Abstract
Hackathons are techno-creative events during which participants get together in a physical location. They may be hosted by civic communities, corporations or public institutions. Working individually or in teams, usually for several days, participants develop projects such as hardware or software prototypes. Based on a digital ethnography of two events in the Netherlands and Denmark, this article investigates project development practices at hackathons. In particular, it analyses how participants organized their project work and which technologies were used in support of their creative endeavours. Hackathons are increasingly competitive rather than collaborative events, involving time pressure, inducements such as prizes, and requiring efficient skills utilization. I argue that this facilitates the following tendencies: Firstly, strategic effort is put into final presentations. Projects need to be convincingly presented, and persuasively pitching an idea becomes crucial. Secondly, there is only limited time for personal learning, since participants’ existing skills need to be efficiently applied if a team wants to stay competitive. This encourages division of labour within groups: a tendency which seems especially problematic given that IT skills biases are often expressed in terms of gender. Thirdly, participants are more inclined to use technologies that are proprietary but appear ‘open enough’. In light of this observation and by drawing on the concept of
Keywords
Introduction
During the OpenBSD hackathon in 1999, a group of volunteer programmers got together at a venue in Calgary, Canada. For 1 week, they joined forces and worked on an open-source operating system (see OpenBSD, n.d.). The event was based on practices of collaborative software development that were already common in developer communities back then. However, for the first time, the term ‘hackathon’ was used to describe such a meeting. What started in the context of an open-source project was soon discovered by companies. Later in the year 1999, Sun Microsystems hosted a hackathon dedicated to the digital assistant Palm-V. By now, all kinds of hac[king-mar]athons tap into the innovation capacity of collaborative programming and prototyping (see e.g. Goggins et al., 2014; Kaltenbrunner and Echtler, 2014; Quilez and Pol, 2014).
During hackathons, participants meet in physical public or private spaces in order to create software and/or hardware prototypes. They receive catering and might even stay overnight, since these events usually take several days. Nowadays, there are still hackathons organized by non-profit communities or foundations aimed at the development of technologies for the common good. Such rather socially oriented objectives apply for instance to the 2013 GNU’s hackathon for the 30th anniversary of the free software operation system. 1 At the same time, such events are increasingly common in commercial settings, for example hosted by companies looking for a technological solution to an in-house problem or trying to trigger employees’ creativity (see Rosell et al., 2014). An example are the regular Facebook hackathons, organized since 2004, with which the company states to give ‘[…] our employees the opportunity to try out new ideas and collaborate with other people in a fun environment’. 2 This popularization of hackathons has created discrepancies and frictions, as pointed out by Briscoe and Mulligan (2014: 4), ‘[M]any hackathons have benefited from professional organisation, utilising corporate sponsorships and investor-participation. However, this has occurred in some instances with tensions due to the socially orientated innovation often prevalent in earlier hackathons’.
The authors describe how monetary benefits have been perceived as contradictory to the values relevant to hackathons which emphasized intrinsic, philanthropic motivations. While Briscoe and Mulligan accurately highlight the existence of tensions between different types of hackathons, it remains to be explored how competitive (monetary) inducements and the involvement of sponsors may influence hackathons ‘on the ground’. Therefore, this article will empirically explore how project development practices at hackathons have developed in increasingly professionalized contexts.
Trainer et al. (2016: 8) provide insights into the socio-technical trade-offs of hackathons, suggesting that during their involvement participants negotiate ‘[…] between advancing technical work and building social ties’. Critical reflections on this issue have also been voiced by hackathon participants themselves. In a We worked on whatever we felt like, asked each other about our projects, helped debug things when we got stuck. Everyone was there for the joy of building things with technology. Nobody cared about anything else. Later on, the CSUA [
Approach and main aims
Methodologically, this article is based on digital ethnography, involving participant as well as non-participant observations and interviews during two hackathons. I will elaborate on this approach further below. The analysis presents insights from a Strategic effort is put into persuasive presentations; the idea needs to be convincing, but the technological implementation not necessarily completely functional. There is only limited time for personal learning and development of new skills, since participants’ expertise needs to be efficiently applied. This is particularly problematic, since different skills (levels) at hackathons are often expressed in terms of gender – also due to a general gender bias in IT domains. Technology choices and their utilization are approached pragmatically: Participants are inclined to use technologies that are proprietary rather than open source but appear ‘open enough’.
In light of the latter argument, it is important to stress that utilized technologies may enforce technological (in-)dependencies and signify particular values regarding production, technological transparency and information freedom. The following section will therefore first reflect on the significance of techno-political implications more generally. It will do so by drawing particularly on Postigo’s concept of
With this analysis, I aim at contributing to the critical debate on hackathons as productive, but likewise ideologically significant fields of hacking cultures. Authors such as Irani (2015: 801) have already thoroughly analysed how hackathons encourage and produce ‘entrepreneurial subjects’: the author illustrates how a hackathon in India ‘[…] rehearses an entrepreneurial citizenship celebrated in transnational cultures that orient toward Silicon Valley for models of social change’ . Similarly, Gregg (2015) suggests that ‘[h]ackathons enable aspiring professionals to demonstrate technical skills and immaterial qualities of employability’. These authors critically analyse selected hacking events and their implications for created subject positions. However, they pay less attention to the development that hackathons are no longer platforms where only equally qualified professionals or students meet. Neither are the motivations to join a hackathon always to be found in networking with peers, for instance. Instead, the popularization of hackathons has also facilitated a moderately increased heterogeneity of participants. While one may argue – as Nandi and Mandernach (2016) do – that hackathons
Technology as resource and opportunity
Participants’ technology choices at hackathons seem particularly relevant since the utilized tools are by no means neutral but have techno-political implications. Postigo suggests (2012: 177) that technology may function as
As Postigo (2012: 8) points out with regard to, for instance, technologies circumventing copy protection:
Hacking cultures: FOSS/free and open-source hardware
Hacking cultures are strongly related to (often even identical with) communities concerned with the development of Free and open-source software (FOSS) (Coleman, 2004, 2009, 2012; Himanen, 2010; Jordan, 2008, 2016; Lin, 2007; Nissenbaum, 2004; Söderberg, 2008). The historical evolution of the open-source movement (OSM) ‘[…] can be traced back to the “hacker culture” that created Unix, Linux, and parts of the Internet infrastructure’ (Zhao and Elbaum, 2003, 66; see also Bergquist et al., 2011; Hippel and Krogh, 2003; Kelty, 2008). Open source as production and development model ensures that anyone may have unrestricted access to a product’s structure, blueprint, and design. The open-source model can be applied to a wide range of sectors (see Kogut and Metiu, 2001; McLellan et al., 2012; O’Boyle, 2011). In the context of software, open source implies that the source code of a programme is accessible to the public, can be used and modified. 4 The possibility of its commercial reuse is a condition for being acknowledged as open-source software.
The notion of open-source hardware (OSH) transfers the open-source software concept to material technology and components (on open-source appropriate technology, see Pearce, 2012; Powell, 2012). It refers to hardware which is provided with detailed information allowing for reproduction and further development of a material device. Originally, the emergence of OSH is related to the Open Design Foundation. 5 The concept extends the idea of detailed documentation of programming processes to the documentation of hardware development. The aim is to allow for hardware reproduction from scratch. Hardware design may be documented by mechanical drawings, providing the integrated (graphic) circuit layout. In this sense, OSH is a systematic continuation of the open-source software ideas. The licenses used for OSH are often derived from OSS licences; they are however closer connected to patent law rather than copyright law.
Hacker values
Historically, the OSM is a spin-off of the free software movement (FSM). Both share the basic assumption that access to the source code is ‘beneficial’ (see also Coleman, 2004; Söderberg, 2008). However, they do so for different reasons. The FSM stresses altruistic motives; the OSM highlights practical advantages: ‘[F]ree software bases its activity on the argument that sharing code is a moral obligation and open source bases its activity on a pragmatic argument that sharing code produces better software’ (Yeats, 2007: 13). The FSM suggests that the freedom to access, understand and modify software is a societal right which is infringed by proprietary (closed-source) software. In this sense, proprietary software inhibits citizens’ individual and communal possibilities for learning, sharing and intellectual development (Stallman, 2007). Despite these differences, in the sense of Postigo’s notion of
Going back to the hacker ethic, depicted by Levy in 1984, ‘[h]ackers believe that essential lessons can be learned about the systems – about the world – from taking things apart, seeing how they work, and using this knowledge to create new and even more interesting things’ (Levy, 1996 [1984]). The author explains the need for non-proprietary, open systems, ‘If you don’t have access to the information you need to improve things, how can you fix them? […] The best way to promote this free exchange of information is to have an open system’ (Levy, 1996 [1984]). Yet, as Coleman and Golub (2008: 255) remark with reference to Elias Ladopoulos (Acid Phreak, 1990), there is no [T]he FSF [Free Software Foundation] was never the only game in town. There was always a quieter, less confrontational and more market-friendly strain in the hacker culture. The pragmatists were loyal not so much to an ideology as to a group of engineering traditions founded on early open-source efforts which predated the FSF. (Raymond, 2005)
Early hackathons and topical literature
While the term ‘hacking’ has been used in developer contexts since the 1960s, it was only in the late 1990s that the term hackathon emerged. It is beyond the scope of this article to provide an overview of the different historical (communal, corporate or institutional) contexts and related motives for which this notion was appropriated. It would likewise be interesting to investigate how the term simply labelled and reframed long-existing types of developer events. Drawing on Foucault, Jordan highlights with regard to hacking culture that one should avoid writing ‘history from the point of view of either the “now”, seeing past events as significant only if they lead to our present state, or in a closely related way, the “victor”’ (2016: 2). While this is likewise true for hackathons, a ‘genealogy’ of these hacking events would require more than a sub-section in this article. What I am therefore presenting in the following sections is by no means a complete overview of hackathons’ various manifestations and phases. Instead, the following reflections are merely meant to provide insights into developments that are particularly relevant for understanding the background and tensions regarding the investigated hackathons.
The term itself was originally used as metaphor for early firewall testing, ‘Too often a firewall test is viewed as a kind of “hackathon”. Organizations may authorize someone to conduct the testing, but this person may “disappear behind a black curtain”’ (Moyer and Schultz, 1996: 12). With regard to activities involving collaborative programming and software development, hackathon was first prominently used in 1999. According to OpenBSD, the term was coined for their event taking place on 4–6 June 1999, ‘In the months leading up to this, either Theo or Niels Provos had coined this new word “hackathon”’ (OpenBSD, n.d.). Only a few weeks later, in September 1999, another pioneer hackathon took place in San Francisco. It was part of a JavaOne conference (Aviram, 1999) and called ‘The Hackathon’. This illustrates how the coining of the term was subject to claims and negotiations.
In the Sun hackathon, participants were framed as competitors. They were asked to write a programme in Java for the personal digital assistant Palm-V (released in February 1999) and were competing for monetary prizes. In contrast, the idea behind the OpenBSD hackathon was that developers would work collaboratively towards a common goal. The latter event was open to invited participants only. While the Sun hackathon took place in a commercial context, the OpenBSD hackathon was part of a community insisting on uncompromised open-source code and software licensing. These early hackathons already illustrate crucial differences between contemporary events: Some hackathons are conceptualized as collaborative, temporary think tanks working on ideas that are supposed to contribute to the common good. Others are used as fruitful breeding ground for commercially promising prototypes: ‘During the 2000s hackathons became significantly more widespread, and began to be increasingly viewed by companies and venture capitalists as an approach to quickly develop new software technologies, and to locate new areas for innovation and funding’ (Briscoe and Mulligan, 2014: 4). In such hackathons, subgroups or individual participants usually compete with each other rather than collaborating on a common project. Meanwhile, hackathons are indeed frequently suggested as problem-solving tools for various issues (Aungst, 2015; Johnson and Robinson, 2014; Munro, 2015). This perspective seems however rather simplistic and has been criticized (Irani, 2015; Porway, 2013).
Briscoe and Mulligan suggest differentiating between tech-centric and focus-centric hackathons. ‘Tech-centric’ refers to events focusing on software development using a specific technology or application; ‘focus-centric’ hackathons require participants to address societal issues or business objectives (see Briscoe and Mulligan, 2014: 5ff.). Regarding the projects developed at these events and the kinds of interaction taking place, one needs to take into account that many hackathons are predominantly frequented by male participants. A more extensive investigation focused on gendered innovation and hackathons as often male dominated domains – related to the programming communities they address (Adam, 2003; Jordan and Taylor, 2004: 116ff.) – would therefore be insightful. I will come back to this important point, but it is not the main focus of this article.
Digital ethnography as research approach
This study is based on the digital ethnography approach suggested by Pink et al. (2016; see also Underberg and Zorn, 2013). The authors introduce this qualitative approach as way to explore ‘[…] the digital-material environments that we inhabit and how human activity and the environments in which it takes place are co-constitutive’ (Pink et al., 2016: 152). Earlier methodological deliberations suggested for ethnographic research on digital practices, such as virtual ethnography (Gatson and Zwerink, 2004; Hine, 2000, 2008; Dominguez, Beaulieu and Estalella, 2007) or Internet ethnography (Miller and Slater, 2001), already referred to the relevance of physical practices and spaces for understanding digital/online activities. Pink et al. however particularly highlight the necessity to methodologically traverse between online and offline – just as the subjects of digital media research do. The authors emphasize that digital ethnography is in fact
In particular, this article was inspired by the chapter ‘Researching events’ (Pink et al., 2016: 147ff) aimed at ‘[…] understanding the digital, material, affective, and social relations of events’ (p. 152). As the authors stress, digital ethnography is not a static template which may be applied but rather needs to be individually developed. I have structured my analysis according to the three initially mentioned themes that I encountered during my observation and that highlight the connection between digital practices and physical conditions: relevance and implications of persuasive presentations, efficient skills utilizations and learning limitations and pragmatic technology choices and uses.
I focus on these aspects since they were recurring, dominant themes demonstrating the interplay between organizational decisions and participants’ project development practices. 6
My insights are derived from field research at two hackathons: a SHD in Eindhoven (30–31 August 2014) and
During the SHD, I did participant observation via having an active role in the hackathon. I was part of a group of seven people with whom I experienced the development process. Initially, 14 groups were working on competing projects during this hackathon, but not all groups stayed until the end of the event (eventually 12 projects were presented). I did informal interviews with 21 participants, 2 of them were female, and recorded interviews with the main organizer before and during this hackathon. For
With regard to methodological decisions and limitations, I would like to highlight the following three aspects: Firstly, after looking at possible field sites, I decided to select hackathons that were comparatively less commercial and took place in the context of non-profit institutions. Therefore, one should also acknowledge that these hackathons are often characterized by the best intentions and aims on side of the organizers. I chose not to include strictly corporate hackathons, since their aims, suggested data and technologies (soft- and hardware) are often predefined. At the same time, I also did not investigate hackathons that were set in (techno)politically idealistic contexts, for example, organized by free software communities. This thematic focus and the restriction to two cases imply that my observations merely open up the discussion and present a perspective on certain hackathons.
Secondly, due to the open nature of my methodological approach, I did not systematically gather exact demographic information on, for instance, participants’ age. While most participants were between 20 and 45 years old, I do acknowledge that more concrete demographics might be insightful. However, initial inquiries about participants’ age and background rather seemed to inhibit their willingness to engage in in-depth conversations. Thirdly, I chose the two approaches described above – being part of a developer team and being an observer – since I experienced during prior participation in hackathons that the active involvement gives me different access and insights into the digital tools used by participants. At the same time, this approach is very immersive and interviewing participants other than team members is often only possible during breaks. Moreover, during the SHD, participants might have been more hesitant to share their opinions and approaches, since they could have perceived me as member of a competing group. While I might have appeared like a ‘neutral’ external observer during
Case studies and analysis: Hackathon practices
The SHD in Eindhoven (GASlab, Eindhoven University of Technology) was organized by the Mad Emergent Art Centre. SHDs are a community-run hackathon type initiated in 2010. They focus on interdisciplinary innovation and prototyping broadly related to science. Participants at the event were mainly industrial and graphic designers, artists, programmers and software developers as well as engineers. Participants worked together in groups of 2–7 people, and a jury was invited to judge their projects. It consisted of creative industry practitioners and university researchers. Prizes up to €500 were given and assigned to themes. At the end of day 2, all project teams presented their ideas and the jury allocated the prizes, sponsored by companies such as Lumens Group and Endnote.
The
At the beginning of the hackathon, speakers posed practical problems, for example, concerning the conservation of art works or audience involvement and presented heritage data sets. Most projects had a strong relation to the issues posed during the initial talks, but participants were free to choose a topic and some worked on unrelated ideas. Similar to the SHD, many participants had a professional background as programmers/developers, engineers, designers, tech-journalists or artists; only a few of them were related to open-source/open knowledge initiatives such as Wikimedia or Open Street Map. Participants received rather ‘symbolic’ prizes such as books and shirts for their projects. Moreover, the winning project was chosen based on a public vote among the participants. However, the event was used as networking platform: by pitching their ideas, some participants were hoping to receive job assignments, since this had happened after
Relevance and implications of persuasive presentations
My first argument is that in (even mildly) competitive hackathons, strategic effort is put into persuasive presentations. The project idea needs to be convincingly presented, while the technological implementation does not necessarily have to be completely functional.
Already the spatial setup of

Hack4DK at the Statens Museum for Kunst.
Trainer et al. (2016) differentiate between four project development phases at hackathons: (1) group
It might seem counter-intuitive to start my analysis with this aspect of hackathons, given that presentations are usually the concluding part of a hackathon. However, one has to be aware that the responsibility for preparing a presentation is often determined by groups at the very beginning. This condition is particularly relevant for my second argument on skills development and learning.
Content-wise, particularly projects’ societal relevance and usefulness were important qualities. Participants extensively addressed in their presentations the purposes for which their projects could be used. For example, the group which I joined at the SHD developed a project called Connected Light. Technically, the team aimed at creating a device combining physical card gaming with virtual gaming. Its highlighted societal purpose was to allow elderly people to interact with a remote player without having to use a computer. Similarly, the project BatSense, also developed at SHD, aimed at creating a prototype for a device that translated a sensor’s visual ‘perceptions’ into vibrations, allowing a blind person, for instance, to acquire an artificial sense. Both projects won prizes – for Social Innovation and the Best Maker Trophy.
8
In the context of
Projects involving hardware development usually presented a partly functional prototype or illustrative mock-up/simulation. In contrast, participants’ programming efforts and the created code were rather invisible. Such an ‘invisibility of code’ might seem surprising, since programming was one of the main tasks at both events. Code sharing platforms such as
However, the actual code and the process of creating it were at best mentioned very briefly in the final project presentations at both hackathons. Process shot pictures (Figure 2) were included in the presentations, but participants did not show the code in detail. Illustrative representations of coding as practice were used in the sense of technology as resource: as images hinting at a project’s technical feasibility. In contrast, abstract, in-depth presentations of the code were avoided. This observation indicates that groups design their presentation in anticipation of a general audience and jury members – which also means that the overall idea pitch and feasibility arguments, rather than the software details, are decisive.
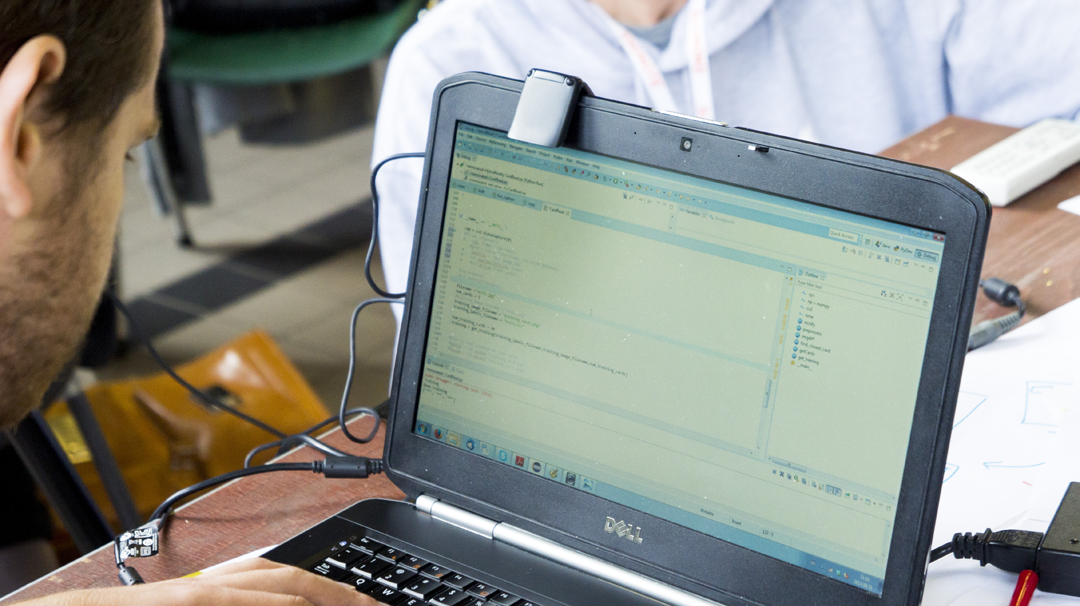
Process shot showing the coding for Connected Light.
Efficient skills utilizations and learning limitations
My second argument is that there is limited time for personal learning and development of new skills, since participants’ expertise needs to be efficiently applied. This is particularly problematic in cases where different skill sets or levels are expressed in terms of gender.
Within project development practices during both events, all teams tended to establish a distinctive division of labour at the start of their work. In light of time pressure and competitive setups, group members decided to take over tasks which required skills that they already possessed. This applied to the teams to whom I spoke to at
Regarding the aforementioned project development phases suggested by Trainer et al. (2016) –
Participants’ decisions to take over certain tasks were influenced by a sense of fairness, paired with the need for effectiveness […] social coding tools sometimes fell short is that not all participants were familiar with them, nor did they have the incentive to become familiar with them if they did not plan to use them beyond the hackathon. […] Less specialized tools seem particularly important when mixing groups that do not share a common tool set. (Trainer et al., 2016: 11)
This insight is particularly relevant for hackathon organizers who wish to encourage learning at their events. Likewise, it illustrates the need for critical studies regarding the learning potential, conditions and limitations of hackathons (see, for instance, Nandi and Mandernach, 2016). The described tendency is especially problematic, since different skills (levels) of hackathon participants are often gender specific. At both hackathons, female participants were less likely to engage in programming or hardware building. This issue is closely related to the IT sector and hacking communities being traditionally male-dominated domains (see, for instance, Lewis, 2015; Wajcman, 2007; Webster, 2014). In order to stay competitive, more technical tasks were taken over by participants who already possessed programming skills or hardware knowledge (e.g. see Figure 3). In many cases, female participants were responsible for design matters, in particular for creating and giving the presentation. If hackathons want to encourage participants to train in new or little developed skills and thereby contribute to addressing an existing gender bias in IT professions, organizers would need to provide incentives for personal skills development rather than foster an environment that privileges efficient skills utilization. The tendency to encourage efficiency has been countered, for example, with the recent phenomenon of […] a format inspired by participatory design approaches to creatively develop technology and a rejection of high-pressure, end-product-focused hackathon practices that reward speedy coding over effective problem solving. Rather than racing to complete or compete, the un-hackathon was about collaboration, brainstorming, and better understanding […]. (Bailey Hogarty et al., 2015)

Tweet published by the Danish Statens Museum for Kunst.
While un-hackathons aim at overcoming the goal-oriented setup of hacking events more generally, there are also initiatives that specifically target women. For example, in the game development sector, ‘[t]he masculinist character of video games culture broadly, and production specifically, has prompted the creation of several initiatives to attract, support, and retain women interested in the game industry’ (Harvey and Fisher, 2013: 363). Harvey and Fisher analyse the Canadian non-profit
Technology choices and utilization
My third argument, building on the initial two observations, is that certain participants are more inclined to use technologies which are proprietary but operationally open enough. This seems particularly relevant, since such technologies are staged as potent enablers of innovation, especially during the final presentations.
While presenting their projects, participants particularly drew attention to the hardware that enabled the realization of their ideas. Two devices were most frequently used and presented in this context: Raspberry Pi and Arduino (Uno). It seems insightful to look into the chosen hardware, since the presentations implicitly communicated that these tools are well-suited for innovation practices, as a ‘[…] resource not only to experience content, but to modify it and to participate in it’ (Postigo, 2012: 176).
Raspberry Pi
The Raspberry Pi is a microcomputer that is used for a wide range of single board computing projects. The product was developed by the Raspberry Pi Foundation, a registered UK charity since May 2009. While the device involves OSH units such as openly documented graphics hardware, main parts such as the CPU/chip design are closed source. In an interview, Eben Upton – co-founder of the Raspberry Pi Foundation – explained the reasons for the proprietary hardware approach: Raspberry Pi is not open hardware, and there is no plan currently to release the board design.…While we’re supportive of the open hardware movement, we don’t believe that releasing designs for very high-technology, hard-to-manufacture products like the Pi brings significant direct benefits to end users. (Brodkin, 2014)
During
The project was realized in different ways by two participants. While using the same hardware (Raspberry Pi and a sensor for humidity/temperature detection), they employed different software approaches. One participant created the required software ‘from scratch’ and programmed the necessary code in Python. He was aware that there were easier options, but he wanted to realize the project in a way that made it independent of external services or providers. The other participant drew on a Google application programming interface. The main reason, he explained, was that this year – after having attended
In both cases, however, the Raspberry Pi logo was prominently featured in the presentations and staged as ‘the hardware behind the projects’. It was shown in presentation slides (Figure 4) and also added separately onto the box used for the demonstration of the prototype (Figures 5 and 6). Moreover, the Raspberry Pi was already featured prominently as part of the prototype name. After the hackathon, the project’s further development was circulated via Twitter (Figure 7). Thus, the technology as such was mediated in multiple ways: it was not simply presented as a technological prototype but was literally boxed as a material digital object (Figures 5 and 6) and linguistically framed as part of the project’s title. In terms of technology as resource, the Raspberry Pi was shown as a potent device supporting techno-creative practices. Only a closer look at the hardware conditions reveals that in the sense of technology as opportunity, developer’s interactions are limited to the software level. Also, on the surface – with regard to the presented hardware which was the same for both approaches to the

Final presentation of Raspberry Preserve at Hack4DK.

Inside of the Raspberry Preserve prototype.
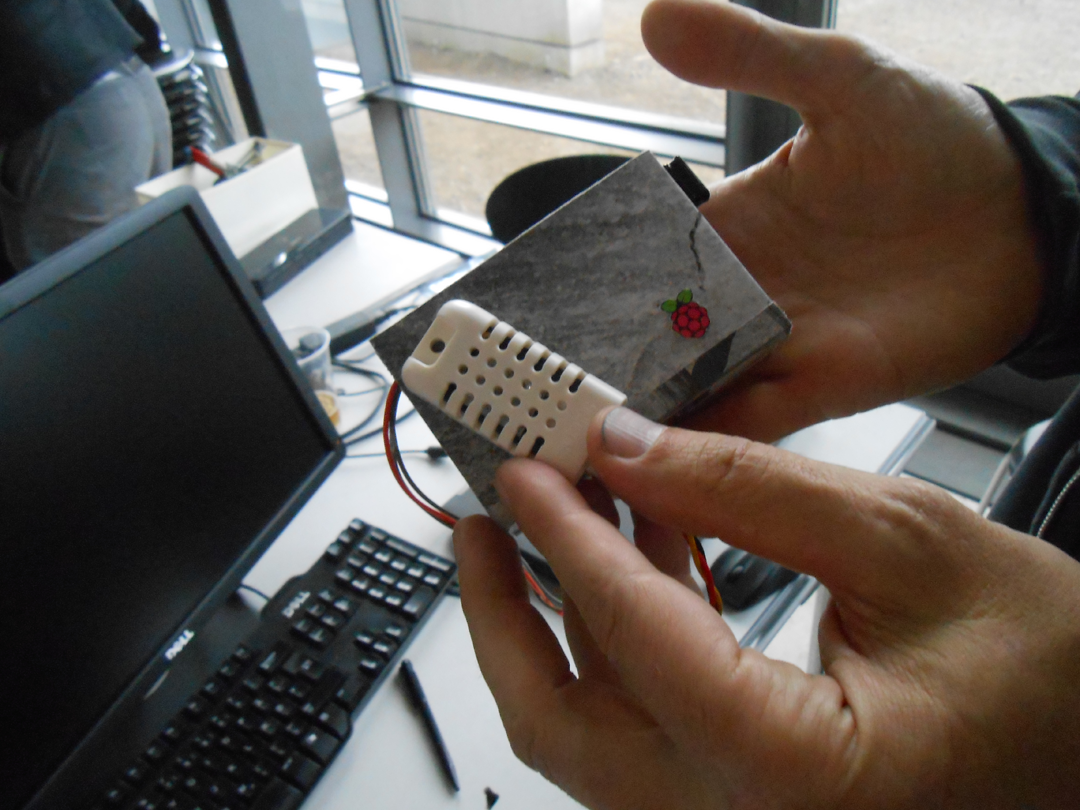
The Raspberry Pi logo, added to the box of the Raspberry Preserve prototype.
Tweet on the finalization of Raspberry Preserve.
Besides these actual implementations, the Raspberry Pi was also used as indicator of a project’s realistic implementation – as ‘signifier of its feasibility’. During the SHD, the hardware implementation of Connected Light had to be simulated and was only suggested in theory. However, the schematic overview shown in the final presentation concretely suggested using a Raspberry Pi (see Figure 8), using the hardware’s image as a potent enabler of digital creativity and realistic solutions. In this context, the technology was not explained in detail, but the Pi was presented rather self-evidently as a commonly known solution for such purposes. Here, the participants built on a pre-established image of the technology and mobilized positive connotations related to technological openness. 11
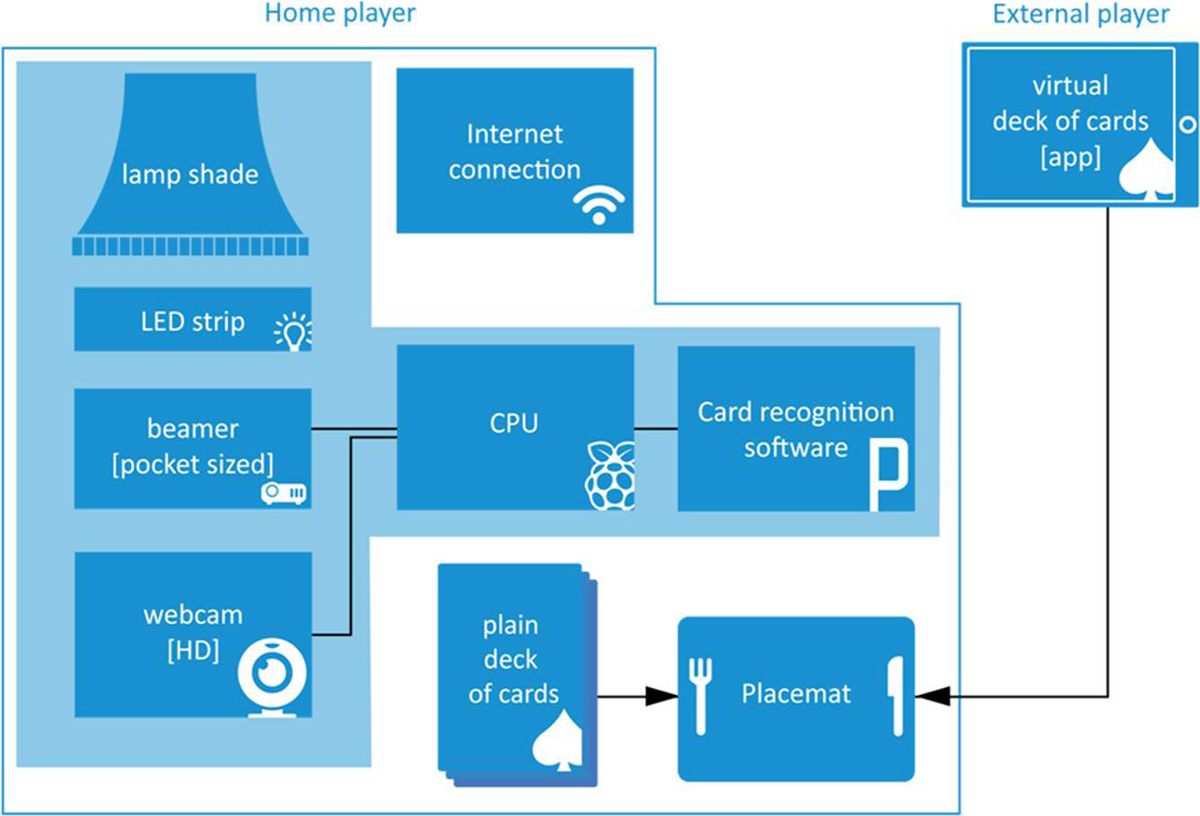
Schematic overview of Connected Light presented at the Science-Hack-Day.
Arduino (Uno)
Besides the Raspberry Pi, Arduino hardware was relevant to both events, particularly at the SHD: Arduino is a small microcontroller built on a printed circuit board, which supports the development of interactive projects. It can be connected to sensors and motors, allowing interaction with its physical environment. One might find some debate about whether Arduino is in fact open source (regarding up to which level), however, it can be seen as an OSH as well as open-source software project since the designs are available under copyleft licenses.
12
Different boards are available, but I encountered mainly the
Before the start of
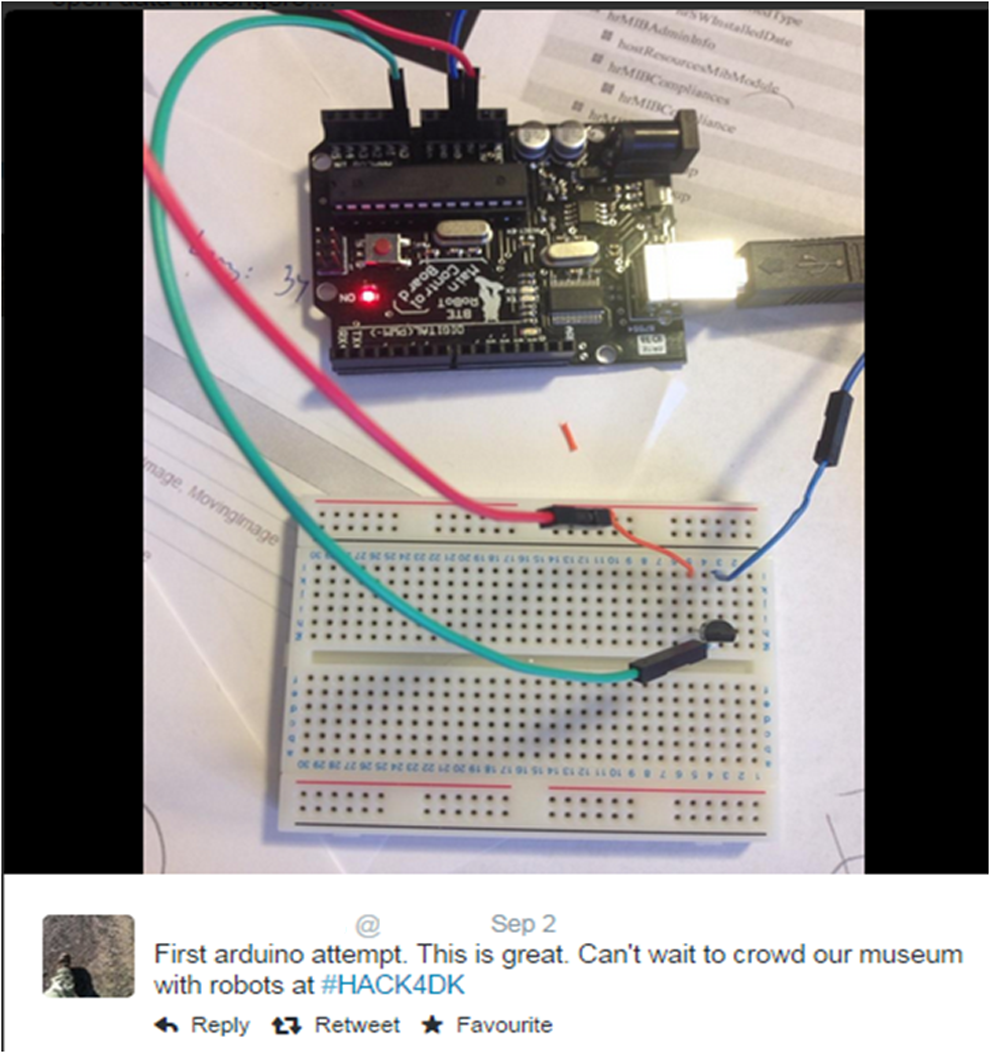
Tweet published before the start of Hack4DK 2014.
Both hackathons indicate that the time pressure and competitiveness of such events encourage pragmatic decision-making and interactions. The utilized technologies need to support straightforward, rapid development processes, and the same goes for participants’ skills. This observation provides further support to Pink et al.’s emphasis on processes of co-constitution (2016: 152) – echoing, of course, the notion of co-construction which has long been crucial to science and technology studies as well as other disciplines critical of techno-deterministic theories. Here, participants’ attitudes, project development decisions, technology choices and the digital material event environment yield intricate interplay and event dynamics. While proprietary options such as application programming interface (APIs) lock projects into a position depending on the provider, they may allow participants to realize functional, creative prototypes more easily and within a short time. West (2003: 1382) described such technological options as ‘partly-open strategy’ aimed at ‘attracting user-programmers’: ‘Such strategies presume that there is an intermediate level of disclosure and granting of rights (between fully open and fully proprietary extremes) that will be valuable to users without compromising the IPR owners’ competitive concerns’ (West, 2003: 1382). Various reasons may contribute to participants’ inclination to draw on such partly open options: during hackathons, it seems to be mainly a question of technologies’ competitiveness and efficiency.
Participants’ technology choices seemed related to two crucial factors: Does the technology allow for its adjustment to the project’s purposes; and can this adjustment be realized quickly and easily? While open-source options may meet the first criterion, they often come along with a high appropriation threshold in terms of required knowledge, skills and time. Moreover, factors such as technological independence are not assessed during most hacka-thons and such a criterion does therefore not act as potential encouragement for the use of open-source software. Zooming out of the local hackathon spaces, these observations also indicate the development that closed-source software has adapted features of open-source software. West (2003: 1259) described this as a trend towards ‘hybrid standards strategies [which] reflect the competing imperatives for adoption and appropriability’. While appropriability refers to approaches which ensure that a company will receive returns on their innovation (e.g. through licensing), adoption denotes the actual acceptance and usage of a product (which is in turn essential for a product’s economic success). A ‘partly open’ strategy mediates between these factors. However, while a developer might be practically able to use an API in a similar way to an open-source code, the legal implications and dependences are crucially different. Such technologies imply that certain modes of cultural production can be achieved even with closed-source software. At the same time, they enforce usage conditions that are based on a hierarchical relationship between individual developers and corporations such as Google Inc. providing the API. In the sense of technology as opportunity, they create a hierarchical relationship between consumers and content (Postigo, 2012: 177) by enforcing technological and legal dependencies. As linguistic resource, staged at hackathons, they signify that digital creativity may thrive even under proprietary conditions and information/code non-transparency.
Conclusions: Persuasive, efficient, open enough?
Competitive hackathons overall encourage participants to be pragmatic about their decisions and involvement. Project development practices are decisively co-constituted by the need to efficiently utilize team members’ skills and available technologies. Firstly, since convincing, final presentations and persuasively pitching an idea increase the likeliness that a group might be selected as winner, significant efforts are invested in the final phase of
Thirdly, competitive hackathons tend to promote the use of operationally ‘open-enough’, but proprietary technology such as ‘open APIs’. Proprietary options were accepted as long as they enabled quick and straightforward development processes. Criteria such as projects’ sustainable technological independence, as enabled by open-source-software, were prone to being neglected by participants, since these aspects were not rewarded in terms of projects’ evaluation. For many participants, technologies merely needed to be open enough − so that they were able to interact with them in a productive way.
This ‘hacker pragmatism’ has also been highlighted in other developer communities and contexts via the notion of ‘open source pragmatist’ (Raymond, 2005; Yeats, 2007). Workflows and project development at the investigated hackathons indicate that initial advantages of open-source software/OSH are often countered by an increasing openness of proprietary options. Open APIs are an illustrative example: while the actual software may be in fact proprietary, they offer the opportunity to interact and access a software application. As Lyman (2012) argues in a controversial online discussion, we may have ‘reached a point when non-open source software is often “open enough”’) for certain audiences: APIs are where a lot of the action is and the same kind of buzz that fuelled open source. Open source still has its advantages and benefits that cannot be matched by APIs, but OSS supporters and vendors need to be aware the closed competition is also evolving and getting smarter – and more open. (Lyman, 2012)
Competitive setups, prizes, peer pressure and tight schedules at hackathons encourage participants to go for quick fixes, often enabled by open-source alike tools such as proprietary ‘open’ APIs. These hacking events likewise encourage groups to focus on persuasive project presentations rather than the development process and participants’ individual learning curve. Since the threshold in terms of necessary skills and time for using open-source options is often higher than for using proprietary solutions, participants tend to choose technology based on the criterion that it is ‘open enough’, that is, allowing for sufficient creative interaction. This dynamic fosters development practices during which participants’ personal skills development and projects’ sustainable technological independence are secondary.
Drawing on digital ethnography for an investigation of two case studies, this article illustrates how hackathons as digital-material environments co-constitute participants’ interaction and technology use. It shows that time pressure and (even mildly) competitive inducements may impede inclusive, instructive approaches: during events frequented by audiences with different IT skill levels, these conditions may inhibit those participants with lower skill levels to train in even basic expertise in, for instance, coding or electronics. Moreover, they encourage project development processes which are very focused on efficient group work and the final ‘staging’ of results. In light of some of the broader tendencies in hacking cultures such as the notion of ‘open-source pragmatist’, one may be inclined to ask to what extent these empirical observations may be indicative of broader developments.
In particular, issues related to creativity and inclusivity are noteworthy here. Regarding creativity, the term ‘hacking’ has traditionally referred to the process of solving an issue in a smart, possibly unexpected way. In contrast, the type of hacking which is now dominant at many hackathons indicates rather result-oriented approaches to innovation and how it is ultimately presented. Hartmann et al. (2008) suggest the notion of ‘opportunistic design’ in order to denote quickly implemented, experimental hacks and prototypes at events such as hackathons. They use this term to describe, for instance, approaches such as ‘copying and pasting source code from public online forums into one’s own scripts’ or ‘“Frankensteining” software and hardware artifacts together by joining them with physical and digital hot glue and duct tape’ (p. 46). The authors are not critical of these practices per se: they do note, however, that they usually ‘happen on short timelines’ (p. 52). While it should not be simply assumed that this kind of creativity is necessarily less preferable to others, it seems worth investigating how dominant it may be in contemporary hacking practices and what this implies for notions of technological creativity. Regarding diversity, this is not yet a strong feature of hacking culture/s overall – mostly evident in terms of gender, but also with regard to ethnicity (Adam, 2003; Fox et al., 2015; Henry, 2014; Jordan, 2008: 125ff.). Efforts to counter this and enhance inclusivity in civic developer contexts are evident in the development of feminist hackerspaces (Toupin, 2014), as well as feminist hackathons (D’Ignazio et al., 2016). That this is a well-known issue, however, only stresses the need to devote more attention to investigating gender- and social diversity–related issues in this field. In particular, we need insights into factors which may inhibit or facilitate the involvement of underrepresented social groups in techno-creative initiatives and how likely they are to engage in particular tasks. While this article contributes to the conceptual debate regarding our scholarly understanding of hacking and digital creativity, it also highlights the need to develop inclusive approaches to promoting IT skills acquisition.
Footnotes
Acknowledgements
The author would like to thank the two anonymous reviewers for their constructive, valuable feedback on this article, the editors for their support, and Karin Wenz for involving her in the
