Abstract
Can social media revert the top-down dynamics of securitization? Limited by the notion that ‘security is only articulated in an institutional voice by the elites’, the role of non-elite actors has remained understudied. Only recently has it been proposed that lay actors can become influential security agents through their online activity. However, social media’s capacity to revert the top-down dynamics of securitization remains contended. To explore this puzzle and seeking to update the theory of securitization to the modern context of political communication, this study employs a semi-supervised machine learning approach to analyse a novel dataset of over 10 million Twitter messages by five elite and non-elite actor groups discussing the Amazon rainforest fires in 2019. Finally, the study uses vector autoregression (VAR) models to explore who leads and who echoes the securitization process. The results show that both elite
Introduction
One of the fundamental ways in which political communication is important is that it can affect the ways in which threats are interpreted. This process is captured and explained by the concept of ‘securitization’, which was coined by the Copenhagen School of Barry Buzan, Ole Wæver, and Jaap de Wilde (1998). Rather than treating security as a given object, securitization theory understands security as a linguistic practice through which an issue becomes a matter of insecurity (Aradau et al., 2014). Thus, securitization does not seek to solve security problems but to understand ‘what people do’ to bring security into existence (Aradau et al., 2014). Most prominently, the concept of securitization has been used to point to the discursive construction of particular issues as security threats (McDonald, 2008), producing an impressive body of highly cited literature (see Buzan et al., 1998; Buzan and Wæver, 2003; Wæver, 1995; Wæver et al., 1993) by an increasing number of scholars who shifted their focus from materialistic–realist threats to discursive security practices. Yet, despite its popularity, studies of securitization have been limited to spheres where communication typically develops from the top-down, such as speeches by political elites, state institutions or the media, overlooking the role of non-elite actors in the formative process of (in)security (Downing and Dron, 2020a; Ingraham and Reeves, 2016).
While the contribution of the concept of securitization to our understanding of security and its construction is not up for question, this study argues that the framework has been problematically narrowed by the notion that ‘security is only articulated in an institutional voice by the elites’ (Wæver, 1995: 57). This manifests in the following two ways: (1) It hinders the concept from adapting to alternative settings of political communication and (2) it conveys securitization solely as a top-down process. Addressing these limitations, this study proposes to update the existing theory to the modern context and dynamics of political communication marked by the advent of social media. Interpersonal conversations about public issues have always been an important part of the public sphere (Habermas, 1962; Katz and Lazarsfeld, 1955). In other words, I propose that non-elite actors, as well as the traditional elites, can behave as securitizing agents both online and offline. However, with the advent of social media, the role of non-elite actors is increasingly important and empirically attainable for analysis. Compared with mainstream media and other forms of traditional political communication (e.g. presidential speeches), social media accommodate a wider range of actors and are more accessible in terms of making effective claims about threats (Makhortykh, 2018). To substantiate this framework, my analysis takes the 45th G7 summit as a case study and focuses on one salient issue: The Amazon rainforest fires. The salient nature of this event, which has led to high levels of online engagement and intense discussions on Twitter in recent years, provides three advantages to address the question at hand: first, multiple stimuli received from different sources during a small time window facilitate the speed of information flows online (Centola, 2010; Gonzalez-Bailón et al., 2011), which aids the identification of securitization processes. Second, compared to other events like the North Atlantic Treaty Organization (NATO) summit, the G7 is not strictly related to security issues, which avoids selecting on the dependent variable. Finally, from a theoretical perspective, securitization has been criticized due to its Westernized framework (Wilkinson, 2007). Focusing on the G7 summit, therefore, aims to address these limitations by collectively examining securitization in Western and non-Western settings.
The goals of this study are threefold: (1) To update the theory of securitization to the modern context of political communication marked by the advent of social media, (2) to analyse the role of elite and non-elite actors in the process of securitization relating to the Amazon rainforest fires and (3) to address previous methodological shortcomings by pursuing a novel text-as-data approach. First, the study collects all tweets shared between February 2019 and September 2019 – the 7 months leading up to and including the 45th G7 summit – by five actor groups of manually identified users: politicians and governmental institutions, advocates, politicians’ Twitter friends, the media and citizens on Twitter. The study then offers a methodological contribution by developing a securitization–desecuritization dictionary, which is employ together with a semi-supervised semantic scaling model (Watanabe, 2021) to position each tweet on a unidimensional scale and identify securitizing moves. Finally, the study uses vector autoregression models (Sims, 1980) to explore whose expressed perceptions of insecurity more strongly predict the relationship between citizens and politicians (Barberá et al., 2019; Gilardi et al., 2021).
The study proceeds in five sections. First, it begins by scrutinizing the Copenhagen School’s framework to highlight the opportunities presented by the advent of social media to re-engage with modern readings of securitization. Then the research design is outlined, describing the extensive dataset developed and employed in the analysis, and explaining the contribution of the methodology employed in this study. The fifth section presents the findings, which suggest that, rather than describing a linear top–down process, securitization develops as a responsive activity, where elite
Theory and hypotheses
The Copenhagen School and beyond
The claim that security is a ‘speech act’ was famously proposed by the Copenhagen School of Barry Buzan, Ole Wæver, and Jaap de Wilde (1998). Based on the use of security language, the speech act possesses a performative capacity that allows it to enact an issue as a security problem and creates the reality in which that problem will be dealt with (Austin, 1975; Stritzel, 2014; Wæver, 1995). Thus, ‘because it is in this practice that the issue becomes a security issue’ (Buzan et al., 1998: 24), and not necessarily by the presence of a ‘real’ existential threat, securitization is conceived as a self-referential practice, which is successfully achieved through a three-stage process (see Figure 1). First, a securitizing agent pronounces a (single) ‘speech act’ that describes an issue as an existential threat (Buzan et al., 1998). Then, the audience accepts the security discourse and allows the application of extraordinary measures to protect the referent object (Buzan et al., 1998; Wæver, 1989: 42). Thus, it is through a single utterance that presents an issue as an existential threat to a referent object, and which has the effect of breaking the established bounding rules to justify the use of extraordinary measures, that an issue becomes securitized (Buzan et al., 1998).
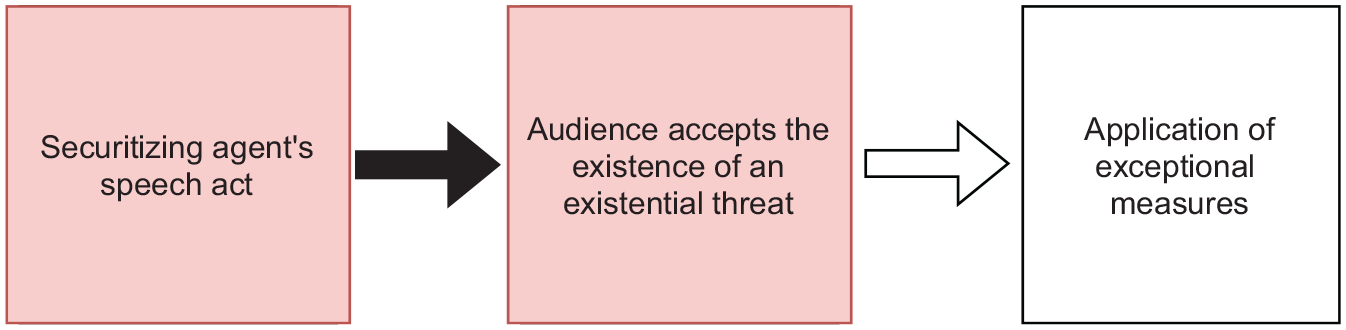
The Copenhagen School’s framework of successful securitization.
There is one additional element to the Copenhagen School’s conceptualization of securitization: the authority position of the speaker. In an attempt to strengthen their speech act approach, the Copenhagen School argues that ‘security is articulated only from a specific place, in an institutional voice, by elites’ (Wæver, 1995: 57). This explicit focus on particular security agents is justified by Wæver and his colleagues on the basis of the (empirical) assumption that security is ‘very much a structured field in which some actors are placed in positions of power by virtue of being generally accepted voices of security, by having the power to define security’ (Buzan et al., 1998: 31). Thus, this leads to the expectation that
Unfortunately, while strengthening the speech act approach, this claim has also resulted in a fixed conceptualization that disregards the everyday practices by non-elite actors who actively engage in the production of securitization. Indeed, given that the authority position refers to the subjective position of the speaker in relation to the audience, a wide range of agents could behave as securitizing actors. Securitization, therefore, like politicization, could be enacted in a forum other than the state. However, by attributing the performative power to a single actor and a one-time utterance (Butler, 1997; Wullweber, 2013; Wodak, 2001), the concept of the speech act undermines the intersubjective element of security and stands in opposition with the Copenhagen School’s own description of securitization as ‘the process of constructing a shared understanding of what is to be considered and collectively responded to as a threat’ (Buzan et al., 1998: 26; Léonard and Kaunert, 2010). Even more, this top–down approach necessarily hinders the applicability of the Copenhagen School’s framework, in so far it could not possibly take account of the wide range of actors who collectively bring security into existence. In the words of Wullweber (2013),
the process of securitization is under-theorized, especially since the majority of analysis still focus on the politics of the state or elite groups without sufficient taking into consideration the struggles within civil society at large. (p. 20)
This study addresses these limitations by seeking to update the existing theory to the current context of political communication marked by the advent of social media. Contemplating social media’s ‘democratic’ nature, the analysis aligns with the modern readings of securitization that account for the everyday (in)security enactments produced by elite
Social media: a new sphere of securitization
Social network platforms, such as Twitter and Facebook, have become a central part of the political communication space (Nielsen and Schroder, 2014). Although all media are somewhat ‘social’ and interactive in nature (Hogan and Quan-Haase, 2010), social media platforms offer the opportunity to a large number of geographically distant users to gather around a message (Rasmussen and Ihlen, 2015). In fact, as a result of the ready-made tools put at our disposal by these platforms, social media has empowered users to ‘share and distribute information, create viral events, enrich content through metadata [. . .] collaborate to produce knowledge, and build on others’ work’ (Nahon, 2015: 41). The micro-blogging site Twitter, for example, has become one of the main communication channels in daily politics (Barberá, 2015). Once considered a source of ‘pointless babble’ and a website to share personal status updates, Twitter has increasingly become an instrument in times of disaster, for event-following, and revolutions and uprisings (Barberá, 2015; Rogers, 2018).
Regarding securitization, social media fosters more inclusive understandings of the formative process of (meanings of) security. Compared with mainstream media and other forms of traditional political communication (e.g. presidential speeches), social media accommodate a wider range of actors and are more accessible in terms of making effective claims about threats (Makhortykh, 2018), diminishing the gatekeeping power of more traditional agents (Gilardi et al., 2021). Indeed, previous research has suggested that due to social media’s network structure, formed by a patchwork of ‘personal publics’ (i.e. what Facebook calls ‘friends’ and Twitter calls ‘followers’), social media users have the potential of generating a reverse flow of information (Sayre et al., 2010) from the bottom-up. As a result, considering social media as a new sphere of securitization provokes a shift away from the traditional and state-centred securitization models towards a more decentralized approach. A testable hypothesis that derives from this argument is as follows:
Alternative elite actors
Although more strongly related to the political communication literature than to the concept of securitization, a large body of literature has argued in favour of the salient role of the mass media as an agenda-setter and/or its central position as the triggering mechanism by which novel threats are constructed and communicated to the public (Rogers Neuman et al., 2014; Soroka, 2002; Wagner et al., 2002; Walgrave et al., 2008; Walgrave and Van Aelst, 2006; Wouters and Walgrave, 2017). Cohen (1963) clearly expresses this argument by stating that the press ‘may not be successful much of the time in telling people what to think, but it is stunningly successful in telling its readers what to think about’ (p. 13). The media highlight problems for politicians to solve, and they increase the salience of issues that the public might consider relevant (Barberá et al., 2019; Rogers et al. 1993; Wouters and Walgrave, 2017), with clear evidence showing that the media are very likely to lead public opinion (Boydstun, 2013; Iyengar and Kinder, 2010; McCombs and Shaw, 1972; Zaller, 1992). What is more, with the advent of platforms like Twitter, the number of people who report getting their news through social media is growing (Gottfried and Shearer, 2016) attributing social media an engendering role for the agenda-setting effect of the press through the increased incidental exposure to political information among those who might otherwise choose to avoid it (Feezell, 2018: 482). Hence, building on this literature, we should expect that:
Like the media, there is little question of the salient role interest and advocacy groups play in the crafting of political debates (Terkildsen et al., 1998). As agenda-setters, interest groups are highly contingent on their ability to expand or contain an issue and its related policy discourse (Cobb and Elder, 1983; Gamson and Lasch, 1983; Schattschneider, 1960; Turner and Killian, 1957), thus, in many cases contributing to the construction of novel threats. Since the rise of social media, advocates and interest groups have turned to these platforms to mobilize public opinion at a global scale, giving way to powerful social movements such as the School Strike for Climate, Me Too and Black Lives Matter (Chalmers and Shotton, 2016). However, while the extent to which social media contributes to the agenda-setting power of these agents remains unclear and cyber-sceptics and cyber-enthusiasts remain divided by the idea of ‘Advocacy 2.0’, there is little question that social media is now commonplace in many advocacy activities (Chalmers and Shotton, 2016: 375). Thus, this other body of research leads to the expectation that:
Endogenous securitization
Platforms like Twitter have shifted the paradigm from a broadcasting model (one-to-many) to a peer-to-peer (many-to-many) distribution system (Varol et al., 2014). A similar dynamic is described by the sociological approach to securitization, which defines it as a relational process among a myriad of actors (Balzacq, 2011; Roe, 2012; Salter, 2008; Stritzel, 2014; Williams, 2010). From the perspective thus defined, securitization emerges from processes of reciprocal and continued communication, where the separation between speaker(s) and audience(s) is blurred (Balzacq, 2008, 2010, 2015; Huysmans, 2011; Stritzel, 2011, 2014; Wullweber, 2013). Thus, rethinking securitization in the social media age not only requires that we reconsider ‘who can speak security’ (Vultee, 2010) but also the form of the communication dynamics at play.
Different to other social media platforms like Facebook, Twitter allows users to ‘follow’ others without a compulsory reciprocal response. This provides for a structure that disperses conversation rather than constraining it within bounded spaces or groups (Boyd et al., 2010; Bruns et al., 2015). Thus, it allows for different kinds of users to interact directly with one another, engaging in a responsive activity within the same symbolic framework, and embedded in a common social network (Barberá, 2015; Barberá et al., 2015; Papacharissi, 2022). This type of communication dynamic can be described as endogenous, given that users can simultaneously act as ‘speakers’ and ‘audiences’ by synchronously engaging in large-scale, reciprocal, dynamic, and multi-directional conversations with other members of the online space. Hence, accounting for the nature of this new medium and for the modern readings of securitization, rather than describing securitization as a linear and unidirectional process with a single speaker and a passive audience, we can expect that:
Data and methods
I collect tweets sent by five actor groups that have been identified as possible securitizing agents: politicians and governmental institutions, advocates, politicians’ Twitter friends, the media, and citizens on Twitter. Groups are formed by users, individually identified through manual coding. To collect their timelines, the rtweet package (Kearney, 2016) and the Twitter REST Application Programming Interface (API) 1 were employed. The study focuses on the seven G7 countries and collects tweets sent in the time period from February 2019, when the first Sherpa (emissary) meeting took place, to September 2019, when the 45th G7 summit was concluded.
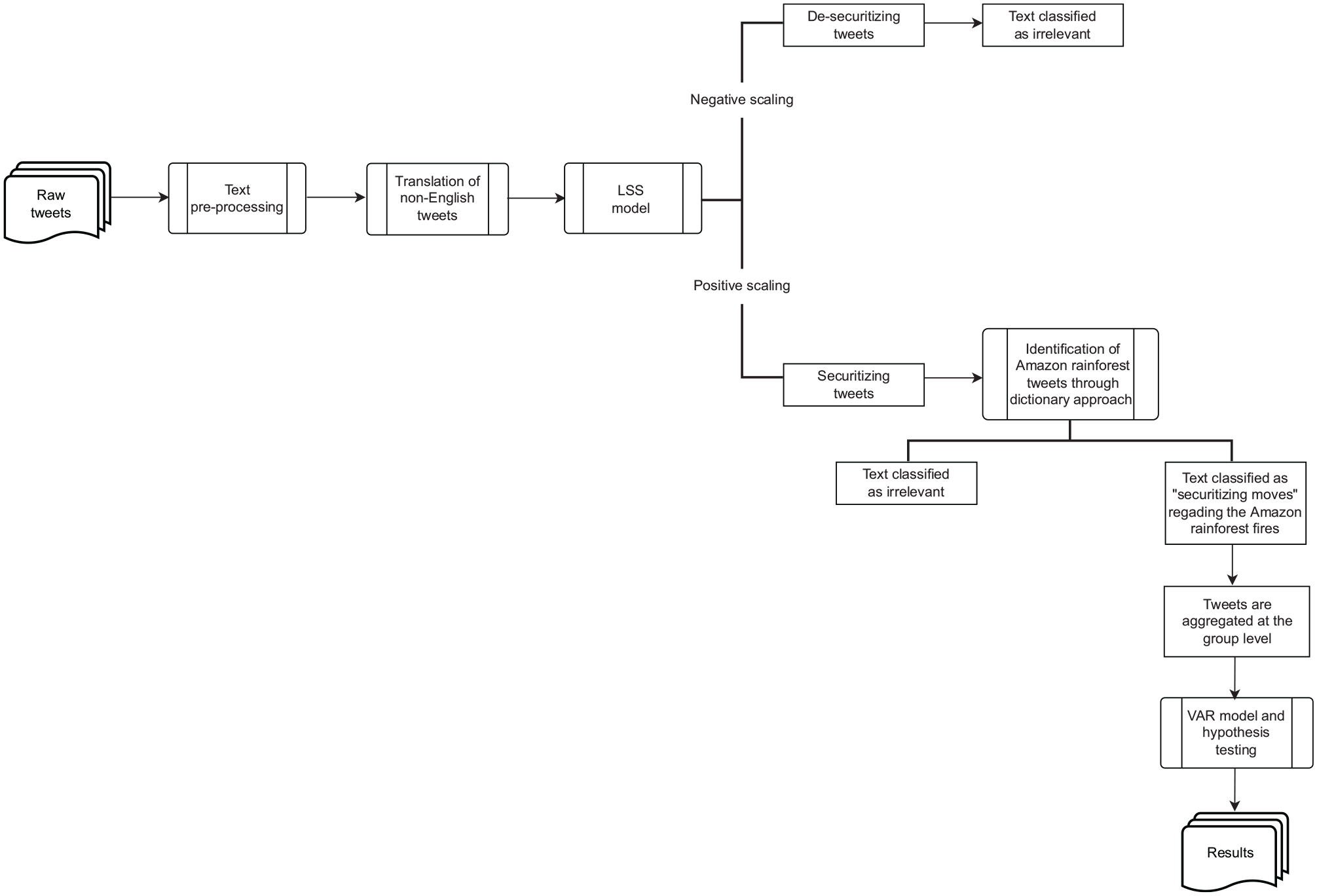
Workflow.
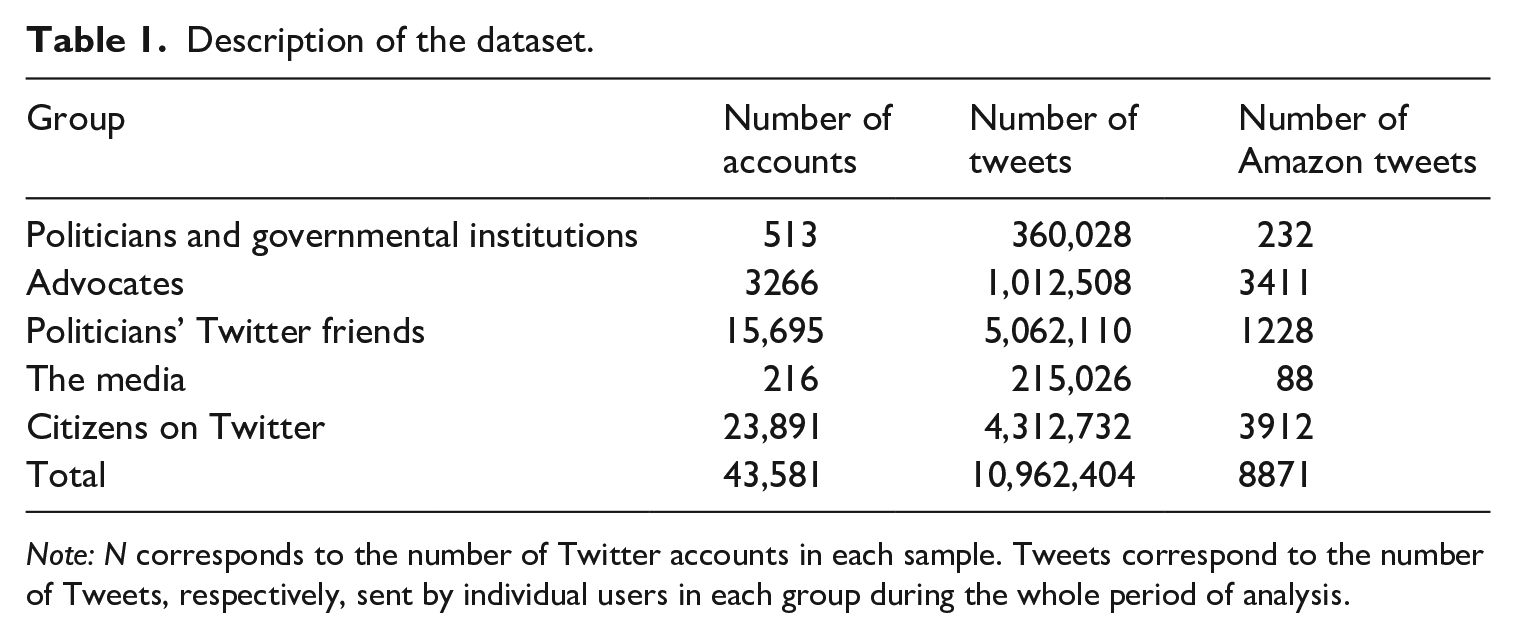
Tweets
Splitting the samples into actor groups enables the identification of the securitization processes that develop at different levels of analysis. Thus, it serves the study in its aim to challenge the state-centred top-down approach adopted by earlier work as it integrates non-elite actors into the analysis. After identifying these five user samples, all the tweets they sent during the period of the analysis (February 2019 to September 2019) were collected. The final number of users and tweets in each group can be found in Table 1. The advantage of this data collection strategy over a streaming approach (i.e. collecting live data or searching for specific hashtags and keywords) is its transparency related to the sampling techniques employed. When using the Twitter streaming API, users can expect to receive approximately 1% of the public tweet volumes at any time. However, even with large datasets, the obscure sampling methods applied by the Twitter algorithms may produce an inaccurate representation of the overall platform’s data (Mortatter and Pfeffer, 2014).
Description of the dataset.
Latent semantic scaling
The major methodological challenge faced by this study is the operationalization of securitization and the securitizing moves. A vast amount of literature has developed around this task, proposing different methodological approaches (Baele and Sterck, 2015; Huysmans, 2000; Stritzel, 2014). Here, the study relies on quantitative text analysis (QTA) tools to approach this challenge and employs the semi-supervised Latent Semantic Scaling (LSS) algorithm (Watanabe, 2021) to perform content analyses of the tweets and identify the securitizing moves. The advantage of using computerized techniques is not only their efficiency but also their capacity to analyse large volumes of text, which is very costly for human coders to achieve.
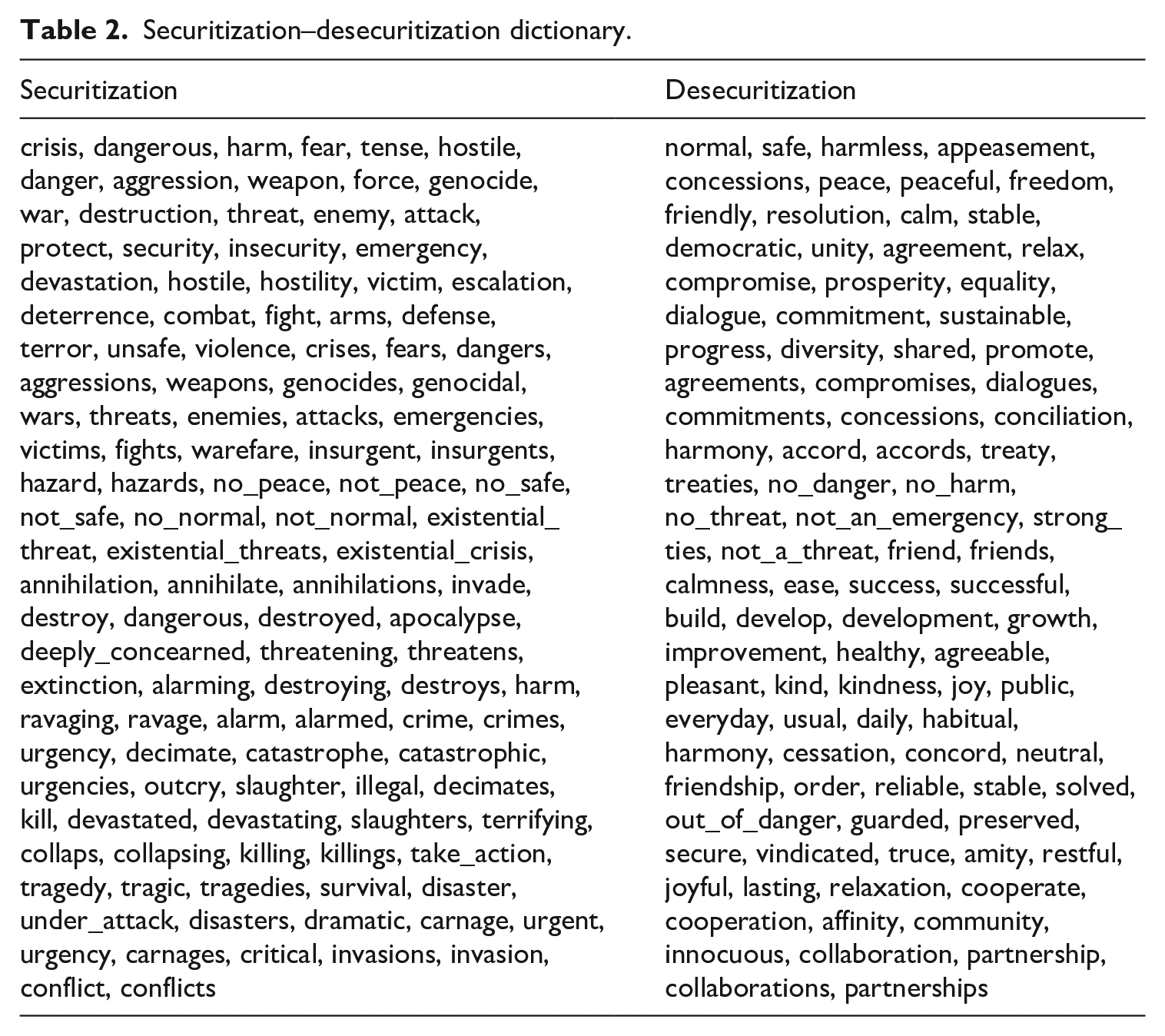
LSS 3 is based on a technique known as Latent Semantic Analysis (LSA) and combines dictionary and word-embedding analysis. It estimates the semantic similarity of words based on their surrounding contexts and assigns them continuous polarity scores according to their proximity to seed words. With a reported 70% accuracy (Trubowitz and Watanabe, 2020; Watanabe, 2017; Watanabe, 2021), the overall score of a document is then calculated as a weighted average of the semantic scores of the words in it (Watanabe, 2021). Originally, LSS requires two human inputs: a feature that specifies the concept of interest and a set of seed words that define the dimensions of scaling (e.g. while ‘migration’ might be a feature, positive-negative could be the dimensions of scaling determined by the seed words). The effectiveness of this method is demonstrated in ground-breaking work by Watanabe et al. (2019), who analyse threat perceptions on British newspaper articles. Here, the study elaborates upon this approach but develops a novel securitization–desecuritization dictionary that is employed as a unique input and can both specify the concept of interest and define the dimensions of scaling. The dictionary is based on (but not identical to) the UN Glossary of Terms and Concepts in Peace and Conflict Studies (Baele and Sterck, 2015) and assigns a scaling value of 1 to (in)security words and −1 to desecuritization ones. The dictionary and its scaling capacity are tested and validated in Appendix B (Supplemental material). Hence, securitizing moves are identified by a positive document scaling value, while desecuritization is indicated by negative values. By employing a unique human input and developing a comprehensive dictionary, the approach developed in this study offers a significant contribution: The model can be employed to analyse other security issues not considered in this study. This is further discussed in Appendix C.3 (Supplemental material).
Before applying the LSS model, the text is pre-processed by removing stop words, punctuation, symbols, numbers, emojis, URLs and infrequent words (Benoit et al., 2018; Lui and Baldwin, 2014). Re-tweets are not removed, and this decision is explained and validated in Appendix C.4 (Supplemental material). To obtain a homogeneous corpus that permits the application of dictionary-based models, all non-English tweets are identified and translated into English using the Google Translate server (De Vries et al., 2018; Lucas et al., 2015). The potential issues that may arise from this step are considered in Appendix B.3 (Supplemental material), together with its validation. Observing that securitization may develop as repeated ‘little security nothings’ (Huysmans, 2011), the data are not aggregated, so every tweet represents a ‘document’ in the context of the semantic scaling algorithm. LSS performs better with shorter text because longer text contains a diverse set of dimensions (Watanabe, 2017; Watanabe and Zhou, 2020), which makes the model especially suitable for this study.
Issue focus: the Amazon rainforest fires
By July 2019, over 7200 square miles of the Brazilian rainforest were burned. Although the Amazon rainforest had been burning for several years during the summer months, in 2019, a significant saliency was attached to the issue, leading to a signed agreement at the G7 summit to provide resources to the Brazilian state to stop the fires. Social media played a significant role in taking the issue from a national to the international level, shown by the tweets from political elites like Emmanuel Macron, who depicted the fires as an international emergency that required immediate attention (see Figure 3).

Tweet by Emmanuel Macron.
The example of the Amazon rainforest fires is, therefore, an interesting issue to analyse the processes of securitization on Twitter, as it may provide answers regarding the models of responsiveness of online securitization processes.
Identifying relevant tweets
To identify tweets from the corpus that refer to the Amazon rainforest fires, the study employs a supervised approach and develops a dictionary (Dun et al., 2021). This dictionary was developed through repeated and manual sampling operations that resulted in a list of 28 gold-standard N-grammes of extrapolatory terms, hashtags and word combinations. Moreover, when irrelevant tweets were identified in the samples, the same procedure was performed to produce a list of unwanted terms, which mostly referred to Amazon.com. The dictionary displayed in Appendix A (Supplemental material) is the result of these coding operations.
After applying the dictionary to the corpus, a third filtering operation was performed: I filtered the remaining tweets to obtain only those identified as securitizing moves based on the results obtained from the application of the LSS model (while securitizing tweets receive a positive fit score, desecuritizing tweets receive a negative score). For this last step, the data were dichotomized at different levels establishing different thresholds to codify tweets as securitizing, neutral or desecuritizing. The last column in Table 1 describes the dataset resulting from these filtering operations when the lower boundary is set at fit = 0, 2 for a tweet to be considered a securitizing move.
Autoregressive models
To test the hypotheses, the study takes advantage of the time series nature of the dataset to establish who first presents the issue of the Amazon rainforest fires as a matter of international security by drawing on vector autoregression models (VAR; Sims, 1980). VAR models explain the evolution of multiple variables based on their own lagged values as well as the lagged values of other terms, thereby allowing the analysis of the relation between several evolving variables. VAR models are well suited to capture the process between endogenous variables and have been used by similar studies (Barberá et al., 2019; Edwards and Wood, 1999; Gilardi et al., 2021; Kilian and Lütkepohl, 2017; Wood and Peake, 1998).
I build the model on the design of Barberá et al. (2019). They used a VAR model with a set of stationary time series
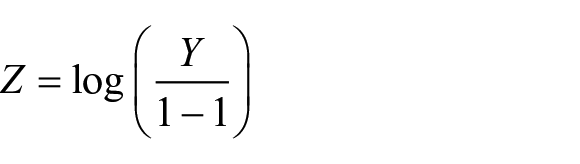
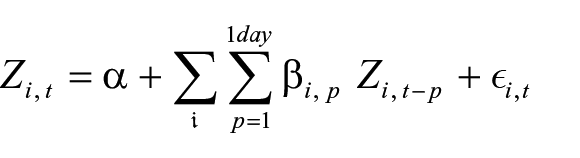
The model allows for the estimation of how much the expressed threat perception by one group needs to change on average to predict a subsequent reallocation of expressed threat perception of another group. Since the results of these models can be difficult to interpret directly, the study uses cumulative impulse response functions (IRFs), which indicate how an x-unit increase in security language use by one group predicts the cumulative threat perception that other groups express in reference to the same issue over time. This is done for brief changes in attention of 10 percentage points (from 0% to 10%) for just 1 day at day 0. This change is calculated in a simulation for up to 60 days after the initial increase. These cumulative impulse responses can be calculated for a varying number of subsequent days. The study calculates and reports them for a 7-day period in Figure 5. Other estimated lag structures from 1 to 15 days are reported in Appendix C.1 (Supplemental material).
Results
Recall that the goals of this empirical analysis are twofold: (1) To operationalize securitization based on the text shared on Twitter and (2) to understand whether non-elite actors can behave as securitizing agents on social media. To achieve these goals, the study first presents the validation analysis of the LSS model and the securitization–desecuritization dictionary. Further exploration into the scaling capacity of this semi-supervised model is presented in the Appendix (Supplemental material). Moreover, I present four sets of results regarding the connection between politicians, citizens on Twitter, the media and advocates to assess each group’s capacity to behave as securitizing agents and test the proposed hypotheses.
Polarity scores of tweets
The semi-supervised nature of the LSS model implies that it is necessary to validate the results in order to ensure that the model is correctly capturing securitization. Semantic validity is a useful concept to employ in this context, as it refers to the degree to which the analytical categories of text (the model securitization–desecuritization terms) correspond to the meanings attributed by the reader (Krippendorff, 2018; Mikolov et al., 2013). As stated earlier, LSS scales words from the corpus according to their proximity to seed words. Hence, for the results to demonstrate semantic validity, securitization-related words should be scored with a positive value and desecuritization words with a negative value.
Figure 4 shows polarity scores assigned by the LSS model to every word in the corpus based on their semantic proximity to seed words (horizontal axis) and their frequency (vertical axis). Highlighted words correspond to the seed words displayed in Table 2. Words close to zero on the horizontal axis are neutral, meaning that they have the same semantic distance to securitization and desecuritization seed words. On the right-hand side of the plot, words such as ‘weapons’, ‘attack’, ‘terror’, ‘dangerous’ and ‘crimes’ are scored strongly as securitization terms, and on the left-hand side, words like ‘development’, ‘collaboration’, ‘sustainable’, ‘dialogue’ and ‘diversity’ are scored strongly as desecuritization terms. Thus, these results show potential for corroborating the effectiveness of the dictionary and the algorithm for correctly capturing securitization. An extended list of the 40 most extreme securitization and desecuritization terms identified by the LSS model, together with additional validity checks can be found in Appendix B (Supplemental material).
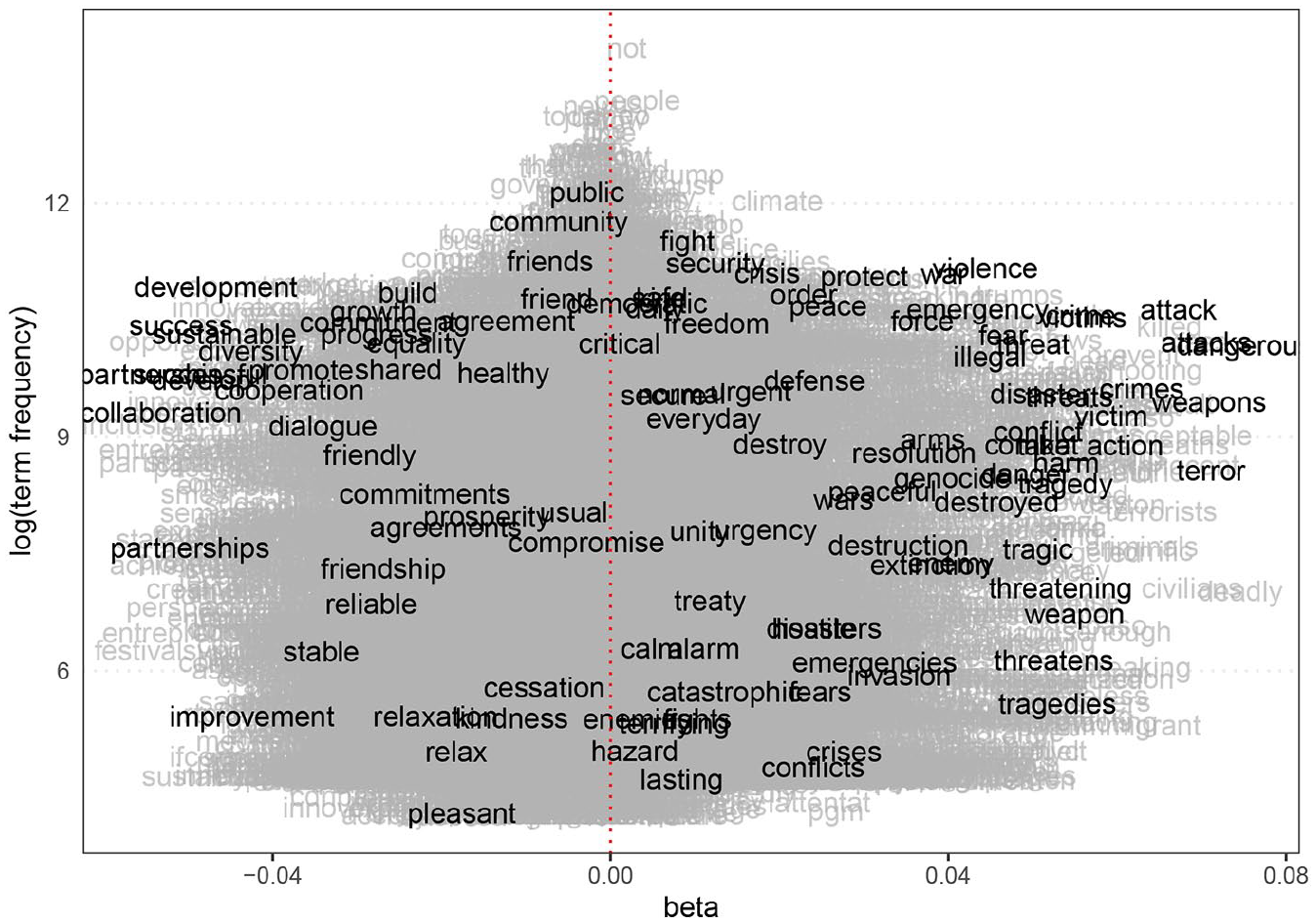
Polarity scores and frequency of words. Securitization and desecuritization words are in the right and left-hand side of the plots, respectively.
Securitization–desecuritization dictionary.
Who gets a say?
The key substantive question this study seeks to answer is whether the expressed threat perception of political elites on social media leads or echoes that of the general public, and vice versa. Is it true that security is only articulated in an institutional voice by the elites? Or can securitization develop from the bottom-up facilitated by the new conditions offered by social media?
Figure 5 shows the ability of the group in the panel title to lead the process of securitization of the Amazon rainforest fires. Specifically, the figure shows how the expressed threat perception of the groups along the y-axis responds to a one-time, 10 percentage-point increase in the use of security language by the group in the panel title 7 days ago. The predicted responses (95% confidence interval lines) are expressed in percentage points (0–100 scale). For example, the left block on the bottom shows the effect of such an increase in the expressed threat perception of politicians on all other groups. These results indicate that when politicians employed security language to discuss the issue of the Amazon rainforest fires, the expressed threat perceptions of advocates, politicians’ Twitter friends, and more strongly citizens on Twitter, increased between 0 and 4 percentage points in the following week.
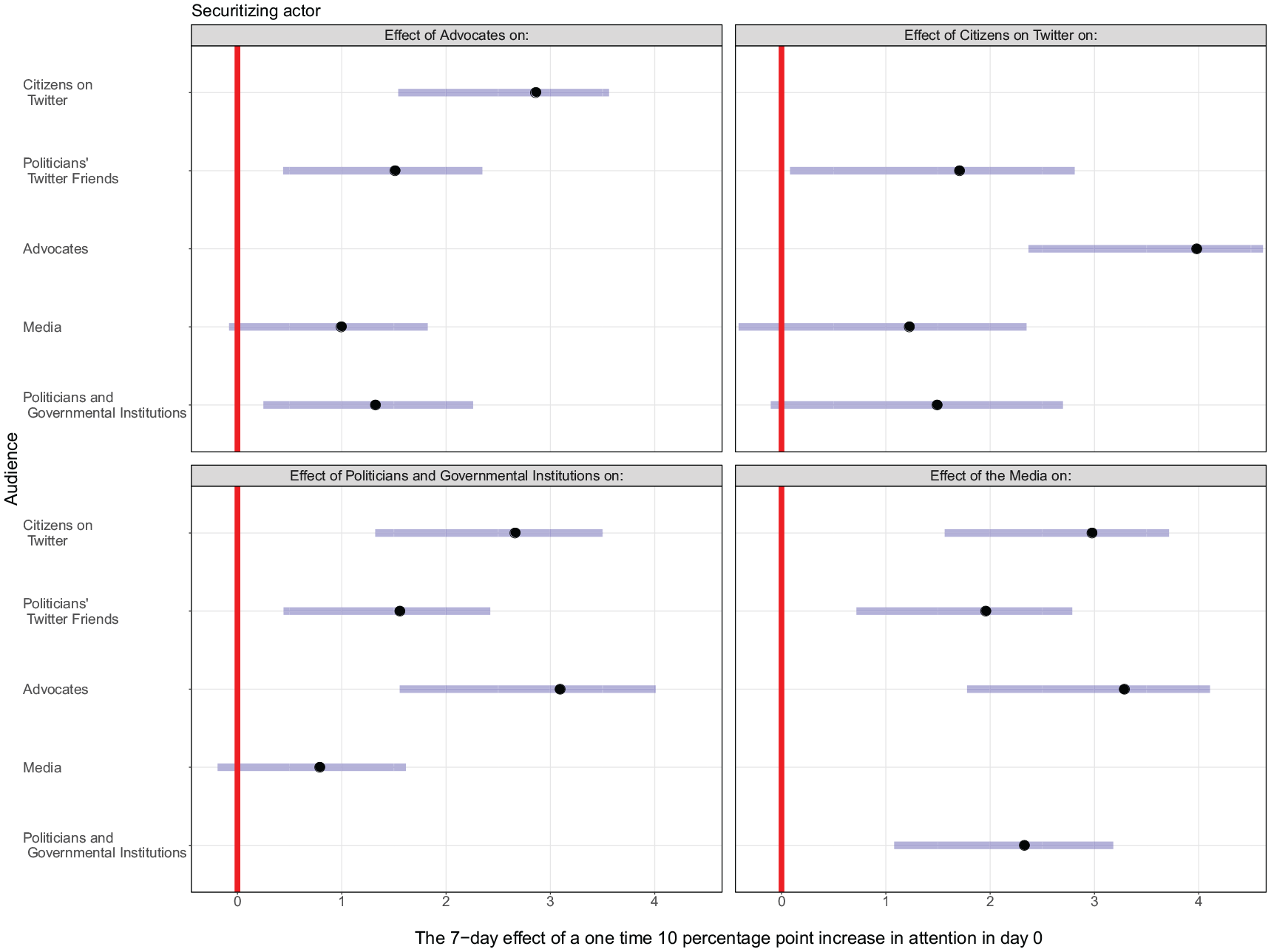
Threat responsiveness for politicians, the media, advocates and citizens on Twitter. Bars denote 95% confidence intervals.
Overall, Figure 5 offers several insights. First, most correlations are significant and positive. Null effects are only observed for the media’s responsiveness to other groups and politicians’ responsiveness to the increase in citizens’ expressed threat perception. As an effect, a second observation is the high degree of mutual influence among various groups. Only in the case of the media, the results show a unidirectional dynamic, where a strong responsiveness effect on other groups is accomplished but a low or insignificant response from the media to the other groups is observed, meaning that the media behaves as a securitizing actor but not as an audience. Third, both the media and politicians drive the strongest relationships (in terms of effect size). These results are consistent with findings supporting the salient agenda-setting role of the media and the privileged position of politicians as securitizing agents (Barberá et al., 2019; Buzan et al., 1998; Gilardi et al., 2021). Thus, Figure 5 provides initial support for the first
Top-down or bottom-up?
As shown in Figure 5, we can observe a high degree of mutual influence. For example, the expressed threat perception of politicians predicts the expressed threat perception of advocates, but the opposite is also true. Thus, to test the working hypotheses, there is a need to compare the mutual responsiveness between groups more directly. On balance, does one group lead more than it is led, or do they lead and echo each other roughly to the same extent? The study tests the direct comparisons by calculating the differences between the responsiveness of each pair of actor groups against each other (Gilardi et al., 2021). The results of this analysis are displayed in Figure 6. The 95% confidence interval of the differences is based on 1000 simulated effects of each group’s responsiveness on another actor, subtracting the values of the same pair of actors in the opposite direction (Gilardi et al., 2021). This allows us to test if one group leads the other more than echoes it.
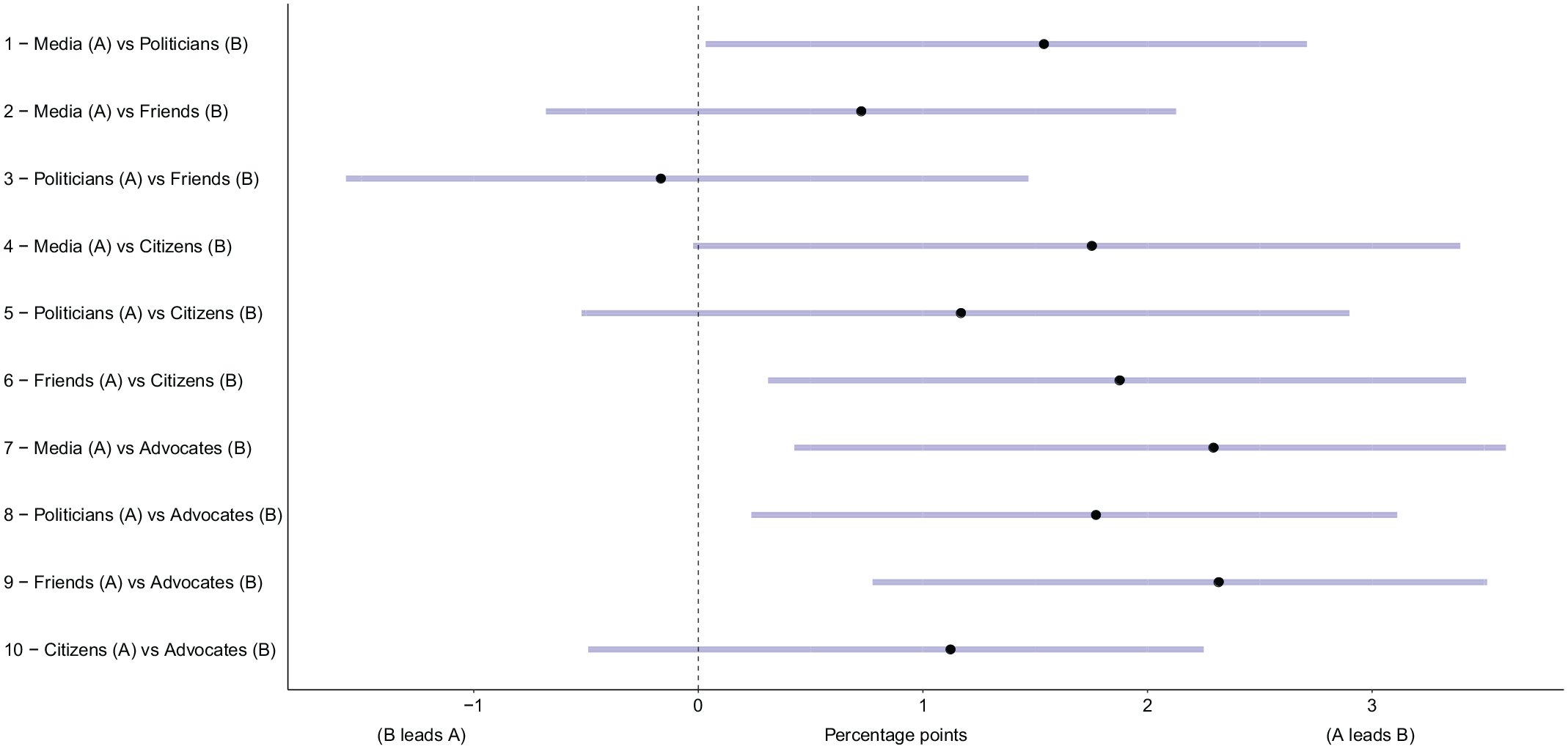
Responsiveness differences. Bars denote 95% confidence intervals.
Figure 6 shows that, in most cases, actor groups both lead and echo each other in roughly the same extent. For example, as shown in row 5, when politicians post about the Amazon rainforest fires employing security language, it leads citizens on Twitter to also employ security language to discuss the issue. But the relation goes also in the opposite direction; when citizens on Twitter present the issue of the Amazon rainforest fires as a security threat, politicians respond by also expressing a stronger threat perception. Figure 6 shows that for most groups, the strength of those relationships is roughly the same – indicated by the intersection between the confidence intervals and the dotted vertical line placed at zero – such that no group leads the others more than it is led by them. Thus, these results provide support for the endogenous model
Yet, there are five important exceptions to this pattern: First, as shown in rows 1 and 7, advocates and politicians are more responsive to the media than the media are to them. Second, advocates and citizens are more responsive to politicians’ Twitter friends than vice versa (as seen in rows 6 and 9). Finally, when comparing politicians and advocates in row 8, we can observe that advocates have a higher responsiveness to politicians’ expressed threat perceptions than contrariwise. These patterns, however, provide further support in favour of the endogenous model
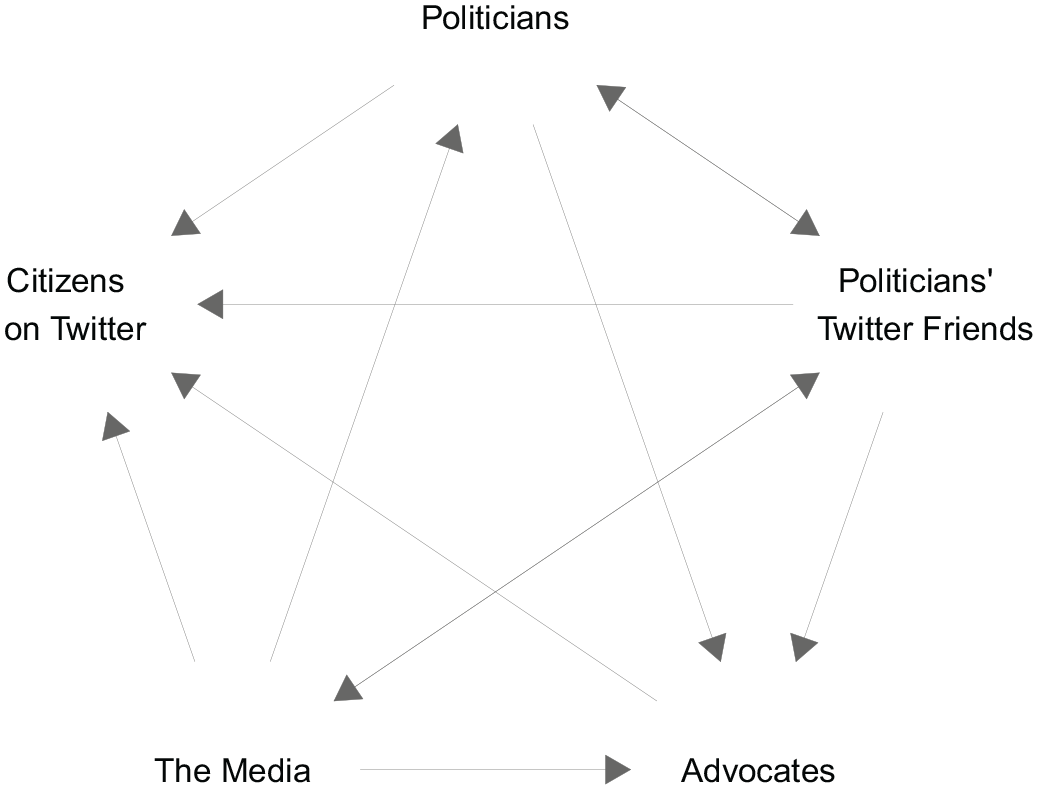
Securitization dynamics. Arrows indicate responsiveness among groups.
Conclusion
Political communication is core to the theory of securitization. Rather than treating security as a given object, securitization theory understands security as a linguistic practice through which an issue becomes a matter of insecurity. However, the claim proposed by the Copenhagen School that ‘security is only articulated in an institutional voice by the elites’ (Wæver, 1995: 57) has led to a narrow framework that disregards the active participation of non-elite actors in the process of securitization. While the contribution of the concept to our understanding of security and its construction should not be up for question, this study highlights the need to update the theory of securitization to the modern context of political communication marked by the advent of social media. To this purpose, this study developed an empirical approach that characterized the securitizing moves by politicians, the media, advocates, politicians’ Twitter friends and citizens on Twitter using Latent Semantic Scaling on the text of tweets sent between February 2019 and September 2019 (the 45th G7 summit). The study, thus, has been able to create fine-grained measures of securitization to analyse not only the extent to which the traditional political elites echo shifts in the use of security language by the public, but also to analyse the effect these non-elite agents have on other traditional gatekeepers, such as the media and advocates.
The study models how public and political expressed threat perceptions predict each other using a VAR model accounting for endogenous effects. First, the role of politicians as leading securitizing agents was corroborated. However, while changes in the use of security language by politicians in their posts about the Amazon rainforest fires led to a positive response by citizens on Twitter, politicians’ Twitter friends, and advocates, the effect was not significantly stronger than the reverse dynamic. Therefore, these results provide evidence against the hegemonic role assigned to the traditional political elites by the Copenhagen School’s framework as the only securitizing agents in the new reality of a social media environment. In other words, politicians were found to behave both as speakers and audience(s) in the online process of securitization of the Amazon rainforest fires.
While this study did not find sufficient evidence to conclude that citizens can independently lead the process of securitization, citizens were found to behave as securitizing agents before the elite groups considered in the analysis. Lay actors should, therefore, be regarded not just as a passive audience but as active agents in the formulation of securitization. This claim is further supported by the findings reported in Appendix D (Supplemental material). This study, therefore, suggests that social media exhibits new opportunities to understand the formative process of (meanings of) security, accommodating a wider range of securitizing actors and diminishing the gatekeeping power of more traditional agents (Gilardi et al., 2021). Overall, this study aligns with the literature that proposes to reconceptualize the spheres of securitization together with the actors involved in its development. Rather than reducing securitization to a single act by a single actor, the results displayed here strengthen the claim to broaden the securitization framework to account for the wide range of actors and the processes of co-production from which securitization is conceived. In fact, rather than supporting the linear, unidirectional and top-down communication dynamic proposed by the Copenhagen School, the results obtained from this analysis suggest that securitization develops as an endogenous process, where the expressed threat perception of each actor group depends on the use of security language by all other groups.
The analysis is limited to the 45th G7 summit and the issue of the Amazon rainforest fires. Nonetheless, I argue that the findings presented in this study are likely to be generalizable to other contexts and issues and have core implications for the ways in which we conceive and analyse securitization. This claim is supported by the results presented in the Appendix (Supplemental material). One of the fundamental ways in which political communication is important is that it can affect the ways in which people interpret threats. However, the communication dynamics that give way to the construction of security problems on social media had remained understudied, despite the significant attention granted to this sphere and its users by the political communication literature. This study, therefore, contributes to our understanding of securitization both theoretically and methodologically. It expands our knowledge of the role that non-institutional spheres and non-elite actors play in the formative process of securitization while demonstrating how tools from the Computational Social Science toolbox can be applied to re-examine theoretical questions in the field of security studies. Most importantly, it shows that our online behaviour can have a significant impact on the ways in which threats are conceived at a larger scale.
Supplemental Material
sj-pdf-1-nms-10.1177_14614448221111009 – Supplemental material for Who gets a say in this? Speaking security on social media
Supplemental material, sj-pdf-1-nms-10.1177_14614448221111009 for Who gets a say in this? Speaking security on social media by Natalia Umansky in New Media & Society
Footnotes
Acknowledgements
I am grateful for the valuable feedback provided by James P. Cross, Kohei Watanabe, Martijn Schoonvelde, Alessia Paccagnini, Maël Kubli, and the participants of the panels and workshops in which previous versions of this article were presented. I would also like to thank the two anonymous reviewers for their constructive comments, which helped strengthen this piece.
Funding
The author disclosed receipt of the following financial support for the research, authorship and/or publication of this article: Natalia Umansky received financial support from the School of Politics and International Relations at University College Dublin under the Iseult Honohan scholarship.
Supplemental material
Supplemental material for this article is available online.
Notes
Author biography
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
