Abstract
Anonymity on the Internet is a contentious issue; by some seen as an important freedom to be protected, while others argue for increased identification to protect groups at risk of exploitation. The debate reflects a dichotomous view of online anonymity; you are, or you are not anonymous. However, anonymity is a complex process played out on different levels and defined by various actors. While empirical studies show this, theoretical synthesis is lacking. This essay provides perspective on anonymity online by comparing two critical cases, online auctions and online gaming, we corroborate results from a 4-year interdisciplinary project with researchers from sociology, economics, and computer and system sciences. We argue that one should talk about anonymities in plural form, as online anonymity is not a state but a relational process. We put forth a conceptual model, which unpacks online anonymity as interdependent macro structures – legal, commercial, and technological – and micro/meso facets – factual, social group, and physical – to be used in future research.
Introduction
Anonymity on the Internet has become a contentious issue; it protects freedom of speech yet hampers accountability of, for example, crime or harassment. Online anonymity is seen by some scholars as an important freedom which needs to be protected from, foremost, meddling nation-states and corporate interests (Castells, 2002; Lessig, 2006). At the same time, others argue for increased identification online in order to protect youth and other groups at risk of exploitation, antisocial, and fraudulent behaviours (Citron, 2014). Crudely, the polarised debate stands between the proponents of the ‘real name Internet’ of e.g. Facebook and the anonymous or pseudonymous Internet of e.g. Reddit. These positions mirror the common understanding of anonymity as a dichotomy – either you are anonymous, or you express your ‘true’ self.
Researchers before us have argued that this dichotomous view of anonymity is too limiting and that we need a new understanding of anonymity on the Internet (Kennedy, 2006; Marx, 1999; Nissenbaum, 1999; van der Nagel and Frith, 2015). Being nameless does not cover what it means to hide one’s identity online. While a great deal has been written about online anonymity in the early days of the Internet (e.g. Donath, 2002; Turkle, 1995) as well as more recently (Sharon and John, 2018) most studies have focused on anonymous communication on a micro level, such as user expressions and experiences of online anonymity in person-to-person interaction. While studying online anonymity on a micro level is significant for gaining a deeper understanding of online interactions such a perspective leaves out processes and norms on a macro level, which are key to understanding how anonymity forms online.
In this article, we argue that online anonymity is a process played out on multiple levels and regulated and defined by various actors, and while empirical studies show this, theoretical synthesis is lacking. This essay aims to begin to fill that gap, by proposing a framework of online anonymity that takes into account interactions, relationships, and structures, on a micro/meso and macro level. We thus answer the call for attention to structures, and not only the individual level of online social life (Stalder, 2002), of critical importance today in the shadow of invasive Big Data. This means that online anonymity is performed, negotiated, communicated, and perceived by people, as well as sanctioned, organised, and regulated by law, businesses, hardware, software, and IT-networks. In a 4-year interdisciplinary research project (2014–2017) on online anonymity we research social interaction in two anonymous and semi-anonymous venues; online auctions and online gaming. The period allowed for thorough data collection, analyses, and interdisciplinary collaborations. Here, we synthesise and draw on the research experiences of the project. Through an analysis of the two cases (auctions and gaming), we propose a multi-layered conceptual model which can be useful in studies of online anonymity. We focus on anonymity between users and delimit our engagement with related concepts such as privacy; where privacy relates to concealing private information while anonymity relates to concealing identity-bearing information. Private information and identity bearing information can overlap, an example being when information availability and processing is so plenty (Big Data) that all information can become private and identity bearing (Acquisti et al, 2016). In this essay however, we focus on anonymity. We view identity bearing information as being conveyed in three main forms, by factual information, social group membership, and embodied expressions.
Anonymity is approached from our respective social science fields of sociology, economics, human-computer interaction, and computer and system sciences, and thus draw mainly on literature from these fields. Online anonymity is, in its essence, a multifaceted phenomenon that can best be understood from an inter-disciplinary approach. We see anonymity as a relational process, consisting of factual, social, and physical facets active on the micro/meso level of human interaction intersecting with legal, commercial, and technical structures exerting influence on a macro, structural level. Our multi-dimensional model of online anonymity is intended as a tool for researcher’s thought process when studying online anonymity.
Previous research on anonymity online
Understandings of online anonymity often draw on (offline) definitions of what it is to be anonymous. According to Pinsonneault and Heppel (1997), anonymity is the inability to identify the sender of a message, and Marx (1999) calls it one polar value of a broad dimension of identifiability versus non-identifiability. Anonymous (1998) divides anonymity up in complete anonymity, partial anonymity, or non-anonymity. Recent research has also questioned such definitions of anonymity as being too narrow (Kennedy, 2006; Nissenbaum, 1999; van der Nagel and Frith, 2015). In general, increased complexity has defined how our understanding of online anonymity has evolved.
While definitions of anonymity offline still have their base in ideas about wearing masks or not revealing a name, for example, whistleblowing or voting, online anonymity is different. Many of the basic social cues about personality offline are absent online (Donath, 2002) and Johnson (1997) when argues that while anonymity offline requires significant effort, due to the nature of networked interaction anonymity online is more akin to the natural state. In the contemporary context of Big Data, users still perceive themselves as anonymous towards each other while the data collecting parties become invisible to users (Pasqual, 2016).
As anonymous online spaces have moved from chatrooms and message boards in the 1990s towards more dynamic spaces in the 2000s reaching a large audience, such as Facebook and today’s smart-enabled applications, it has coincided with more centralised platforms, that to a lesser degree, allow users to hide their identities. For example, on bulletin boards, aliases and pseudonyms were common, while many current social network services such as Facebook, Instagram, Tinder, et cetera require legal names. This has been called the real names Internet (boyd, 2014; Froomkin, 2017). One argument in the development towards real names is that it helps promote trust, cooperation, and accountability (Millen and Patterson, 2003) as anonymous messages are less trustworthy (Rains, 2007). While there are often choices for who can see identity information on platforms, users seldom make an active choice, ending up with the default option of revealing all identity information to all users (see discussion of default options in various settings in Mullainathan and Thaler, 2000). However, the real name Internet has also led to a popularisation of new anonymous platforms such as Yik Yak, Whisper, and Sahara.
For the past decade, governments have made laws around new online technologies, and this has partly included restraining anonymous communication, where both governmental and commercial interests are now controlling legal aspects of online anonymity (Froomkin, 2017). As a consequence, online anonymity has been discussed as an important freedom which needs to be protected (Castells, 2002; Lessig, 2006). While others are clamouring for increased identification online in order to protect youth and other groups at risk of exploitation, antisocial, and fraudulent behaviours (Citron, 2014). Increased restrictions have, however, been found to lead to a greater call for technical solutions for being anonymous online (Larsson et al., 2012).
Anonymity between users
Even though anonymous interaction is a defining fact about online interactions, much research has highlighted the various contexts and cases where this is negotiated and broken in contact between users. Examples range from Kendall’s (1998) work on how people who conceal their identity or cross-perform social identities are met with suspicion or even hostility, to research on how impairment does not vanish in digital spaces (Saltes, 2013). Social identity belongings such as gender, age, race, ability, sexuality, et cetera are more or less visible online. Both explicitly, we tell people about who we are, or implicitly, others infer from how we type, move in a game, talk, or from pictures and videos. Even in Nakamura’s (2002) early work on what she critically calls ‘identity tourism’, where users played around with social identity categories such as gender, age, or ethnicity it is clear that our social identities do not stop to matter online as one would expect in a completely anonymous space. Even on platforms that attempt complete anonymity – such as 4chan where all users simply go by the username anonymous – repeated interactions and typing styles contributes to creating fleshed out identities (Philips, 2015).
So while anonymous online life has been seen as disembodied, this assumption does not hold in empirical work. For example, Saltes (2013) study of self-disclosure on an online dating sites for people with impairments demonstrates that the embodiment of impairment does not vanish in digital space but individuals are confronted by a heightened sense of bodily awareness at a time when they most want to appear desirable; in text- based virtual online worlds user’s online bodies are typed into being in processes of embodiment (Sundén, 2003); on online forums users draw on shared bodily experiences such as illnesses to create a sense of shared identity (Daniels, 2009), and in online games, players create lasting groups based on offline social identity characteristics (Eklund, 2015). Still, unless brought to bear, our embodied selves are not as readily available as in offline interaction. We can more easily attempt to hide our physical and emotional reactions as communication is mediated. Through visual cues, typing styles, or movement of digital avatars, users expresses and signals identity facets to interactional partners. Online interaction is partly physical and users draw on embodied resources in interaction (see Dourish 2004).
Indeed, a dichotomous and contextless view of online anonymity only speaks to a limited range of previous research, some of which is presented here. We need new ways of understanding the breadth of what it means to be known or unknown on the Internet. In line with this, we argue that anonymity is not simply whether one’s legal name is known or not, but whether various aspects of our selves, who we are, can be identified by others, consciously or unconsciously. These others can be single individuals, groups of people, or even organisations and nation states.
Approach
This essay’s goal is to develop a theoretical, conceptual model drawing on two critical, empirical cases (Flyvbjerg, 2006). We build on results from a 4-year project (Online anonymity, 2014-2017) where we conducted two complementing case studies; a study of social interaction in online gaming and an experiment at an online auction site. We wanted to find common trends across multiple venues where people come together online, and where the status of anonymity changes over time. In online games, many gamers consciously or unconsciously reveal identity bearing information through extensive social interaction, on auction sites, accumulated reputational feedback connected to a username is key for selling and buying and once an auction is won the buyer and seller’s identities are automatically revealed by the platform to facilitate payment and shipment of goods. These cases are thus in some sense similar to each other, and in other senses very disparate.
In a constructivist approach, we draw on results from the project in order to theorise anonymity online. The conceptual framework presented is inspired by the process of theorising as defined by Swedberg (2011). We thus use our cases as ‘critical dialogue partners’ (Alvesson and Kärreman, 2011 p. 16) rather than to prove or test a finished theory. Proving or disproving a theory needs to be done with different empirics than the ones the theory was constructed from. We, in the words of Alvesson and Kärreman (2011), start from the ‘mystery’ that came to the fore in our project, where we found ourselves unable to fully explain how anonymity mattered in our cases using current theory and by thinking on what our cases had in common, and where they differed, we focus on breakdowns derived from empirical observation to develop theory. The method and data collection of the original case studies can be found in the Supplementary Material. Below we briefly describe the cases in order to give context to the study at hand.
Online gaming
Our case study of online gaming concerned social interaction and anonymity in this venue. In focus was the game World of Warcraft (Blizzard, 2004), which has been called the most influential massive multiplayer online game, 16 years after release it has less than 5 million players (statista.com). In order to play, users create an account which can also be used to play other Blizzard games. World of Warcraft (henceforth WoW) is set in a Tolkien-inspired fantasy world where players get together or play solo moving around the world in quest of monsters to kill, treasures to find, and honour to gain. Social interaction, both brief and extended, collaborative or competitive, is a key feature of the game. Identity bearing information is thus negotiated throughout play.
Online auctions
Tradera is the largest consumer-to-consumer auction platform in Sweden. Since 2015 it is owned by PayPal. It has about 2.5 million users and ~2 million weekly listings. In order to buy and sell, users have to create an account with Tradera. Buyers and sellers can build a reputation by providing publicly visible feedback to each other after auctions are completed. During bidding buyers and sellers have limited information about each other, the main visible information is feedback from previous auctions, the number of completed auctions, and usernames. After the auction is completed, but before feedback can be provided, Tradera automatically reveals the real names and home addresses of the seller and buyer to each other.
A multidimensional model of online anonymity
Studying our two cases has showed us that online anonymity cannot be placed on a single scale but should be understood as a multileveled phenomenon consisting of three regulating structures – legal, commercial, and technological on a macro and – identity bearing information conveyed in three main forms; by factual information, social group membership, and embodied expressions on micro/meso level. Figure 1 illustrates the conceptual model of online anonymities where these structures and facets are inter-linked. In the following sections, through our two cases, we detail the structures and facets.
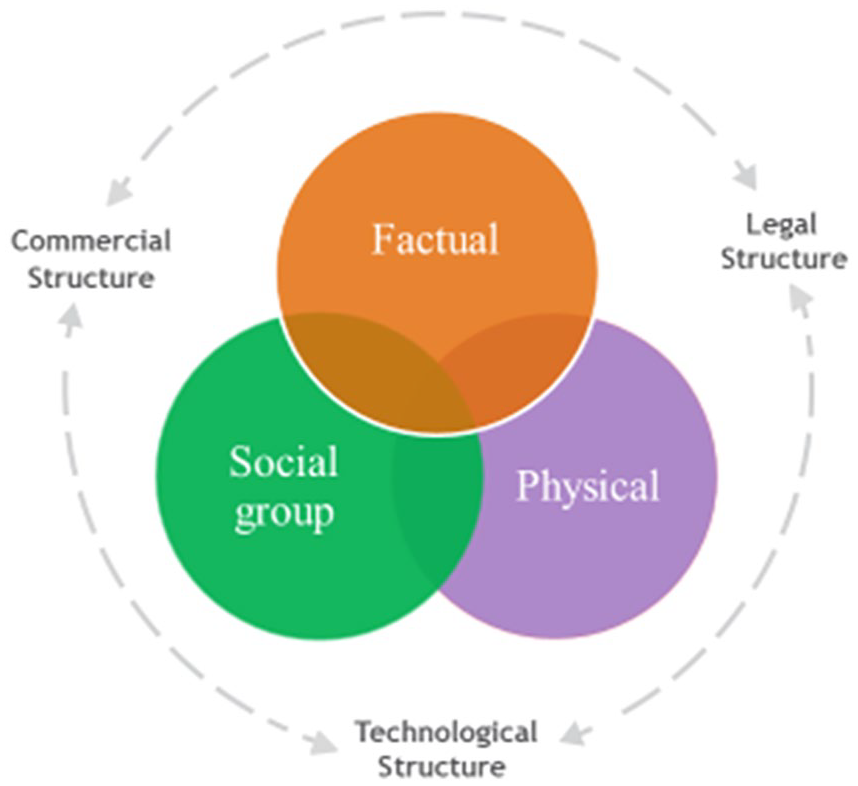
The conceptual model of online anonymity: a visual representation showing three structures and three facets, all dependent and changeable over time.
Legal structure
National and international legal systems usually treat anonymity as a mean to protect personal identity. There exists no single legal concept of anonymity; it differs between sectors as well as countries. In both democratic and totalitarian states accountability has recently been targeted in legal changes (Froomkin, 2017). Today governments issue control online to a large extent through chokepoint regulations, that is, targeting intermediaries, such as Internet Service Providers, requiring for example, retention and transmission of data that can identify users. According to the seminal work by Benkler (2006), this type of policy is effective because it takes into account that the Internet depends on networks – the largest social network services and search engines thus become the target of these chokepoint regulations.
The TOS (terms of service) of Tradera explicitly states that users are subject to Swedish and European commercial laws of buying and selling. Tradera requires a social security number connected to each account; it is thus not possible to create a new account to clean one’s reputation. The requirement thus enhances accountability. Social security numbers in Sweden (like other Nordic countries) is a unique number of an individual, akin to but not the same as in, for example, the U.S. The number directly reveals the birth date and gender, and the number is used in all official and many private interactions. The Swedish law is thus a framework guiding Tradera’s possibility to collect identifying information of users. For example, the extent to which credit information can be collected is stipulated by law, while collecting, for example, navigation information is less regulated.
When it comes to online gaming, there is less legal regulation. Laws mainly come into play in regulating the use of private data. The information Blizzard and Tradera gather is controlled by the EU wide GDPR (2016/679) regulation; which determines what can and cannot be done with personal data. Both state and intra-state laws frame how end-users reveal their identities on both Tradera and in World of Warcraft. Both companies require users to give up personally identifying information in order to access their services, yet legal structures determine which data the companies can ask for and how they can treat these data.
Commercial structure
Regulations of anonymity online also stem from commercial structures (e.g. Acquisti et al., 2015) and the Internet is increasingly dominated by commercial interests. EULAs (end user licence agreements) and TOS (Terms of Service) specify under what conditions end-users can use a software or service. Users often accept without reading or understanding these agreements (Obar & Oeldorf-Hirsch, 2018). Many EULAs/TOS give the right to the software owner to alter, use, and share content individuals create, including photos and location. Information on individual behaviour has become a valuable economic asset for both public and commercial purposes (Spiekermann et al., 2015). Identifying customers directly or indirectly through personal information can ease billing or is seen as a way to prevent toxic behaviour. For example, Facebook users are required to use real names and many news sites and blogs require identification through a Facebook account to comment and take part in public debate.
On Tradera, the EULA and privacy policy details how Paypal use and collect private information. By accepting the EULA, users agree that the site can re-use every piece of information the user place/create on the platform. The commercial structure thus specifies the borders of the user’s discretion of anonymity vis-à-vis others, for example, Tradera retains the right to disclose all personal information about a user in their EULA. However, Tradera’s EULA currently gives buyers and sellers some discretion regarding how to be anonymous towards each other.
In WoW players sign a EULA with Blizzard regulating what the player can do with/in the software they have purchased. This contains specific information detailing how players may or may not be anonymous, for example, Blizzard requires all users to be ‘natural persons’ and create an account, submitting their name, address, and e-mail. In addition, for most, playing means registering a credit card with Blizzard to pay the monthly fee. Registering a credit card and creating an account means to surrender your identity to the company, who via this information can link players across games and in-game characters, something other players are not able to do. The EULA also specifies that Blizzard can gather IP-addresses and non-personal user data. The EULA thus regulates to what extent and in what way users must reveal their identity and identity-related information vis-à-vis the company.
Without understanding the consequences of the future downstream uses of personal data, it is impossible for users to weigh the costs and benefits of directly or indirectly revealing their identity by sharing this type of information, the only real option being refraining from using a service. An example is the Facebook data held and used by Cambridge Analytica in the 2016 US election, which highlights how difficult it is for individuals to anticipate how their data might be used. However, although the commercial structures guide user’s anonymity, users engage in resisting commercial interests, as well as laws, by for example, installing ad-blockers, using private browsing, or VPN tunnels.
Technological structure
We recognise the technological structure as the software and hardware of the Internet and applications, which allows computer-mediated interactions. It is in part both the conventionalised set of principles and values, and the development of architecture and applications enabling and limiting programmers in developing and designing user spaces as well as new technology (Lessig, 2006).
How applications enable anonymity for individual users is much in the hands of programmers and firms who develop them. In WoW, Blizzard attempted to implement a so-called real identity system on their forums in 2010. The real-id system is an optional feature in Blizzards cross-game identification system. Here players who so wish can connect their various game personas to one account that have their real name. The proposed change on the forums would have made it impossible to post without submitting one’s real name and verifying it. This design change shows that how platforms are designed affect how people can be anonymous. In the end, this change was never implemented due to massive negative feedback from the player community (Albrechtslund, 2011).
At Tradera, during an auction, reputational feedback and geographical location is the only information the platform forces the users to share between them. Users have control over the extent of identity information the username signals. Users thus have some discretion on anonymity in relation to each other. However, when an auction has ended, Tradera automatically sends an email to the winning bidder and the seller revealing their respective real names and home addresses. This feature shapes the way anonymity plays out between users. The technical structure guide how the Internet works and in contribution to platform design lay the ground for how users can shape their and other users’ anonymity online.
Summing up structures
Our three suggested structures – legal, commercial, and technological – dependently afford many interactions and behaviours in our two cases. Foremost, commercial interests in WoW intersect with how the architecture of the game is designed. As we saw in the Real ID case, however, these types of structures are not fixed but constantly change and evolve due to the actions of many different types of stakeholders. Tradera abides by Swedish and EU laws, yet the borders of the laws are used in the EULA to enable Tradera to store and use personal identifying information. Anonymity between end-users is, to a large extent, shaped by the technological structure of the platform. These macro-level structures shape opportunities for end-users and their possible expressions of anonymity.
The dependency between the structures, illustrated by the dotted arrows in Figure 1, can further be exemplified by Larsson et al.'s, (2012) research where legal structures spurred development of new technology for circumventing the law. They found that the more restrictions on anonymity, the larger the call for technical solutions for being anonymous online within the file-sharing community (Larsson et al., 2012). The technical structure provides ways for how governments can regulate the Internet and how companies can build products for it, but laws, business interests, and uses feed back into how the Internet’s structure evolves. The structures thus change in response to use and subversion (Kennedy et al., 2016). In our two case studies, we see different power dynamics in play, with stricter legal control over buying and selling than online gaming. Figure 2 illustrate how the different structures can be leveraged in understanding anonymity in these cases. However, for individuals, laws might be less visible than the designed structure of the platforms in question. However, a common thread in our research suggests that embedded in the structures are facets of anonymity that to varying degree guide interactions between users.
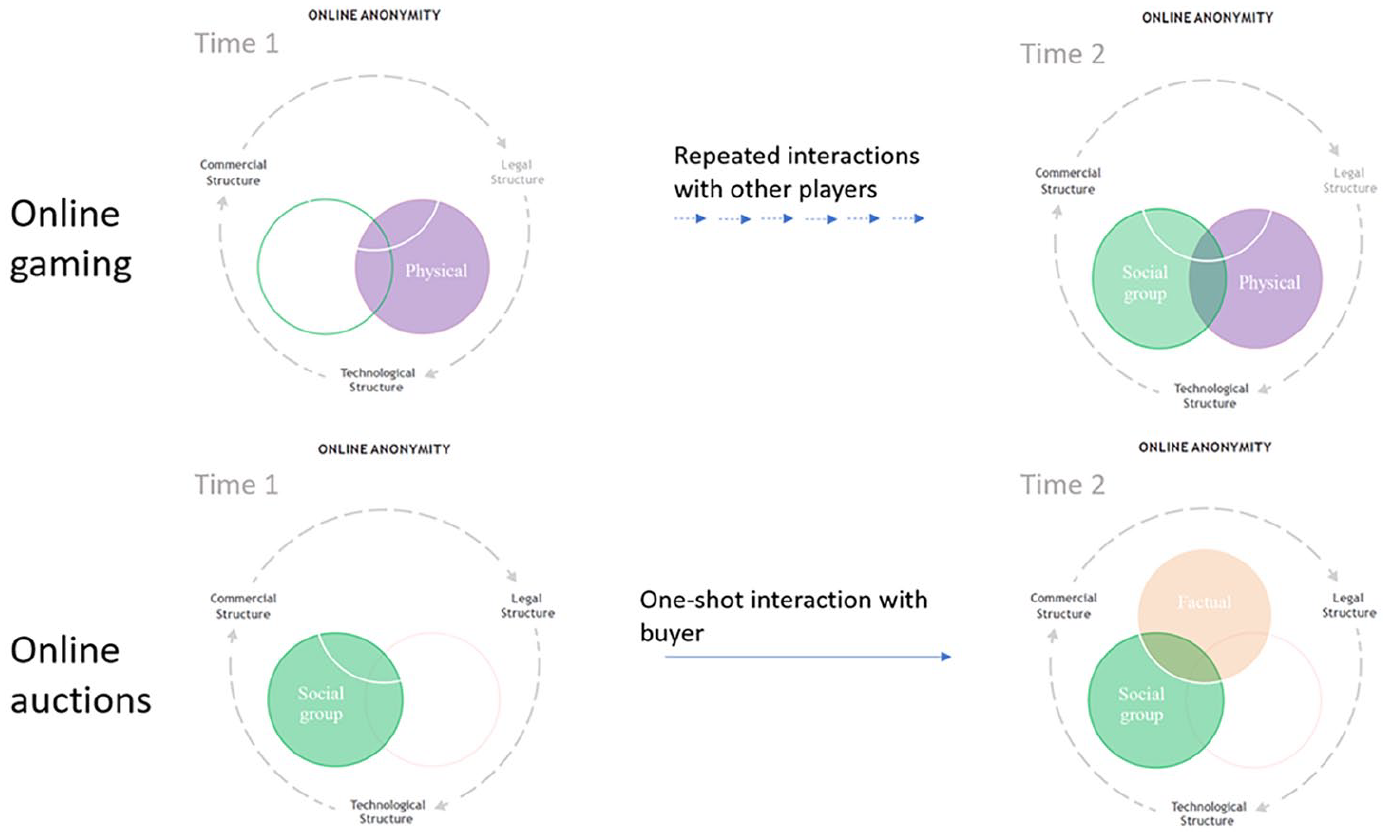
Adapted conceptual model of online anonymity highlighting leveraged structures and facets for our two empirical cases at two time points.
Facets of anonymity
We have come to understand online anonymity as a multidimensional assembly of facets on a micro/meso level, shaped by macro-level structures. This represents a perspective where anonymity online is constructed by and embedded within social, physical, and technological experiences, relationships, implementations, and services. Analytically, the facets can be studied separately, although many aspects of them overlap in concrete uses.
Factual anonymity
Factual anonymity pertains to traceable information about individuals, that is, surname, first name, social security number, et cetera. It can also include digital identifiers such as IP-address and other quasi-identifiers, which together indicate a legal person. Factual anonymity is how anonymity, often, has been defined and measured (see Marx, 1999; Pinsonneault and Heppel, 1997). As detailed above, we have seen a shift towards less factual anonymity online, that is, requirements of traceable information on behalf of platforms. A centralisation of actors, such as Facebook, used for authenticating oneself on other sites contributes to this development.
In online games and auctions, pseudonyms are still the norm, although users, as detailed above, are not always factually anonymous vís-a-vís platforms. However, as shown in the example of the real-ID for WoW, the idea of the real name Internet is moving into gaming as well. The argument is that real names promote less toxic behaviours between players (Albrechtslund, 2011), although we are aware of no systematic review which has investigated the available research on the topic, our impression is that the vast amounts of research have at best drawn mixed conclusions.
On Tradera, users are factually known to the platform, as they are required to provide their social security number. However, between users, the sellers and bidders can at the initial stage chose what factual information to provide when shaping their usernames, geographical location, or account description. After a successful auction, to manage payment and shipment of gods Tradera reveals, through e-mail, the seller and buyer’s real names and addresses, making them factually known to each other.
In online gaming, as on Tradera, users are not factually anonymous to the platform but have a high degree of influence over how much of their factual information is shared between players. Being able to choose how much of their factual identities are known to other players is seen as an important right (see Albrechtslund, 2011).
Besides collecting and storing social security numbers, Tradera collects a series of factual pieces of information on their users, such as IP-address, and sometimes information from third parties, such as credit details, allowed by users signing the EULA. The amount of data collected prevents users from being factually anonymous vis-à-vis the platform and third parties. Similarly, Blizzard explicitly states that players must provide accurate and up-to date personal information and further that they allow third parties to collect information such as IP-addresses for advertisement purposes.
Acquisti et al. (2015) has discussed this uncertainty regarding the consequences of this type of data collection – usually, the data holder knows more about the collection and usage of data than the sharing individual, and this is surely true in both our cases. All information individuals reveal online can be used to trace a person’s legal identity. It is thus possible for private and public entities to identify individuals without explicitly asking for their identification. This development has further complicated the boundary between the private and public person (Stalder, 2002). Expectations of anonymity play a role here; identity might be easily traceable for someone with the necessary skills, yet individuals often believe that they are factually anonymous across time and space (Skopek, 2015).
Factual anonymity thus pertains to information about individuals (and other entities) linked to them as legal entities and in our two cases we see how users both are and are not factually known on the same sites, at the same time, depending on if we look at it from the platform owners’ or users’ perspectives. This means that measuring whether someone is (factually) anonymous or not in a specific moment in time, depends on towards whom we are anonymous.
Social group anonymity
We know from studies on online life that there are different expectations put on individuals labelled or identifying as female, male, black, white, straight, gay, etcetera (Kendall, 1998; Nakamura, 2002; Turkle, 1995). Even when users are factually anonymous, personal characteristics, signalling group identity, such as gender, race, and sexuality matters. How users express themselves in text or pictures when interacting with other users can become social disclosure.
When having a choice, not revealing aspects of one’s social identity is sometimes used as a strategy to avoid sexual harassment or discrimination based on gender stereotypes (Eklund, 2011). However, in the case of Tradera, we have seen in our work that choosing to hide one’s social identity initially, in a competitive market, can lead to discrimination in reputational feedback from sellers with stereotypical perceptions of social identities, since Tradera automatically revels the social group identity between sellers and buyers by providing the factual information of real names after a completed auction (Von Essen and Karlsson, 2019). In contrast, selection by identity can be used to form safe spaces, such as gender separatist discussion forums which can be seen as a strategy to handle negative aspects of online life by users being factual anonymous but simultaneously sharing specific identity cues, such as gender (Clark-Parsons, 2018). In online games, it is clear that social identities are key. In our studies, we have seen how offline identities such as gender, ethnicity, language, and so on shape online social life; offline similarities, contribute to players ‘feeling like they knew each other’ (Eklund, 2015). Even when not sharing real names, shared social identities on multiple levels such as being students, living close by in the physical world, talking the same language and so on contributed to players forging bonds to one another, specifically because they felt like they knew something about who the other person was while still being factually anonymous.
Our cases highlight that social identities matter for how we are known online. Traditional social group belongings shape how we act towards each other. In this light, the classic online chat question, ASL(R/P)? (age/sex/location, race/picture) speaks to user’s desire to fix their interactional partners along social identity lines. Note that real name is not among these questions. Users of anonymous platforms seem driven to constantly engage in processes of de-anonymization, in other words, they want to know who they are interacting with (see Sharon and John, 2018). Playing an online game together or selling things on online auctions under a handle, an individual can nonetheless reveal key social identity features – willingly or unwillingly – which will tell others about who we are; which in turn affect interaction between users.
Social group anonymity thus pertains to individual’s social identities and how much of these become explicit or implicitly known/not known to interactional partners. In both our cases of online auctions and online gaming, time moves users from a state where other users might know very little, to more being known. In online gaming, it is because we get to know each other as we play together. While in the case of Tradera, it is the design of the platform which forces disclosure on users. Key for us, is how factual and social anonymity does not map perfectly onto each other, even though there is obvious overlap. Users can, for example, be factually anonymous while socially known. These social cues revealed in online interactions are, however, also key in targeted advertisement online. By using social identity information as proxies, commercial actors model consumer preferences for commercial purposes. Here, the socially negotiated becomes factual information.
Physical anonymity
Physical anonymity pertains to how our bodies and emotions offer social affordances for interaction online. They are resources for social interaction that, in a sense, tell people about who we are. Users can also draw on embodied resources in order to appear as credible individuals online and to get to know people and be known in turn.
Social psychology studies have repeatedly shown how body language affects our interpretation of messages (Duclos et al., 1989), for example, smiling might make something funnier (Strack et al., 1988). The lack of such embodied resources has been considered a chief factor behind online disinhibition (Lapidot-Lefler and Barak, 2012) as well as the closely related concept deindividuation (Potmes and Spears, 1998): a lack of restraint manifested in various behavioural patterns, such as impulsivity and disregard of others, and often referred to as a mechanism behind online harassment. However, in many online contexts, users draw on a wide array of embodied resources in interaction that signals identity and credibility.
At Tradera, sellers can use pictures to display their product or an elaborate text description to increase their chances of selling. In various markets, such as clothes, portraying the product on an actual body might signal information on the usability of the product, and thus credibility. The body can increase social presence by revealing that a seller is an actual person (Short et al., 1976). The picture also reveals social cues, such as gender, that the bidder might ascribe to the seller, which on bidding sites can lead to discrimination in sale price (Doleac and Stein, 2013).
Although online spaces are limited in terms of bodily smells, facial expressions, and voice, socio-technological services offer ways for embodied interactions. Images are commonly used in dating apps and using an unrepresentative picture is often seen as lying about one’s identity. Other examples are virtual bodies in the forms of graphical avatars, which users draw on and embed aspects of themselves in. Creating an avatar in WoW can be a highly personal and conscious process in which players embed the avatar with meaning reflecting their perceived identity. There is a wealth of research exploring the intensely personal relationships game-players have with their own and their friend’s avatars, who sometimes are treated as extensions of one’s self (e.g. Boudreau, 2012). Violations of avatar integrity have also been shown to sometimes be felt as akin to violations of one’s physical body (see Sundén, 2010).
Another strand of research on embodied resources online deals with the display of emotions. Emotions are contextual physical and mental expressions that enter every aspect of human life. The lack of emotional cues online is a well-known communicative problem and concretised in the prevalent use of emoticons to augment meaning in textual interaction (Rezabek and Cochenour, 1998). Studies increasingly show how emotions matter online (Malmqvist, 2015). Appropriate emotional reactions for the space and action in question contributes in making users appear as credible individuals towards others. At Tradera bidders should enter the bid representing the maximum value they desire to pay for a goods and under standard economic assumptions, the bidders should not consider the value that another bidder places on the same item. Empirically it is, however, well known that there is a substantial share of emotional reactive bidders, that for example places last-minute bids (Anwar et al., 2006).
In online gaming, shared emotional experiences can lead to feelings of kinship (Eklund, 2015). Sharing intense emotional experiences when you win and lose while playing is one of the bases for how players create bonds with each other, a shared history and feelings of affinity.
Physical anonymity thus pertains to embodied resources – displayed through visuals, audio, interaction, etcetera – in online communication and how much of these individuals draw on and display – consciously or unconsciously – to interactional partners.
Summing up facets of anonymity
Factual anonymity is how we often see anonymity defined on the micro-level of user interaction online, yet it seems clear that this is just one facet of what it means to be known and unknown online. Factual anonymity might be key when users interact with platform owners, yet many subtler social cues also disclose ‘whom we are’ even if disconnected from our legal name. We expect all facets to interlink at some point, and this is especially clear in that legal names and pictures often contain social group identifiers. In Figure 1 this is illustrated by the over-lap of these facets in the central diagram. While the myth of the disembodied Internet is still a common understanding of online life, increasing evidence rather points to how bodies, including emotions, are communicative resources online, both their presence and their absence. When we interact online, various ways of communicating will be more or less rich, and communicative cues expressed in interaction can be, willingly or unwillingly, shared via text, voice, or visuals.
In our cases, focusing on interactions between users, different structures and facets came to matter for our understanding of interaction in these spaces. As we have detailed above, in WoW legal regulations matters much less than the commercial and technological structures, design changes have far reaching consequences for individuals’ opportunities to engage together. Factual identities are not primarily significant for the relationships people build in the game, instead social group belongings as well as embodied practices are central as players interact over time. As a player began playing, social group identities were not yet known to others but required repeated interaction over time. On Tradera, all three structures matters to understand how users could/could not be anonymous in the space. We studied buying and selling of cinema tickets and here physical aspects came to be less important in understanding what was going on, as a critical event occurred – a completed auction between one buyer and one seller. Figure 2 illustrate how different structures and facets were leveraged in understanding anonymity in these cases, and how these changed over time. Structures and facets affect each other as people interact and context shape their interrelated importance.
Discussion
Through our two cases, we have explored how legal, commercial, and technological macro-level structures shape factual, social group, and embodied micro/meso-level facets of online anonymity. All of these or only one dimension at a time change the opportunity for or nature of online anonymity, as shown in the examples from our two cases in Figure 2. In practice, neither structures nor facets stand on their own but constitute parts of the whole of online anonymity. In addition, time matters as users move between various states of anonymity at various time points and in different venues and social groups online. As is the case for both online gaming and online auctions.
Seeing anonymity in this light focuses on the relationships between actors, rather than the state of actors; in other words, anonymity as a relational process (see Emirbayer, 1997). This allows us to understand anonymity not as a state, but as a process, further dependent on subjective interpretation of social situations. Anonymity is made and remade in social interaction. However, we do not argue for a pure process-based approach. Rather, we see structures as creating bases for a process to take place (Ahrne and Sundberg, 2007). Thus, our proposed structures provide material necessities that allow certain ways of doing anonymity on a micro-level. Our approach thus draws on both substance and process. Moreover, it might indeed matter more whether I perceive myself as anonymous than whether I actually am anonymous (see also Kennedy, 2006). There is thus both an objective and subjective quality to online anonymity.
Online anonymity is dependent on the platform we use, on our interactions with this platform and other users/agents, as well as the legal system we reside in, it is thus situated as well as relational. Online anonymity thus comes to be in the relationships between ourselves, other users, platforms, and other potential agents. The visual model in Figure 1 illustrates this point.
We believe that this way of looking at anonymity, understood in a multidimensional sense has the potential to guide research forward on social aspects of online life. We invite researchers to remix and reuse the model to suit their own empirical research and fields. We hope that thinking about anonymity in this multilevel way means that researchers can state which aspect of anonymity they are studying, in order for others to situate the research and relate it to studies before and after. As we have attempted in Figure 2. We need to find ways of talking about anonymity in our research that can be drawn on, compared to, and built on by others.
Conclusion
In this essay, the traditional way of defining anonymity as being nameless has been shown to be insufficient when talking about anonymity in our two case studies of online auctions and online gaming, due to the multilevel nature of online interactions. Instead, we have shown that we should talk about anonymities in plural form, as online anonymity is not a state but processes along factual, social, and physical lines, across time, guided by structures on a legal and commercial scale, and by network technologies, which relies heavily on perceptions and interpretations on the micro-level of being anonymous. We thus define anonymity as a combination of anonymity facets, factual, social, and physical, afforded by technological, legal, and commercial structures.
This interdisciplinary article has argued for a relational understanding of anonymity online and puts forth a multi-dimensional model. Our conceptual model unpacks online anonymity as a combination of macro and micro/meso factors: factual, social, and physical facets shaped by structures. We want to stress that anonymity on the Internet is as complex and multifaceted as our identities and with this study, and through our conceptual model we want to facilitate researchers from all disciplines to treat it as such.
Supplemental Material
sj-pdf-1-sro-10.1177_13607804211019760 – Supplemental material for Beyond a Dichotomous Understanding of Online Anonymity: Bridging the Macro and Micro Level
Supplemental material, sj-pdf-1-sro-10.1177_13607804211019760 for Beyond a Dichotomous Understanding of Online Anonymity: Bridging the Macro and Micro Level by Lina Eklund, Emma von Essen, Fatima Jonsson and Magnus Johansson in Sociological Research Online
Footnotes
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research was funded by The Swedish Research Council, project number 2013-01789.
Supplemental material
Supplemental material for this article is available online.
Author biographies
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
