Abstract
This article explores the racial politics underwriting cybersecurity’s recent human turn toward the issues of online disinformation and ‘foreign influence’ in US politics. Through a case study of the Black Lives Matter (BLM) movement, this article’s first half considers how contemporary cybersecurity has produced ‘racial division’ as an object of security by framing the BLM movement as a geopolitical vulnerability open to foreign manipulation through social media. In its emphasis on the political protest as a site of insecurity, I argue that contemporary cybersecurity has widened its traditional spatiality ‘beyond the computer’. In the article’s second half, I argue that the racialization of cybersecurity has underwritten a politics of truth ultimately concerned less with parsing true from false, and more with defining the boundaries of secure political knowledge and communication. I argue that contemporary cybersecurity has produced an idealized subject for whom an obligation to possess contingent forms of knowledge becomes a condition of secure political subjectivity. I conclude with a critique of contemporary cybersecurity’s tendency to portray dissident political movements like BLM as ignorant or disinformed.
Introduction
Testifying as an expert witness on cyberwarfare before the US Senate in October 2017, Foreign Policy Research Institute fellow Clint Watts made the incredible claim that during the 2016 US presidential election ‘the largest and most successful information attack in world history’ had been perpetrated against the United States (Senate Judiciary Committee, 2017). According to Watts, the attack sought to ‘destroy our democracy from the inside out’ by ‘pit[ting] Americans against each other’. A ‘war on information itself’ (Ashok, 2016), its aim was, as Politico magazine put it, to ‘undermine the idea that there is objective truth’ (McKew, 2017). Significantly, Watts argued that the attacks worked to ‘amplify social divisions’, including efforts to ‘orchestrate protests and rallies’ and ‘dupe’ Americans into ‘unwittingly furthering’ adversarial foreign policy goals. The context of Watts’s testimony was widespread reporting in September 2017 that Russian-backed social media actors had worked to encourage and exploit the growing Black Lives Matter (BLM) movement, particularly the National Football League (NFL) players’ protest led by Colin Kaepernick.
While cybersecurity has traditionally been understood as the protection of digital networks and infrastructures, post-2016 cybersecurity discourses have stressed its increasingly human dimensions, notably around the issues of disinformation, manipulation, and political influence. As one 2019 trade conference suggested, cyber operators from the military and government are now faced by a new question: ‘who, not what, will be targeted by hostile cyber operators?’. 1 In tracing its human turn, this article explores how the politics of race and truth have been central to a new and expansive vision of cybersecurity. The article’s first half demonstrates that contemporary cybersecurity has been underwritten by an uneven racial politics in which Black political projects, notably the BLM movement, have been presented as strategic vulnerabilities open to foreign manipulation through social media. In claiming that the BLM movement produces ‘racial division’ qua cyber-vulnerability, I argue that contemporary cybersecurity seeks to suppress forms of racial protest, preferring the tolerance of racial inequality to its amelioration.
In its second half, the article argues that the racialization of cybersecurity has produced a politics of truth concerned less with parsing true from false, and more with defining the boundaries of secure political knowledge and communication. I argue that contemporary cybersecurity has produced a model political subject for whom a contingent ‘obligation to know’ serves as the basis of a secure political subjectivity. I suggest furthermore that the secure subject of cybersecurity has been reimagined as the basis upon which the security of the broader democratic polity rests. I show that contemporary practices of ‘securing truth’ therefore appear in a double sense: as the act of parsing ‘good’ information circulation from ‘bad’, but also as the power of ‘secured truth’ to secure the subject of cybersecurity. I conclude by critiquing the racialized nature of the subject of cybersecurity, its normative obligation to disavow ‘divisive’ political projects, and cybersecurity’s broader effort to identify dissident political projects as ignorant, ‘idiotic’, or disinformed.
In considering how race and ‘truth itself’ have been positioned as referent objects of cybersecurity, I do not suggest that questions concerning cybersecurity’s traditional referents are settled. These remain contested and fruitful avenues for research (Betz and Stevens, 2013; Deibert, 2002; Deibert and Rohozinski, 2010). In critiquing cybersecurity’s politics of race and truth, this article contributes to a growing critical literature on the human dimension of cybersecurity (Balzacq and Dunn Cavelty, 2016; Dunn Cavelty, 2007, 2013; Hansen and Nissenbaum, 2009; Kaiser, 2015; Stevens, 2016) as well as its politics of technology and expertise (Amoore, 2020; Dunn Cavelty and Egloff, 2019; Shires, 2018; Stevens, 2020; Timcke, 2017, 2021). Its primary contribution is to critique the construction of ‘truth’ as an object of cybersecurity (Buzan et al., 1998; Lewandowsky, 2020) and to show how contemporary cybersecuritization has produced uneven and racialized foreclosures of democratic politics (Aradau, 2004; Hansen, 2012).
Cybersecurity and the politics of race
Discourses of cybersecurity have traditionally been dominated by political imaginaries of data, technology, and technical expertise. Since 2016, however, the issue of race has been remarkably visible in cybersecurity’s popular construction. In this article’s first half, I document contemporary cybersecurity’s construction of ‘racial division’ as a fundamental stake of its human turn. I show that cybersecurity’s claim on ‘racial division’ has transformed the political landscape on which it operates, widening its aperture to encompass protest and political dissent more broadly. I conclude by arguing that an unspoken yet fundamental condition of contemporary cybersecurity is the production of ‘racial unity’ based upon the tolerance of racial inequality rather than its amelioration.
‘The Divided States of America’
In the Fall of 2017, National Football League players readied for a second season of on-field protests, drawing attention to issues of racialized violence and inequality in the United States. Begun the previous season by San Francisco 49ers quarterback Colin Kaepernick, the protests were widely associated with the growing Black Lives Matter (BLM) movement. As the season began, social media tags like #taketheknee and #boycottNFL quickly achieved viral status (Kelly, 2016; More, 2018). However, reports soon began to circulate that the online activity was being stoked by covert Russian operatives seeking to ‘stir up divisions in the United States’. Invoking classified intelligence briefings, Senator James Lankford (R-OK) claimed that Russian ‘internet trolls’ – paid or state-sponsored social media users – had been exploiting the controversy to ‘create doubt and sow chaos in U.S. institutions and government’ (Dupree, 2017).
After a Senate Homeland Security Committee hearing with heads of US intelligence agencies on 27 September, Lankford ‘made an individual decision to start talking publicly’ about Russian propaganda, releasing an example of what he said was a Russian Twitter account posing as ‘Boston Antifa’, an anti-fascist activist group. The tweet he circulated (see Figure 1) was notable for its geolocation in Vladivostok, which was widely reported as evidence of its Russian origin (Barrett, 2017). However, the tweet was a joke: ‘Boston Antifa’ was a parody account based in Oregon State, and the account’s geolocation had been manually set to Vladivostok to satirize so-called Russiagate discourse (Taibbi, 2017). Nevertheless, Lankford’s claims about the tweet’s Russian origins, backed by intelligence authority, were widely reported in the US press.

A joke tweet from an Oregon-based Twitter account makes light of perceived ‘culture war’ issues. Senator Lankford claimed there was ‘a high likelihood it was connected to some Russian entities’ (Taibbi, 2017).
The episode appeared in the wake of revelations a month earlier that the Moscow-based Internet Research Agency had spent $100,000 to purchase 3000 Facebook advertisements in the lead-up to and aftermath of the 2016 US presidential election (Leonnig et al., 2017). Though a small sum compared to the $6.5 billion spent by both parties on the election (Shane and Goel, 2017), the ads were framed in US media as the tip of the ‘Russiagate’ iceberg that would lead to further explosive revelations. While reporting on ‘Russiagate’ to this point had largely stressed Russian efforts to bolster Donald Trump’s xenophobic ‘alt-right’ base (Porter, 2017; Shane, 2017), the Facebook revelations combined with the NFL controversy to mark a turning point toward emphasis upon left-wing and Black political activism as vehicles for Russian cyberwarfare.
Indicative of this shift, the Washington Post reported that the Facebook ads revealed ‘a deep understanding of social divides in American society’, with some ads ‘promoting African American rights groups, including Black Lives Matter’ (Timberg, 2017a). In the following days, congressional leaks to the press revealed that ‘at least one’ Facebook ad had targeted the cities of Ferguson and Baltimore, notable locations of major Black Lives Matter protests in 2014 and 2015 (Byers, 2017). Citing anonymous sources, the Washington Post described one ad featuring ‘photographs of an armed black woman “dry firing” a rifle – pulling the trigger of the weapon without a bullet in the chamber’. While this ad has not surfaced along with Facebook’s later release to the Senate, textual descriptions of the ‘dry-firing’ images circulated widely in the press, stressing the point that the ad ‘may have been designed to encourage African American militancy’ (Timberg, 2017b). A former CIA analyst suggested that this targeting of ‘certain communities and issues’ was ‘consistent with [Russia’s] overall goal of creating discord’ (Sheth, 2017). Meanwhile, stories emerged placing the BLM movement within a ‘history of Russian involvement in America’s race wars’ (Ioffe, 2017). The Atlantic, for example, identified Russian efforts to exploit BLM protests as ‘just another page from the old Soviet handbook’, which included notable cases like the 1931 Scottsboro Boys trial and the 1957 Little Rock crisis.
After two months of intense press coverage, at the 31 October Senate Judiciary Committee (2017) hearing on ‘Extremist Content and Russian Disinformation Online’, US Senators lambasted representatives of Facebook, Twitter, and Google for failing to curb Russian interference into US political life. Dianne Feinstein (D-CA) stressed that Russia ‘sought to sow discord and amplify racial and social divisions among American voters’. Chuck Grassley (R-FL) claimed that Russia had ‘spread stories about abuse of black Americans by law enforcement’ to ‘worsen racial tensions and possibly violence’. The Russians ‘take a crack in our society and turn it into a chasm’, argued Angus King (I-ME). In a later House Intelligence Committee hearing, Adam Schiff (D-CA) noted the ‘Kremlin objective’ of ‘sowing discord’ by ‘inflaming passions on divisive issues’ (Siegel, 2017).
At the Senate hearing, expert witness Clint Watts made the claim that Russia had ‘perpetrated the largest and most successful information attack in world history’ (Senate Judiciary Committee, 2017). In his testimony, Russian cyberwarfare assumed almost supernatural proportions, appearing as ‘dark arts of manipulation and subversion’ that sought to ‘destroy our democracy from the inside out’. Perhaps the most prominent cyberwarfare expert in US media, Watts stressed the matter of war: the Russians, he testified, ‘use information as a weapon of warfare’ (Rubin, 2017). Invoking ballistic imagery of ‘information missiles’, Watts claimed that information leaks now gave Russia ‘nuclear fuel for information atomic bombs’ and that ‘America’s war with itself has already begun’. He warned that we all must act now on the social media battlefield to quell information rebellions that can quickly lead to violent confrontations and easily transform us into the Divided States of America. (Senate Judiciary Committee, 2017)
The senators agreed. ‘This is about national security’, said Committee Chairman Richard Burr (R-NC). ‘I don’t think you [tech companies] get it,’ Feinstein inveighed. ‘What we’re talking about is a cataclysmic change. What we’re talking about is the beginning of cyberwarfare’ (Soergel, 2017).
Protest as a site of cybersecurity
On the back of his ‘star performance’ (Pesca, 2017) before the Senate, cyberwarfare expert Clint Watts established an organization called the Alliance for Securing Democracy (ASD), with funding from the US State Department and the German Marshall Fund. 2 Its purpose was to ‘publicly document and expose Vladimir Putin’s ongoing efforts to subvert democracy in the United States and Europe’ (Rosenberger and Fly, 2017). Its primary tool was a website called the ‘Hamilton Dashboard’ that claimed to ‘help journalists and ordinary people alike identify Russian messaging themes and detect active disinformation’ by tracking 600 Twitter accounts that it claimed were ‘meaningfully linked’ to Russia (ASD, 2017). Although the Alliance did not disclose its data, its methodology, its 600 monitored accounts, or the nature of their meaningful links to Russia, the group’s efforts were central to publicizing connections between Black political activism and Russian cyber operations. By September 2017, the Alliance’s divinations were exhaustively and often singularly cited in media reports as evidence that NFL protests were ‘linked to Russian influence operations’ (Wakabayashi and Shane, 2017; see also Riechmann, 2017). Speaking to PBS, an Alliance spokesperson claimed that ‘clearly [the Russians] found something that works with the NFL’ (Einbinder, 2017).
While traditional answers to questions concerning the spaces to which cybersecurity belongs have appropriately emphasized the network and cyberspace, cybersecurity’s human turn has widened the aperture of its spatiality. Through the lens of cybersecurity, the NFL players’ protest appeared not as the materialization of organic political dissent, but as a site from which foreign antagonists stir ‘division’ in the national polity. In this geographical imagination (Gregory, 1994), the space of cybersecurity is reconstituted around questions of race, unity, domestic order, and geopolitical competition. The protest thus appears in this imagination as a site where cybersecurity’s divergent political geographies are reterritorialized (see Ó Tuathail, 1996) ‘beyond the computer’. 3
In the wake of the NFL players’ protests in the Fall of 2017, other Black Lives Matters protests were similarly positioned as sites of cyber-insecurity where ‘foreign powers were able to land and manipulate boots on American ground’ (Kosoff, 2017). Claiming that Black political organizers had been ‘tricked into working for Russia’ (Adams and Brown, 2017), stories stressed that ‘targets seem to primarily have been black activists’ (Kosoff, 2017). In this political imagination, Black activists appear not as American citizens exercising rights of speech and assembly, but as targets of foreign cyberwarfare offensives whose racialized political project produces unique and acute forms of vulnerability and manipulability. The protest consequently appears as an extension of the ‘social media battlefield’, and Black activists are imagined as soldiers whose ‘boots on the ground’ are directed by geopolitical adversaries. The protest and the protestor therefore appear as both targets of and vehicles for foreign cyberwarfare.
While the charge of ‘sowing division’ has landed primarily at the feet of Black activists, similar claims have been made concerning the 6 January 2021 Capitol Hill riot in Washington, DC. On the Carlos Watson Show (2021), former Central Intelligence Agency director John McLaughlin claimed he would ‘not be surprised if, when we unpack what happened on Capitol Hill . . . we will find [social media] personalities and identities that ultimately will turn out to be Russian’. US Speaker of the House Nancy Pelosi similarly called the riots ‘a gift to Putin’, adding that ‘these people, unbeknownst to them, maybe, are Putin puppets’ (Jewers, 2021). Mirroring the ‘boots on the ground’ narrative attached to the BLM movement, Hillary Clinton called the riot an ‘invasion’ and recommended ‘a 9/11 [style] commission’ to investigate its link to Russian cyberwarfare efforts. In framing the Capitol Hill riot as a foreign cyberattack, these statements not only work to obscure and externalize the domestic basis of right-wing extremism in the United States, but also further the reconstitution of the protest as a site of cybersecurity – as a target of, and medium for, cyberwarfare.
Through the logic of cybersecurity, the protest thus appears as a ‘seam’ (Cowen, 2014: 82), a ‘liminal zone between inside and outside space’ in which lines between military and police authority are blurred. This reconstitution of the space of cybersecurity has been achieved in part through an imaginative transposition of political dissent to the register of geopolitical contest, a reflection of the ‘swift erosion of distinctions between domestic and foreign spaces taking place today’ (Bousquet, 2018: 193). In this geopolitical imagination, cyberwarfare extends foreign territory into the United States and protesters appear as manipulable, unwitting subjects whose ‘boots on the ground’ traverse the liminal political borders thereby produced. Contemporary cybersecurity thus builds upon the axiom that ‘cyberspace makes us vulnerable’ (Barnard-Wills and Ashenden, 2012: 118; see also Kaiser, 2015) by extending the logic of cybersecurity ‘beyond the computer’ into corporeal spaces of political protest.
Unity, race, and cybersecurity
Simone Browne (2015: 16) notes that ‘enactments of surveillance reify boundaries, borders, and bodies along racial lines’. In framing the BLM protest as a liminal space in which fluctuating geopolitical borders are traversed by subjects that appear both inside and outside the body politic, contemporary cybersecurity has similarly reified boundaries along racial lines. To the extent that exploitation of ‘racial division’ has been framed as a fundamental feature of cyberattacks against the United States, a begged yet unspoken premise concerning the production and defense of ‘racial unity’ underwrites contemporary cybersecurity as its normative condition. In framing ‘racial tension’ as an object of insecurity, cybersecurity belies what Browne (2015) calls a ‘prototypical whiteness’: challenges to the status quo of racial hierarchy are understood as normatively dangerous, and Black activists appear as invaders ‘outside the virtuous domestic community of the American homeland’ (Bialasiewicz et al., 2007: 417; see also Alves, 2014).
By contrast, reported details of attempts at Russian infiltration into Black activist movements belie the hype. As Buzzfeed reported, in 2016 Russian agents were purported to have contacted several Black American organizers under the alias of ‘BlackMattersUS’ – meant to appear as a spinoff or affiliate of Black Lives Matter – offering advice, encouragement, or petty cash to cover costs of protest organization (Adams and Brown, 2017). However, of the three individuals identified by Buzzfeed, one did not organize protests at all, breaking contact with his interlocutor after several stilted exchanges. A second activist organized local self-defense classes for several weeks, beginning only after the 2016 election, and similarly breaking contact when the arrangement began to seem suspicious. A third activist organized two protests, one in September and another in October of 2016. Both were in response to the killing of Keith Lamont Scott, a Black man shot to death by police in Charlotte, North Carolina. While reporting stressed that the activist had been ‘tricked’ into organizing the protests, they were in fact part of a series of national protests, many of which had been organized by the American Civil Liberties Union and the National Association for the Advancement of Colored People in direct response to the killing.
Despite weak evidence tying the Black Lives Matter movement to foreign online influence, ‘racial tension’ has become a central theme of contemporary cybersecurity discourse. Since ‘racial tension’ appears not only as an outcome but also as a medium of cyberwarfare, cybersecurity not only seeks to mitigate online attempts at producing racial tension, but also understands ‘racial tension’ itself as productive of cyber-insecurity. This radical expansion of cybersecurity in turn corresponds to a flattening of the uneven landscape of racial inequality in the United States. On this flattened terrain, ‘racial division’ appears to be equally the product of racial justice activists, on the one hand, and the far-right white nationalists who oppose them, on the other. As one DC-based think-tank put it, ‘left-wing and right-wing extremists feed off each other by reinforcing each other’s grievance narratives’ (Hawn, 2021). However, as BLM activist Anoa Changa (2017) observes, framing black activism as ‘divisive’ treats the alt-right and white nationalists as if they are on equal footing with those struggling for racial justice. The underlying presumption is that addressing systemic issues of equity and human rights is the problem, and not the denial of rights itself.
Through the logic of cybersecurity, the political contours of ‘racial tension’ have been flattened such that normative appeals to ‘racial unity’ equate sources of ‘division’ across the political spectrum. Taking aim at both ‘left-wing and right-wing extremists’, the DC-based New Lines Institute suggests that the United States should ‘enact legal reform officially defining . . . what ideologies are considered extremism while enforcing regulations that hamper extremists’ ability to organize and spread their ideology online’ (Hawn, 2021). Racialized discourses of (counter-)extremism (Younis, 2021) are thus folded into cybersecurity’s ambition to flatten and suppress ideologies it deems extreme or divisive. Through the lens of cybersecurity, the social and political contours of protest movements are thus radically distorted, with racial inequality, police violence, Black political agency, and white supremacism receding from view. In their place, cybersecurity appears overdetermined by the presumed malleability of Black activists, as well as the white nationalist ‘grievance narratives’ these activists are said to reinforce.
As noted by History and African American studies professor Gerald Horne, the association of Black activism with right-wing extremists and geopolitical rivals carries with it the implicit suggestion that ‘black people should not be protesting in the streets about being executed without due process of law by officers of the state’ (Horne and Changa, 2017). Contemporary cybersecurity has thus placed normative demands on Black Americans to curtail the kinds of political activism it claims produce ‘racial division’ in the body politic. While it is possible to envision alternative responses to the insecurities of racial inequality through political projects of recognition and redistribution, these remain foreclosed possibilities in contemporary cybersecurity discourses. In their place, contemporary cybersecurity strives not for redress of the hierarchical structures that produce ‘racial tension’ qua insecurity, but for policing and pacifying the effects those structures produce. In this political imagination, ‘racial unity’ consists not in the elimination of racial inequality, but in its forbearance. Cybersecurity’s human turn has thus turned the structure of racial inequality upside down: the victim of racism appears as the political order to which calls for racial justice are addressed, and its crisis consists not in the violence of inequality, but in the ‘tension’ produced when the oppressed seek redress.
Cybersecurity and the politics of truth
Contemporary discussions surrounding the so-called post-truth era have revolved around claims concerning foreign cyberwarfare and online political influence (Alterman, 2018). As Politico suggests, ‘truth itself’ appears existentially threatened by foreign cyberwarfare programs ‘designed to undermine the idea that there is objective truth’ (McKew, 2017). This ‘war on truth’ has in turn been framed as an ‘information war against global democracy’ (Calabresi, 2017), in which democracy appears not only as a target but also as the medium of attack: ‘the Russians have always used the openness of democracy against us’, a former British official told Wired magazine. ‘Russia knows how to effectively exploit the seams and systemic weaknesses in Western democracies’ (Graff, 2017). In the second half of this article, I consider how contemporary cybersecurity practitioners have attempted to ‘secure truth’ against cyberattack. I argue, however, that cybersecurity’s politics of truth have been concerned less with parsing true from false, and more with defining the boundaries of secure political knowledge and communication in a democratic society.
More than matters of fact, I suggest that cybersecurity’s politics of truth revolve around contingent forms of knowledge concerning a constellation of domestic and geopolitical concerns. I argue that these politics of truth produce a confessional political subject for whom an ‘obligation to know’ serves as the basis of a secure political subjectivity. ‘Securing’ truth therefore appears in a double sense: as a verb parsing ‘good’ information circulation from ‘bad’, but also as an adjective describing the power of ‘truth’ to make the subject of cybersecurity secure. I conclude by demonstrating the convergence of cybersecurity’s politics of race and truth in its construction of the figure of the disinformed racial subject. Showing that contemporary cybersecurity has worked to portray social movements for racial justice as ignorant, ‘idiotic’, or disinformed, I close by arguing that critical security scholars should resist attempts to ‘suspend the political’ (Swyngedouw, 2017: 56) and refuse cybersecurity’s overdetermination of dissident political projects.
Securing truth
One of the first and most significant illustrations of ‘securing truth’ against cyberattack took form as a bizarre political drama at the outset of the ‘Russiagate’ scandal in the weeks following the 2016 US presidential election. Perhaps the first major newspaper to suggest the existence of a ‘sophisticated Russian propaganda campaign . . . undermining faith in American democracy’, the Washington Post profiled an anonymous organization called PropOrNot [Propaganda or Not], a newly formed ‘nonpartisan collection of researchers with foreign policy, military and technology backgrounds’ that claimed to have identified ‘the startling reach and effectiveness’ of Russian propaganda (Timberg, 2016). Like the Alliance for Securing Democracy, however, PropOrNot refused disclosure of its methodology, data, and even the identity of its own members. In place of supporting evidence or documentation, the group circulated a list of 200 websites it claimed were ‘routine peddlers of Russian propaganda during the election season’. While notable political figures promoted the Post’s story, 4 critics – including several left-leaning news sites that found themselves listed – objected to PropOrNot’s ‘200 websites’ as a blacklist (Chen, 2016). After considerable backlash, the Washington Post story now carries a substantial editor’s note distancing its reporting from PropOrNot’s methods and conclusions.
Scrutiny of PropOrNot’s efforts to ‘secure truth’ reveals not so much specific practices but a generalized ‘rhetoric of technique’ (Sherry, 1987: 226) in which highly specialized forms of digital investigation purport to reveal covert programs of propaganda and disinformation. Despite the nondisclosure of PropOrNot’s data or methodology, the Washington Post nevertheless pointed to its use of ‘internet analytics tools to trace the origins of particular tweets and map the connections among social-media accounts that consistently deliver synchronized messages’ (Timberg, 2016). Though it remains unclear what constitutes consistency or synchronization, 5 PropOrNot’s rhetoric of technique centered upon the premise that it could employ digital methods to arbitrate the security of political communication (PropOrNot, 2016). Attempts at ‘securing truth’ can therefore be understood as a kind of ‘technification’ – that is, ‘the constitution of an issue as reliant upon expert, technical knowledge for its resolution and hence as politically neutral or unquestionably normatively desirable’ (Hansen and Nissenbaum, 2009: 1157; see also Hagmann and Dunn Cavelty, 2012; Huysmans, 2006; Timcke, 2021). While this rhetoric of technique suggests the authority of contemporary forms of open-source and forensic evidentiary investigation (Weizman, 2017), PropOrNot’s work has on the contrary been marked by opacity and secrecy (see Kearns, 2017; Thomas, 2020; Van Veeren, 2019).
Scrutiny of PropOrNot’s (2016) so-called Black Friday Report suggests that, more than technical analysis, its conclusions turn upon what it calls ‘the Russian propaganda line’, a broad set of indeterminate criteria relating to generically ‘positive’ news coverage of Russia, Iran, and China, as well as generically ‘negative’ news coverage of the United States, NATO, ‘mainstream media’, and ‘moderates of all stripes’. Though couched in a rhetoric of digital technique, PropOrNot’s analysis turns out to revolve around a geopolitical axis on which adversarial cyberwarfare is said to ‘tarnish trust in democratic institutions’ (Brandom, 2017). In this political imagination, any information critical of US institutions appears as Russian propaganda ipso facto, irrespective of its truth or factuality. PropOrNot’s analysis therefore produces the connections it purports to reveal: rather than revealing material connections among coordinated parties, PropOrNot’s analysis works in reverse by identifying a broad ‘Russian propaganda line’ and attributing the label of Russian propaganda to whatever can be interpreted as toeing it. As its report readily admits, independent of questions about whether the sites we’ve identified are being knowingly directed and paid by Russian intelligence officers, or whether they even knew they were echoing Russian propaganda at any particular point – if they display the characteristics [of the Russian propaganda line], they are at the very least acting as ‘ useful idiots ’ of the Russian intelligence services, and are worthy of further scrutiny. (PropOrNot, 2016)
While presenting itself as a bulwark in the ‘war on truth’, PropOrNot does not in practice attempt to parse true from false. More than matters of fact, its efforts revolve around matters of geopolitical concern. In concluding its blacklist report, PropOrNot called for official investigation into websites that ‘run counter to Western interests’. The sites, it argues, ‘and more to the point the people who operate them’, should be ‘of interest to the security services of the Western countries in which they live, work, and acquire services related to their websites’. While these statements beg questions concerning the nature of ‘Western interests’, they also illustrate the extent to which contemporary cybersecurity discourses have attempted to structure a politics of truth not in relation to matters of fact, but in relation to a constellation of specific (geo)political interests. In this light, ‘securing truth’ is grasped more readily as the practice of managing circulations of information, of parsing ‘good’ circulation from ‘bad’, and of making circulations of information contingent upon US political interests (Dillon and Lobo-Guerrero, 2008; Foucault, 2007: 18).
This observation is supported by scrutiny of PropOrNot’s blacklist, 6 an incongruous inventory of Russian state outlets (sputniknews.com) mixed with sources outside the US political mainstream, from the so-called alt-right (infowars.com, drudgereport.com) to the democratic-socialist left (counterpunch.org, nakedcapitalism.com), to Black activists (blackagendareport.com), to the supernatural and outlandish (endtimesheadlines.org). Though seemingly incongruous, the listed websites reflect the ‘domestic cleavages’ said to threaten US political institutions. ‘It doesn’t even matter what their political leanings are,’ claims Clint Watts. ‘Russia just pushes populists against the establishment’ (Perlroth, 2020). In this political imagination, distinctions between left and right political projects are again flattened into a contest between a ‘moderate’ establishment and ‘populists’ who threaten its political stability. Thus the Black Lives Matter protest becomes functionally identical to the right-wing anti-immigration rally: in posing a flattened ‘populism’ against a ‘moderate establishment’, cybersecurity discourse identifies political projects outside the establishment mainstream as ‘excesses of democracy’ (Ó Tuathail, 1996) in need of moderation by a professional class of political and military experts who represent moderate and therefore ‘secure’ politics.
In this formulation, criticism of ‘moderates of all stripes’ is transmuted ipso facto into adversarial propaganda, and the spectrum of ‘moderate politics’ is shifted away from political projects that produce ‘racial division’ in their demands for racial equality. Since democracy appears not only as the object but also as the medium of cyberwarfare, contemporary cybersecurity demands a ‘post-political’ foreclosure of democratic excesses that challenge the stability of political order (Swyngedouw, 2018). While cybersecurity actors thus position themselves as ‘truth-tellers’ deciphering underlying realities (Crampton and Ó Tuathail, 1996), the politics of truth they advance appear less concerned with parsing true from false, and more with questions concerning the shape and possibility of democratic politics. Practices of ‘securing truth’, though framed in terms of esoteric technical analysis, have on the contrary tended to assert authority where evidence is wanted.
The subject of cybersecurity
In its emphasis on defending democracy and securing truth, contemporary cybersecurity has become increasingly ‘human centric’ (Cheng et al., 2019). While the status of the individual as an object of cybersecurity has been debated in existing scholarship (Carr, 2016; Collier, 2018; Hansen and Nissenbaum, 2009), in this penultimate subsection I argue that cybersecurity’s politics of truth have produced a corresponding ‘subject of cybersecurity’ for whom an ‘obligation to know’ (Foucault, 2014a: 256; 2014b: 93; see also Legg, 2016, 2019) becomes the basis of secure political subjectivity. If, as Walker contends, ‘the subject of security is the subject of security’ (Walker, 1997: 78, emphasis in original), I follow him in asking how the modern subject is being reconstituted and what security could possibly mean in relation to it.
This subject of cybersecurity is defined neither through its possession of digital rights (Deibert, 2018) nor through humanitarian discourses of human security (Watson, 2011). Rather, this subject of cybersecurity is defined by a contingent relationship to practices of ‘securing truth’ that render it resistant or resilient to disinformation and manipulation. More than the result of parsing fact from fiction, however, the subject of cybersecurity appears overdetermined by concern with what Foucault (2014a: 19) calls ‘the strange truth that the individual must produce about himself’. A strange truth indeed: as one former CIA analyst sees it, ‘if we are confident in ourselves, these Russian attacks have little effect’ (Sipher, 2018). For Politico, ‘understanding how the Kremlin has tried to achieve [its goals] is absolutely essential’ (McKew, 2017). In these formulations, knowledge, and particularly knowledge of oneself, appears as the basis of a new human-centric paradigm of cybersecurity. ‘If it sounds alarming,’ advises Time magazine, ‘it helps to understand the battlespace of this new information war’ (Calabresi, 2017).
These suggestions of talismanic knowledge-as-security appear widely in popular cybersecurity discourse, often taking the form of direct second-person addresses to a quotidian you, stressing the individual scale of cyberwarfare and its targets. As one anonymous intelligence source told Time magazine, ‘the Russians target you and see what you like, what you click on, and see if you’re sympathetic or not’ (Calabresi, 2017). Politico addressed its reader more directly: ‘if you understand what the Kremlin is up to, the news is grim, but it also gives us a clear path to fight back’ (see Figure 2). The imperative to ‘understand what the Kremlin is up to’ appears here as a kind of ‘obligation to know’ for the subject of cybersecurity. To be secure, one must know. In this formulation, truth appears not just as an object whose contingent circulation must be secured, but also as a possession that of itself secures the subject of cybersecurity.

The obligation to know: Hailing the subject of cybersecurity (McKew, 2017).
Here the scales of cybersecurity’s governmental structure converge upon the double meaning of ‘securing truth’: securing the contingent circulation of information at the level of population has its counterpart in the subject of cybersecurity whom truth secures. In both cases, the relationship between security and truth consists not in parsing the true from the false, but in tying the security of the nation to the individual’s obligation to know. The subject of cybersecurity therefore understands itself as a ‘double subject’ who is subject to but also an actor in the operation of power (Foucault, 2014b: 81). It apprehends itself not as a sovereign political citizen but as a target – as an object of enemy technique, a site of struggle, liable for defeats, and obligated to know the truths that make it secure. As Bousquet (2018: 197) observes, if ‘the classical political subject was a result of centralized forms of observation, today the object of targeting practices is also always its subject’.
Special stress upon the ‘psychological’ nature of cyberwarfare reinforces the scale of the individual as its key terrain (Farish, 2007; Whyte, 2018a, 2018b). As Timothy Snyder warns, ‘Russia was always better than us when it came to penetrating their enemies and breaking them down from within’ (Illing, 2018). Mirroring anxieties surrounding the porous and permeable nation, cybersecurity discourse stresses the penetrability of the individual – of what Deutsche (1991: 27) identifies as the otherwise assumed ‘complete masculine subject’. Here the individual and the state collapse in the production of cybersecurity as a kind of ‘scaled intimacy’ (Cowen, 2004; Jones and Fowler, 2007), reflecting the neoliberal tendency to make the modern subject the hegemonic terrain of politics and the ‘desideratum in contemporary discussions of security’ (Dalby, 2000: 14). Disarticulated and atomized, the subject of cybersecurity must retreat further from popular political activity, since popular (or ‘populist’) non-individualized political action – such as participation in protest movements – is precisely the ‘divisive’ political condition that only personal awareness can mitigate. Cybersecure subjectivity therefore appears as a kind of post-political dis/avowal (Foucault, 2014a; Swyngedouw, 2018): to be secure one must avow political moderation, trust in institutions, and disavow racialized excesses of democracy. Contemporary cybersecurity thus ‘tells us who we must be’ (Walker, 1997: 71) and lays out the conditions under which we become secure.
Emphasis upon the individual as the terrain of cybersecurity furthermore corresponds to an imagined national community (Anderson, 1983), and to Others outside it whose political horizons must be foreclosed. Cybersecurity therefore involves defining the boundaries of the ‘homogeneous and virtuous domestic community’ (Bialasiewicz et al., 2007: 417), specifying for and against whom democracy must be secured. It decides who is secure in the possession of truth and who is the ‘useful idiot’ in whom insecurity lurks. It materializes racialized Others as threats (Campbell, 1992) who have failed in their obligation to know, while also ‘maintaining certain collective identities, certain senses of who we are’ (Dalby, 2002: 163). In addition to these overt acts of Othering, cybersecurity furthermore enacts an internalization of judgement such that individuals ‘refrain from doing what would characterize them, in their own eyes, as abnormal’ (Vaz and Bruno, 2003: 278).
In addition to casting the martial gaze on civil society (Bousquet, 2018: 192), cybersecurity thus directs the individual to cast a martial gaze upon itself. Contemporary cybersecurity augments the modern subject that has, as Foucault suggests, been conditioned by ‘a Christian notion of continual, exhaustive confession in the face of state apparatus, securing not only a docile body but also an anxious, self-disclosing citizen’ (Salter, 2007: 49). As Clint Watts put it, ‘you cannot counter back . . . unless you know what your nation’s policies are, what your belief systems are’ (Seldin, 2017). In this strange formulation, vulnerability to cyberattack consists in not knowing who you are. Despite its presumptively technical nature, contemporary cybersecurity has posed more fundamental, non-technical questions concerning subjectivity and truth (Foucault, 2017); about ‘who are we and to what space we belong’ (Harvey, 1990: 426–427). These turn out to be political questions.
‘Useful idiots’: Cybersecurity’s racialized subjects
Viana and Da Silva (2021) note that recent US law enforcement discourses surrounding ‘Black racial extremism’ reproduce in the United States what Krishna (2019: 292) has identified as the tendency to frame the Third World as ‘a space of ontological deficit rather than an historical outcome of First-World colonialism’. Similar emphasis on Black deficit has dominated the politics of truth in contemporary cybersecurity discourses. In the geopolitical imagination of cybersecurity, racial justice activism appears not as an organic or appropriate response to material conditions of inequality and oppression, but as a kind of ignorance, a failure of one’s ‘obligation to know’ one’s personal and geopolitical responsibility. Supreme Court Justice Ruth Bader Ginsberg, for example, called the NFL players’ protest ‘dumb’ (Rhodan, 2016), while other Black activists have been widely disparaged as ‘useful idiots’ whose supposed ignorance, manipulation, and exploitation pose new threats to national security (Bauder, 2020; Navarro, 2020; Polus, 2020).
As Black activists have noted, these defamatory claims have had a chilling effect on their work and its reception (Del Valle, 2017; D. R. Ford, 2019; Lindsay, 2017). Commenting on BLM activist Anoa Changa’s appearance on an RT [Russia Today] news segment in 2018, National Public Radio (NPR) reported that the network [RT] gives Changa another platform to get her message out. She denounces what she calls racial injustice and oppression. These concerns fall in line with what experts call a key message of Russian propaganda – amplifying existing political and social divisions. (Kauffman, 2018)
While RT is widely understood as an arm of Russian state public diplomacy (Yablokov, 2015), criticism of Changa went beyond this association to present her and other activists as ‘parroting Russian talking points’ (Kauffman, 2018). More than criticism of Changa’s decision to appear on RT, this framing suggests that discussions of racial inequality in the United States constitute Russian propaganda ipso facto. As PropOrNot (2016) stresses, ‘independent of [being] knowingly directed or paid by Russian intelligence officers, [individuals] echoing Russian propaganda [are] at the very least acting as “useful idiots” of the Russian intelligence services’. Since the denunciation of racial injustice and oppression ‘falls in line with Russian propaganda’, subordination of racial justice to national security appears as prudence, while failure to forebear it is decried as ignorance.
On this account, NPR did not challenge the factuality of Changa’s statements. Rather, it called into question her capacity for autonomous political agency, characterizing her activism as ‘parroting’ Russian propaganda. Glen Ford, the late editor of Black Agenda Report – incidentally one of the 200 websites on PropOrNot’s blacklist – similarly notes the logic underwriting the ‘useful idiot’ narrative: ‘folks fear being called “witting or unwitting dupes,” and when Russian click-baiters mimic the language and symbolism of the Black liberation movement, corporate media infer that the Black people that genuinely hold those positions have absorbed them through Russian-tainted social media’ (G. Ford, 2019). As these rebuttals illustrate, association with foreign propaganda not only works to delegitimate Black activists, but also calls into question their capacity for unadulterated political agency. Like Foucault’s judge, physician, and psychiatrist, cybersecurity shifts power ‘away from the subject as authority on the self’, while seeking not only to ‘describe what is normal and what is abnormal, but also to define what is true and what is false about that individual’ (Salter, 2007: 58). The normative identification of Black activists as ‘duped’ or ‘disinformed’ thus provides disenfranchisement with a paternalistic gloss, what Viana and Da Silva (2021: 25) elsewhere identify as the counterinsurgent tendency to ‘treat dissent as disinformation’.
Emphasis on the ignorance of Black activists furthermore obscures the broader historical myopia upon which such constructions of Black ignorance are premised (see Mills, 2007). As Changa (2018) notes, ‘there’s nothing new about American institutions attacking and delegitimizing the work of Black activists and organizers’. While ‘the old Soviet Playbook’ and ‘Russia’s history in America’s race wars’ have supplied historical frames for popular reporting on Russian cyberwarfare, these frames ignore how association with foreign subversives has long been used to menace and intimidate Black Americans participating in political projects for recognition and redistribution (see Figure 3). Attending to this history, James Baldwin wrote in 1961 that ‘when the South has trouble with its Negroes . . . it blames “outside” agitators and “Northern interference.” When the nation has trouble with the Northern Negro, it blames the Kremlin’ (Baldwin, [1961] 1998: 181). Such was the case when in the 1960s Lyndon Johnson ordered the illegal surveillance of the Black Power and antiwar movements, premised upon his conviction that they were financed and fomented by the Soviet Union (Harris, 2005: 538). Similarly, and despite failure to uncover these connections, Richard Nixon expanded counterintelligence operations to attack activist movements and insinuate their foreign origins (Hersh, 1974; Jeffreys-Jones, 1989: 199; Weiner, 2007: 285). In this tradition, within a week of George Floyd’s murder by Minneapolis police, former US National Security Advisor Susan Rice appeared on CNN’s Situation Room to suggest that the resulting protests were ‘right out of the Russian playbook’ (Marrow, 2020).
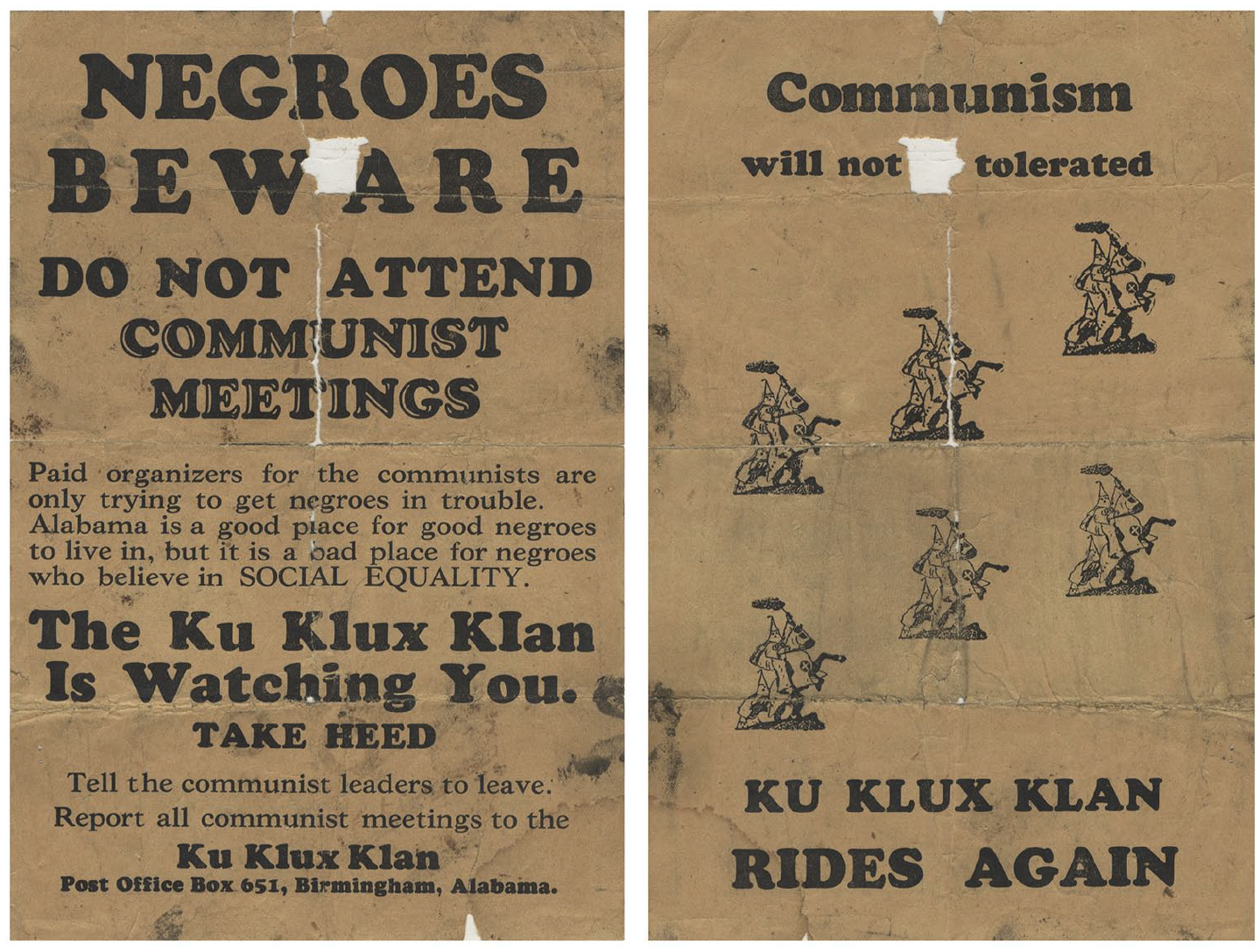
A 1930s Ku Klux Klan flyer threatens Black Americans participating in political projects for social equality, insinuating a connection to foreign ‘paid organizers’ (Alabama Department of Archives and History, c. 1930).
Under cover of digital esoterica, cybersecurity has produced a politics of truth in which forms of ignorance useful to the state not only are cultivated but also serve as a condition of possibility for designating dissident political movements as themselves ignorant, idiotic, or disinformed. ‘Useful ignorance’ of longstanding efforts to foreclose Black political projects in the name of national security is therefore central to the politics of truth coalescing within contemporary cybersecurity discourses. This politics of truth consists not in parsing true from false, but in the uneven circulation of knowledge and ignorance in proportions optimal to the conduct of statecraft. Cybersecurity thus attempts to draw boundaries around what is permissible through democratic politics, and for whom. The ‘normal politics’ against which exceptional cybersecurity circumstances arise therefore reveal themselves as highly racialized (Howell and Richter-Montpetit, 2020). While designating Others as ignorant or idiotic, cybersecurity’s politics of truth provide the United States, as James Baldwin ([1961] 1998: 180) observed, ‘yet another means of avoiding self-examination’.
Conclusion
Whereas cybersecurity once primarily concerned the protection of electronic networks, this article has traced the emergence of a new human-centric paradigm of cybersecurity and its relationship to the so-called post-truth era. In this paradigm, depoliticization has lost its subtextuality: as it admits, the Alliance for Securing Democracy explicitly seeks to ‘depoliticize efforts to counter foreign interference’ (Berzina et al., 2019). While cybersecurity actors thus position themselves as capable of providing technical solutions to political problems, cybersecurity’s ‘rhetoric of technique’ has in fact been underwritten by opaque and often highly racialized judgements concerning who must be made secure from whom. These judgements work to constrict and unevenly foreclose democratic possibilities in the name of defending democracy. However, such efforts are paradoxical on their own terms: ‘democracy’ is secured only through its uneven foreclosure, while ‘truth’ is subordinated to the maintenance of political order.
Closer scrutiny of efforts to ‘secure truth’ reveals that cybersecurity practitioners have been less concerned with parsing true from false, and more with managing the shape and possibility of contemporary political communication. More than supplanting ignorance with knowledge, practices of ‘securing truth’ in the United States have involved the circulation of knowledge and ignorance in proportions optimal to specific goals of statecraft. This has been achieved in part through an imaginative transposition of political dissent to the register of geopolitical contest. Collapsing domestic and foreign affairs into its politics of truth, cybersecurity has thus expanded its scope far beyond its traditional digital referents.
In placing responsibility for the ‘post-truth’ malaise on malicious foreign actors and racialized domestic communities, US political institutions elide accountability for their own role in the erosion of trust and confidence in government. Productive steps to address the crisis of democracy are readily available through direct means like voter enfranchisement and gerrymander reform, or indirectly through political projects of recognition and redistribution. Leaving deeper problems in place, contemporary cybersecurity tends only to assert authority where democracy is wanted. Scholars of cybersecurity should therefore remain critical of contemporary efforts to ‘secure truth’ and the political foreclosures they license.
Footnotes
Acknowledgements
I am grateful to Maja Zehfuss, Martin Coward, and Catriona Gold for their insight and generosity. I am also grateful to Emily Gilbert at Security Dialogue, as well as to three anonymous reviewers for their supportive reading and encouragement.
Funding
The author disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was made possible by a British Academy Newton International Postdoctoral Fellowship.
