Abstract
How can we make sense of tensions and contradictions in digitally mediated practices of anonymity and identification? This article calls for foregrounding computer protocols as key sites for locating how agency amongst increasingly complex sets of relations between human and non-human actors is impacting contemporary (in)security. We distinguish agency within and between contemporary finance/security infrastructures by tracing the development, application and updating of a particular set of computer protocols – blockchains. Locating agency at the site of these and other computer protocols, we argue, exposes security politics that have largely remained overlooked in the ongoing engagement of critical security studies with science and technology studies. Widening engagements with security devices, this article also broadens the interdisciplinary engagements of critical security studies with new media and software studies.
Introduction
In 2014, Islamic State of Iraq and the Levant (ISIS) announced it would accept donations in the leading ‘cryptocurrency’, Bitcoin. This was surprising given that Bitcoin’s pseudonymous features give everyone, including security agencies charged with countering the financing of terrorism, an overview of all Bitcoin transactions. While granting some degree of anonymity to senders and receivers of this electronic token, Bitcoin’s transparent public ledger also provides the data employed by security agencies around the world to tie cryptocurrency transactions to individual users with increasing precision. Such identification practices have unsurprisingly been decried by privacy advocates as ‘a prime example of a tool where risks, harms and costs far outweigh the potential benefits resulting in a lack of proportionality or necessity, and where the pursuit of private profit ends up taking precedence over the public good’ (Monero Policy Working Group 2021). Yet, in spite of confiscations of cryptocurrency and criminal convictions of their users, 1 Bitcoin and even its more privacy-orientated competitors have continually been mobilized to finance a wide range of activities with security implications, from the ‘Freedom Convoy’ that surrounded the Canadian capital of Ottawa in 2022 to Ukrainian resistance to Afghan, Iranian, North Korean and Russian attempts to escape sanctions (Ashraf and Nelson, 2022; Campbell-Verduyn and Giumelli, 2022; Pessarlay, 2022).
How can critical security studies make sense of tensions and contradictions in increasingly digitally mediated practices of privacy and identification? This article advances understanding of contemporary security politics by locating what we call infrastructural agency in sociotechnical activities occurring at key, but overlooked, sites of contemporary activity – computer protocols. It argues that two forms of infrastructural agency shape tensions in privacy and identification practices in the case of cryptocurrencies like Bitcoin that build on blockchain protocols. First, locating what we call infrastructural agency points to continuities and changes in security practices emerging from human and non-human relations centred around computer protocols. Second, identifying interstructural agency helps us understand tensions in security practices stemming from relations between infrastructures. Together, locating inter- and infrastructural agency exposes security politics that have so far remained overlooked in critical security studies, which have instead usefully foregrounded algorithmic and information communication technologies.
In their ‘encounter with the marvellous minions’, critical security studies have very productively ‘opened up a wide world of infrastructural politics to exploration, sensitizing security studies scholars to the wondrous worlds of codes, algorithms, protocols and other security devices’ (Leander, 2019: 25). Critical security studies’ scrutiny of security devices has focused largely on algorithms. Foregrounding computer protocols, we argue, deepens understanding of how relations between devices like algorithms and their human creators and users impact security practices in particular ways. Linking science and technology studies’ conceptions of infrastructures as sociotechnical relations with insights from fields of study that have foregrounded protocols as sites of political analysis (Cramer and Fuller, 2008; Galloway, 2004), this article broadens critical security studies’ encounters with the ‘marvellous minions’ that Leander (2019) identifies and widens interdisciplinary encounters beyond critical security studies’ productive waves of recent engagements with science and technology studies (Bellanova et al., 2020).
We proceed in three steps. A first step introduces computer protocols as entry points for locating agency in infrastructures that are increasingly digitally mediated as the internet has expanded. We situate our analysis broadly, tracing how the (re)design of internet protocols impacted practices of privacy and identification in the earlier 1.0 and existing 2.0 versions of the World Wide Web. In a second step we turn to examining how the creation and updates of blockchain protocols, starting with Bitcoin in 2009, have continued to shape security practices as the so-called ‘Web3’ emerges as an ever-broadening space of technological experimentation beyond just cryptocurrencies. Zooming in on sociotechnical relations shaping the development, maintenance and updating of blockchain protocols, we argue that critical security studies can make sense of evolving tensions in security practices emerging from what we call infrastructural agency. Zooming out, meanwhile, on relations between an emergent blockchain-based infrastructure and a longer-existing surveillance infrastructure elucidates how privacy and identification practices are being (re)shaped in what we call interstructural agency. In a third and final step, we reiterate how locating infrastructural agency at the site of computer protocols sheds light on evolving tensions in contemporary security practices. Widening critical security studies’ engagement with ‘marvellous minions’ that include but go beyond algorithms, we conclude, broadens the productive interdisciplinary interactions of critical security studies to new media and software studies.
Computer protocols as sites of security politics
A protocol, generally, is a form of ‘correct or proper behavior within a specific system of conventions’ (Galloway, 2004: 7). There are cultural protocols for introducing and greeting one another, diplomatic protocols for how relations between states are to be ‘properly’ carried out, and organizational protocols for acceptable behaviours between staff and employees in institutions. All protocols set out particular paths for information to be communicated, transmitted and acted upon that have varying implications for (in)security.
Critical security studies are familiar with how Know-Your-Customer (KYC) protocols specify proper conduct for financial institutions, like banks, to identify and share information on their clients in supporting growing international Anti-Money Laundering and Countering the Financing of Terrorism (AML/CFT) efforts since the 1980s (Amicelle, 2011; Lagerwaard, 2020; Marlin-Bennett, 2016). Growing attention within critical security studies has been given to secrecy protocols specifying standards to maintain confined communication of information and/or the anonymity of those transmitting it (Bosma et al., 2020; Walters, 2020). Technologies, human practices and sociotechnical relations all play crucial roles in the (re)formation of these protocols. Yet, computer protocols as sites of agential activity in security politics have remained underappreciated.
Computer protocols are digitally encoded standards defining how information is transmitted in and across networks of computers and human users. They shape the sending and receiving of digitized information in ways that can determine possibilities for often-conflicting security practices, including those of privacy and surveillance in such a digitally mediated world. Analysing computer protocols as sites where digitally mediated practices of privacy and identification are (re)shaped brings together and advances two intersecting debates in critical security studies. First are debates over agency in the ongoing ‘technologization’ of security (Kaufmann, 2016; see Orlando, 2020). Second, and relatedly, are debates over the human–non-human relations ‘mobilizing’ (in)security in sociotechnical infrastructures (Hönke and Cuesta-Fernandez, 2018). Tracing the (re)formation of standards of behaviour amongst computers and their users brings together and advances critical security studies debates on techno-agency and infrastructural politics. Responding to calls to consider the agential qualities of infrastructures (De Goede, 2020) and to situate techno-agency in wider ‘infrastructural geopolitics’ (De Goede and Westermeier, 2022), we widen the ongoing interdisciplinary encounters of critical security studies to new media and software studies.
Techno-agency: What do computer protocols do?
Agential qualities – who and what impacts the world – have increasingly been associated in critical security studies with relations between technologies, their developers and their users. Moving from an overly simplified stress on agency as the ‘capacity to act’ defined a priori (Orlikowski, 2007: 1438), technological agency is being reconsidered as an iterative process, one in which humans construct technologies that impact their users and designers through unforeseen uses and effects. Yet, attempts to attribute agency to relational processes remain highly ‘context dependent’ (Hoijtink and Leese, 2019: 11). Their specificity along with the growing complexity of multiple-use technologies, like Bitcoin, all limit more general claims as to where ‘techno-agency’ might be found, assessed and potentially countered. Locating agential qualities in activities surrounding the development of computer protocols, we contend, widens possibilities for linking specific sociotechnical relations to their wider ‘emergent security’ implications while avoiding ‘the centrality of human intentionality as a basis for constructing enmity, and by acknowledging the role of codes/software unexpected paths’ (Fouad, 2022: 768).
The politics of computer protocols were first examined in software studies, the interdisciplinary field that Fouad (2022) and other critical security studies scholars have engaged (Leese et al., 2022). Here, activities involved in the (re)development of computer protocols are agential in shaping ‘operations that are allowed and assigned a priority or blocked’ (Cramer and Fuller, 2008: 151). The ‘qualitative discontinuity’ resulting from the redevelopment of the Transmission Control Protocol/Internet Protocol (TCP/IP), for instance, long influenced possibilities for discriminating between types of internet traffic (Fuller and Goffey, 2009: 150–151). The (re)formation of such behavioural standards for transmitting packets of digital information, 2 that also include the likes of the Hypertext Transfer Protocol (HTTP), have continually impacted the ability of internet users to access and communicate information on the World Wide Web.
Yet despite their ‘diffuse and extensive’ presence, computer protocols and their agential qualities are often relegated to what Fuller and Goffey (2012: 1) call grey media – ‘technologies that are operative far from the more visible churn’ and that are frequently invoked and recognizable ‘yet rarely recognized or explored’, including by scholars. What software studies call for then is to expose more widely the agential properties of such media, amongst others by tracing their facilitation of activity that is produced when devices, practices, protocols and procedures, gadgets and applications, mesh and synchronize simultaneously [creating] vast black-boxed or obscurely grayed-out zones, taken for granted, more or less stabilizing and stabilized artifacts, that permit the abstract social relations characteristic of ‘frictionless’ communication to take root. (Fuller and Goffey, 2012: 4)
Building on software studies, critical security studies can draw security politics and implications of agential relations stemming from the development, maintenance and updates of computer protocols. A first set of protocol-level activities with agential effects on security involves the development of initial standards for how information is transmitted in and across networks of computers and human users. To relate to one another, computers ‘must speak the same language’ (Galloway, 2004: 12; emphasis in original). Without this shared language, computer networks remain ‘non-interoperable’. Digital interoperability tends to coalesce around shared norms and expectations, including those of privacy and identification.
Another set of agential effects on security practices stemming from the (re)formation of computer protocols can be found in relations with the network and application ‘layers’ of what have been called ‘stacks’ (see generally Bratton, 2016). Figure 1 illustrates the schematic depictions of hierarchies among ‘layers’ of digital ‘stacks’. Despite the oversimplification, the stack metaphor draws useful attention to two specific sets of relations shaped by protocol-level activities: network formation based on a computer protocol; and application development as the tip of digital stacks that get ‘adopted, implemented, and ultimately used by people around the world’ (Galloway, 2004: 7).
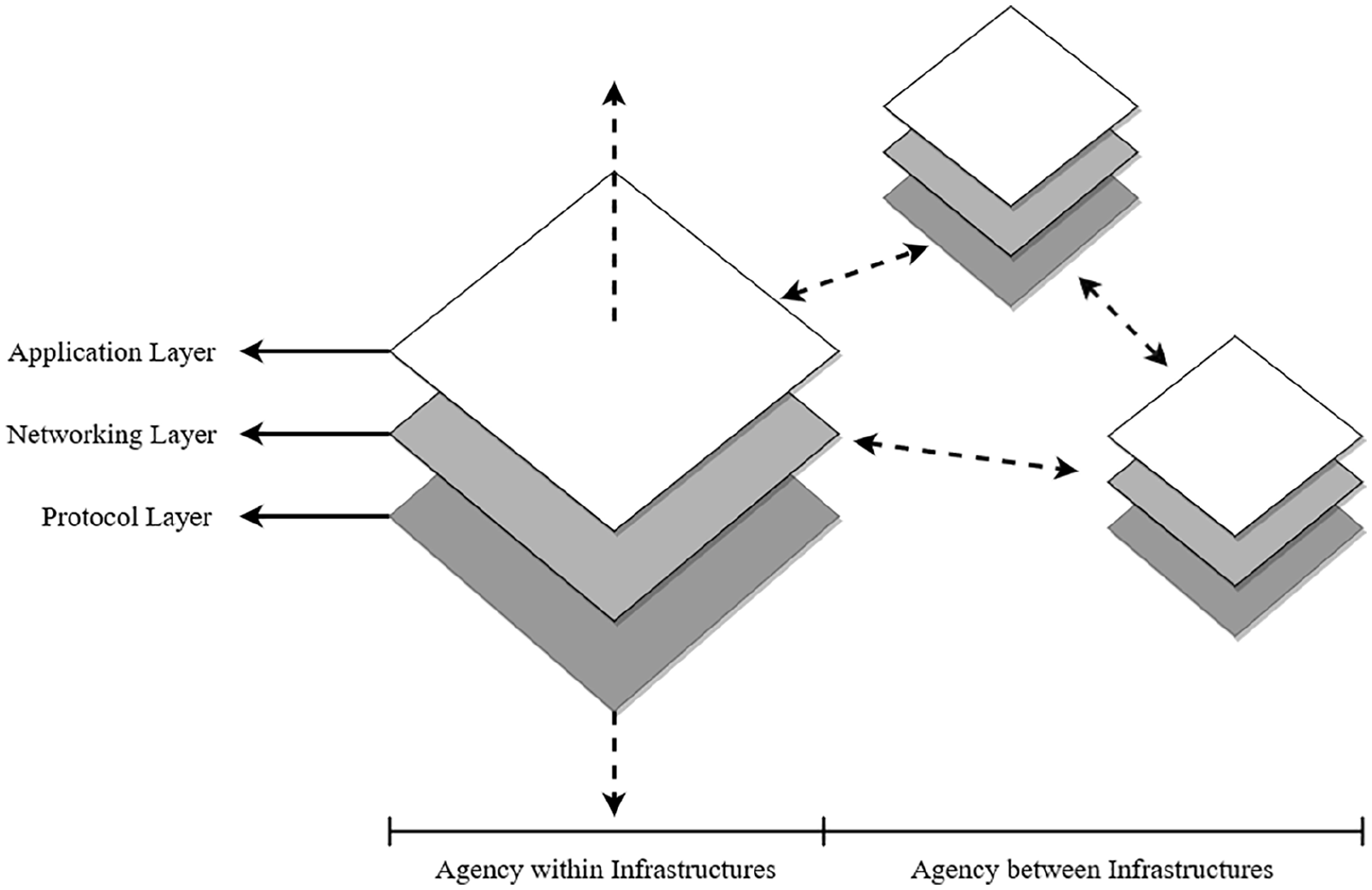
Relations between ‘layers’ of digital ‘stacks’. Source: authors, adapted from Bratton, 2016.
The key point here is that neither digital networks nor the applications based upon them can be built, run or reformed without the secure and consistent communication standards developed and maintained at the site of computer protocols. The security practices emerging in and across networks and surfacing with particular everyday applications – like cryptocurrencies – are all shaped by activities at the underlying protocol ‘layer’. The ‘protocol politics’ (DeNardis, 2009) at stake here have been foregrounded in studies tracing how the maintenance and updates of internet protocols have shaped the practices of the networks and applications of the World Wide Web. To set the stage for our analysis of the internet-based blockchain protocols emerging since 2009, we proceed by surveying briefly how activities in (re)developing the internet protocols have had agential impacts on privacy and identification practices.
Firstly, the (re)development of internet protocols has had agential effects on security politics in networks of computers and users building on top of them. The original development of the Internet Protocol (IP) in the 1970s involved specific sociotechnical relations between mainframes and graduate student researchers at the United States Department of Defense. The Advanced Research Projects Agency (ARPA) is often linked to the national security origins of the internet as a network-of-networks intended for information transmission both within the USA and between its allies in the context of the Cold War. Updates to the IP in the late 1980s and 1990s were however demilitarized and undertaken via email lists of the Internet Engineering Task Force and civilian organizations composed largely of white, middle-aged, university-educated men. Nisha Shah (2009: 139) notes how these developers all possessed ‘a certain level of technical proficiency and knowledge’ and ‘with the time and willingness to participate’. These concentrated communities of ‘code rebels’ (Levy, 2001) leveraged cryptographic technologies for securing communication in increasingly commercial activities across a network-of-networks that was privatized after the Cold War. 3 Concentration in the communities designing and maintaining the internet’s underlying protocols was later echoed in the growing monopolization of the internet following the millennial dot-com bubble burst. The eventual dominance of Microsoft and the GAFA (Google, Amazon, Facebook, Apple) Big Tech multinational firms renewed fears of vulnerabilities in informational security practices (Barwise and Watkins, 2018; Lovink, 2022). These were exemplified most prominently by reoccurring technical outages. In the case of Facebook, a major outage led to the bulk of what is considered to be the internet for millions in South Asia and elsewhere to be inaccessible for hours (Isaac and Frenkel, 2021). This specific episode highlights a first way in which activities at the site of computer protocols help to locate security politics in the (re)formation of digital networks, including that of the internet as the network-of-networks (DeNardis, 2012).
Secondly, sociotechnical activity at the site of computer protocols such as IP have impacted the security politics of application-building on standards for relations between computers and their users. Internet protocols shaped the various iterations of the Web, the key application that built on top of the network-of-networks. Web 1.0 of the early 1990s allowed for relatively anonymous information communication practices across relatively decentralized networks-of-networks. By contrast, the Web 2.0 that emerged in the 2000s and 2010s became governed by concentrated ‘walled gardens’ (O’Reilly, 2009), the platforms maintained by those dominant USA-based technology firms. These Big Tech firms banded together in 2017 to develop the Content Incident Protocol (CIP) that sought to standardize communication of user identification information in order to curb ‘a real-world terrorism or violent extremist event’ (GIFCT, n.d.). The CIP built on earlier standards introduced on top of the TCP/IP, such as the Domain Name System (DNS) protocol that translated website names into computer-identifiable addresses. What the development of these new protocols shows is how the openness and shared communication standards set by communities of TCP/IP developers in the 1980s progressively gave way to new standards for user identification that have underpinned Web 2.0. These standards were increasingly challenged after 2009 as privacy-centric blockchain protocols emerged and became part of what, more than a decade later, underpins the Web3 applications traced in the next section.
In sum, the evolution of the internet’s security politics can usefully be understood by foregrounding the sociotechnical development and maintenance of computer protocols like the IP. Privacy and identification practices in the network-of-networks that is the internet have all been shaped by the sociotechnical relations involved in creating, maintaining and updating standards for behaviour. Critical security studies’ understanding of techno-agency is advanced by highlighting the relational activities evolving at the sites of computer protocols, especially when linked to wider efforts to conceive infrastructures relationally.
Locating agency in infrastructural relations
Countering common-sense notions of infrastructure as objects or static ‘things’ are science and technology studies-inspired accounts of infrastructures as evolving sets of relations between social actors and material objects that have gained currency in critical security studies (Bellanova and De Goede, 2022; Glouftsios, 2020; Nolte and Westermeier, 2020; O’Grady, 2021). An infrastructural turn has usefully built on earlier critical security studies’ critiques of instrumentalist and functionalist efforts to designate critical infrastructures as ‘objects in need of protection’ (Aradau, 2010; Brassett and Vaughan-Williams, 2015; Dunn and Kristensen 2020). The agency of humans positioning some infrastructures as ‘critical’ is limited to states and corporations acting on or over infrastructures that these actors deem to need ‘protection’. This constrained version of agency overlooks the wider impacts of seemingly apolitical relations both within communities deemed worthy of protection and between such communities and those deemed unworthy of protection. Critical infrastructures thus disentangle from one another the various relations designated or passed over as vulnerable leading to profound disconnections, for instance between ‘critical’ sewage systems from wider ecological systems. Efforts to designate ‘critical infrastructures’, in other words, overlook both sociotechnical entanglements within and between infrastructures understood relationally.
Critical security studies can further the understanding of digitally mediated security practices by repurposing the critical in critical infrastructures to focus on key activities within and between sets of sociotechnical relations. Rather than simply stressing limits on how a government or corporation acts on infrastructure, critical security studies can tease out the impacts on security practices of relations between groups of human and non-human agents, including computer developers and engineers, as well as in the material cables, wires and computers underpinning increasingly digital infrastructures. Within this widened focus, computer protocols form a productive entry point and site for locating more specifically which, amongst myriad sociotechnical relations within and between infrastructures, are those most relevant to the evolution of security practices. Probing computer protocols helps pinpoint more precisely those relations underpinning digitizing infrastructures that may ‘have more currency than others’ (Czarniawska, 2004: 783). Put differently, foregrounding computer protocols as sites of activity helps locate agential qualities within the many (sets of) relations whose formation and reformation potentially shape security practices, such as of privacy and identification. It can provide insight into how, when and where key sociotechnical relations impact digitally mediated security practices, for instance by tracing who is ultimately responsible for how ‘thinking infrastructures’ achieve any or all of the following: Configure entities (through tracing, tagging); organize knowledge (through search engines); sort things out (through rankings and ratings); govern markets (through calculative practices, including algorithms) and configure preferences (through valuations and recommender systems). (Kornberger et al., 2019: 2)
Locating which sociotechnical relations enable (in)security without reifying and returning to more conventional and instrumental understandings of agency on or over infrastructures can benefit from new media and software studies of what breakdowns, stoppages or cessations emerge from ‘infrastructures [that] are plugged in other infrastructures’ (Pipek and Wulf, 2009: 454). Repurposing the ‘critical’ from the notion of ‘critical infrastructures’ can also benefit from distinguishing between inter- and infrastructural agency.
What we designate as infrastructural agency involves the impacts of sociotechnical relations at the site of protocols on the security politics of the networks and applications layered on top of standards of proper behaviour. Relations at the site of computer protocols can be agential not only within an infrastructure but also in the networks and applications centred around different standards of behaviour. Interstructural agency, meanwhile, involves the impacts that relations at the sites of different computer protocols have on one another. The ‘installed base’ (Star, 1999: 381) of an infrastructure is not entirely ‘hard-wired’ (De Goede, 2020: 356). Sociotechnical relations shift – often subtly – as alternative bundles of sociotechnical relations arise and interact with sociotechnical relations that already exist. In the case of activity at the site of computer protocols, Beuster et al. (2022) note how ‘[o]nce operationalised in infrastructures, protocols act immanently conservative and upgrades transcending its encoded rules, such as new functionalities, often must be invoked from the outside’. This understanding is useful for balancing the continuities invoked by the ‘hard-wiring’ of sociotechnical relations with the persistence of possibilities for change emanating from experimentation with other ways of wiring the world (Morozov, 2012).
The next section traces the emergence of the so-called ‘Web3’ infrastructure based on blockchain protocols whose continuing entanglement with the internet protocols underlying Web 2.0 have shaped security practices since 2000. We argue that locating infrastructural agency in the formation and ongoing interaction amongst infrastructures marked by differences and contestations helps us to understand evolving tensions and contradictions between identification and privacy practices at the contemporary finance/security nexus.
Locating infrastructural agency within and between finance/security infrastructures
This section traces the sociotechnical relations that have had key impacts on digitally mediated privacy and identification practices since 2009. Locating infrastructural agency in the emergence of a novel privacy infrastructure and interstructural agency in the ongoing relations between new attempts to enhance anonymity with a countervailing identification infrastructure based around KYC protocols, we argue, helps make sense of continuities and changes at the contemporary finance/security nexus.
The finance/security nexus consists of two ‘realms’ typically considered as separate, but which meet in ‘profound historical and conceptual interrelations that makes one unthinkable without the other’ (Westermeier, 2019: 111). Both mundane practices, such as the surveillance of digital transactions, as well as epochal events like the 2007–2008 global financial crisis are regarded in studies of this nexus as reflective of the ‘cross-colonization of finance and security logics’ (Amicelle, 2017: 119). The finance/security nexus has evolved over centuries as risk management practices underpinning sectors like insurance have involved and affected both state and human security (Lobo-Guerrero, 2012, 2016). The continuing motion of longer temporal threads are emphasized in the science and technology studies-inflected notion of finance/security infrastructure, where a stress on an ‘installed base’ (Star, 1999: 381) of sociotechnical relations evolving over time links colonial-era inequities (De Goede, 2020) with contemporary cross-border digital systems maintained by bodies like the Society for Worldwide Interbank Financial Telecommunication (SWIFT). 4
In tracing the implications for security practices of activities that (re)develop a particular set of protocols – blockchain – we respond to prompts to further draw out the agentic qualities of infrastructural relations between technical objects and practices (De Goede, 2020), as well as related calls to probe how an ‘ever-increasing appetite for financial data proceeds in the name of security’ (Westermeier, 2019: 116). Financial data at stake stem from the generation, retention and circulation of identity information on users of applications based on blockchain protocols in what we call a ‘privacy infrastructure’. 5 Locating agency in sociotechnical relations at the site of this particular set of computer protocols highlights both continuities and changes at the contemporary finance/security nexus.
As the first subsection traces, infrastructural agency in the creation and maintenance of blockchain protocols has enabled varying degrees of anonymity, disintermediation and immutability. Locating this first form of infrastructural agency helps draw out the security politics stemming from sociotechnical relations occurring in the formation of this protocol, as well as consider the impacts of these relations on the networks and applications that together have formed a novel privacy-focused finance/security infrastructure since 2009.
A second subsection then locates interstructural agency in the relations between this blockchain-based, privacy-orientated infrastructure and the far longer-standing identification-focused infrastructure. Attempts to address the various insecurities prompted by the former, we show, impact and are impacted by the ongoing evolution of the latter. We draw out continuities and changes in identification and privacy practices at the finance/security nexus in official documents from international finance/security agencies, primary documents such as White Papers that spell out the standards set out in protocols such as Bitcoin, as well as English-language reports from technology industry news sites Coindesk and CoinTelegraph.
Agency within a blockchain-based privacy infrastructure
Infrastructural agency stems from both ‘moments of creation’ and subsequent updates to protocols like Bitcoin. Each moment involves sociotechnical relations that materialize specific security practices, as we show in the case of a novel finance/security infrastructure emerging following the global financial crisis of 2007–2008.
Infrastructural agency can be located in two sets of infrastructural relations. First are the relations between actors and objects that form protocols such as Bitcoin and its competitor Ethereum. Second, infrastructural agency is also located in the relations between these protocols and the other ‘layers’ that together form an infrastructure: networks and applications (see Figure 1 above). Locating infrastructural agency within an emerging blockchain-based finance/security infrastructure, we argue, helps make more nuanced sense of continuity and change in the security politics of privacy and identification. This subsection shows how instabilities and illicit activities facilitated by sociotechnical relations within this new privacy-orientated infrastructure are neither entirely novel nor merely hard-wired. Tracing infrastructural agency, we instead highlight an evolving mix of continuity and change in key practices at the contemporary finance/security nexus.
We begin with Bitcoin. A set of very specific sociotechnical relations between computer programmers and algorithmic, cryptographic and time-stamping technologies underpinned the genesis of the Bitcoin protocol, carrying important implications for identification and privacy practices. In 2008, at the height of the most severe financial crisis since the Great Depression, a still unidentified person(s) using the pseudonym Satoshi Nakamoto circulated on a cryptography newsletter a white paper calling for the development of a payment protocol, or ‘cryptocurrency’ (Nakamoto, 2008). 6 Nakamoto released a first version of the Bitcoin protocol to a geographically dispersed group of coders who experimented with the proposed design to instigate the Bitcoin protocol in 2009. The ‘Bitcoin standard’ (Ammous, 2018) specifies harnessing cryptographic, time-stamping and other existing technologies to exchange digital tokens through privacy-orientated means. Greeted cautiously in cryptographic communities, the initial version of the Bitcoin protocol began to be improved as groups of pseudo-anonymous coders exchanged money-like tokens and collaborated further with one another online.
Two overlapping security implications immediately emanated from the specificities of the sociotechnical relations involved in the creation of the Bitcoin protocol. First was the emphasis on privacy embedded in the reliance on cryptography to ensure a high degree of difficulty in identifying exactly who exchanged digital tokens with whom. Second was a complicating of identification practices through a stress on decentralization or ‘distribution’ of authority. Not only has the author(s) of the Bitcoin white paper still not been identified, despite widespread efforts, but the decentralized standard for exchange, verification and publication of digital transactions meant that no one particular person remained ‘in charge’. The lack of identification at the protocol level has impacted the evolution of privacy and identification practices in wider finance/security infrastructure emerging around Bitcoin.
The first key way in which sociotechnical relations at the ‘birth’ of the Bitcoin protocol were agential was in shaping the security practices emerging in the networks of this alternative finance/security infrastructure. Not unlike the evolution of the internet itself, the Bitcoin standard was formed by a largely homogenous group of actors that, although geographically dispersed, consisted largely of white men based in the Global North possessing knowledge of cryptographic technologies and little regulatory expertise, beyond desires to escape all existing laws and regulations. The activities of the identified members of this small group experimenting with cryptographic technologies impacted the security politics of the Bitcoin network most clearly by attracting illicit or regulatory-subverting behaviours. The attractiveness of Bitcoin’s privacy-enhancing features was most famously exemplified by its exclusive use for payments on Silk Road, an online marketplace that, amongst other goods and services, facilitated purchases of drugs and weapons. Anonymity as set out in the Bitcoin protocol shaped the development of the wider user network. Though not solely pursuing nefarious activities, Bitcoin users were attracted by possibilities of maintaining privacy and avoiding the KYC checks that had expanded to banks and other financiers ‘in the frontline’ as part of the war on terror and war on drugs (De Goede, 2017). In some cases, the Bitcoin user network consisted of activists and whistleblowers. In other cases, including that of ISIS noted above, the privacy-enhancing features of the original blockchain protocol attracted fraudsters, money launderers, terrorism financiers and criminals. Even if the hard-to-measure cases of the former outweighed the latter, illicit uses of Bitcoin enabled by its underlying protocol instigated the very interactions with AML/CFT regulators that developers and early users of Bitcoin had sought to avoid.
A second way in which sociotechnical relations that informed the development of the first cryptocurrency impacted security practices is through the particular applications that emerged from the original Bitcoin protocol. Despite intentions and persistent pretensions to function as an alternative peer-to-peer payments system distinct from the (central) banks involved in the 2008 global financial crisis, the cryptocurrency created by the Bitcoin protocol generated highly volatile speculation and instabilities of its own. Applications of this computer protocol enabled speculation that became increasingly difficult – though not impossible – to undertake after 2008. Bankers whose activities were restricted by post-crisis regulation turned to Bitcoin as digital chips as the ‘casino capitalism’ popularized by Susan Strange (1986) became increasingly extreme in the 2010s (Maurer, 2016). The quasi-anonymity of the Bitcoin attracted difficult-to-trace risky applications that concealed the identities of users speculating on massive swings in value.
Another blockchain protocol developed in 2014–2015, Ethereum, further widened nefarious networks and speculative applications, solidifying and extending the central security practices that Bitcoin had established in this alternative finance/security infrastructure. The Ethereum protocol provides standards for secure exchange, verification and publishing of transactions but of a broader range of digital objects than simply money-like cryptocurrencies. The particular sociotechnical relations between technical objects (time-stamping technologies and hashing algorithms), human actors (hackers, programmers, developers) and practices (financial cryptography) that developed this second major blockchain protocol had agential impacts on its wider network of actors. Users attracted by the open-source standards facilitated by the Ethereum protocol included hackers testing the informational security of this second major blockchain and others seeking to develop an expanded set of applications facilitating privacy practices. Like the developers of Bitcoin, the main developer of Ethereum, the Russian–Canadian Vitalik Buterin (2013), advanced standards of behaviour to generate ‘financial freedom’. A growing range of so-called ‘decentralized finance’ (DeFi) applications arose based on this protocol. 7 These applications once again attracted financiers seeking possibilities to undertake speculative exchange beyond the increasingly regulated financial system. Most prominent here was the rise of ‘non-fungible tokens’ (NFTs) as digital representations of everything from art to worker contracts. While providing novel financing tools to artists and others shut out of traditional finance, NFTs mostly boomed as speculative assets whose price crashed spectacularly in 2022. The informational security and privacy practices provided by Ethereum’s standards for developing ‘smart contracts’ automatically executing preset contractual terms made this expansion of speculative activity possible. Like Bitcoin, the privacy features of the Ethereum protocol and lack of KYC checks in its applications generated DeFi as the ‘wild west’ of finance (Kruppa and Murphy, 2019) not only for speculation, but equally for money laundering and other illicit activities (Attlee, 2022; Young, 2020).
The activities and relations between human actors and technologies informing the initial development of Bitcoin and Ethereum have had an impact on the security practices of a wider blockchain-based alternative infrastructure since 2009. Agency within this new privacy-orientated finance/security infrastructure cannot merely be located in these initial ‘moments of creation’ but also in seemingly routine protocol maintenance work. Updates to protocols occur daily and even hourly. Yet, not all changes to the protocol are as impactful on other security practices across infrastructural layers. Sociotechnical relations informing two protocol updates to Ethereum and Bitcoin, in 2016 and 2017 respectively, were significant in their shaping of privacy practices in the networks and applications spawned by this infrastructure after 2009.
A first protocol update that we can consider as agential in its impacts on security practices involved the introduction of a new standard of acceptability in Ethereum. In 2016, coders led by the protocol’s co-founder Buterin initiated a ‘technical fix’ to the hack and theft of $150 million raised through an experiment with the automatic allocation of crowdsourced funds called The DAO. This acronym stands for decentralized autonomous organization, digital entities which combine blockchain-based smart contracts (Dupont, 2017; Hütten, 2019). Insecurity sparked by the hack split the different coder groups involved with Ethereum. Protocol ‘purists’ defended the original yet clearly flawed Ethereum protocol, while key ‘insiders’ like Buterin sought to update and alter the standards. The former were outmanoeuvred by the latter ‘interventionists’. The blockchain split into ‘Ethereum Classic’ and a new ‘Ethereum’ blockchain. These changes led to a widening of activities that grew, rather than reduced, insecurities by inducing an explosion of further attempts to automate finance/security through smart contracts. 8 Instead of ending after the failure of the 2016 hack, efforts to develop DAOs were resurrected in a post-2019 boom in DeFi applications. The instability of yet another boom-and-bust cycle was once again marked by widespread frauds perpetrated by mostly – though not always – anonymous users.
A second agential moment impacting security practices across the blockchain-based infrastructure was undertaken a year later. The 2017 Bitcoin protocol update sought to attend to growing delays in processing its transactions that were hampering the daily exchange of goods and services. Purists and interventionists once again debated splitting or ‘forking’ the original Bitcoin blockchain protocol. As with Ethereum, the purists lost out to those seeking the wider usage of the cryptocurrency who established a new protocol, called Bitcoin Cash (BCH), that maintained the original features and transaction history of what was renamed the Bitcoin Core (BTC). Once again, the privacy features of the original protocol were not significantly altered. What was changed, however, was the behavioural standard enabling further spin-offs, or ‘forks’, of blockchain protocols. The 2017 update solidified the notion that protocols could be spun off from earlier protocols. The new BCH protocol split into two as Bitcoin Cash Satoshi Version and Bitcoin Cash Adjustable Blocksize Cap were created in 2018. Like the earlier 2017 update, the second protocol change was a contentious affair. Users who sought to expand the usage of cryptocurrencies ultimately won, thereby widening the possibilities for speculation and illicit uses of the now various versions of the Bitcoin protocol. Attempts to encourage a more ‘everyday’ use of the token as a real ‘currency’ sparked a seemingly ever-widening competition for financial and security advantages between the hundreds of ‘altcoins’ that arose in the aftermath of the 2017 protocol update. 9 An Initial Coin Offering (ICO) boom occurred in 2018 as speculative investment flowed into pre-sales of tokens in processes comparable to the Initial Public Offerings (IPOs) of company stocks. This boom was marked by an explosion in fraud that yet again enhanced insecurities (Tiwari et al., 2020). Moreover, the growth of blockchain protocols in turn marked an expansion of efforts to set standards for enabling communication not merely between users of a single cryptocurrency network but across them in a wider, expanding blockchain-based alternative finance/security infrastructure.
Such ‘meta-level’ attempts to develop protocols for relations amongst protocols have led to an ongoing struggle for ‘cross-chain interoperability’ to connect different protocols built on the two main blockchains, Bitcoin and Ethereum. These efforts have parallels with standardization in the existing finance/security infrastructure, such as the European Union’s ‘regulatory push for interoperability’ in digital markets (Westermeier, 2020: 2058). Attempts to develop one protocol to standardize the increasingly fractured blockchain-based finance/security infrastructure, however, diverted scarce resources for maintaining and updating existing blockchain protocols. This dispersion of both computing power and human attention rendered protocols like Ethereum more and more vulnerable to the kinds of cyberattacks exemplified most dramatically by The DAO (Voell, 2020).
In 2022, a long-delayed update of the Ethereum protocol was finally undertaken. The mechanism specified for verifying transactions in this blockchain was shifted from the proof-of-work consensus, which originated and has persisted in the Bitcoin protocol, to proof-of-stake. In the former, users harness growing amounts of costly computational power to solve complex computational puzzles, racing to verify transactions to win newly minted tokens with transaction fees paid by users. In the latter consensus mechanism, transaction validators prove their commitment to the blockchain by ‘staking’ a certain amount of ETH, Ethereum’s’ ‘native’ token, which stands to be lost if stakers act maliciously. The protocol switch to a radically different method of processing transactions impacted the security practices surrounding Ethereum by moving it closer to US regulatory reach. Most stakers are estimated to reside ‘directly or indirectly under U.S. jurisdiction’ (Georgiades, 2022). However, unlike the energy-intensive proof-of-work consensus mechanism, staking operations can no longer be located by tracking abnormally high electricity consumption.
Sociotechnical activities both at the birth of and at key updates to protocols impact security politics. The infrastructural agency traced here involved geographically dispersed communities harnessing cryptographic technologies to form and maintain two blockchain protocols in ways that shaped networks formed and applications emerging from privacy practices after 2009. The new standards of behaviour introduced by blockchain protocols, however, not only spurred the formation of a new privacy-centric finance/security infrastructure; they have also instigated a flurry of developments in an existing identification-focused finance/security infrastructure.
Locating agency between privacy and identification infrastructures
The initial design of, and subsequent updates to, protocols can also impact other infrastructures. What we call interstructural agency refers to how sociotechnical relations at the site of protocols impacts relations between other sets of sociotechnical relations, or infrastructures. This subsection highlights how sociotechnical relations at both the ‘birth’ of and subsequent updates to blockchain protocols have impacted, and in turn been impacted by, an existing finance/security infrastructure orientated less towards secrecy and privacy and more towards identification practices. We trace both the impacts of activities at the site of blockchain protocols on the security politics of the existing identification infrastructure and vice versa. Locating intrastructural agency, we argue, helps to make nuanced sense of the push-and-pull of privacy and identification practices at digital frontiers of the contemporary finance/security nexus.
Agency between infrastructures is most clearly illustrated in efforts by actors in the existing identification finance/security infrastructure to designate relations with the blockchain-based privacy finance/security infrastructure as ‘critical’ (Financial Stability Board, 2022). A sole emphasis on the agency exercised by formal regulators, however, would leave new and updated blockchain protocols as grey media, backgrounding their ongoing agential impacts both in and between new and existing infrastructures. A whole set of new protocols has emerged from consultation between networks of actors central to both ‘new’ and ‘old’ finance/security infrastructures, including coders and regulators of leading intergovernmental organizations like the Financial Action Task Force (FATF). Decades-long discussions and technological experiments led to a controversial compromise in which existing identification practices that enforce AML/CFT standards were extended to certain, but not all, blockchain-based privacy-centric activities. In particular, the collection of personally identifiable information through KYC standards, along with protocols for storing and transmitting identity data to which banks and other institutions in the existing finance/security infrastructure had long been subjected, was extended to cryptocurrencies and other so-called ‘virtual assets’.
Interstructural agency can be seen in how the formation of blockchain protocols triggered the extension of the Travel Rule, a key standard in the identification infrastructure, to the privacy infrastructure centred around blockchains. More of a recommendation for proper behaviour amongst organizations, the Travel Rule is itself a protocol allowing banks sending and receiving transactions to obtain customer identity information and to let this identity information ‘travel’ amongst them. The extension of the Travel Rule exemplifies how protocol-level activities in one infrastructure instigated continuities and changes in security practices in another. Locating the interstructural agency of activities at the site of protocols helps avoid understanding digitally mediated practices as entirely ‘hard-wired’ and unchanging on the one hand, as well as entirely novel on the other. Critical security studies gain more nuanced appreciations of the unexpected paths of ‘emergent security’ (Fouad, 2022) in the ongoing push-and-pull between identification and privacy politics by zooming in on activities at the site of protocols.
Interstructural agency can be located in both compliance and defiance. Following these twin processes illustrates how privacy and identification practices are shaped not just within but also between complex sociotechnical infrastructures. In a first instance, the process of compliance involves acquiescence with rules and regulations through the development of new protocols, which we call ‘add-ons’. 10 Most prominent ‘add-on’ protocols are those facilitating the compliance of blockchain-based transactions with the aforementioned Travel Rule. A flurry of ‘add-on’ protocols emerged after 2019 to provide a common language for communicating identity information between ‘virtual asset service providers’ (VASPs), the FATF’s technical name for entities facilitating the buying, selling or trading of cryptocurrencies and other blockchain-based products. The Switzerland-based OpenVASP network emerged from discussions and experiments between dozens of ‘identity start-up’ firms in novel relations with one another. The developments this network drew from new Ethereum-based protocol were said to put ‘privacy of transferred data at the center of its design’ (Riegelnig, 2019: 1). This network attempts to ‘square the circle’ of enabling VASPs to collect and transfer data on customers while ensuring that user anonymity is protected through the use of peer-to-peer messaging system Whisper, which employs ‘so-called dark routing to obscure message content and sender and receiver details to observers, a bit like anonymous web browsing using Tor’ (Allison, 2020). The attempt to balance privacy and identification practices with OpenVASP is one outcome of interstructural relations between actors and networks of new and established finance/security infrastructures. Similar ‘add-on’ standards include the likes of open-source peer-to-peer VASP Address Confirmation Protocol, developed by California-based CipherTrace (2019), a firm with close ties to the US Department of Homeland Security, and bought by Mastercard in 2021.
Locating add-on protocols developed for obtaining and sharing user identity information between VASPs as resulting from interstructural agency helps to illustrate both continuities and changes in security practices. Such specific ways of combining privacy and identification practices striving to collect yet also limit user information, as well as retain yet share it, were unlikely to emerge solely from a privacy-centric blockchain infrastructure or from an identification infrastructure. They are rather the outcomes of unfolding relations between these antagonistic infrastructures. A large part of what blockchain protocols originally arose to counter after all was precisely such identification and exchange of information. The significant but far-from-wholesale shift towards implementing standards for identification in this new privacy infrastructure is enabled by the creation of ‘add-on’ protocols developed by the likes of Taiwan-based Sygna, which emphasizes the need to maintain privacy practices while enable ‘VASPs to share encrypted transmittal information with each other securely and privately’ (Sygna, 2020). Foregrounding infrastructural agency at the site of computer protocols enables the more nuanced evolution in privacy and identification practices at the finance/security nexus to be understood. Locating what we call interstructural agency specifically foregrounds not only overlapping relations between infrastructures but also the relations that push infrastructures apart.
A second set of sociotechnical relations between infrastructures impacting the evolution of digitally mediated security practices at the site of computer protocols involves defiance. These processes were most prominently illustrated after 2019 as further ‘add-on’ protocols developed to escape the expansion of (limited) information-gathering and sharing by the Travel Rule. So-called ‘privacy protocols’ like Cashshuffle/Cashfusion, Lelantus, MimbleWimble and OpenBazaar arose, promulgating standards for enhanced, though rarely complete, anonymity for blockchain-based digital transactions. Some of these enhanced privacy protocols built on top of existing blockchain protocols, as Enigma (n.d.) did with Ethereum. Other ‘add-on’ blockchain privacy protocols developed entirely new standards of behaviour between human actors and non-human objects. Most prominently, the CryptoNote protocol underlying privacy-coin Zcash set a standard for minimal information-provision through the use of zero-knowledge cryptography. 11 Wasabi Wallet, a project enabling so-called secret contracts, meanwhile, allows its users to exchange without ever ‘seeing’ data, through novel transaction-scrambling standards. 12 The aforementioned post-2019 explosion of DeFi applications based on the Ethereum protocol also saw the expansion of ‘decentralized exchanges’ (DEXs), forums where peer-to-peer agreements to directly exchange digital tokens without identity verification by formal intermediaries are made. Other such Ethereum-based decentralized applications (DApps) that emerged in the post-2019 DeFi boom 13 included Tornado Cash, which offered updated ways of ensuring private finance transactions. Foregrounding activities at the sites of protocols highlights how the process of defiance in relations between infrastructures has nuanced implications for security practices. While numerous blockchain protocols emerged post-2019 to comply with the Travel Rule and other longstanding KYC protocols, other blockchain protocols doubled down on privacy practices. This defiance in turn has led to further developments in identification practices, which led to the arrest of a Tornado Cash coder in 2022 (Jagati, 2022).
Locating interstructural agency at the site of computer protocols helps to make nuanced sense of the evolution of security practices. Sociotechnical relations between existing and new infrastructures shape security politics through the two processes which we have traced here, that of compliance and defiance. Interstructural agency emerges out of collaboration amongst seemingly opposing standards for privacy and identification practices. Agency between infrastructures also emerges out of divergencies in the doubling-down on opposing privacy and identification practices. Locating the agential impacts of sociotechnical relations at the site of computer problems enables critical security studies to make sense of ‘emergent security’ (Fouad, 2022) in ways that navigate between continuity and change.
Conclusion
This article has argued for security studies to consider computer protocols as productive entry points for locating how what we call infrastructural agency shapes digitally mediated tensions between privacy and identification practices. Our analysis has distinguished inter- and infrastructural agency in the development and updating of computer protocols. Impacts on security practices of sociotechnical activities at the site of blockchain protocols on the digital networks and applications built upon them are forms of agency within infrastructures. Implications of sociotechnical relations at the site of protocols on other sets of sociotechnical relations are understood as agency between infrastructures. Locating these twin forms of infrastructural agency at the site of a particular set of computer protocols – blockchains – helps us make sense of the evolution of digitally mediated practices of privacy and identification since 2008. We have traced the formation and expansion of an alternative privacy-orientated finance/security infrastructure to activities at the sites of protocols like Bitcoin and Ethereum. Locating agency in updates and developments at the sites of these and other protocols helps us interpret the interactions of novel and longer-standing finance/security infrastructures over the decade following the 2007–2008 global financial crisis and beyond. Key sociotechnical relations underpinning both the initial and continual exercise of infrastructural agency within and between these finance/security infrastructures reveal overlaps and divergences in privacy and identification practices since 2008. Tracing the ‘birth’ of computer protocols, and their key updates and reformations, reveals security politics that are neither entirely dynamic nor wholly static. Activities at the site of blockchain protocols highlight a finance/security nexus in continual flux, where novel privacy practices both diverge from and reinforce identification practices.
By probing computer protocols, critical security studies can advance debates over infrastructures and techno-agency. Future research can further broaden the intersections of such discussions by asking, for instance: Who (re)develops the standards for digital communication between computers and between computers and humans? What networks and applications do certain computer protocols support? Which do they exclude or marginalize? How do computer protocols facilitate or hamper particular sociotechnical relations both within and between infrastructures?
Locating infrastructural agency at the site of computer protocols can shed further light on the security politics of digital ‘traceability’ by scrutinizing the identification standards emerging as part of Central Bank Digital Currencies (CBDCs). The standards for interoperability between CBDCs, some but not all of which are based on blockchain protocols, as well as between the identification practices they enable and the privacy of ‘analogue’ cash and coin-based monetary relations, are promising areas of future research at the finance/security nexus. Such investigations could foreground ‘protocological’ relations between coders and international bodies beyond the FATF, like the International Organization for Standardization (ISO), locating infrastructural agency in their shaping of the possibilities for privacy and identification practices (Campbell-Verduyn and Hütten, 2021). In locating infrastructural agency at the sites of computer protocols, critical security studies research can further widen engagements with science and technology studies, new media and software studies to include critical code studies (Marino, 2020) in order to tease out the security politics of evolving relations between human and non-human actors. Explicit attention to ethics and moral tensions informing and emerging from these interactions and those activities they enable could contribute to debates over what has been regarded by some as the more positive implications stemming from the development of a ‘two-tier financial ecosystem’ (Kapsis, 2020), one centred around privacy and the other around identification practices.
What our locating of infrastructural agency in activities at the sites of computer protocols ultimately hopes to stimulate is a politicization of seemingly esoteric sites where contemporary security practices are shaped and can also be challenged. Locating infrastructural agency in the (re)formation of standards guiding human–non-human relations is an important step in widening critical security studies’ encounter with the ‘marvelous minions’ whose (re)production increasingly shape digitally mediated contemporary security politics.
Footnotes
Acknowledgements
For constructive comments that substantially improved earlier versions of this article we thank the journal editor and three reviewers, Amir Kamel, Bernhard Reinsberg, Carola Westermeier, Hans Hansen, Jaya Klara Brekke, John Morris, Linda Monsees, Matthias Kranke, Nick Bernards, Ruben Kremers, as well as participants in the ‘Anticipatory Global Governance’ workshop at the European Workshops in International Studies, Kraków, 26–29 June 2019; the ‘Algorithmic Knowledge in Culture and Media’ workshop held at the Open University of Israel, Tel Aviv, 24–25 October 2019; the ‘Finance/Security Infrastructures’ workshop held at the University of Amsterdam, 13 November 2019; the Finance & Society conference, London, 12–13 December 2019; and the Security Studies Chair Group Research Colloquium at the University of Groningen in March 2022.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
