Abstract
Recent democratic backsliding in Eastern Europe challenges the optimism of two decades of scholarship on post-communist democratization. The most severe form of backsliding—state capture by ruling parties—has occurred in countries formerly regarded as paradigms of successful democratic transition. Despite research on different kinds of capture, little is known about the overall process by which political parties capture a state. In response, we develop a conceptual framework that identifies four interconnected strategies and corresponding tactics: (1) exploiting crises to advance political agendas, (2) deactivating controls to constrain oversight, (3) milking cash-cows to generate income, and (4) manipulating the political system to institutionalize rents. To demonstrate the analytical value of the framework, we compare how Fidesz in Hungary and VMRO-DPMNE in North Macedonia achieved a state of capture. Notwithstanding contextual differences, the analysis shows that the political parties of interest employed the same set of strategies.
How do political parties capture newly democratic states? Explorations into democratic subversion and state capture have been dominated by queries into their causes and consequences. Despite extensive research, scholars have paid little attention to the processes of democratic subversion that result in state capture. This gap limits scholarly knowledge of state capture—understood as a situation in which a group of actors gain control over a significant number of state bodies, procedures, and policies with the intent to subvert their effectiveness for the group’s benefit. Empirical work on state capture originated in the late 1990s from the World Bank Institute, where a group of economists described state capture as a phenomenon in transition economies in which firms influenced the “rules of the game” through illicit payments to public officials. 1 The term has undergone a conceptual transformation over the years and morphed to include the capture of any state institution by any political or economic group, including parties, incumbents, and bureaucrats. 2 Some scholars also view state capture as one form of corruption and/or distinguish between various types of capture (e.g., corporate, party, or regulatory capture), which further muddles our understanding of state capture.
Due to these different approaches, the literature on state capture has become atomized into different disciplines. For example, individual studies have focused their attention on economic capture by firms, institutional defects that lead to capture, capture as a result of political patronage and bribes, public procurement corruption, or on various configurations of political party competition. 3 While it is clear that state capture involves collusion between political and economic actors, we know far less about how these pieces fit together as a whole and enable ruling parties to halt democratization processes and make a U-turn toward authoritarianism. In other words, we lack a systematic understanding of the causal pathway by which political parties capture their states.
To fill this gap, we develop a conceptual framework that merges findings from the comparative democratization literature with insights from electoral behavior, economic and political capture, and public crisis management. A necessary first step toward formulating a comprehensive theory of state capture is to devise a framework that encompasses political parties’ repertoire of actions. Although it is tempting to first research the explanatory factors that lead parties to engage in capture, we turn the problem around and work backward. Put differently, our paper addresses the question of
Our conceptual framework, illustrated in Figure 1, proffers that political parties achieve state capture by employing four interconnected strategies: (1) exploiting national crises, (2) deactivating controls, (3) milking cash-cows, that is, acquiring public resources and converting them into assets for the party, and (4) using legislative majorities to reshape the political institutions to their benefit. Each strategy, pursued through various tactics, provides the capturing party with unique benefits that facilitate the use of the other strategies. The strategies do not follow a particular sequence and the numbering is for organizational purposes. The illustrative cases demonstrate that the strategies complement one another and may be deployed simultaneously. Moreover, the deployment of each strategy and the degree to which a captor accrues the associated benefits depend on the political context and the captor’s resources. Indeed, any major party may employ the first three strategies, whereas strategy four requires the captor party to have a legislative majority. 4 Parties must successfully deploy all four strategies to achieve state capture.
Conceptual framework
We elucidate how the framework advances scholarly knowledge by outlining how Fidesz in Hungary and VMRO-DPMNE 5 in North Macedonia employed these strategies. The two countries stand out as paradigmatic examples. Both countries were in the top tier of post-communist democracies within their respective regions of Central and Eastern Europe and the Western Balkans in the mid-2000s. Yet Hungary and North Macedonia underwent a democratic backlash so severe that by the mid-2010s, they were described as captured states. Their political contexts, however, including the parties’ trigger points and ultimate outcomes, differ significantly. Our framework therefore addresses recent appeals for a better understanding of democratic subversion. 6 Further testing of the framework can provide scholars and policy practitioners with empirically founded insights on the strategies capturing parties employ and how to counter such attempts.
In the next section, we explain the four strategies that comprise our framework. We then describe the two illustrative cases and our empirical approach. In the fourth section, we sketch out how Fidesz and VMRO-DPMNE implemented the four strategies to achieve state capture. We conclude with a discussion of how the framework helps to identify attempts at state capture and how the four strategies work together.
Achieving State Capture: Conceptual Framework
We assume that political parties seek policies, votes, and office. Second, leaders of captor parties desire to capture democratic states and are willing to use a by-any-means-possible approach. Thus, they share behavioral traits with autocratic rulers as well as traits studied in the comparative democratization, electoral behavior, state capture, and public crisis management literatures. 7 Third, the capacity to implement any of the four strategies is contingent on captor parties having sufficient organizational and financial resources to carry out the individual tactics within each strategy. Developing a conceptual framework that captures such a diverse set of behaviors is akin to solving a jigsaw puzzle with its pieces missorted into multiple boxes. By sorting through these “literature-boxes,” four state capture strategies emerge (shown in Table 1), each with their own target group, tactics, and direct benefits.
The Four State Capture Strategies with their Associated Tactics and Direct Benefits
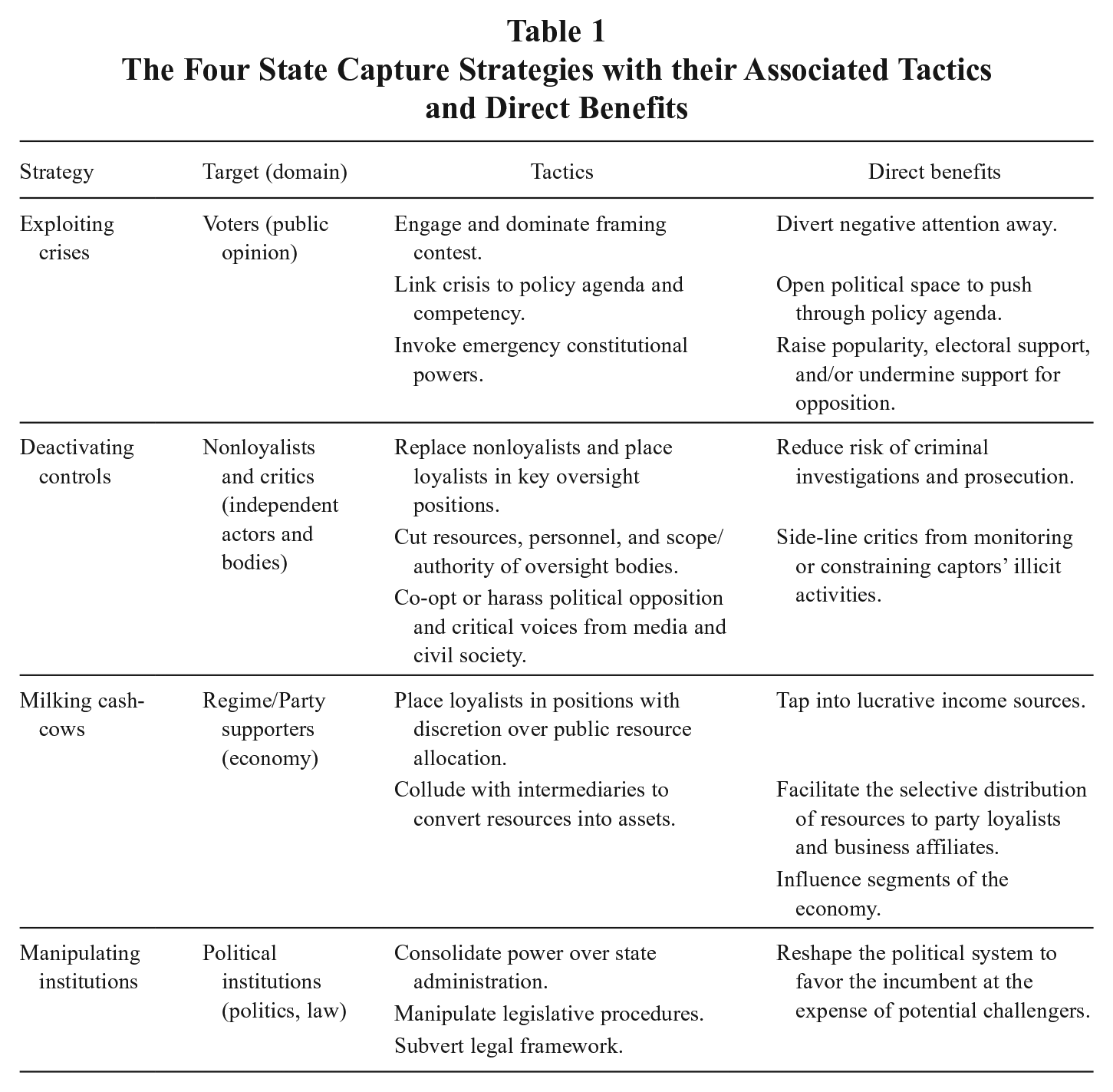
Together, the four strategies form the causal pathway through which political parties achieve state capture. Each strategy, if successfully implemented, enables captors to accrue specific benefits that facilitate their broader quest to exploit vital institutions, as well as the deployment of other strategies. While strategies are long-term oriented and not necessarily sequential, tactics refer to the operational actions of captors to implement a strategy. Within our discussion of each strategy, we note the sequencing of specific tactics and whether a tactic is formal or informal. While any major political party may implement the four strategies, the degree to which it accrues the associated benefits and the specific tactics it can deploy depend on the political context, the captor’s resources, and the behavior of other actors. 8
Strategy 1: Exploiting Crises
National crises simultaneously present challenges and opportunities for political parties. Challenges arise because policymakers deal with complex issues under conditions of uncertainty and urgency. However, such conditions also create opportunities for captors to exploit crises to their advantage, 9 which is defined as “the purposeful utilization of crisis-type rhetoric to significantly alter levels of political support for public office-holders and public policies.” 10 Thus, crisis exploitation targets voters and functions within the domain of public opinion.
Crisis exploitation benefits captors by concealing inconvenient truths from the public (e.g., introducing unpopular reforms or dealing with corruption allegations) and diverting attention toward other issues. If successful, the strategy enables captors to push through policies and mobilize voter support, while undermining political competitors. For instance, by framing a crisis as a threat to national values, incumbents can co-opt the opposition and silence potential critics. Conversely, opposition parties can exploit a crisis to undermine an incumbent’s legitimacy and credibility among voters. Since crises are largely perception-based, the potential of reaping these benefits may even embolden captors to manufacture a crisis, even if none exists in the public’s mind. 11
To successfully implement the strategy, captors need to employ two tactics sequentially. The first tactic is informal and rhetorical, centering on dominating the framing contest. For this, the captor proclaims a national crisis, citing concerns related to national security, the economy, public health, or a natural disaster, to name a few. Whether the crisis objectively exists, is exaggerated, or entirely manufactured is not of theoretical concern. What matters is that the captor dominates public discourse around the crisis—its origins and how to deal with it. Dominating the framing contest forces other actors to address the event as a crisis, regardless of their own assessments. Next, the captor employs the second tactic, linking the management of the crisis to the party’s policy agenda. This tactic aids the party to push through its preferred legislation and policies. 12
Incumbents may also exploit crises to invoke formal, emergency constitutional powers to their advantage. These emergency provisions often temporarily suspend individual rights and expand executive power, and they have been associated with coups, electoral interruptions, and the suppression of minority and opposition groups. 13 Take, for instance, President Trump’s rhetoric on the recent immigration crisis. Appealing to voters on the basis of national security, he forced Democrats to engage in negotiations over a border wall with Mexico, which led to a government shutdown and a national state of emergency. 14 In sum, crisis exploitation assists captors to concentrate power by increasing their public support, which then assists captors to pursue their policy agenda. This agenda centers on formal rules that expand executive authority and limit competition, thus opening up space to pursue the remaining strategies.
Strategy 2: Deactivating Controls
The second strategy involves the captor’s efforts to incapacitate key oversight bodies and critical voices, which undermines their ability to act as watchdogs. 15 The domain corresponds to independent actors, organizations, or mechanisms that constrain the party’s efforts to capture the state. Within a political party, likely targets of the party’s leadership are factions or individuals that threaten leadership control. Other targets are oversight bodies and mechanisms operating within the political system, such as the judiciary, legislative positions and committees with agenda-setting powers, anti-corruption agencies, and law enforcement. The final target group exists outside the formal political system, including the media, civil society, academia, and private businesses. This strategy provides two benefits to the capturing party. First, it reduces the risk of criminal investigations and prosecutions of loyalists. Second, the strategy eventually forces political rivals, the media, and civil society to practice self-censorship. By deactivating these watchdogs, the capturing party delegitimizes independent, critical voices and neutralizes their ability to constrain the captors. Extensive financial and political resources provide captor parties with leverage that increase their chances to successfully implement the strategy.
Deactivating controls involves a combination of formal and informal tactics. One informal tactic is to use party patronage to purge nonloyalists from public positions tasked with political oversight and replace them with loyalists. 16 The tactic also allows captors to target controls outside the political system. For example, a party undermines critical media coverage when it encourages party-friendly businesses to buy up media outlets or establish new ones. 17 A complementary tactic uses formal channels to deactivate controls, such as cutting an oversight body’s budget or manipulating its scope of authority. Finally, a third set of tactics concentrates on intimidating and co-opting political rivals and other critics. As incumbents, captors may systematically harass rivals through legal means, for example, barring the opposition from competing in elections for obscure legal reasons or passing legislation that reduces state subsidies. Harassment can even escalate to arresting critical public figures and discrediting civil society organizations. 18 The symbiotic nature of the four strategies is again apparent as deactivating controls enables the party to pursue the other strategies without resistance.
Strategy 3: Milking Cash-Cows
Cash-cows are positions under the purview of the public administration with discretion over the distribution of public resources. We follow existing conceptualizations of cash-cows as “points [in the public administration] from which the system is milked.” 19 To milk cash-cows, the capturing party needs to have access to public resource distribution before colluding with intermediaries, who then convert the acquired resources into cash or other material assets. Such intermediaries, generally lawyers or consultants, are industry-insiders with the know-how to circumvent legal procedures and set up complex corruption schemes that divert resources to the captors. Naturally, success of the strategy depends heavily on the expertise of these intermediaries.
Milking cash-cows falls within the economic domain as it enables captors to tap into lucrative sources of income and finance their other activities. Certain cash-cows also boost the party’s ability to influence segments of the economy. Consider, for example, the sale of natural resources: The captor can use its control over natural resources to allocate contracts to business allies, ensuring that they too benefit. On a smaller scale, the captor also influences the economy by relying on selected intermediaries to convert the acquired public resources into usable assets. These intermediaries have an unfair market advantage as they profit from opportunities closed to other market-actors. The cash-cow strategy, therefore, benefits both sides since milking cash-cows generates income, strengthens their relationship, and allows them to expand their influence. 20 The party can also use the additional income to reward its supporters.
Milking a cash-cow involves three sequential tactics that are informal or quasi-legal. The captor first employs party patronage to gain control over positions with discretionary powers to distribute public resources. Common targets are high-level officials in public procurement agencies and in state-owned or partially state-owned companies. Once the captor gains control over public resource distribution, it switches to the second tactic. Captors now collude with an intermediary, who covertly converts the acquired public resources into usable income. Public domains at high risk are, among others, the public procurement process, the distribution of public funds, and the sale of public assets. 21 Incumbent captors can employ a third tactic—renationalizing profitable businesses or even entire sectors to create new cash-cows to milk. Again, the strategy complements the other strategies as it provides the captor with necessary capital.
Strategy 4: Manipulating Political Institutions
The final strategy targets formal political institutions. Unlike the previous strategies, to successfully implement the strategy, the captor needs to have a legislative majority and/or control the executive branch. The main benefit of the strategy is the outcome itself: a system of rules, laws, and procedures that favor the captor while constraining potential challengers. 22 Moreover, the party institutionalizes its advantages, thus deriving benefits after leaving office. 23
Prior scholarship on democracies and authoritarian regimes describes numerous tactics available to captors. 24 The first group of tactics endeavors to consolidate power within the state administration and has a broader scope than the second and third strategies. 25 Examples include revising appointment procedures, creating new oversight bodies while sidelining others, and centralizing control over the administration, including the judiciary. The second group of tactics centers on manipulating legislative procedures, such as modifying majority requirements to pass bills or appoint public office holders. The incumbent can also modify agenda-setting rules, thus controlling which bills reach the floor and which are kept out of discussion. Manipulating agenda-setting rules compromises the opposition’s ability to check or delay bills, let alone introduce any. 26
The third group of tactics concentrates on subverting the legal framework, including tampering with the constitution and the electoral system. Incumbents may introduce policies that fragment the opposition, thwarting their attempts to coordinate and challenge the incumbent. 27 Other tactics include manipulating campaign finance laws, political parties’ or voter registration requirements, electoral threshold requirements, and electoral redistricting. 28
On their own, none of these strategies and tactics are suspicious; indeed, most of them take place in established democracies. 29 Hence, we do not suggest that observing a few of these tactics is suspicious. But we do suggest that if we observe captors routinely employing tactics from all four strategies, a country is under threat of state capture.
Strategies of State Capture in Hungary and North Macedonia
To highlight the analytical value of the framework and illustrate how the four strategies operate, we present the examples of Fidesz in Hungary and VMRO-DPMNE in North Macedonia. Our two cases share contextual similarities which made state capture unexpected and unforeseen, yet the triggers and ultimate outcomes differ in ways that prevent us from fitting our framework to the cases. In terms of similarities, in the mid-2000s, experts considered both countries on the path to becoming successful post-communist democracies. Additionally, during the regime change, elites designed the two political systems with the intention of avoiding future state monopolization.
Moreover, Hungary is a parliamentary republic headed by a prime minister. To ensure that no party could reshape the political system alone, the 1989 Constitution required a two-thirds majority to pass laws affecting freedom of speech, electoral rules, parliamentary procedures, or the law enforcement. 30 In addition, until 2011, Hungary had a proportional representation system that fostered diverse political representation. 31 North Macedonia has a semi-presidential system, with a popular election for the president. The 2001 Ohrid Framework Agreement established ethnic power-sharing arrangements to give greater political voice to the Albanian minority, and in 2002, the country adopted a closed-list proportional electoral system. Consequently, governing coalitions have consistently included one predominantly Macedonian party and one Albanian party. 32 North Macedonia’s constitution also requires a two-thirds majority to pass amendments and a “double-majority”—a majority of all parliamentarians plus a majority of parliamentarians representing Albanian and other ethnic minorities—to pass legislation addressing culture and language policies or the composition of state bodies. Despite their consensual political institutions, both VMRO-DPMNE and Fidesz managed to engineer large legislative victories and outright legislative majorities as they intensified efforts to capture the state. Their relative organizational and electoral strength compared to their coalition partners enabled the captors to co-opt their partners and pursue the four strategies virtually unimpeded.
The cases vary in their triggers and final outcomes, demonstrating the generalizability of our framework across different political contexts. Fidesz and VMRO-DPMNE were both in government from 1998 to 2002 and lost their immediate reelection bid before coming back into power in 2006 and 2010, respectively. However, the parties launched their state capture campaigns at markedly different points in their political trajectories. In contrast to VMRO-DPMNE, which began to engage in state capture processes once it was securely back in office, Fidesz started while still in opposition. 33 These different trajectories suggest that the trigger for Fidesz was losing power in an election, whereas for VMRO-DPMNE, the triggers were two crises: the name dispute with Greece and the 2008 financial crisis. The parties continuously applied the first three strategies as the political context facilitated their deployment. Once the parties gained a legislative majority, they deployed the fourth strategy. And whereas VMRO-DPMNE left office in 2017 following the fallout from its wiretapping scandal, Fidesz remains in power. North Macedonia is therefore no longer viewed as an example of active capture. 34
Recent academic research and policy analyses concede that both parties captured their respective states. In Hungary, Fidesz returned to power with a two-thirds majority in 2010. Since then, Fidesz has successfully altered the power constellation of the economy and surrounded itself with major economic players. 35 The party also gained control over key political institutions, thus threatening judicial and media independence, and jeopardizing public procurement competition, to name a few examples. 36 As Krekó and Enyedi argue, “Orbán and his party not only keep a firm grip on the legislative and executive branches, but also dominate virtually all spheres of social life, including commerce, education, the arts, churches, and even sports.” 37
VMRO-DPMNE launched its state capture campaign in 2008, following the botched NATO accession of North Macedonia, due to the name dispute with Greece.
38
Already the main governing party, VMRO-DPMNE, nevertheless called for early parliamentary elections three months later, where they won an absolute parliamentary majority, gaining 18 additional parliamentary seats. Over the next years, VMRO-DPMNE consolidated power until 2015, when leaked wiretaps exposed the full extent of state capture. The wiretapping scandal revealed that the government illegally spied on approximately 20,000 individuals from the opposition, the media, civil society, ambassadors, along with VMRO-DPMNE members, and its coalition partner: The massive surveillance, from at least 2010 to 2014, seems to have targeted thousands, including nearly all top opposition and government officials, as well as ambassadors and media figures. The fraction of published wiretaps focuses on what appear to be conversations of senior government persons plotting to subvert elections, manipulating courts, controlling a nominally independent press and punishing enemies. Many who should be responsible for dealing with apparent illegalities are themselves implicated.
39
The taped conversations prove that VMRO-DPMNE captured major state and nonstate actors, including big businesses, media outlets, and even academia. The following year, the European Union (EU) noted that independent regulatory, supervisory, and advisory bodies were unable to function proactively, effectively, and free from political pressure, leading to limited oversight of the executive. 40
How Fidesz and VMRO-DPMNE Captured their States
Fidesz and VMRO-DPMNE navigated their way through the political landscape by (1) exploiting crises, (2) deactivating controls, (3) milking cash-cows, and (4) manipulating political institutions. To illustrate how the two parties implemented the four strategies, accompanying tactics, and accrued the benefits, here we sketch out how both captors handled major political events in each country, selected on the basis of their importance and data availability. A critical reader may have concerns that our selection of events and sources are biased. To assuage these concerns, we reiterate that the purpose of our article is to conceptualize the actions—including broad strategies and operational tactics—that parties use to capture states, rather than to conduct formal hypothesis testing. We therefore present only a small number of events to illustrate in enough detail how a political party implements each strategy. Adding more events would compromise the analytical quality of the entire manuscript. The selection of sources for these events is based on whether they include relevant information for our conceptual framework: the main target group for each strategy, the sequence of tactics, and whether the capturing party received any direct benefits. The cases of Fidesz and VMRO-DPMNE therefore provide a glimpse of how captors skillfully implement these strategies to capture the state.
Strategy 1: Crisis Exploitation
Fidesz
Fidesz shows an exceptional ability to exploit crises. While in the opposition, the party amplified the Őszödi-speech scandal involving then-Prime Minister Gyurcsány of the Hungarian Socialist Party to delegitimize the government. 41 In May 2006, the recently reelected prime minister gave a highly critical speech at a private party meeting. He admitted that the party had lied during the reelection campaign and warned that they would now have to clean up their act. In September, parts of the speech leaked to the press and were published. Fidesz, the main opposition party, opportunistically framed the situation as a national crisis. Some experts suggest that Orbán knew about the existence of the tapes before they were published and had used the summer to build up to their release, for example, by hinting that any government that admitted to grave mistakes has lost its right to rule. 42
After the tapes leaked, Fidesz ensured that the issue dominated public discourse. For example, the party called a no-confidence vote on Gyurcsány, left the parliament when the prime minister spoke, and Orbán gave speeches to incite public criticism. 43 Some even blame Fidesz’s actions for inciting violent riots in the autumn of 2006. 44 Meanwhile, Fidesz also used powerful rhetoric to present itself as the only viable alternative against an illegitimate and corrupt government that had lied to its citizens. Ultimately, the government’s popularity dropped drastically, while Fidesz strengthened its position in parliament and among voters. 45
While in office, Fidesz’s reaction to the refugee crisis in 2015 illustrates how captors exploit an international emergency to divert the public’s attention away from internal scandals. Although Fidesz won a two-thirds majority in the 2014 parliamentary elections (with a junior coalition partner), they soon faced widespread criticism from several sides and a drop in popularity. 46 Coincidently, masses of refugees gathered at Hungary’s borders as the European refugee crisis peaked. Orbán used the situation to alarm Hungarians, stressing that unless stopped, refugees would overrun Hungary, introduce terrorism, and destroy Hungary’s Christian values. The public’s attention shifted away from their dissatisfaction with the government; instead, they rallied around Fidesz and its fight against international and domestic critics. The support enabled Fidesz to pass legislation that granted the government greater discretion to invoke a state of emergency and gave the police and military extensive powers to violate civil liberties. 47 These developments supported the other strategies, providing Fidesz with additional legislative tools to intimidate critics.
VMRO-DPMNE
VMRO-DPMNE also exploited and escalated national crises in ways that increased its electoral support and provided cover for the other strategies. In 2008 and 2009, North Macedonia faced two separate crises. The first was a diplomatic crisis with Greece, which climaxed at the 2008 NATO summit where Greece vetoed the country’s membership. Because Macedonia also refers to a region within Greece, the Greek government claimed that the name threatened the territorial sovereignty of their state. 48 The name dispute thus derailed progress toward NATO and EU membership. It occurred shortly before the global financial crisis hit North Macedonia and caused a major recession. The events therefore endangered VMRO-DPMNE’s public support.
In response, VMRO-DPMNE exploited the crises in ways that exacerbated the situation for ordinary Macedonians while improving the party’s public support. Instead of negotiating with the Greek government, VMRO-DPMNE framed the dispute as an assault on Macedonian national identity and its existence as a state. The framing tactic distracted the public from being excluded from the EU and NATO, and the recession, while enabling the party to intensify the diplomatic rift with Greece. Ultimately, VMRO-DPMNE benefited from a rally-around-the-flag effect, picking up twenty-six additional seats in the 2008 snap elections following the NATO fiasco, which gave it an absolute majority in parliament.
Bolstered by its win, the VMRO-DPMNE government ignored the advice of economists who proposed to fund major infrastructure and public work programs to provide large-scale employment and stimulate the economy. 49 Instead, VMRO-DPMNE embarked on a nationalistic process of “antiquization” by establishing linkage between contemporary ethnic Macedonians and North Macedonia’s ancient past. 50 Embodied by the infamous Skopje 2014 project, the government spent approximately 680 million euros to construct lavish monuments, government buildings, and various cultural structures and symbols. Consequently, Skopje 2014 intensified the name dispute and became a hotbed of illicit activities that favored political insiders. 51 Yet VMRO-DPMNE’s tactics were successful in mobilizing public support while distracting the public from massive corruption and foreign policy failure. They also provided VMRO-DPMNE with opportunities to implement the other strategies, including expanding their control over cash-cows during the Skopje 2014 project.
Strategy 2: Deactivating Controls
Fidesz
Orbán showed the first signs of systematically targeting legislative and government checks during Fidesz’s first term in power. Fidesz has shown such extensive proclivities in this area that we cannot even discuss a fraction of examples. Among the most controversial uses of party patronage are the appointments of the chief public prosecutor, the heads of the constitutional court, and the Hungarian tax authority, along with the presidents of the national bank and the state. 52 When Fidesz returned to power in 2010, their efforts to fill the state administration with loyalists intensified. Starting from the top and moving downward, the party purged nonpartisan staff from the public administration. 53
While businesses close to Fidesz entered the media sector in the nineties, Fidesz expanded efforts to control the media after losing their 2002 reelection bid. By 2016, six years after Fidesz returned to power, their hold over the media took on such proportions that it became difficult to speak of media freedom in Hungary. Apart from relying on positive coverage from media outlets affiliated with pro-Fidesz businesses, Fidesz also started to intimidate and harass critical media outlets, forcing them to either closedown or lose control to Fidesz’s allies. By 2018, most media outlets were captured. 54 Ultimately, the subversion of controls silenced critical voices, limited the opposition’s ability to mobilize against Fidesz, and reduced the risk of criminal investigations and prosecution of loyalists. Additionally, deactivating Hungary’s oversight bodies enabled Fidesz to more actively pursue the other strategies.
VMRO-DPMNE
VMRO-DPMNE similarly deactivated controls to maintain impunity for loyalists involved in criminal activities and to delegitimize critical voices. In 2008, VMRO-DPMNE began to use its legislative majority to rig the judiciary and anticorruption agencies by appointing party loyalists to key positions. By 2010, the European Commission (EC) warned about potentially illegal dismissals in the State Audit Office and among judges and prosecutors investigating corruption, and the undue influence of the minister of justice (a VMRO-DPMNE appointee) on the Judicial Council and Council of Public Prosecutors. 55
In 2015, the main opposition party leaked wiretapped recordings that revealed VMRO-DPMNE’s numerous crimes. International condemnation compelled the party to appoint an independent special prosecutor to investigate VMRO-DPMNE’s activities. Nevertheless, VMRO-DPMNE tried to undermine the legitimacy of the Special Prosecutor’s Office, repeatedly questioning the agency’s independence and accusing it of working for the opposition. The party’s control over the judiciary became obvious when various courts, judges, and prosecutors were uncooperative with the special prosecutor’s requests for detentions and search warrants. 56 The obstruction climaxed in 2016 when President Ivanov issued pardons for fifty-six individuals—mostly top VMRO-DPMNE officials, including the prime minister and the former ministers of transport and the interior—who had been indicted for electoral fraud and corruption charges. 57 Although the pardons were illegal, most state institutions remained loyal to the party and accepted them. For example, the constitutional court backed Ivanov’s pardons by making electoral fraud a pardonable office. Similarly, many investigated individuals were released from prison or detention, and the special prosecutor’s investigations temporarily stopped. 58 However, mass protests and international diplomatic pressure forced President Ivanov to revoke the pardons and allow the special prosecutor’s work to resume.
The party also prevented media and civil society organizations from performing their role as watchdogs. Most shocking was the 2010 raid on A1 TV, a government-critical television station, whose owner and fourteen employees were arrested. 59 Such open harassment resulted in media self-censorship for fear of government retaliation, often through defamation and libel suits that imposed high fines on critical journalists. 60
Strategy 3: Milking Cash-Cows
Fidesz
For years, Fidesz’s main cash-cow was the public procurement process connected to various EU funds. By joining the EU in 2004, Hungary became eligible to receive large EU funds largely aimed at improving the country’s ailing infrastructure. 61 But instead of ensuring a fair public procurement procedure to distribute the funds, Orbán readily admitted to favoritism. 62 Investigative journalists calculated that between 2010 and 2014, the main recipients of these funds were companies connected to three men: Simicska, Mészáros, and Tiborcz—a long-term friend, the mayor of Orbán’s hometown, and Orbán’s son-in-law, respectively. Although difficult to prove conclusively that the companies’ financial success benefited Fidesz, all three individuals have supported Orbán and Fidesz in various forms. 63
Another example of milking a lucrative cash-cow is the case of the national tobacco shops. In 2011, Fidesz created a state monopoly on the sale of tobacco, renationalizing the market and then granting concessions via public tenders to operate small tobacco shops. In 2013, the government ran the first round of tenders. 64 The entire process soon came under fire. The opposition and even a few party-supporters accused Fidesz of unfairly favoring their supporters. 65
VMRO-DPMNE
The wiretapping scandal and special prosecutor’s investigations revealed the breadth of VMRO-DPMNE’s strategy to milk cash-cows for financial gain and economic influence. Consequently, several party officials who illegally manipulated procurement contracts were convicted. This includes the former Prime Minister Gruevski, whom courts found guilty of illegally purchasing a bullet-proof Mercedes limousine. Courts also convicted the former interior minister and her assistant for favoring a Mercedes dealer during the tender. 66
The wiretaps reveal numerous schemes to milk cash-cows. By controlling the distribution of government contracts, the party ensured that their business allies would win contracts. This included encouraging them to form consortia so they would not lose out on tenders. In exchange, the firms would split their profits with the party leadership. The head of the Macedonian power company Elem acted as an intermediary, collecting the politicians’ share of the profits and transferring them to the secretary general of the government. One such prominent example of Elem’s involvement is Operation Tariff, which involved software acquisition for Elem that was worth four million euros and involved seven government officials. These officials awarded the contract to a consortium that failed to provide legally required documentation. 67
Strategy 4: Manipulating Political Institutions
Fidesz
Fidesz employed all three groups of tactics to manipulate Hungary’s political system while in office, effectively reshaping political institutions in their favor at the expense of potential challengers. Under the guise of introducing necessary reforms, the party amended legislative procedures on several occasions, disabling oversight over government activities while strengthening government control. An early example was to reduce weekly parliamentary sessions to once every three weeks. This procedural change strengthened Fidesz’s control over the legislative agenda and reduced parliamentary oversight. During their second term, Fidesz introduced a “speedier” legislative process, drastically decreasing the time between the introduction and adoption of a bill. 68 Both events showcase how Fidesz impaired parliament’s ability to check government activities and the content of new laws.
When Fidesz came back to office with a qualified majority, it had parliamentary support to aggressively reshape the legislative framework. Within two years, the party curtailed constitutional court powers, undermined media independence, and manipulated the electoral system. Take the latter example, where Fidesz followed the adage of “divide and conquer” by introducing legal hurdles for opposition parties to mobilize supporters and coordinate their campaigns. Ultimately, the changes institutionalized a strong incumbent bias. 69
Fidesz also extensively employed the third group of tactics, that is, consolidating power within the state administration. For example, Fidesz altered selection procedures for constitutional court judges by giving appointment powers to the Fidesz-controlled parliament. The party also targeted less conspicuous areas, for example, centralizing the education system by creating a new supervisory body and authorizing the education ministry to appoint the heads of schools. 70
VMRO-DPMNE
Following its reelection in 2008, VMRO-DPMNE strategically used its legislative majority to co-opt its Albanian coalition partner and manipulate the political system. The party aggressively took control of the legislative agenda and formed a coalition with the largest Albanian party, leaving them just three seats shy of a two-thirds majority. Next, VMRO-DPMNE took advantage of the opposition’s boycott of parliament in 2011 and 2014. In 2011 alone, the government rushed through approximately 200 laws during the four months of the boycott, including a controversial law on lustration that required the vetting of journalists, professors, and civil society activists for ties to the former communist secret service. The government could so replace the sitting president of the constitutional court with a former advisor to the prime minister. During that time, only two months before early parliamentary elections, VMRO-DPMNE also amended the country’s electoral code by a narrow vote margin. One of these amendments added three parliamentary seats, allocated to representatives of the Macedonian diaspora. VMRO-DPMNE candidates went on to win these seats. 71
This pattern of legislative manipulation and agenda-control persisted throughout VMRO-DPMNE’s rule. And as the special prosecution’s investigation revealed, the former prime minister and several top government officials from VMRO-DPMNE participated in electoral fraud during the 2013 local elections. 72 VMRO-DPMNE manipulated the elections to increase its electoral share of mayors and municipal councilors across the country.
Conclusion
To answer the question posed in the title, we developed a conceptual framework to identify a political party’s repertoire of actions. We synthesized theoretical and empirical research on comparative democratization, electoral behavior, state capture, and public crisis management. Our approach is therefore akin to solving a jigsaw puzzle with pieces missorted into several literature boxes. Armed with a framework of how political parties capture young democracies, we then explored the cases of Fidesz in Hungary and VMRO-DPMNE in North Macedonia. Our framework thus systematized how the actions of these two parties resulted in state capture.
In contrast to traditional research, we worked our way backward from the outcome in question, which enabled us to identify the main pathways through which political actors capture a state. While the article is largely conceptual, we demonstrated the analytical value of our framework by applying it to two paradigmatic cases. In addition to sketching out how each party captured the state, this article provides insight into the strategies that democratically elected politicians use to subvert democracies from within. 73 Specifically, we propose that political parties capture young democracies by (1) exploiting crises to advance their political agendas, (2) deactivating controls to constrain public oversight, (3) milking cash-cows to generate additional income, and (4) manipulating political institutions to institutionalize advantages. To deploy these strategies, political actors use specific tactics, depending on the political context and their available resources.
As Fidesz and VMRO-DPMNE show, both parties implemented each strategy to capture their states. First, they both exploited national crises—either real or manufactured—to bolster public support, divert negative attention away, push through their policy agendas, and delegitimize political opponents. Both employed the second strategy of deactivating controls by purging nonloyalists and replacing them with hand-picked appointees, cutting resources to oversight bodies, and undermining critical voices. In this manner, they effectively reduced the risk of criminal prosecutions for party loyalists while sidelining critics. For the third strategy, the parties milked cash-cows by establishing discretionary control over public resource distribution and converting resources into usable assets. Moreover, both parties developed elaborate schemes to rig public procurement contracts and monopolize control over segments of the economy. Finally, they used electoral majorities to manipulate political institutions. By subverting the legislative framework—altering the electoral system or the constitution—and consolidating their power over the state administration, the parties reshaped the entire political system to their advantage.
Our sketch of how Fidesz and VMRO-DPMNE employed the four strategies and associated tactics provides two valuable insights. First, the cases reveal that the four state capture strategies operate interdependently. Only by deploying all four strategies can captors cover the range of targets and domains needed to cement control over state institutions and subvert their effectiveness for the captors’ benefit. Second, our framework is not limited to particular actors, sectors, institutions, or triggers. The framework shows that captor parties not only collude with a variety of actors but also silence critics across governmental and nongovernmental institutions. Depending on the context and captor’s available resources (e.g., parliamentary strength, popular support, competitive environment, and finance), political actors may deploy any of these strategies, sometimes individually, other times simultaneously, and occasionally they may repeat the same strategy. Ultimately, the strategies are general enough to be implemented across a variety of political contexts by any major political party. What differs are the specific tactics employed.
To illustrate these two insights, imagine a major opposition party that has just successfully exploited a scandal surrounding the incumbent. Apart from attracting more supporters, the party is in a stronger position to push their political agenda and influence political appointments to key positions. In this manner, they can deactivate key controls, including the public prosecutor and the highest courts, and gain access to cash-cows. For instance, by placing party loyalists to head the public procurement process and aligning with intermediaries who convert resources into assets, the hypothetical party can now milk the cash-cow. The derived benefits embolden them to repeat the cycle of exploiting crises, deactivating controls, and milking cash-cows. If unconstrained, the party will eventually gain a majority and implement the fourth strategy—manipulating the political system in their favor—by consolidating power over the state administration and subverting the legal framework.
What can we gain from applying the framework to future and past research? For one, the framework contributes toward a comprehensive theory of state capture by identifying the underlying mechanisms that connect a variety of inputs (such as party features or the competitive environment) to the outcome of state capture. More broadly, it contributes to a novel, agent-based theory of democratic backsliding. 74 The framework may also act as an early warning system for policy organizations by laying out concrete steps captors may take to subvert a democracy. Although all political parties employ some of the tactics mentioned here, the framework allows us to examine whether a political party has employed tactics from several strategies. Moreover, our framework is generalizable not only to contemporary cases but also to post-communist transition that began three decades ago. For example, parties in Bulgaria, Romania, and Slovakia engaged in at least some of the four strategies soon after the collapse of communism, which set them on an illiberal path during the 1990s. 75 While Fidesz and VMRO-DPMNE began to capture their states more recently and more skillfully, the four strategies have a three-decade history in Eastern Europe.
Finally, what are some implications that arise from our analytical framework? Rather than testing a particular hypothesis, we contribute to recent works on state capture and democratic subversion by identifying new research questions. What resources does a political party need and under what conditions? Do the state capture strategies vary between parties from established and young democracies? What could international actors, such as the EU, do to counter the rising threat of state capture? And finally, at what point is the threat of state capture averted? In sum, the four complementary strategies identified in this paper provide useful guidelines for future research that develops a full causal theory of state capture in established and young democracies alike.
Footnotes
Acknowledgements
Earlier versions of this article were presented at the 2018 Annual Convention of the Association for Slavic, East European and Eurasian Studies in Boston and the 2019 International Political Science Association Colloquium in Sarajevo. We thank conference participants for their invaluable feedback. The authors also thank the editors, two anonymous reviewers, Timofey Agarin, Abdylmenaf Bexheti, Lenka Buštíková, Misa Popovic, Graeme Robertson, Arturas Rozenas, and Milada Vachudova for their helpful comments.
