marketplaces. But with a focus on illicit online trading, less attention has been paid to the structures of groups that carry out cybercrimes in an operational sense. In economic parlance, some such groups may be known as ‘firms’. This concept has been a significant part of the literature on more traditional forms of organised crime, but is not widely discussed in the cybercrime discourse. The focus of this article is, by way of a case study of the Gozi malware group, to explore the applicability of the concept of firms to the novel environment of cybercrime.
Introduction
The relative glut of data on cybercrime marketplaces has led to a growing understanding of how these forums function and their role within the illicit digital economy (see, for instance, Décary-Hétu and Dupont, 2013; Dupont et al., 2017; Dupont and Lusthaus, 2021; Holt, 2013; Holt and Lampke, 2010; Motoyama et al., 2011). While marketplaces are undoubtedly an important part of the cybercrime economy, less attention has been paid to the structures of groups that carry out cybercrimes in an operational sense (see Broadhurst et al., 2014; Leukfeldt et al., 2017c; Lusthaus, 2018b; Musotto and Wall, 2020; Wall, 2014). That is, those groups which are the source of the products and services that are brought to market. We might regard these as enterprises, businesses or companies. But in traditional economic terms, the concept of firms is standard and foundational (on theories of firms see Gibbons, 2005). In short, a firm is a profit-making entity supplying a service or good (Sullivan and Sheffrin, 2003).
The concept of firms has been a significant part of the literature on more traditional forms of organised crime (most notably Reuter, 1983; for a review see von Lampe, 2016: 127-157). But its application to cybercrime is less developed. Some comparative research has been done on cybercriminal business models (Broadhurst et al., 2014; Leukfeldt et al., 2016; Leukfeldt et al., 2017a; Lusthaus, 2018b), and the idea of cybercriminal networks has begun to gain greater prominence (see e.g. Leukfeldt et al., 2017b; Leukfeldt et al., 2017c). Yet, only a handful of scholars have directly touched on the concept of a firm or the oft-linked area of transaction cost economics (Herley and Florêncio, 2010; Lusthaus, 2018a; Paquet-Clouston et al., 2018; see also Hardy and Norgaard, 2016). The concept has not been probed in depth, and key questions remain to be answered. Do cybercriminal businesses match our conventional expectations of what a firm is? Do they differ from (non-digital) criminal firms? Does the concept of a firm help us understand the organisational structure of cybercriminal groups?
The focus of this article is, by way of a case study, to explore the applicability of the concept of firms to the novel environment of cybercrime. The first section of this article provides theoretical background on the concept of the firm. The second section addresses the data and methods employed in the study. The third section is the core case study of the Gozi group, one of the leading malware producers and distributors of its time. This section analyses the group's background, structure and operations. A discussion section then follows, linking this case study to broader themes of interest.
Theory
To explore whether the concept of firms is applicable to cybercrime, we must first outline theoretical background on the nature of both legal and criminal firms. This analysis draws on a range of social science contributions, across not only criminology, but also sociology and economics.
The nature of firms
While definitions, like the one in the introduction, see firms as profit-making entities, this does not tell us much about the nature of firms. The terms business, enterprise or even company might be equally applied. Such a broad approach would incorporate huge swathes of commercial activity, in line with the thinking that ‘firms can take many different forms, each with its own sociological profile: partnerships, family firms, joint-stock corporations, and so on’ (Swedberg, 2003: 74). Rather than getting caught in the quagmire of exhaustively listing every type of firm that might exist, a more useful analytical exercise is to engage with the question of why firms emerge instead of other possible structures. In short, what is it that firms offer to those inside them?
The most useful body of theory to assist with this task is known as transaction cost economics. In his archetypal paper, Coase famously posits that firms emerge due to costs associated with engaging with markets. These include: costs in purchasing the goods/services, bargaining costs, information costs and concerns regarding trade secrets and enforcement (Coase, 1937). In some cases, bringing certain partners within a firm structure may enhance overall production and economic gains. If the costs of using the market are too high, a firm would be employed.
In perhaps its most influential application, Williamson endorsed and expanded Coase's approach in later decades. He summarises the transaction costs of engaging with markets in two categories: (1) ‘ex ante costs of drafting, negotiating and safeguarding an agreement’; (2) ‘ex post costs of maladaptation and adjustment that arise when contract execution is misaligned as a result of gaps, errors, omissions, and unanticipated disturbances’ (Williamson, 1996: 379). For Williamson there are clear reasons why a firm (‘hierarchy’ in his terminology) or market will be used in a given case. When transactions are rare and/or straightforward, a market is more appropriate than a firm. Firms are more likely to be used when transactions are frequent, defined by uncertainty and/or asset specificity is high – for example, when a customised product or service might not be of value to other buyers (see Williamson, 1975).
There are some glosses that should be provided to the school of Coase and Williamson. First, it should not be assumed that when either a firm or market approach is chosen that such a choice is a perfect one. This would constitute what Granovetter (1985) regards as a functionalist fallacy: just because certain economic organisations exist does not mean they are inherently efficient. In fact, there are empirical examples of seemingly inefficient business choices and poor organisational decisions (see DiMaggio and Powell, 1991). Second, networks have now attained an important theoretical role in the literature, alongside markets and firms. While Coase does not address networks, Williamson adds a third “hybrid” form to account for long contractual relations (Williamson, 1996: 104-105). This alteration suggests that certain examples may fall between either markets or firms. This view is championed more pointedly in the work of others, such as Powell (1990), who posit that networks are of great significance.
The other complicating factor is defining the limits of firms. Firms do not exist in isolation, but interact with other firms and individuals (Davis and Powell, 1992; Swedberg, 2003: 99). Firms may partner in various ways, from a temporary basis up to when multiple firms are consolidated into a single legal entity. Between these two extremes, Granovetter (2005) suggests some firms may formally or informally connect themselves in a persistent way to form a ‘business group’. Whether defined as a business group, or a partnership more broadly, there are a range of relationships between firms, such as joint ventures and franchising.
Finally, the internal structure of firms should be delineated briefly. Weber provides the classical analysis of this topic. One of his main contributions is the idea that a firm's property is distinct from its individual members (Weber, [1923] 1981: 228). Beyond that, he establishes three main categories of those inside a firm: entrepreneurs, bureaucrats, and workers. The entrepreneur is “the leading spirit”, the bureaucrat is trained for a clearly defined responsibility, while the worker is dependent on the employment the firm provides (Weber, [1922] 1978: 1403). In more modern firms, this roughly appears to equate with the categories of leaders, middle management and then lower tier employees.
Criminal firms
Discussions of criminal firms have been largely in line with the broader social sciences literature on firms. In his review of illegal enterprises, (von Lampe, 2016: 127) suggests that criminal firms are ‘delineable organisational entities that are roughly similar in function to organisations in the legal economy, commonly referred to as businesses, business enterprises, enterprises, corporations, or firms’. He also carries over a similar tripartite division to Powell and others, in that he sees these firms sitting alongside both illegal markets and illegal networks (127).
Despite this broad similarity, analyses of criminal firms often allow for a much more informal conceptualisation. This is likely because criminal enterprises operate under the threat from law enforcement, and without the state apparatus regulating their dealings (Campana and Varese, 2013; Morselli et al., 2007; Reuter, 1983). An obvious point, which sometimes goes unstated, is that many criminal firms will not be legally registered, abide by corporate law, or pay tax (except in cases of front companies or legitimate businesses that ‘turn bad’). While legal companies are at least partly defined by possessing their own independent capital, this does not appear to be as great a concern for scholars of illicit firms, who focus on intangible assets like reputations for violence (see Gambetta, 1993; Reuter, 1983; and for a critique Sugden, 1995).
Criminal firms are also likely to be relatively small. Responding to the previously held view that criminal groups were large, shadowy and monolithic enterprises exerting considerable control over illicit markets, Reuter's pathbreaking empirical research suggests that gambling and loan-sharking in New York were instead principally carried out by small, competing and short-lived firms (Reuter, 1983). This was due to a number of factors: the need for secrecy, the risks associated with expansion, and the difficulties in monitoring employees (Reuter, 1983). In studying the so-called ‘Capone Gang’, Haller (1990: 218) argues that this group should not be viewed as one large, tight hierarchy, but rather as ‘a complex set of partnerships’. There were four ‘senior partners’ of Capone and his closest associates, which one might reasonably conceive of as a firm. But this central group affiliated with a network of other entrepreneurs who were engaged in a range of activities: ‘the coordination was exerted through a series of deals with relatively independent businessmen to operate separate, small-scale enterprises’ (222).
Many criminal firms appear to lie close to the boundary of the firm, and perhaps not that far from falling into a network or market structure. But where is this boundary drawn for those inside a group? Largely in line with Weber, scholars conceptualise illegal enterprises as having four layers: entrepreneurs, managers, permanent employees who often work on salary/commission, and temporary workers (see for instance Caulkins et al., 2009). Reuter (1985) argues that if an individual works exclusively for, and is largely controlled by, a leader of an illicit firm, then this person is an employee. But if they work for multiple firms and are paid based on results, then they are often an “independent supplier” (Reuter, 1983: 49). One related challenge of delineating the boundary of a criminal firm is that there is often a high degree of fluctuation of those who are involved within particular firms and the roles they play (Bright and Delaney, 2013; Kleemans and Van de Bunt, 1999).
Data and methods
When evaluating the applicability of the concept of firms to cybercrime, it is most sensible to carry out this analysis by way of case study. Successful case studies of conventional criminal groups have been carried out in the past (see, e.g. Hornsby and Hobbs, 2006; Levitt and Venkatesh, 2000). This approach provides a strong degree of specificity and detail. We have chosen to focus on a malware group, as their products are vital to the broader cybercrime economy and are a damage multiplier, by allowing far less skilled cybercriminals to operate successful enterprises. Our case study is of the criminal group behind the Gozi malware, which was initially detected at the turn of 2007 and operated in its original form until late 2010 (for background on Gozi see Krebs, 2013; USDOJ, 2013). There are a number of reasons for this choice. First, during its time of operation, the Gozi Trojan was one of the most significant pieces of malware available and was widely exploited across the world. Second, the case has largely passed through the justice system with several key players convicted. This reduced certain complexities around ethics and risk. Practically, it also meant that more information could be accessed, both from investigators and public sources, than in active cases.
Another key consideration is that we believed the Gozi case might be of analytical interest in understanding the nature and evolution of malware business models. As discussed below, the case appears to bridge between the early forms of financial malware, where all aspects of the enterprise were controlled internally, and the situation that is faced today, which is less centralised and more service based (see EC3, 2020; van Oss, 2011). Gozi presents an archetypal case that we might expect is typical of groups that followed, and one that also helps us understand the broader dynamics of the evolution of banking Trojans and the organisational structures behind them. The generalisability of this choice will be explored in further detail in the discussion section, when we compare the case of Gozi to other examples to determine external validity. 1
This paper makes use of a qualitative approach. It draws together data from a range of different sources, to paint a more complete picture of the Gozi group. The key data includes US indictments, complaints and other legal documents concerning the case that are publicly available. We gathered seven of these documents, which ranged from 2 to 26 pages. We were also given access to a confidential investigatory report that contained rich information on the group, including some of their communications. To gain more detailed information on certain points, we carried out interviews with individuals involved in investigating the group. This included both those from the public and private sectors, and in more than one country. In total there were five participants, identified only as P1-5 herein, to preserve their anonymity. Some were interviewed in person, others over the phone. Finally, in a time intensive process, we made use of law enforcement records to verify some important findings coming out of the above data sources. Due to security/sensitivity reasons, these records were not opened to us as a primary source that could be scoured at will. Rather one co-author was able to engage with law enforcement agents to check specific points of interest in this paper against records to ensure they were accurate.
This approach provides a strong degree of triangulation in order to enhance the validity of this research (on validity see, for instance, Hoyle et al., 2002). Triangulation involves combining multiple methods/data to reduce potential biases in the research design (Denzin, 1978; Patton, 2002: 555-563). Our approach draws on both the analysis of written sources, as well as conducting interviews. The written and interview data have been derived from multiple jurisdictions. The interview participants also come from different perspectives, in that they span law enforcement, related parts of the public sector, and the private sector. Additionally, they have different investigation expertise, ranging from the human, to the technical and the financial. Despite these efforts, the main challenge to validity is that the cybercriminal perspective is not directly represented. As such, the findings in this paper are likely to reflect the investigation perspective, and be missing certain details and richness that could only be garnered by direct contact with the offenders in this case. There are consistent questions around access and accuracy when interviewing cybercriminal offenders, but it is possible to do so (Hutchings and Holt, 2018; Lusthaus, 2018a, 2018b). Nonetheless, for the scope of this article, the decision was made to focus our limited resources on the investigation data, especially as it would have been very difficult to protect the identities of the small number of offenders centrally involved in Gozi.
Case study: The Gozi group
Gozi was a piece of banking malware known as a Trojan horse. Along with Zeus, other well-known examples have included Spyeye, Carberp and Emotet. Simply put, the goal of these Trojans is to capture user credentials for online bank accounts, allowing the cybercriminals to extract the funds from those accounts. Gozi used what's known as the ‘man-in-the-browser’ technique, which allows the offenders to collect data that has been entered into Internet browsers. 2 In order to get the malware onto the victim computers, the Gozi group had to exploit vulnerabilities in the browser or plugins (e.g. a PDF reader). Gozi was first detected at the turn of 2007 (Jackson, 2007), and originated in the first phase of banking malware.
In this first phase, several groups developed themselves into well run malware crews. Their success initially was based on keeping the malicious code proprietary and the infrastructure under their own control. Zeus, which also came to notice in 2007, was a good example of this (on Zeus see Hutchings and Clayton, 2017). Until the source code was leaked in May 2011, the Zeus malware was coded, developed and maintained by the same group (Goodin, 2011). There were a number of core functions within this business model, as made clear by van Oss (2011). While the developer provided the malware, another part of the group had to distribute it and infect machines. These machines became part of a ‘botnet’ and had to be managed by a ‘botherder’. Online banking credentials needed to be harvested from the botnet and stored in so-called ‘drop zones’. Once harvested, one or more group members were required to perform the fraudulent transactions that would transfer the money out of victim accounts. Last, was the ‘cashout’ process, where individuals had to extract the money from the accounts that received the stolen funds.
The second phase of the banking malware evolution would soon follow. It became far more common for developers to sell or rent their malware to other parties, rather than exclusively exploit it themselves. This is often referred to as ‘malware-as-a-service’ or, more broadly, ‘cybercrime-as-a-service’ (EC3, 2020; The PhishLabs Team, 2014). The Gozi group's contribution was in this second phase, when they developed a partnership model that would become commonly used by a range of other groups.
Gozi organisational structure
In order to run a malware development group, it remains essential that some kind of coder or programmer be centrally involved. But the case of Gozi suggests that the leader of the group may instead be an effective manager who has some technical interests and organises the efforts of others. It is not necessary for this person to be a leading coder in their own right. For Gozi, this entrepreneur was Nikita Kuzmin, known online as 76 (and sometimes as Ya), who coordinated the group's activities from Russia and was widely believed to be the ‘brain’ and the ‘ideas man’ (P5).
3
Although some investigators were hesitant to label him the ‘boss’, they nonetheless saw him as the central node within the organisational network and believed that it was Kuzmin's vision to create the most powerful banking Trojan in the world (P3; P4). In order to do that, he needed to bring in the right talent and expertise: a developer, a botnet manager (‘botherder’), an expert in injecting malicious code, spammers and money mules (P3; P4). One participant summarised matters like this: There were different skill sets for each person. 76 was a ‘project coordinator’. He oversaw everything as the business manager. Under him you had people doing different aspects of the business. You had server people, people writing and updating the code, people dealing with the injects. Then you had other people coming in and out of the group that would be contracted to spread the malware, different people writing spam templates, selling email lists, down to different cashout groups. There were different roles involved (P5).
Nonetheless, the core group was small. The majority of the coding of the Gozi Trojan was carried out by a person with the nickname Zufyx, who was based in Russia. There was also the chief lieutenant xxx, who was kept on salary and, according to interviews, paid between US $50,000-60,000 a year (P1; P2; P3; P4). The complete core group is represented in Figure 1, with the dotted lines indicating ‘freelance contractors’ (independent suppliers) who provided regular and important services from the outside. The central team was Russian-speaking, though may have been from more than one country (P5).
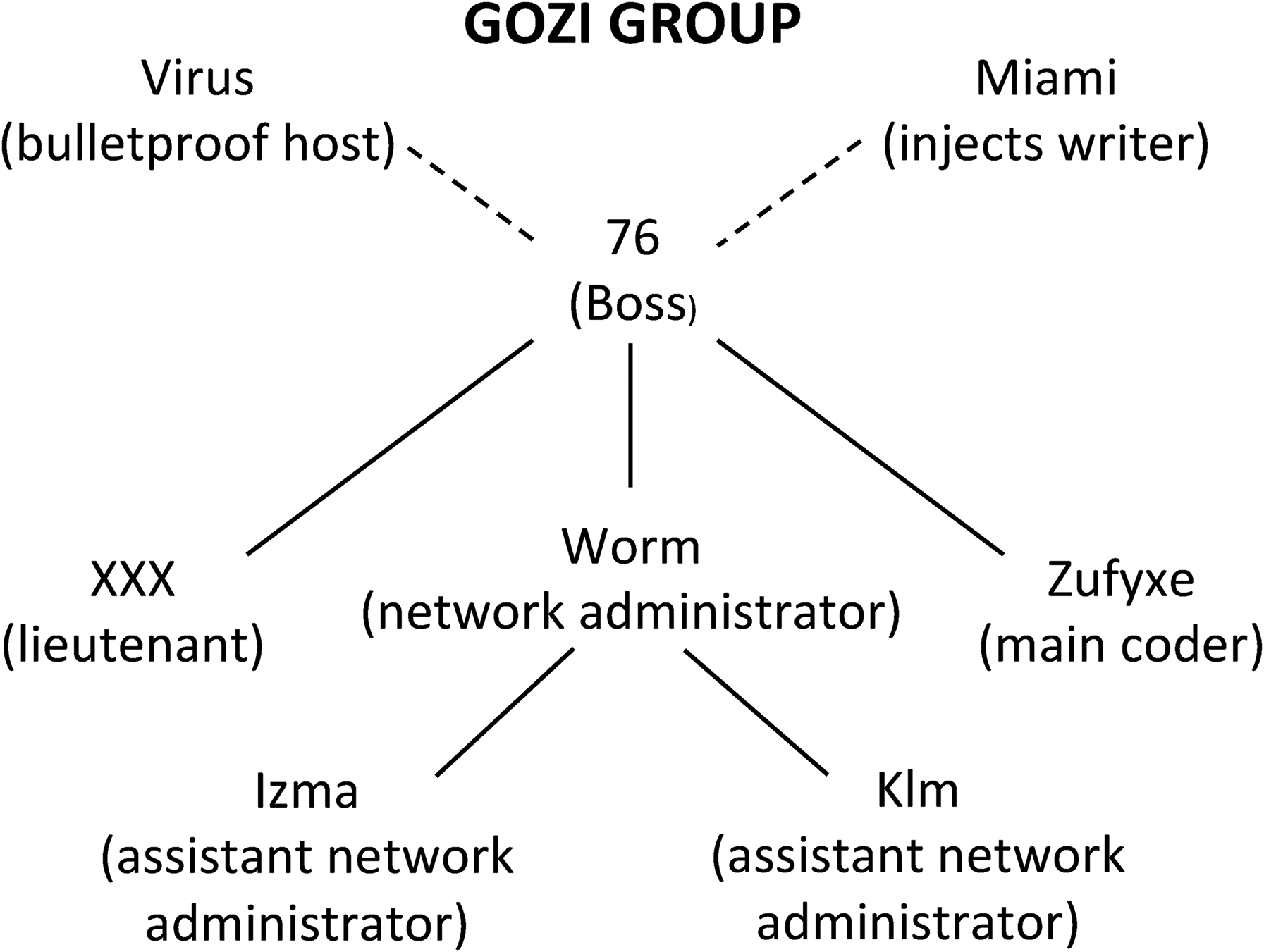
Structure of the Gozi group.
None of the data provided clear evidence of how the group met. Regardless of origin, it appeared that the group primarily communicated through the Jabber (XMPP) messaging service. Some interview participants believed that the Gozi group only sparingly made use of forums, even to promote their product, often preferring to engage with partners who were already known contacts. Compared to forums, Jabber can be a much more private (and encrypted) way for small groups to engage with each other and coordinate their business. Some suggested that Gozi acted almost like a ‘ghost group’ (P1; P2). As argued by Lusthaus and Varese (2021), the offline and local dimension of cybercrime also should not be ignored (see also Leukfeldt et al., 2017a; Lusthaus, 2018b). But in the Gozi case, there was limited data available on this point, other than that some of the members likely met in person (P1; P2), and that 76, aka Nikita Kuzmin, lived in Moscow and was socially active and known within his environment. 4
Connected to the core group, there were a number of others who played a role within the Gozi enterprise. But, as per Reuter's delineation, it is most accurate to view some of these functions as the work of independent suppliers. For instance, a Latvian known online as Miami was brought in as a specialist in ‘injections’ (P1; P2; P3; P4). This involves finding ways of exploiting software bugs so that the malware can be placed on victim computers. Miami appears to have been picked by 76 (P1; P2). It is likely that he was paid per inject, at least initially, rather than on salary as the core group members were. 5 Significantly, Miami didn't just work for Gozi as the core group did, but was also known to provide similar services to a number of competitor malware groups such as Zeus and Spyeye. 6 Virus, a Romanian national who provided bulletproof hosting services for Gozi, also served a number of different customers. 7
There was also the possibility of external organisational elements responsible for supporting and/or protecting the Gozi group. While one investigator had seen organised crime involvement in other similar cases (P5), based on what is known in the Gozi case, there was not strong evidence for the involvement of organised crime groups (P1; P2; P3; P4). Two participants believed that Kuzmin was previously linked to the infamous cybercriminal group, the Russian Business Network (P3; P4), which some argue had connections to the Russian mafia (see Graham, 2009: 173; Krebs, 2014: 22–23). This is a somewhat tenuous connection.
In terms of local protection, a more fruitful line of inquiry might relate to the political system instead. Gozi employed a similar tactic to some other Eastern European groups: they did not target ‘home’ victims within their own country or region, in order to avoid potential threats of prosecution (P1; P2). But beyond this, some interview subjects suggested that the group may have enjoyed some form of political protection through nepotism or corruption. One investigator noted that ‘corruption is rampant over there. I don't think that's a secret’ (P5). Kuzmin is not a hardened criminal, but rather comes from an ostensibly well-off family. It is noteworthy that he is the son of a famous Russian singer called Vladimir Kuzmin. Two participants hypothesised that this status within Russian society, and his father's influential connections, may have helped the younger Kuzmin avoid arrest within his home country (P1; P2). Although their investigation did not lead them into hard evidence that Kuzmin and the Gozi group were directly connected to elements of the Russian government, these participants argued that some level of protection remains a possibility (on corruption and cybercrime more broadly see Lusthaus, 2018b: ch 7). 8
The partnership model
If the sole function of the Gozi group were malware production, the structure of the enterprise would be relatively simple. The core group would sell their product to various customers and those cybercriminals would make use of it themselves to steal banking credentials and then extract funds from the victim accounts. In reality, the business model was more complicated, and changed over time. In the early days of Gozi, 76 employed a service model, where he sold credit card data and bank account access through his platform. But this created concerns that it exposed him to prosecution.
76 later developed a different model that removed him from the coalface of criminality, and saw him act more as a coordinator, rather than the lead actor (P1; P2). The malware group held the source code and infrastructure, but provided access to their botnet for others to harvest credentials and carry out the banking frauds (P5). Key to this approach was bringing on partners who were respectively responsible for driving traffic (for infections) and cashing out. Unlike Miami's injection involvement, which looked more like a freelance relationship, these partners operated in a coordinated way with the central team as part of sustained campaigns. The software, traffic and cashout elements of the business were all ‘interdependent’ (P2). Each of these teams received roughly a third of the overall profits from each effort. Often these teams were responsible for particular geographical regions. Figure 2 outlines the broader structure of the Gozi network.
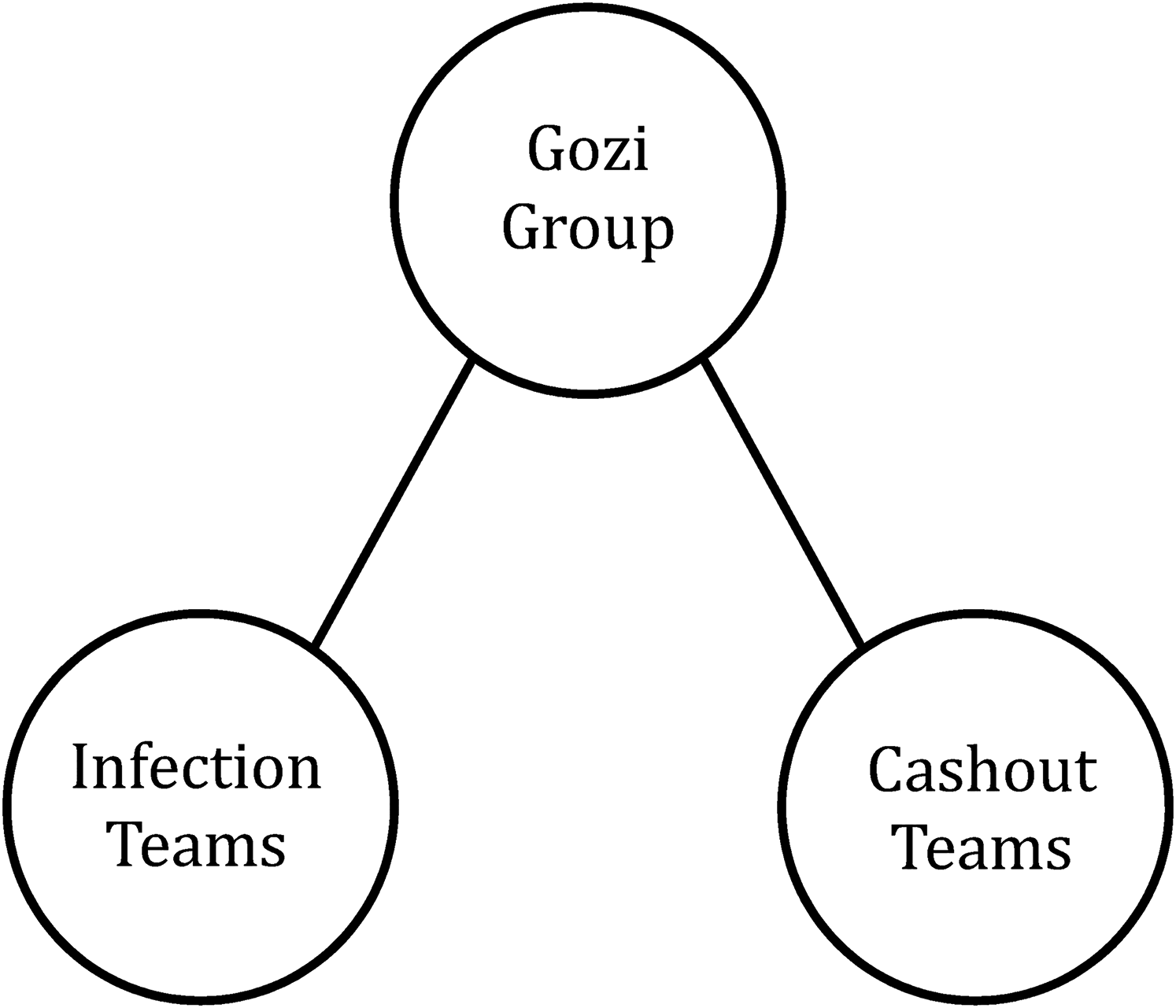
Gozi partnership structure.
This approach seemed to be a departure from both the original model of using malware only within the group, and the simple model of selling/renting the malware to others. As one participant put it: ‘Normally you buy Zeus and you use it, and you run your business alone.’ But the Gozi case was different because 76 was maintaining greater control over those teams exploiting the malware (P1). This made the group somewhat unusual when compared to other contemporaneous operations. It was essentially a core group that connected with partners who performed other functions for them. The core group neither carried out all the functions, nor did it wash its hands of many of them by purely selling/renting the product. It is also not accurate to view this structure as an outsourcing model because 76 didn't simply pay a fee to specialists to provide their services. It appears more apt to suggest that this was akin to a partnership model of one kind or another, where the Gozi group brought on new associates in a range of jurisdictions and provided them with a cut of the profits, in return for their involvement. While allowing 76 to step back from heavy operational involvement, this model also appears to have allowed him to maintain a level of control (P3; P4).
The Gozi firm
In applying the concept of the firm to Gozi, the core structure that produced the malware is well suited to this label in a number of respects. The team had a defined hierarchy and operated together for some time with a clear profit motivation. The entrepreneur and project manager, 76, oversaw the finances with earnings estimated to be about US$700,000 per year. 76 ensured that his team members were regularly paid. 9 There was value in internalising the different specialisations into the firm, rather than relying only on market relationships. There was a high degree of asset specificity, as the core roles were highly specialised and tailored to the Gozi malware. The transactions between these individuals were very regular, and would otherwise have been characterised by a high degree of uncertainty on the cybercriminal market. Nonetheless, there were limits to the firm. For instance, some functions were provided by freelance contractors like Miami, who also worked for other competitor groups. 10
This Gozi firm was very business-like and professional in how it operated. To provide but one example, two investigators described how, before the start of a campaign, the group tested the functionality of a bank account they controlled. They would log into the account multiple times and then make small legitimate payments of about US $50 to recipients like charities. After that, they might begin to make larger payments, perhaps even beyond the level of funds in the account, and thereby would receive an error message. They would never do anything illicit with this account. In short, they were gaining an idea of how the bank account functioned, so they could fit the malware to it, as the illicit transfers that would follow as part of the scam would be automated by the malware rather than being carried out by a human. They even kept control of this account once the campaign had begun against victims, and used it to troubleshoot any problems that emerged (P3; P4).
We must also apply the firm concept to the broader structure of the Gozi network, which is perhaps a poorer fit. The transfer and cashout teams that the core group engaged with in each jurisdiction were not members of the central hierarchy. In reality, they were more like partners than firm members, not dissimilar to Haller's analysis of the Capone group. Law enforcement sources suggest that some cashout partners may even have worked with other malware operations, as well. While one might argue over whether this partnership arrangement technically should be classified as a business group, franchise or other structure, it is essentially a compromise between insourcing and outsourcing. Rather than contracting with transient external partners, it involves bringing longer-term affiliates into the brand and broadly within the firm's umbrella. The advantages of such an approach are that it transfers many of the costs and risks to the affiliates, while allowing the core firm to retain a degree of control. It allows the firm an expanded pool of profits beyond what the core group could achieve on its own, combined with a more sheltered role within the criminal activity.
New Gozi firms?
The leader of the original Gozi crew was arrested in 2010 while travelling through San Francisco. 11 But that is not the end of the Gozi story. As if emphasising the distinction between the technical and human components of cybercrime, the Gozi malware itself continues to play a role. In short, new players have taken over the business. It is not yet clear exactly who's behind these operations, but it appears that components of the Gozi source code continued to be used past 76's time in control. This might have been the result of leaks or sales of the code (Brumaghin and Unterbrink, 2018). It would be valuable for further research to track exactly how the Gozi code was appropriated over the years and found its way into different operations. This is a similar process with what followed the release of the Zeus source code, with the developments of new variants emerging over time (see for instance EC3, 2014).
Analysis of the current status of the Gozi malware is more speculative as the cases are open so it is more difficult to gather reliable data, beyond public reports. While researchers have used a range of different names to describe the malware (e.g. Rovnix, ISFB, Papras and Ursnif), it also appears credible that the Gozi malware did not continue on just one track after the demise of the original firm, but was possibly adopted by more than one group (Exploits Team, 2014). One clear suggestion of this, is the Goznym Trojan, which appears to have been created as a hybrid between Gozi and another piece of malware called Nymaim (Brewster, 2016). Some of the crew behind that operation were recently arrested in a widely publicised operation (Greenberg, 2019).
Discussion and conclusion
The case study of the Gozi group exhibits core elements that one would associate with firms. In broad terms, it is a group of multiple individuals who operate for profit over a number of years. This firm structure increases efficiency and profits by internalising core components of the malware business. Following Williamson, this matches theoretical expectations in that the transactions within the Gozi group were very frequent, otherwise characterised by uncertainty if sought through a criminal market, and defined by high asset specificity, in that the malware is highly sophisticated and peculiar, requiring significant expert and tailored functions from members of the group.
But if one takes a more restrictive definitional approach, the firm in this example shares much more in common with the looser conception of criminal firms, than it does with more rigid conceptions that often apply to legal enterprises. We did not find evidence that the Gozi group was legally incorporated, or that it possessed its own independent capital. Leaving aside freelancers and partners, the core Gozi firm was likely made up of perhaps only six individuals, ranging from an entrepreneur down to employees. It only survived for a few years. As such, this example supports the views of those like Reuter who see criminal firms as being primarily small and short-lived. The larger criminal network, which may have included many tens of individuals from across the globe, more accurately reflects a partnership model or business group, than one single hierarchical organisation. In short, there was likely a range of other small distinct firms, along with individuals, who engaged with the Gozi enterprise interdependently.
One might expect cybercrime to offer innovative and new organisational structures. But facing familiar challenges around secrecy, monitoring and expansion – perhaps exacerbated by a digital setting – the firm structure in this case was largely in keeping with the structure of conventional criminal groups. As one participant put it: ‘People continue to look at cybercrime as this highly technical wizzbang thing – oh it's on a computer and I can't understand it and try to ignore it… But when you strip away the technical aspects of it, it's really just business. It's no different running a malware group than somebody running a numbers scheme. It's just one's technical and one isn't… it's just an avenue for making money’ (P5).
This view is supported by other analyses that suggest that cybercrime shares much in common with traditional business, and is even ‘boring’ in some respects (Lusthaus, 2018b: ch 3; Collier et al., 2021).
Of course, there are limitations involved with our findings, most notably that the paper contains a sole case study. The reasons for this choice were strong. We believed that the type of richness and nuance provided by such an unusually deep investigation would make an important contribution to the literature. But gathering such detailed, non-public, confidential, and triangulated data around this one case was extremely time-consuming, taking a number of years. Additional cases, with the same level of detail, were not feasible to include.
But this does raise the question of external validity. As we cannot address this through the case study itself, we briefly survey some broader elements within our data, the existing literature and public source information. Some of our main findings can be supported in this way. For instance, a major comparative study suggests that malware groups are usually quite small, with a rough maximum of eight core members (Lusthaus, 2018b: 56). Additionally, there is support for the idea that groups like Gozi can dissolve after a relatively short period, or realign their composition and business models. One of the indicators of the churn and fragility of this business is that enterprises are often termed as ‘projects’ (P5).
We can also use public information that is available to generalise our findings to more recent malware groups. In these cases, the basic firm structure and operations, along with the nature of their freelance relationships and partnerships appear to be similar to Gozi. 12 These examples also support the argument that there has been an evolution of the malware business model from something kept completely ‘in house’, to newer approaches which are far more service based, first in the form of rent-out schemes and eventually as partnership or affiliate models. This can be seen with significant malware operations like Bredolab and Emotet. Bredolab came to prominence in 2009, towards the end of Gozi's period of operation. While it was also a Trojan like Gozi, it was used as a platform for a wider set of purposes: to deliver spam, fake anti-virus or other pieces of malware, including banking Trojans. As such, the Bredolab botnet was rented out to affiliates, who in turn used the botnet to generate malicious traffic, pay-per-click installs or deploy malware (on Bredolab see Graaf et al., 2013; Kirk, 2010; Sancho, 2009). Emotet shows the continued expansion of this service-based approach. The malware first appeared in 2014 as a banking Trojan that spread by phishing emails, but over time it matured into a malware-as-a-service firm that acted as a door opener for a range of other malware groups such as Ryuk, a ransomware group, or Trickbot, a data-stealing Trojan enterprise. It appears that the group behind Emotet started to sell access to its infrastructure around 2017. It has been a top threat globally (on Emotet see Johnson, 2021; SophosLabs Research Team, 2019).
While it is plausible that a number of our findings may apply to malware groups more broadly, it is possible that other types of cybercriminal groupings take different forms, and further research on these variations is required. As part of this, certain complexities may emerge. For instance, there are some known counter-examples where cybercriminal firms appear to be much larger and more structured than the Gozi group, even operating out of physical office spaces, being legally incorporated and/or having independent capital. These include examples like the Russian Business Network and Liberty Reserve (Graham, 2009; Halpern, 2015). These cases involve activity that looks legitimate, such as acting as an Internet Service Provider or a virtual currency company, but where the customer base is largely criminal. Such shades of legitimacy may play a role in how corporatized these groups become and how closely they begin to resemble legitimate firms. One could develop a hypothesis for further testing: the more obviously illegal an activity is, and the harder it is to hide or shield, the more likely that a cybercriminal firm will be smaller and shorter-lived.
The second main limitation of this article moves in the opposite direction of the first: we were unable to obtain a complete picture of the Gozi group due to data constraints. This relates to the secretive nature of both the group and investigations into it. There are likely investigation documents that exist, but are not publicly available and which were not made available to us. There are also limits to any police investigation, both in terms of the evidence that can be gathered, but also that information gathered for the purpose of prosecution does not always match scholarly needs. Additionally, not having access to the cybercriminal perspective means that more detail on the inner workings of the group cannot be included. As a result, there are a number of facets that remain murky, including accounting for all those involved in the criminal network and the full scope of any offline dimension, along with whether the firm had its own independent capital.
In sum, what does the application of the concept of the firm to cybercrime, and the Gozi case in particular, teach us? First, and most importantly, the concept appears to have strong relevance, despite any novel aspects of cybercrime. While academic work has made detailed contributions on the ‘Dark Web’ and the general trade of illicit goods and services online, and law enforcement policy circles have also adopted a market-focussed approach characterised by a crime-as-a-service model (see, for instance, EC3, 2018), it is also important to clearly situate the individuals and groups that produce or exploit the products and services that are traded. But rather than reinventing the wheel, conceptualising cybercrime should draw on existing theory. This tells us that not only are markets important, but so too are networks and firms.
Second, the firm demarcation can provide added clarity when discussing cybercriminal groups and organisations. It helps us understand those tighter hierarchies, when contrasted to looser networks and markets. Some groups will not meet the definition of a firm, and are networks instead. Some cybercrime will involve individuals, who also are not part of firms. Cybercriminal enterprises may involve constellations of different firms and individuals working together, but not within one tight hierarchical structure. In short, the firm is a very useful concept to understand groups, their boundaries, and how they interact with other structural aspects of this criminal industry.
Finally, this analysis is valuable because in order to develop appropriate responses to cybercrime, we need a more complete understanding of what the underground looks like, incorporating all its component parts. We also need to better understand how these concepts interrelate. For instance, it is likely that some firms operate within certain marketplaces, and these are not mutually exclusive concepts. By comprehending how cybercriminal markets, networks and firms interrelate and cause harm, one can develop more focussed ideas around limiting this damage, where best to target interventions, and, ultimately, how to disrupt these structures.
Footnotes
Acknowledgements
We are very grateful to our interview participants, who were very generous with their time and expertise. This article could not have been written without their input. We thank the editors and the anonymous reviewers, who provided extremely clear and constructive critiques, which greatly strengthened this work. Federico Varese also provided very valuable comments and advice on this paper.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship and/or publication of this article.
