Abstract
This article examines United States v. Lawal as forensic ethnography. It reads courtroom transcripts, cooperating witness testimony, and exhibits as cultural artefacts that disclose the symbolic, strategic, and infrastructural logics of hybrid online fraud. The analysis draws on Federal Bureau of Investigation (FBI) testimony, money mule accounts, and prosecutorial framing to explore how romance fraud and Business Email Compromise (BEC) schemes converge through shared infrastructures and distributed role allocation. The analysis produced several themes. Here, I foreground three that carry the article’s central analytic weight. (1) Hybrid cybercrimes exceed typological boundaries and challenge law enforcement classifications. (2) Cybercriminal identity operates as functionally modular, distributed across multiple actors, accounts, and personas, which enables operational flexibility and risk dispersion. (3) Laundering infrastructures, though sophisticated, remain fragile, reflecting both aspirational and precarious logics of transnational capital flows. The analysis also reveals how offenders linguistically reframed victims as “clients” or “my partner's clients”. They deployed commercial vocabulary as a neutralisation strategy that repositioned fraud as a business practice. The article treats legal archives as state-produced knowledge systems and theorises “laundering circuits” and “emotional scripts” as conceptual frameworks. These frameworks illuminate how digital fraud functions as both a dramaturgical performance and a structurally embedded response to global inequality.
Keywords
Introduction
Classic Baggie? What sort of name is that? Well, back in 2007, Classic Baggie was very publicly known to be friends with two other famous Nigerian money launderers, named Hushpuppi and Mompha (Warner, 2024a, p.2).
Between 2019 and 2020, more than $3.6 million in proceeds from romance fraud and Business Email Compromise (BEC) moved through bank accounts controlled by a single Nigerian national living in Indianapolis (U.S. Department of Justice, Office of Public Affairs, 2025; Warner, 2024a). When federal prosecutors indicted Olugbenga Lawal in the District of Delaware, they characterised him not as an isolated fraudster but as a critical node in an international criminal organisation that had defrauded US victims of millions of dollars (U.S. Department of Justice, Office of Public Affairs, 2025). The conviction that followed exposed not merely individual culpability but the infrastructural logics of hybrid cybercrime. This article examines the transnational laundering circuits through which hybrid online fraud converts intimate deception and corporate compromise into mobile, investable capital. In United States v. Olugbenga Lawal, prosecutors framed Classic Baggie as “the leader of an international criminal enterprise” (Warner, 2024a, p.1). Because Lawal refused to plead guilty and proceeded to a full jury trial, unusually rich evidentiary materials that are often never made public (because most defendants plead) entered the record (Warner, 2024a). The case therefore provides a rare empirical window into how hybrid fraud and laundering are organised, narrated, and contested in court.
Against this backdrop, economic cybercrime prosecutions have become key sites for understanding how digital fraud is structured, narrated, and legitimised. Beyond their legal function, courtroom transcripts and exhibits provide a rare empirical window into the hidden infrastructures of cases (Gilbert & Heydon, 2021; Moore et al., 2021). They capture not only technical evidence but also the voices of offenders, prosecutors, investigators, and judges as they grapple with the complexity of cyber-enabled crime. Read as sociocultural texts, these records illuminate how fraud is organised, rationalised, and contested in public forums.
This analysis examines the United States v. Olugbenga Lawal case (District of Delaware). It is one of the most extensively documented US prosecutions of a Business Email Compromise (BEC) network with integrated romance fraud schemes (Warner, 2024a). The cybercrime case is qualitatively rich, featuring trial exhibits, witness testimonies, and prosecutorial arguments, all based on full trial transcripts and evidentiary records, and worthy of academic engagement to sharpen its sociological eye. Unlike many studies that rely on police press releases (Hock et al., 2025), secondary accounts (Keith & Scheuerman, 2022), or victims’ narratives (Button et al., 2025c), this dataset offers exchanges in which fraud is performed, explained, and resisted in a legal setting. It provides an opportunity to analyse courtroom testimony, exhibits, and judicial reasoning to understand how hybrid frauds are structured, legitimised, and sustained.
Olugbenga Lawal is a Nigerian national. Studies show that West African diasporic offenders coordinate with co-offenders in their countries of origin, deploying false identities, and laundering routes shaped by geographic and social ties (Abubakari & Amponsah, 2025; Button et al., 2025a; Lazarus, 2025). Such findings affirm that cybercrime is not merely a technical deception but a socially embedded and transnational practice (Lazarus et al., 2026; Sarkar & Shukla 2023; Wall, 2021). Insights from the Tripartite Cybercrime Framework (TCF), which proposes a motivation based typology of cybercrime (socio economic, psychosocial, and geopolitical), are also revealing (Ibrahim, 2016). These findings suggest that socioeconomic cybercrime involving these diasporic groups is consistently more prevalent than psychosocial and geopolitical cybercrime (Auwal & Lazarus, 2025). This socioeconomic dominance is also evident in victim records, for example from the United States Federal Bureau of Investigation’s Internet Crime Complaint Center (IC3) (Engle et al. 2026), and in wider discussions of the victimisation of senior citizens globally (Lazarus, Tickner & McGuire, 2025). The Lawal proceedings resonate with this literature yet offer distinctive empirical richness: they capture, in real time, how offenders narrated role flexibility, affective manipulation, and laundering infrastructures within a judicial arena.
By reading the Lawal case file as a form of forensic ethnography, this article advances three contributions to the sociological analysis of online deviance. First, it demonstrates how identity modularity enables actors to flexibly assume multiple roles across fraud modalities. Second, it shows how BEC schemes and romance fraud are strategically interwoven, producing a dual-modality fraud structure. Third, it situates laundering within transnational circuits that highlight the organisational reach of such enterprises. Collectively, this study contributes to ongoing debates on transnational criminal economies and the sociotechnical performance of fraud.
Against this backdrop, the article addresses three research questions:
How does the Lawal case illustrate identity modularity as a structural feature of hybrid fraud? In what ways are BEC and romance fraud schemes coordinated as dual modalities of deception? How do the laundering circuits revealed in the proceedings reflect wider transnational flows of illicit capital?
Literature Review
Prior research has highlighted how diasporic actors build cybercrime strategies across borders, with collaborations between overseas operatives and local partners forming transnational laundering pipelines (e.g., Abubakari & Amponsah, 2025; Button et al., 2025a). Institutional corruption and insider collusion can enable such pipelines by providing access and information that help cybercriminals bypass security infrastructures (Richards & Eboibi, 2021). Such pipelines operate within a globalised cybercrime ecosystem, sustained by innovation and the coordinated activities of dispersed participants (Kraemer-Mbula et al., 2013). Empirical findings have also questioned typological models that isolate romance fraud, cryptocurrency fraud, BEC, and laundering as discrete practices (Abubakari & Amponsah, 2025; Garba et al., 2026; Lazarus, 2025). Instead, scholars argue that West African diasporic actors deploy fluid, hybrid strategies that cut across categories, merging affective deception with corporate fraud in versatile portfolios (Abubakari, 2024b, 2025; Mpofu et al., 2022). Studies further indicate that these portfolios are sustained through modular identities, mule hierarchies, and a wider range of enabling organisational vehicles that function as routine conduits for laundering (Abubakari & Amponsah, 2025; Button et al., 2025b). Identity multiplicity is not accidental concealment but a fundamental feature of cyber-fraud, embedded in demographic flows and geographical contexts (Cross & Holt, 2021, 2023; Soares et al., 2025; Soares & Lazarus, 2024). This resonates with the Olugbenga Lawal case, where the use of interchangeable aliases and fabricated corporate entities facilitated the simultaneous operation of romance and BEC schemes in the United States, with laundering circuits extending to West Africa.
While this scholarship highlights the fluidity of diasporic fraud networks, much of the literature has nonetheless preserved a categorical distinction between romance fraud and BEC. This divide warrants closer scrutiny. Complementary offender-based accounts provide further insight into these dynamics. Lazarus's (2025) study documents how BEC networks resist rigid hierarchies, relying instead on flexible arrangements where roles and rewards are adaptive, relational, and digitally mediated. Such findings extend other observations about horizontally organised cybercrime markets (Levi, 2022; Lusthaus et al., 2024, 2025). The present study builds on this scholarship by shifting the analytical frame outward: from the micro-politics of role distribution to the external infrastructures, identities, shell companies, and international transfers that underpin deception and laundering. This perspective emphasises how diasporic cybercrime is scaffolded not only by actors and their roles but also by durable, jurisdictionally dispersed tools of impersonation and asset conversion (Abubakari & Amponsah, 2025; Button et al., 2025a; 2025b).
However, the convergence of romance and corporate scripts cannot be fully understood without examining the laundering practices that sustain them. It is here that tactical dualism acquires its spatial and aspirational dimensions, extending beyond deception to the transformation of illicit capital. The literature on romance fraud and BEC has generally treated them as distinct crime scripts. Romance fraud schemes are framed primarily through emotional manipulation, victim vulnerability, and gendered dynamics (Abubakari, 2025; Amirkhani et al., 2024; Bilz et al., 2023; Cross & Holt, 2023; Lazarus et al., 2023; Soares et al, 2025; Thumboo & Mukherjee, 2024), while BEC is cast as a form of corporate crime involving impersonation, email compromise, and financial diversion (Cross & Gillett, 2020; Lazarus, 2024; Lazarus, 2025). This bifurcation has obscured how these modalities are tactically fused within a single fraud architecture. This fusion also reframes the victim side of the ledger, where ‘identity theft’ and fraud harms are patterned, unevenly experienced, and often under-disclosed. Work on crisis fraud also shows that victims’ risk evaluation can be shaped by heuristics such as affect and scarcity, which compress judgement under emotionally charged conditions (Chang & Chong, 2021). Victimisation research likewise cautions against treating “identity theft” as a single experience: nationally representative survey analyses identify distinct victim subgroups and multiple victimisation profiles (Nevin et al., 2025). Identity theft can also produce harms beyond financial loss, including reported emotional impacts and physical ailments (Randa & Reyns, 2020). Disclosure is patterned: the odds of reporting identity theft are lower when others are present during interviews, especially spouses or older household members (Maher & Hayes, 2025).
Emerging case files suggest that the West African context, particularly in Nigeria, is increasingly adopting hybrid portfolios that combine romance scripts with various impersonations (Garba et al., 2026; Lazarus et al., 2025; Soares et al., 2025). However, empirical studies that trace this fusion in a single case remain rare (Abubakari & Amponsah, 2025). The Olugbenga Lawal proceedings, therefore, offer an essential contribution, showing how romance and BEC schemes were co-engineered within the same logistical frame. This dual-modality illustrates what may be termed tactical dualism: the ability of cybercriminals to exploit affective trust (through romantic intimacy) and transactional trust (through business correspondence) in parallel. In this article, tactical dualism refers specifically to the coordinated switching and layering of romance scripts and BEC tactics within the same fraud operation, where affective and corporate deception work in tandem, share infrastructures, and are redeployed opportunistically as situational demands shift. This approach is consistent with scholars’ observation that offenders diversify their scripts (Hutchings & Holt, 2015). In this sense, money laundering is not reducible to fixed typologies but better understood through crime script analysis as a chain of interlinked services, formal procedures, and managerial practices (Gilmour, 2023a, 2023b). Tactical dualism highlights the strategic combination of fraud types and overlapping identities, resulting in a repertoire that is both resilient and adaptable.
Laundering is too often conceptualised as mere concealment to evade regulators (Bramantyo, 2025; Gilmour, 2023a, 2023b; Levi, 2022). Such a narrow lens obscures its aspirational and spatial dimensions. Empirical studies show that illicit proceeds are frequently channelled back to West Africa, where they are reinvested in legitimate enterprises (e.g., in real estate, education, and music industries) (Abubakari & Amponsah, 2025; Abubakari & Blaszczyk, 2024; Lazarus, 2025; Lazarus & Okolorie, 2019). Such reinvestment not only reshapes the geography of illicit finance but also situates laundering within broader cultural economies and postcolonial asymmetries, where capital flows articulate claims to legitimacy and autonomy. These practices signal not only status consolidation but also strategic withdrawal from Global North oversight. Theoretically, this reinvestment resonates with Hall's (2012) cultural economy of crime, in which illicit capital is aestheticised and legitimised through consumer and entrepreneurial narratives. Anti-colonial discourses further clarify the issue, emphasising how crime can be seen as intertwined with asymmetric North-South power dynamics (Aas, 2012; Agozino, 2003; Lazarus & Button, 2022). Further empirical work shows that some West African fraudsters frame their actions as legitimate retribution for colonial injustice (Lazarus et al., 2025). The Olugbenga Lawal case makes these dynamics visible: proceeds were not merely concealed but redeployed in Ghana for educational and commercial purposes. This article frames this as criminal futurity, the conversion of transient fraud schemes into durable, place-based assets that confer legitimacy, enable social mobility, and cultivate autonomy. In doing so, it contributes by challenging typological and techno-centric models of cybercrime, offering instead a sociologically grounded account of fraud as a globalised, adaptive, and performative enterprise.
Identified Gaps and Study Contribution
Despite substantial advances in the literature on online fraud and cybercrime networks, three critical gaps remain. Empirically, prior scholarship has underexplored courtroom materials as ethnographic data, rarely integrated socio-technical and relational frameworks, and seldom analysed the convergence of romance and BEC fraud within institutional contexts (cf. Abubakari & Amponsah, 2025; Kipfelsberger & Gottschalk, 2025). As a result, courtroom and legal documents remain under-analysed as cultural artefacts that reveal how cybercrime is operationally and discursively constructed. Theoretically, existing frameworks tend to privilege either socio-technical mechanisms, such as platform affordances and digital tools, or social relationships and role dynamics, thereby overlooking how material infrastructures and interpersonal ties jointly sustain hybrid fraud schemes. This article constitutes the first empirical study to apply a dual-theoretical model (Actor-Network Theory, ANT, and Social Network Theory, SNT) to the analysis of both BEC and online dating fraud. For instance, Lazarus (2025), who operationalised the same dual-theoretical framework, focused exclusively on BEC schemes. Evidentially, few studies have traced the convergence of romance and BEC frauds within institutional settings such as criminal prosecutions, where emotional, financial, and organisational logics visibly intersect (e.g., Abubakari & Amponsah, 2025). By addressing these gaps, this study provides an empirically grounded and theoretically integrated account of hybrid cyber-fraud. It demonstrates how relational and infrastructural elements coalesce in practice. Building on this foundation, the next section introduces the dual-theoretical model that underpins the analysis.
Theoretical Framework
This analysis draws on both Actor-Network Theory (Callon, 1986; Latour, 2017; Vicsek et al., 2016) and Social Network Theory (Granovetter, 1973; Granovetter, 1983; Simmel, 1964), to examine how romance fraud and BEC schemes converge in United States v. Lawal. Integrating Actor-Network Theory and Social Network Theory illuminates the social and technological architectures underpinning cybercrime networks. It also explains how these hybrid operations function through shared infrastructures, fluid role transitions, and transnational coordination.
Actor-Network Theory
ANT conceives social phenomena as assemblages of human and non-human actants whose relationships co-produce outcomes (Callon, 1986; Latour, 2017; Vicsek et al., 2016). Within hybrid fraud ecosystems, this approach clarifies how software, email protocols, money-transfer systems, and emotional scripts interact with offenders and victims to generate criminal events. Rather than viewing agency as an individual, Actor-Network Theory disperses it across interconnected nodes that collectively sustain deception. Following Lazarus (2025), Actor-Network Theory helps reveal the fluidity and adaptive logic characteristic of BEC operations. Participants shift between technical and affective functions, and infrastructures continually adjust to new constraints. Such dynamism explains how illicit enterprises endure despite arrests or platform interventions; their resilience lies in continuous realignment among heterogeneous actants.
Social Network Theory
SNT complements ANT by focusing on social relationships and relational structures through which cooperation occurs (e.g., Granovetter, 1973, 1983; Simmel, 1964). It underscores how interpersonal ties, often weak, transient, or digitally mediated, enable transnational collaboration among offenders who may never meet in person. In Lazarus (2025), this perspective exposed how BEC actors coordinate across borders through trust-based exchanges and flexible subnetworks. Applied here, Social Network Theory explains the distributed labour visible in Lawal: Distinct actors perform emotional, transactional, and laundering roles connected through encrypted communication and shared profit motives. It also illuminates how cultural and contextual factors, including local patronage, informal economies, and blurred boundaries between criminal and bureaucratic actors, shape the configuration of these networks.
Integrative Perspective
Although Actor-Network Theory and Social Network Theory share a concern with connectivity, adaptability, and distributed agency, their emphases differ. Actor-Network Theory incorporates technological and material actors into its analysis of network formation, whereas Social Network Theory concentrates on human social ties and structural patterns (Vicsek et al., 2016). Integrating the two allows for a more comprehensive understanding of hybrid cybercrime. Actor-Network Theory reveals how infrastructures enable fraud, and Social Network Theory elucidates how relationships sustain it. Both theories clarify the operation of what may be called ‘laundering circuits’ and ‘emotional scripts’. These are systems in which human affect, technological mediation, and financial exchange intertwine to reproduce transnational digital fraud (cf. Lazarus, 2025). The distinct yet complementary emphases of Actor-Network Theory and Social Network Theory are summarised in Table 1, which outlines their core propositions and clarifies how each contributes to understanding the structural and relational dynamics of hybrid cybercrime (cf. Lazarus, 2025).
Key Propositions of Actor-Network Theory and Social Network Theory*.
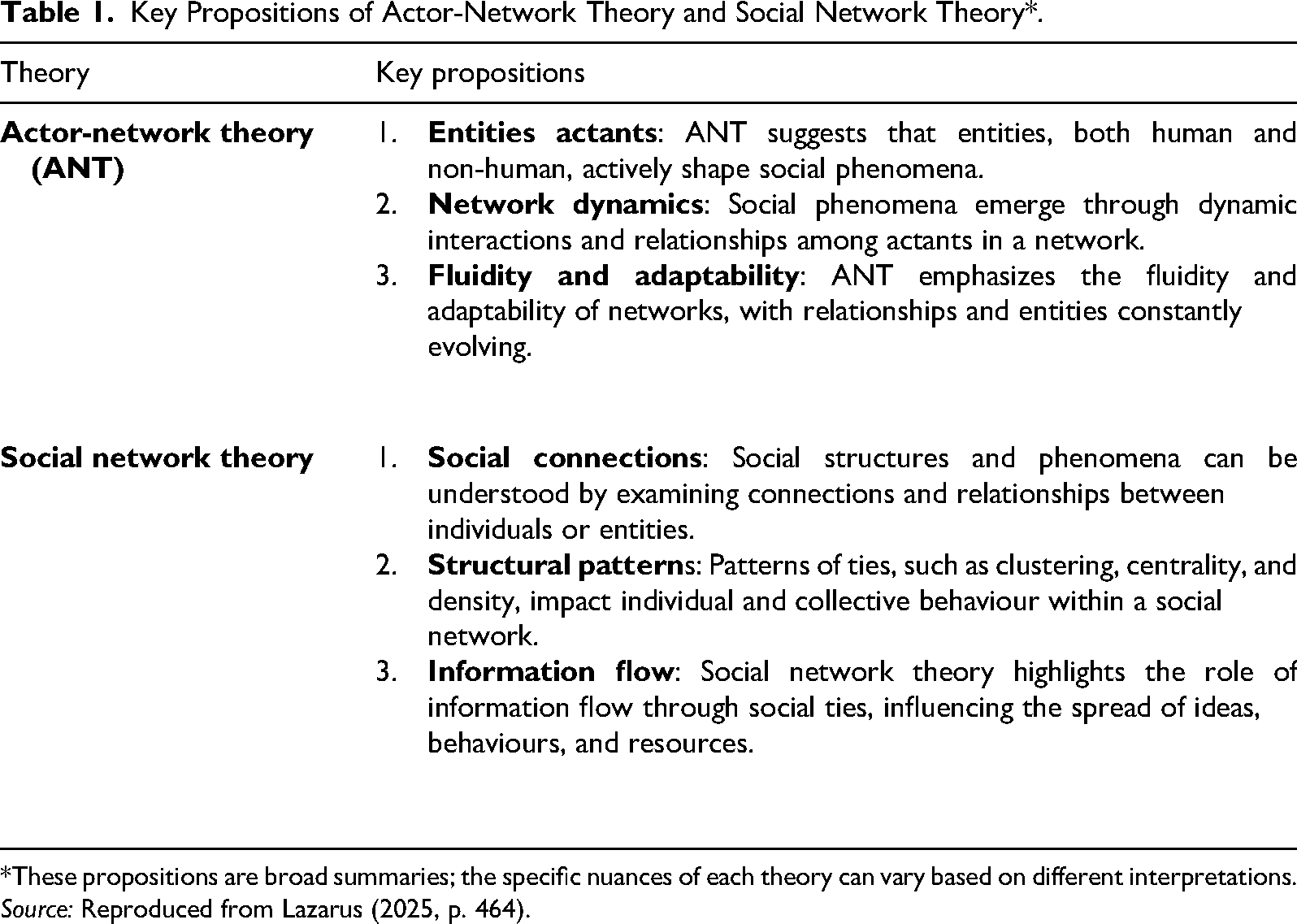
*These propositions are broad summaries; the specific nuances of each theory can vary based on different interpretations.
Source: Reproduced from Lazarus (2025, p. 464).
Methods and Materials
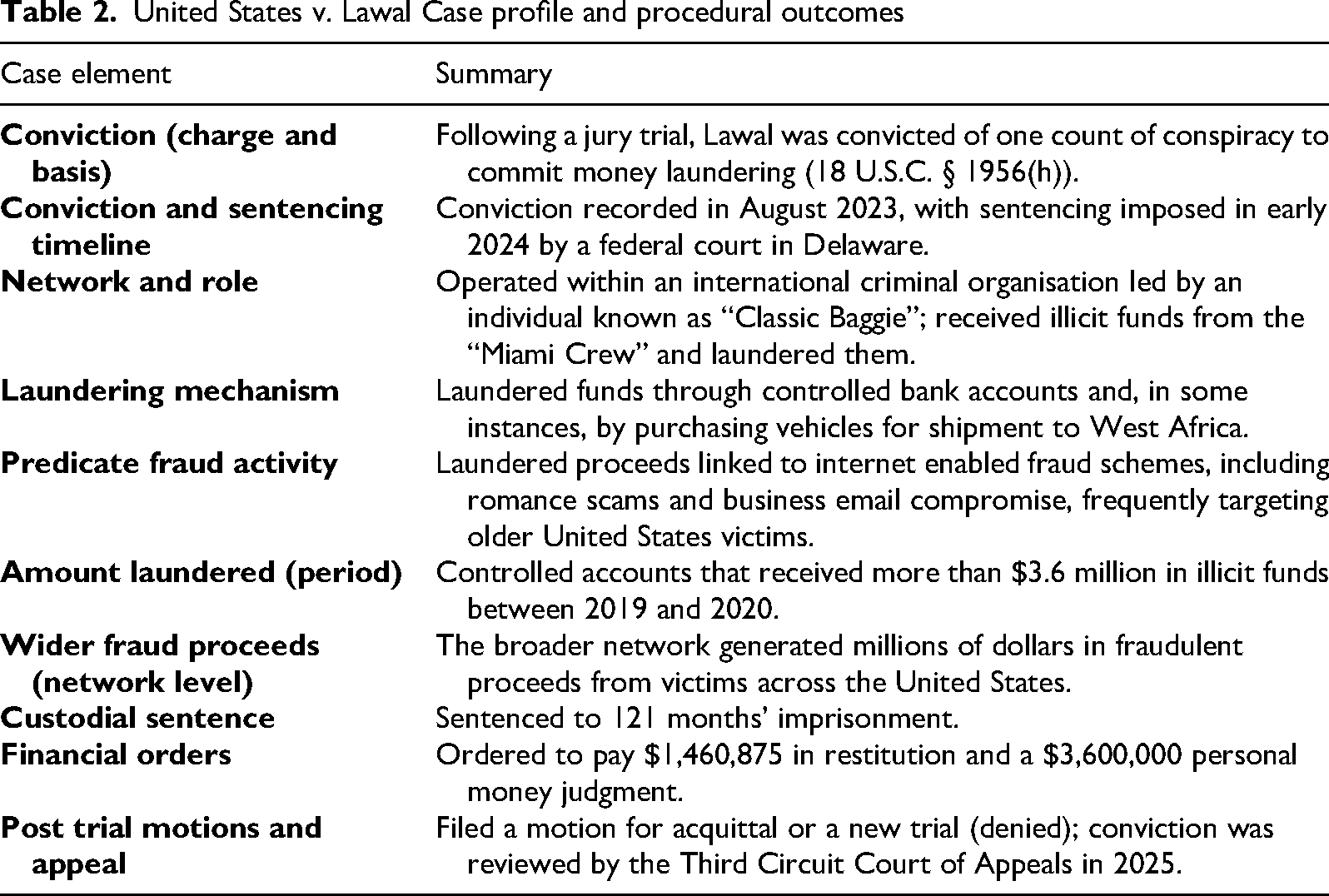
This section outlines the dataset and analytic strategy, highlighting how courtroom records were systematically examined through a thematic framework. This article examines United States v. Olugbenga Lawal (District of Delaware), documenting US prosecutions of a BEC network with integrated romance fraud schemes (see Warner, 2024a; 2024b). The credibility of this approach is two-fold. On the one hand, legal documents, reinforced by their consistent use in prior scholarship (e.g., Matthijsse et al., 2023), underpin their suitability as a data source for the present study. On the other hand, like prior studies (e.g., Kipfelsberger & Gottschalk, 2025; Marquart & Thompson, 2024), this study employs a single-case approach. By treating these materials as cultural artefacts rather than solely as legal evidence, this study advances a forensic ethnography of hybrid fraud. The focus is not merely on what crimes were committed but on how fraudsters, cooperating witnesses, and law enforcement narrate their practices. The table below summarises the key case details, financial figures, and procedural milestones (e.g., Warner, 2024a; 2024b; U.S. Department of Justice, Office of Public Affairs, 2025; USA v. Olugbenga Lawal, No. 24-1100, 3d Cir. 2025; Table 2).
This study is grounded in a forensic ethnographic orientation (Degenshein & Leslie, 2025; Gill, 2021; Pool, 2017). By doing so, it treats courtroom transcripts, testimonies, and exhibits not merely as legal evidence but as sociocultural texts. Legal proceedings are understood as sites where competing narratives of fraud are staged, contested, and legitimised. This epistemological stance permits attention to how different actors, fraudsters, prosecutors, Federal Bureau of Investigation (FBI) agents, judges, and cooperating witnesses frame the organisational logics, moral vocabularies, and infrastructural practices of hybrid online fraud. In this sense, courtroom documents are analysed as artefacts that make visible the symbolic and infrastructural dimensions of BEC and romance fraud schemes.
Analytic Framework
Data analysis followed thematic analysis (Braun & Clarke, 2006), which emphasises the interpretive and situated role of the researcher. Braun and Clarke’s (2006) thematic analysis was selected as a flexible yet systematic tool to identify patterns of meaning across the corpus. It balances semantic (surface-level) and latent (underlying) readings.
An extensive seventy-two-page set of courtroom transcripts and exhibits were reviewed in full to preserve contextual integrity. However, only text segments that contained narrative, descriptive, or interpretive value for understanding fraud operations (e.g., direct testimony, prosecutorial commentary, or investigative summaries) were coded for analysis. Non-substantive procedural text (e.g., pagination headers, scheduling remarks) was excluded. This ensured a complete yet analytically focused engagement with the dataset.
Analytic Procedure
Materials
The primary dataset comprises seventy-two-page extensive courtroom transcripts and exhibits from United States v. Olugbenga Lawal and related proceedings. Court transcript excerpts and trial documentation were accessed through leading cybercrime expert Gary Warner's publicly available archives (e.g., Warner, 2024b). His blog archives serve as an accessible public record of cases that otherwise remain difficult to access due to PACER fees and restricted courthouse access. These materials include:
Witness testimonies FBI investigative accounts Prosecutorial examinations and judicial exchanges Exhibits such as WhatsApp messages, wire transfers, limited liability company (LLC) incorporation records, and bank documents
Supplementary sources also include editorial commentary curated by Gary Warner, in his ′Classic Baggie′ blog series (e.g., Warner, 2024a), alongside US Department of Justice press releases and indictments (e.g., U.S. Department of Justice, Office of Public Affairs, 2025; USA vs Olugbenga Lawal, 2025). While some may undermine the value of ‘soft’ materials such as editorials, and press releases, their use here is fourfold. First, contextual framing: to situate the case within its wider legal, media, and public discourse environment. Second, discursive analysis: To examine how prosecutors narrativise fraud compared to how journalists or commentators frame it, and to trace the rhetorical strategies through which cybercrime is ‘talked about’, justified, or politicised. Third, supplementary triangulation: to fill gaps where court filings remain silent (e.g., on motivations or wider network references), thereby strengthening reflexivity and reducing dependence on any single narrative. Fourth, comparative perspective: Merging official/state accounts and independent commentary prevents overreliance on any single narrative. These materials are therefore not primary evidence but ancillary scaffolding that sharpens interpretation.
Court Transcript Analysis and Methodological Considerations
Oral testimony often contains incomplete sentences, false starts, and grammatical irregularities inherent to spoken language. Following established practices in legal ethnography and court document analysis (Ewick & Silbey, 1995; Presser, 2009), this study presents testimony in ways that preserve substantive meaning while ensuring readability. Where minor grammatical adjustments have been made to spoken testimony, these do not alter the semantic content or evidential value of witness statements. Thematic questions used as subheadings are analytical organising devices generated by the researcher to synthesize courtroom exchanges, rather than verbatim questions from trial proceedings. All analytical claims remain traceable to specific exhibits and testimony archived in Gary Warner's (2024b). Through the iterative coding and refinement process, several themes were produced. The analytic process yielded a set of interconnected themes that capture both the operational and symbolic dimensions of hybrid fraud. These themes synthesise the inductive coding process and highlight the patterned ways in which courtroom actors narrated, contested, and legitimised the activities under scrutiny. A summary of the thematic architecture is presented in Table 3.
United States v. Lawal Case profile and procedural outcomes
Thematic Analysis Summary Map of Online Fraud Schemes and Money Laundering.
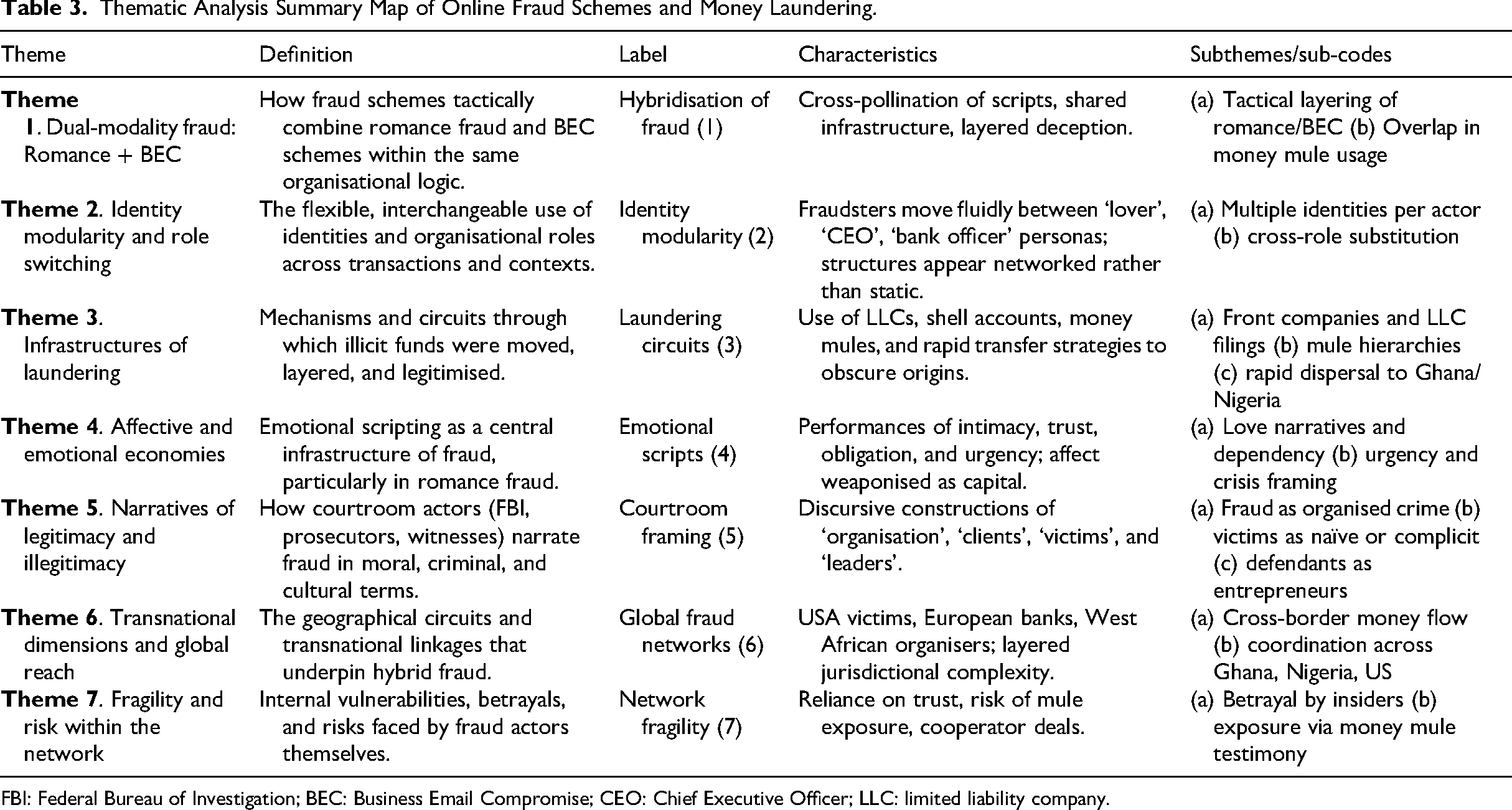
FBI: Federal Bureau of Investigation; BEC: Business Email Compromise; CEO: Chief Executive Officer; LLC: limited liability company.
The final analysis produced seven interconnected themes, as detailed in Table 3. The Findings section presents the four central themes that capture the operational and affective architecture of the fraud network. The subsequent Discussion section integrates all seven themes to develop the broader theoretical argument, examining the network's structural, discursive, and transnational dimensions.
Findings
Thematic analysis of the courtroom transcripts produced four interrelated themes that illuminate the organisational, affective, and infrastructural dimensions of hybrid fraud. Following Braun and Clarke's (2006) reflexive approach, the results are presented thematically, supported by extracts from trial transcripts and exhibits. Subheadings are framed as questions that reflect the interrogative structure of courtroom proceedings, though they represent thematic syntheses rather than verbatim questions from the trial transcript. These analytical questions organise witness testimony, evidentiary materials, and cross-examination exchanges into coherent themes. Quoted material represents either direct witness statements (where verbatim reproduction is possible) or substantive paraphrase of testimony (where consolidation serves analytical clarity), with all claims traceable to trial documents.
Theme 1: Identity Modularity and Adaptive Roles
Read across the wider testimony, this exchange highlights the fungibility of account ownership within the fraud network. Rather than being tied to fixed personal identities, financial infrastructures were treated as interchangeable tools. Accounts in one's own name, those borrowed from associates, or fabricated identities were mobilised fluidly to ensure efficiency. The emphasis on who could move the money fastest points to an operational logic in which speed and adaptability outweighed the legitimacy or stability of identity documents. As Hermann testified elsewhere about Classic Baggie's instructions: “he would tell me to send $50,000 to Lawal with an address or something like that, send CashApp to Lawal and send me the details and things like that, yeah.” What mattered operationally was not whose name appeared on the account, but who could execute transactions most rapidly and reliably. In effect, personal identity became modular, reconfigured to meet the immediate transactional demands of the enterprise.
Interpreted across the wider testimony, the testimony demonstrates a collective elasticity in role allocation. Tasks such as maintaining romance chats, moving funds, or liaising with intermediaries were not rigidly assigned but circulated among members depending on availability and circumstance. This capacity for substitution reduced vulnerability to disruption, ensuring continuity even when individual actors were absent or incapacitated. It reflects a resilience strategy common to loosely structured cybercriminal organisations: redundancy in skills and responsibilities allowed the fraud to persist without interruption. The courtroom dialogue, therefore, reveals a system less reliant on rigid hierarchies and more on pragmatic adaptability, where labour and identity were redistributed as situational needs demanded.
Theme 2: Dual-Modality Fraud (BEC and Romance Scams)
Read across the wider testimony, this statement demonstrates the strategic layering of fraud modalities, where romance narratives were deployed as complementary mechanisms to BEC schemes. For some victims, corporate impersonation and financial manipulation were insufficient to secure compliance; the emotional intimacy of a romance narrative provided an alternative entry point. The juxtaposition of ‘not all fell for the business emails’ kind of narratives with the assumptions that ‘many would believe the love angle’ stories highlights a calculated diversification of tactics, akin to risk management in licit enterprises. Here, affective manipulation was not incidental but deliberately cultivated as an additional revenue stream, reinforcing the hybrid nature of the operation.
The testimony stresses the seamless integration of professional and intimate fraud practices directed at the same targets. Interpreted across the wider testimony, communications have been managed on a timed rotation as strategic business tactics. Actors maintained some contact via email, keeping it formal and transactional. Other contacts shifted to more intimate messaging platforms like WhatsApp to sustain trust, soften suspicion, and keep the same target engaged through different persuasive registers within a single ongoing interaction. This pattern suggests deliberate temporal coordination and a functional division of labour. It exploited both rational and emotional registers of trust while masking inconsistencies across channels. In effect, hybrid fraud operated as a choreographed performance. It simultaneously inhabited the logics of commerce and intimacy to deepen victim entrapment.
Theme 3: Affective Infrastructures and Moral Vocabularies
Interpreted across the wider testimony, this extract highlights the deliberate reframing of victims through commercial terminology. By substituting ‘clients’ for ‘victims’, offenders discursively repositioned fraud as a business transaction rather than a moral violation. The language of commerce functioned as a neutralisation strategy, legitimising exploitation by aligning it with market logics in which payment implies consent. In this framing, victims were stripped of vulnerability and instead cast as voluntary participants in a transactional exchange. Such discursive manoeuvres created an affective infrastructure that insulated offenders from guilt. They also reinforced a collective self-image of professionalism and entrepreneurial legitimacy.
The testimony illustrates the linguistic distancing enabled by commercial terminology. By referring to victims as “my partner's clients,” Hermann repositioned fraud within a business framework. This discursive shift, characteristic of neutralisation techniques, worked to depersonalise targets and insulate participants from moral accountability. Some regional studies also trace comparable neutralisation vocabularies in popular culture, including in Afrobeats and Nigerian hip hop lyrics that recode fraud as hustle, status, or enterprise, and that sometimes re-label targets as clients or even through dehumanised terms such as “maga” or “mugu” (stupid animals) (see Lazarus, 2018, 2023; Lazarus et al., 2026 for full analysis). Such semantic manoeuvres created an affective infrastructure that normalised exploitation through the language of commerce, reinforcing a collective self-image of professionalism rather than criminality.
Theme 4: Transnational Laundering Circuits
Read across the wider testimony, this testimony underlines the use of layering as a deliberate laundering tactic. Moving funds through multiple accounts, often under different names, fragmented the audit trail and complicated regulatory detection. By wiring to intermediaries abroad, the fraudsters embedded their financial flows within legitimate cross-border banking infrastructures, exploiting weak points in oversight systems. The statement also illustrates how laundering was not a discrete step but an integral part of the fraud's architecture, linking frontline cash-outs to transnational financial mobility. This layering practice highlights the infrastructural sophistication of hybrid fraud, where deception and laundering were inseparable elements of the same operation.
Interpreted across the wider testimony, the extract demonstrates the distributed and transnational character of the laundering network. Funds did not terminate with the immediate offenders but were channelled through trusted regional contacts who handled collection and reinvestment. The reliance on unseen but reliable partners reflects the extended organisational reach of the fraud, where geographic distance was bridged by trust, coded communication, and reputation within illicit markets. It also accentuates how hybrid fraud was sustained by diasporic networks that enabled capital to circulate beyond the jurisdiction of US enforcement. By situating laundering nodes in Nigeria and West Africa, offenders leveraged both the infrastructural opportunities and jurisdictional fragmentation of the global financial system, making prosecution and recovery particularly challenging.
The four themes above reveal that hybrid fraud cannot be reduced to technical manipulation or opportunistic theft. Rather, it operates as a cultural, organisational, and infrastructural performance in which deception, affect, and financial engineering are deeply entangled. Identity modularity demonstrates how actors fluidly exchanged roles, ensuring resilience and continuity within the fraud economy. Dual-modality fraud, where romance fraud schemes were woven into BEC schemes, shows how professional and intimate registers of deception were deliberately combined to maximise extraction from victims. Affective infrastructures and moral vocabularies expose how offenders reframed victims as ‘clients’, neutralising moral responsibility and legitimising exploitation through the language of business. Finally, transnational laundering circuits anchor these practices in global money flows, embedding local acts of deception into international financial infrastructures and diaspora-based networks.
In this sense, hybrid fraud is best understood as more than an assemblage of crimes; it is a sociotechnical system of deceit that adapts, legitimises itself through cultural narratives, and thrives in the interstices of global financial governance. These findings invite a critical discussion of how hybrid fraud challenges prevailing models of cybercrime analysis, law enforcement, and criminological theory. The following section explores these implications, situating the results within wider debates on organisational flexibility, affective labour in fraud economies, and the structural conditions that sustain transnational illicit enterprise.
Discussion
The following seven fundamental themes form the backbone of this discussion. They also expose its paradox: a structure that is at once resilient and yet internally fragile. This duality provides the frame through which the Lawal case is interpreted, not only as an episode of transnational deviance but also as a contribution to the sociology of deviance more broadly. It complements contributions, such as a collection of studies in the Journal of Economic Criminology, which reveal a growing recognition of hybridised fraud schemes infrastructures (Abubakari, 2024a; Button & Carter, 2024; Cole, 2024; Cretu-Adatte et al., 2024; Lazarus et al., 2025; Marquart & Thompson 2024; Whittaker et al., 2024; Yoshida, 2025). While these strands of research foreground offender narratives (Abubakari, 2024a), victim experiences (Meikle & Cross, 2024), and hybrid typologies (Maras & Ives, 2024), few studies have examined how these dynamics materialise within institutional contexts such as legal proceedings (e.g., Abubakari & Amponsah, 2025). Building on the existing scholarship addressing romance fraud (Aborisade et al., 2024; Lazarus et al., 2023; Maras & Ives, 2024; Wang, 2026), and Business Email Compromise (BEC) (Cross & Gillet, 2020; Lazarus, 2024; Lazarus 2025), the present article extends these debates through forensic ethnography, theorising the Lawal case as a site where ‘emotional scripts’ and ‘laundering circuits’ function as infrastructural logics in hybrid online fraud.
Theme 1: Dual-Modality Fraud (Romance and BEC)
One of the most striking features of the Lawal proceedings was the tactical convergence of romance fraud and BEC within the same organisational logic. Witness testimony captured this hybridisation clearly: We were using the romance money that was deposited into an account’. Rather than operating as discrete schemes, romance and BEC were layered, co-dependent strategies drawing on shared infrastructures such as mule networks, shell accounts, and communication scripts.
This dual-modality illustrates what may be termed tactical dualism, the ability of fraudsters to exploit affective trust (through romantic intimacy) and transactional trust (through business correspondence) in parallel. In doing so, actors maximised the efficiency of existing infrastructures, blurring distinctions that law enforcement and academic taxonomies often treat as separate. Scholarship on cyber-fraud has long noted the fluid boundaries between fraud categories, where offenders innovate by recombining scripts and resources to evade detection (Button et al., 2025a, 2025b; Dwight et al., 2025; Holt & Lee, 2022). The Lawal case advances this understanding by showing how cross-pollination is not incidental but central to the organisational model.
The hybridisation of romance fraud and BEC schemes also complicates criminological attempts to categorise fraud according to offender motivation or modus operandi. As Abubakari and Amponsah (2025) demonstrate, West African diasporic fraud networks often integrate multiple fraud types within the same enterprise, shifting flexibly between modalities according to opportunity. This adaptability challenges static typologies of cybercrime that distinguish ‘romance fraudsters′ from ‘BEC actors’ as if they were separate populations. Instead, the evidence suggests a modular enterprise in which scripts are interchangeable and infrastructures are shared. This fluid interplay between emotional and transactional infrastructures exemplifies what Actor-Network Theory (Callon, 1986; Latour, 2017) describes as the co-production of outcomes through human and non-human actants. Communication platforms, payment systems, and emotional scripts function here as interacting nodes in a network that sustains deception. At the same time, Social Network Theory (Simmel, 1964; Granovetter, 1973) helps explain how relational ties between offenders enable such hybrid operations to persist across social and digital boundaries.
By exposing the organisational logic of dual-modality fraud, the Lawal case highlights how fraud is best understood not as discrete schemes, but as ecologies of deception in which multiple modalities coexist, overlap, and reinforce one another. This recognition has important implications for law enforcement and criminological theory: it calls for analytical models that foreground hybridity, convergence, and tactical flexibility rather than rigid categorical distinctions.
Theme 2: Identity Modularity and Role Switching
Another defining feature of the Lawal proceedings was the fluidity with which offenders inhabited multiple roles and identities across different fraud contexts. As one witness explained: How about Mike Miami? A. That's me, also. Q. And Michael Hermann? A. That's me’. Interpreted across the wider testimony, this malleability highlights what may be termed identity modularity (the capacity to adapt personas to shifting situational demands, thereby sustaining deception across romance and BEC schemes alike).
Seen through a Goffmanian lens (Goffman, 1959), these practices reinforce the dramaturgical character of fraud. Online offenders, such as illicit website developers, do not metaphorically wear masks but perform roles attuned to the expectations of their clients, audiences, strategically mobilising scripts of intimacy, professionalism, or authority (Whittaker et al., 2025). Identity here is not a mere disguise layered over an authentic self but an infrastructure for deception: a toolkit of personas that can be activated, rotated, or retired depending on opportunity. The performative agility of identity modularity also extends discussions of symbolic capital within criminal economies. In conventional markets, credibility accrues from authenticity and reputation; in fraudulent markets, it derives from adaptability and resonance with the target's frame of reference (Bourdieu, 2011). By adopting different identities, such as lovers, CEOs, and bank officers, fraudsters exploited trust from various symbolic registers. The modularity itself became a form of capital: An organisational resource that allowed fraud schemes to expand across different victim groups and transaction types.
This flexibility resonates with emerging criminological literature on the performative and symbolic dimensions of cybercrime. Studies of cybercriminal networks have shown that false identities are not only covers for deception but structuring devices that sustain continuity across fraud schemes and maintain organisational coherence (Leukfeldt & Holt, 2020; Lusthaus et al., 2024, 2025). The Lawal transcripts deepen this insight by illustrating how modular roles were deployed dynamically within ongoing schemes, often shifting in real time to match the emotional or transactional needs of the target. Indeed, identity modularity underscores the need to reconceptualise cyber-fraud not as a practice of static impersonation but as a system of performative infrastructures. Fraud is sustained through the capacity to improvise and reconfigure roles, producing continuity not from authenticity but from strategic modularity. This performative flexibility aligns with Actor-Network Theory′s conception of distributed agency, in which roles are not fixed but emerge through shifting alignments of human and technological actors (Latour, 2017). From a Social Network Theory perspective, modular identities also reveal how social positions are fluidly reconstituted within overlapping networks of trust, signalling a structural adaptability central to hybrid cybercrime (Granovetter, 1983).
Theme 3: Infrastructures of Laundering
The Lawal proceedings also foregrounded the infrastructures through which illicit funds were channelled, layered, and ultimately legitimised. One witness described the instrumental use of corporate registrations: She was in charge of opening up LLC's. Of course the more LLC's you have, the more business bank accounts you can open, and the more money you can receive’. This points to what can be termed laundering circuits, mechanisms that enable illicit capital to move swiftly across borders while minimising traceability. Additionally, Hermann's testimony also revealed how funds were recovered once they reached West African networks: “And he got it in few different ways, either it will be through let's say, it will be through buying a car, like he'll buy a car in the U.S. and ship it, the car will be bought with the money that we have in our bank account for example, and the car gets shipped to Nigeria, and when it gets to Nigeria, they sell it and he recovers his money that way. Originally he said that he had a money transfer business where people, for example, give him money in Nigeria, 10,000, whatever amount and then he would give them the money in equivalent in the U.S.” This dual-pathway recovery system, luxury car export-resale and informal money transfer - demonstrates the sophistication of laundering circuits. The car mechanism provided tangible asset conversion, while the “money transfer business” operated as a hawala-style informal banking system, enabling capital repatriation without formal wire transfers. Both pathways exploited regulatory gaps between jurisdictions.
These practices resonate with the classic placement-layering-integration model 1 (Cassella, 2018; Gilmour, 2023; Sultan & Mohamed, 2024), yet the transcripts reveal significant local improvisations. Rather than the enduring shell companies often associated with organised financial crime, offenders used LLCs as disposable scaffolding: ephemeral vehicles created for a single transfer, then dissolved. This strategy represents a significant innovation within the layering stage of the classic placement-layering-integration model. The use of ephemeral LLCs introduces a fleeting layer of obfuscation. This added layer renders complex transactions virtually untraceable, thereby refining our understanding of how local improvisations reshape conventional laundering sequences. Such short-lived entities functioned as temporary cloaks, buying just enough legitimacy to pass compliance checks before vanishing from institutional records. At the same time, money mule hierarchies underpinned the dispersal of funds across multiple accounts and jurisdictions. Mule testimonies in the case revealed a layered structure in which low-level participants deposited or withdrew funds, often under vague pretences. At the same time, higher-level organisers coordinated rapid transfers to Ghana or Nigeria. This mirrors findings in some studies, which show that laundering infrastructures depend on both complicit actors and unwitting intermediaries, thereby blurring the lines of culpability (e.g., Lord et al., 2019; Otusanya et al. 2011; Wang, 2025).
The transcripts also highlight the dual character of these infrastructures: Sophisticated in design, yet precarious in execution. The speed with which funds were moved across international banking systems illuminates the offenders’ tactical agility, while the reliance on disposable LLCs and vulnerable mules reveals inherent fragility. A single compliance alert, insider betrayal, or mule cooperation could unravel the entire network. By situating these practices within criminological debates, the Lawal case illustrates that laundering infrastructures are not stable, corporate-style entities but shifting circuits of legitimacy and concealment. They combine formal mechanisms of finance with informal trust networks, creating a hybrid economy in which capital mobility depends as much on improvisation as on institutional sophistication. Actor-Network Theory provides a lens for understanding these laundering circuits as assemblages of human and non-human actants (e.g., mules, LLCs, banking APIs, and verification software) whose coordinated interaction produces illicit mobility (Callon, 1986; Vicsek et al., 2016). Complementarily, Social Network Theory foregrounds how interpersonal trust and weak ties within cybercriminal networks facilitate the flow of information and funds across jurisdictions (Lazarus, 2025).
Theme 4: Affective and Emotional Economies
The Lawal transcripts reveal how emotional manipulation operated not as an accessory to fraud, but as a central infrastructure of deception. One exchange captures this dynamic with striking clarity: They were older people that had money. And they think they in love with this person that is behind a computer, and they asking them for favors, and the favors turned into money, and that's when they start sending money to help them out’. Here, intimacy and urgency were fused into a scripted sequence, converting affect into a form of economic leverage. This illustrates what may be termed emotional scripts, performative narratives of love, trust, and crisis that offenders deploy to transform sentiment into financial gain.
Such practices echo Bandura's (1999) account of moral disengagement, particularly mechanisms of cognitive restructuring and victim dehumanisation. By recasting romance as a means to secure ‘help’ or ‘support’, offenders reframe exploitation as mutual obligation. Intimacy becomes instrumentalised, with the victim's affective investment re-coded as a resource within the fraud economy. In this way, emotional attachment is not incidental but weaponised as capital, sustaining transactions that technical deception alone could not achieve. This dynamic also aligns with scholarship that treats fraud as a dramaturgical performance. Building on Goffman's (1959) notion of role-playing, the transcripts show that fraudsters rehearsed and enacted identities, lover, partner, dependent, within carefully staged interactions. These affective roles were not spontaneous improvisations but rehearsed scripts, strategically sequenced to build trust, escalate commitment, and generate urgency. As numerous research findings on online romance fraud (e.g., Aborisade et al., 2024; Abubakari, 2024a; Cross & Holt, 2023; Feng, 2025; Lazarus et al., 2023; Meikle & Cross, 2024; Soares et al., 2025; Soares & Lazarus, 2024; Thumboo & Mukherjee, 2024) have shown, offenders rely on narrative arcs that mimic romantic intimacy yet are oriented toward exploitation.
The case materials highlight that emotions functioned as infrastructural devices, much like bank accounts or LLCs. Just as laundering circuits enabled financial flows, affective economies enabled trust flows, legitimising requests, masking deception, and sustaining long-term victim engagement. The emotional labour invested by offenders, from daily chats to declarations of love, became part of the operational scaffolding of fraud. Indeed, the Lawal case underscores that cyber-enabled fraud is not reducible to technical breaches or financial transfers. It is also a socio-technical dramaturgy in which emotions are rehearsed, scripted, and monetised. Recognising affect as capital complicates conventional distinctions between rational-economic and emotional-intimate domains, showing instead that successful fraud thrives at their intersection. Actor-Network Theory situates emotion within the architecture of action, treating it not as a residue of motive but as an operative actant, in concert with digital media and financial instruments, which helps generate fraudulent outcomes (Latour, 2017). Social Network theory, in complementary fashion, locates these affective exchanges within the patterned flow of relations, where intimacy becomes a conduit through which resources, obligations, and coordinated behaviours circulate (Granovetter, 1983).
Theme 5: Narratives of Legitimacy and Illegitimacy
The courtroom is not only a site of legal adjudication but also of discursive struggle, where competing vocabularies of legitimacy shape the meaning of fraud. In Lawal, this tension was crystallised in FBI testimony establishing Classic Baggie's organizational role. When asked whether the south Florida group was operating independently, the agent testified: “We learned that the group was operating at the direction of an individual in Nigeria... he's better known publicly and to law enforcement as Classic Baggie.” According to documentation of the proceedings, the prosecutor characterised this as an international criminal enterprise. Here, fraud is cast firmly within the lexicon of organised crime, signalling hierarchy, coordination, and collective culpability. Such framing aligns with criminological research that emphasises how state actors construct the crimes of particular groups as existential threats by embedding them within broader narratives of societal decay, moral decline, and institutional fragility (Cohen, 2011; Garland, 2001). Yet this framing was contested within the courtroom itself. Defendants often resisted the language of ‘victims’, preferring instead to describe those they deceived as ‘clients’ or my partner's clients’. This semantic shift worked to neutralise blame by reframing fraud as a transactional relationship rather than predation, echoing Sykes and Matza's (1957) techniques of neutralisation. What prosecutors identified as exploitation, defendants reframed as entrepreneurialism, a form of digital hustle akin to legitimate business dealings. This contest over terms reflects broader cultural struggles over the moral boundaries of economic activity, including the emergence of cybercrime training academies (known as Hustle Kingdoms) (Lazarus et al., 2025; Lazarus & Soares, 2024). In diasporic and postcolonial West African contexts, informal economies have long blurred the line between necessity and criminality (Lazarus, Button & Adogame, 2022; Umar, 2023; Zakari & Button, 2022).
The discursive clash between entrepreneurial self-presentation and prosecutorial insistence on criminal organisation underscores that fraud is not only an illicit practice but also a symbolic economy. In the courtroom, categories such as ‘victim’, ‘entrepreneur’, and ‘organisation’ do cultural work: they assign blame, attribute agency, and delineate the contours of moral order. As scholars of legal sociology note, trials are performances where legitimacy is enacted and contested through language (Conley & O’Barr, 1990). The Lawal proceedings exemplify this, showing how offenders and state actors alike mobilised competing narratives to position fraud either as a business gone awry or as organised criminality. These divergent framings reveal the cultural contest at the heart of economic cybercrime. The same set of practices, setting up shell companies, cultivating online relationships, moving money across borders, was narrated as entrepreneurial innovation by some. By others, it was cast as organised fraud. The case demonstrates that legitimacy in cybercrime is not inherent but negotiated, contested, and performed in public forums such as the courtroom. From an Actor-Network Theory perspective, the courtroom operates as a networked arena in which human and material actants (defendants, prosecutors, legal documents, and digital technologies) interact to stabilise competing claims to truth (Callon, 1986; Latour, 2017). Social Network Theory, in turn, highlights how these performances are situated within broader relational fields of meaning and moral affiliation, linking local courtroom exchanges to transnational circuits of reputation and legitimacy (Lazarus, 2025, p.463-464; cf. Simmel, 1964).
Theme 6: Transnational Dimensions and Global Reach
The Lawal proceedings underscored that contemporary fraud is not contained within national borders but is sustained through global financial and social circuits. As one witness put it: We learned that the group was operating at the direction of an individual in Nigeria’. Interpreted across the wider testimony, this evocative image highlights the speed and reach of cyber-enabled fraud, in which illicit flows travel across continents in a matter of hours. The phenomenon exemplifies what scholars describe as ‘time–space compression’ (Harvey, 1989, p.98): the shrinking of distance and time through technological infrastructures that enable transactions to move faster than the legal frameworks designed to regulate them.
The global dimensions of hybrid fraud networks are visible in the coordination between US victims, European banks, and West African organisers. These overlapping jurisdictions expose law enforcement's structural limitations: while fraud moves seamlessly across borders, investigations must navigate fragmented accountability regimes (e.g., Abubakari & Amponsah, 2025; Lazarus, 2025; Levi, 2022). The result is similar to what scholars describe as ‘jurisdictional asymmetry’ (cf. Hombrado, 2011, p. 492). This article interprets jurisdictional asymmetry as the stalling or collapse of legal processes when offences are dispersed across states with uneven enforcement capacities and divergent legal regimes. At the same time, the transnational reach of these networks reveals their resilience. When one jurisdiction tightens its scrutiny, operations adapt by rerouting funds through alternative corridors, whether via European intermediary accounts, diaspora money mules, or West African shell companies (Abubakari & Amponsah, 2025). The ability to pivot geographically underscores that global fraud networks are not merely collections of actors but dynamic infrastructures that capitalise on the unevenness of global financial regulation.
The Lawal case thus illuminates a paradox. On the one hand, it demonstrates the remarkable reach and coordination of cyber-fraud, where money can circulate transnationally with minimal friction. On the other hand, it reveals how prosecutions are often forced into partial narratives, prosecuting only the actors within reach of a given legal system while leaving the wider network intact. This fragmentation reflects the structural gap between the global logics of fraud and the localised logics of law. Actor-Network Theory clarifies this tension by tracing how digital infrastructures (e.g., email systems, payment gateways, and corporate registries) function as global connectors that outpace local legal mechanisms (Vicsek et al., 2016). In parallel, Social Network Theory provides insight into how cross-border social ties and diasporic affiliations sustain these global flows, illustrating the interdependence of technical and relational connectivity in transnational cybercrime (cf. Granovetter, 1973; Lazarus, 2025).
Theme 7: Fragility and Risk Within the Network
Although the Lawal proceedings illuminated the transnational sophistication of hybrid fraud schemes, they also revealed something else. Often in the quiet ruptures of testimony, the fragility upon which such enterprises precariously rest came into view. Networks that appear seamless in the movement of money across borders are, at their social core, always vulnerable to collapse. Fraud organisations may operate with what seems like precision. Multiple LLCs are opened and closed with bureaucratic efficiency. Funds are wired across continents in the span of hours. Narratives of romance or corporate authority are performed with studied conviction. Yet all of this rests upon the unreliable scaffolding of interpersonal trust between actors who are themselves bound by secrecy, fear, and opportunism.
Theme 7a: Recruitment Through Incremental ComplicityThis fragility begins at the point of recruitment itself. Hermann's testimony revealed how individuals were drawn into the network through calculated escalation rather than coercion. Describing his initial involvement, Hermann recalled: “That started in -- at the end of -- towards the end of 20 -- November of 2019. He asked me to pick up $25,000 from someone in Fort Lauderdale in Florida, and it was supposed to go towards the purchase of the watch, because he was making payments, and I told him that we couldn't take cash because of the way my partners accept money, it has to be straight wired, the way you have been paying is already complicated, so I can't add cash to it, it's going to be too much, he did insist that I go pick up the money, because he said it would be safe with me, than the person he had the money with, so I went and picked up $25,000.” This exchange captures the threshold moment where legitimate business dealings morphed into criminal complicity. Hermann's initial resistance: “I can't add cash to it, it's going to be too much”, was overcome through Classic Baggie's reassurance that the money would be “safe” with Hermann. The framing of criminal activity as protective custody illustrates how trust-based manipulation facilitated recruitment. Small favors (holding $25,000) became gateways to larger laundering operations, demonstrating how cybercriminal networks expand not through coercion but through incremental normalisation of deviant activity.Yet this same trust-based recruitment strategy that enabled the network's expansion also ensured its vulnerability. The interpersonal bonds forged through “small favours” and shared profits proved brittle under state pressure.
Theme 7b: Testimony and BetrayalIt was here that the testimony of cooperating insiders and low-level money mules became most revealing. The very individuals tasked with moving and obscuring illicit funds also represented the weakest links in the chain. Their loyalty was contingent and easily unsettled once drawn into the orbit of law enforcement pressure. As one mule admitted under cross-examination, the shell company to which his name was attached existed only for the briefest of moments, long enough to open an account, receive a wire, and then vanish. Yet when questioned by investigators, he readily disclosed not only the transactional flows but also the identities of those further up the ladder. In doing so, he laid bare a structure that technological encryption had otherwise concealed. The same Hermann who initially resisted cash involvement: “it's going to be too much”, ultimately became the state's most detailed witness, methodically reconstructing the network's operations for prosecutors. This betrayal was not anomalous but structurally inevitable: actors recruited through trust and incremental complicity retained the capacity to exit through cooperation with authorities.
What emerges, therefore, is a paradox at the heart of cyber-fraud economies. The very dispersal of roles and functions that allows such networks to expand across continents is also what produces their brittleness. Each distributed node represents a possible breach, and each interpersonal relationship a potential site of betrayal. In this sense, resilience is not secured through technological sophistication. However, the advanced use of encrypted messaging platforms or disposable LLC filings may be an option. Rather, it is maintained through social secrecy and the careful calibration of trust. Both remain fragile under the pressures of greed, competition, and state coercion. Thus, the Lawal case reminds us that behind the prosecutorial characterisation as an international criminal enterprise lies a more precarious reality. In other words, behind the prosecutorial label of an ′international criminal enterprise′‚ lies a more precarious reality. It is a loose assemblage of actors whose capacity to endure rests less on invulnerability than on a continual balancing act. Exposure and concealment are perpetually negotiated. The same social fabric that sustains illicit enterprise also contains within it the seeds of its unravelling.
This paradox, where the same distributed structure that sustains illicit enterprise also renders it prone to collapse, has theoretical consequences. Recruitment through trust creates immediate operational capacity but long-term structural vulnerability. The paradox aligns with both theoretical perspectives. Actor-Network Theory exposes the instability of networks when a single actant (e.g., a money mule, platform algorithm, or communication channel) fails. Social Network Theory, in turn, highlights the fragility of trust-based structures where weak ties and opportunistic exchanges make betrayal inevitable (Callon, 1986; Granovetter, 1973, 1983). Together, these frameworks reveal that fragility is not an aberration but a structural feature of distributed criminal systems. These dynamics have direct consequences for regulation, investigation, and financial compliance, set out below in a focused set of policy and practice implications.
Policy and Practice Implications
The Lawal case yields actionable insights for regulators, law enforcement, and financial institutions confronting hybrid forms of online fraud. The findings underscore that cyber-enabled financial crime is not simply a technical or economic offence.
It is an adaptive socio-technical system sustained by relational, emotional, and infrastructural logics. Responding effectively, therefore, requires approaches that mirror this hybridity.
Regulation and Compliance Reform
Evidence from the Lawal proceedings highlights that laundering circuits exploit regulatory fragmentation. This is particularly evident in the formation and dissolution of LLCs used as disposable financial vehicles. Regulators should consider mechanisms for real-time verification and transparency of corporate registrations. These may include cross-border data sharing between company registries, banks, and financial intelligence units. Policies that address ‘ephemeral’ corporate entities could limit the use of shell firms as transient laundering infrastructures. Additionally, streamlining Know Your Customer processes across jurisdictions may reduce the asymmetries that allow transnational funds to move faster than investigative capacity.
Early Detection and Intelligence Integration
The case demonstrates that hybrid fraud schemes, combining romance and BEC elements, remain undetected because investigative systems treat emotional and commercial frauds as separate domains. Integrating relational and transactional data analytics could change this. For example, linking suspicious email correspondence with reported romance fraud could allow financial institutions and enforcement agencies to identify cross-modality patterns earlier. Enhanced coordination between cybercrime units and financial regulators could also support joint typology databases. Such databases would capture the convergence of emotional manipulation and business deception.
Law Enforcement Practice
The ethnographic evidence reveals that networks depend as much on interpersonal trust and affective persuasion as on technological sophistication. Training for investigators should therefore extend beyond forensic accounting to include behavioural and cultural competencies. These competencies include understanding emotional scripting, symbolic narratives of legitimacy, and postcolonial moral economies that offenders invoke. Building capacity for forensic ethnographic methods is also critical. Systematic analysis of courtroom transcripts, communication scripts, and digital artefacts would strengthen investigative insight into the social architectures of fraud.
Financial Sector Engagement
Banks and fintech platforms occupy a crucial position in detecting and disrupting money laundering circuits. However, compliance teams often focus narrowly on transaction anomalies rather than on narrative coherence (how storylines in communication mirror fraudulent intent). Developing cross-disciplinary threat intelligence teams could enhance the identification of hybrid fraud schemes. These teams should combine financial analysts, linguists, and sociologists to interpret both quantitative and qualitative indicators. Moreover, partnerships between banks and social media companies could help flag transfers linked to manipulative emotional scripts before losses escalate.
Transnational Cooperation and Capacity Building
The Lawal case exposes the structural limits of national jurisdiction when offenders operate across legal systems of uneven capacity. Policymakers could strengthen bilateral investigative frameworks with West African jurisdictions by supporting digital forensics infrastructure and data-sharing agreements. They could also integrate non-Western epistemologies of fraud into policy design. Recognising how offenders frame deceit as economic opportunity or digital entrepreneurship can inform culturally sensitive prevention messaging.
Ethical and Preventive Communication
Public awareness campaigns should evolve beyond warning about ‘romance scams’, or ‘business frauds’ as distinct threats. Instead, communication should stress their shared infrastructures and emotional architectures. This would help potential victims and intermediaries recognise hybrid manipulation tactics more effectively. While these recommendations translate the study's conceptual contribution into clear policy and practice orientations, they position cyber-fraud as an ecosystem of technological, emotional, and institutional interdependencies. By treating fraud as both a financial and relational system, regulators, financial actors, and law enforcement agencies can intervene earlier and more effectively within the circuits where deception, capital, and affect intersect.
This study, therefore, directly responds to three gaps identified in the literature. It provides empirical depth by treating courtroom proceedings as ethnographic data rather than as legal artefacts; theoretical integration by combining Actor-Network and Social Network perspectives to link infrastructural and relational dynamics; and evidential novelty by demonstrating how romance and BEC schemes converge within a single organisational system. In doing so, it anchors its contribution within emerging debates on hybrid fraud infrastructures and extends current criminological understanding beyond behavioural or technological models. While the preceding section outlines how the Lawal case informs practical interventions for regulators, law enforcement, and financial institutions, its implications extend beyond the policy arena to the theoretical domain.
Theoretical Implications
The United States v. Lawal case contributes to criminological and sociological research by reframing cyber-enabled fraud not merely as a technical act of deception or the deployment of digital infrastructure, but as a hybrid cultural and organisational practice situated within transnational networks. The evidence highlights online fraud as both socio-technical and socio-cultural. Indeed, the activities of the offenders mobilise modular identities, affective scripts, and global laundering infrastructures, while being embedded within broader structures of the global political economy (Franceschini et al., 2024; Hall & Yarwood 2024; Lazarus et al., 2026; Lazarus, 2026; Luong & Ngo, 2024; Sarkar & Shukla, 2024). From this case, six theoretical interventions emerge.
Hybrid Modality and Tactical Dualism
The co-existence of romance fraud and BEC within Olugbenga Lawal's network illustrates what may be termed tactical dualism, the blending of intimacy-driven narratives and corporate impersonation within a single operational repertoire. Rather than opportunistic deviations, these hybrid scripts represent deliberate strategies of flexibility and scalability, extending prior observations of diversification in cybercrime (Hutchings & Holt, 2015). Fraud is staged across multiple registers, emotional, financial, organisational, where each script reinforces the other, maximising reach across victim groups. Drawing on the dual-theoretical framework introduced earlier, this discussion interprets the findings through Actor-network theory and Social Network theory. Considered as a whole, these two perspectives position hybridonline fraud as both an infrastructural and relational system, providing the conceptual foundation for the following theoretical interventions.
Identity Modularity as Criminal Infrastructure
The repeated switching between roles, boyfriend, grieving heir, business partner, corporate vendor, demonstrates identity modularity, a performative system where fluid personas function as infrastructural components of deception. Drawing on Goffman's (1959) dramaturgy and Donath's (1999) analysis of digital persona construction, Olugbenga Lawal's practices suggest that identity is not simply a disguise, but an operational toolkit calibrated to fit shifting contexts. Modularity provides continuity. While one persona falters, another emerges to sustain credibility, highlighting identity not as concealment but as an adaptable architecture of fraud.
Laundering Circuits and Improvised Infrastructures
The use of disposable LLCs, shell companies, and mule hierarchies exemplifies what can be termed laundering circuits. These infrastructures embody the classical placement-layering-integration sequence of money laundering (Cassella, 2018; Naylor, 2004; Sultan & Mohamed, 2024), yet with improvisational twists. Rather than permanent vehicles for wealth management, LLCs in this case acted as disposable scaffolding, entities created to open an account, receive a wire, and then dissolve. Testimony reveals both the sophistication and precariousness of these circuits, reminding us that laundering is a practice of continuous improvisation as much as institutionalised routine.
Emotional Economies and Moral Disengagement
Online fraud in Olugbenga Lawal's case hinged on the instrumentalisation of affect. Scripts of love, urgency, and dependency were weaponised to convert intimacy into capital. This resonates with Bandura's (1999) framework of moral disengagement. Empirical findings on online fraud issues in Nigeria and beyond, using Bandura’s moral disengagement framework (Lazarus, 2018; Lazarus, Olaigbe & Lazarus, 2026), show how offenders justify deception by reframing intimacy as transactional and displacing responsibility. Emotions functioned as rehearsed scripts. They were strategically deployed to produce dependency and accelerate financial compliance. Online fraud is therefore revealed not simply as deception, but as a socio technical dramaturgy in which affect is cultivated as resources within illicit economies.
Courtroom Framing and Competing Moral Vocabularies
The courtroom emerged as a contested arena in which competing narratives of legitimacy were advanced. Prosecutors framed Lawal as part of an ‘international criminal organisation’ (Warner, 2024a, p.1), stressing structure and victimisation, while defence accounts positioned him as an entrepreneurial actor navigating global opportunity. This tension illustrates the cultural sociology of fraud. What counts as entrepreneurship or organised cybercrime is negotiated through competing moral vocabularies, each invested in producing legitimacy or illegitimacy (see Lazarus, Olaigbe & Lazarus, 2026, drawing on Sykes & Matza, 1957; Bandura, 1999). Such framings are not incidental but constitutive, shaping how fraud is recorded, judged, and remembered.
Network Fragility and Contingent Trust
Despite global reach, the network's endurance rested on fragile trust relations. Insider cooperation, mule testimonies, and law enforcement pressure revealed how easily the infrastructure could be undone from within. Cybercriminal networks, though technologically sophisticated, are sustained primarily through secrecy and interpersonal trust, both of which are precarious under conditions of surveillance, greed, and betrayal (cf. Lazarus, 2025; Levi, 2022). The Lawal case, therefore, draws attention to the paradox of online fraud schemes. These hybrid fraud schemes are structurally resilient across borders, yet internally vulnerable to collapse. These interventions extend debates on organisational crime and transnational deviance by positioning hybrid fraud not as ad hoc criminality but as a structured, dramaturgical, and affective enterprise, sustained by modular identities, improvised infrastructures, and fragile trust.
Limitations of the Study
This study employs a single-case design centred on the Lawal proceedings. While single-case approaches are well-established, the reliance on a US Department of Justice pretrial detention memo and associated court documents creates interpretive limitations. As state-authored data, these records are shaped by prosecutorial logics of establishing risk, culpability, and organisational structure, rather than providing ethnographic texture or offender self-narratives. Offender rationalisations appear only indirectly, filtered through state interviews, testimony fragments, or inferred from communications and laundering practices.
Nonetheless, the richness of these legal records allows them to be read as criminological archives, revealing architectures and imaginaries of fraud otherwise inaccessible to researchers. When treated as forensic ethnography, they provide a unique vantage point into hybrid fraud, offering both empirical depth and conceptual leverage. Despite interpretive limits, the OlugbengaLawal case advances theoretical debates by reframing fraud as dramaturgical, infrastructural, and globally entangled, while exposing the paradox of resilience and fragility at its core.
Conclusion
This article advanced three interlinked propositions. First, hybrid fraud schemes exceed typological boundaries and demand alternative conceptual vocabularies. Second, that identity within cybercrime is not merely enacted but functionally distributed across infrastructural roles. Third, that illicit capital flows often reflect aspirational logics rooted in postcolonial geographies of value. By treating courtroom documents and testimonies as ethnographic artefacts, the study contributes to criminological understandings of crime, mobility, and symbolic power in a digitised and structurally unequal world. Through a case-based analysis of the United States v. Lawal, the article illustrated how contemporary cybercrime operates as tactically hybrid, affectively scripted, and transnationally embedded. The analysis traced the convergence of romance fraud and BEC as modular scripts; the instrumental use of disposable companies and aliases as laundering scaffolds; and the circulation of stolen funds as expressions of both criminal futurity and fragile dependence on social trust. These insights reinforce existing literature on fraud diversification and laundering mechanisms while opening new pathways for theorising cyber-enabled crime as a socio-technical dramaturgy situated within global hierarchies.
Rather than treating Lawal's operation as the work of an isolated entrepreneur, the case underscores the importance of viewing hybrid fraud schemes as structurally and symbolically embedded within broader circuits of digital labour, courtroom contestation, and capital mobility. The conversion of intimacy into transactional leverage, and of wire transfers into dispersed accounts across Delaware, Accra, and Lagos, reveals a logic that extends beyond short-term theft. Online fraud here emerges as both precarious and aspirational: a technology of reinvention, tethered to global infrastructures yet perpetually haunted by betrayal, exposure, and collapse. At a theoretical level, the paper introduces conceptual tools, including laundering circuits, emotional scripts, and network fragility, that may be extended to other cases where fraud is simultaneously resilient and vulnerable, global and intimate. These terms are not offered as fixed typologies, but as situated heuristics that foreground the evolving complexity of online fraud and its embeddedness in moral rationalisations, spatial strategies, and contested narratives of legitimacy.
Nonetheless, the analysis is limited by its reliance on a single legal case. Future research should triangulate such data with interviews with offenders and victims, tracing how these infrastructures are lived and contested outside the courtroom. Future research would also benefit from integrating indictments with other layers of legal process, including appellate opinions, as well as with investigator narratives, thereby expanding the empirical and interpretive scope. Still, the present study demonstrates that legal documents, when read ethnographically, can serve as critical archives of deviant practice, revealing not only what offenders do but how states narrate their actions, how networks fracture under pressure, and how illicit capital moves across borders faster than law enforcement can follow. This paper argues that hybrid online fraud, when viewed through the lenses of modality, identity, and mobility, demands a rethinking of its criminological classification and its cultural economy. It is not enough to categorise fraud schemes by surface method or victim profile. To understand the full architecture of digital deception, we must attend to its infrastructures of laundering, its affective dramaturgies, and its spatial trajectories. By integrating Actor-Network and Social Network perspectives, the study situates hybrid cyber-fraud within interconnected technological and relational systems, spotlighting how infrastructures and social ties co-produce deception and mobility across borders. The Olugbenga Lawal case, thus, invites comparative dialogue between North and South contexts on the symbolic economies, vulnerabilities, and global circuits that define the cultural sociology of fraud today.
Footnotes
Acknowledgements
The author gratefully acknowledges Gary Warner for generously sharing resources related to United States v. Olugbenga Lawal, including his Classic Baggie blog series. His contributions enhanced the empirical depth of this article.
Funding
The author received no financial support for the research, authorship, and/or publication of this article.
Declaration of Conflicting Interests
The author declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Permission to Reproduce Material
Permission to reproduce material from other sources was not required.
