Abstract
This article investigates the temporal and material relations of secrecy and revelation through the lens of haunting. Critical security scholars have contributed to a deeper understanding of (state) secrecy by unpacking the material and discursive practices that conceal, reveal, or expose information, showing that there is no linear process from secrecy to transparency and accountability. In this article, I contribute to this literature by developing haunting as a concept to study how secrets from the past continue to shape the possibilities of political and legal debate in the present and future. I propose attending to how secrets can haunt specifically in situations where legal transgressions and violent politics are erased. I illustrate this conceptual framework through a case study of two secret operations in the War on Terror by the Dutch Ministry of Foreign Affairs. I illustrate how in both instances, secrets refused to remain buried, but rather came back to haunt public and political discussions about accountability. Based on the empirical insights, the conclusion presents future possibilities for studying secretive security issues through a framework of haunting.
Introduction
In 2019, two investigative journalists revealed that the Dutch government was involved in a secret programme to support armed groups in Syria (Holdert and Dahhan, 2018a). The purpose of this so-called Non-Lethal Assistance programme (hereafter NLA programme) was to strengthen the position of Syrian ‘moderate’ armed groups vis-a-vis terrorist organizations and the Syrian regime (Holdert and Dahhan, 2018c). The publication of the secret support sparked a scandalous media representation of the NLA programme, including allegations that it could be a violation of international law. Media attention was focussed on speculations about terrorist groups benefitting from the materials sent as part of the programme. Domestic lawyers involved in terrorism trials in the Netherlands anticipated a great impact on the possibility to prosecute and convict terrorism offences regarding terrorist organizations in Syria. Despite these concerns, the concrete impact on terrorism trials remained very limited and the potential breach of international law was dismissed by the Ministry of Foreign Affairs (TK, 2018–2019, 32623, nr. 247: 4).The lack of accountability after the secrets were published concurs with Stampnitzky’s (2020: 608) analysis of revelations of torture in the War on Terror, where ‘[i]t is commonly assumed that exposures lead directly to accountability, or realigning actions so as to be compatible with stated normative commitments’. Yet, as she eloquently shows, the revelation of state secrets does not automatically translate into a correction of norms violated, but is a political process that requires more scholarly attention to better understand its effects.
In a similar way, there is more to the story of the NLA programme than a (disappointing) revelation of state secrets. As I will show in this article, during the process of scandalous exposés related to the NLA programme, secret information was first revealed, then reclassified. Important documents containing state secrets disappeared, only to reappear later through accidental leaks. Even though many details of the programme were accidentally revealed, this information remained officially classified and could not be used in a court of law. Furthermore, the legal discussions about the programme were linked to previous Dutch interventions that were also (partially) secret. While there were no concrete legal consequences for the violations of legal norms, the NLA programme continues to be invoked during court cases and legal debates. This is an example of a state secret that lingers, not fully materializing into accountability or normative change, yet also not completely covered up or dismissed. How can we understand the afterlives of secret counter-terrorism practices, especially when those secrets remain in an ambiguous state?
To answer this central question, I propose to study secrecy and state violence through the lens of haunting (Gordon, 2008). While critical security scholars have enriched our understanding of secrecy as a complex sociomaterial practice (De Goede et al., 2019), or by unpacking the processes of exposure and revelations (Birchall, 2021; Stampnitzky, 2020), the debates on critical security studies, secrecy and silences pay surprisingly little attention to the temporal dimensions of secrecy. Nevertheless, to better understand how past secrets shape politics in the present or future, we need examine temporal workings of secrecy. The concept of haunting allows researchers to unpack how secrets follow a non-linear temporality where secret operations refuse to remain in the past and continue to shape what is made (un)intelligible in the present and future. Thus, by using haunting as a conceptual metaphor, this article offers a fresh perspective on how the unruly, invisible and often violent histories of state secrecy are part of the present and future. Haunting as a concept strengthens the scholarly debates in critical security studies on secrecy, showing how (partial) revelations of legal transgressions and erased forms of violence haunt political and legal debate in the present and future. More broadly, haunting connects the security studies to debates on temporality, secrecy and silence, and allows researchers to explicitly engage with the non-linear and disruptive ways in which materials reveal, conceal, or suppress secrets.
The purpose of this article is to set forth a novel theoretical framework of haunting to study secrecy in security settings. First, I briefly summarize the different strands of research within critical security studies on secrecy. After this summary, I develop a conceptual framework on haunting, building on the literature on secrecy and connecting to broader themes in international relations on temporality, legality and memory. In the second part of the article, I empirically illustrate how we can mobilize haunting for studying state secrecy in case of legal transgressions, applying the concept to an empirical case study of two counter-terrorism interventions by the Dutch state. The conclusion summarizes how haunting pushes current debates by allowing researchers to capture the non-linear temporalities of secrecy and security. Furthermore, haunting strengthens the literature on materiality and secrecy by emphasizing the agency of ‘buried’ or ‘erased’ materials coming back to haunt. In sum, this article proposes that haunting is useful for understanding secrecy in the War on Terror, but its applicability extends to other fields of controversies and violent histories.
State secrecy in critical security studies
Over the past years, critical security scholars have expanded our understanding of secrecy not as a given, but as a practice involving multiple security actors and devices (De Goede and Wesseling, 2017; De Goede et al., 2019; Walters, 2021). This comes as no surprise, as the field of security is inherently characterized by practices of classification and confidentiality, especially when it comes to counter-terrorism policies (Gilbert, 2023).
Within critical security studies, several conceptual debates have furthered our ability to study secrecy. Critical security scholars (De Goede and Wesseling, 2017; Glouftsios, 2023), inspired by actor-network theory, have proposed to study the material devices and processes that produce secrecy. Burying documents, classifying reports or severely obstructing freedom of information (FOI) requests show the central role materials can have in maintaining secrecy (Hughes and Garnett, 2019). Within this research agenda, secrecy is not a general phenomenon that is easily translatable into a theory, but researchers attune to the fluid and material characteristics of secrecy and its practices (Glouftsios, 2023; Walters, 2021). This research approach illustrates that secrecy is a complex process of publication, withdrawal, concealment and other messy material practices.
More recently, critical security studies scholars have turned their attention to the process of revelation and exposure, critiquing the assumption that secrecy opposes openness (Birchall, 2021) or forms ‘a stumbling block on the road to transparency’ (De Goede and Wesseling, 2017: 259). Treating exposure not as a sudden revelation that breaks through the veil of secrecy but as ‘a socially and politically constructed process’ is at the core of Stampnitzky’s (2020) argument. She proposes to distinguish between an exposure, which is the release of classified information, and a revelation, where information gains meaning through a process of public recognition. Similarly, Rappert (2010) and Gilbert (2023) have reflected critically on moments of disclosure, criticizing the assumption that these moments are an unmediated exposure to the truth. This research agenda illustrates how processes of exposure, revelation, or access require further scholarly attention to better understand what is made possible or knowable (Aradau, 2017; Birchall, 2021; Gilbert, 2023; Rappert, 2010; Stampnitzky, 2020).
Lastly, critical security scholars have proposed to study the material and discursive processes that lead to afterlives, such as public inquiries, memory-related practices, or journalism. This strand of research is particularly important to further develop our understanding of the normative aspect of secrecy. As such, scholars such as Stampnitzky (2020), Birchall (2021) and Aradau (2017) push back against a linear trajectory that supposes that revelation of secrets will lead to transparency, knowledge, acknowledgement of wrongdoing and justice. For example, the exposure of information on the use of torture by the US government in the War on Terror did not automatically lead to a normative reaction or accountability (Stampnitzky, 2020). Particularly in the context of the War on Terror, which is heavily characterized by classified information for security purposes, it is important to understand the afterlives of secret state programmes. Kearns (2017), for example, draws our attention to the notion of ‘residues’ as a way to understand absences in the public knowledge in the aftermath of drone warfare. He defines residues as ‘processes of state violence that are ongoing in the present but remain absent from the public sphere’ (2017: 16). This aligns with the growing research agenda to take secret state actions as researchable, even if it is through fragments, memories or leaks, by moving beyond the stark bifurcation of knowledge on the state as public or concealed, absent or present (Gilbert, 2023; Hughes and Garnett, 2019: 222; Rappert, 2010).
These debates within international relations and critical security studies illustrate a growing and vibrant debate on secrets and their (material) afterlives. The notion of secrets coming back to haunt is recognized on a superficial level by security scholars (Kearns, 2017; Rappert, 2010; Walters, 2021). De Goede and Wesseling (2017: 264) write that ‘Secrets continue to haunt the publicness of post-9/11 security programmes, in the sense that they entail complex regulations of knowledge and have a material effect on how public debate is (not) able to unfold’. It should not come as a surprise that the field of security politics is haunted by a violent past. Devetak (2005: 622) argues that ‘politics and international relations have always been haunted by monsters and ghosts . . . but since September 11, the gothic scene has become a much more prominent discursive feature of international relations’. While this shows that critical security scholarship has already hinted at state secrecy in the War on Terror as a haunted practice, a comprehensive understanding of haunting as a useful concept in security studies has not been developed.
Haunting for critical security scholars
The concept of haunting and the literature on spectrality is indebted to Derrida’s (1994: 75) work ‘specters of Marx’, where he proposes that ‘the ghost should remain, be lived with, as a conceptual metaphor signaling the ultimate disjointedness of ontology, history, inheritance, materiality and ideology’. Although this article does not delve deeply into Derrida’s work or the ‘spectral turn’ (Del Pilar Blanco and Peeren, 2013), it follows Derrida’s suggestion to stay with the ghostly and the haunted. Scholars such as Gordon (2008), Spivak (2013), Salem (2019) and Del Pilar Blanco and Peeren (2013) use haunting as a conceptual tool to interrogate forms of knowledge production, and as a vocabulary to capture what is systematically removed from visibility and written out of history, yet somehow remains lingering in articulations in our daily lives. Haunting is political: the politics of slavery, national security, imperialism continue to haunt new political projects or ideologies and shape what can be said or done in novel forms of governance (Salem, 2019).
This theoretical framework sets out how haunting as a concept is useful for security scholars studying state secrecy. Haunting provides a non-linear temporal approach to research how the past controls the present and future. In a sociolegal context, haunting allows us to understand how normative legal decisions in courts are shaped by, and cannot escape, historical violence and silence (Wilke, 2010). Similarly, haunting has been used to understand how societies in transition are haunted by previous politics, oppression and state violence (Gordon, 2008; Salem, 2019). In this framework, I set out how critical security scholars can use the concept to research how secrets from the past hold a power over the future, shaping the possibilities of political debate and contestation. As such, this conceptual framework illustrates how haunting is a useful tool to problematize the linear path from secrecy to knowledge to accountability by illuminating the non-linear temporalities of secrets and their political or legal effects. I propose that two characteristics of haunting are essential to deploy the concept for the study of secrecy: first, a non-linear engagement with temporality, and second, attention to silences and absence. Both characteristics place haunting in the existing debates in international relations on temporality, memory, materiality, but also push our understanding of secrecy and security.
Secrecy, security and temporality
Secrets are inherently entangled with temporality. Secrets can be temporally limited when documents or policy information are automatically declassified after an amount of time (Thompson, 1999). Sometimes secret spaces contain traces of multiple pasts, rather than only a singular temporality, as they become repurposed or reclassified (Walters, 2020). Specifically for security scholars, understanding the temporality of secrecy is essential as pre-emptive security measures are also justified by temporal practices. Think for example of pre-emptive security logics that build on imaginations of a potential terrorist attack (Anwar, 2022), climate disaster (Wolff, 2021), or the framing of violence in wartime (McIntosh, 2022; Palestrino, 2022). Secrecy in security measures is therefore already entangled with temporal politics.
Similarly, narratives of the past have been essential in the securitization of memories, shaping identities of states and their security policies (Mälksoo, 2015; Purdeková, 2022; Steele, 2013). Indeed, memory studies have contributed greatly to international relations scholarship by illustrating how events in the past continue to shape security objectives, (state) identity and politics in the present (Mälksoo, 2015). There is an obvious link between haunting and the security–memory nexus as established by other scholars (Derrida, 1994; Gordon, 2008; Roccu and Salem, 2019). Both memories and haunting cannot be confined to the realm of the past, nor are they an individual private experience. Rather, they continue to shape social relations, material conditions and politics of the future (Salem, 2019). As a concrete example, Gordon (2008) and Hartman (2008) have studied the transatlantic slavery archives as haunted records of an unfinished past. Those who are forced into slavery and erased from historical records are not absent but continue to linger and live on in memories (Hartman, 2008) but also in material and political relations in the present and future (Gordon, 2008). Similar to memories, haunting provides the vocabulary and ontology for studying events that continue to linger on, even after they were supposed to be ‘finished’ or ‘forgotten’ (Gordon, 2008; Purdeková, 2022).
While the literature on secrecy in critical security studies has moved beyond the assumed binary between secrecy/transparency (Birchall, 2021), scholars have paid only limited attention to how secrecy and transparency are linked with temporality. Haunting as a concept is useful for critical security scholars when unpacking how secrecy orders and disrupts temporality. While governments might aspire to contain information in a specific time through secrecy measures, haunting allows us to study ways in which past secrets or future revelations can determine the conditions of what can be said in present-time political and public debate. Thus, haunting attunes us to disruption: past violence, exploitation, or imperialism does not only shape our present and future understanding of (international) security, but the concept allows us to study how silenced episodes of violence come back to haunt, demonstrating an unexpected agency to make the past knowable. Haunting moves us beyond a linear narrative on temporality by allowing researchers to actively investigate reparations, recognition, restoration and other practices that transcend the neat categories of past, present, future (Gordon, 2008). Such moments are temporal practices but require a specific non-linear attention to temporality that haunting provides.
Silence and security
Scholars studying archives have reflected extensively on how to study silences and histories that are silenced (Gordon, 2008; Hartman, 2008; Manchanda and Salem, 2020), for example by re-telling their stories through fiction and fabulation (Hartman, 2008). Similarly, international relations scholars have examined silences in international relations as a spectrum: not the opposite of disclosure but rather as ‘layers of silences’ through ‘ambiguities, delays, explicit refusals to answer’ (Schweiger, 2022). Schweiger’s layers of silences speaks explicitly about the question of accountability in relation to silence and speaking up. Schweiger (2022: 125) warns us that ‘[c]alling for less secrecy can end up reaffirming the power position of Western state actors who are asked to speak while the subaltern become further essentialised and silenced’, thus resulting in further injustice.
Haunting as a metaphor provides a novel way to study secrecy through its disruptive temporal understanding. Through haunting, we acknowledge that secrecy is not a matter of transparency or disclosure (Birchall, 2021), but that the concealed knowledge or erased experiences live on in various and unexpected ways. More specifically, as Gordon (2008: xvi) writes, haunting occurs not for all secrets, but ‘what’s distinctive about haunting is that it is an animated state in which a repressed or unresolved social violence is making itself known’. As such, haunting pushes the existing literature on secrecy and transparency (Birchall, 2021; De Goede and Wesseling, 2017), as well as the debates on silences (Rappert, 2012; Schweiger, 2022), by focusing on a longer temporality in which secrets return or how material traces of the secret re/disappear again. According to Gordon (2008), haunting makes itself known through ‘uncanny repetitions’. Thus, haunting specifically draws our attention to reappearances of security objects: whether classified documents (Gilbert, 2023), residues (Kearns, 2017), or restored malls after a violent attack (Purdeková, 2022), haunted secrets are repetitive. Therefore, haunting as a concept moves us beyond the acknowledgement that materials break through binaries of secrecy and transparency: haunting requires attention to how objects are lost, gained again, reshaped or disappear (Gordon, 2008; Hartman, 2008). Haunting does not end with (partial) disclosure, as haunting rejects a linear approach to temporality altogether, but rather invites us to look at reappearances of materials and their resistance against disappearance. Indeed Spivak (2013) proposes that ‘the end of the ghost dance is to make the past a future’, referring to a future in which past injustices are faced and accounted for. In other words, researching secrecy through haunting is less about the visibility of the knowledge or the concealed materiality, and more about how secrets of the past hinder normative response or obstruct accountability.
Haunting and political possibilities
The two interrelated characteristics, namely a non-linear focus on temporality and a novel attention to silences through reappearances, are key to understand the conceptual relevance of haunting. By following a non-linear temporality, haunting allows us to study how past secrets and silence around violence and transgression shape the possibilities of accountability in a present and future. Therefore, we gain a better understanding how state secrecy shapes security policies, particularly in the absence of accountability and normative change.
It is no coincidence that the contributions mentioned in this conceptual part mainly focus on the workings of empire, colonialism and violence. As Stoler (2016) has argued, postcolonial politics, even if their workings are made invisible, continue to haunt and shape contemporary political narratives. As explained above, there are different ways to examine violent injustices, ranging from memory studies to tracing the spectres of coloniality. Yet, what is distinct about haunting is that it attunes us to how past violence shapes political possibilities particularly sensitive to postcolonial and imperialist politics (Gordon, 2008; Salem, 2019). Haunting is not only about acknowledging or remembering the past, but understanding how it fits into a longer colonial trajectory and how its afterlife creates or prohibits opportunity for (future) political change. For example, Salem (2019) shows how Nasserism as a political project in postcolonial Egypt has profoundly influenced ideas about what politics should look like, shaping the (im)possibilities of a capitalist politics in Egypt. Similarly, Wilke (2010) uses haunting to trace the trials of Nazi perpetrators and the impunity of Nazi judges, illustrating that the prosecution of former Nazis in the 1990s in Germany was haunted by earlier judicial decisions in 1940–1950. Earlier trials and injustices curtailed the possibilities of the court to sentence, for fear of moral and legal criticism. In sum, secrets come back to haunt the present in situations of an absence of accountability or justice for legal or normative transgressions.
Haunting therefore shapes the conditions of security policies and politics more broadly (Salem, 2019), yet has not explicitly addressed secrecy as an inherent part of security (but see Walters, 2021). It is through secrecy that policies gain or lose legitimization. Security professionals insist on keeping information classified, to not alert potential terrorists or criminals to their security measures (De Goede et al., 2019; Walters, 2021). Secrecy holds power over security practices, by creating hierarchies of knowledge and authenticity, even though secrecy is fragmented, sometimes invisible, and not easily accessible (Walters, 2021). Considering such characteristics of secrecy, haunting provides a useful vocabulary to study how secrecy works as a condition for security practices. It can attune us to how erased histories of state violence and imperial forms of governance shape security politics during and after revelations of security secrets. Thus, as I will illustrate with an empirical case study below, haunting is different from Kearns’ (2017) conceptualization of ‘residues’, ‘absent-presences’ (Rappert, 2010), amnesia (Purdeková, 2022), or silence (Schweiger, 2022), and pushes our understanding of how haunted secrets of the past live on in our present and future.
Haunted histories of military intervention: A methodology
This article illustrates the relevancy of haunting through an empirical case study of two Dutch counter-terrorism interventions, namely the Dutch participation in the 2003 intervention in Iraq, led by the US, and the NLA programme between 2015-2018. I started this research by studying the news coverage around the NLA programme. During the data collection, I learned about another counter-terrorism intervention in 2003. Secrets were revealed about both interventions in a very similar way, as were the legal boundaries that had been crossed. In the public inquiry that followed the revelation of the NLA programme, this 2003 scandal was frequently mentioned and seemed to ‘haunt’ what happened in the programme. For this reason, I proceeded to analyse the two cases side by side, to better understand how these past events from 2003 had impacted the NLA programme more than 10 years later and how haunting connected both secrets. While the 2003 scandal was not the initial focus of this research, Gordon (2008: 37–39) argues that haunting requires a methodology of detours.
Between 2018 and 2022 I collected data to conduct a qualitative analysis on the question of secrecy and haunting. I collected various sources of government documents, including the FOI requests on all governmental correspondence about the NLA programme consisting of 600+ pages, reports of both public inquiries of the NLA programme published in 2022 (Commissie Cammaerts, 2022) and the Iraq intervention published in 2010 (Commissie Davids, 2010) and parliamentary debates on the NLA programme (TK, 2018–2019, 32623, nr. 247; TK, 2018–2019, 32623, nr. 268; TK, 2019–2020, 32623, nr. 292). This data was complemented by court transcripts of terrorism trials debating the NLA programme (The Appeal Court of The Hague, 2019; The District Court of Rotterdam, 2019) and news reports by NOS/Nieuwsuur (Holdert and Dahhan, 2018a, 2018b, 2018c). The documents were retrieved by searching LexisNexis and the Dutch database for government documents using keywords including ‘NLA program’; ‘non-lethal assistance’; ‘Syria’.
I analysed two public inquiries reports and news coverage related to both scandals in line with the conceptual framework established in the previous section. After a process of coding the documents along these themes, I traced how the data of the NLA programme related to the data of the Iraq intervention of 2003. Reading both public inquiry reports through the lens of haunting shows us how the two interventions, a decade apart, haunt each other. This is a methodology of detours, following the data rather than selecting it, and allowing the secrets to haunt freely. In the following sections I unpack the afterlives of both secrets using haunting as a conceptual framework. The conclusion connects the empirical insights of this study to a conceptual framework of haunted materials that can be explored in further research.
Haunting as temporal ordering
In 2003, the Dutch government politically supported the US-led coalition in Iraq that eventually resulted in the toppling of former Iraqi president Saddam Hussein (Aalberts, 2011). Participating in this coalition was already highly contested and questioned by legal advisors within the government and members of Parliament (Aalberts, 2011). At first, the discussion mainly concerned information of foreign intelligence services claiming the presence of weapons of mass destruction, which formed the justification of the intervention (Commissie Davids, 2010). However, approximately in April 2003, an administrative memo was sent to the Minister of Foreign Affairs clearly outlining the judicial concerns of the legality of the US-led intervention and concluding that the legal justifications for the intervention could best be understood as ‘paper thin’ (see Figure 1). The memo, however, never reached the minister as it ‘disappeared’. At the top of the memo, a military officer scribbled ‘Carefully store in a drawer for the next generation. The discussion is now closed.’
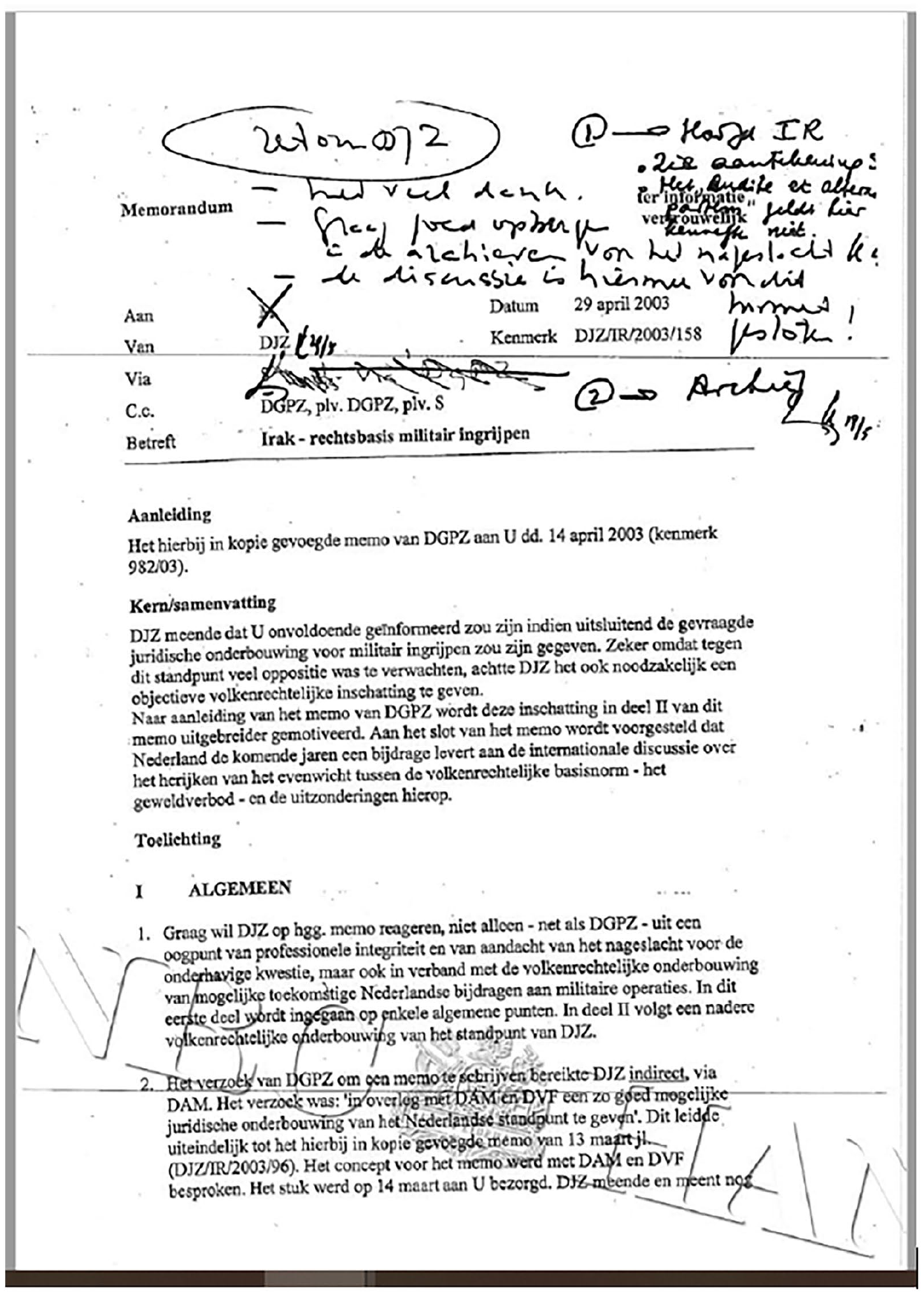
Screenshot by the author of the disappeared memo to the minister as published in the NRC Handelsblad.
The note on the memo, ‘Carefully store in a drawer for the next generation. The discussion is now closed’, showed the desired temporal working of the secret: to be erased from the present, and to be considered by future colleagues as a question that came to a (temporary) closure. Secrets and their revelations illustrate a temporal practice of placing certain objects and information into the past, present or future.
After the memo was leaked and printed in the Dutch newspapers in 2009, a committee was established to conduct a public inquiry into Dutch support of the Iraq invasion. The Commissie Davids was tasked with reconstructing the events and material documentation that could answer questions of international law and domestic political procedures. The report was published in 2010, consisted of more than 500 pages, and laid bare the poor decision making in 2003. The report was therefore considered a public acknowledgement of past wrongdoings and provides clear recommendations for the future: an international lawyer should be consulted for advice on new interventions, information sharing between the departments should be improved, and classified information should be periodically evaluated on their secret status (Commissie Davids, 2010). In other words, not only was there a collective agreement on preventing such legal and political scandals, but there was also a clear outlook for the future on ways to act differently.
This ‘future’ came in 2015, when the Ministry of Foreign Affairs was contemplating whether to join other European states in supporting moderate armed groups in Syria. Bureaucrats at the Ministry of Foreign Affairs argued that seeking official advice from the newly appointed lawyer on the legality of the programme and possible breaches under international law was not necessary (Commissie Cammaerts, 2022). Strictly speaking, the NLA programme was framed as a civil operation and only provided non-lethal assistance. The materials that were part of this so-called non-lethal assistance were pick-up trucks, satellite phones, medical kits and food packages. The question whether these materials could potentially be used for lethal objectives during combat was strategically dismissed (Anwar, 2024). The choice to conduct a civil operation rather than providing groups with military support justified the decision to avoid seeking legal advice from international lawyers on the legality of the programme. The Ministry only sought internal advice that classified the secret programme as ‘a grey area’ and ‘risky but acceptable under international law’ (Commissie Cammaerts, 2022).
This example illustrates how secrecy can hold a temporal power over events and how past secrets disrupt or shape the present. Secrets are not contained controversies in a closed-off past but can haunt the future by shaping the boundaries of political and legal discussion. In the NLA programme, the decision-making process related to providing non-lethal support was clearly haunted by these earlier revelations from 2003: the Dutch government wanted to participate in an international effort to strengthen Syrian armed groups, yet did not want to be involved in another scandal around military interventions and transgressions of international law. In seeking a ‘grey area’ by framing the operation as a civil, rather than military operation, the Ministry of Foreign Affairs circumvented a public and political debate on legality. The Dutch government therefore posed the NLA programme as a novel type of intervention, in an attempt to escape the haunting of the 2003 intervention and the recommendations of the Commissie Davids. In doing so, the programme could be decided in a present in which the legality of the intervention is simply undecided and unprecedented. Haunting illuminates a form of politics behind secrecy: the act of burying and neglecting, and the strategic dismissal of the past. However, as I will show, the government was not able to fully escape the hauntings of the 2003 intervention.
After the NLA programme, including its funding and cooperating parties, was exposed, a public inquiry was again conducted to investigate decision making on the legality of non-lethal assistance to Syrian armed groups. In its report, the Commissie Cammaerts (2022) connected the insistence of the Dutch government to keep the NLA programme secret and the reluctance of seeking international legal advice to the decision-making process around the Iraq intervention. In appendix M of the report (2022: 51) it argued that ‘the tensions that shape the practices of internal lawyers is previously discussed in the Commissie Davids. This committee recommended a grounded contribution of international legal expertise.’ In general, the investigative committee of the NLA programme came to similar conclusions as the Commissie Davids: there were limited options to share information between departments as a result of state secrecy, the Ministry of Foreign Affairs ignored critical advice from legal experts inside the department, the secret status of information was not re-evaluated after exposure, and official legal advice was not sought, resulting in the Dutch government likely breaching international regulations. According to the report, it was not unusual that the Ministry turned to ‘internal lawyers to “fix” a judicial solution and to “polish” this until it has an acceptable shape’ (Commissie Cammaerts, 2022: 51, appendix M).
Taking a closer look at our case study, it becomes clear that state secrecy and their (partial) revelations often attempt to order objects, events and information in the past, present and future. Burying documents to keep secrets functions as a tactic to keep information in the past, or ‘to close a discussion’. Similarly, the exposure of secrecy also leads to attempts by the government to restore a disturbed temporality. What has been obfuscated in the past needs to be investigated in the present to take lessons for the future. In the public inquiry following the NLA programme revelations, the Commissie Cammaerts (2022: 8) stated that ‘complete transparency can contribute to the closure of the debate around the NLA program’. Both public inquiries are supposed to investigate the obfuscated information in a temporal order and to make visible what the government knew and decided at what time. In such a way, public inquiries produce a narrative that orders and contains specific documents and events in a linear fashion.
Haunting shows us how secrets work through uncanny repetitions beyond a linear temporality. Secrets that are supposed to remain in the past come back and shape the conditions of politics in the present and future. In our case study this became evident: the decision to frame the NLA programme as a civil operation, rather than a military one, was an attempt to erase past legal controversies on justifying interventions. As such, the decision making of the NLA programme was haunted by the scandal that followed the 2003 Iraq intervention. Similarly, the subsequent accountability mechanisms in the form of public inquiries illustrate a desired temporal ordering from secrecy to transparency to normative transformation. However, deploying the lens of haunting, we can better understand how in the absence of legal accountability, ‘closed’ discussions become alive again, and how political decision making in the present is haunted by past state secrets.
Little pockets of haunting, or present-absences in classified documents
In both the NLA programme and the Iraq intervention, paper documents were deliberately buried or concealed as a means to uphold secrecy. In 2010, the Commissie Davids reconstructed the journey of the ‘disappeared’ memo containing a critical note on the legal justification for the intervention in Iraq. This advice was not necessarily new, the legal department (DJZ) had always positioned itself critical towards the United States’ claim that there was an international legal basis for military intervention in Iraq. Indeed, the head of the legal department confirmed that they stopped producing any written reports because nothing was done with their critique (Commissie Davids, 2010: 251). The secretary-general who buried the memo recalled that he did not see the added value of the ‘8 page long and mostly repetitive memo’ (Commissie Davids, 2010: 250). The memo should, however, not be taken as a buried document that simply reappears, but rather we should stay with its ghostly position. At first glance it was reported (Oranje, 2009) that this buried memo contained crucial information that could have altered political decision making in this period on joining the United States in their intervention. However, through the public inquiry report, we learn that this information and critique was not necessarily new or crucial, and even before being buried in a drawer the information in the memo was already known, but strategically ignored. Through this lens, the memo is haunted: information it contained was visible and public, yet secretive and obfuscated at the same time.
This haunted position of documents can also be illustrated through the process of publishing FOI request on the NLA programme 10 years later. On 8 November 2018, a FOI request to publish information on the NLA programme by two journalists was granted and over 1800 pages were sent containing the documentation of the NLA programme, including email exchanges with suppliers and the coordinators, pictures of the materials sent, and inventory lists. In the pictures showing the delivery of the materials, the faces of the people were covered, but logos and flags still lead to the identification of the groups – information that was supposed to be a state secret. Furthermore, it was now confirmed that aside from food and medicine, the Dutch government also provided pick-up trucks, satellite phones, laptops and military vests.
On 22 November 2018, all the documents were retracted by the government. After thorough investigation and additional measures, on 12 June 2019, the government published again the documentation of the NLA programme, this time with more information blacked out and documents labelled as classified information (TK 2019–2020, 32623, nr. 292: 2). Yet, still the documents revealed secret information about individuals and groups involved in the programme and the government was forced to retract more information. In the final publication of the FOI request on 28 November 2019, even more information was blacked out (TK 2019–2020, 32623, nr. 292). According to the government, the accidental revelation of state secrets is the result of ‘an assemblage of actors including the huge volume of documents and required practices of blacking out information, the less-than-optimal facilities such as software and working spaces and the lack of experience of the officials tasked with this responsibility’ (Commissie Cammaerts, 2022: 33).
Figure 2 shows black stripes and boxes concealing the information that was previously exposed, which we can better understand as little pockets of haunting: information that was revealed in the past, inaccessible in the present; information that is already known yet made unknowable in a new form. Because of this process, both the materials and the information they contain can be best understood to be in a state of haunting, where it is not possible to treat the data as public knowledge, yet it is no secret either. Working with FOI requests is important for academics and journalists to contest state power; however, Gilbert (2023: 189) reminds us that ‘even full access to government archives would only provide a partial account’. The reappearance of the documents and the information they contain point us to an unresolved question of accountability.

Screenshot by the author from a document in the FOI request on the NLA programme, showing the blacking out of information. All documents available through: https://www.rijksoverheid.nl/documenten/woo-besluiten/2022/12/20/besluit-op-wob-woo-verzoeken-over-nla-programma-syrie.
Indeed, the haunted state of the documents has a great impact on questions of accountability and justice. In 2017, the Appeal Court in The Hague heard a case of an individual who allegedly had travelled to Syria and joined Jabhat al-Shamiya. The defence lawyer argued during the appeal trial that the case should be dismissed because this organization had received material support as part of the NLA programme. Because the names of the groups participating in the NLA programme were officially a state secret, the Dutch government would not confirm or deny that this organization was a participant which received material support. Nevertheless, the lawyer brought the news coverage of the accidental revelations as part of their evidence, to argue that: ‘When the government supports certain organization, it legitimizes these groups. The state should give a good example and as a citizen you should be able to trust the actions of the Dutch government.’ 1
Because of this sitting, members of Parliament requested an explanation from the Ministry of Foreign Affairs as to whether Jabhat al-Shamiya should be classified as a terrorist organization or a moderate armed group. Here the Minister of Foreign Affairs simply stated that there is no international definition of terrorism and that different departments use different criteria to define groups or individuals (TK 2018–2019, 32623, nr. 247: 23). The Ministry of Justice and the office of the prosecution applies a legal framework, while the Ministry of Foreign Affairs ‘simply’ follows the UN and EU terrorism lists. To the questions on the conditions and decisions of the NLA support to this organization, the Minister replied: ‘The government does not make any public statements about supported or not-supported groups. The answer to this question can be found in the confidential document of this reply’ (TK, 2018–2019, 32623, nr. 247: 24). This refusal to answer in public is important, not only because this information has already been revealed, but also because it would fundamentally challenge the legality of the NLA programme if terrorist organizations had been supported. 2
What both examples illustrate is the simultaneous existence of ‘knowing and not knowing’ of documents (Gordon, 2008: 110). Blacking out (published) data, containing explanations in a confidential part of a public meeting, or simply making documents disappear, are different material practices that aim to conceal and erase particular past events to avoid accountability for counter-terrorism policies. This practice concurs with what Gordon (2008: 110) describes as producing haunted secrets: ‘everyone must know just enough to be terrified, but not enough either to have a clear sense of what is going on or to acquire the proof that is usually required by legal tribunals or other governments for sanctions.’ In our example of state secrecy, haunting goes even further. Even if courts or Parliament demand a full disclosure of evidence for the purpose of legal proceedings, our empirical examples illustrate that this demand in turn produces new forms and techniques of obfuscation and haunting. Mechanisms of accountability therefore end up producing their own forms of haunting, limiting possibilities for normative change in the future.
Haunting of imperial histories
The two previous sections have illustrated how practices of secrecy order events in time and how a lens of haunting allows for an investigation into the disruptions of such linear temporal narrative. Furthermore, I have shown how haunting attunes us not to what becomes visible, but how knowledge remains in a haunted state, obstructing justice and accountability. So far, I have focused on how the two secret operations haunt each other. In this section I investigate how both interventions are haunted by broader questions of violence, empire, and justice or accountability.
The question of (military) intervention in the War on Terror has long been the subject of contentious political and legal debate. Anthonie Anghie writes that the War on Terror has fundamentally changed the concept of (military) intervention in both international law and relations (2007: 276). Initially, during the invasion of Iraq, this discourse was centred around the principle of self-defence. The discourse rested on the portrayal of rogue states posing a threat through their possession of weapons of mass destruction, and the responsibility to promote liberal democratic values. According to Anghie, the War on Terror’s legal justification is based on the construction of a rogue ‘Other’ and should not be understood as an exceptional way to justify interventions in the Middle East, but a continuation of an imperialist mission to intervene and civilize the former colonies, ‘thus affirming the enduring hold of these formations on the structure and imagination of international law’ (Anghie, 2007: 292).
The legal debates are crucial here, because not only in this empirical case study but also Stampnitkzy’s analysis of torture (2020), it is the legality of the intervention that is at the core of what holds the secret together and what causes the scandal when revealed. State legal practices are key to security measures, both in maintaining secrecy (e.g. classification rules) and lifting secrecy (e.g. FOI requests or public inquiries). Nevertheless, such legal procedures are filled with ghostly possibilities, as Wilke (2010: 88) proposes that ‘Attempts to address state atrocities are bound to encounter ghosts: past injustices make their presence felt in a time that is not properly theirs, courts are unsettled in their authority by the inheritances they have made, and the asserted line between past and present appears elusive’.
The secrecy around the interventions does not only concern whether there are enough legal arguments to justify a Dutch contribution to a (military) intervention, but equally on what secret information such decisions can be based, and to what extent a public debate is possible. The committee that evaluated Dutch policies around the Iraq intervention drew a devastating conclusion: there was no argument that would justify the breach of the non-intervention principle and relevant information was kept from Parliament (Commissie Davids, 2010). Similarly, the committee that evaluated the NLA programme concluded that the government wrongfully assumed that civil assistance was an exception to the non-intervention principle (Commissie Cammaerts, 2022).
In other words, what haunts both cases is how secrecy was strategically used to conceal transgressions of international law. Both operations justified the absence of international law in public debate on grounds of ‘national security’. In the case of the Iraq intervention, classified information by the US intelligence services could not be discussed in public, and in the NLA programme the characteristics of the groups and their combat status or history could not be discussed in Parliament out of safety concerns if it became known that the organizations cooperated with the West. Both forms of denying a debate on legality are not novel: imperialist motives to intervene in the Middle East have historically been discussed in selective circles, closed off from the public, with little regard for the sovereignty of the countries to be invaded (Anghie, 2007).
Injustice encompasses much more than simply the transgression of legal boundaries; it concerns those violent instances that have been condemned to the past (discussion is now closed) within social structures of domination (Gordon, 2008: xix). Indeed, these instances are haunted because the larger structures of domination or colonialism remain uninterrogated and evidence of violence is erased. Similarly, the secret programmes fit into a history of transgressing international law without accountability, and as such both programmes are haunted by imperialist assumptions on accountability when it comes to interventions in the Middle East. Whether it is the materialization of evidence of civilian deaths (Rappert, 2012), weapons of mass destruction that lingered as ‘an absence of evidence but not evidence of absence’ (Thomas, 2017), or F-16 fighter planes that leave a data trace of casualties (Gould and Stel, 2022), violent security policies leave their material traces, albeit seldom followed by accountability or normative change. Following these materials, as they haunt our knowledge and security practices, can illuminate ‘that all these ghostly aspects of social life are not aberrations but central to modernity itself’ (Gordon, 2008: 197).
In our case, the civilizing argument continues to inform notions of statehood, legitimate violence and exploitation (Tzouvala, 2020). The concept of haunting shows us that those contemporary doctrines, including the way knowledge is concealed or presented to justify these legal doctrines, find their origins in racialized tropes and colonial imaginaries (Tzouvala, 2020). Part of the violence in both interventions is the way the postcolonial world and its populations are rendered disposable or invisible. Public inquiries might strive to full transparency and accountability, yet limit this notion to ‘civilized countries’ and foreclose how interventions continue colonial legacies. Haunting should attune us to what this future might look like, not from the perspective of bureaucrats in the West, but free from imperialist (epistemic) violence.
Conclusion
In this article, I have presented a new conceptual framework to study secrecy and its ambiguous afterlives. The concept of haunting allows researchers to study how secrecy shapes politics in the past, present and future. Through the empirical case study, I show that despite the efforts to make documents disappear or unreadable, materials persistently resurface. Haunting draws our attention not only to reappearing secret documents, but to what kind of security knowledge and measures are produced through them. Through haunting, I argue that the re-emergence of documents creates new insights, opportunities for inquiries, and connections to older scandals. Haunting opens up the possibility for researchers to examine how (partial) revelations of state violence haunt and persist to shape political and legal debate in a non-linear way. This analysis fits into a growing and vibrant literature in security studies on temporality, silence and memory, yet pays more specific attention to the way secrets are temporally ordered to dis/foreclose normative questions.
Concretely, I propose some reflections on how haunting contributes to the literature on secrecy and security. First, attuning to forms of haunting forces us to reflect on the temporalities of secrecy. In the scholarly debates on secrecy and security, the assumption of moving from full secrecy to full transparency remains pertinent (Birchall, 2021). Haunting challenges this assumption and therefore strengthens the existing contributions within critical security studies pushing back against the binary of secret knowledge as either opaque or transparent (Birchall, 2021). Nevertheless, while in critical security studies scholars have already focused on the detailed process through which secrets are maintained or lost (De Goede et al., 2019; Walters, 2021), there is little reflection on how secrecy is entangled with temporalities. Haunting provides an opportunity for researchers interested in secrecy and (critical) security studies to examine how material processes around secrecy and revelation are entangled with the production of temporalities of the past, present and future. The concept of haunting reminds us that such processes are not linear but unpredictable, uncanny, and complicate what we assume about temporality. The ghost, as Del Pilar Blanco and Peeren (2013: 13) describe, is a form of traumatic repetition ‘which is always both revenant (invoking what was) and arrivant (announcing what will come) – as operating on a number of temporal planes, most crucially the future and its possible interactions with the present and the past’. Haunting forces us to take seriously the non-linear and disruptive temporal ways in which materials keep, lose, obfuscate, or expose secrets.
Second, haunting provides a concrete vocabulary to complicate the assumed linear process from secrecy to exposure to accountability (Stampnitzky, 2020). Security scholars have already acknowledged that secrets can be ‘unsecret but they remain opaque’ (Birchall, 2021: 180). In the cases above, I illustrated how secret information can be in a liminal state of exposure and secrecy at the same time. Haunting is particularly useful for studying moments where security policies result in legal transgressions and moments of injustice. In such instances, haunting pushes us not only to examine secrecy, but to investigate how information can remain in a haunted state, which prevents knowledge from materializing in courts, public debates and other arenas of accountability. Here, haunting allows us to study how material objects used in public inquiries, court cases and other mechanisms of accountability – which are dependent on full transparency –noperate in a security setting where secrets are layered and complex (De Goede et al., 2019; Schweiger, 2022).
Finally, I propose that taking haunted secrets seriously requires an engagement with violence in the context of imperialism or fascism (Gordon, 2008; Manchanda and Salem, 2020). Mbembe (2013) and Gordon (2008) use haunting to not only unravel this violence, but to investigate what fictions or imaginaries of states are entangled with the practice of burying secrets. This is not to claim that all state secrets on violence have a linear identifiable linkage with colonial governance or imperial projects. Mbembe (2013) reminds us that ghosts do not operate along a genealogy. Nevertheless, colonial and imperial pasts are essential in understanding why states are reluctant to commit to normative change after the revelation of secret security measures. While our case study was particularly frightening, haunting can evoke a range of affective emotions. In sum, haunting points to questions of temporality, accountability and justice in the afterlives of secrets not only useful to unpack secrets in the War on Terror, but for security studies more broadly.
Footnotes
Acknowledgements
This article has improved significantly thanks to the suggestions of both reviewers. I am especially thankful to the editors of Security Dialogue for their guidance in this process, as well as their trust and confidence in this article. William Walters, Keri van Douwen and Beste İşleyen have provided essential feedback on earlier drafts of the article and I am grateful for their support. My sincere thanks to the panellists and discussant of ‘Critical Security Methods’ at the 2023 ISA conference for their critical questions and engagement with the paper.
Funding
The author received no financial support for the research, authorship, and/or publication of this article.
