Abstract
We conducted two studies examining the factors underlying individuals’ legitimization of hackers (digital actors operating on the internet). Drawing on the social banditry framework, and research on political action, we focused on the mediating role of anger in the association between external political efficacy and perceived legitimization of hackers’ actions. Specifically, we manipulated whether the system was responsive to participants’ demands following unfair treatment in a university (Study 1) and in an online work platform (Study 2) context. In Study 1 (N = 259) British undergraduate students read about unfair “grading” practices. They were then informed that the management was either willing (high external political efficacy) or unwilling (low external political efficacy) to investigate the matter. In Study 2 (N = 222), British participants were recruited via Prolific Academic and were presented with a scenario describing an unfair rejection of their work. They were then informed that the platform admin was either willing or not willing to investigate their case. Across studies, participants were informed that hackers had attacked the website. Supporting the social banditry framework, results indicated that individuals who perceive the system as unresponsive to their demands tended to legitimize hackers’ actions via stronger perceived anger against the system. Implications of the results, and future directions are discussed.
Citizens’ direct engagement in political action is an important aspect of democracy (de Moor, 2016). By voting or demonstrating, individuals are able to promote or resist social change, alter status relations in society and highlight the importance of specific social issues that concern them. The internet has provided individuals with many additional avenues to voice their discontent (Di Maggio et al., 2001; Meyer & Tarrow, 1998; Norris, 1996; Van Laer, 2010). A large body of research in psychology has so far examined the psychological predictors of these forms of “direct engagement” (Becker & Tausch, 2015; Saab et al., 2016; van Zomeren et al., 2004; Zaal et al., 2011). However, direct engagement in political action is not the only way people can voice discontent. When individuals perceive the political and social systems as unresponsive to their voice and demands, they may rely on the disruptive potential of other actors to exert revenge against, and disrupt the status quo on their behalf. Individuals may, thus, express their dissent vicariously by supporting such actors (Travaglino, 2017).
The increasing relevance of the internet and the digital revolution has affected many spheres of life by completely transforming the way in which individuals share information and communicate with each other. The internet creates links and communications that are a-geographical and synchronous: in the blink of an eye individuals across geographical and social boundaries can share and publish information easily and almost costlessly, bypassing those gate-keeping functions that have been traditionally served by mass media outlets and providing information directly to those among the broader public who are interested in it (Earl & Kimport, 2009; Taewoo, 2012). This revolution has inevitably impacted the realm of politics and collective action and enabled the emergence on the political scene of new actors such as “hackers” and “online trolls” (Coleman, 2014; Goode, 2015; Jordan & Taylor, 1998; Travaglino, 2017; Wong & Brown, 2013; Woo et al., 2004). Their highly public actions are sometimes designed to generate amusement, awareness, and to be seen as widely as possible. For instance, in 1996, Swedish hackers defaced the American CIA’s website, changing the title from “Central Intelligence Agency” to “Central Stupidity Agency”.
Despite the increasing political and social relevance of these online groups, very little is known about the psychological determinants of their support and perceived legitimacy among the wider community. Understanding why individuals may express dissent vicariously by supporting and legitimizing actors such as hackers is important for at least two reasons. First, individuals’ legitimization of these (and similar) actors may enable such actors to gain and exert social influence and power, and to avoid detection from the authorities (Travaglino & Abrams, 2019). In other words, public legitimization of these actors limits the state’s capacity to express sovereignty and has significant implications for democracy, because the actions of these groups are rarely (if ever) subject to public scrutiny or characterized by transparent decision making (Kuldova & Quinn, 2018; Lea & Stenson, 2007; van Dun, 2014). Second, after learning of, and interacting with these actors, individuals may embrace more radical political positions and, in some circumstances, become even more likely to engage in radical actions. Research shows that prior contact with radical groups may precede individuals’ engagement in more radical forms of political action or limit opposition against them (Drury & Travaglino, 2019; Sageman, 2004, 2008; Wiktorowicz, 2005).
To understand the way in which individuals perceive hackers’ actions, Travaglino (2017) recently proposed a social banditry framework (SBF). The SBF draws on Hobsbawm’s (1959) sociological and historical analysis of banditry in pre-industrial, peasant societies. Hobsbawm (1959) famously referred to these bandits as “social” because, despite acting illegally, they were liked and protected by the communities where they operated. Bandits’ actions against the powerful provided otherwise voiceless masses with an opportunity to express their grievances. In this article, we draw on the SBF (Travaglino, 2017), and report two experiments examining for the first time the role of individuals’ perceived responsiveness of the system (i.e., external efficacy; Niemi et al.,1991) in sustaining individuals’ legitimization of hackers’ actions. Specifically, we propose and demonstrate that when individuals perceive the system as unresponsive to their demands, they will feel more anger towards the system and, subsequently, be more likely to legitimize hackers’ disruptive actions.
Direct and Vicarious Political Dissent
Research in social psychology has examined why people actively engage in direct forms of political participation, and why they refrain from doing so (Klandermans, 1997; van Stekelenburg & Klandermans, 2013; van Zomeren et al., 2012; van Zomeren et al., 2008; Verba et al., 1995). According to the dual pathway model of political action (van Zomeren et al., 2004), the two key paths leading to direct engagement are injustice appraisal-anger (Jost et al., 2012), and efficacy (Bandura, 1982; van Zomeren et al., 2008; Verba et al., 1995).
When individuals perceive the system as unjust, they are motivated to participate in political protest and collective action to promote social change. Perceptions of unfairness trigger anger, which is a key factor motivating people to mobilize against the source of injustice (e.g., Jost et al., 2012; Leach et al., 2006; Verhulst & Walgrave, 2009; van Zomeren et al., 2004). Anger is an intensive emotional state linked to high physiological arousal. It may fuel individuals’ motivation to fight back against unfair treatment (see Leach et al., 2006, p. 1234).
Importantly, however, individuals’ likelihood of taking part in political action is also predicted by the extent to which individuals feel their actions will help them to achieve their goals (Klandermans, 1997; van Zomeren et al., 2008). When individuals do not perceive they have the resources to affect the political decision-making process, or when they consider their governments to be unresponsive towards their demands and needs (i.e., low political efficacy), direct engagement in political action is less likely (Balch, 1974).
In such circumstances, we contend, individuals do not just passively accept unjust arrangements. Rather, they might fall back on an alternative way of expressing dissent. Travaglino (2017) proposed that individuals may plead their own cause vicariously by supporting actors that challenge the status quo, dispute core social discourses, and disrupt the functioning of the system (see also Travaglino & Abrams, 2019). These actors (i.e., bandits) generally operate outside the official realm of politics and are often regarded as criminals by the state (Hobsbawm, 1959; Schneider & Schneider, 2008). Such indirect expressions of dissent were termed “vicarious”.
A modern example of bandits is hackers operating on the internet (Wong & Brown, 2013). We contend that individuals’ legitimization of, and support for hackers is a key expression of vicarious dissent, because hackers’ actions are highly visible and public, require expertise that laypeople do not generally have, and often (but not exclusively) may be aimed at government agencies, corporations and other powerful entities. In this article, we report two experiments examining what motivates individuals to support and legitimize hackers’ actions.
Bandits, Hackers and the Social Banditry Framework
Hobsbawm (1959) first used the term “social banditry” to indicate those individuals who in peasant societies were not integrated within rural communities and were forced to the margins. They were generally outlaws or criminals. What made them “social” was that they allegedly never robbed or looted peasant’s harvests in their own territories. Rather, they tended to attack mostly the rich and the powerful (i.e., those with property), or were perceived as doing so. As a result, they often had the support of local communities and were at times even considered as mythical heroes, e.g., Robin Hood (Hobsbawm, 2000). In reality, however, bandits consisted of bands of armed and violent men who damaged peasants as much as the powerful (Blok, 1972; Joseph, 1990). Nonetheless, in the eyes of peasants, bandits’ predatory actions represented a challenge to the economic and social institutions of the time (Hobsbawm, 1959). Peasants had no way to express their discontent against the powerful. The rigid pre-industrial system in which they lived did not provide them with a channel to voice their demands and alter the status quo. Thus, support for bandits’ actions became a concrete manifestation of their inchoate anger against social arrangements they perceived as unfair (Travaglino, 2017).
In the digital era, the opportunity to exchange information rapidly and the availability of synchronous communication has redefined the concept of political action. Additionally, with the rise of micro media (such as emails and cell phones) and middle media (such as websites and online campaigning), formal and informal organizations and individuals can manage information, communicate and coordinate with each other in a way that was previously possible only for formal organizations (see, for example, Bennett, 2003; Neuman, 1991).
These changes have also provided a platform for the emergence of novel disruptive actors. Hackers are individuals who use their informatic expertise to disrupt the current social, economic or political systems (Wong & Brown, 2013). They organize themselves into groups where membership is defined by self-identification. Hackers are connected and communicate through the web, usually using pseudonyms to preserve their anonymity. Their actions generate public amusement and include trolling (i.e., using pranks), spamming, disrupting access to websites, doxing (broadcasting a target’s personal information), and disseminating disturbing content online (Coleman, 2014). Hackers have substantial impact on the costs of computer security for public institutions and corporations (Voiskounsky et al., 2013). In addition, hackers and their supporters may sometimes become echo-chambers of radical views, through which individuals could build radical networks (cf. Malthaner & Waldmann, 2014).
Similarly, to the bandits first described by Hobsbawm (1959, 2000), hackers’ motivations are inherently ambiguous. Some individuals engage in hacking merely for personal enjoyment, amusement or even material gain, without any explicit political or social agenda. Others define themselves as “hacktivists”, taking action against those companies, governments, and individuals who they consider as a threat to their norms and values (such as openness and free circulation of information on the internet; Coleman, 2014; Milan, 2013). Regardless of their motivations, however, hackers might be considered as a modern instance of social banditry because their actions are criminalized by the state and yet they may earn people’s admiration and support by enabling individuals to express their dissent vicariously.
Previous research has investigated individuals’ vicarious dissent in the context of attitudes towards Anonymous, a well-known group of hackers (Travaglino, 2017). Travaglino’s (2017) SBF posits that individuals who perceive the system as unjust but simultaneously feel they do not have the means to oppose it (i.e., low political efficacy), are more likely to express their anger against the system as support for disruptive actors such as hackers. To test this idea, Travaglino (2017) used two cross-sectional studies and demonstrated that individuals were more likely to engage in direct forms of political action to express social discontent (e.g., voting or demonstrating in the streets) when they perceived the system as unjust but felt they had higher political efficacy, replicating the basic tenet of the dual pathway model (van Zomeren et al., 2004). However, when individuals perceived lower political efficacy, they felt stronger anger against the system, which subsequently predicted stronger support towards Anonymous’ actions.
Here, we extend this research by addressing the important question of what type of political efficacy determines individuals’ legitimization of hackers’ actions. An important limitation of Travaglino’s studies (2017) is that they used a generalized measure of political efficacy that did not distinguish between different key aspects of this construct. Moreover, the correlational nature of the studies meant that no causal conclusions could be drawn on the relationship between efficacy and individuals’ support for Anonymous. In this article, we extend this research by experimentally manipulating the responsiveness of the system (external political efficacy; Niemi et al., 1991). In addition, we examine individuals’ legitimization of non-specific hackers’ action to generalize the findings beyond the specific group of Anonymous.
Political Efficacy and Banditry
As discussed earlier, individuals are more likely to engage directly in political action if they feel they have the means to achieve their goals, a concept known as efficacy (van Zomeren et al., 2013). At the societal level, individuals’ feelings towards institutions are a key predictor of individuals’ political engagement (Campbell et al., 1954). Campbell et al. (1954, p. 187) defined the concept of political efficacy as “the feeling that political and social change is possible, and that individual citizens can play a part in bringing about this change”.
There is a vast literature on the role of political efficacy in political action (e.g., Flavin & Keane, 2012; Karp & Banducci, 2008; McAdam, 1982; Smets & van Ham, 2013; Tarrow, 2011). This research supports the idea that individuals’ feelings of political efficacy may concern two distinct spheres (Niemi et al., 1991). Individuals’ beliefs about their own ability to understand and control the political process are referred to as internal political efficacy. In contrast, external political efficacy refers to individuals’ beliefs about the responsiveness of the system to their political demands. These constructs have different implications in the social sphere (Balch, 1974).
According to the SBF, feelings of external political efficacy should be of particular relevance in individuals’ appraisals and legitimization of hackers’ actions. Hobsbawm’s (2000) analysis of social banditry proposed that peasants protected and aided outlaws because outlaws embodied their anger and resentment against a system unresponsive to their desire for more just social arrangements. Indeed, at the time, the masses operated in a structural system that was perceived as unalterable because authority was rooted in unmovable traditions, divine rights or superior might.
In socio-psychological terms, this analysis seems to imply that individuals’ feelings about the responsiveness of the system play a key role in the legitimization of hackers’ actions. Thus, here, we propose and test the idea that individuals who feel the system is not responsive to their aspiration for more justice, might see the (potentially illegal) actions of hackers as more legitimate.
Anger Against the System
We contend that individuals’ legitimization of hackers’ actions is an expression of anger against the system, following the system’s unresponsiveness to individuals’ demands for more just arrangements. Work on the social psychological underpinnings of political action has generally focused on emotional expressions at intergroup levels of analysis (Iyer & Leach, 2008; Mackie et al., 2008). Relatively little research has examined the outcomes of individuals’ feelings and emotions at the levels of institutions and the system (Solak et al., 2012; cf. Iyer et al., 2007). Solak et al. (2012, p. 679) define system-level emotions as “emotions that are experienced as a direct or indirect result of subjective or objective system-level characteristics”. Perceived structural injustice that is not addressable within an existing system is known to generate anger, and this feeds into a desire to change the system (Abrams et al., 2020). In the present research, we focus specifically on system-level emotions and posit that these should reflect individuals’ appraisals of the system’s responsiveness. Specifically, we test the idea that a system that does not listen to individuals’ grievances may trigger anger, which then motivates legitimization for social banditry against the system. Thus, stronger anger against the system should mediate the association between external political efficacy and legitimization of hackers’ actions.
Overview of the Studies
We present two studies examining individuals’ legitimization of hackers’ actions in the contexts of a university (Study 1) and an online survey platform (Study 2). Across studies, individuals were presented with a description of an unjust situation (i.e., an unjust grading process or an unfair exploitation of their work). We subsequently manipulated individuals’ feelings of external political efficacy by altering the responsiveness of the system. In line with the SBF and previous evidence (Travaglino, 2017), we predict that individuals should feel angrier when the system is described as unresponsive to their demands (i.e., lower political efficacy). Individuals’ anger against the system should in turn predict stronger legitimization of the hackers’ actions.
Across studies, we also measure and control for individuals’ feelings of internal political efficacy. Internal political efficacy refers to individuals’ beliefs about their own competence to deal with the system. We predict that this variable should be less relevant in the context of indivve system rather than against the individuals’ own abilities to engage with political issues. Finally, we control for gender and ageiduals’ legitimization of hackers because support for these actors is a reaction against an unresponsi given the male stereotypes linked to hackers and the fact that younger people might have more familiarity with this phenomenon (Bakker & de Vreese, 2011; Tanczer, 2016). All results reported below are substantively the same if these covariates are not added to the model. The studies report all conditions and no participants were excluded from the analyses. Anonymized materials and data are available upon request from the first or second author.
Study 1
Method
Participants and Design
Two-hundred-fifty-nine British university undergraduate students (222 females, 37 males) took part in this study. The mean age was 19.87 years (SD = 3.62). The majority of the participants reported to be White (53.7%) whereas the remaining participants were Black (11.6%), Asian (9.7%) or from mixed and other ethnicities (24.7%). Participants took part in exchange for course credits via the online software Qualtrics. No participants were excluded or included following data analysis (except deletions due to missing cases). Participants were randomly assigned to one of two conditions (external efficacy: high vs. low). A sensitivity power analysis using G*Power (Faul et al., 2007) indicates that this sample size enables us to detect a small-to-medium effect size, f = 0.17, at 80% power (α = .05).
Procedures and Materials
Participants were invited to take part in a study related to issues with the grading process. After reading an informed consent sheet, participants were asked to provide demographic information (age, gender, ethnicity). Subsequently, participants read a brief scenario (identical across conditions) presenting an unfair grading process after a university exam. The exam was described as important to students’ careers and future prospects, to augment the psychological relevance of the manipulation. Specifically, participants read: You have just received the results of a university exam. There was a lot of pressure for you to do well in this exam. The grade will determine whether you are able to enroll in the master’s program you wish to pursue next year. However, you are worried about your performance on this last exam. Many of the questions were unclear, not directly touching on the content taught to you in the lectures. Indeed, the grade you receive is lower than you had hoped for. When looking at the transcript you find your exam to have been graded unfairly. Most of the feedback refers to content you have not been taught, despite having attended the relevant lectures over the previous term. As the results mean a lot to you, you and your colleagues who also have been affected decide to bring this up to the university’s exam office. You all explain to the staff working there that you feel your grades have been awarded unfairly and your reasons for this.
After this introductory cover story, the text changed depending on the condition.
Low External Efficacy Condition
Participants in this condition read about the system being unresponsive to requests to address their grievances about the unfair grading process. In response to your complaint, the office does not agree to talk to the Head of School. They do not seem to take your complaint very seriously. They do not show any interest in investigating the matter and just tell you that there is no option to regrade the exam regardless of the results or the type of feedback.
High External Efficacy Condition
Participants in the high external efficacy condition read the following text indicating that the university system was willing to address their grievances.
In response to your complaint, the office agrees to talk to the Head of School. They assure you that they will take your complaint very seriously. They tell you they will investigate the matter and that there will be an option to regrade the exam if results of the whole cohort are abnormally low or the feedback is seen as not reflecting the core learning objectives of the module.
Participants were then asked to complete the measures described below in relation to the scenario they had just read.
Manipulation Checks
The manipulation was intended to affect individuals’ sense of external efficacy, while describing a situation which was equally unfair across conditions. To test whether the manipulation worked as intended, we adapted two items from a measure of external political efficacy (Lee, 2006) and four items from the System Justification Scale (Kay & Jost, 2003). Specifically, external efficacy was measured by asking participants to indicate how much they disagreed or agreed with the following statements: “The university responds to students’ opinions effectively” and “The university’s exam office responds to students’ opinions effectively” (1 = strongly disagree, 7 = strongly agree; Spearman-Brown r = .92). Perceived fairness was measured using these four statements: “The way in which the exam had been graded was unfair”, “All students had a fair shot at achieving a good grade”, “The exam system is set up so that students usually get the results they deserve” and “I find the university grading system to be unfair” (1 = strongly disagree, 7 = strongly agree; α = .72).
Internal Efficacy
To control for participants’ sense of internal efficacy we measured this construct using the following two items adapted from a measure of internal efficacy (Niemi et al., 1991): “I have enough ability to talk about and participate in decisions about how exams should be graded” and “I have enough ability to understand how exams should be graded” (1 = strongly disagree, 7 = strongly agree; Spearman-Brown r =.69).
Anger Against the System
Anger against the system was measured using the following three items adapted from Travaglino (2017): “The response of the exam office angers me”, “I am furious about the way in which the exam office handled my complaint” and “When I think about the university’s exam system I feel outraged” (1 = strongly disagree, 7 = strongly agree; α = .89).
After measuring these constructs, participants were informed of the hackers’ attack against the school. Participants read that a group of hackers had defaced the school’s website, leaving the following message “learn to do your job” on the front page. In addition, participants were informed that the hackers’ actions had made the website inaccessible for three days. They were then asked to respond to some items.
Legitimization of Hackers’ Actions
Individuals’ legitimization of hackers’ actions was measured using six items. Participants were asked to indicate how much they disagreed or agreed with the following statements: “The aims of the hackers are legitimate”, “The hackers’ activities deserve respect”, “The hackers’ activities are dangerous for democracy” (reverse-coded), “The hackers deserve admiration”, “The hackers and like-minded groups are criminals” (reverse-coded) and “The activities of the hackers may have positive consequences for university students” (1= strongly disagree, 7 = strongly agree). The items formed a reliable scale (α = .74).
Results and Discussion
Manipulation Checks
The responsiveness and perceived fairness of the system are related constructs (Cichocka & Jost, 2014). To examine whether the manipulation affected individuals’ feelings of external efficacy but not of perceived fairness we used two ANCOVAs. We tested the effect of condition on external efficacy controlling for perceived fairness and, conversely, the effect of condition on perceived fairness controlling for external efficacy. Results indicated that the manipulation significantly affected individuals’ feelings of external efficacy, F (1, 253) = 99.80, p < .001, ηp² = .28. Participants reported higher external efficacy in the high efficacy (M = 4.97, SD = 1.34) condition, compared to the low efficacy (M = 3.09, SD = 1.47) condition. Conversely, the effect of condition on perceived fairness of the grading system was not significant, F (1, 253) = 0.196, p = .659, ηp² = .001, and similar in the high (M = 4.13, SD = 1.03) and low (M = 3.74, SD = 1.00) efficacy conditions. The results indicated that the manipulation successfully affected individuals’ external efficacy, whereas the overall situation was perceived as equally unfair. 1
Perceived Legitimacy of the Hackers’ Actions
In line with the social banditry framework, we hypothesized that lower external efficacy would trigger individuals’ anger against the system. In turn, anger against the system should predict a stronger legitimization of the hackers’ actions. To test these hypotheses, we used a mixed structural equation model whereby the external efficacy manipulation (1 = low external efficacy, 2 = high external efficacy) predicted individuals’ anger against the system, which in turn predicted individuals’ legitimization of the hackers’ actions. Gender, age, and internal political efficacy were covariates in the model. Analyses were run in R using the lavaan package (Rosseel, 2012). The model’s fit was adequate, χ2 = (68, N = 247) = 105.21, p = .003, Comparative Fit Index (CFI) = .97, Standardized Root Mean Square Residual (SRMR) = .04, Root Mean Square Error of Approximation (RMSEA) = .05. Results are summarized in Figure 1, and Table 1 presents means, standard deviations and correlations among variables.
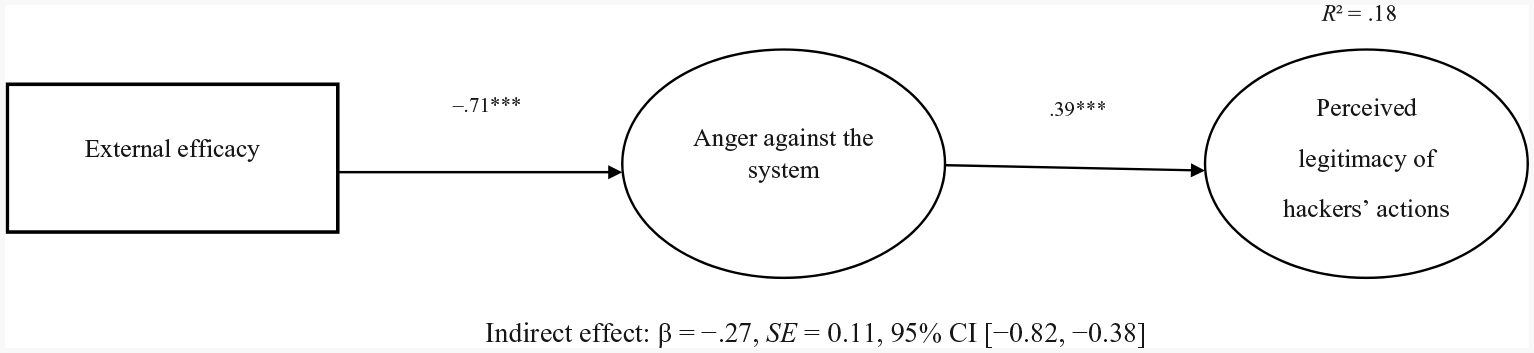
Structural equation model showing the coefficient for the indirect effect of the manipulation of external efficacy on the perceived legitimacy of hackers’ actions via anger against the system in Study 1.
Means, standard deviations and correlations among variables in Study 1.
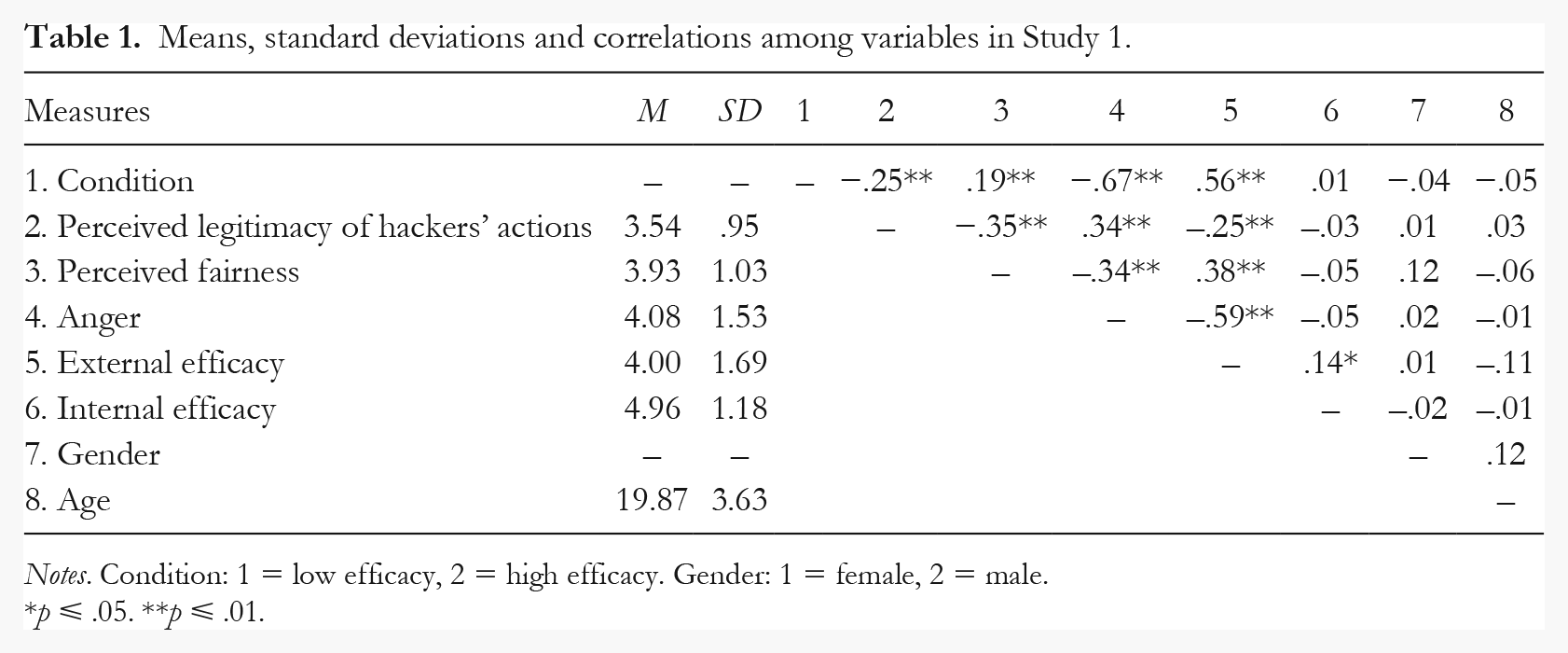
Notes. Condition: 1 = low efficacy, 2 = high efficacy. Gender: 1 = female, 2 = male.
p ⩽ .05. **p ⩽ .01.
Anger was negatively predicted by condition, β = −.71, SE = 0.16, p < .001. This is consistent with previous findings from Tausch et al. (2011, Study 3) and Travaglino (2017), and suggests that perceiving the system as unresponsive increases individuals’ anger against the system. Supporting the idea that social bandits are supported because their actions embody individuals’ anger against the system, legitimization of the hackers’ actions was predicted by anger, β = .39, SE = 0.27, p < .001. Internal efficacy did not predict anger against the system, β = −.09, SE = −0.10, p = .15, or perceived legitimacy, β =.01, SE = 0.01, p = .89. In line with our hypothesis, inspection of the indirect effect revealed a significant indirect effect of condition on individuals’ legitimization of the hackers’ actions through anger β = −.27, SE = 0.11, 95% CI [−0.82, −0.38]. Thus, the results provide evidence for the SBF. In the next experiment, we attempt to replicate this pattern of findings in a different context, using a non-student sample.
Study 2
Method
Participants and Design
Two-hundred-twenty-five British participants (160 females, 64 males, 1 other) took part in this study. The mean age was 35.16 years (SD = 11.26). The majority of the participants were White (89.8%), the remaining were Asian (4%), Black (1.8%), or from mixed and other ethnic groups (4.5%). Participants were recruited using the Prolific Academic platform via the survey software Qualtrics and were compensated for their participation.
As a selection criterion, participants must have taken part in at least five prior studies on Prolific Academic to ensure that they had some familiarity and involvement with the platform. As in Study 1, participants were assigned to one of two between-subject conditions (condition: high external efficacy vs. low external efficacy). A sensitivity power analysis using G*Power indicates that this sample size enables us to detect a small-to-medium effect size, f = 0.19, at 80% power (α = .05). No participants were dropped from the analyses (except deletion due to missing cases) and no participants were added to the sample following the analysis.
Procedure and Materials
Participants were asked to take part in a study about payment procedures on Prolific Academic. After completing the measures, participants were debriefed in writing, thanked, and compensated for their time. Procedures were similar to those of Study 1 but were adapted to the context. Prolific Academic is a platform where participants can take part in studies in exchange for payment. Researchers have the opportunity to reject participants’ submissions if they do not meet some pre-specified conditions, or are suboptimal (for instance, failure to respond correctly to an attention check). Rejection of a submission may limit participants’ ability to take part in further studies, but the researchers have still access to the submission, creating the potential for unfair dynamics.
Participants were first presented with an informed consent sheet and they provided some demographic information (gender, age, ethnicity). Subsequently, participants read a scenario describing a situation in which a researcher unfairly rejected their and other workers’ submission.
Think about a study you recently took part in, on the platform Prolific Academic. You carefully read the instructions and the participation criteria, which clearly stated you were a suitable participant. Moreover, you were careful in answering the questions honestly and put a lot of thought into your answers. The day after completing the study you receive a notification that your submission was rejected. The reason provided to you was that you failed two out of three attention checks. You find this unfair because you really did not see any attention check despite putting a lot of attention in the study. You also read a post on a forum in which many other people complained about being rejected from the same study due to the same reason. Due to the fact that you really have put effort and time in the study, you first contact the researchers to ask them to reverse the rejection, but because you receive no answer you contact Prolific Support. In your email you provide a detailed explanation of why you think your submission should not have been rejected.
The subsequent text varied across conditions.
Low External Efficacy Condition
In response to your complaint, Prolific Support does not agree to help you discuss the matter with the researcher or make an enquiry on your behalf. They do not seem to take your complaint very seriously. They do not show any interest in investigating the matter and just tell you that there is no option to review the rejection/approval process.
High External Efficacy Condition
In response to your complaint, Prolific Support agrees to mediate between you and the researcher. They assure you that they will take your complaint very seriously. They tell you they will investigate the matter and that there will be an option to revise the whole rejection/approval process if anomalies are to be found in the rejection criteria used by this specific researcher.
Following the manipulations, participants were asked to respond to some items.
Manipulation Checks
To examine whether the scenario successfully affected individuals’ feelings of external efficacy, but was perceived as equally unfair across conditions, we adapted the same items as in Study 1. Specifically, two items were used to measure participants’ feelings of external efficacy (“The Prolific Support Team responds effectively to people who take part in the studies” and “Researchers who recruit participants on Prolific Academic respond to participants’ requests effectively”; Spearman-Brown r = .84) and four items were used to measure participants’ perceived unfairness of the system (“The way in which this submission was rejected was unfair”, “All participants had a fair shot at getting paid for their contribution on Prolific Academic”, “I find the system to administer studies on Prolific Academic unfair” and “Prolific academic is set up so that participants usually get the outcome they deserve”. This scale failed to achieve good reliability, α = .53, which improved if the first item was dropped, α = .64. Below, we present results using all four items but using only three items does not alter the pattern of findings.
Internal Efficacy
Two items were used to measure participants’ perceived ability to engage with the issue, “I have enough ability to understand the criteria for rejecting a submission on Prolific” and “I have enough ability to talk about and participate in decisions about how submissions should be evaluated on Prolific” (1 = strongly disagree, 7 = strongly agree; Spearman-Brown r = .86).
Anger Against the System
Anger against the system was measured using three items, “The response of the Prolific Support team angers me”, “I am furious about the way in which Prolific handled my complaint” and “When I think about Prolific’s support system I feel outraged” (1 = strongly disagree, 7 = strongly agree; α = .89).
Following the measures, participants were presented with a scenario similar to the one used in Study 1. Specifically, the scenario described some hackers attacking the support website, leaving the following message on the front page, “learn to do your job”. Participants’ were also informed that this created a disruption whereby the website was not accessible for three days.
Legitimization of Hackers’ Actions
The same six items as Study 1 were used to measure participants’ legitimization of hackers’ actions (1 = strongly disagree, 7 = strongly agree). The items formed a reliable scale (α = .74).
Results and Discussion
Manipulation Checks
To examine whether the manipulation affected participants’ feelings of external efficacy independently of the perceived fairness of the system, we used two ANCOVAs as in Study 1. Results indicated that the manipulation significantly affected participants’ external efficacy F (1, 222) = 64.56, p < .001, ηp² = .23, controlling for perceived fairness. As expected, participants perceived stronger external efficacy in the high (M = 5.44, SD = 1.00) compared to the low (M = 3.90, SD = 1.75) efficacy condition. Conversely, participants’ perception of fairness was not affected by the manipulation controlling for external efficacy F (1, 222) = .44, p = .51, ηp² = .002. The situation was perceived as equally unfair in the high (M = 4.40, SD = 0.57) vs. low (M = 4.46, SD = 0.73) condition.
Legitimization of Hackers’ Actions
Data were analyzed using the same procedures as in Study 1. Specifically, we tested a structural equation model with latent variables whereby the manipulation of external efficacy predicted anger against the system, which in turn predicted the legitimization of the hackers’ actions. Gender, age and internal political efficacy were covariates in the model. Figure 2 summarizes the model, and Table 2 presents means, standard deviations and correlations among variables. The model’s fit was adequate, χ2 = (68, N = 225) = 114.34, p < .001, CFI = .97, SRMR = .06, RMSEA = .055.
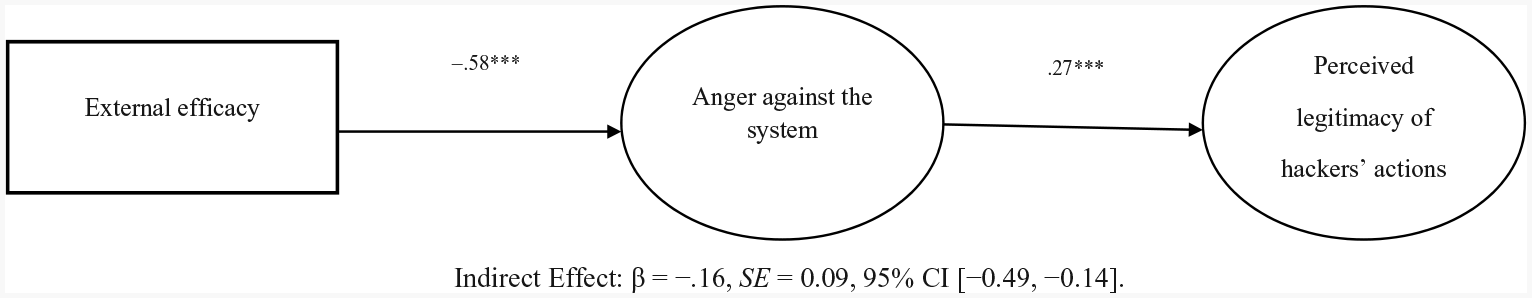
Structural equation model showing the coefficient for the indirect effect of the manipulation of external efficacy on the perceived legitimacy of hackers’ actions via anger against the system in Study 2.
Means, standard deviations and correlations among variables in Study 2.
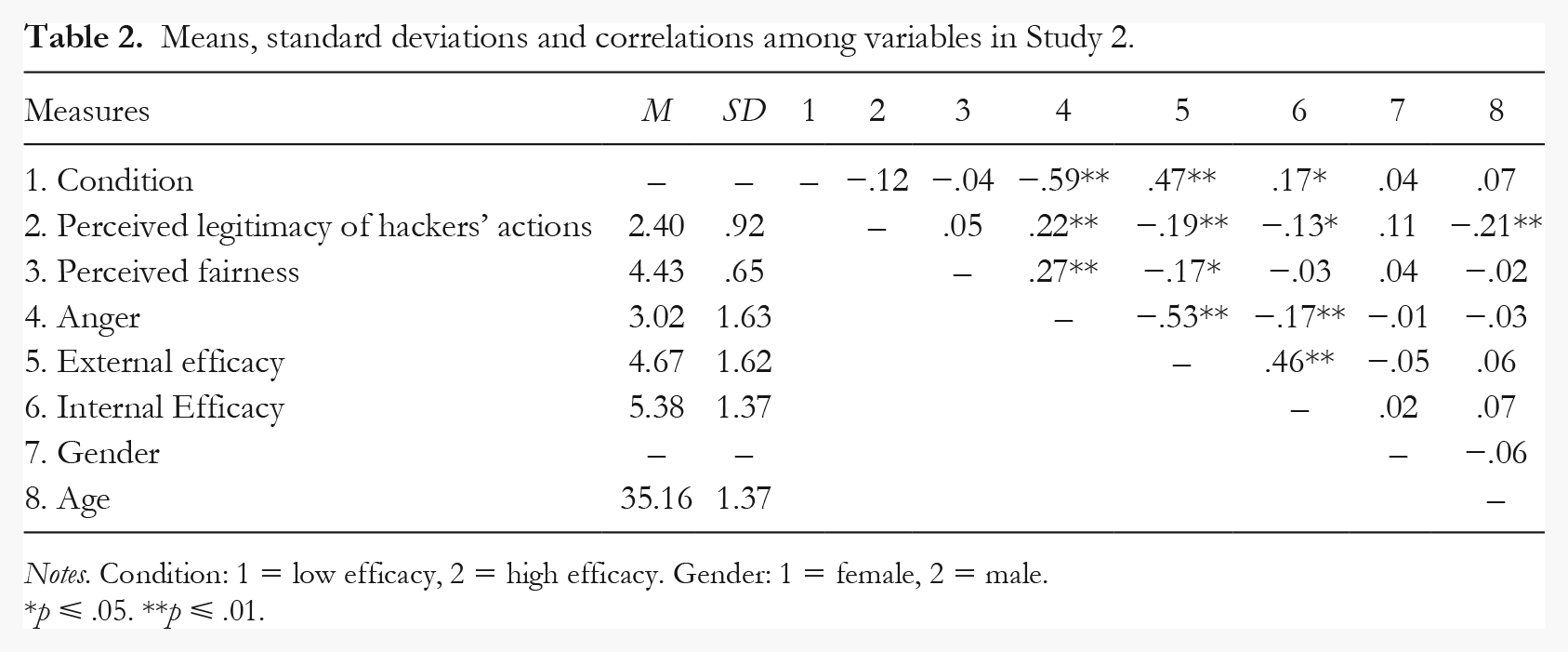
Notes. Condition: 1 = low efficacy, 2 = high efficacy. Gender: 1 = female, 2 = male.
p ⩽ .05. **p ⩽ .01.
In line with the SBF and replicating results from Study 1 in a different context, anger was affected by condition, β = −.58, SE = 0.19, p < .001. Participants felt more anger against the system when the system was described as unresponsive to their demands and needs. In turn, legitimacy of the hackers’ actions was positively predicted by anger, β = .27, SE = 0.05, p < .001. The indirect effect of the manipulation of perceived external efficacy via anger on the perceived legitimacy of the hackers’ actions was significant, β = −.16, SE = 0.09, 95% CI [−0.49, −0.14]. As in the previous study, internal efficacy did not significantly predict anger, β = −.03, SE = 0.04, p = .58 or the legitimization of the hackers’ actions, β = –.08, SE = 0.06, p = .50, in line with the idea that it is the perceived system’s unresponsiveness that drives individuals’ support for social bandits.
General Discussion
Hackers and other online actors are playing an increasingly important role on the political scene (Coleman, 2014). These groups operating on the internet have attacked key targets, including governments and financial institutions. As more and more aspects of individuals’ social lives (i.e., voting, exchanging goods and money, interfacing with bureaucracies) take place in the digitalized world, it is important to examine how hackers are perceived by others. In this article, we have proposed that the social banditry framework (Travaglino, 2017) provides us with a useful theoretical basis for understanding individuals’ reactions to hackers’ actions. Specifically, we argued that the system’s responsiveness to individuals’ demands for fairer social arrangements is a key factor determining individuals’ legitimizations of hackers’ actions.
Results from two studies supported this contention. In two experiments, we manipulated the extent to which the system (i.e., the university in Study 1, or an online survey platform in Study 2) was responsive towards its users, following an unfair episode. In Study 1, the episode concerned unfair “grading” practices among students, whereas in Study 2 it was an unfair exploitation of users’ work. Across studies, results indicated that individuals in the low external efficacy condition reported more anger against the system. In turn, anger predicted individuals’ legitimization of hackers’ actions following a hacker attack. Importantly, across studies, the manipulation checks indicated that the system was perceived as less responsive in the low efficacy condition, but as equally unfair across conditions. The results cannot, therefore, be attributed to differences in individuals’ perceptions of unfairness, which remained similar across conditions, but depended specifically on perceiving the system as irresponsive their grievances. Moreover, we also measured, and controlled for, participants’ feelings of internal efficacy. The findings showed that the latter construct was not systematically linked to anger nor to individuals’ legitimization of the hackers’ actions.
Taken as a whole, this pattern of findings provides support for the SBF (Travaglino, 2017). The notion of social banditry was originally proposed by Hobsbawm (1959) to explain peasants’ support for violent outlaws in pre-industrial societies. Bandits’ actions enabled individuals who had no access to other political channels to express their grievances in a vicarious form. Thus, bandits earned the support of the community, which created myths and legends to celebrate bandits’ actions and protected them from the law. In line with this analysis, the present studies demonstrated that external efficacy is a key factor involved in individuals’ support for hackers. Systems that do not provide participants with the ability to express their aspirations for more justice trigger more anger. This anger, in turn, is an important predictor of individuals’ support for, and legitimization of, bandits’ disruptive actions against the system.
Direct and Vicarious Dissent: Theoretical Contributions
Research in social psychology has focused on individuals’ engagement in direct forms of political action such as protesting or voting (e.g., Becker & Tausch, 2015; van Zomeren et al., 2008). This research indicates that stronger efficacy, injustice appraisals and anger are important predictors of individuals’ engagement. Research has generally paid less attention to the way in which individuals express dissent when legitimate routes to social change are ineffective or blocked (cf. Abrams et al., 2020), they do not feel they have the means to achieve social change. Moreover, we are aware of no studies in psychology focusing specifically on individuals’ perceptions of responsiveness of the system (i.e., external political efficacy) in relation to alternative forms of dissent. Indeed, current psychological models of political engagement often assume passivity and inaction as a consequence of lower efficacy (e.g., van Zomeren et al., 2012) or other barriers to participation (Klandermans & Oegema, 1987). Alternatively, lower political efficacy has been linked to violent political engagement (Tausch et al., 2011, Study 3), although it should be noted that Tausch et al. (2011) used a generalized measure of political efficacy that did not distinguish between internal and external efficacy.
In this research, we extend previous work by proposing an additional avenue that individuals may use to voice their discontent. We contend that individuals may express discontent vicariously, by supporting disruptive actors that attack the system on their behalf. Specifically, in line with the SBF, the results of our studies indicate that support for, and legitimization of these actors may reflect individuals’ anger against an unresponsive system.
The notion of “vicarious dissent” and the SBF enable us to move past the dichotomy between “action” and “inertia”, which characterizes much of the psychological research on individuals’ dissent. For instance, although there are circumstances in which individuals do not seem to be directly challenging the status quo, it does not follow that they are supinely accepting it. Rather, the present studies indicate that individuals may find alternative ways to express their grievances. Such alternatives are perhaps harder to detect, but they may serve an important function in the longer run, including fostering people’s resilience and exposing them to the idea that the system can be questioned and challenged, thus shaping politicized identities in opposition to the status quo (see also Hobsbawm, 1972; Travaglino, 2017).
However, these alternative forms of dissent may also involve some risks for security and democracy. Research on social banditry in sociology or history has often debated the question of whether certain specific groups in various geographical locations were in fact social bandits, as opposed to merely self-interested criminals or even violent outlaws who preyed on defenseless communities on behalf of the powerful (Blok, 1972; Hobsbawm, 1972; Joseph, 1990; Schneider & Schneider, 2008). Nowadays, this same ambiguity may frame hackers’ actions. Some hackers may engage in attacks against governments “only for fun”, others may have a more developed political agenda (Coleman, 2011), and others still may work on behalf of governments and other powerful hidden entities (van der Walt, 2017). In addition, hackers operate in secrecy (Voiskounsky et al., 2013), and it is often difficult to discern who is the author of an online attack, or their objectives and motivations. This means that, generally, their decisions cannot be publicly scrutinized or altered. Without external accountability, hackers’ and other banditry’s actions could easily degenerate, damage “wrong targets”, violate the fundamental principle of due process, or foster mistrust in institutions.
Despite these ambiguities, we contend that individuals may, in certain circumstances, legitimize hackers’ actions because those actions offer a way to manifest individuals’ anger against the system. Therefore, from a psychological point of view, rather than whether bandits are genuinely “political”, it is perhaps more important to speak of a “social banditry function” that may characterize certain actions or groups, regardless of their actual motivations and objectives. Additional research is needed to examine other predictors of individuals’ legitimization of such actors, as well as other online and offline groups that may perform such a social banditry function (e.g., mafias, terrorist organizations, and paramilitary groups).
Finally, it is also important to consider how the SBF fits the theoretical distinction between normative and non-normative forms of political engagement. Research on non-normative political action has so far examined the predictors of individuals’ direct engagement in actions that are violent and illegal, or more generally depart from the norms of society (Becker & Tausch, 2015; Tausch et al., 2011). The SBF provides a complementary perspective by investigating those instances in which individuals express their dissent vicariously, legitimizing disruptive groups and actors who dwell at the margins of legality (or whose actions are outright illegal). The SBF, in other words, aims at explaining the circumstances in which some individuals may be keen to support groups that are unaccountable, sit outside normative power structures, and whose actions may potentially represent a danger also for their own security (Jordan & Taylor, 1998; Voiskounsky et al., 2013).
Clearly, vicarious dissent could be expressed both in relation to normative and non-normative avenues. For instance, individuals’ support for mafia groups, criminal organizations that heavily rely on illegal activities and the use of violence, involves different socio-psychological predictors compared to their support for hackers, online activists and pranksters that do not always act illegally and even more seldomly use violence (Travaglino & Abrams, 2019). Moreover, there might be important differences between the psychological determinations of individuals’ support for humorous, relatively harmless forms of hacking, and more serious and dangerous ones. Moreover, future research should examine vicarious expressions of dissent in the context of actors who attack an unfair authority with legal means. In the present studies, we focused on individuals’ legitimization of semi-legal actions. Conversely, the official authority might be attacked by actors who are outside the system but act legally or according to different sets of laws, as, for example, in the case of an international court. Future studies may provide further insight into this important extension of the SBF, by examining the legitimization of normative attempts to challenge an unfair authority and by comparing them to illegal ones.
Limitations and Future Directions
This research is the first to experimentally demonstrate how individuals’ sense of external efficacy affects their support for social bandits. This research has some limitations which should be taken into account in the interpretation of the results. One limitation is that we did not ask participants whether they had experienced previous situations or events similar to those described in our manipulation. The chronic experience of the system’s unresponsiveness or unfairness may have a stronger impact on individuals’ expressions of vicarious dissent, compared to transient ones. The results of the present studies are, however, in line with those of previous survey research examining more stable individuals’ perception of the political system in relations to hackers (Travaglino, 2017).
Moreover, while stressing the role of external efficacy, it is also important to note that the SBF holds that an individual’s perception of an unjust system is an important determinant of their support for banditry (Travaglino, 2017). Future research should extend the present work by directly manipulating the perceived fairness of the system in order to establish at what point it sets a boundary or threshold condition for the impact of external efficacy to occur.
Future research could also manipulate the hackers’ explicit motivations in order to understand under which circumstances “bandits” are more likely to lose support, and perhaps increase opposition. For instance, hackers who explicitly aim at personal gains may be seen as motivated by selfish aims, and therefore may be less likely to earn people’s support. In addition, identification with the group targeted by hackers (e.g., identification as university students, or national identification) may be negatively linked to support for hackers. This is because higher identification may be associated with more trust towards the system and stronger external efficacy, or because individuals who identify with a group may be more likely to express their dissent directly rather than vicariously.
Relatedly, an additional important task for future research is to examine other social and psychological mechanisms that explain why individuals express support for “bandits”. According to Subašić et al.’s (2008) model of political solidarity, there are situations in which a “silent majority” may stop siding with an established societal authority and sympathize with, or sustain a minority in position of disadvantage. This realignment of the majority is made possible by processes of redefinition of the self, during which individuals dis-identify from the authority and identify, instead, with the minority that is challenging it. A similar process may also take place in the context of individuals’ support for bandits, whose challenge to the system may enable individuals to question the meaning of their relationship to the authority, embrace alternative definitions of who they are and ultimately switch their allegiances (Travaglino, 2017).
There are also important differences between this model and the SBF. Central to the political solidarity model is the analysis of when and why a silent majority expresses support for the struggling minority treated unfairly. Conversely, the SBF addresses situations in which it is a smaller group of individuals with access to special resources (e.g., hackers’ technical skills and abilities, traditional bandits’ capacity for violence, or criminal organizations’ access to weapons) who purport to make the interests of the majority. Moreover, according to Hobsbawm (1972), support for banditry grows out of an expression of individualistic desire for revenge, rather than a collective program for social change (see also Travaglino, 2017). Nonetheless, future research should examine the social identity and self-categorization processes involved in individuals’ support for banditry (cf. Abrams et al., 2020).
Finally, it is important to investigate the role of different emotional reactions against the system in sustaining individuals’ vicarious expressions of dissent. In the present research, external efficacy was a predictor of anger against the system. This finding was in apparent contrast with some of the research conducted using the dual pathway model, in which instrumental (i.e., efficacy) and emotional (i.e., anger) considerations are described as independent paths to political engagement (van Zomeren et al., 2012). Research on the dual pathway model has generally examined how individuals perceive the group’s ability to achieve social change, rather than their sense of efficacy in relation to the responsiveness of the system (see also Tausch et al., 2011; Travaglino, 2017; Travaglino & Moon, in press). Moreover, this research has yet to assess the role of anger against the system (Travaglino & Moon, in press). Future research should consider the role of different forms of efficacy, in relation to different targets (e.g., the system, the group) in order to provide a better understanding of the relationships between efficacy, emotions and dissent.
Additionally, the experience of schadenfreude could help explaining why individuals may sometimes legitimize forms of disruptive and illegal dissent such as banditry (Heering et al., 2020). The literature on schadenfreude contends that when individuals witness the misfortune of someone that they perceive as higher in status they will draw pleasure from it. Previous research on schadenfreude (Leach et al., 2003) also suggests that, in the intergroup context, a powerful outgroup will be perceived as more “deserving” of misfortunes when its superiority is perceived as illegitimate (e.g., Doosje et al., 1995; Ellemers et al., 1997). The role of schadenfreude may be especially relevant in the context of banditry in general, and of hackers in particular because of their use of humor to attack the powerful (Milan, 2013).
Conclusions
The last 30 years have seen rapid growth of digital information and communication technologies (ICTs). The diffusion of ICTs has happened at a much faster pace compared to other technological advancements as telephone or TV (Van Laer, 2010). This has inevitably led to many changes in different spheres of life, not least in politics and in the context of collective action (Christensen, 2011; Di Maggio et al., 2001; Norris, 2001), where the internet has provided the opportunity for new forms of protest and expression to arise. Hacking and online activism are examples of novel forms of protest that have been made possible by, and entirely rely on, the web. These forms of protest have become increasingly influential, garnering significant media attention and spurring public debate around issues of security, privacy and freedom (Tomblin & Jenion, 2016).
Hacking and other illegal (or semi-legal) forms of online action may undermine public institutions and security, increase the costs of operating online systems, and even destabilize democratic decision making due to their unaccountability. They may also shed light on the weaknesses of official authorities, thus posing a real threat to the legitimacy and the stability of the system. It is, therefore, not surprising that these actors are often criminalized by the state (Schneider & Schneider, 2008).
Nonetheless, hackers’ actions may be perceived as legitimate by the wider public and these actors may be supported by people who may perceive them as a way to “get back at” a system that does not listen to their demands. In line with this idea, we have demonstrated the importance of external efficacy and anger in individuals’ vicarious dissent, and support for hacker groups. The findings suggest that open and responsive political systems that grant individuals the ability to express their grievances may see reduced support for this and other forms of social banditry.
Footnotes
Authors’ note
Maria S. Heering and Giovanni A. Travaglino contributed equally to this manuscript and their names appear in alphabetic order.
Declaration of conflicting interests
The authors declared the following potential conflicts of interest with respect to the research, authorship, and/or publication of this article: One of the authors is part of the editorial team of this journal.
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
