Abstract
Drawing on rational choice and social learning theories, this study examines how social networks, subcultural immersion, and specific activities shape dark web actors’ perceptions of risks and rewards. Using original 2024 survey data from 123 active dark web users recruited across English- and Russian-language forums and Telegram channels, we analyze how peer involvement, sustained participation in deviant subcultures, and interest in particular illicit activities influence perceived risks of detection and perceived benefits. Findings suggest that larger peer networks and deeper subcultural immersion may lower perceived risks and heighten perceived rewards. We also find important activity differences: interest in malware correlates with lower perceived risks, ransomware with higher perceived risks, and selling illicit goods with particularly high perceived rewards. These results underscore the fluid, socially constructed nature of risk and reward perceptions in clandestine spaces, offering rare empirical insight into the subjective mechanisms underlying cybercriminal choices and informing targeted prevention strategies.
Introduction
In recent years, the dark web, part of the unindexed “deep web,” has emerged as a central hub for cybercriminals. It hosts a myriad of anonymous marketplaces and forums that foster the development of increasingly sophisticated forms of cybercrime (Kaur & Randhawa, 2020; Ngo et al., 2023), including the distribution of illicit materials and stolen data, creation of malicious software, human trafficking, and other offenses. Given the role of the dark web in facilitating cybercrime, understanding how individuals navigate and operate within these clandestine digital environments to engage in criminal activities is crucial for developing targeted strategies to combat them.
Whereas research seeking to unveil how cybercriminals operate has flourished in recent years (e.g., Leukfeldt & Holt, 2019; Weulen Kranenbarg et al., 2023; Woodhams et al., 2021), direct assessments based on self-reported data from individuals active on the dark web remain rare (Mirea et al., 2019; Partin, 2025). Likewise, the degree to which various factors influence how users interact with these systems and perceive the risks and rewards of cybercriminal activities remains insufficiently understood (cf. Ahmead et al., 2024; Bossler, 2021; Décary-Hétu et al., 2023; Hsieh et al., 2023; see also Holt & Lee, 2023).
This study advances the literature by (a) employing survey data collected from 123 active users of the dark web, and (b) analyzing how personal characteristics and behaviors, including peer involvement, subcultural immersion, and illicit activity preferences, influence dark web actors’ perceptions of cybercrime risks and rewards. By examining self-reported perceptions of crime risks and benefits and computer-mediated interactions within the anonymous environment of the dark web, this research provides rare insight into illicit online behavior that observational data may not capture.
Cybercrime on and off the Dark Web
Illicit surface and dark web forums and marketplaces have attracted considerable scholarly attention, with researchers advancing our understanding of the operational dynamics of these digital environments (Copeland et al., 2019; Décary-Hétu et al., 2023; Holt & Lee, 2023; Kloess & van der Bruggen, 2023; Laferrière & Décary-Hétu, 2023; Leclerc et al., 2021; Lee et al., 2022; Ouellet et al., 2022; Pete et al., 2020; Smirnova et al., 2024; Woodhams et al., 2021). While understanding the role of these platforms in facilitating and advancing criminal supply chains is crucial for developing effective interventions, gaining insight into the individuals who inhabit these spaces, including their characteristics, thoughts, and behaviors, is equally important.
Recent years have seen flourishing research examining the characteristics, behaviors, and motivations of those engaged in illicit online activities. This growing body of work has explored cybercriminals through multiple lenses, including personality traits (Weulen Kranenbarg et al., 2023), peer influences and co-offending patterns (Weulen Kranenbarg et al., 2019; Weulen Kranenbarg et al., 2022), the structure of criminal networks (Bekkers et al., 2024; Leukfeldt & Holt, 2019), the impact of life circumstances (Weulen Kranenbarg et al., 2021), motivations for dark web use (Woodhams et al., 2021), pathways into cybercrime (Loggen et al., 2024), and the range of offenses committed (Burruss et al., 2021; O'Malley & Holt, 2020).
Researchers have also examined offending trajectories (Hoffman et al., 2024; van der Bruggen & Blokland, 2021), attitudes toward cybercrime (Holt, Leukfeldt, & van de Weijer, 2020), reactions to law enforcement and policy interventions (Chopin & Décary-Hétu, 2023; Décary-Hétu et al., 2023), and risk management strategies among vendors selling illicit goods online (Laferrière & Décary-Hétu, 2023; Roddy & Holt, 2022). Much of this research draws on data scraped from forums, marketplaces, and archives of defaced websites. Complementing these approaches, studies using self-reported data have also proliferated, though they remain largely focused on student and general population samples. These studies often examine the role of theoretically significant predictors of cybercrime involvement (Burruss et al., 2021; Fox & Holt, 2021; Holt et al., 2021, 2024; Holt & Steinmetz, 2020; Hsieh et al., 2023; Kim et al., 2024; Louderback & Antonaccio, 2017; Partin, 2025; Weulen Kranenbarg et al., 2022).
A smaller but important body of work has employed surveys and qualitative interviews with known or suspected cybercriminals to shed light on their motives, behaviors, and networks. For example, Mirea et al. (2019) interviewed 17 dark web forum participants about the criminogenic nature of the dark web; Steinmetz (2014) conducted an ethnographic study of a hacker group to examine their backgrounds and demographics; Romagna and Leukfeldt (2024) explored the emergence and development of 21 hacktivist networks through interviews with 30 self-identified hacktivists; and Collier and coauthors (2021) interviewed 11 providers of “booter” services to investigate their work strategies. In turn, Weulen Kranenbarg (2022) surveyed traditional and cyber-offenders to compare co-offending patterns. While these studies offer valuable insights, they have not explicitly examined precursors to the decision-making processes of individuals who operate in illicit online environments.
This is not to say that cybercrime decision-making has been entirely overlooked. Scholars have examined how actors weigh risks and rewards and employ risk-avoidance strategies, using data from forum posts, vendor advertisements and activities (e.g., Décary-Hétu et al., 2023; Holt et al., 2023; Smirnova & Holt, 2024), as well as survey research with college student samples (Bossler, 2021; Partin, 2025). Yet these approaches have important limitations. College students and general-population respondents may not capture the lived experience of those embedded in the unique social, technical, and normative environment of the dark web. Likewise, observational data from forums and markets illuminate expressed attitudes and behaviors, but they cannot fully reveal how actors themselves perceive and evaluate the risks and rewards of their participation.
This study addresses a critical gap in research by examining the precursors to the decision-making of dark web users—a population distinct from typical cybercrime research samples. Active in clandestine, anonymized online spaces, these individuals operate under unique opportunities, constraints, and norms where behavioral modeling and peer reinforcement mechanisms fundamentally shape the perceptions of risks and rewards associated with cybercrime (e.g., Collier et al., 2021; Holt, 2010, 2019; Stalans & Donner, 2018). Interactions with experienced actors and exposure to subcultural narratives that normalize illicit activities socialize users into these communities, influencing their cost-benefit calculations (Akers, 1998; see also Holt et al., 2017). Understanding how dark web users perceive the risks and rewards of engaging in cybercrime is crucial to capturing offender choice processes in their real context. By eliciting self-reported data from this group, the study deepens understanding of the cognitive and situational factors shaping behavior in one of the most consequential domains of cybercrime—the dark web.
Deciding to Commit a (Cyber)crime
Rational Choice and Social Learning
Due to its premeditated nature and perceptibly low probability of detection, cybercrime is often regarded by scholars as a product of rational choice. Rational Choice Theory (RCT), originating from the works of Beccaria, 1764/1983) and Bentham (1789/1948), gained prominence with Becker’s (1968) argument that individuals weigh potential benefits and costs (sanction risks and severity) before deciding whether to engage in a particular behavior. In contemporary criminology, sanction risks primarily refer to the perceived certainty of formal (e.g., arrest) or informal (e.g., shaming by friends) punishment, although other risks associated with crime involvement, such as the risk of victimization by other crime actors (McCarthy & Hagan, 2005), are also considered. Crime costs are conceptualized as the anticipated severity of punitive outcomes or prospective systemic losses, while crime rewards can be multidimensional, spanning material (i.e., financial), psychological (e.g., emotional stimulation), and social (e.g., status-related) domains (Hoeben & Thomas, 2019; Thomas, 2024). Individuals are thus expected to engage in crime when the perceived rewards of criminal involvement outweigh their risks and costs.
The framework of rational choice has also been expanded to include a number of psychological, social, and contextual factors that may influence the choice process by calibrating the perceptions of risks, costs, and rewards associated with criminal activity. For instance, while personal experiences with crime and punishment matter for shaping personal perceptions of the sanctions and rewards associated with criminal behavior, so do the experiences of one’s peers (Stafford & Warr, 1993). On the one hand, this influence may be normative (Akers, 1998; Sutherland, 1947), as peers communicate information about the risks and rewards of criminal activities based on their own experiences. For example, an individual with no prior knowledge of credit card fraud may befriend a skilled carder 1 who boasts the illicit income they have earned while downplaying the likelihood of punishment. Through this interaction, the individual adopts definitions that frame carding as a high-gain/low-risk activity. These normative perceptions, reinforced by peer approval and success stories, serve as a basis for the positive reinforcement of involvement in carding (Akers, 1998). On the other hand, peer influence can also be situational, shaping opportunities for criminal involvement, such as enabling someone to join a group of professional hackers (Haynie & Osgood, 2005), and altering a person’s perceived balance of benefits and risks. This shift may result, for example, from the erosion of personal responsibility occurring when crimes are committed within a group (e.g., McGloin & Thomas, 2016).
Recent accounts of rational choice have extended these arguments to theorize about the effects of subcultural immersion on rational calculus, highlighting the importance of normative processes within the criminal group (e.g., circulating definitions conducive to crime and socializing with people who see crime as highly rewarding and less risky), as well as exposure to a large number of people who have successfully avoided punishment (Matsueda & Lanfear, 2020; Thomas, 2024), in shaping individual perceptions of risks and rewards associated with crime. It would be reasonable to expect, then, that dark web forums and markets could serve as subcultural settings that shape individual perceptions of such risks and rewards associated with cybercrime involvement. The networks formed on these platforms often allow those boasting high yields and low risks associated with their activities to be more visible and, thus, more influential in shaping the perceptions of other actors.
Social Learning and Subcultural Influences on Cybercrime
Recent empirical research substantiates the salience of social learning mechanisms and subcultural dynamics in cybercrime engagement (Holt, 2007; Miller & Morris, 2016; Stalans & Donner, 2018). For example, Holt et al. (2010) demonstrate the applicability of social learning theory’s core constructs (Akers, 1998) to cyber-deviance, finding that differential association with deviant peers and favorable definitional orientations toward cybercrime significantly predict offending among college students (see also Hutchings & Clayton, 2016). Complementing these findings, Dearden and Parti’s analysis of 1,109 online participants corroborates the predictive validity of social learning processes in cyber-offending trajectories (Dearden & Parti, 2021). Extending this theoretical framework to predict attitudes, Holt and colleagues (2017) document the influence of subcultural value systems on the motivational structures of ideological hackers (see also Holt, 2007), whereas Chua (2025) shows that differential association and differential reinforcement affect expressed extremist ideology among users of online forums. Furthermore, ethnographic and network analyses of hacker communities (Steinmetz, 2014) and dark web social structures (Décary-Hétu & Dupont, 2013) reveal organized collectives characterized by normative frameworks, status hierarchies, and systematic socialization processes that facilitate cybercrime involvement.
In sum, the convergent evidence from multiple methodological approaches establishes that participation in cybercrime, as well as the decision-making processes and perceptual factors underlying such involvement, may be fundamentally shaped by social learning dynamics and subcultural immersion rather than solely individual-level factors.
Current Study and Hypotheses Development
Drawing on rational choice theory and social learning perspective, we argue that individuals’ perceptions of risks and rewards in clandestine digital environments are shaped by peer involvement, immersion in the cybercriminal subculture, and specialization in specific forms of cybercrime. First, the behavior of peers plays an important role in such perceptual shifts. When individuals observe their peers successfully engage in cybercrimes, the rewards of such activities may seem more attainable, while the risks are likely to appear less pronounced (Stafford & Warr, 1993). This dynamic may be further reinforced when peers openly share their successes or provide guidance on mitigating risks. Moreover, the presence of cybercrime-active peers increases opportunities for collaboration in illegal ventures, such as establishing Malware-as-a-Service 2 operations or participating in organized hacking groups. These collaborative efforts may possibly not only enhance the perceived rewards by helping pool individual resources and expertise to be more productive, but also diffuse the sense of individual accountability, further diminishing the perceived risks associated with this crime (Matthews & Agnew, 2008). Taken together, these mechanisms lead us to expect that:
Greater peer involvement in cybercrime-related activities will be associated with lower perceived risks and larger perceived rewards related to cybercrime.
We also rely on the arguments of social learning theory (Akers, 1998; Sutherland, 1947) to argue that deep immersion into the dark web subculture may affect how actors perceive risks and benefits of the dark web. Personal or vicarious exposure to forums, marketplaces, and communities where illicit activities are glorified pushes a person to redefine acceptable behavior and re-gauge the costs and rewards associated with it. In addition, significant engagement in the dark web subculture may be also facilitated by acquiring more cybercrime-involved friends through the dark web communities. Within this environment, the premium is placed on seemingly unpunishable risk-taking activities, while success in cybercrime is celebrated. This creates a feedback loop that lowers perceived risks and emphasizes the benefits of being active in cybercrime, thus producing definitions conducive to involvement in these activities (Sutherland, 1947; Akers, 1998; see also Stafford & Warr, 1993). In this situation, exposure to dark web subcultures functions to lower perceived risks while amplifying perceived rewards.
Stronger immersion in dark web subcultures will be associated with lower perceived risks and higher perceived rewards of engaging in cybercrime.
Finally, we propose that another factor, specialization in dark web activities, likely recalibrates one’s perception of the risks and rewards associated with criminal behavior. It is reasonable to assume that, in many forms of cybercrime, individuals who have acquired the necessary skills and insider knowledge begin to perceive their activities less as risky ventures and more as professional challenges (e.g., Bada & Chua, 2024). The presence of like-minded peers in online communities can reinforce this perception, while observing personal or vicarious gains may further underscore the perceived rewards of such activities (e.g., Stafford & Warr, 1993). As a result, certain forms of cybercrime, such as carding or malware development, can come to be viewed as both rewarding and relatively low risk, which may normalize or even glamorize participation. For instance, a producer of some malware might see their work as low risk because their involvement is limited to writing malicious software leaving it to others to deploy it and infect targeted computers. Similarly, a carder could feel insulated from the risk of punishment by purchasing sensitive data from other parties and operating through intermediaries (e.g., the so-called “drops”). Finally, individuals with focused skill sets allowing them to engage in specific types of cybercrime may become more embedded in niche dark web networks that celebrate their successes causing them to overestimate their ability to control the risks associated with their activities. To summarize, we propose that:
Specialized interests in dark web activities, such as carding, malware development, illicit goods trading, hacking, or ransomware, will be associated with lower perceived risks and higher perceived rewards of cybercrime.
Overall, our study seeks to make several important contributions to the literature on decision-making and its precursors in the context of the dark web. First, it draws on recently collected unique self-reported survey data from 123 active users of the dark web, offering a rare and direct perspective on the subjective experiences and attitudes of individuals operating within these hidden online spaces. Such data provide valuable insight into how actors themselves perceive their actions and their consequences that are shaped by computer-mediated interactions. Second, the study sheds light on the sociocultural process that influences the precursors to cybercriminal decision-making by examining how peer behaviors, subcultural immersion, and specialization in dark web activities shape actors’ perceptions of risks and rewards. In particular, it investigates whether engagement with like-minded peers, sustained participation in deviant subcultures, and the development of specialized skills can normalize and even glamorize illicit online activities, while also reinforcing the sense of control over potential risks. Third, the study shows that risk and benefit perceptions in clandestine digital spaces are not static but are shaped and adjusted through social interactions in online environments and participation in specific digital subcultures.
Methods
Data
In this study, we draw on survey data collected in 2024 from a sample of 123 individuals, aged 18 and older, who were active on the dark web. The study protocol, including all recruitment and data collection procedures, was reviewed and approved by the first author’s Institutional Review Board (protocol #22-10-17, approved 06/02/2023). Respondents were recruited through a multi-platform strategy that included dark web forums, surface web forums dedicated to dark web discussions, and Telegram channels popular among dark web users. The platforms we approached varied in focus, including hacking, fraud, and general dark web discussion communities. At the outset, we contacted the administrators of 63 platforms, with 54 declining to respond, 4 responding to refuse participation, and 5 platforms granting permission to post recruitment messages. As part of these negotiations, we entered into a nondisclosure agreement with participating platform administrators to ensure that the identities of the platforms and their users would not be revealed. This agreement was an additional safeguard designed to protect participant privacy and prevent any inadvertent disclosure of sensitive community information. Platform inclusion criteria required active communities with regular posting activity related to hacking, digital fraud, and broader dark web activities (e.g. chatter about dark web forums and markets as communities), with English or Russian as primary languages, and public accessibility without special vetting requirements.
Recruitment was conducted in both English and Russian, with identical recruitment messages, consent screens, and survey instruments provided in each language. Initial translations of the recruitment messages, consent screen, and questionnaire from English into Russian were completed by linguists with the knowledge of both languages and cybersecurity terminology expertise, followed by back-translation conducted by independent translators to ensure accuracy. The final versions were pilot tested with native Russian speakers familiar with online community terminology.
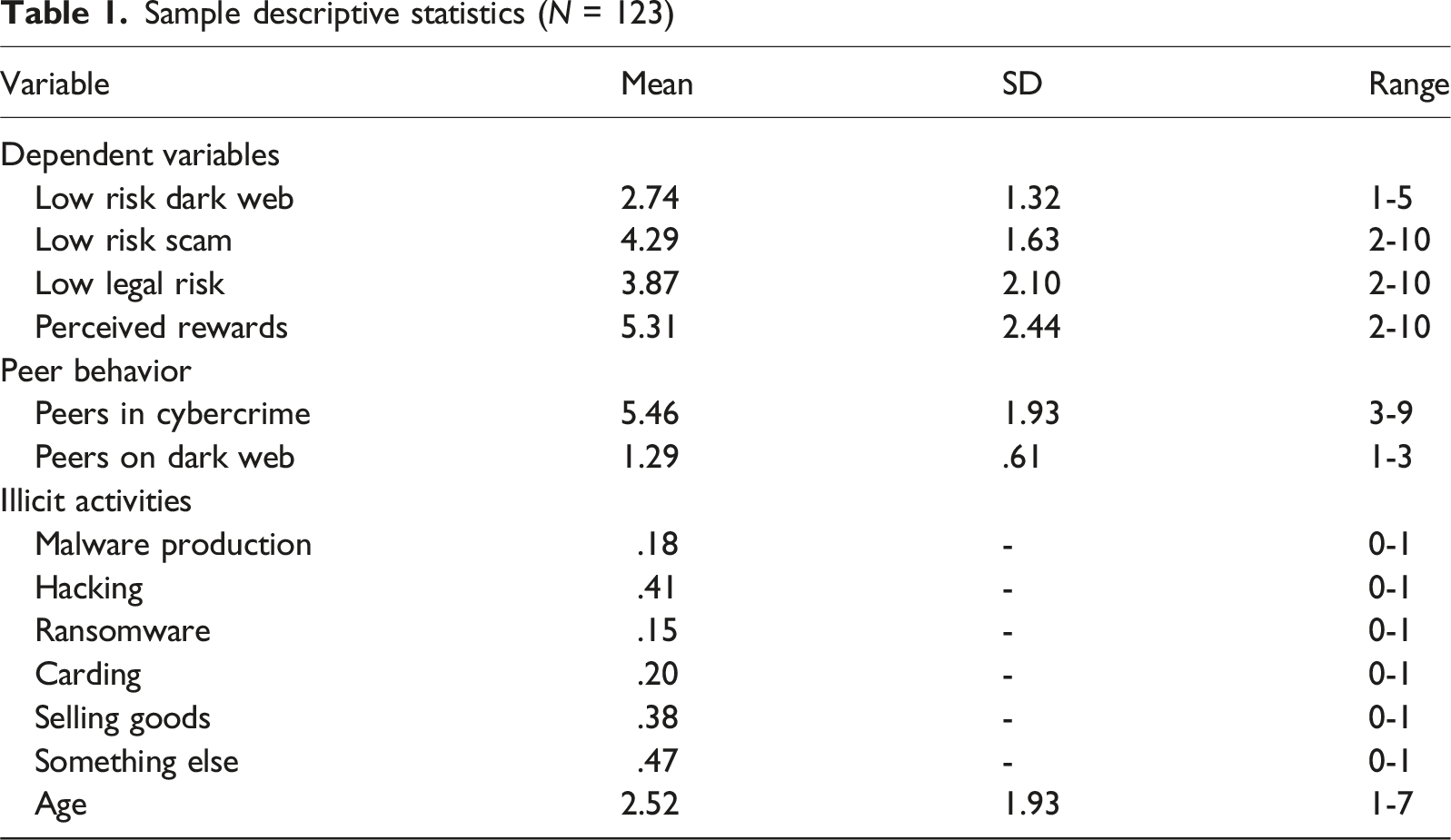
Sample descriptive statistics (N = 123)
In sum, our recruitment strategy enabled access to a diverse cross-section of individuals embedded in distinct dark web subcultures and activities and provided a rare empirical basis for examining how these actors perceive the risks and rewards of their activities.
Measures
Dependent Variables
Perceptions of Risks
In this study, we examine three types of risk perceptions: (a) personal perceptions of the safety of the dark web, (b) perceived risks of being scammed, and (c) perceived legal risks. While the items measuring scam and legal risks are not as broad as the question about the perceived safety of the dark web, they provide insight into the level of caution respondents exercise in precarious situations, helping us understand how risky they perceive dark web platforms to be in practice. 3
Risks of the Dark Web. The perceived safety of the dark web was operationalized with one survey item. Respondents were asked to indicate their level of agreement with the question “I feel safe engaging in online transactions on the dark web.” Response options ranged from 1 (“Strongly disagree”) to 5 (“Strongly agree”). Therefore, higher scores corresponded to lower perceived risks associated with the dark web. We recognize that quasi-continuous response formats (e.g., 0–10 scales) could have increased measurement sensitivity. However, we used concise Likert-type scales to reduce respondent burden in the dark-web environment and to maintain consistency with established criminological research on risk and reward perceptions (Antonaccio et al., 2011; Neissl et al., 2019; Tittle et al., 2010).
Risks of Scam. The perceived economic risks associated with dark web activities were tapped by the following two vignettes involving decision-making in economically risky situations: (1) “Let us talk about your experiences on the dark web marketplaces. It is your first time dealing with a seller who is selling something you badly need. There has been talk on the forum, however, that this seller is a likely scammer. How likely would you be to purchase from this seller if their goods are attractive to you?” and (2) “You have previously engaged in a transaction with a seller, and it went without a hitch. There has been talk on the forum, however, that this seller is a likely scammer. How likely would you be to purchase from the same seller if their goods are attractive to you?” The responses ranged from 1 (“Very unlikely”) to 5 (“Very likely”). We produced a summative scale comprised of the two items where higher scores indicated higher perceived safety (i.e., lower risks) associated with these activities.
Legal Risks. The perceived risks of legal sanctions associated with dark web activities were assessed through a vignette involving decision-making in legally risky situations: “There is a rumor that the administration of the (dark web) forum/market XYZ may now be cooperating with law enforcement.” Respondents were then asked to evaluate how likely they would be to: (a) create posts and (b) to buy or sell items on that forum. The responses ranged from 1 (“Very unlikely”) to (5) (“Very likely”). We produced a summative scale comprised of the two items where higher scores indicated higher perceived safety (i.e., lower risks) associated with these activities.
Perceived Rewards were assessed using two items that measured excitement and profitability of dark web activities. The first item asked respondents to indicate their agreement with the statement: “Illicit dark web activities are exciting to me.” The second item focused on profitability, stating: “I engage in some illicit dark web activities because they are profitable.” Responses were measured on a 5-point Likert scale, ranging from 1 (“Strongly disagree”) to 5 (“Strongly agree”). The items were then summed to produce a scale where higher scores indicated higher perceived rewards.
Independent Variables
Peer Cybercrime Involvement
To measure peer cybercrime involvement, respondents were asked “Think about your friends. In your opinion, how many of your friends have ever done one of the following?” Respondents were then presented with three peer behaviors: “Used computer software to access another person’s computer account or files,” “Sold or bought illicit goods online (data, software, etc.),”and “Did something else on a computer that is “against the rules.” For each of these three behaviors, respondents could select 1 “None,” 2 “A few,” and 3 “Many.” Responses were then summed into an index, with higher scores indicating higher levels of peer cybercrime involvement. The scale reliability coefficient for the index is .79.
Involvement in the Dark Web Subculture
Friends on the Dark Web: To gauge the extent to which the respondents’ peer networks involved friends gained through the dark web, the respondents were asked the following question: “How many of these friends did you first meet on the dark web?” Response options included 1 “None,” 2 “A few,” and 3 “Many.” Because those with a greater number of such friends are likely to spend more time communicating on the dark web, we consider this measure a way to assess respondents’ involvement in the dark web subculture.
Interesting Dark Web Activities: To gauge the types of behaviors respondents themselves engage in, respondents we asked, “Which activities on the Dark web do you personally find most interesting?” Framing the question around personal interests rather than activities allowed respondents to answer without a concern about self-implication. While this measure does not directly tap one’s personal involvement in specific activities, it is reasonable to assume that personal interests are a close match to the types of activities respondents engage in on the dark web. Response options included “malware production,” “hacking,” “ransomware,” “carding,” “selling goods,” or “something else.” While there is potential for some overlap between these categories—given the multifaceted nature of dark web activities—these options were designed to capture distinct and prominent behaviors commonly associated with the dark web engagement. This approach also allowed for a better understanding of the specific individual interests driving dark web interactions. Respondents could select as many activities as they wished. This item was then recoded into six binary variables (one for each behavior) where 0 indicated no interest in the dark web activity and 1 indicated interest in the dark web activity. We also experimented with a summative versatility scale but found it to have no statistically significant effects on any of our dependent variables.
Age
The respondents were also asked about their age with the option of placing themselves in the following age categories: 1. 18–19, 2. 20–24, 3. 25–29, 4. 30–34, 5. 35–39, 6. 40–44, and 7. over 45.
Analytic Strategy
To assess the direct effects of peer activities and personal interests related to the dark web activities on individual perceptions of their risks and benefits, we employed Ordinary Least Squares (OLS) regression. Before estimation, we examined the distribution of the dependent variables and found minimal skewness, eliminating the need for log transformation. To ensure the validity of the regression results, we also checked for multicollinearity among the independent variables. The Variance Inflation Factor (VIF) values for all predictors were below 2, indicating no significant multicollinearity concerns.
We addressed missing data using listwise deletion. Across the variables included in the models, missingness ranged from 0% to 4.88%. As a result, the final analytic samples varied from 114 to 119 cases across models. To assess whether missing data introduced bias, we conducted a series of t-tests comparing the means of included and excluded cases on all analysis variables for which complete data were available. These comparisons revealed no significant differences, suggesting that missing data patterns did not systematically bias the results.
Results
Table 1 shows descriptive statistics for the variables used in the analyses. Our sample is skewed toward younger respondents (cf. Holt & Kilger, 2008), with the average age ranging between 20 and 29. Participants also expressed interest in various dark web activities such as hacking (41%), selling goods (38%), carding (20%), malware production (18%), and ransomware (15%). Additionally, a significant number of respondents indicated interest in activities not explicitly listed in the response options, selecting “something else” to describe their interests on the dark web (47%).
Bivariate correlation matrix
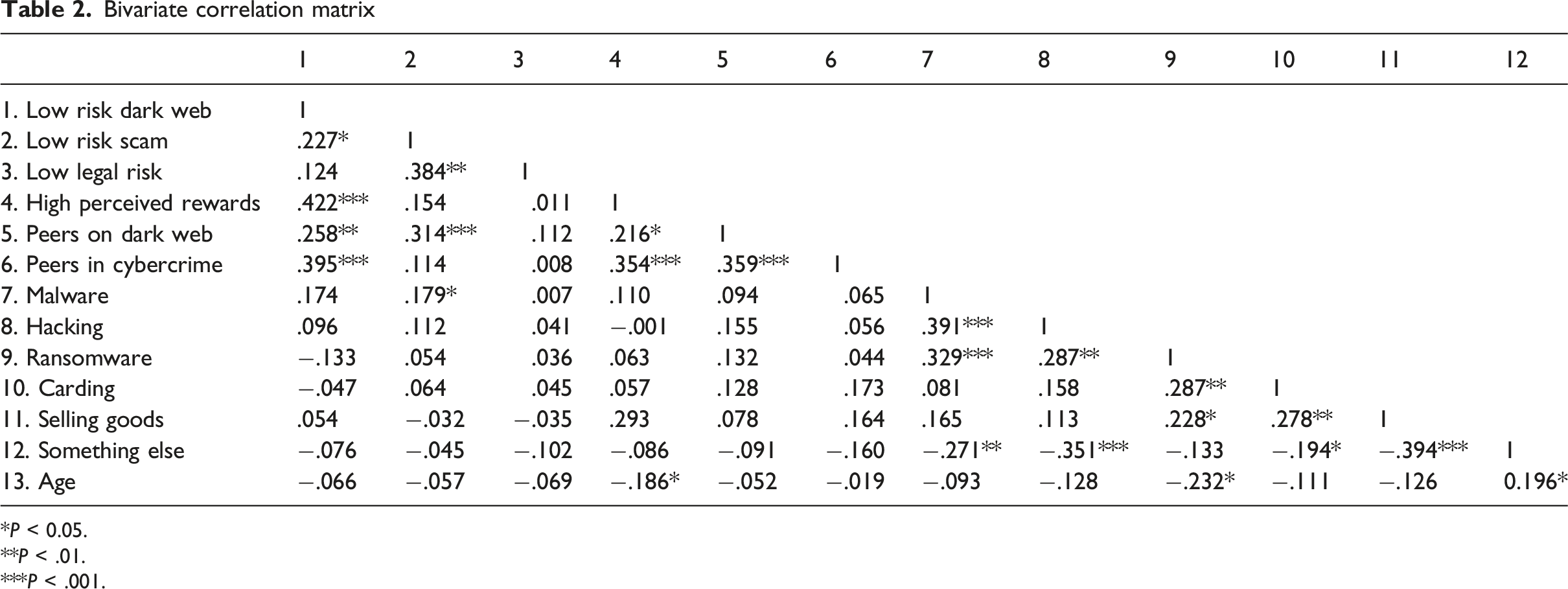
*P < 0.05.
**P < .01.
***P < .001.
OLS regression analyses of peer behavior and online activities on perceptions of risk and rewards associated with engaging in illicit online activities
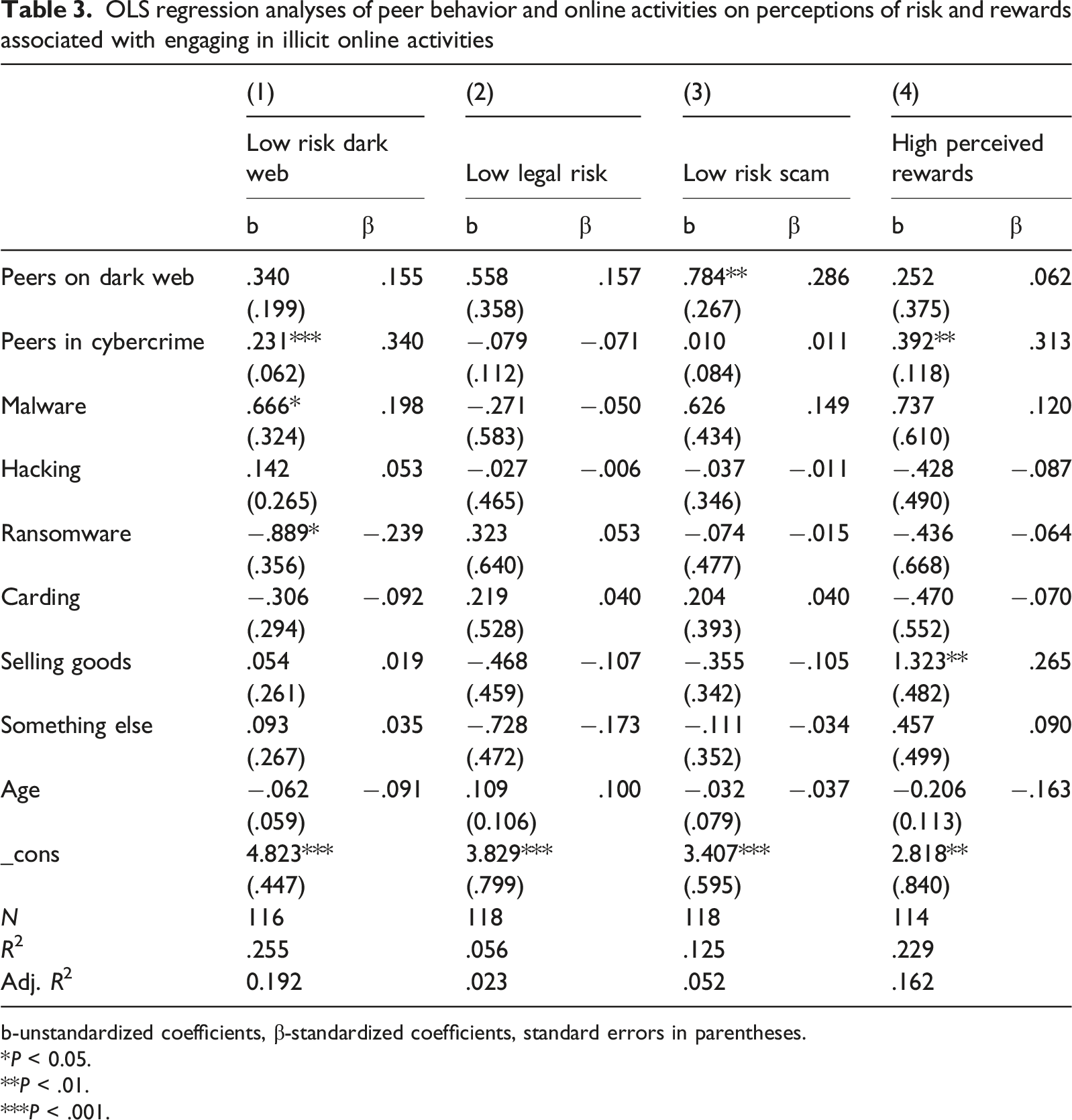
b-unstandardized coefficients, β-standardized coefficients, standard errors in parentheses.
*P < 0.05.
**P < .01.
***P < .001.
In contrast, figures from Model 1 reveal that individuals interested in ransomware-related activities may be less likely to perceive the dark web as safe. In particular, the unstandardized regression coefficient indicates that having such interest is associated with a .889-unit decrease in low risks on the dark web (b = −.889, p < .05). This runs counter to the expectations outlined in Hypothesis 3, which suggests the opposite direction of the relationship. Finally, standardized regression coefficients from Model 1 demonstrate that the predictor with the largest effect in this model is having peers engaged in illicit online activities (β = .340), followed by interest in ransomware-related activities (β = −.239). The graphic summative presentation of these findings is shown in Figure 1(A). Regression coefficient plots with 95% confidence intervals around four outcomes*. *Horizontal lines represent 95% confidence intervals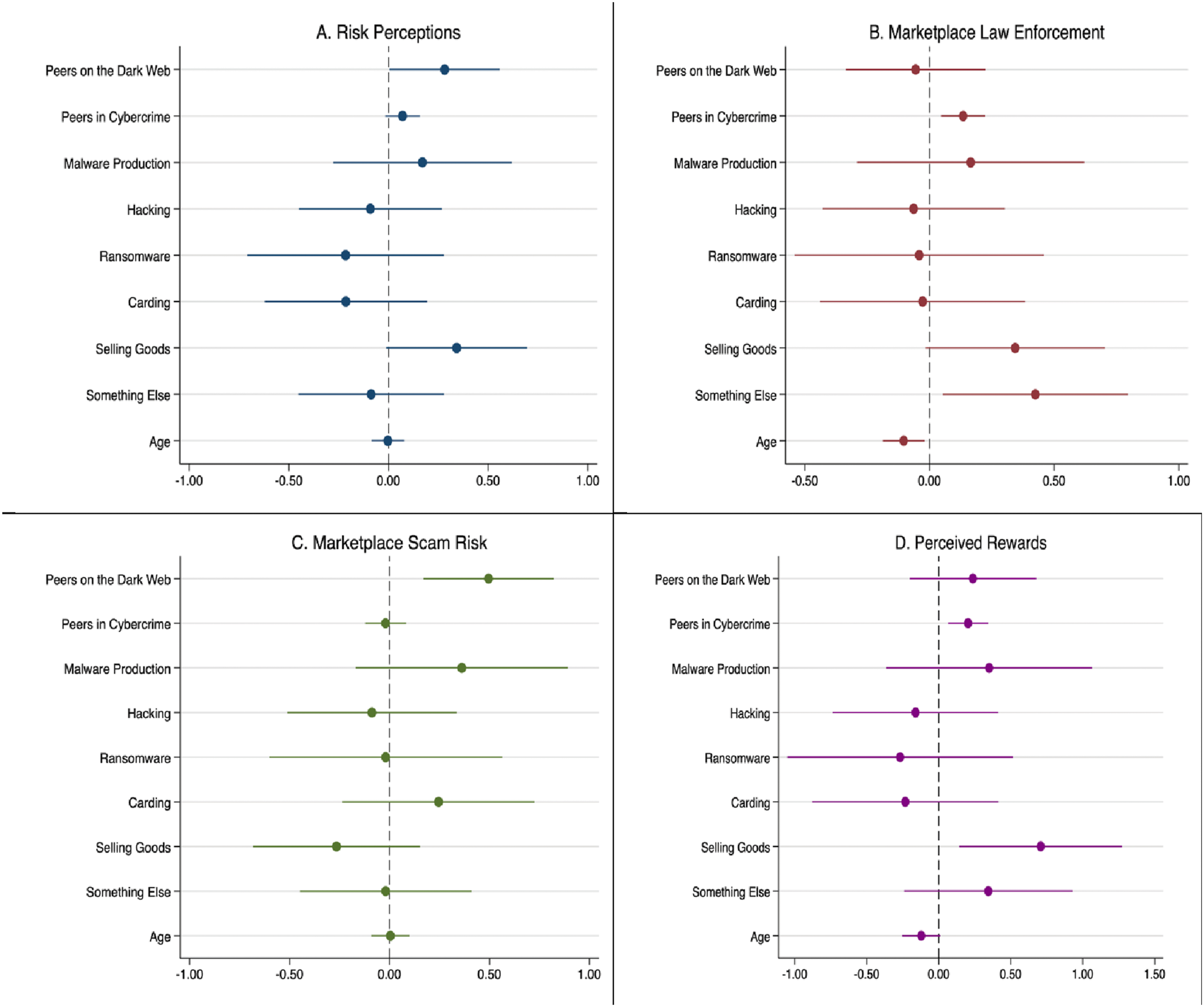
Further, Model 2 in Table 3 assesses whether the independent variables are statistically correlated with perceived legal risks. However, contrary to Hypotheses 1–3, none of the predictors included in this model are significantly associated with the outcome, as confirmed by Figure 1(B).
Next, Model 3 in Table 3 examines whether the independent variables are associated with perceived risks of being scammed. The findings from Model 3 show that the number of peers on the dark web is positively associated with perceived low risks of scam, suggesting that individuals with more friends on the dark web are less likely to perceive the risks of scam as high. In particular, the unstandardized regression coefficient indicates that a one-unit increase in friends on the dark web is associated with a .784-unit increase in low risks of being scammed (b = .784, P < .05).
This finding provides some support for Hypothesis 2. Yet, contrary to Hypotheses 1 and 3, no other predictors reach statistical significance in this model. Overall, the standardized regression coefficient confirms that having peers on the dark web is the predictor with the largest effect in the model (β = .286). The graphic summative presentation of these findings is shown in Figure 1(C).
Finally, Model 4 in Table 3 assesses whether the independent variables are statistically associated with perceived rewards of the dark web activities. Figures from Model 4 reveal that individuals who have more friends engaged in cybercrime are expected to perceive more rewards of the dark web activities. In particular, the unstandardized regression coefficient indicates that a one-unit increase in peers engaged in cybercrime is associated with a .392-unit increase in perceived rewards of the dark web activities (b = .392, P < .01), which provides some support for Hypothesis 1. Further, estimates from Model 4 demonstrate that individuals interested in selling goods may be more likely to perceive higher rewards of the dark web activities. Specifically, the unstandardized regression coefficient indicates that having such interest is associated with a 1.323-unit increase in perceived rewards of the dark web activities (b = 1.323, P < .01). This finding partially supports Hypothesis 3, suggesting that specialized activity interests may heighten perceived rewards. Furthermore, standardized regression coefficients from Model 4 demonstrate that the predictor with the largest effect in this model is having peers engaged in cybercrime (β = .313), followed by interest in selling goods (β = .265). The graphic summative presentation of these findings is shown in Figure 1(D).
Finally, adjusted R2 values for Models 1–4 shown in Table 3 indicate that Model 1 has the largest explanatory power, with the predictors under consideration accounting for 19.2% of the variation in the outcome, perceived low risks of the dark web. It is followed by Model 4, in which the same predictors explain 16.2% of the variation in the dependent variable, perceived rewards.
Sensitivity Analyses
OLS regression analyses of peer behavior and online activities on perceptions of material and psychic rewards associated with engaging in illicit online activities
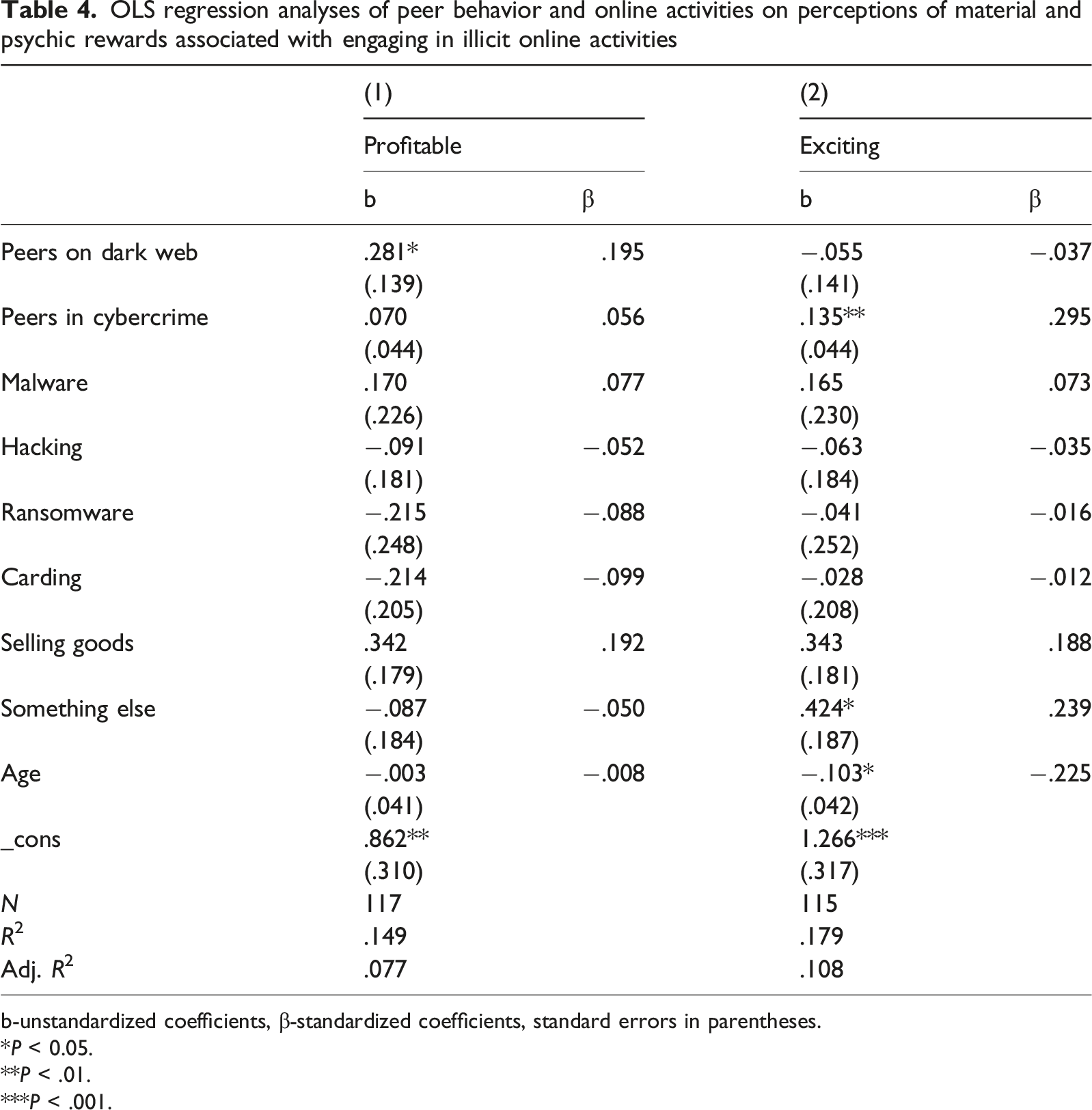
b-unstandardized coefficients, β-standardized coefficients, standard errors in parentheses.
*P < 0.05.
**P < .01.
***P < .001.
Discussion
Our study sought to understand how various factors associated with the social circles and specific activities of dark web actors affect the precursors to offender choices by shaping perceptions of the risks and rewards associated with dark web activities. The unique technological characteristics of dark web platforms, including anonymity tools, encrypted communications, and specialized interfaces, create distinct conditions that fundamentally shape how users form social networks, assess risks, and make decisions within these digital environments. We proposed that having friends on the dark web and a larger number of friends involved in cybercrime would be associated with higher perceived rewards and lower perceived risks related to cybercrime on the dark web. We also expected that those involved in specific cybercrime activities would similarly gauge the risks and rewards of cybercrime. We found mixed support for our hypotheses.
On one hand, we found that peer involvement in cybercrime tended to lower perceived risks of being active on the dark web—this finding aligns with Hypothesis 1. Several explanations, consistent with social learning perspective, may account for this. First, learning about cybercrime from peers engaged in illicit activities can foster a false sense of security, particularly among less experienced users, making the dark web appear safer than it is. Second, deeper integration into cybercrime communities may enhance users’ technological expertise and increase their participation in complex virtual networks that cultivate trust among participants (Aldridge & Décary-Hétu, 2015; Décary-Hétu & Laferrière, 2015). This trust, in turn, reinforces perceptions of safety. At the same time, our findings suggest that perceptions of specific risks, such as being scammed or facing legal consequences, remain unaffected by peers’ cybercrime involvement, which does not support the broad expectations of Hypothesis 1. It is possible that these activity-specific risk perceptions may stem more from direct, personal experience than from vicarious learning (Stafford & Warr, 1993; see also Collier et al., 2019).
In addition, providing support for Hypothesis 1, friends’ involvement in cybercrime led users in our study to view dark web activities as more rewarding (specifically, exciting). These findings align with prior research showing that peers and criminal subcultures can shape decision-making and reinforce illicit activity (Hoeben & Thomas, 2019; Neissl et al., 2019). Peer experiences likely facilitate information sharing about illicit opportunities (Holt, Bossler, & May, 2012; cf., Holt et al., 2021), build trust in online networks (Lusthaus, 2012), enhance technical confidence, and normalize extremist behaviors (e.g., Chua, 2025)—all of which contribute to lowering perceived risks and heightening perceived rewards.
On the other hand, having a larger number of peers on the dark web, the second factor we hypothesized to be associated with personal involvement in the dark web subculture, was associated with lower perceived risks of being scammed. This result is aligned with Hypothesis 2, and it may be because greater peer presence fosters deeper immersion in the illicit subculture and associated cybercriminal networks, giving users more experience with its norms and practices and, in turn, reducing their perceived vulnerability to scams. It should be noted that there may be no real “safety in numbers,” and the perceived invulnerability to scams among these users may be illusory. However, having more peers engaged in similar illicit activities likely reassures actors that they can also succeed without being defrauded (McCuddy & Vogel, 2015; see also Brinck et al., 2023).
Another factor we hypothesized to be linked with involvement in the dark web subculture, focus on specific activities on the dark web, was found to be associated with the precursors to offender decision-making for only three kinds of the dark web activities. First, as expected, we found that malware interests were associated with lower perceived risks of the dark web, the result aligned with Hypothesis 3. This may indicate that individuals interested in malware possess higher technical expertise, treating the dark web as their regular “work environment.” Moreover, those involved in creating and distributing malware typically have advanced skills that help minimize their chances of detection. Alternatively, even minimal knowledge of malware production or use may give dark web users a false sense of invulnerability, making them feel immune to risks (e.g., Jacobs, 2010). Finally, because law enforcement efforts often focus on high-profile financial crimes and large-scale cyberattacks, many smaller-scale malware actors may believe they are unlikely to be actively targeted.
Contrary to our expectations, we found that interests in ransomware were associated with higher perceived risks associated with the dark web. This finding is contrary to Hypothesis 3, and it may indicate that those distributing ransomware on the dark web are more likely to interact directly with victims and, as a result, may be more easily detected and draw the attention of law enforcement. Furthermore, ransomware actors may be generally more aware of the increased attention of law enforcement to ransomware attacks (Meurs et al., 2025). Although ransomware actors tend to operate in large networks that provide resources for laundering illicit proceeds and evading detection (Whelan et al., 2024), these arrangements do not appear to fully erase a concern about the risks of detection.
Yet another notable finding providing some support for Hypothesis 3 is that selling goods on the dark web may heighten the perceived rewards of dark web activities. This finding could be due to the immediacy of the often-significant profits associated with selling illicit goods (e.g., inauthentic documents, drugs, or weapons), with instant gratification positively reinforcing this behavior, particularly among those with low self-control (e.g., Holt, Bossler, & May, 2012) and thus heightening its perceived attractiveness.
Our findings have important implications for cybercrime prevention, underscoring the influence of peer networks, subcultural immersion, and specific activities and experiences on the processes pertinent to decision-making in the dark web environment. In particular, the observation that peer networks and specific illicit activities reduce perceived risks and increase perceived rewards supports the idea that clandestine digital platforms function as “offender convergence settings” (Felson, 2003), fostering trust, information sharing, and social reinforcement (Garkava et al., 2024). Therefore, interventions that disrupt peer reinforcement mechanisms should be a priority for prevention efforts. An example of such interventions is the publicizing of arrests and prosecutions, which can weaken peer ties and erode the illusion of safety.
The results also highlight the value of tailoring interventions to activity profiles. For malware actors, whose technical expertise lowers perceived risks, strategies that inject doubt, such as disinformation about vulnerabilities and detection, may raise risk perceptions. For ransomware actors, who already recognize elevated risks, visible enforcement actions, including arrests, prosecutions, and asset seizures, can strengthen deterrence. For illicit sellers, who perceive high rewards, interventions that destabilize profits through artificial volatility, fake transactions, and supply disruptions can reduce the gratification that sustains engagement. More broadly, warning banners from internet service providers (Holt & Lee, 2023) that emphasize the risks of engaging on dark web platforms could discourage novices.
Market-oriented measures can complement these targeted strategies. Strategic “lemonizing” (Holt et al., 2016; Howell et al., 2022), which infiltrates marketplaces with controlled accounts and deceptive reviews, can undermine trust in market mechanisms. By degrading reliability and profitability, such tactics exploit market dynamics to raise the perceived costs of illicit activity (e.g., Collier et al., 2021; Lusthaus, 2018).
While our study offers valuable insights into the motivations and choices of dark web actors, several limitations merit consideration. Although our sample is larger than in many prior studies based on self-report data from cyber-offenders, it remains modest and drawn from five platforms, which limits generalizability to the wider population of dark web forum users. Representativeness is further constrained by our inability to assess nonresponse bias, since we could not compare participants with those who viewed but did not respond to recruitment, nor determine whether users of responding platforms differ from those of nonresponding ones.
Our recruitment strategy, consistent with comparable studies (e.g., Collier et al., 2021), did not specifically target known cyber-offenders and did not distinguish between highly active and more sporadic participants. Users from groups whose administrators permitted recruitment may have been less involved in serious crime, potentially biasing the sample toward lower-level offenders. The brief survey format may also have attracted casual users, while more embedded actors may have been less willing to participate.
The study was additionally constrained by language and platform restrictions. Recruitment limited to English- and Russian-speaking forums and Telegram channels where posting was permitted means our findings may not capture perspectives from other linguistic, cultural, or more exclusive networks. Finally, as with all self-report surveys, responses may reflect withholding, exaggeration, or social desirability bias despite efforts to design non-implicating questions.
In conclusion, our study shows that reported perceptions of risks and rewards on the dark web may be shaped by a combination of peer dynamics, subcultural immersion, and, to some extent, activity-specific experiences. Peer involvement in cybercrime was associated with lower perceived risks and heightened perceived rewards, while the presence of more peers on the dark web was associated with reduced perceived vulnerability to scams. Specialized activities were associated with differentiated effects, with malware interests linked to lower perceived risks, ransomware interests linked to heightened perceived risks, and illicit selling interests linked to increased perceived rewards. Together, these findings illustrate that offender decision-making on the dark web likely reflects an interplay of social learning processes, rational choice considerations, and the unique effects of technologically mediated environments. Understanding how these factors jointly shape risk–reward perceptions can inform more targeted and effective cybercrime prevention strategies. Future research would benefit from larger, more targeted samples, greater linguistic and cultural diversity, and mixed designs that combine nuanced questioning with qualitative approaches—as well as methods that move beyond self-reported perceptions to capture verified behavioral outcomes—to reduce bias and capture richer detail about actors’ roles, activities, and stated perceptions of risk and reward.
Footnotes
Funding
The authors disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: this research was supported by DHS/CINA under the award #E205949B. 4 The content is solely the responsibility of the authors and does not necessarily represent the official views of the DHS/CINA.
Declaration of conflicting interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Data Availability Statement
The authors do not have sponsors’ permission to share data.
